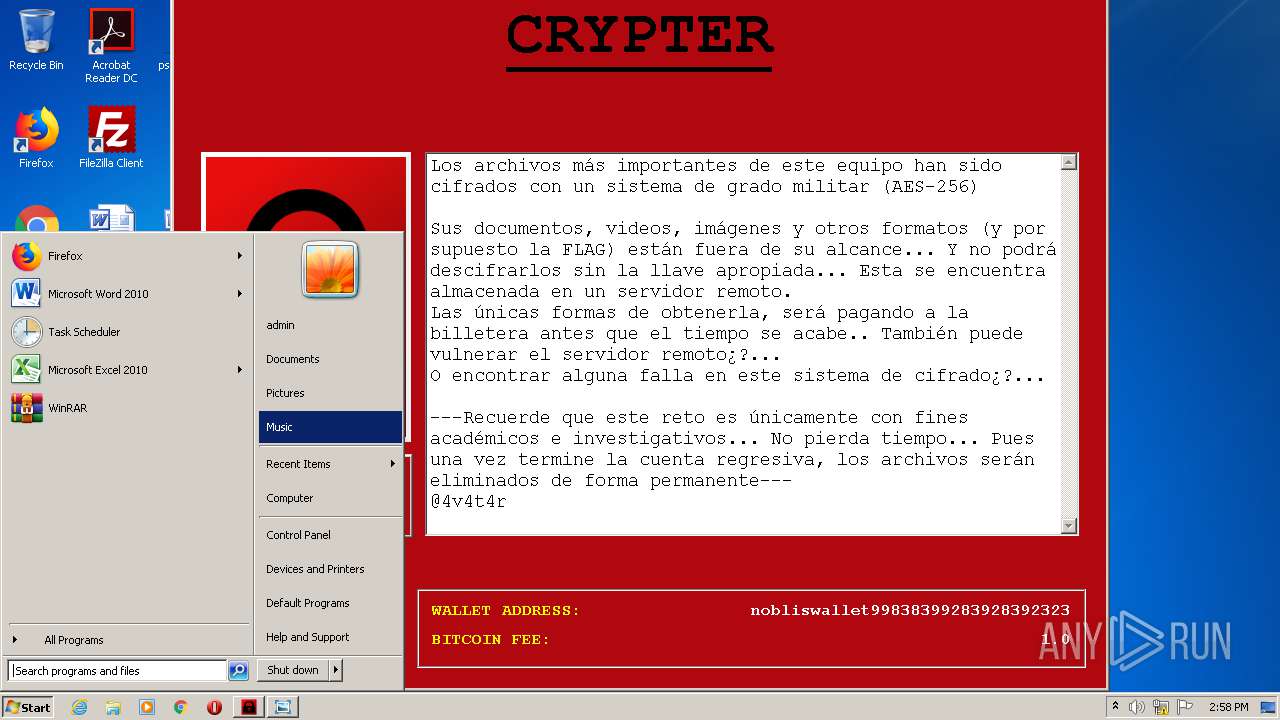
| File name: | NOBLIS RANSOMWARE.exe |
| Full analysis: | https://app.any.run/tasks/0fbc5c44-2a1f-4068-a2a2-809a14c0ce4c |
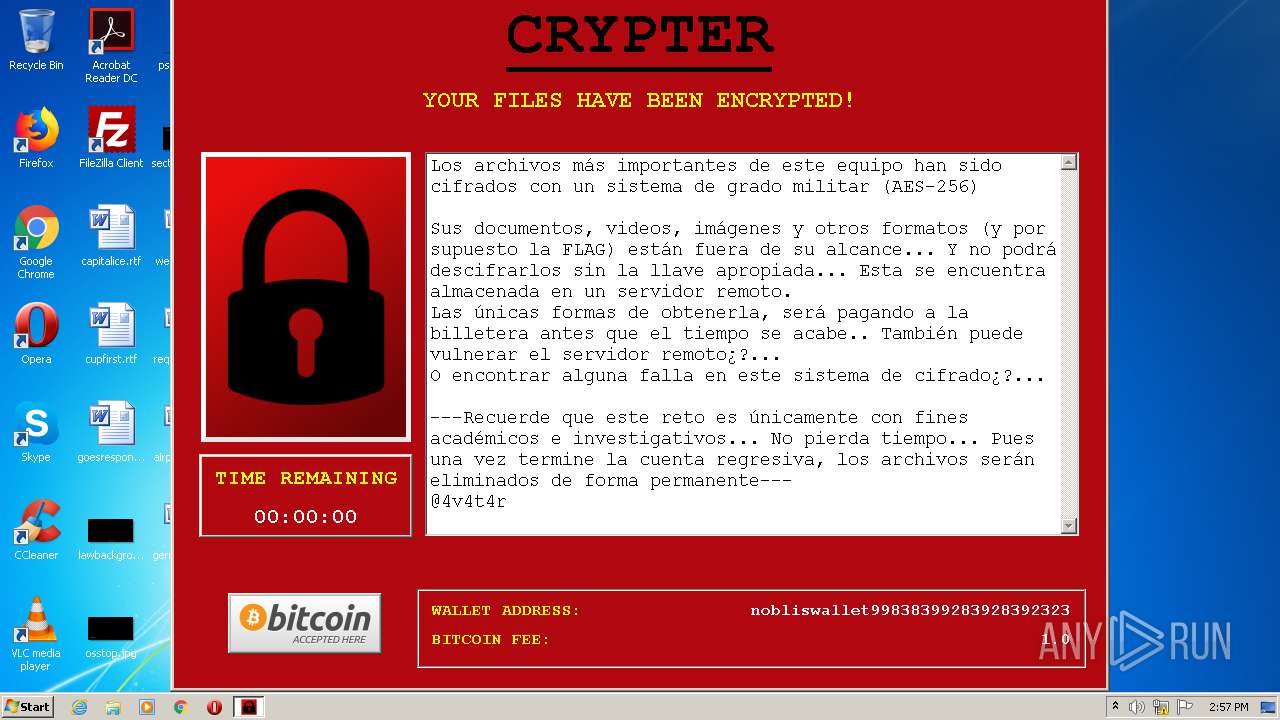
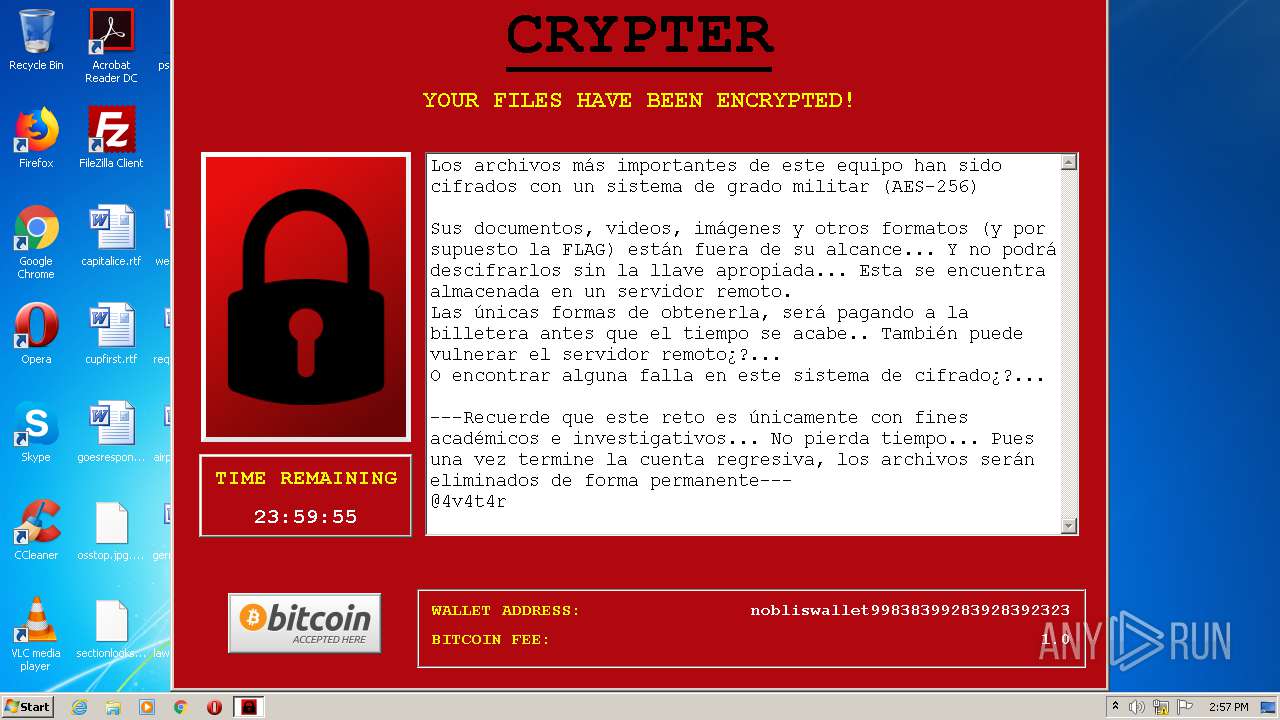
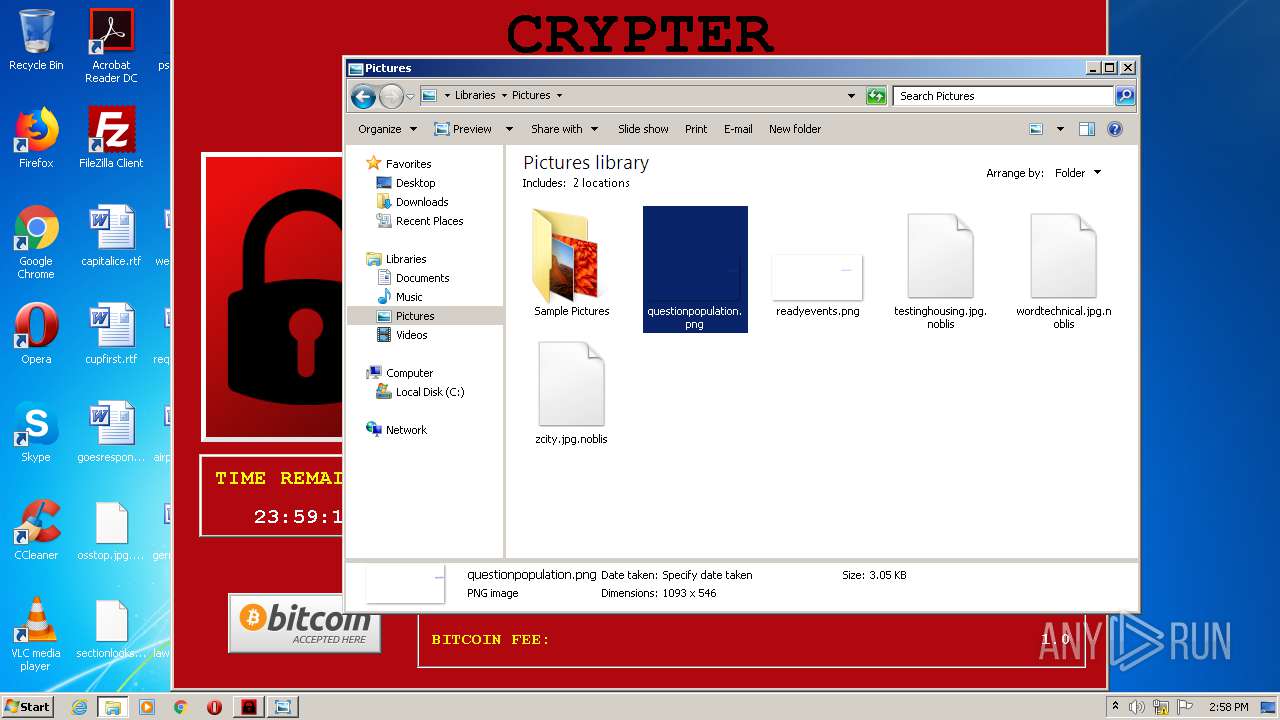
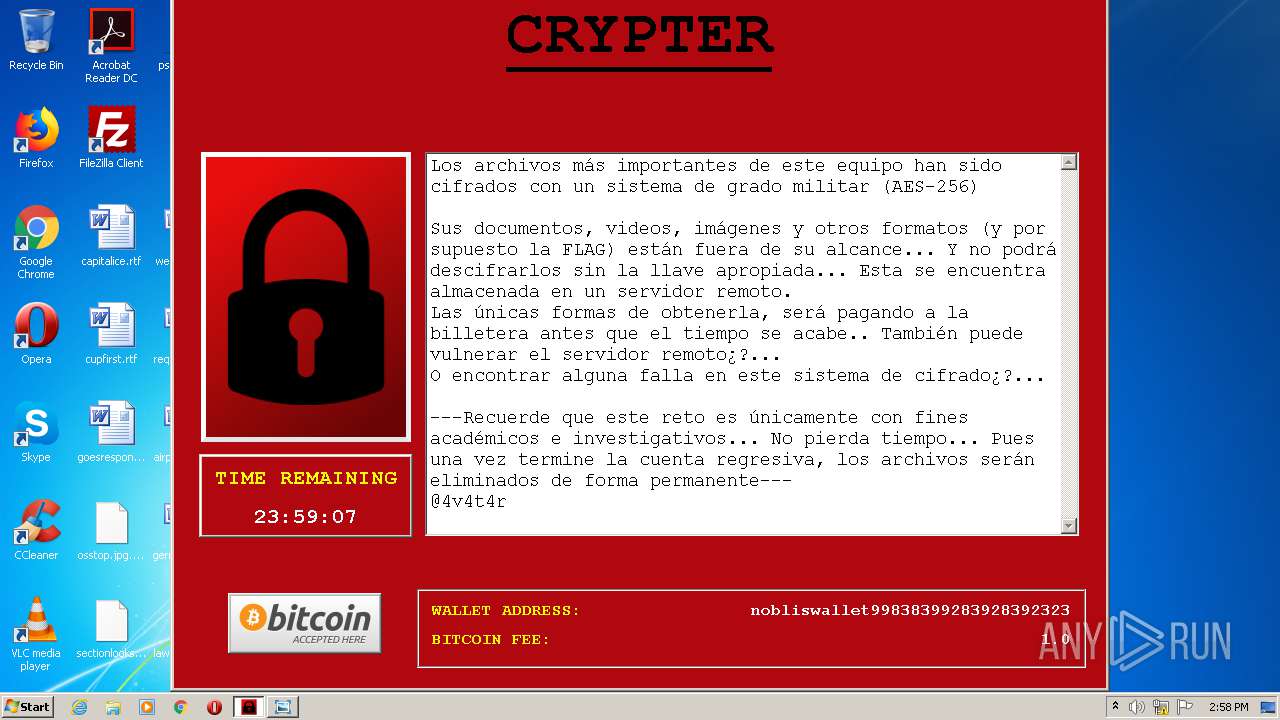
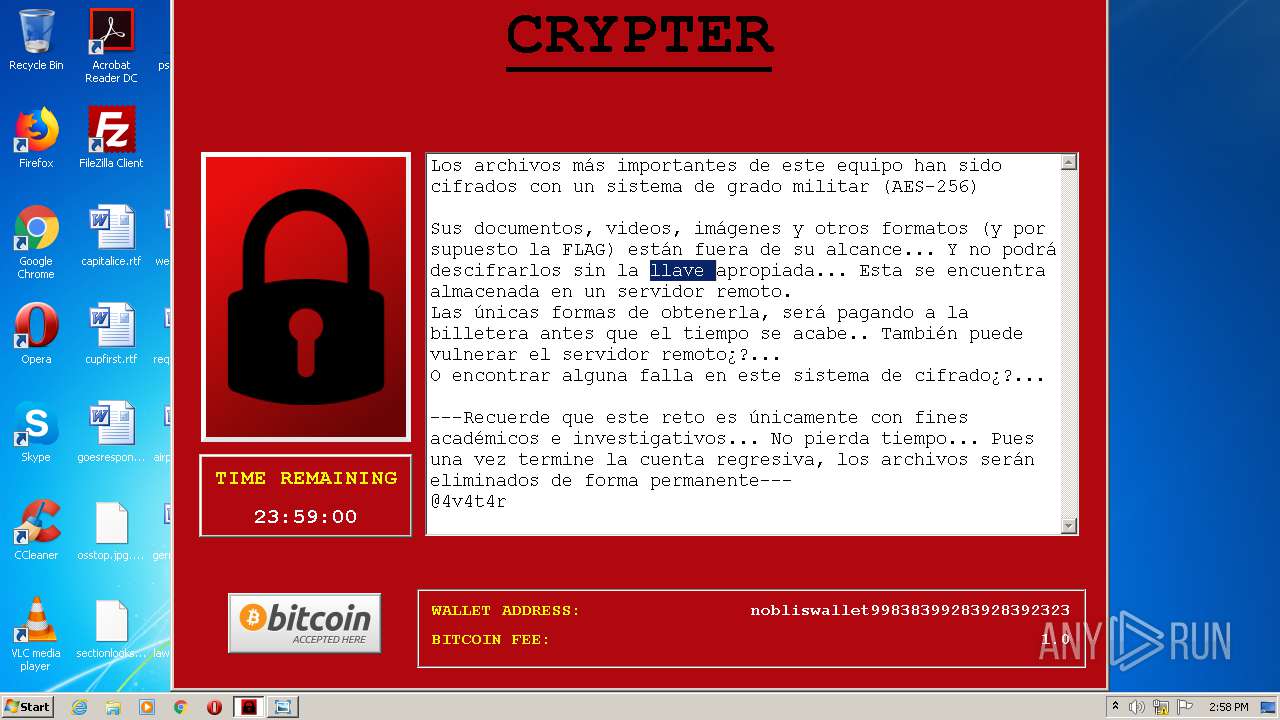
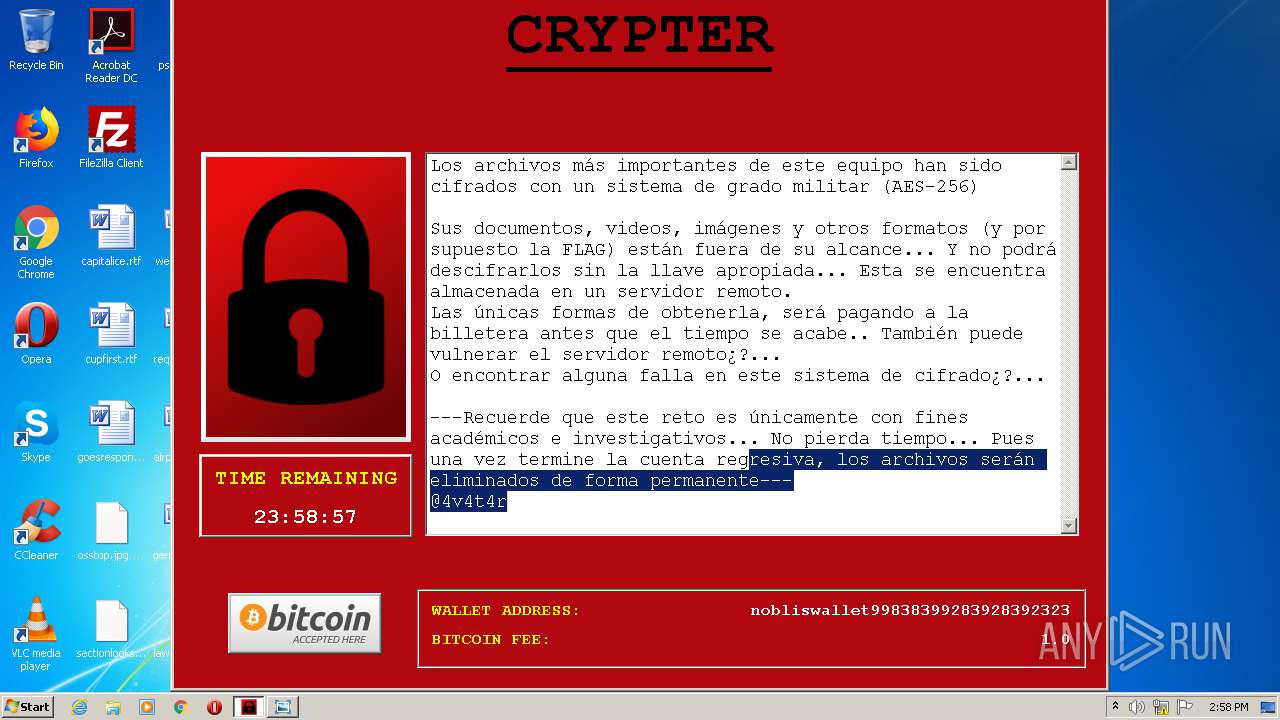
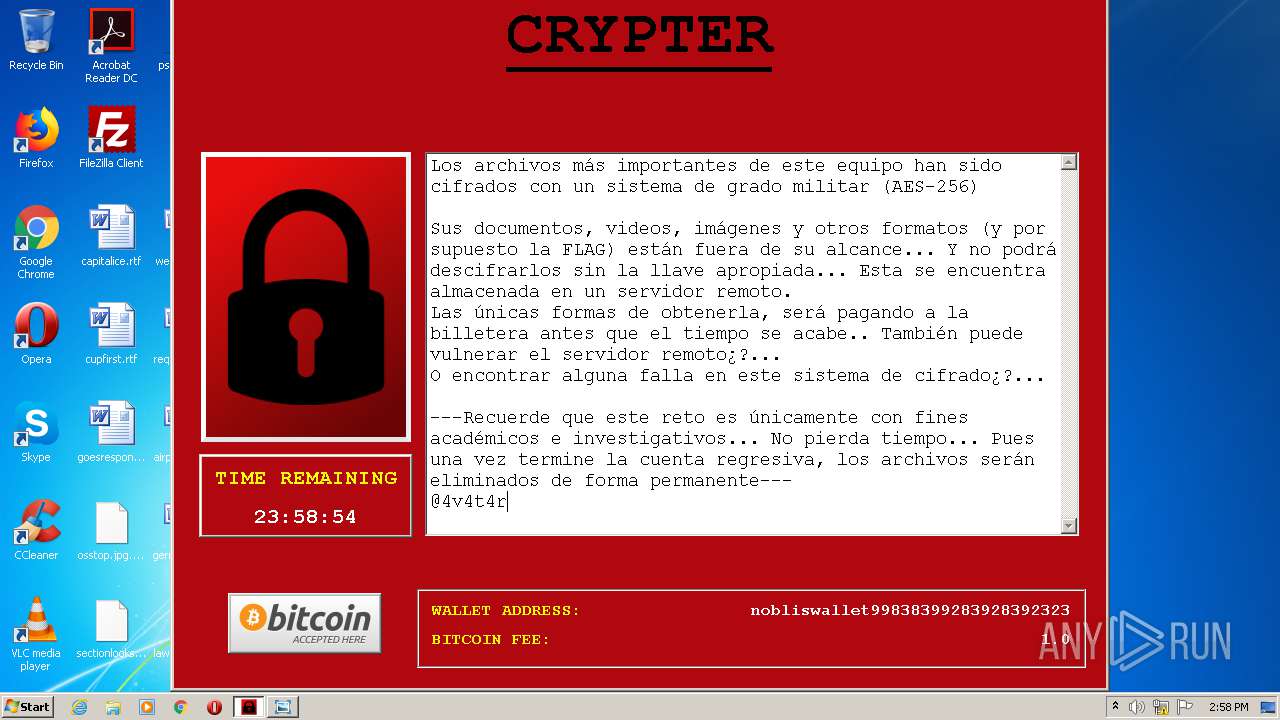
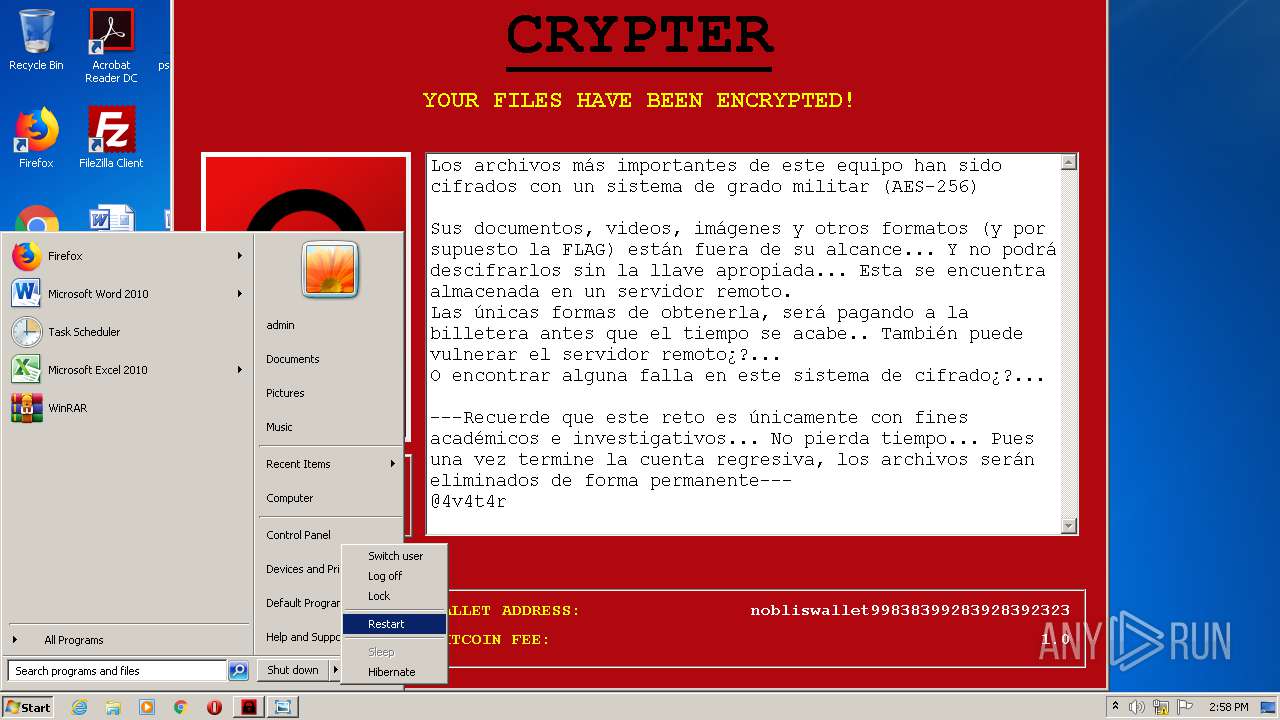
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 14:57:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 3BEEE8D7F55CD8298FCB009AA6EF6AAE |
| SHA1: | 672A992EA934A0CBA07CA07B80B62493E95C584D |
| SHA256: | F0C292785905838D08B27BB99AB260B43FD8DE580DE80017FDAAAB3C3D53D8A6 |
