| download: | eset_nod32_antivirus_live_installer.exe |
| Full analysis: | https://app.any.run/tasks/596f61d7-5397-4880-8b25-802cc6b1c08e |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2018, 17:05:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F2AFF288BD91D2424A956F79DFCFDA27 |
| SHA1: | 76C5049B0B5FDCD3EBA6086EBB5C035FF86AE675 |
| SHA256: | F0FF3FE72A4983CFF2C679BB9740D4DC4AC9B09F34D84E8F3BF8A157C5FB8387 |
| SSDEEP: | 98304:Ps5Ru/VIJvoFlonGoVxO2RXF6+iTxtQQx9yX7QqeWBxmP:UiEj7ZXw+iTY0yXMqjbmP |
MALICIOUS
Application was dropped or rewritten from another process
- BootHelper.exe (PID: 3840)
- eset_nod32_antivirus_live_installer.exe (PID: 2544)
- InstHelper.exe (PID: 2124)
- egui.exe (PID: 3036)
- ekrn.exe (PID: 1612)
Loads dropped or rewritten executable
- eset_nod32_antivirus_live_installer.exe (PID: 2544)
- ekrn.exe (PID: 1612)
- InstHelper.exe (PID: 2124)
- egui.exe (PID: 3036)
Changes settings of System certificates
- ekrn.exe (PID: 1612)
SUSPICIOUS
Executable content was dropped or overwritten
- eset_nod32_antivirus_live_installer.exe (PID: 2544)
- eset_nod32_antivirus_live_installer.exe (PID: 3604)
- msiexec.exe (PID: 4064)
- MsiExec.exe (PID: 3880)
- ekrn.exe (PID: 1612)
- MsiExec.exe (PID: 3140)
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 3880)
Creates COM task schedule object
- MsiExec.exe (PID: 3880)
- MsiExec.exe (PID: 3140)
Changes the autorun value in the registry
- msiexec.exe (PID: 4064)
Removes files from Windows directory
- DrvInst.exe (PID: 3404)
- ekrn.exe (PID: 1612)
- DrvInst.exe (PID: 1420)
- DrvInst.exe (PID: 3156)
Creates files in the Windows directory
- DrvInst.exe (PID: 3404)
- DrvInst.exe (PID: 1420)
- DrvInst.exe (PID: 3156)
- ekrn.exe (PID: 1612)
Creates files in the driver directory
- DrvInst.exe (PID: 3404)
- ekrn.exe (PID: 1612)
- DrvInst.exe (PID: 1420)
- DrvInst.exe (PID: 3156)
Creates files in the program directory
- ekrn.exe (PID: 1612)
Creates or modifies windows services
- ekrn.exe (PID: 1612)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3880)
