| File name: | texttwist-2.exe |
| Full analysis: | https://app.any.run/tasks/683d5ab4-fef0-4094-b956-11a0261ea021 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2020, 22:17:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 6AAEE5FB1F632F782CDA9EFF474F7AF1 |
| SHA1: | EDF7352231D97079618526A7F86DDA78EFDFD598 |
| SHA256: | F0CD9514FEE7F4D0F42F891440C37B3F1BE67687203139FCB12D567C03DD100C |
| SSDEEP: | 24576:WUo+Las4xHuueqjYT3OP5HnoePePnuCTchRE8:JoKM1ju8teGCM6 |
MALICIOUS
Application was dropped or rewritten from another process
- aminstantservice.exe (PID: 3636)
- aminstantservice.exe (PID: 1520)
SUSPICIOUS
Removes files from Windows directory
- aminstantservice.exe (PID: 1520)
Executable content was dropped or overwritten
- texttwist-2.exe (PID: 2500)
- aminstantservice.exe (PID: 1520)
Creates a software uninstall entry
- texttwist-2.exe (PID: 2500)
Creates files in the program directory
- texttwist-2.exe (PID: 2500)
- aminstantservice.exe (PID: 1520)
Executed as Windows Service
- aminstantservice.exe (PID: 1520)
Executed via COM
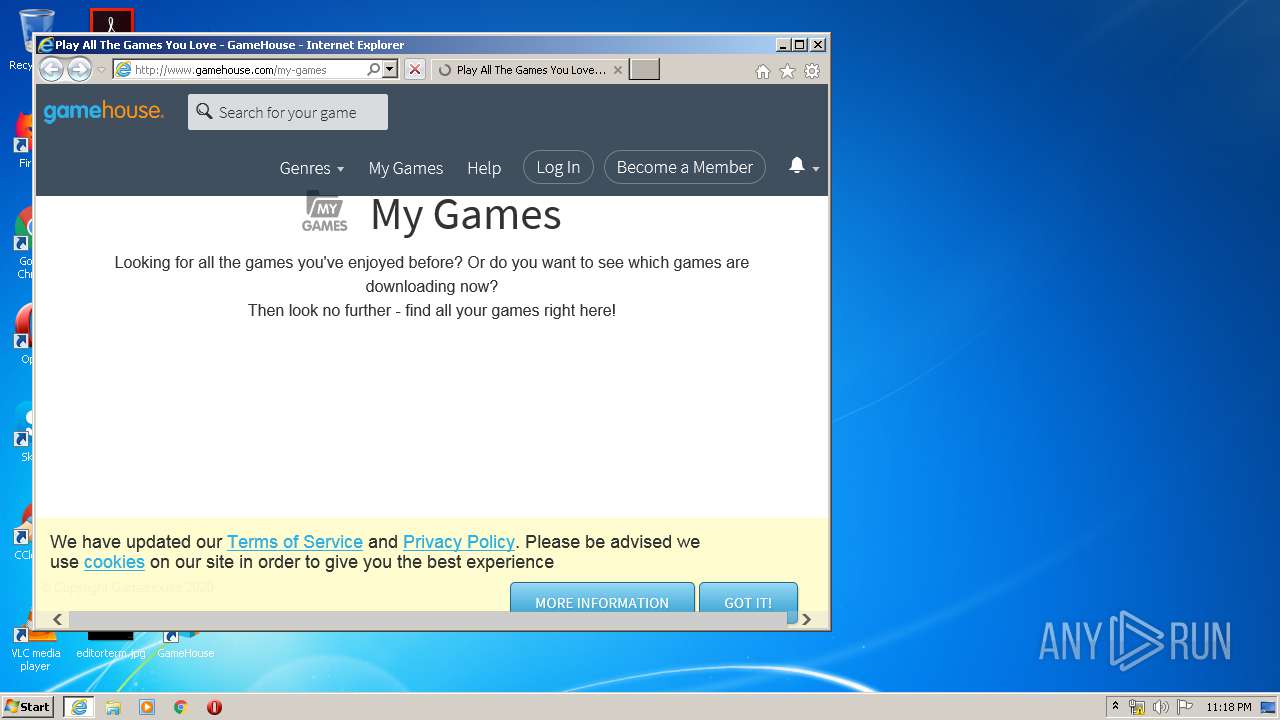
- iexplore.exe (PID: 4068)
INFO
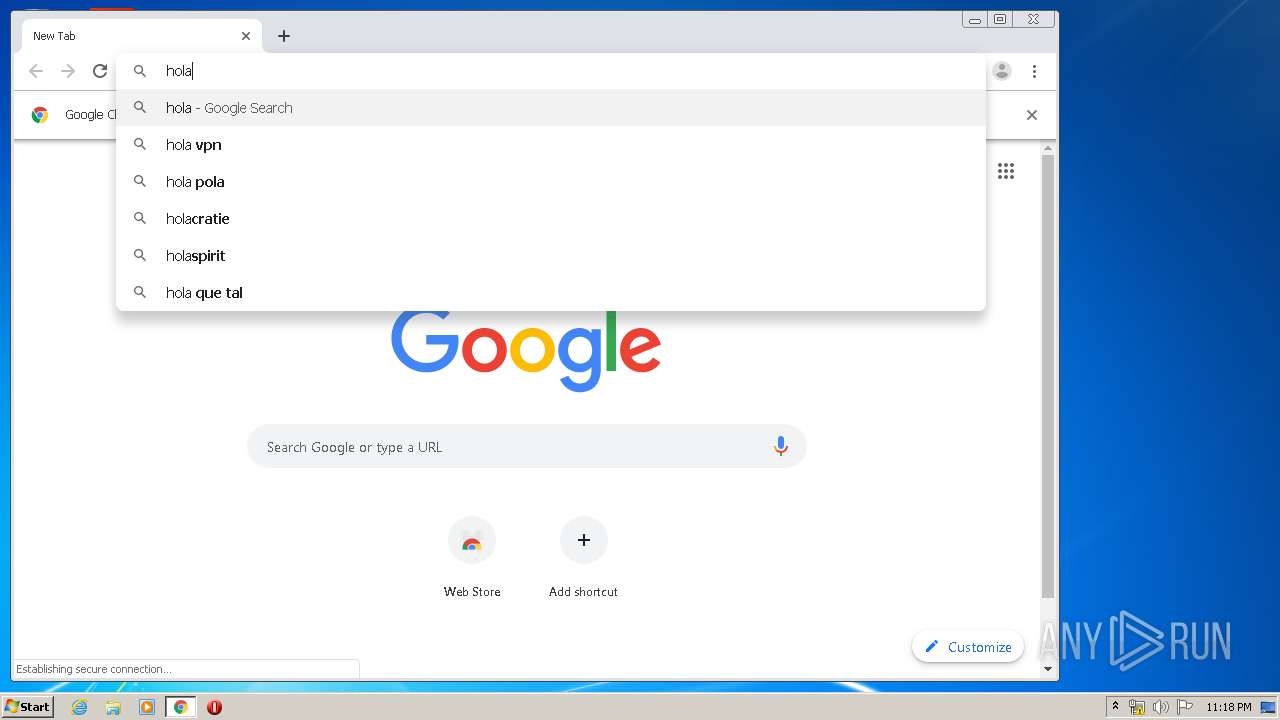
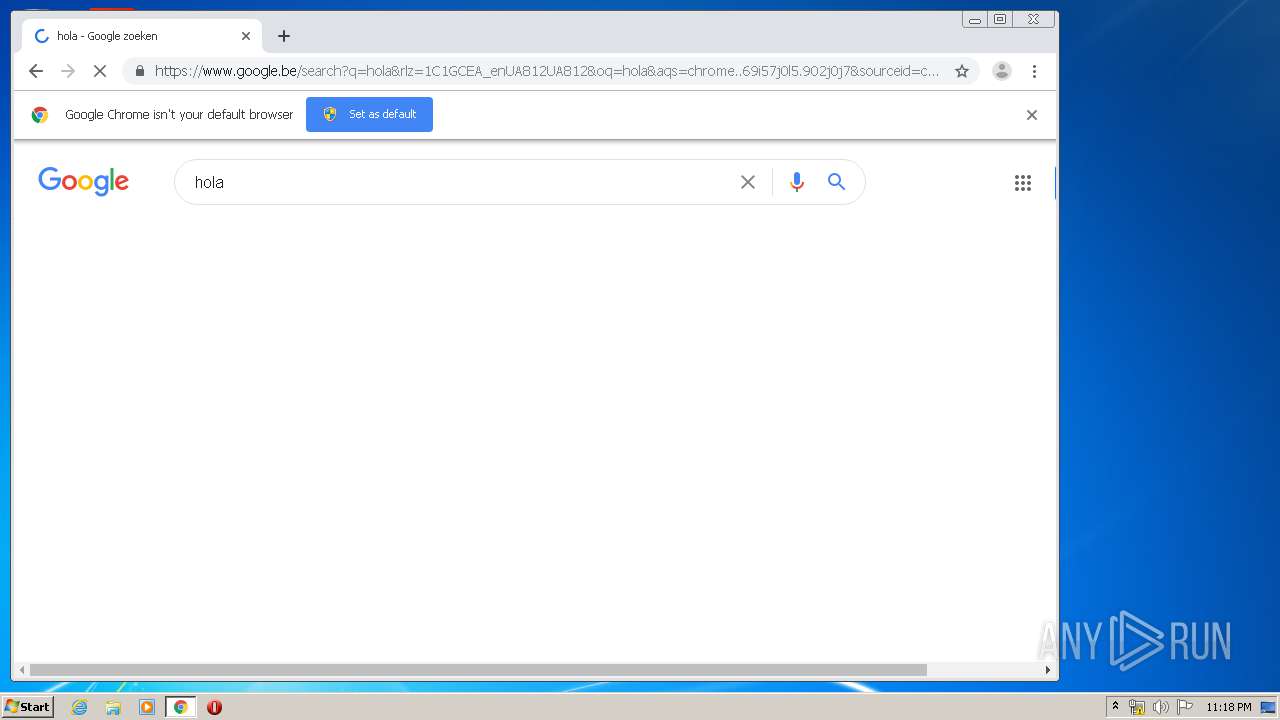
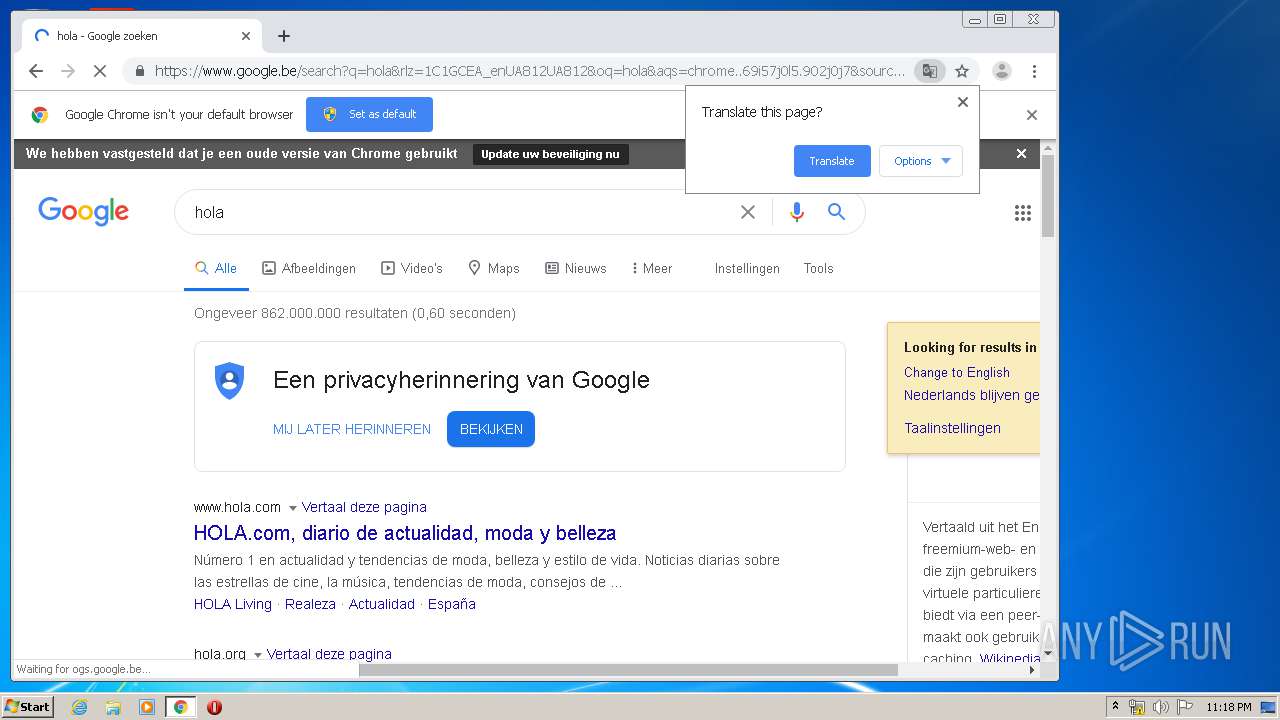
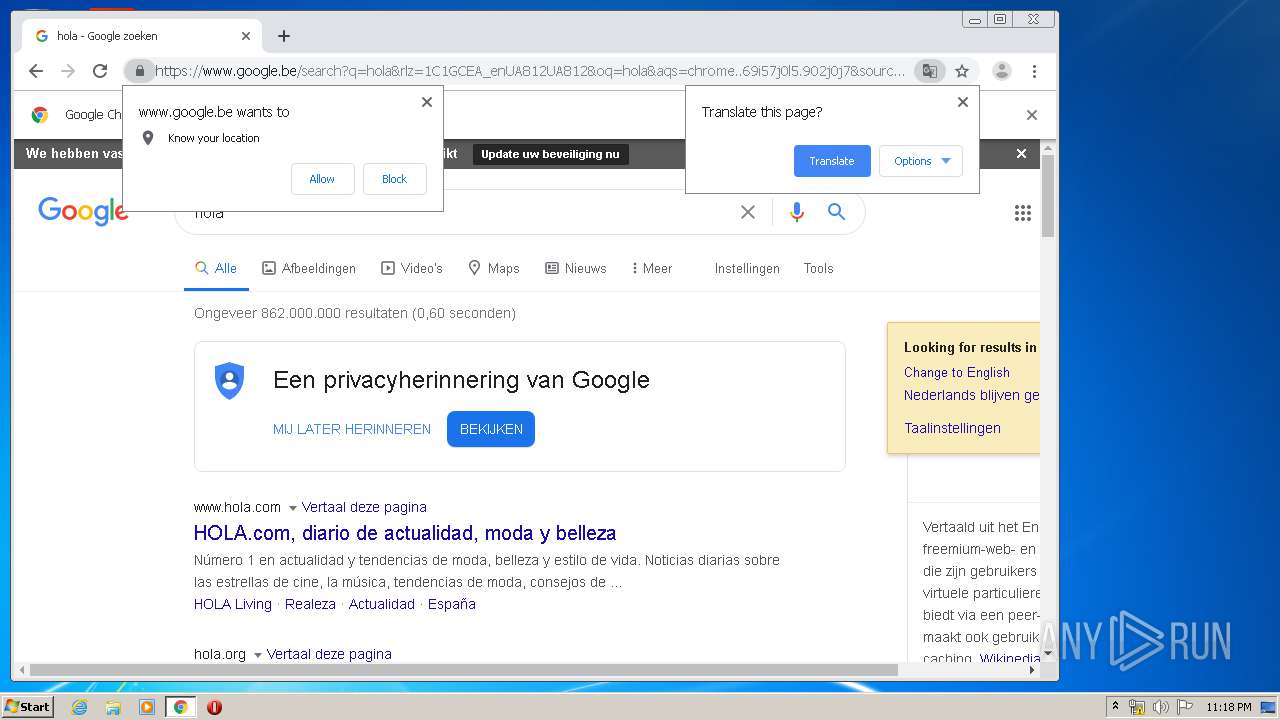
Manual execution by user
- chrome.exe (PID: 3704)
Reads the hosts file
- chrome.exe (PID: 620)
- chrome.exe (PID: 3704)
Application launched itself
- iexplore.exe (PID: 4068)
- chrome.exe (PID: 3704)
Reads Internet Cache Settings
- iexplore.exe (PID: 4068)
- iexplore.exe (PID: 2240)
Changes internet zones settings
- iexplore.exe (PID: 4068)
Reads internet explorer settings
- iexplore.exe (PID: 2240)
Creates files in the user directory
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 4068)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2240)
Reads settings of System Certificates
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 4068)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4068)
Changes settings of System certificates
- iexplore.exe (PID: 4068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:38:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30de |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.60.20.0 |
| ProductVersionNumber: | 8.60.20.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | GameHouse |
| FileDescription: | GameHouse Games |
| FileVersion: | 8.60.20 |
| LegalCopyright: | Copyright (c) 2012 GameHouse |
| ProductName: | GameHouse Games v8.60 |
| ProductVersion: | GameHouse Games v8.60.20 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2015 05:38:49 |
| Detected languages: |
|
| CompanyName: | GameHouse |
| FileDescription: | GameHouse Games |
| FileVersion: | 8.60.20 |
| LegalCopyright: | Copyright (c) 2012 GameHouse |
| ProductName: | GameHouse Games v8.60 |
| ProductVersion: | GameHouse Games v8.60.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2015 05:38:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005AC1 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42222 |
.rdata | 0x00007000 | 0x0000115E | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14378 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.14806 |
.ndata | 0x00025000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x00013128 | 0x00013200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.39251 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19265 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.95426 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 5.12075 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.2865 | 6760 | UNKNOWN | English - United States | RT_ICON |
5 | 5.4012 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.36732 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 5.44866 | 2440 | UNKNOWN | English - United States | RT_ICON |
8 | 5.88913 | 2216 | UNKNOWN | English - United States | RT_ICON |
9 | 5.64819 | 1720 | UNKNOWN | English - United States | RT_ICON |
10 | 5.48119 | 1384 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
81
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13887309221475637 --mojo-platform-channel-handle=3572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16628939878563870906 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=652327623290935439 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\GameHouse Games\aminstantservice.exe" --service-run | C:\Program Files\GameHouse Games\aminstantservice.exe | services.exe | ||||||||||||
User: SYSTEM Company: GameHouse Integrity Level: SYSTEM Description: GameHouse GamesPlayer Exit code: 0 Version: 8.60.20 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4068 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7122502584108436325 --mojo-platform-channel-handle=4556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\Temp\texttwist-2.exe" | C:\Users\admin\AppData\Local\Temp\texttwist-2.exe | explorer.exe | ||||||||||||
User: admin Company: GameHouse Integrity Level: HIGH Description: GameHouse Games Exit code: 0 Version: 8.60.20 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3826534000130990974 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12813910061971509011 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,900195768938885942,7267958033340269772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12008818604665131070 --mojo-platform-channel-handle=3344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 899
Read events
2 017
Write events
4 634
Delete events
2 248
Modification events
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\GameHouse Games\aminstantservice.exe | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | DisplayVersion |
Value: 8.60.20 | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | DisplayName |
Value: GameHouse Games | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\GameHouse Games\ | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\GameHouse Games\ | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | ServicePath |
Value: C:\Program Files\GameHouse Games\aminstantservice.exe | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\GameHouse Games\uninst.exe | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | Publisher |
Value: GameHouse | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | VersionMajor |
Value: 8 | |||
| (PID) Process: | (2500) texttwist-2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GameHouse Games |
| Operation: | write | Name: | VersionMinor |
Value: 60 | |||
Executable files
6
Suspicious files
103
Text files
756
Unknown types
88
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EBDC3B2-E78.pma | — | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\825e1fd9-fcd2-434f-9094-0bd8173981e0.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | texttwist-2.exe | C:\Program Files\GameHouse Games\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 2500 | texttwist-2.exe | C:\Users\admin\Desktop\GameHouse.URL | text | |
MD5:— | SHA256:— | |||
| 2500 | texttwist-2.exe | C:\Program Files\GameHouse Games\aminstantservice.exe | executable | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa94f14.TMP | text | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
289
TCP/UDP connections