| SSDEEP: | 196608:gUWfTu5s5E6s6eLL1mkJ2Z9Jq5dOYo+SJVTXOD0ch:gUWfTuK5E6s6sBmKk9JMo5/eN |
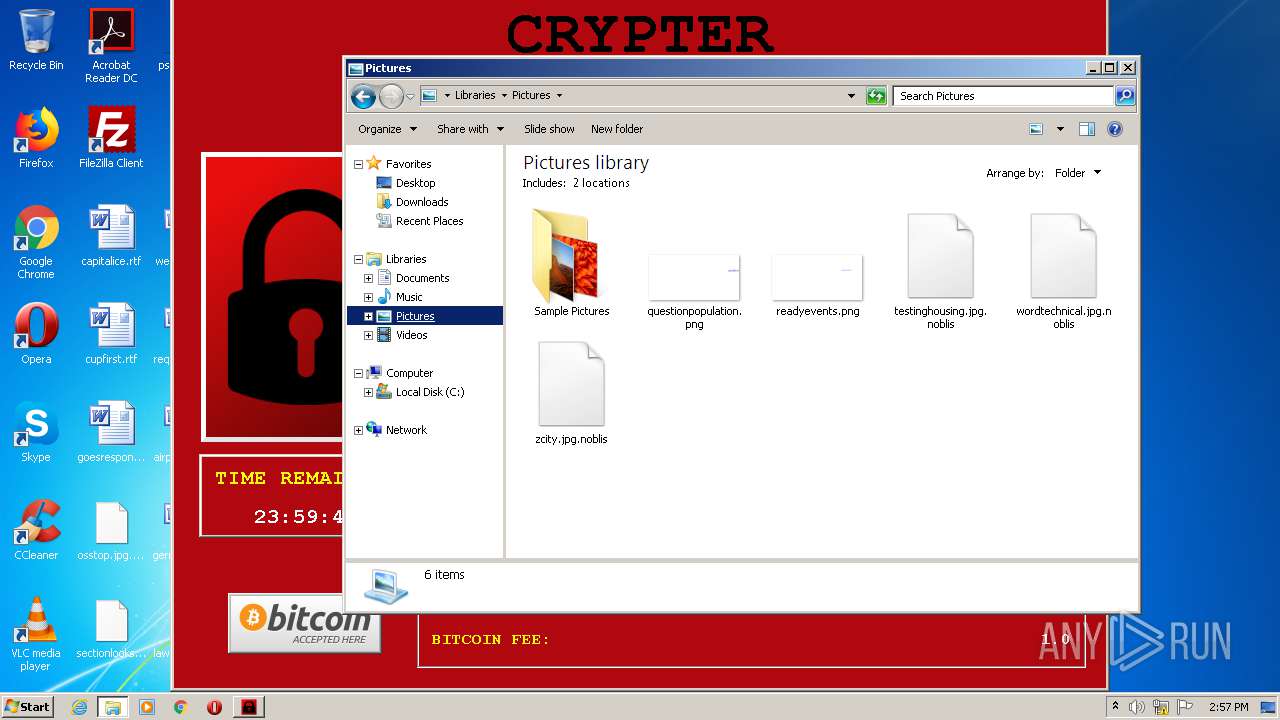
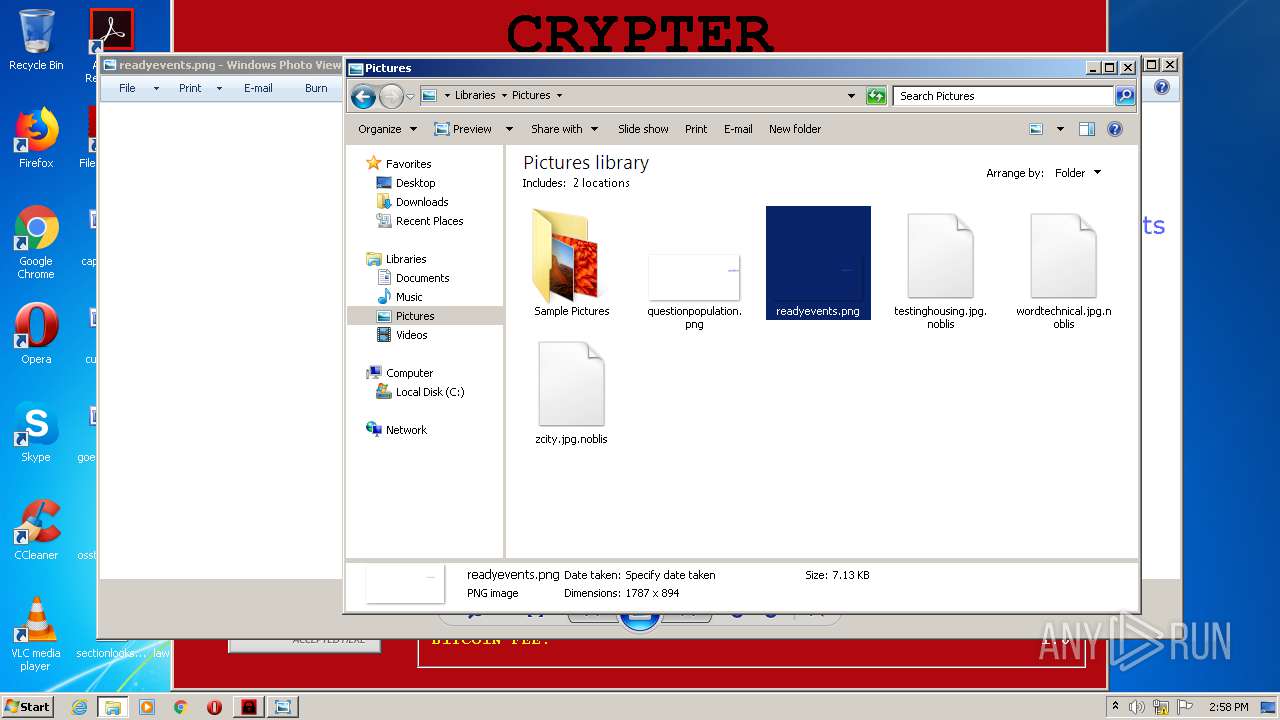
MALICIOUS
Drops executable file immediately after starts
- NOBLIS RANSOMWARE.exe (PID: 2784)
Loads dropped or rewritten executable
- NOBLIS RANSOMWARE.exe (PID: 3476)
Actions looks like stealing of personal data
- NOBLIS RANSOMWARE.exe (PID: 3476)
SUSPICIOUS
Application launched itself
- NOBLIS RANSOMWARE.exe (PID: 2784)
Drops a file that was compiled in debug mode
- NOBLIS RANSOMWARE.exe (PID: 2784)
Executable content was dropped or overwritten
- NOBLIS RANSOMWARE.exe (PID: 2784)
Loads Python modules
- NOBLIS RANSOMWARE.exe (PID: 3476)
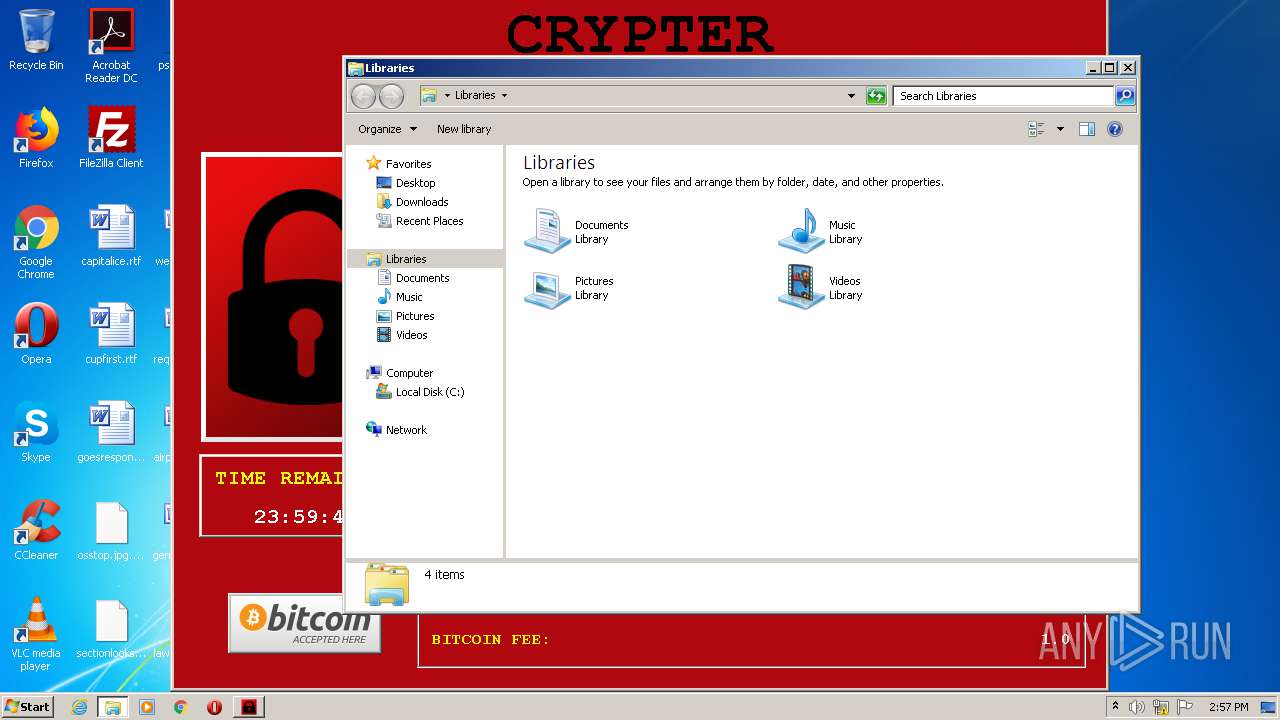
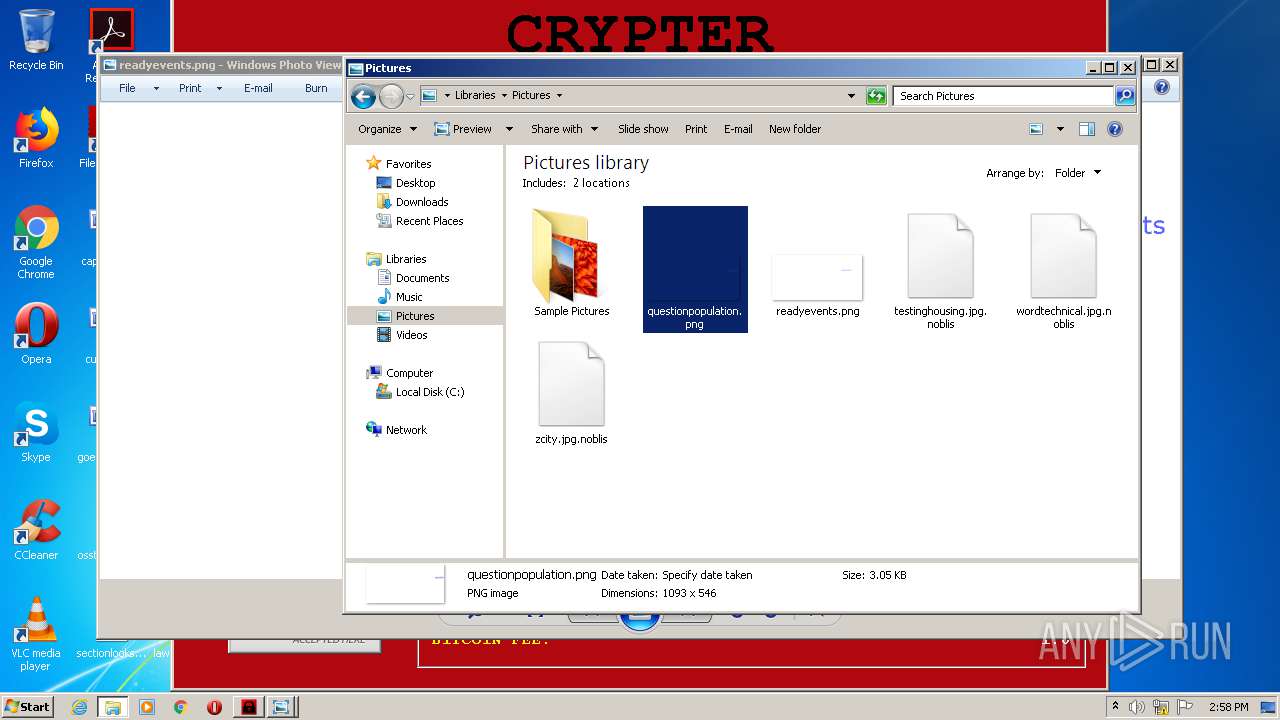
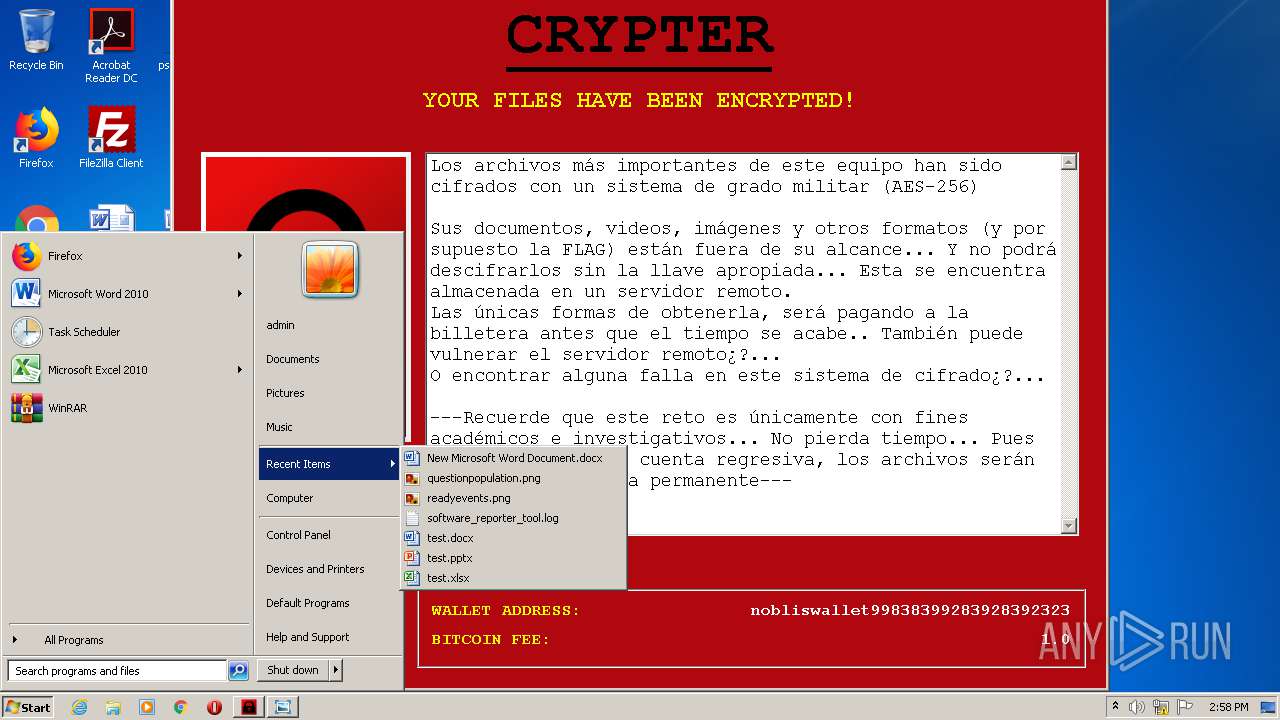
Creates files in the user directory
- NOBLIS RANSOMWARE.exe (PID: 3476)
Executed via COM
- DllHost.exe (PID: 3524)
INFO
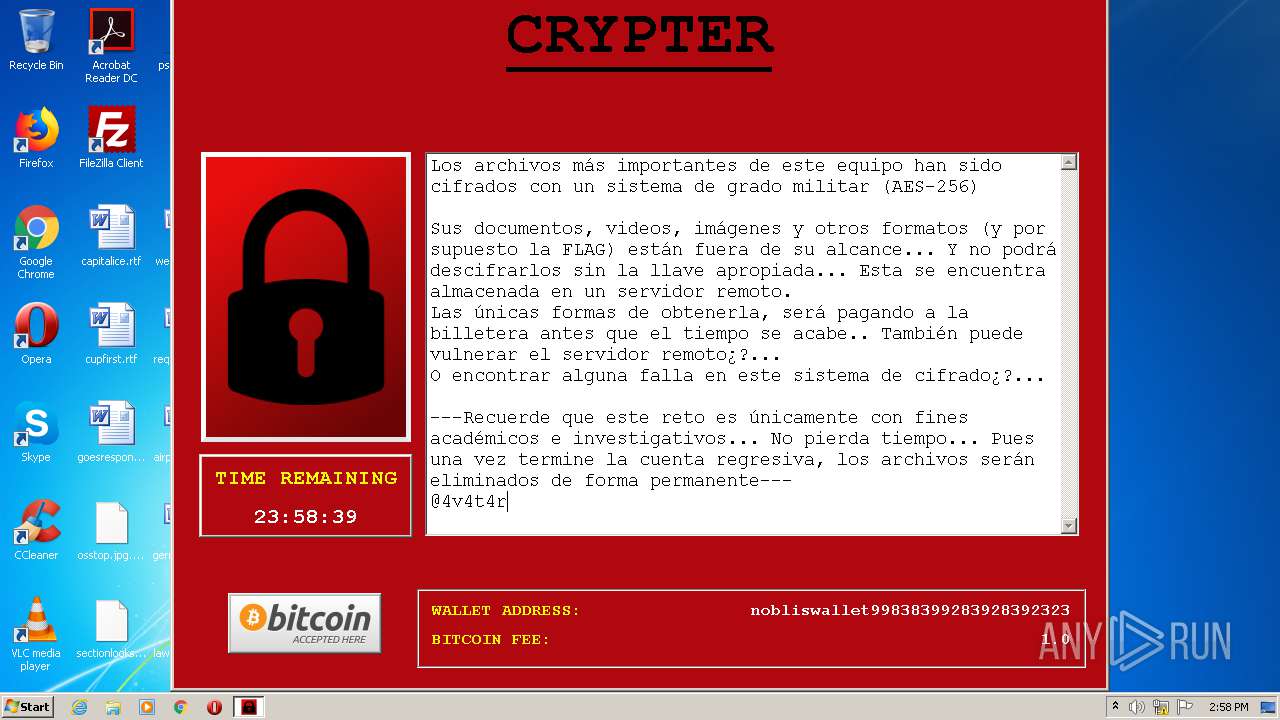
Dropped object may contain Bitcoin addresses
- NOBLIS RANSOMWARE.exe (PID: 2784)
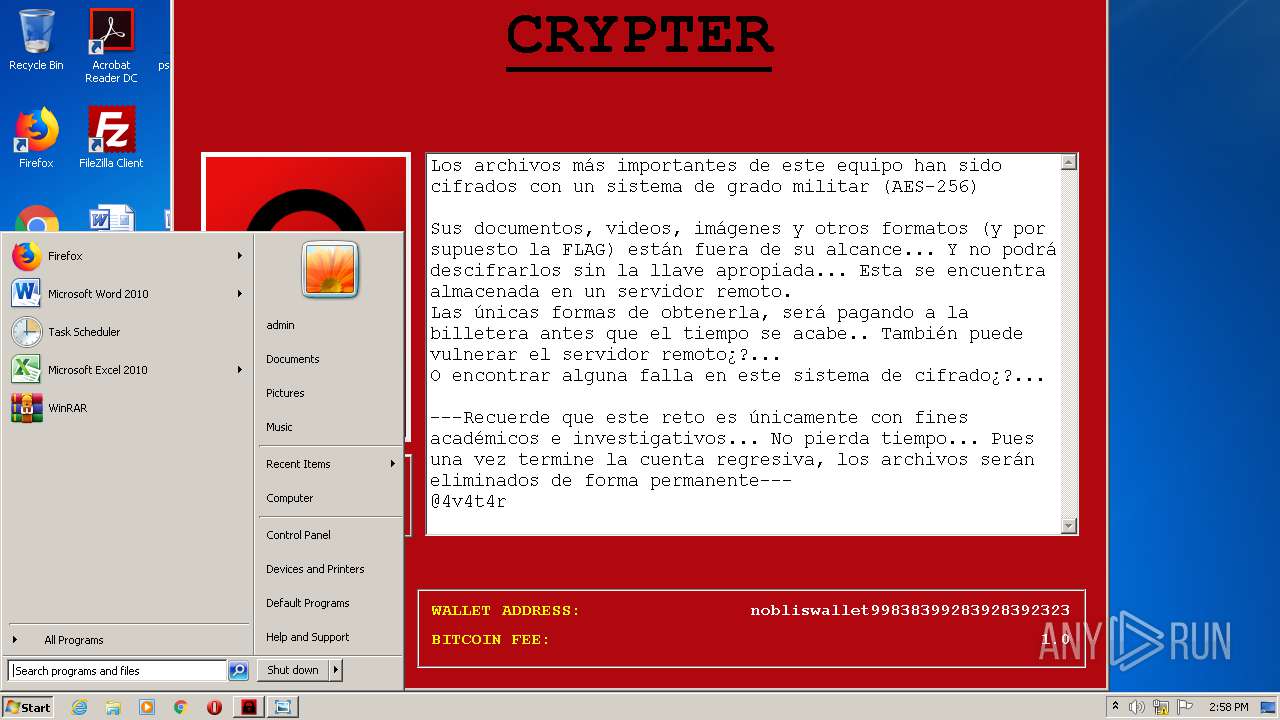
Manual execution by user
- explorer.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.24 |
| CodeSize: | 36864 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | 135168 |
| EntryPoint: | 0x29750 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| TLS Callbacks: | 1 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00021000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00022000 | 0x00009000 | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95097 |
.rsrc | 0x0002B000 | 0x00006000 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.78761 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.81158 | 118 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 3.62348 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
2 | 3.86375 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.80567 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.1418 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.45689 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.1431 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.41413 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.59141 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
USER32.dll |
WS2_32.dll |
msvcrt.dll |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2784 | "C:\Users\admin\AppData\Local\Temp\NOBLIS RANSOMWARE.exe" | C:\Users\admin\AppData\Local\Temp\NOBLIS RANSOMWARE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Modules
| |||||||||||||||
| 2996 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Users\admin\AppData\Local\Temp\NOBLIS RANSOMWARE.exe" | C:\Users\admin\AppData\Local\Temp\NOBLIS RANSOMWARE.exe | NOBLIS RANSOMWARE.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3524 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
412
Read events
405
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3476) NOBLIS RANSOMWARE.exe | Key: | HKEY_CURRENT_USER\Software\Crypter |
| Operation: | write | Name: | (default) |
Value: 1606661849 | |||
| (PID) Process: | (3524) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3524) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3524) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3524) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3524) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
Executable files
35
Suspicious files
38
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Cipher._DES.pyd | executable | |
MD5:8ED4C12155440AAC0DEA7B3B87DD1E93 | SHA256:4F1F636AA4F23AFACF039B03EF75131307A5AA0C9FB1C7046DF2B3C0AF0B8CDD | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Cipher._AES.pyd | executable | |
MD5:5E86145A6DE363FA7C98304AD117428D | SHA256:18A3DBA419252417F7BEA8E1D2A4D804ACA8D00FBA9F54DD598266C2F38C4F9B | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Hash._SHA256.pyd | executable | |
MD5:A5525E17F33ADAF026DDA150E51E3BB7 | SHA256:39421B3B4F3DB77E0B9B312F1367315EB8FBE0778998FF500A4C23A8874544A3 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\bz2.pyd | executable | |