- MsiExec.exe (PID: 3140)
- MsiExec.exe (PID: 1148)
Reads settings of System Certificates
- eset_nod32_antivirus_live_installer.exe (PID: 2544)
- ekrn.exe (PID: 1612)
Dropped object may contain URL's
- eset_nod32_antivirus_live_installer.exe (PID: 3604)
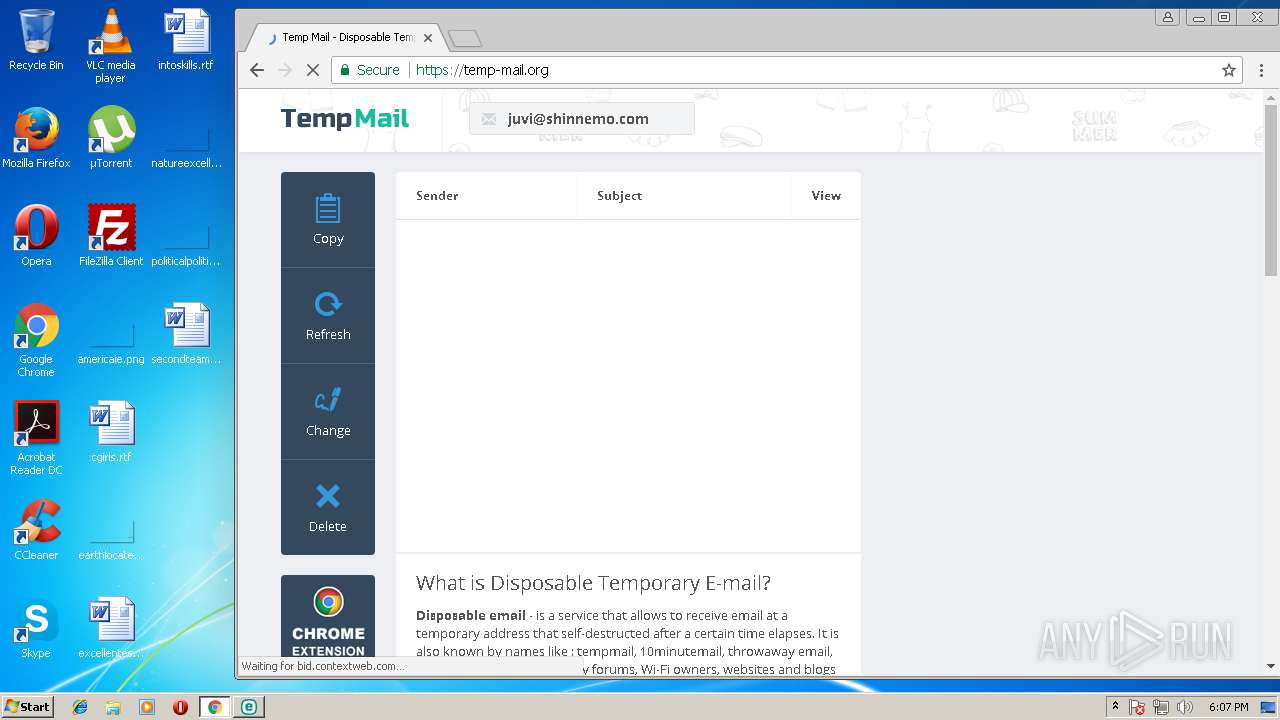
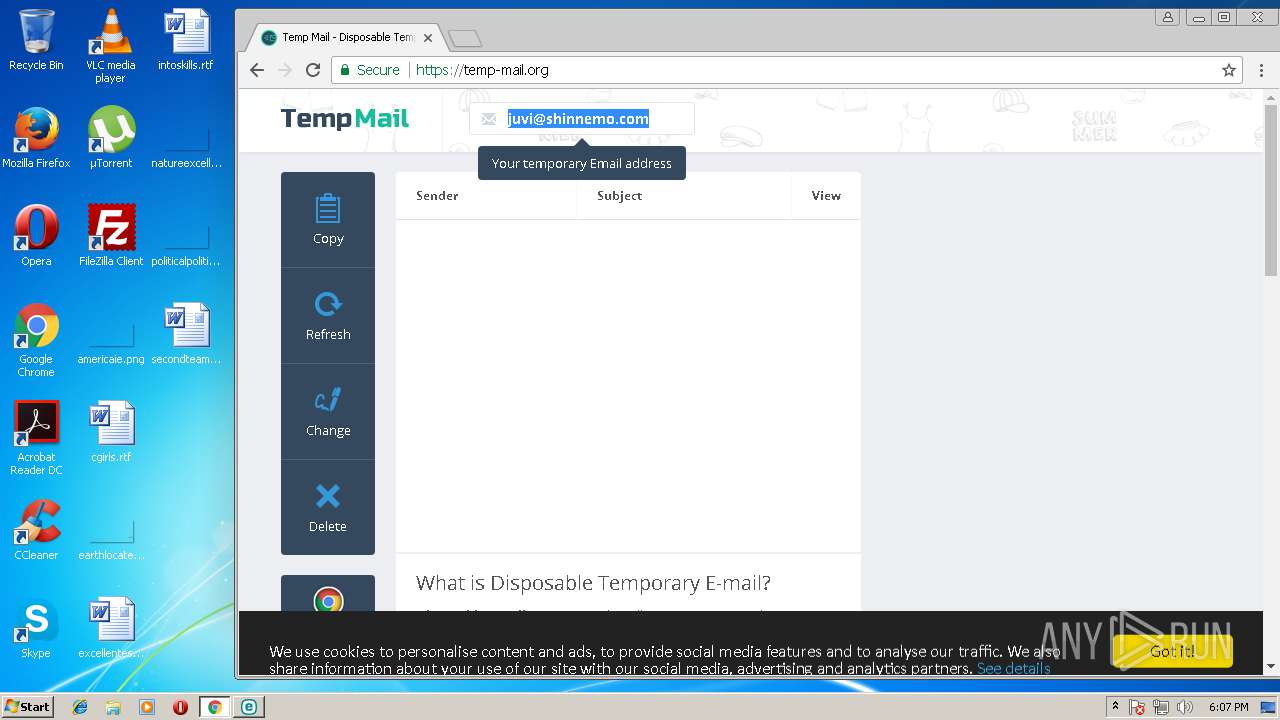
- chrome.exe (PID: 2204)
- eset_nod32_antivirus_live_installer.exe (PID: 2544)
- MsiExec.exe (PID: 3880)
- DrvInst.exe (PID: 3404)
- DrvInst.exe (PID: 1420)
- DrvInst.exe (PID: 3156)
- ekrn.exe (PID: 1612)
- MsiExec.exe (PID: 3140)
- msiexec.exe (PID: 4064)
Application launched itself
- msiexec.exe (PID: 4064)
- chrome.exe (PID: 2204)
Creates or modifies windows services
- msiexec.exe (PID: 4064)
- MsiExec.exe (PID: 3880)
Creates files in the program directory
- MsiExec.exe (PID: 3880)
- msiexec.exe (PID: 4064)
- MsiExec.exe (PID: 3140)
Creates a software uninstall entry
- msiexec.exe (PID: 4064)
- MsiExec.exe (PID: 3880)
Reads Microsoft Office registry keys
- ekrn.exe (PID: 1612)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 1072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
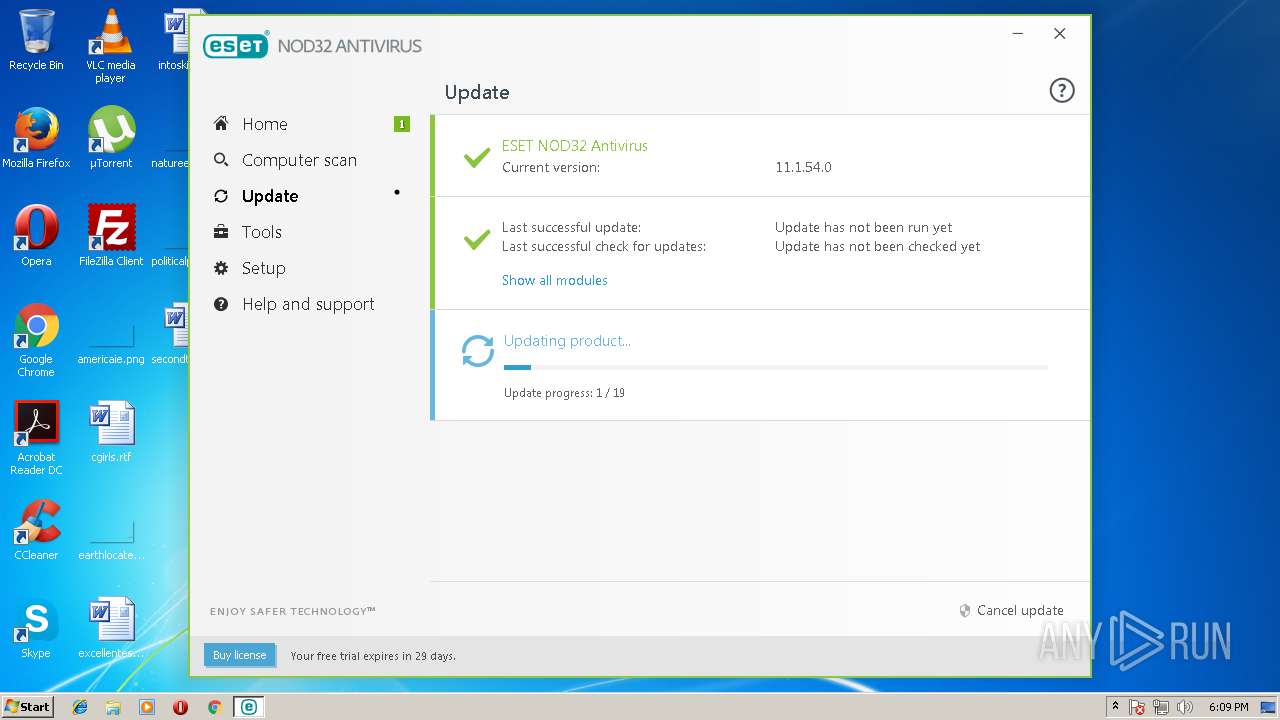
| ProductVersion: | 11.0.26.0 |
|---|---|
| ProductName: | ESET Security |
| OriginalFileName: | Bootstrapper.exe |
| LegalTrademarks: | NOD, NOD32, AMON, ESET are registered trademarks of ESET. |
| LegalCopyright: | Copyright (c) ESET, spol. s r.o. 1992-2018. All rights reserved. |
| InternalName: | Bootstrapper.exe |
| FileVersion: | 10.2.185.0 |
| FileDescription: | ESET Live Installer |
| CompanyName: | ESET |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 11.0.26.0 |
| FileVersionNumber: | 10.2.185.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x5860 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4141056 |
| CodeSize: | 120832 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2018:03:15 11:12:20+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Mar-2018 10:12:20 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ESET |
| FileDescription: | ESET Live Installer |
| FileVersion: | 10.2.185.0 |
| InternalName: | Bootstrapper.exe |
| LegalCopyright: | Copyright (c) ESET, spol. s r.o. 1992-2018. All rights reserved. |
| LegalTrademarks: | NOD, NOD32, AMON, ESET are registered trademarks of ESET. |
| OriginalFilename: | Bootstrapper.exe |
| ProductName: | ESET Security |
| ProductVersion: | 11.0.26.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Mar-2018 10:12:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001D63B | 0x0001D800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61408 |
.rdata | 0x0001F000 | 0x00008F3C | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08267 |
.data | 0x00028000 | 0x0000161C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.62368 |
.rsrc | 0x0002A000 | 0x003E79CC | 0x003E7A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97672 |
.reloc | 0x00412000 | 0x0000186C | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.43798 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.25666 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.66703 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.04319 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.37535 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.81116 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.79 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
102 | 2.91902 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
1000 | 5.05738 | 4611 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
1010 | 7.41713 | 5095 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
Total processes
67
Monitored processes
26
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe" --session-id=P1neO9WreCcU9mqyNtRKAAIx2WH55je80h3fHncf | C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 2 Version: 23.129.0 Modules
| |||||||||||||||
| 1148 | C:\Windows\system32\MsiExec.exe -Embedding F58EA19FBB538C2757D00EF43142C046 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1659944489745115541,12829421662937545022,131072 --service-pipe-token=71D17BA936054C21ED75C7B20CBE88C7 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=71D17BA936054C21ED75C7B20CBE88C7 --renderer-client-id=4 --mojo-platform-channel-handle=1608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1420 | DrvInst.exe "4" "8" "C:\Windows\TEMP\{5c8e63bd-2d0d-6731-ea7d-2f7479dd5209}\eamonm.inf" "0" "6d14d0413" "0000031C" "Service-0x0-3e7$\Default" "000003D0" "208" "C:\Program Files\ESET\ESET Security\Drivers\eamonm" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1659944489745115541,12829421662937545022,131072 --service-pipe-token=F397738E3758274AF31E76E1B7EC728C --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=F397738E3758274AF31E76E1B7EC728C --renderer-client-id=6 --mojo-platform-channel-handle=3264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\ESET\ESET Security\ekrn.exe" | C:\Program Files\ESET\ESET Security\ekrn.exe | services.exe | ||||||||||||
User: SYSTEM Company: ESET Integrity Level: SYSTEM Description: ESET Service Exit code: 0 Version: 10.3.403.0 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1659944489745115541,12829421662937545022,131072 --service-pipe-token=3424601DB240B0D01AC4F1DE40F99F51 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=3424601DB240B0D01AC4F1DE40F99F51 --renderer-client-id=8 --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1659944489745115541,12829421662937545022,131072 --service-pipe-token=9D836CF87121B5D4073EB8164D6F9577 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=9D836CF87121B5D4073EB8164D6F9577 --renderer-client-id=5 --mojo-platform-channel-handle=3240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\eset.temp\{02D83BBE-F95B-0B05-DB14-09CDDD2A52F5}\InstHelper.exe" -ci "C:\Users\admin\AppData\Local\Temp\eset.temp\{02D83BBE-F95B-0B05-DB14-09CDDD2A52F5}\_InstData.xml" | C:\Users\admin\AppData\Local\Temp\eset.temp\{02D83BBE-F95B-0B05-DB14-09CDDD2A52F5}\InstHelper.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: ESET Integrity Level: SYSTEM Description: ESET Install Helper Exit code: 0 Version: 10.3.403.0 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
