| File name: | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe |
| Full analysis: | https://app.any.run/tasks/38cbae5e-acf9-4aac-ab33-dd20033eca62 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 17:03:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 42AFE1D6A53BEB838103E90C2914FD75 |
| SHA1: | 5DE77841CBA9E9894B6791C6E2CA5484F247DE71 |
| SHA256: | F0F070FEB8EB528F9FFCC2680EBE242E2511B13B628AA8CACD2F853474DF594C |
| SSDEEP: | 98304:gqMAnnlGXl7QOQVCLsvgyjP+BqSDp/ykVRuHGERanqyitkD4z9TukNusKPbPqALB:gFpFQjc |
MALICIOUS
Changes the autorun value in the registry
- bomgar-scc.exe (PID: 6412)
Steals credentials from Web Browsers
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Actions looks like stealing of personal data
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
SUSPICIOUS
Starts CMD.EXE for commands execution
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
The process creates files with name similar to system file names
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
Executable content was dropped or overwritten
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
Process drops legitimate windows executable
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
- bomgar-scc.exe (PID: 6372)
The executable file from the user directory is run by the CMD process
- spinner.exe (PID: 6328)
Executing commands from ".cmd" file
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
Starts itself from another location
- bomgar-scc.exe (PID: 6372)
Malware-specific behavior (creating "System.dll" in Temp)
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
Application launched itself
- bomgar-scc.exe (PID: 6412)
Reads security settings of Internet Explorer
- bomgar-scc.exe (PID: 6492)
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
INFO
Reads the computer name
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
- spinner.exe (PID: 6328)
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Checks supported languages
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
- spinner.exe (PID: 6328)
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Reads the machine GUID from the registry
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
The sample compiled with english language support
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
- bomgar-scc.exe (PID: 6372)
Reads Environment values
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Reads product name
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Creates files in the program directory
- bomgar-scc.exe (PID: 6372)
- bomgar-scc.exe (PID: 6412)
- bomgar-scc.exe (PID: 7064)
- bomgar-scc.exe (PID: 6492)
Create files in a temporary directory
- bomgar-scc.exe (PID: 6372)
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
The process uses the downloaded file
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
Reads the software policy settings
- bomgar-scc.exe (PID: 6492)
Checks proxy server information
- bomgar-scc.exe (PID: 6492)
- bomgar-scc.exe (PID: 7064)
Sends debugging messages
- spinner.exe (PID: 6328)
Process checks computer location settings
- bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe (PID: 6204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 03:20:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.2.1.64490 |
| ProductVersionNumber: | 16.2.1.64490 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | bomgar |
| FileDescription: | Bomgar |
| FileVersion: | 16.2.1.64490 |
| LegalCopyright: | Copyright (C) 2002-2016 Bomgar Corporation. Redistribution Prohibited. All Rights Reserved. |
| ProductName: | Bomgar |
Total processes
130
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6204 | "C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe" | C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\start.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6328 | "C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner.exe" --instance-id $SPIN_INSTANCE --icofile $SPIN_ICON | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: spinner Module Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 6372 | "C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\bomgar-scc.exe" "C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe" -install1 "C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe" --installer-pwd "C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\bomgar-scc.exe | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6412 | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe -install2 C:\Users\admin\AppData\Local\Temp\bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\ C:\ProgramData\bomgar-scc-0x675c68f9\ --installer-pwd C:\Users\admin\AppData\Local\Temp | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe | bomgar-scc.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Version: 16.2.1 (64490) Modules
| |||||||||||||||
| 6492 | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe -proxydetect | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe | bomgar-scc.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Exit code: 1 Version: 16.2.1 (64490) Modules
| |||||||||||||||
| 7064 | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe -proxydetect | C:\ProgramData\bomgar-scc-0x675c68f9\bomgar-scc.exe | bomgar-scc.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Version: 16.2.1 (64490) | |||||||||||||||
Total events
4 715
Read events
4 714
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6412) bomgar-scc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Bomgar_Cleanup_ZD126937529171 |
Value: cmd.exe /C rd /S /Q "C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb" & reg.exe delete HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v Bomgar_Cleanup_ZD126937529171 /f | |||
Executable files
61
Suspicious files
18
Text files
92
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\startup_animation_2.bmp | image | |
MD5:0B312FD112C34504680ABCE9FE6EAA13 | SHA256:EB3FF2CACD409461C6A8DDE65D278C296745401FAFFFD6ECDCF470E595C98008 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\startup_animation_3.bmp | image | |
MD5:915B8A9DE4CCEF690B17A5A66B945487 | SHA256:BD8E3F9CCF7F108DEFDF28C74D238AFA01BD22F119A782497C1FFDCDB0CD0CC8 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-2.bmp | image | |
MD5:0B312FD112C34504680ABCE9FE6EAA13 | SHA256:EB3FF2CACD409461C6A8DDE65D278C296745401FAFFFD6ECDCF470E595C98008 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-5.bmp | image | |
MD5:0DB01E512C8B09FEA1C1BCB93DDF0650 | SHA256:B42445F9D216CDEEBB1463F018616AB955FEF00B3F86548D88910CF60C7B5DE8 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-3.bmp | image | |
MD5:915B8A9DE4CCEF690B17A5A66B945487 | SHA256:BD8E3F9CCF7F108DEFDF28C74D238AFA01BD22F119A782497C1FFDCDB0CD0CC8 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-1.bmp | image | |
MD5:7604363A3DB0D8202ABFD9C16D154D4E | SHA256:D732DD994C232E710145E43062E5E085E3897B885ACFB5422B6C395E3295042D | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpb\server.lic | binary | |
MD5:350E6B7B6822281F11BC7DE9CC2859CF | SHA256:C07D44B7EC68A0404B891A13527C8A049064C663B54DBFE15CBC9465C3D4EE9E | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-4.bmp | image | |
MD5:EBCFFEA1A5E062435B12BAFA37509C9D | SHA256:B41EF27CDCDC734B675F6A057D0130DB083B232C1456DF89F6B29DDCF2E01C45 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner.exe | executable | |
MD5:1F56DD87FFD9924203A927E627017571 | SHA256:932ED0CBFAB5B7FB63CC114A59186629C30F38B7646FE1F0D4A5FF1FD0B90BC0 | |||
| 6204 | bomgar-scc-w0dc30jxhz8xzxdjh8xhxw1yehzegggfwxe7h1c408c90.exe | C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\start.cmd | text | |
MD5:208B5729FFADA552D284CF42D8D41B65 | SHA256:2418B877D41897E9ECE2E6A5E36C1D2819C7FA99019C4BB9EB91D1F5D2BA361A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6492 | bomgar-scc.exe | 192.159.120.202:443 | bomgar.ezlinks.com | EZLINKS | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
bomgar.ezlinks.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
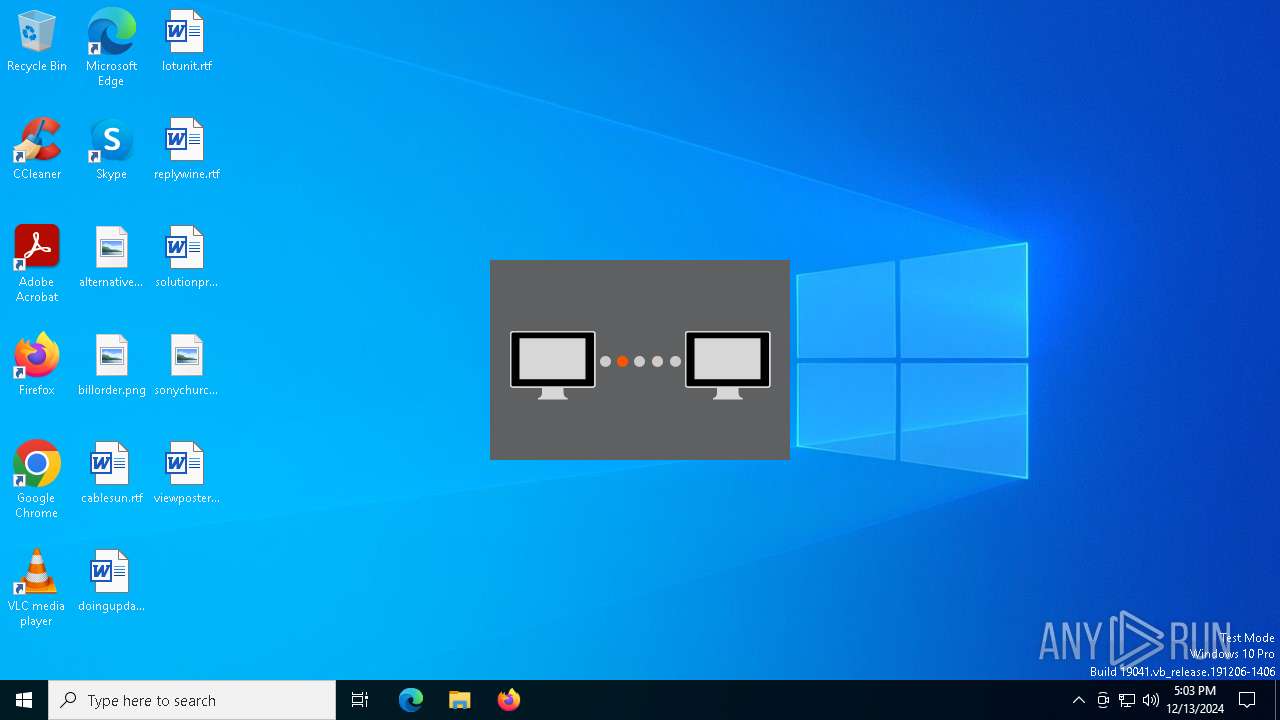
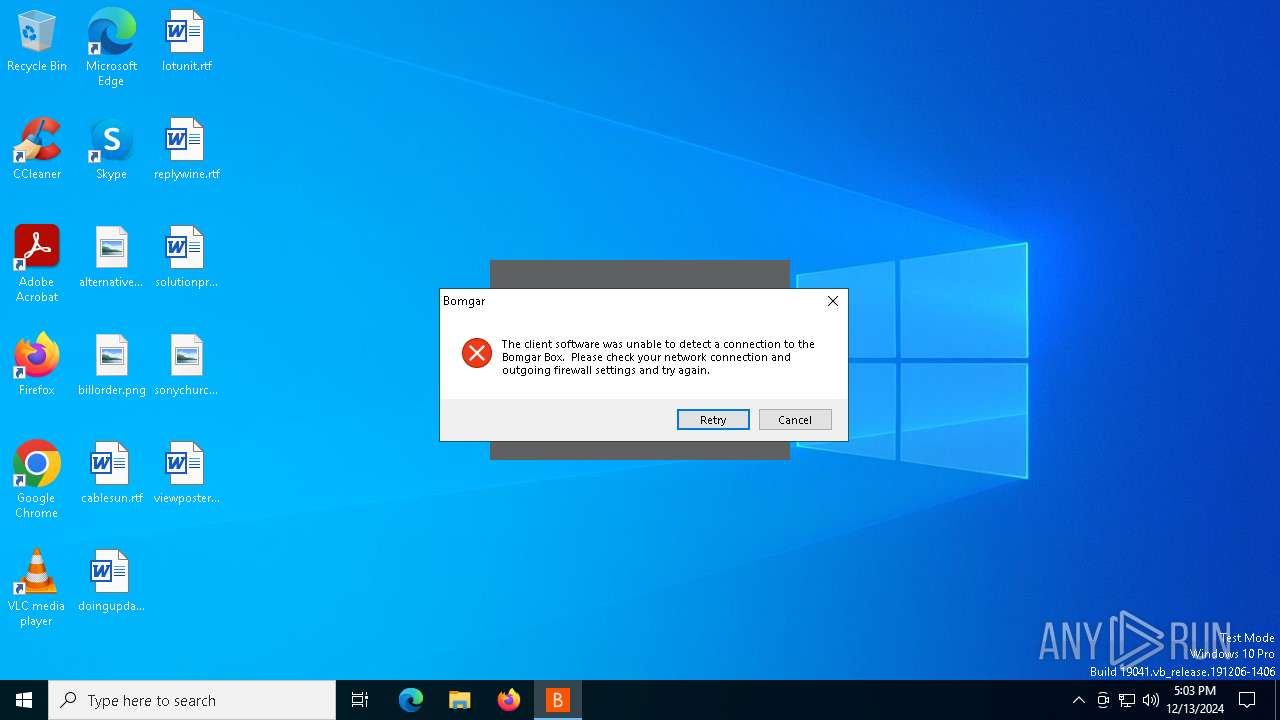
spinner.exe | SPN(18bc):<CMainWindow::CMainWindow
|
spinner.exe | SPN(18bc):>CMainWindow::Create
|
spinner.exe | SPN(18bc):>CMainWindow::CMainWindow
|
spinner.exe | SPN(18bc):image C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-1.bmp
|
spinner.exe | SPN(18bc):image C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-2.bmp
|
spinner.exe | SPN(18bc):image C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-5.bmp
|
spinner.exe | SPN(18bc):image C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-4.bmp
|
spinner.exe | SPN(18bc):image C:\Users\admin\AppData\Local\Temp\nsz5643.tmpspinner-$SPIN_INSTANCE\spinner-3.bmp
|
spinner.exe | SPN(18bc):>CMainWindow::OnCreate
|
spinner.exe | SPN(18bc):<CMainWindow::OnCreate
|