MD5:ABE3F997A7DE5E9B806CBDEBDFA43247 | SHA256:299477F7AC13E3A8EB3BDAC2308F9927101DAFB86342B2C12870F260F57FC4C5 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Util.strxor.pyd | executable | |
MD5:B3391064FF93FD4B32B166CA82161216 | SHA256:5D5D2FEF985003F5B9C5DE61CB5E0B93AD58206E2E57BD3EDA79DE5D89BF4788 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Microsoft.VC90.CRT.manifest | xml | |
MD5:FEDFDF2256720BADEFF9205E784B5DC8 | SHA256:6373FB8261AF01506DC57DEE535A0BE800F3A59B18B0CC1E276807C746329FF6 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Cipher._DES3.pyd | executable | |
MD5:A601CF7B8FB548D1C7462E4B44BFF48E | SHA256:4E4F1F5516C4549C671AB230FDE23FB36F5AD9C448819FA822AEBDADA3E4BE36 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\_hashlib.pyd | executable | |
MD5:D017532ABDFE0A1A0D3DB34D496B4B5B | SHA256:B62439AF70D43C1155042F907F54B1125A6A8D75CB4AF185ACDF9E8B8DC3F9FF | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\Crypto.Random.OSRNG.winrandom.pyd | executable | |
MD5:EFE96E08E4B8B5664648CB0C01D4249D | SHA256:28BFCFD50AF5D822F6DC1B42790695DAFEEF0F0D9511A4D62934FFA0681FE941 | |||
| 2784 | NOBLIS RANSOMWARE.exe | C:\Users\admin\AppData\Local\Temp\_MEI27842\select.pyd | executable | |
MD5:C230627A49C1F714185E18E7E5C3433B | SHA256:6ACF836F842EA680D11AD2F2B311EC7E5388D15C25FA0B5C46E9BC23D8066990 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
NOBLIS RANSOMWARE.exe | ..\..\src\msw\app.cpp(743): 'UnregisterClass(wxWindowNR)' failed with error 0x00000584 (class still has open windows.).
|