2 976
Read events
1 744
Write events
1 196
Delete events
36
Modification events
| (PID) Process: | (3604) eset_nod32_antivirus_live_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3604) eset_nod32_antivirus_live_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2544) eset_nod32_antivirus_live_installer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2204-13175543212472687 |
Value: 259 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3708-13168704147815429 |
Value: 0 | |||
Executable files
208
Suspicious files
159
Text files
259
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\sciter-x.dll | executable | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonARE.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\plgSciterBase.dll | executable | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\BootHelper.exe | executable | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonDEU.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonBGR.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonCHT.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonCHS.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonELL.xml | xml | |
MD5:— | SHA256:— | |||
| 2544 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-669A-1A6A-1756-08CD452002F7}\.res\main\CommonCSY.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | eset_nod32_antivirus_live_installer.exe | GET | 302 | 91.228.165.134:80 | http://go.eset.eu:80/detectav?product=eav | SK | html | 238 b | suspicious |
2544 | eset_nod32_antivirus_live_installer.exe | POST | 302 | 91.228.165.134:80 | http://go.eset.eu:80/versioncheckxml | SK | html | 219 b | suspicious |
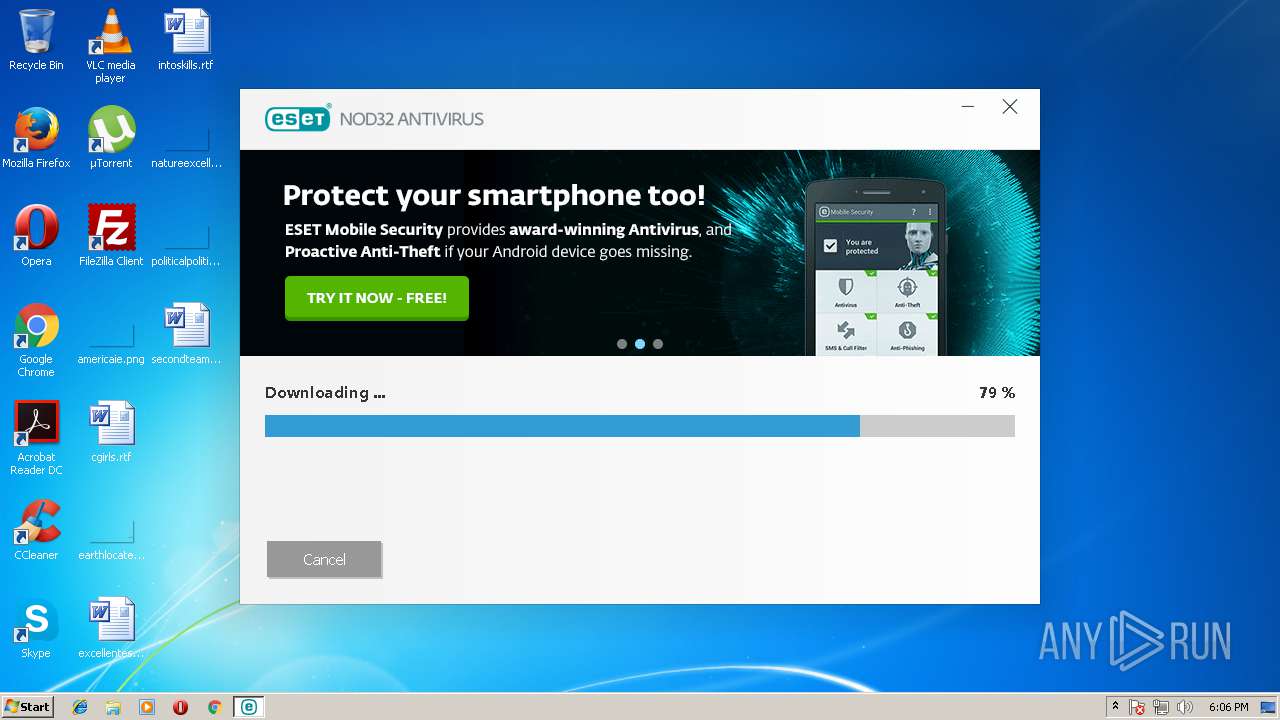
2544 | eset_nod32_antivirus_live_installer.exe | GET | — | 91.228.166.82:80 | http://download.eset.com:80/com/eset/apps/home/eav/windows/v11/11.1.54.0/eav_nt32.msi | SK | — | — | suspicious |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 301 | 91.228.167.30:80 | http://banner.eset.com:80/banner-v2?product=eav&version=11&type=li&lng=1033 | SK | html | 293 b | whitelisted |