163
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
620 | chrome.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2240 | iexplore.exe | GET | 200 | 152.199.23.112:80 | http://cdn.ghstatic.com/gh/website/991d033d825bcf1e977547225f166c5dfa0ac42a/member/scripts/libs/videojs/dist/video-js.min.css | US | text | 13.3 Kb | unknown |
2240 | iexplore.exe | GET | 200 | 152.199.23.112:80 | http://cdn.ghstatic.com/gh/website/991d033d825bcf1e977547225f166c5dfa0ac42a/styles/css/main_shared.css | US | text | 7.06 Kb | unknown |
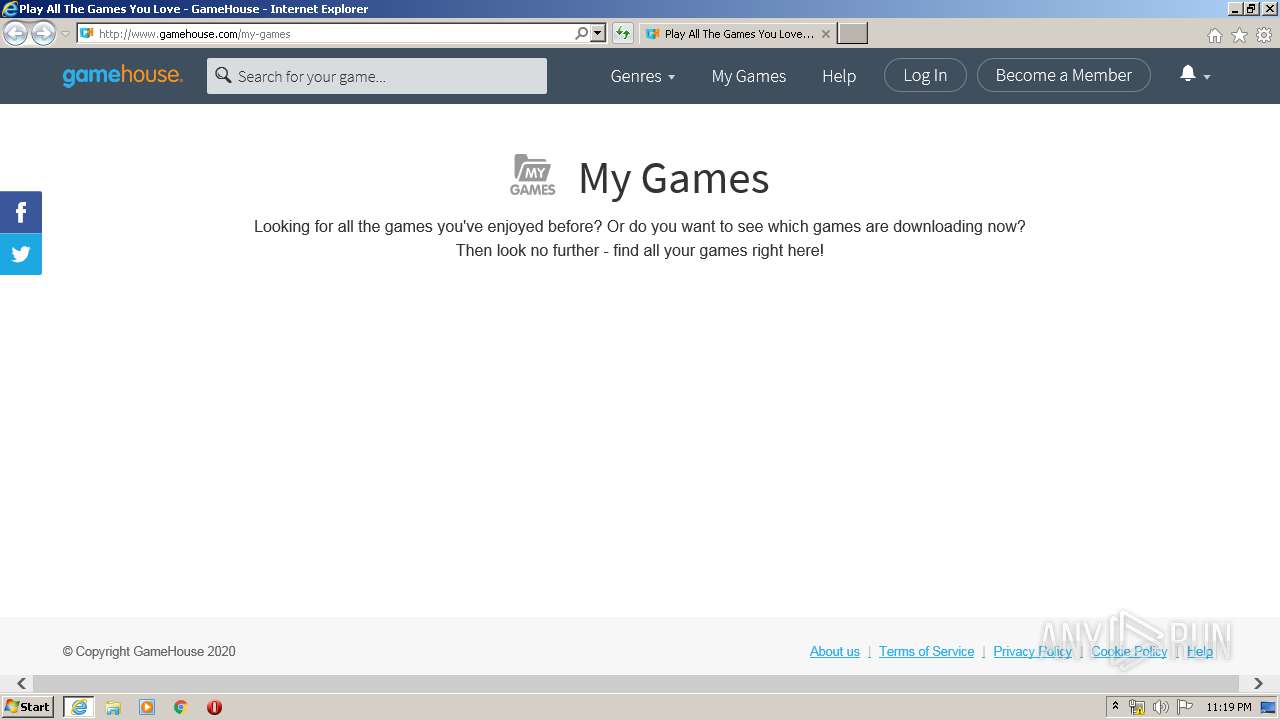
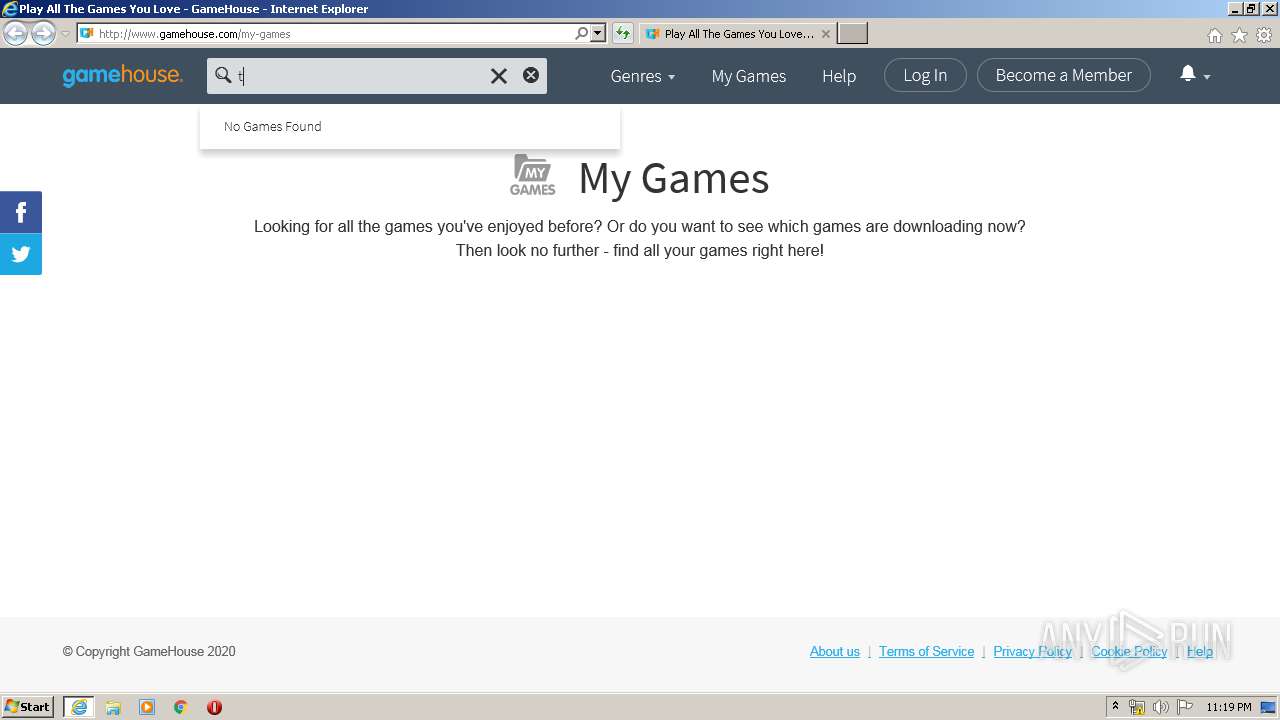
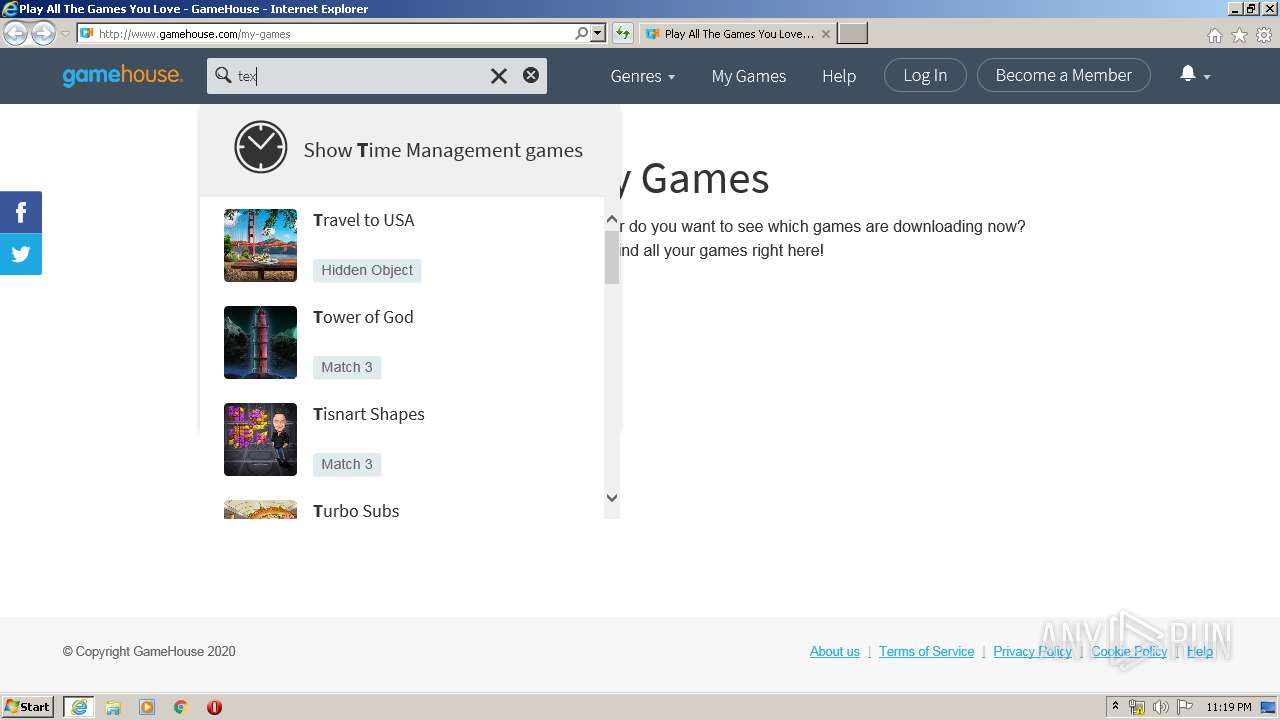
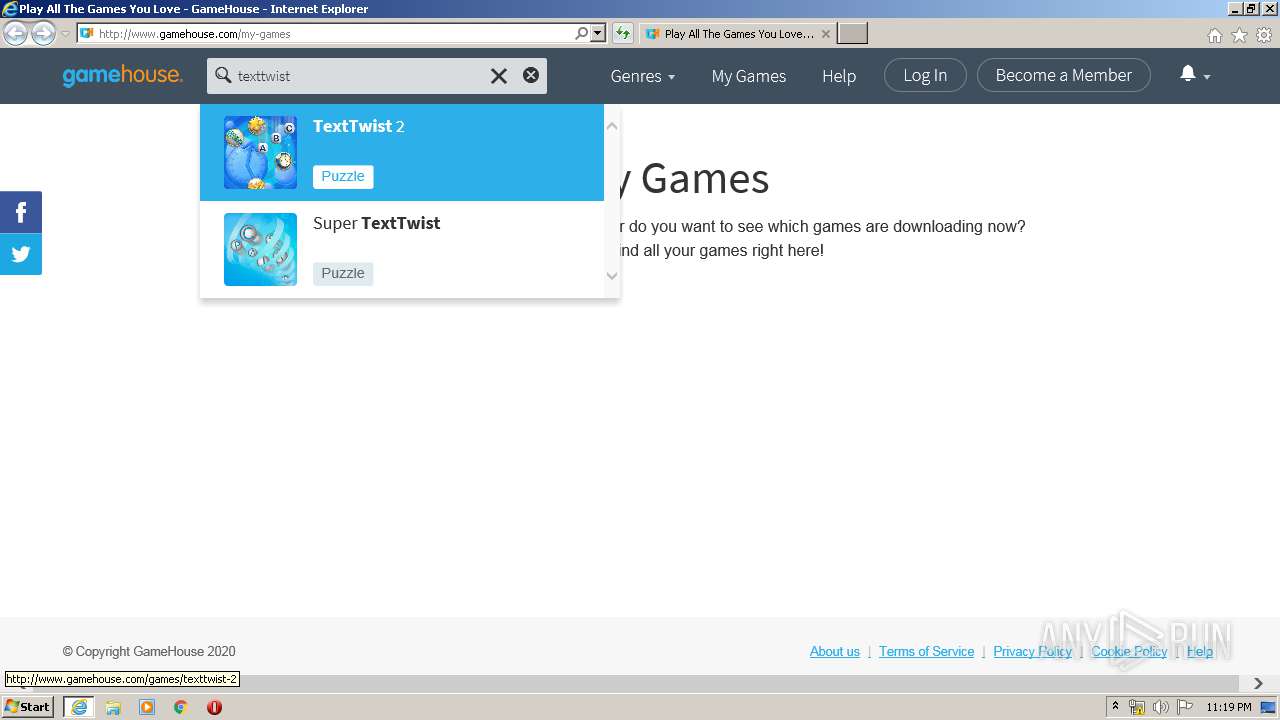
2240 | iexplore.exe | GET | 200 | 91.192.226.195:80 | http://www.gamehouse.com/ | PL | html | 4.22 Kb | suspicious |
2240 | iexplore.exe | GET | 200 | 216.58.208.42:80 | http://imasdk.googleapis.com/js/sdkloader/ima3.js | US | text | 89.5 Kb | whitelisted |
620 | chrome.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
620 | chrome.exe | GET | 200 | 172.217.132.42:80 | http://r5---sn-5hne6nsk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.104.186.91&mm=28&mn=sn-5hne6nsk&ms=nvh&mt=1589494636&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2240 | iexplore.exe | GET | 200 | 152.199.23.112:80 | http://cdn.ghstatic.com/gh/website/991d033d825bcf1e977547225f166c5dfa0ac42a/styles/css/main_member.css | US | text | 13.8 Kb | unknown |
2240 | iexplore.exe | GET | 200 | 216.58.205.234:80 | http://fonts.googleapis.com/css?family=Source+Sans+Pro:400,700,300 | US | text | 270 b | whitelisted |
2240 | iexplore.exe | GET | 200 | 152.199.23.112:80 | http://cdn.ghstatic.com/gh/website/991d033d825bcf1e977547225f166c5dfa0ac42a/member/scripts/libs/angular-messages.min.js | US | text | 1.29 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
620 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 172.217.23.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1520 | aminstantservice.exe | 91.192.226.195:80 | www.gamehouse.com | Intersec Maciej Jan Broniarz | PL | suspicious |
620 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 216.58.212.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 172.217.132.41:80 | r4---sn-5hne6nsk.gvt1.com | Google Inc. | US | whitelisted |
620 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gamehouse.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |