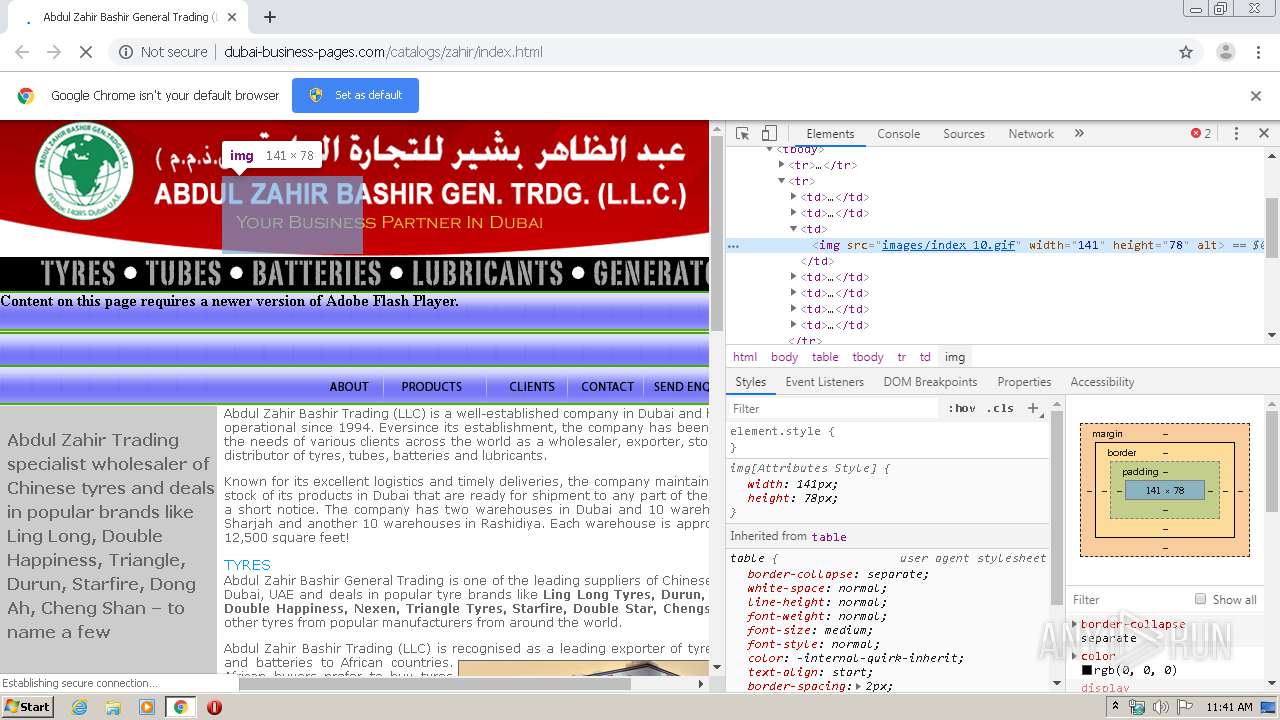
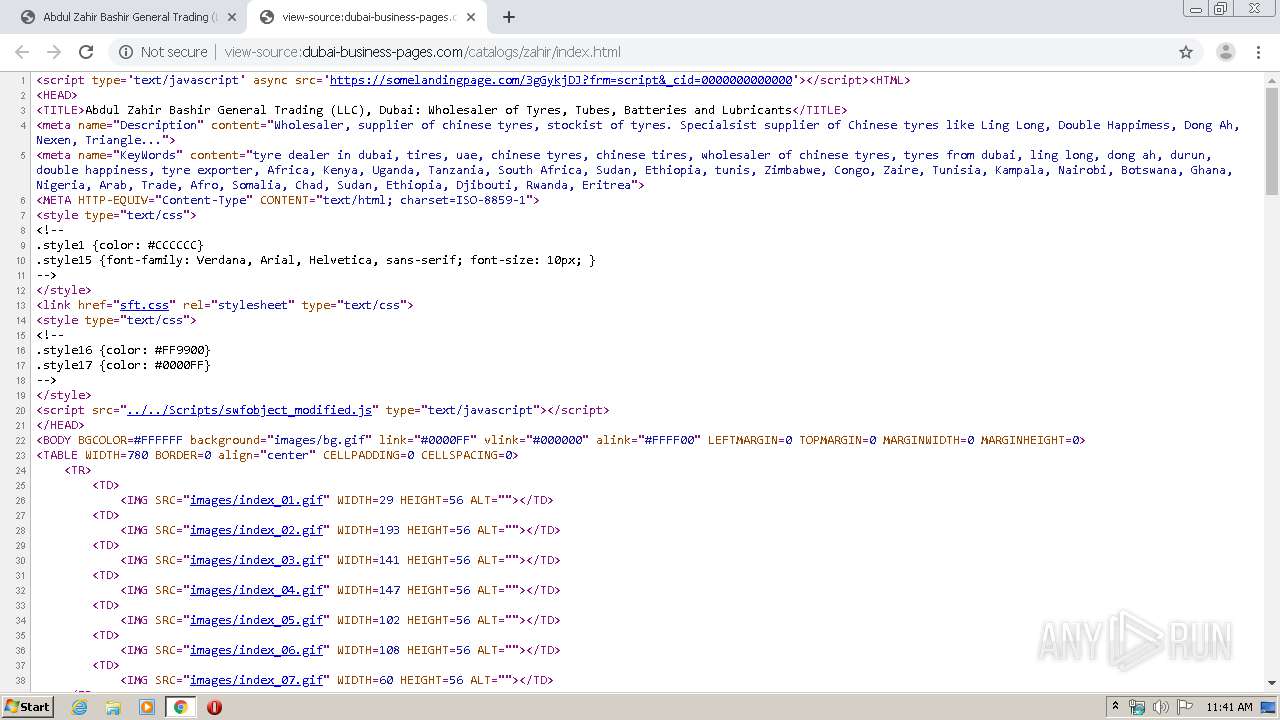
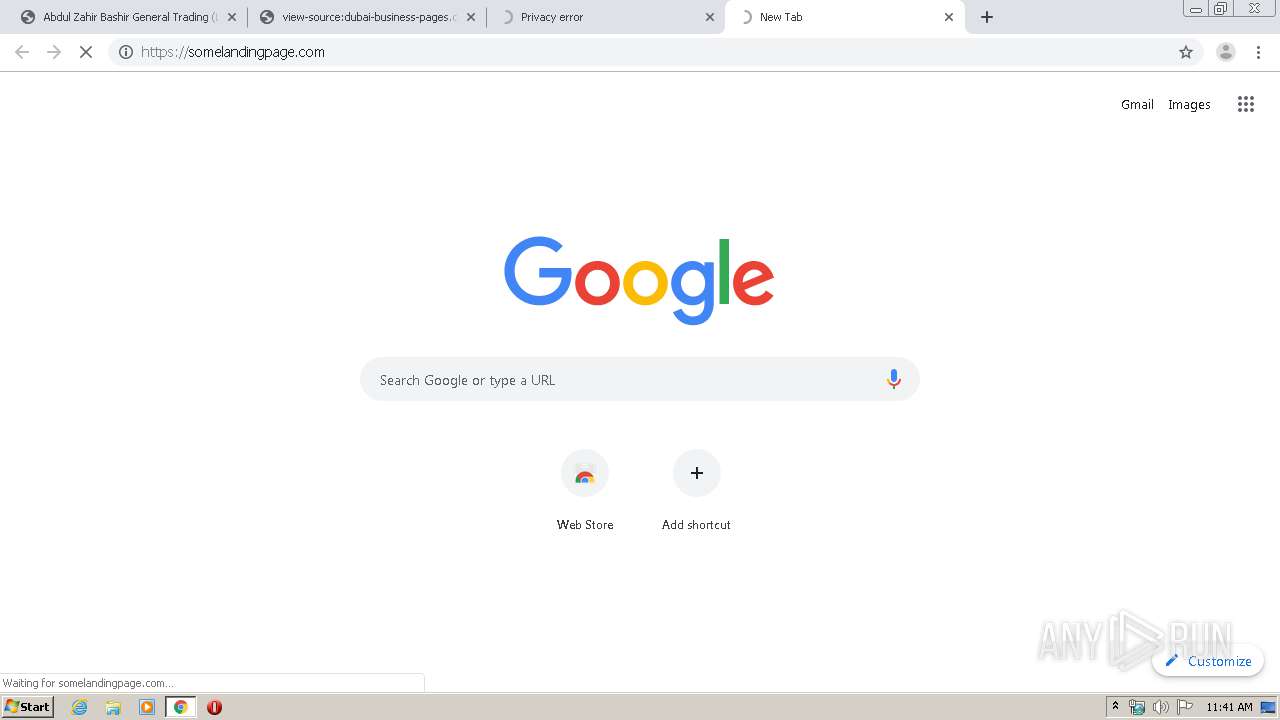
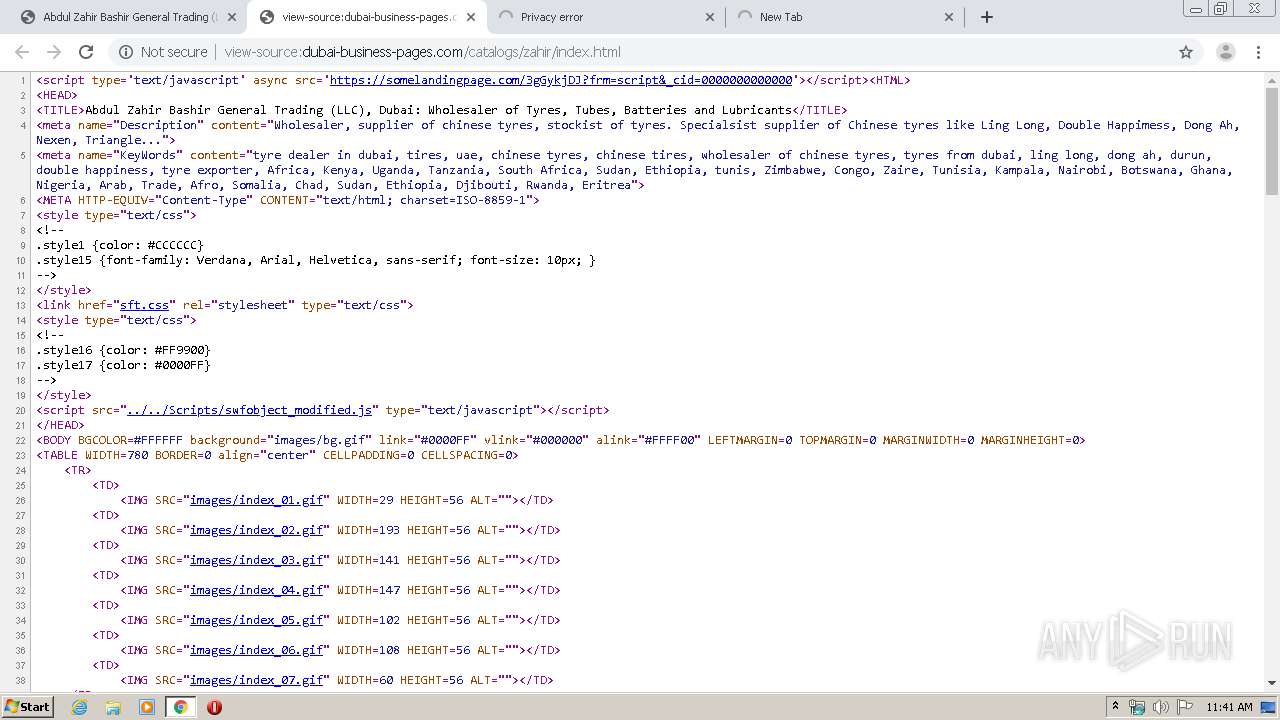
| URL: | http://dubai-business-pages.com/catalogs/zahir/index.html |
| Full analysis: | https://app.any.run/tasks/7058449b-4e82-4799-8b89-7cc189c659c4 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 11:40:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A2D08DA7CA1869E9F837D8AFEF3CD6BE |
| SHA1: | E5F2174C5A7BAB46E1A5226476640CE135D9B7BC |
| SHA256: | F0DB2E5CDC2C40A8DF58BF957FB9E280BB32710EA9B9D754397E05A4B79EFD66 |
