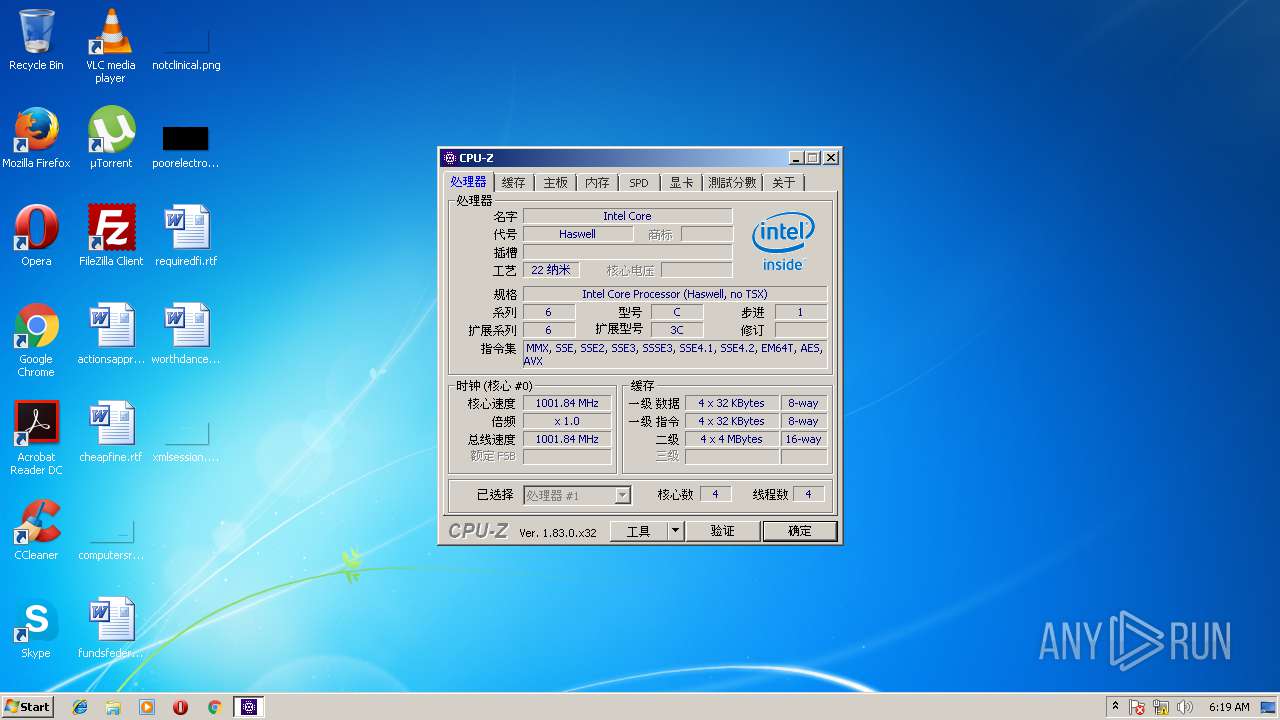
| File name: | cpuz_x32.exe |
| Full analysis: | https://app.any.run/tasks/acc1d66e-c214-46db-9b0e-8340e65487f0 |
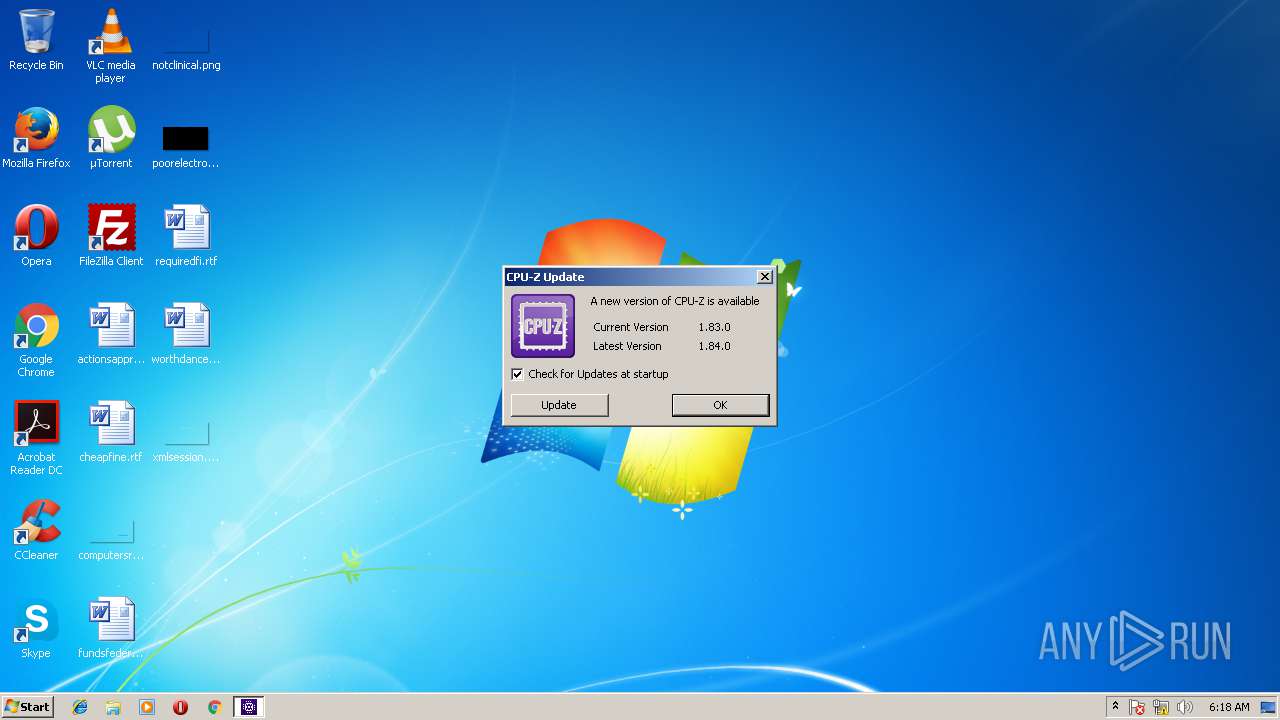
| Verdict: | Suspicious activity |
| Analysis date: | March 24, 2018, 06:18:30 |
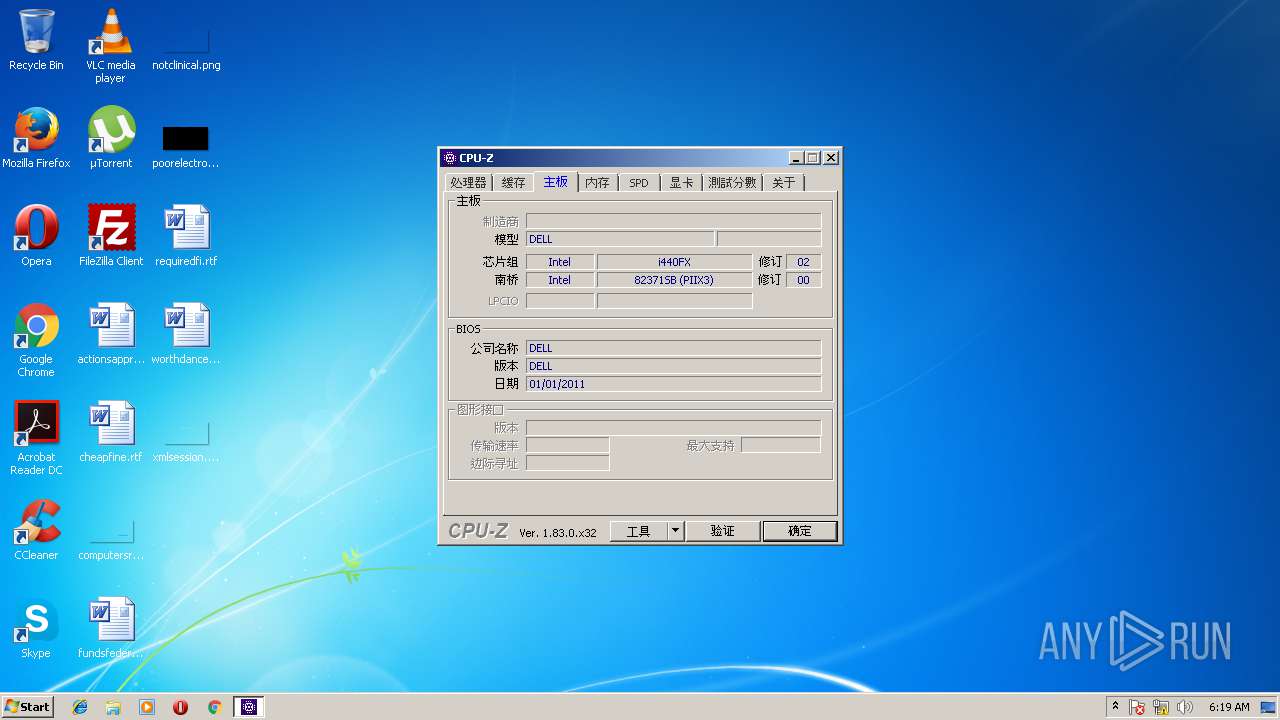
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2194A752F52A0D3828B7314868BC3ABC |
| SHA1: | 01A1C50A8FD536861567F08B77AB878A26FEBF7B |
| SHA256: | F0DE4B42C25C4EFDF3C78CDBF8FE5227ED63B340768A93632AD06C66EFEC2957 |
| SSDEEP: | 49152:Zu1WTO5qvBYoio9KbT6VMc8lcTyYkIKfaLf6kEz9:Y1WSYvg8KkMc6LVkEz9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the Windows directory
- cpuz_x32.exe (PID: 2236)
Low-level read access rights to disk partition
- cpuz_x32.exe (PID: 2236)
INFO
Dropped object may contain URL's
- cpuz_x32.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
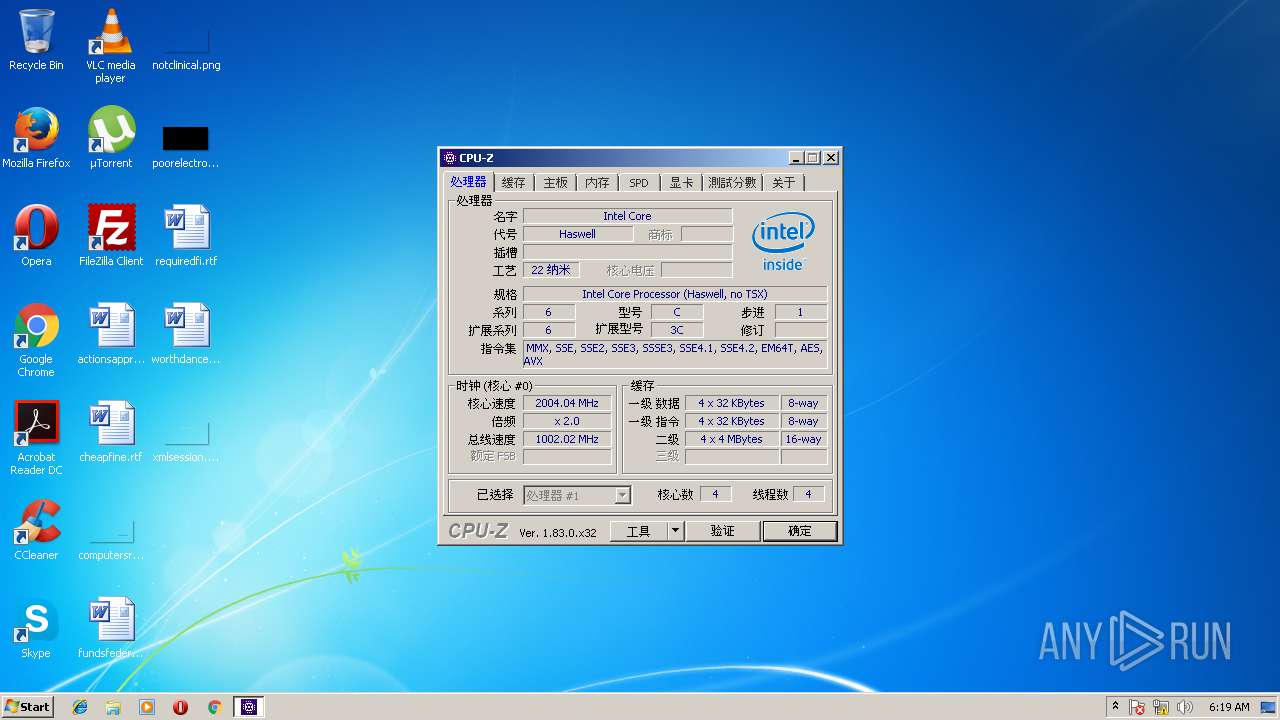
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:25 21:34:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1131008 |
| InitializedDataSize: | 1861120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf4899 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
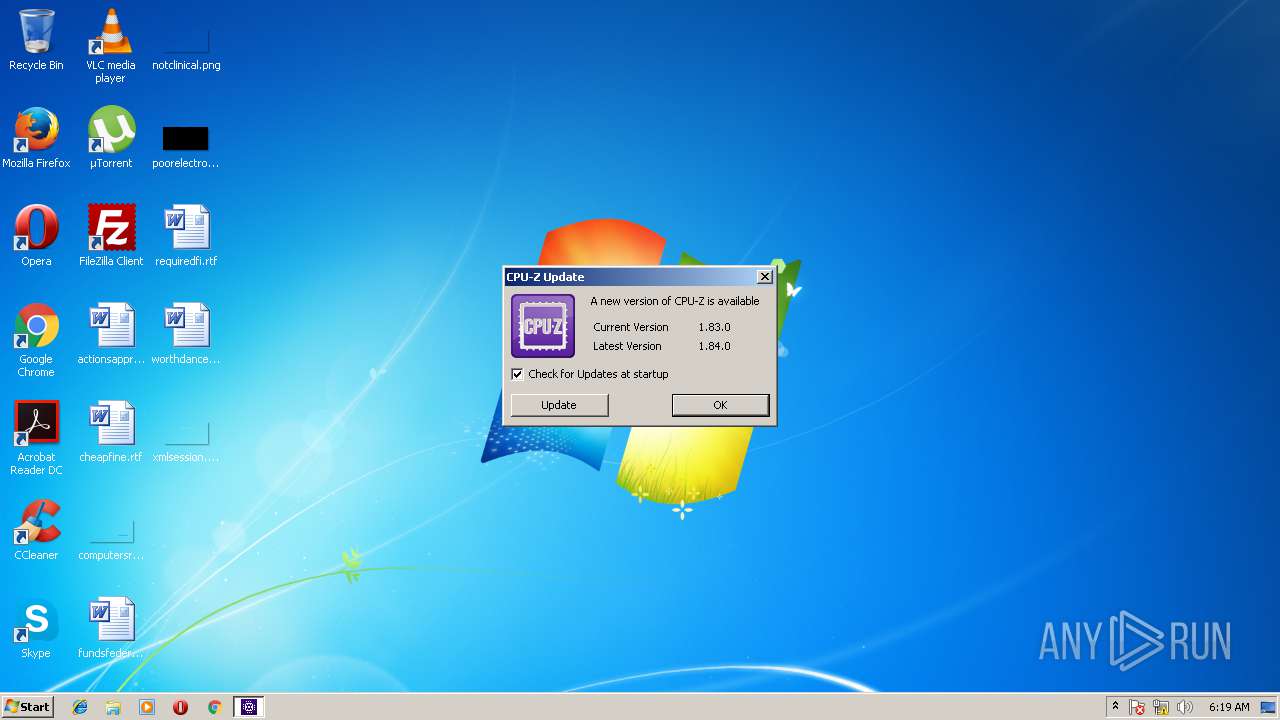
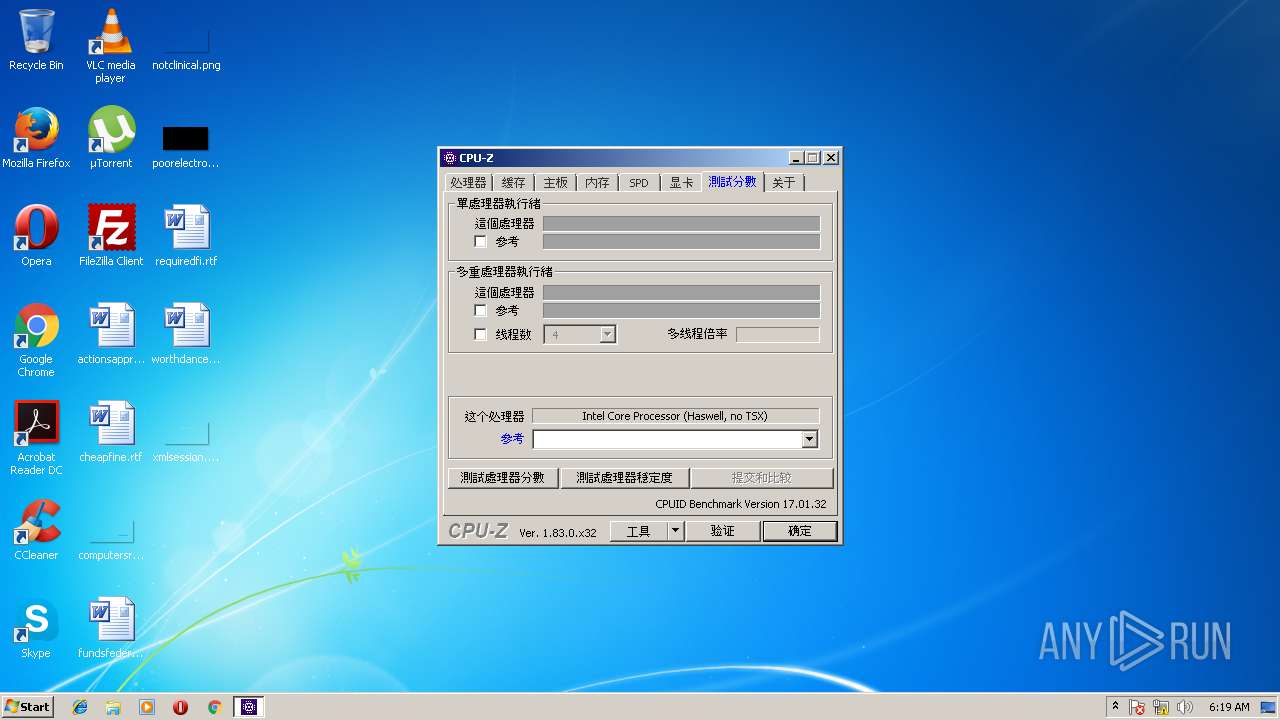
| FileVersionNumber: | 1.8.3.0 |
| ProductVersionNumber: | 1.8.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (1004) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | CPUID |
| FileDescription: | CPU-Z Application |
| FileVersion: | 1, 8, 3, 0 |
| InternalName: | cpuz.exe |
| LegalCopyright: | Copyright (C) 2004-2018 |
| OriginalFileName: | cpuz.exe |
| ProductName: | CPU-Z Application |
| ProductVersion: | 1, 8, 3, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jan-2018 20:34:59 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | CPUID |
| FileDescription: | CPU-Z Application |
| FileVersion: | 1, 8, 3, 0 |
| InternalName: | cpuz.exe |
| LegalCopyright: | Copyright (C) 2004-2018 |
| OriginalFilename: | cpuz.exe |
| ProductName: | CPU-Z Application |
| ProductVersion: | 1, 8, 3, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Jan-2018 20:34:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0011403C | 0x00114200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61729 |
.rdata | 0x00116000 | 0x000446D8 | 0x00044800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.85749 |
.data | 0x0015B000 | 0x00026338 | 0x00021600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.51455 |
.rsrc | 0x00182000 | 0x00160760 | 0x00160800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.99102 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18521 | 971 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.16402 | 69672 | Latin 1 / Western European | French - France | RT_ICON |
3 | 5.63061 | 9832 | Latin 1 / Western European | French - France | RT_ICON |
4 | 6.04253 | 4392 | Latin 1 / Western European | French - France | RT_ICON |
5 | 5.26744 | 1128 | Latin 1 / Western European | French - France | RT_ICON |
6 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 2.34038 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 2.34004 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.51649 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
WININET.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | "C:\Users\admin\AppData\Local\Temp\cpuz_x32.exe" | C:\Users\admin\AppData\Local\Temp\cpuz_x32.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Exit code: 0 Version: 1, 8, 3, 0 Modules
| |||||||||||||||
| 3064 | "C:\Users\admin\AppData\Local\Temp\cpuz_x32.exe" | C:\Users\admin\AppData\Local\Temp\cpuz_x32.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 1, 8, 3, 0 Modules
| |||||||||||||||
Total events
66
Read events
32
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2236) cpuz_x32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cpuz_x32_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | cpuz_x32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\cpuid[1].ver | — | |
MD5:— | SHA256:— | |||
| 2236 | cpuz_x32.exe | C:\Windows\temp\cpuz_driver_2236.log | text | |
MD5:— | SHA256:— | |||
| 2236 | cpuz_x32.exe | C:\Windows\temp\cpuz145\cpuz145_x32.sys | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 188.165.231.119:80 | http://download.cpuid.com/cpuid.ver | FR | text | 88 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 188.165.231.119:80 | download.cpuid.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cpuid.com |
| whitelisted |