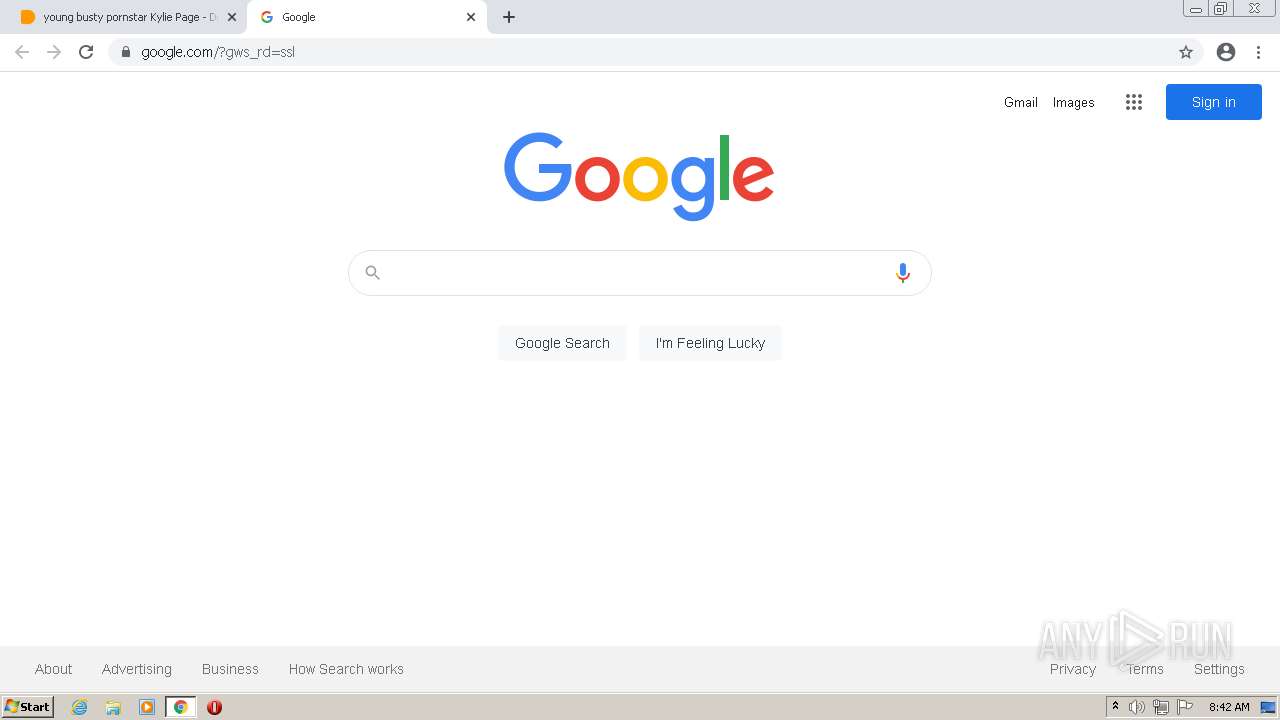
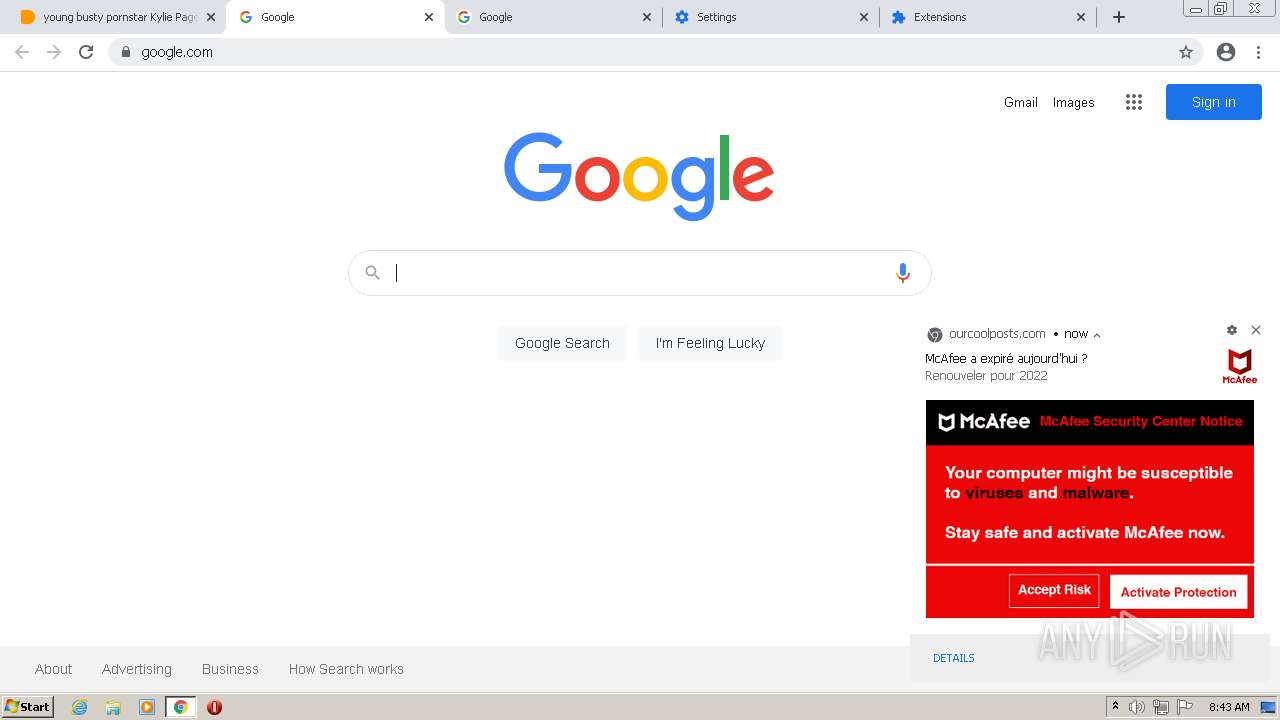
| URL: | https://dood.so/e/s52cqwgt4mbz&kw=["young","busty","pornstar","kylie","page","-","doodstream"]&key=f06f53688194268edaf23d2b44a59e27&scrWidth=360&scrHeight=640&tz=-6&v=21.11.v.2&ship=&res=12.229&dev=r&adb=y&uuid=53224a1a-2e59-4724-be25-7e3bb83b1707:2:1&adb=y |
| Full analysis: | https://app.any.run/tasks/b283c0d4-2057-47fb-997d-9c916f65d330 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2022, 08:42:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 362B039EA076D4B73FF620704A9ECB30 |
| SHA1: | 151F20F29AD9F9D6E86B7D54CC2C68D3EDE33DEB |
| SHA256: | F0E5562937C0ED4CFA549766824F7DD80F2BCB2D06E6898ED5B0DD4693475FC8 |
| SSDEEP: | 6:2SivR0IdxqHFRXTH0UtZVVDT/g4DXuZBpH2JiPHrSI:2IyIlrZjDT/pX47tGI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
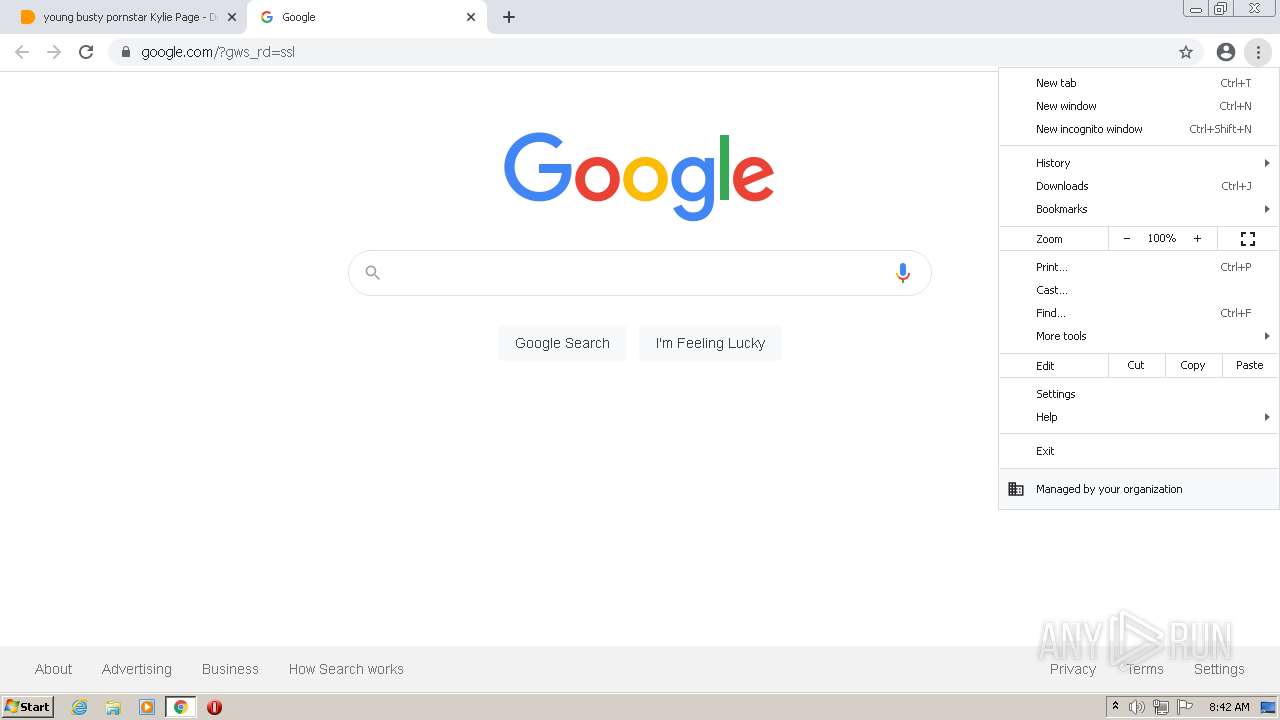
Checks supported languages
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 564)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 420)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 364)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 420)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3980)
Reads the computer name
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 420)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 564)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3812)
Reads the hosts file
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1040)
Reads settings of System Certificates
- chrome.exe (PID: 1040)
Application launched itself
- chrome.exe (PID: 2572)
Reads the date of Windows installation
- chrome.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,14337147932648047661,14931404296522447661,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
15 394
Read events
15 299
Write events
95
Delete events
0
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
45
Text files
108
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6214A1E9-A0C.pma | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1935db.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1935cb.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\770b3730-07fc-4658-a361-b193636acd6d.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c1908c13-00c1-485f-b9df-5e005c99846b.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
91
DNS requests
52
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 172.217.132.39:80 | http://r2---sn-5hne6nsk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=mM&mip=157.97.122.3&mm=28&mn=sn-5hne6nsk&ms=nvh&mt=1645518977&mv=m&mvi=2&pl=24&rmhost=r1---sn-5hne6nsk.gvt1.com&shardbypass=yes&smhost=r1---sn-5hne6nsr.gvt1.com | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | html | 593 b | whitelisted |
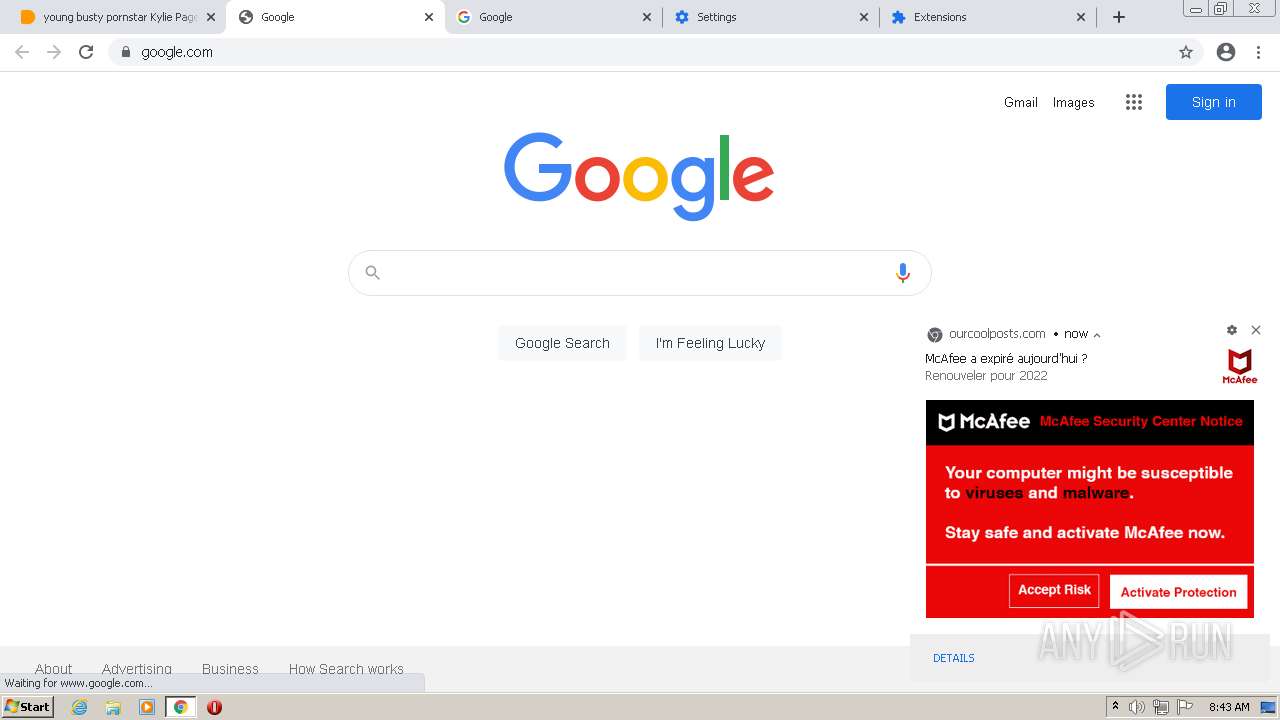
1040 | chrome.exe | GET | 302 | 142.250.185.196:80 | http://www.google.com/ | US | html | 231 b | malicious |
1040 | chrome.exe | GET | 301 | 142.250.181.238:80 | http://google.com/ | US | html | 219 b | whitelisted |
1040 | chrome.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0d2be817671f9ced | US | compressed | 59.9 Kb | whitelisted |
884 | svchost.exe | GET | 200 | 172.217.132.39:80 | http://r2---sn-5hne6nsk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=mM&mip=157.97.122.3&mm=28&mn=sn-5hne6nsk&ms=nvh&mt=1645518977&mv=m&mvi=2&pl=24&rmhost=r1---sn-5hne6nsk.gvt1.com&shardbypass=yes&smhost=r1---sn-5hne6nsr.gvt1.com | US | crx | 2.80 Kb | whitelisted |
1040 | chrome.exe | GET | 301 | 142.250.181.238:80 | http://google.com/ | US | html | 219 b | whitelisted |
884 | svchost.exe | HEAD | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1040 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1040 | chrome.exe | 104.26.12.179:443 | dood.so | Cloudflare Inc | US | unknown |
1040 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
1040 | chrome.exe | 104.26.2.9:443 | i.doodcdn.com | Cloudflare Inc | US | unknown |
1040 | chrome.exe | 192.243.59.12:443 | breakfastinvitingdetergent.com | DataWeb Global Group B.V. | US | malicious |
1040 | chrome.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1040 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1040 | chrome.exe | 104.26.3.9:443 | i.doodcdn.com | Cloudflare Inc | US | unknown |
1040 | chrome.exe | 139.45.195.8:443 | my.rtmark.net | — | US | suspicious |
1040 | chrome.exe | 195.181.175.48:443 | www.blockadsnot.com | Datacamp Limited | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
dood.so |
| malicious |
clients2.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
i.doodcdn.com |
| unknown |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
img.doodcdn.com |
| suspicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1040 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
1040 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |