| File name: | beacon.exe |
| Full analysis: | https://app.any.run/tasks/4d031ade-f5ab-4524-9b1f-2dd32e3fb21e |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 17:12:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 15 sections |
| MD5: | B6DA6E98198299498ABE1B10EAEC5F74 |
| SHA1: | B757D7C52B39633D40519F6092ECBDF5C37C1150 |
| SHA256: | F108A0526F6C52EF8C11806839846E85D5BA2984578E2403CD8F7EAECF828018 |
| SSDEEP: | 98304:KN3od5CrxF/mytwEqNaOhEO1TP6qQNrZSCcrBG9kvQnSTX22FaAdUN0bkc9CMtsh:hl/T1W |
MALICIOUS
Changes the autorun value in the registry
- beacon.exe (PID: 7452)
SUSPICIOUS
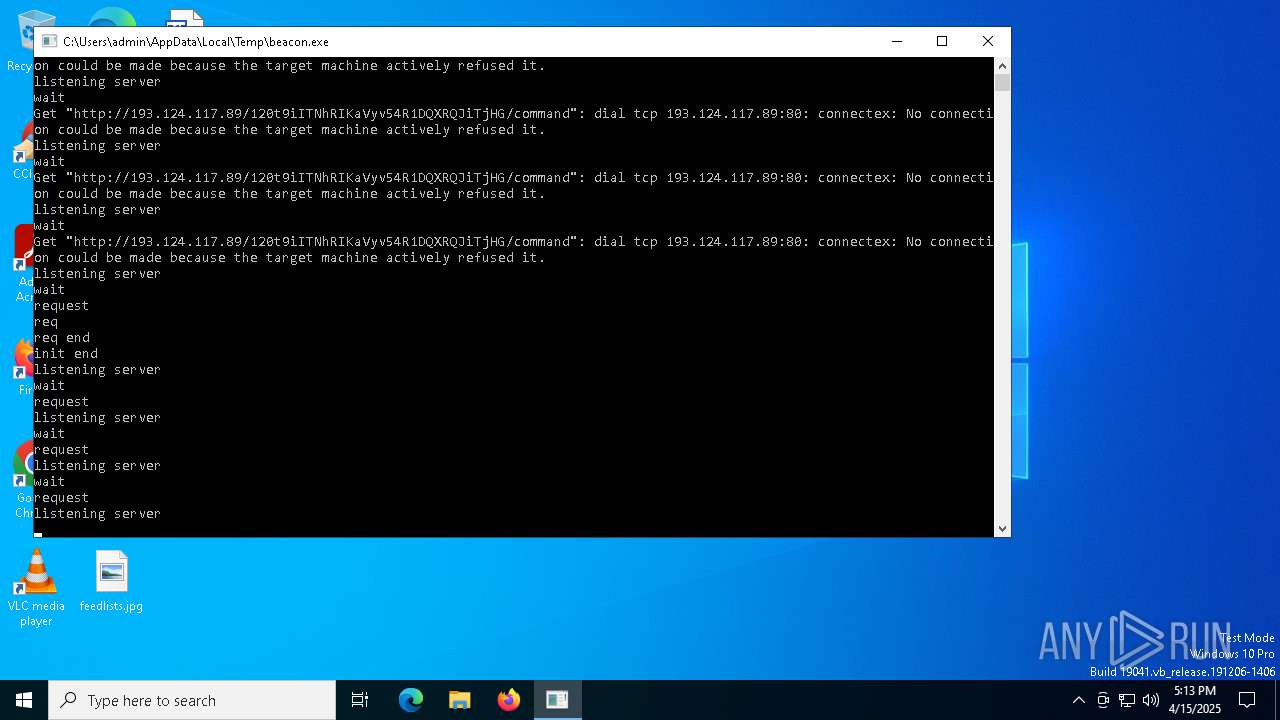
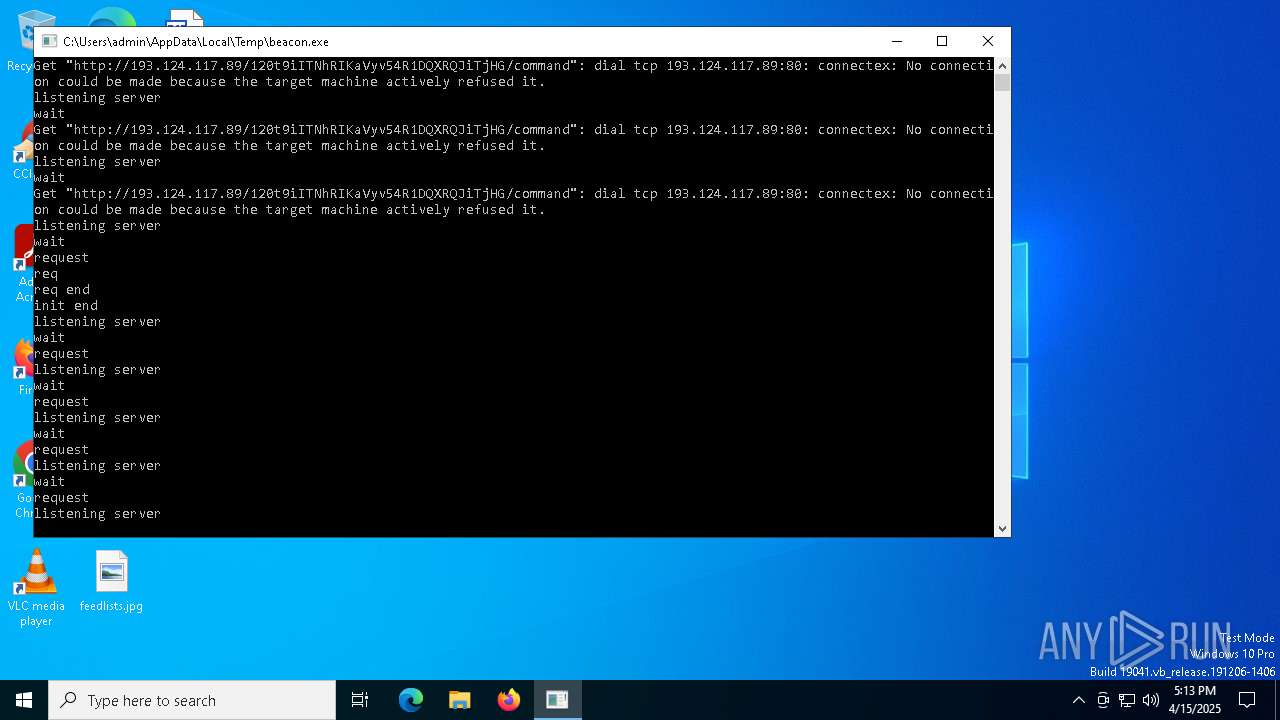
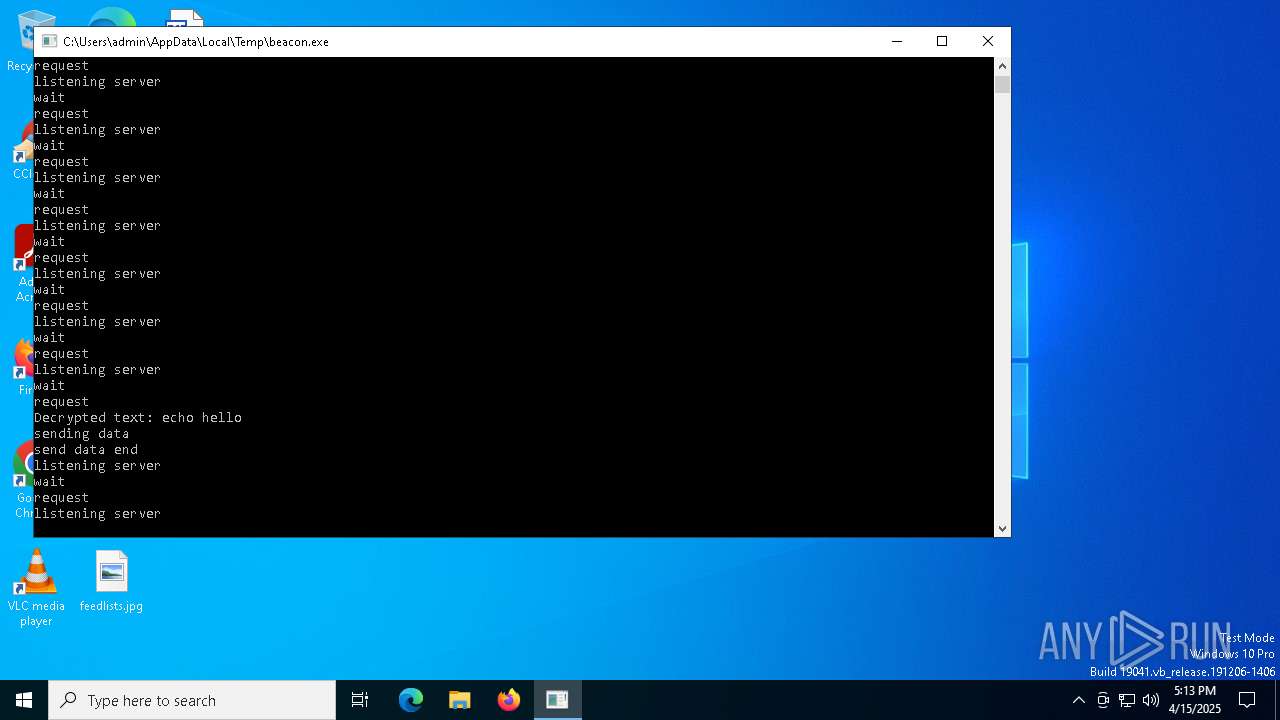
Starts CMD.EXE for commands execution
- beacon.exe (PID: 7452)
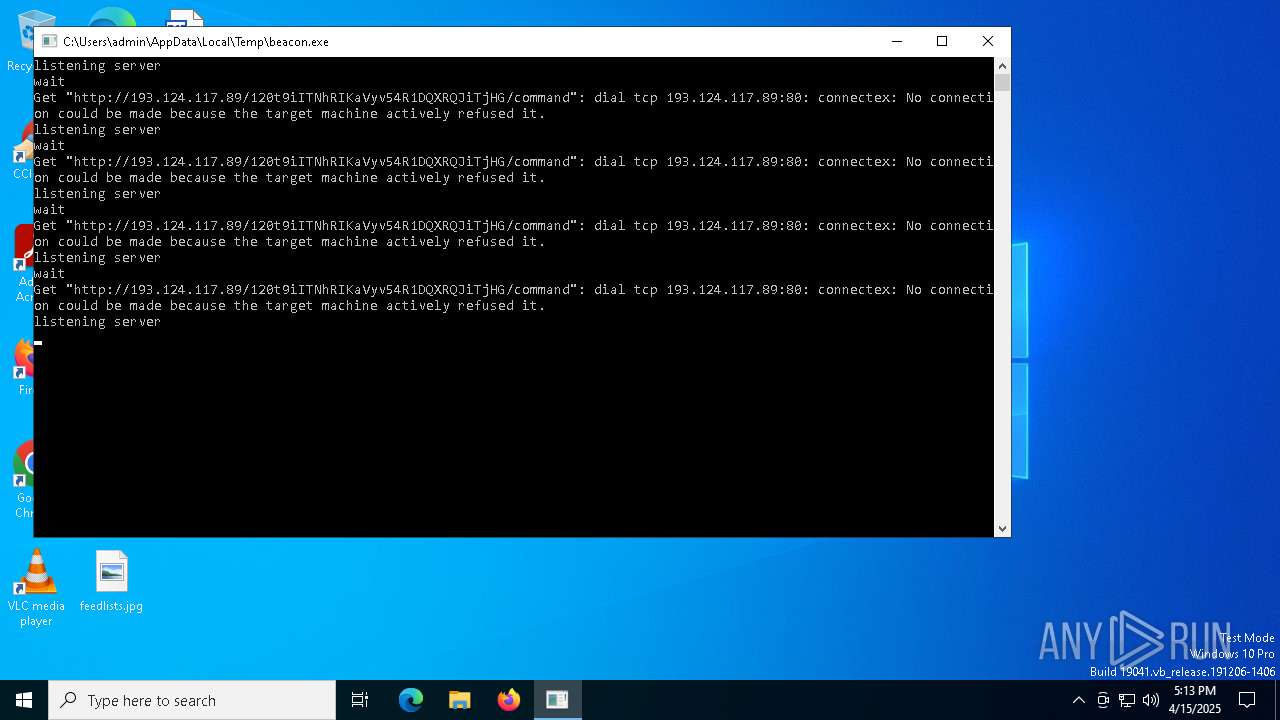
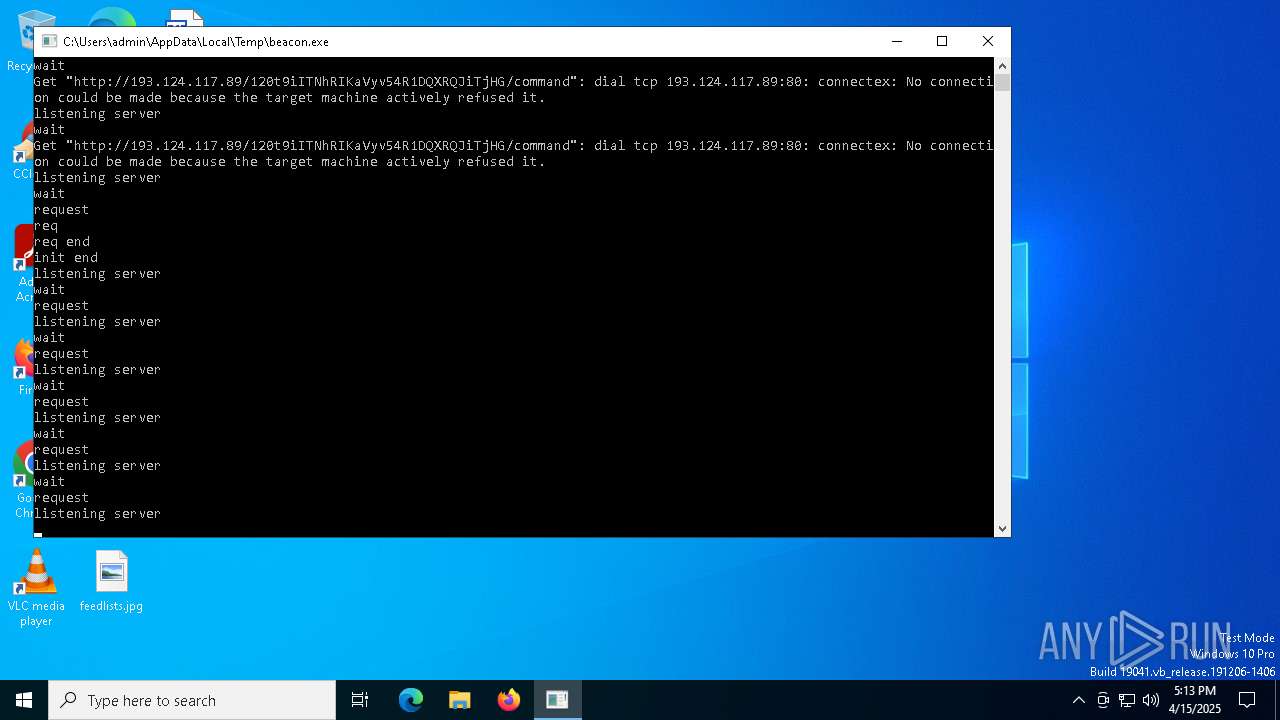
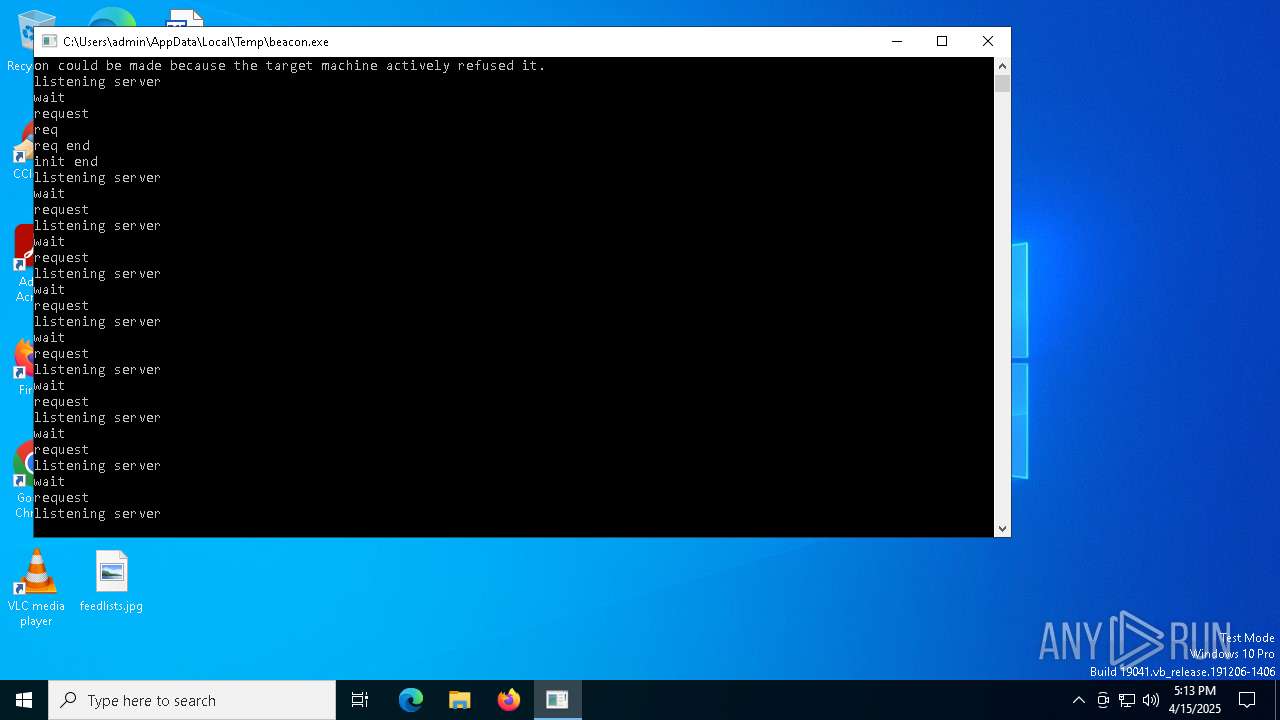
Connects to the server without a host name
- beacon.exe (PID: 7452)
INFO
Detects GO elliptic curve encryption (YARA)
- beacon.exe (PID: 7452)
Checks supported languages
- beacon.exe (PID: 7452)
Reads the computer name
- beacon.exe (PID: 7452)
Application based on Golang
- beacon.exe (PID: 7452)
Drops encrypted JS script (Microsoft Script Encoder)
- beacon.exe (PID: 7452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2659840 |
| InitializedDataSize: | 257024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x74500 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
Total processes
127
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7452 | "C:\Users\admin\AppData\Local\Temp\beacon.exe" | C:\Users\admin\AppData\Local\Temp\beacon.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | beacon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7932 | cmd /C "echo hello" | C:\Windows\System32\cmd.exe | — | beacon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7960 | cmd /C "dir " | C:\Windows\System32\cmd.exe | — | beacon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7996 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
313
Read events
312
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7452) beacon.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Discord |
Value: C:\Users\admin\AppData\Local\Temp\beacon.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
40
DNS requests
11
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
7452 | beacon.exe | POST | 201 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/connect | RU | binary | 18 b | unknown |
7776 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
7452 | beacon.exe | GET | 200 | 193.124.117.89:80 | http://193.124.117.89/120t9iITNhRIKaVyv54R1DQXRQJiTjHG/command | RU | text | 4 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7452 | beacon.exe | 193.124.117.89:80 | — | JSC Mediasoft ekspert | RU | unknown |
6544 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7776 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
7776 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7452 | beacon.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7452 | beacon.exe | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
7452 | beacon.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7452 | beacon.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
7452 | beacon.exe | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
7452 | beacon.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7452 | beacon.exe | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
7452 | beacon.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7452 | beacon.exe | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
7452 | beacon.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |