| File name: | VK Paranoid Tools.exe |
| Full analysis: | https://app.any.run/tasks/60a9f291-8d45-42b5-833b-6c0e029ca080 |
| Verdict: | No threats detected |
| Analysis date: | September 28, 2019, 20:48:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 47FF31BC8227DFB087D0F7F560D13500 |
| SHA1: | 531019E4BD56177246627044F13D795725836998 |
| SHA256: | F0D888A3E8E0325CF9A96D17BDF07131DECBBB24D05EB28BC5CE5C3605AE04A7 |
| SSDEEP: | 49152:DKbh/LEa/B6grA3w9GsXTeLnGEhNYv6fL6OHM61c3JpMAx/h7eTgjN6cS:DKZLjB6wWw1De5hOfu1c5pMAHjN6cS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- VK Paranoid Tools.exe (PID: 3160)
Creates files in the user directory
- VK Paranoid Tools.exe (PID: 3160)
Reads Internet Cache Settings
- VK Paranoid Tools.exe (PID: 3160)
INFO
Reads settings of System Certificates
- VK Paranoid Tools.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:04 17:01:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1348096 |
| InitializedDataSize: | 2779136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f400a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | The best analytic tool for Vkontakte social network. In our opinion, of course |
| CompanyName: | VKPT Software |
| FileDescription: | VK Paranoid Tools |
| FileVersion: | 2.0.0.0 |
| InternalName: | VK Paranoid Tools.exe |
| LegalCopyright: | VKPT © www.vkpt.info |
| LegalTrademarks: | - |
| OriginalFileName: | VK Paranoid Tools.exe |
| ProductName: | VK Paranoid Tools |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jul-2019 15:01:39 |
| Comments: | The best analytic tool for Vkontakte social network. In our opinion, of course |
| CompanyName: | VKPT Software |
| FileDescription: | VK Paranoid Tools |
| FileVersion: | 2.0.0.0 |
| InternalName: | VK Paranoid Tools.exe |
| LegalCopyright: | VKPT © www.vkpt.info |
| LegalTrademarks: | - |
| OriginalFilename: | VK Paranoid Tools.exe |
| ProductName: | VK Paranoid Tools |
| ProductVersion: | 2.0.0.0 |
| Assembly Version: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Jul-2019 15:01:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Mc=\x1116_k\x90\x98( | 0x00002000 | 0x00289890 | 0x00289A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.text | 0x0028C000 | 0x00148E90 | 0x00149000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.14382 |
.rsrc | 0x003D6000 | 0x0001CA96 | 0x0001CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03212 |
0x003F4000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 | |
.reloc | 0x003F6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.35634 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.82853 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.48989 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.92877 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 7.91905 | 15630 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3160 | "C:\Users\admin\AppData\Local\Temp\VK Paranoid Tools.exe" | C:\Users\admin\AppData\Local\Temp\VK Paranoid Tools.exe | explorer.exe | ||||||||||||
User: admin Company: VKPT Software Integrity Level: MEDIUM Description: VK Paranoid Tools Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
206
Read events
148
Write events
58
Delete events
0
Modification events
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_CURRENT_USER\Software\VK Paranoid Tools |
| Operation: | write | Name: | Width |
Value: 1078 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_CURRENT_USER\Software\VK Paranoid Tools |
| Operation: | write | Name: | Height |
Value: 672 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3160) VK Paranoid Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\VK Paranoid Tools_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
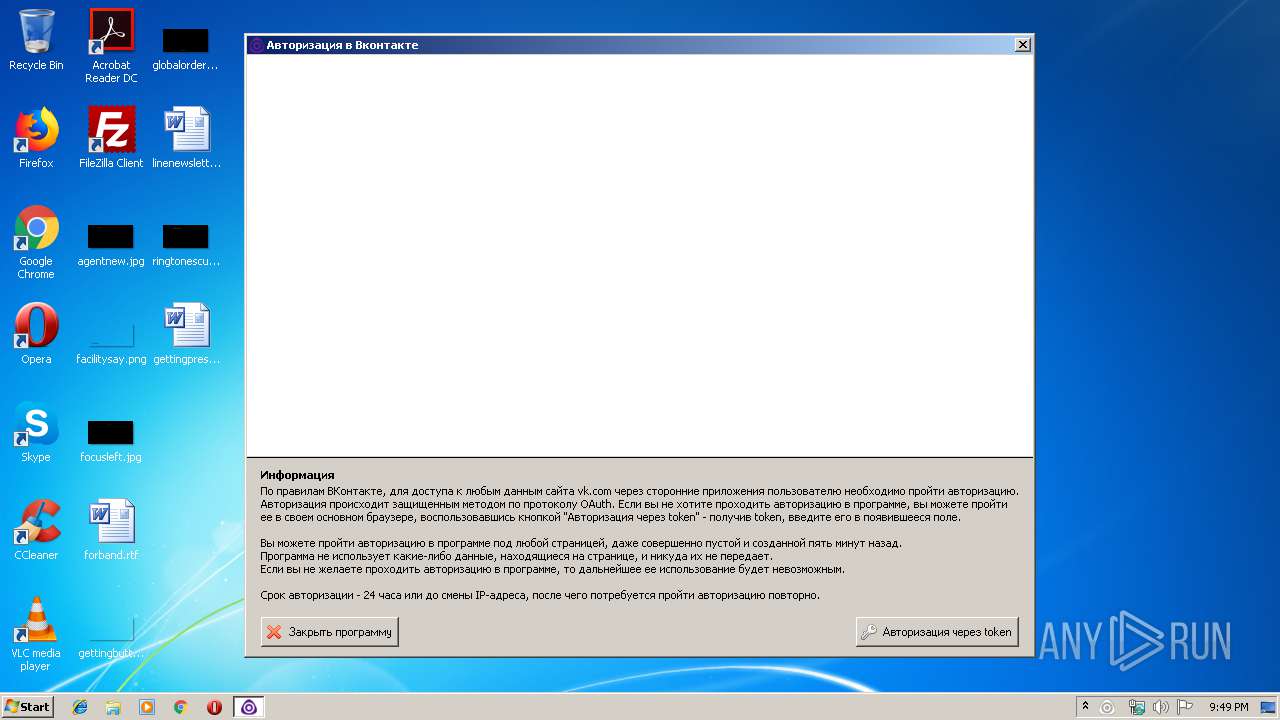
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@vk[1].txt | — | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\fonts_utf[1].css | text | |
MD5:— | SHA256:— | |||
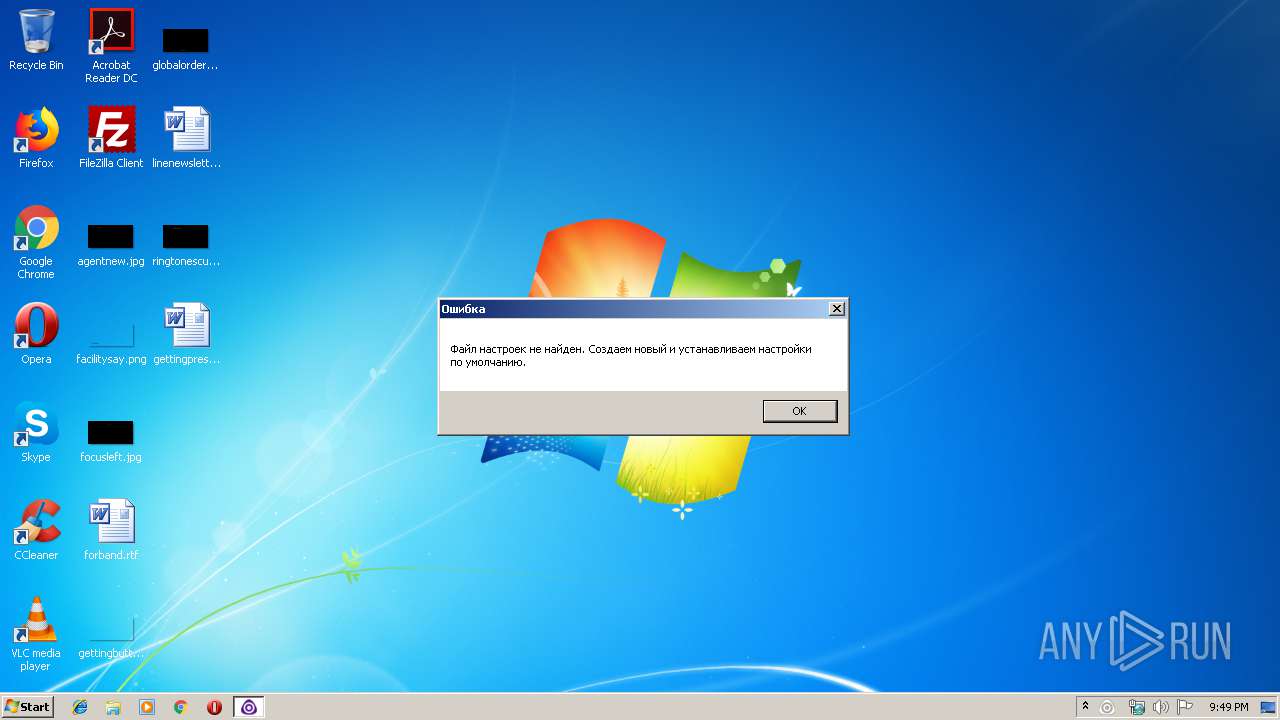
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Temp\VKPT\Settings.pts | pi2 | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@vk[2].txt | text | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\oauth_popup[1].css | text | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\authorize[1].txt | html | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\fonts_cnt[1].css | text | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\common[1].css | text | |
MD5:— | SHA256:— | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\common_light[1].js | text | |
MD5:9167D4CE167039282C210FB35A7A3903 | SHA256:8D51D3444A0BD5851BC1213CAD24CD54D73809210961891C3D9525C03C2206E5 | |||
| 3160 | VK Paranoid Tools.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\logo_vk[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3160 | VK Paranoid Tools.exe | POST | 200 | 104.31.82.223:80 | http://vkpt.info/200/three.php | US | text | 83 b | suspicious |
3160 | VK Paranoid Tools.exe | POST | 200 | 104.31.82.223:80 | http://vkpt.info/200/six.php | US | text | 22 b | suspicious |
3160 | VK Paranoid Tools.exe | POST | 200 | 104.31.82.223:80 | http://vkpt.info/200/two.php | US | text | 27 b | suspicious |
3160 | VK Paranoid Tools.exe | POST | 200 | 104.31.82.223:80 | http://vkpt.info/200/twelve.php | US | text | 339 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
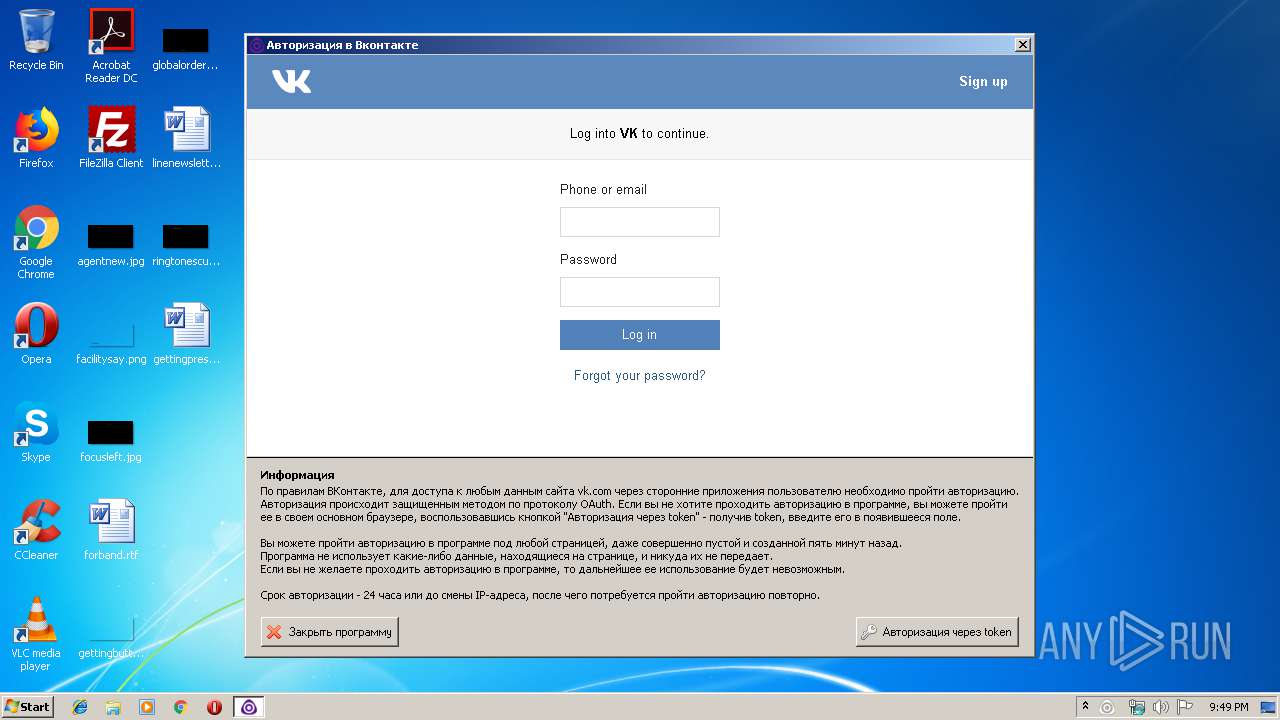
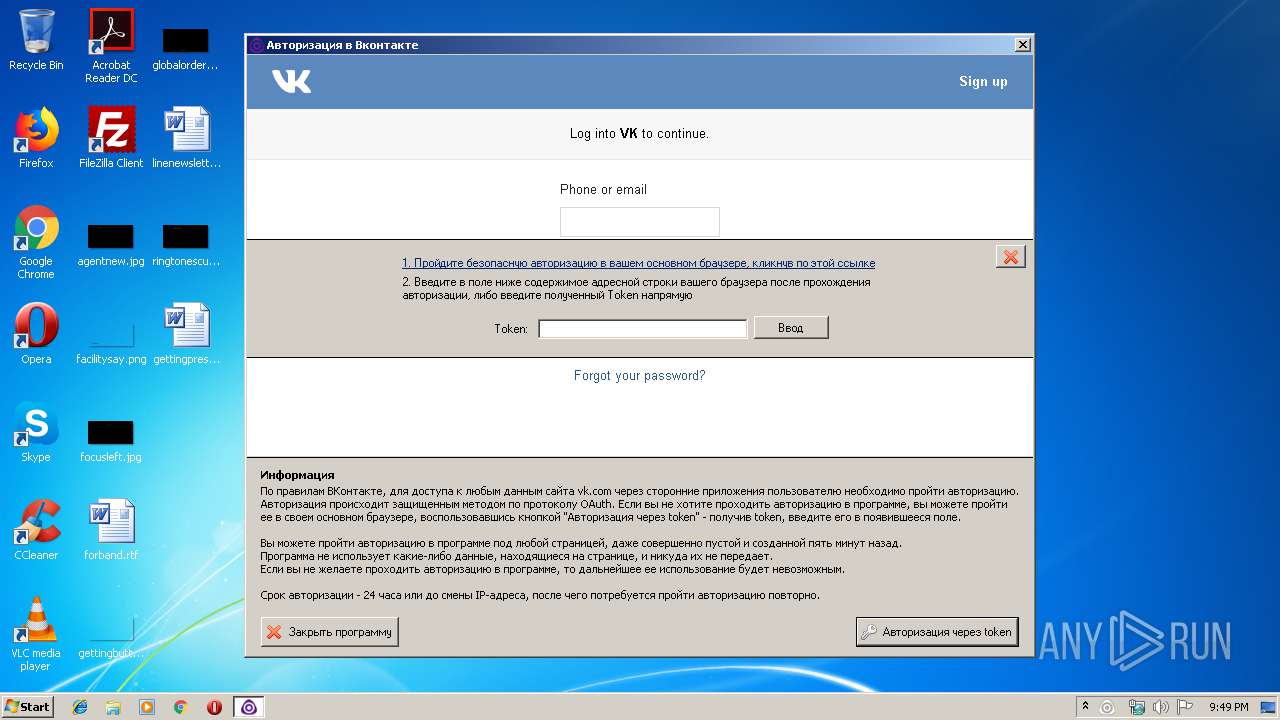
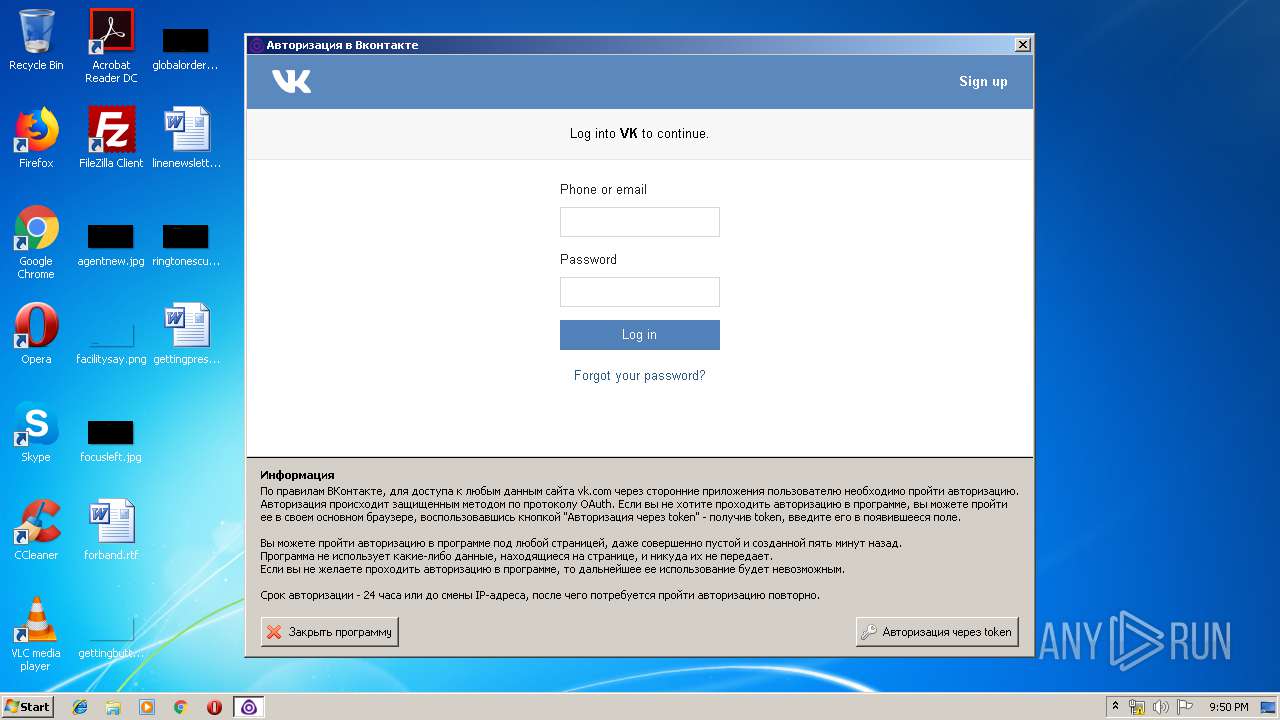
3160 | VK Paranoid Tools.exe | 104.31.82.223:80 | vkpt.info | Cloudflare Inc | US | shared |
3160 | VK Paranoid Tools.exe | 87.240.129.181:443 | oauth.vk.com | VKontakte Ltd | RU | unknown |
3160 | VK Paranoid Tools.exe | 93.186.225.193:443 | vk.com | VKontakte Ltd | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vkpt.info |
| suspicious |
oauth.vk.com |
| whitelisted |
vk.com |
| whitelisted |