| SSDEEP: | 3:N1KaQHEJwL0WWIVEG2ExCWKsIMG:CaSOZlcIMG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3976)
INFO
Reads the hosts file
- chrome.exe (PID: 580)
- chrome.exe (PID: 3976)
Application launched itself
- chrome.exe (PID: 3976)
Reads settings of System Certificates
- chrome.exe (PID: 580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12520318417278192616 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3292 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17028596025196757666 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4998999917547428716 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18268150463061041981 --mojo-platform-channel-handle=4504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15930255487406473660 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15325374771702039322 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9839909717523861866 --mojo-platform-channel-handle=4896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2254627946392921221 --mojo-platform-channel-handle=4144 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 111
Read events
1 019
Write events
87
Delete events
5
Modification events
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3976-13226845263997625 |
Value: 259 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
58
Text files
268
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E511350-F88.pma | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\31fa18fd-3552-4ef4-9475-d84ef614c941.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66a99.TMP | text | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66c6e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
171
TCP/UDP connections
71
DNS requests
34
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
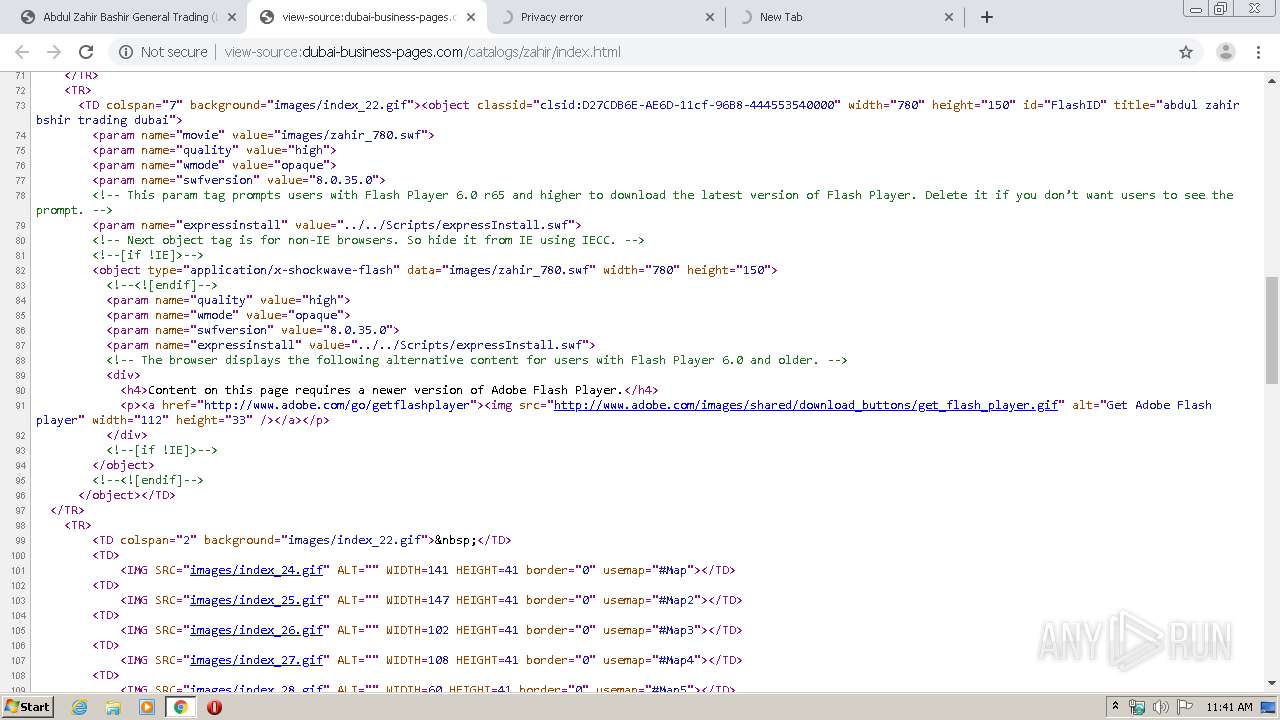
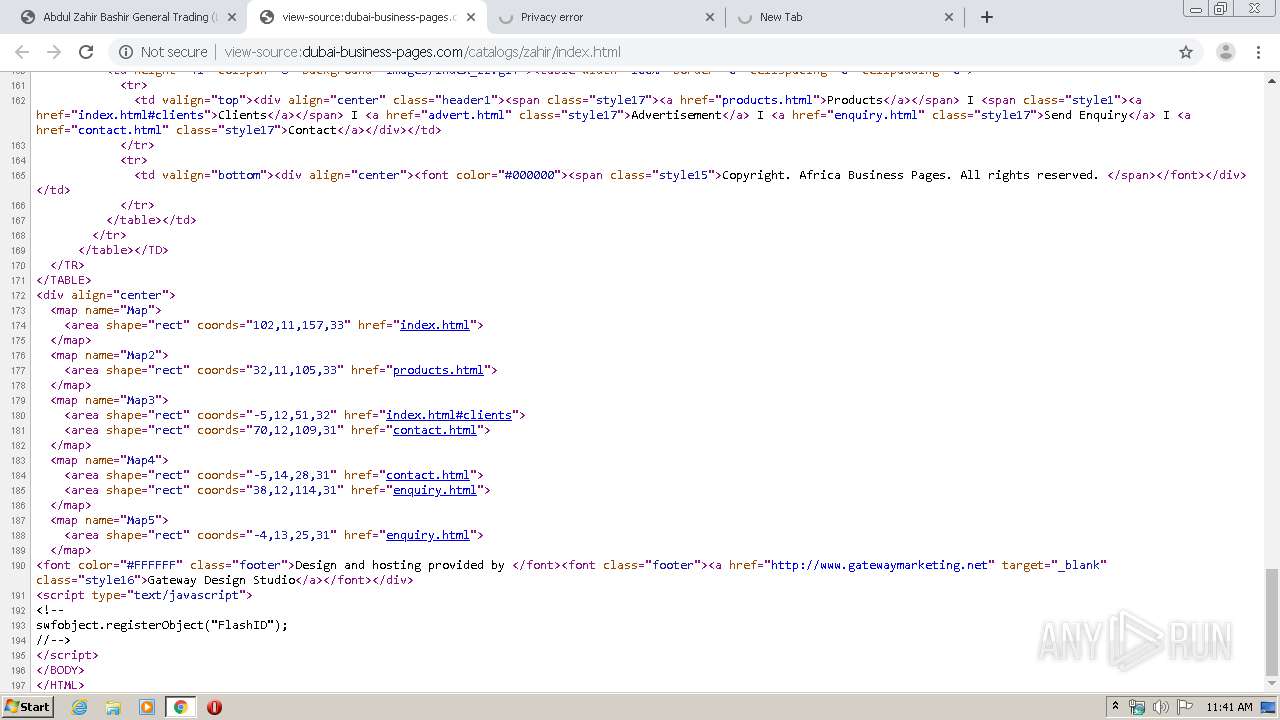
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/sft.css | US | text | 240 b | malicious |
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/index.html | US | html | 4.94 Kb | malicious |
580 | chrome.exe | GET | 302 | 192.185.149.90:80 | http://dubai-business-pages.com/404/index.html | US | html | 304 b | malicious |
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/images/index_04.gif | US | image | 5.41 Kb | malicious |
580 | chrome.exe | GET | 302 | 192.185.149.90:80 | http://dubai-business-pages.com/404/index.html | US | html | 304 b | malicious |
580 | chrome.exe | GET | 302 | 192.185.149.90:80 | http://dubai-business-pages.com/404/index.html | US | html | 304 b | malicious |
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/images/index_03.gif | US | image | 4.99 Kb | malicious |
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/images/index_02.gif | US | image | 7.18 Kb | malicious |
580 | chrome.exe | GET | 302 | 192.185.149.90:80 | http://dubai-business-pages.com/404/index.html | US | html | 304 b | malicious |
580 | chrome.exe | GET | 200 | 192.185.149.90:80 | http://dubai-business-pages.com/catalogs/zahir/images/index_06.gif | US | image | 3.41 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
580 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
580 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
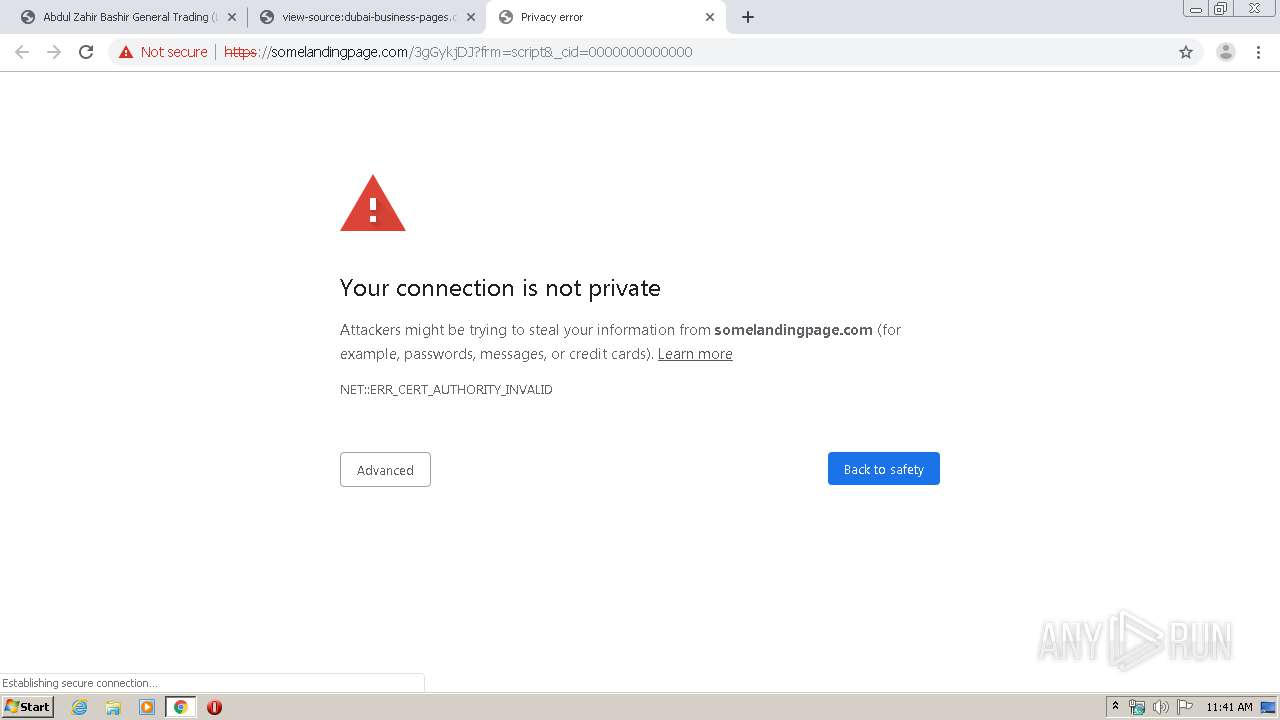
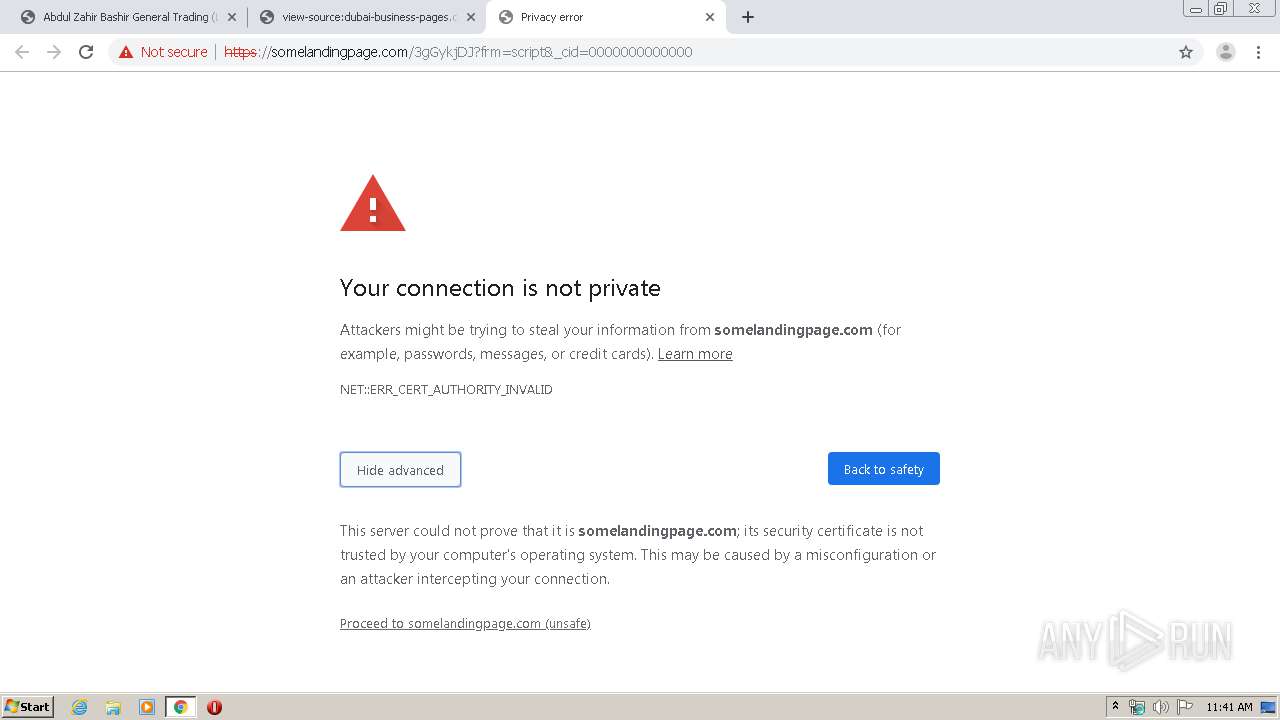
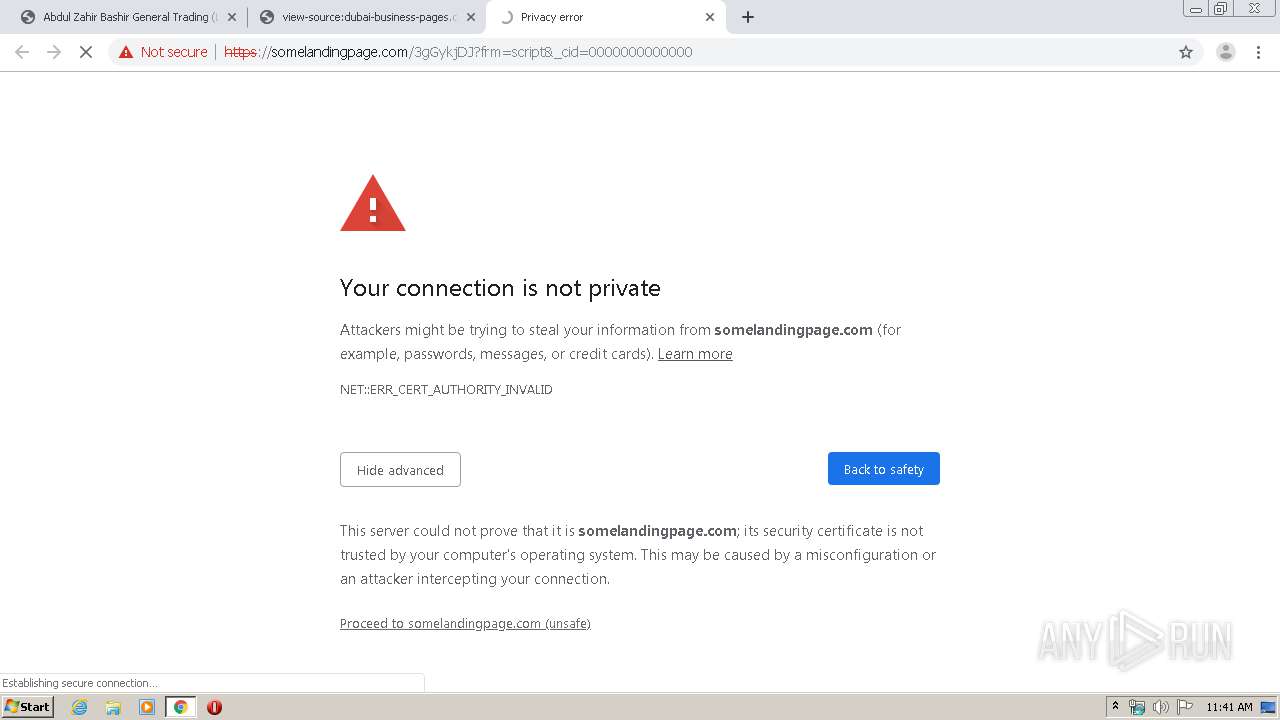
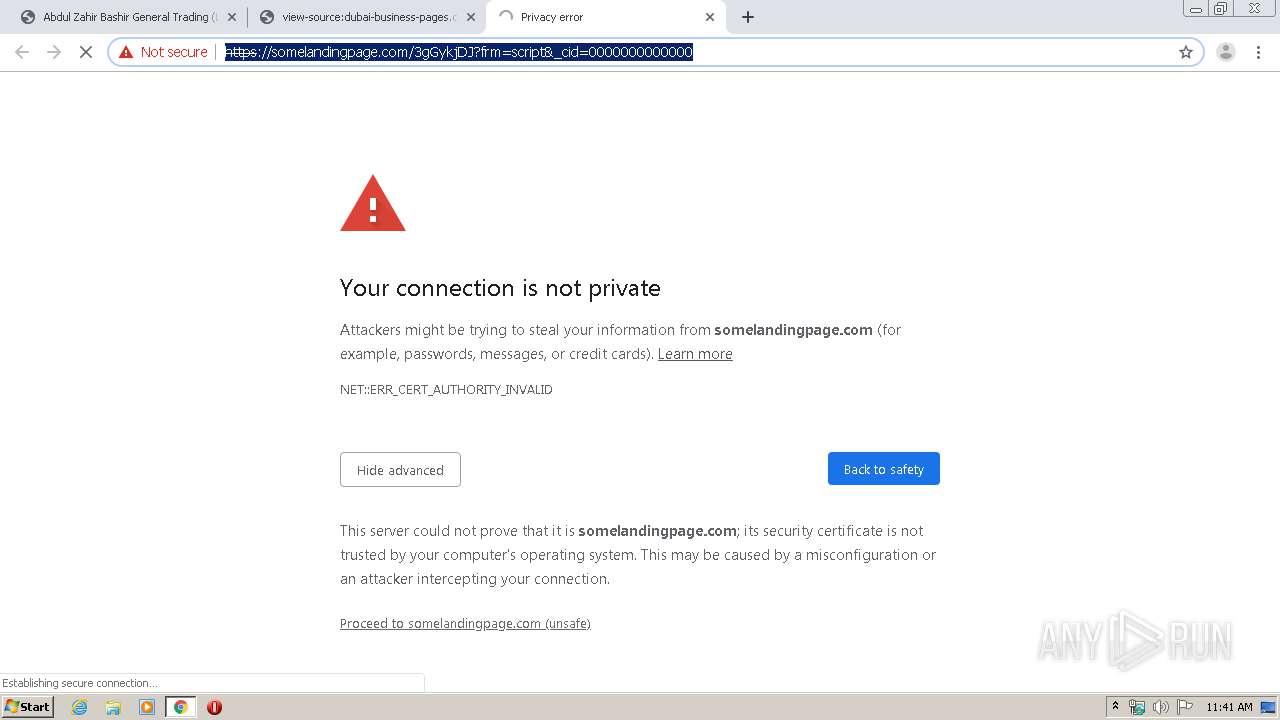
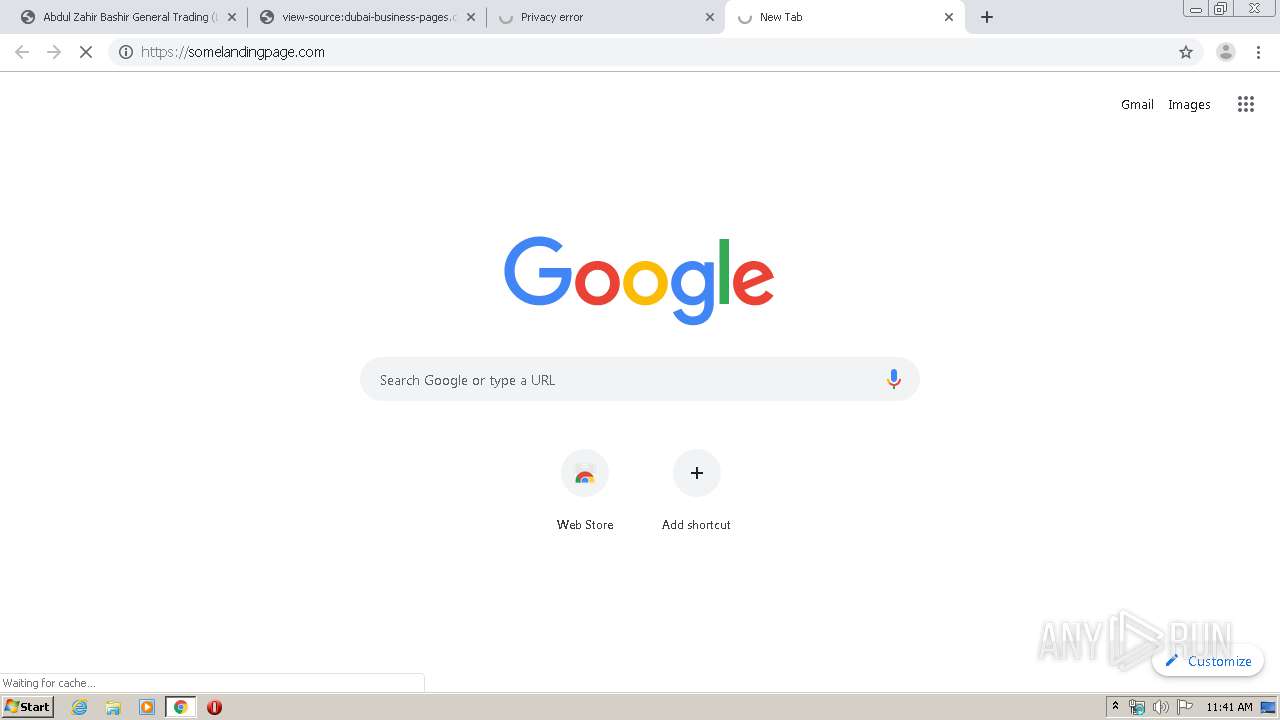
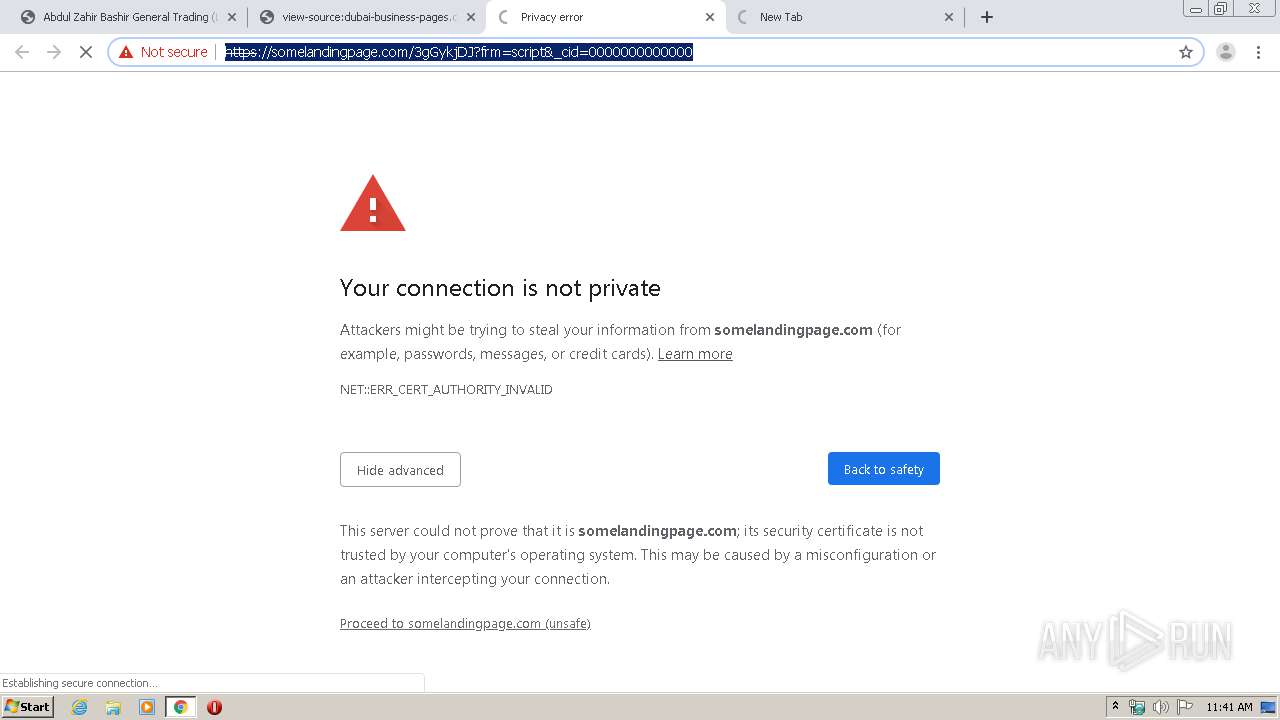
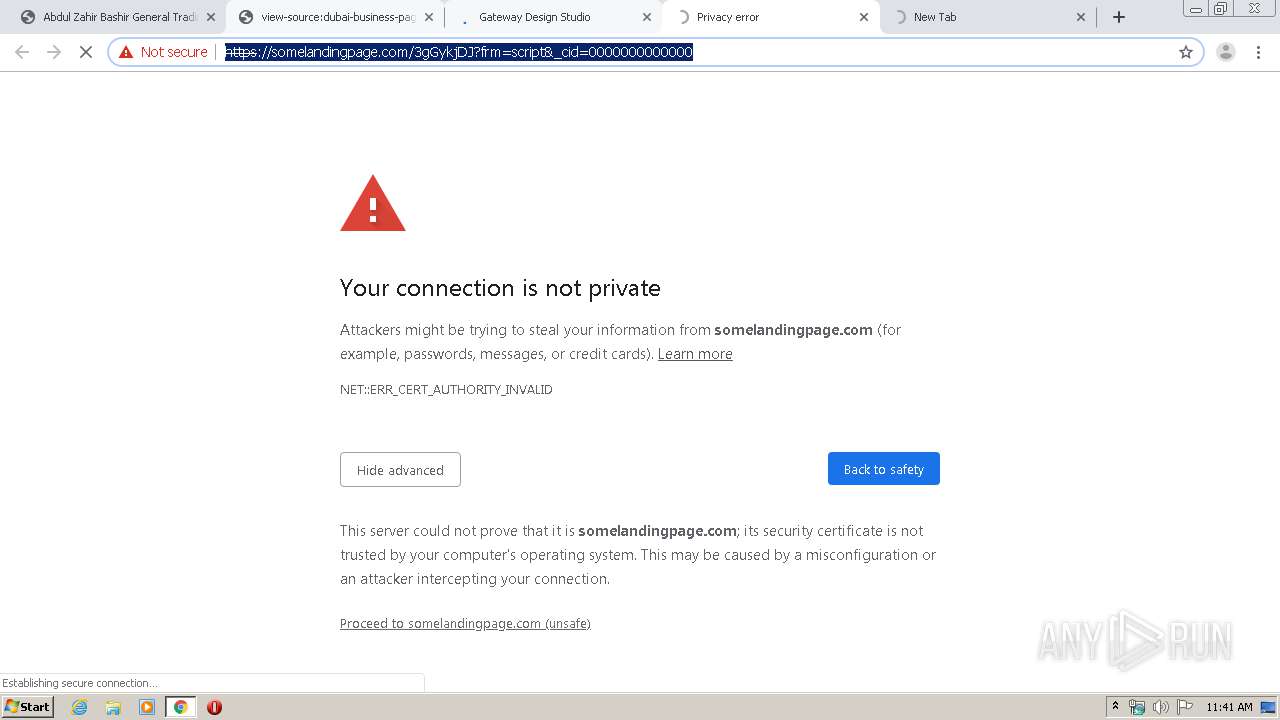
580 | chrome.exe | 13.209.155.49:443 | somelandingpage.com | — | KR | unknown |
580 | chrome.exe | 192.185.149.90:80 | dubai-business-pages.com | CyrusOne LLC | US | malicious |
580 | chrome.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
580 | chrome.exe | 2.21.36.142:80 | www.adobe.com | GTT Communications Inc. | FR | malicious |
580 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
580 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
580 | chrome.exe | 2.21.36.142:443 | www.adobe.com | GTT Communications Inc. | FR | malicious |
— | — | 172.217.16.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
dubai-business-pages.com |
| malicious |
accounts.google.com |
| shared |
somelandingpage.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
www.adobe.com |
| whitelisted |
www.google.com |
| malicious |
www.africa-business.com |
| unknown |
www.gatewaymarketing.net |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |
580 | chrome.exe | Attempted User Privilege Gain | AV MALWARE Unknown EK Exploit Inbound - Hacked Wordpress Sites |