2544 | eset_nod32_antivirus_live_installer.exe | POST | 200 | 91.228.165.81:80 | http://versioncheck.eset.com:80/vcheck | SK | xml | 10.0 Kb | whitelisted |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 302 | 91.228.165.134:80 | http://go.eset.eu:80/banner-v2?lng=1033&product=eav&version=11&type=li | SK | html | 268 b | suspicious |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 200 | 91.228.167.30:80 | http://banner.eset.com:80/banner-v2/?product=eav&version=11&type=li&lng=1033 | SK | text | 497 b | whitelisted |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 200 | 91.228.166.82:80 | http://download.eset.com:80/com/eset/tools/installers/av_detector/v1/1.82.0.0/detectavdb_windefend.dat | SK | binary | 179 Kb | suspicious |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 200 | 91.228.166.82:80 | http://download.eset.com:80/special/detectav/detectav.xml | SK | xml | 503 b | suspicious |
2544 | eset_nod32_antivirus_live_installer.exe | GET | 200 | 91.228.167.30:80 | http://banner.eset.com:80/banner-v2/data/images/li/eav/v11/1033/Banner.png | SK | image | 141 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | eset_nod32_antivirus_live_installer.exe | 91.228.165.134:80 | go.eset.eu | ESET, spol. s r.o. | SK | unknown |
2544 | eset_nod32_antivirus_live_installer.exe | 91.228.165.81:80 | versioncheck.eset.com | ESET, spol. s r.o. | SK | unknown |
2544 | eset_nod32_antivirus_live_installer.exe | 91.228.167.30:80 | banner.eset.com | ESET, spol. s r.o. | SK | unknown |
2544 | eset_nod32_antivirus_live_installer.exe | 91.228.166.82:80 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.eset.eu |
| suspicious |
versioncheck.eset.com |
| unknown |
banner.eset.com |
| whitelisted |
download.eset.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | eset_nod32_antivirus_live_installer.exe | Potential Corporate Privacy Violation | [PT POLICY] Executable application_x-msi Download |