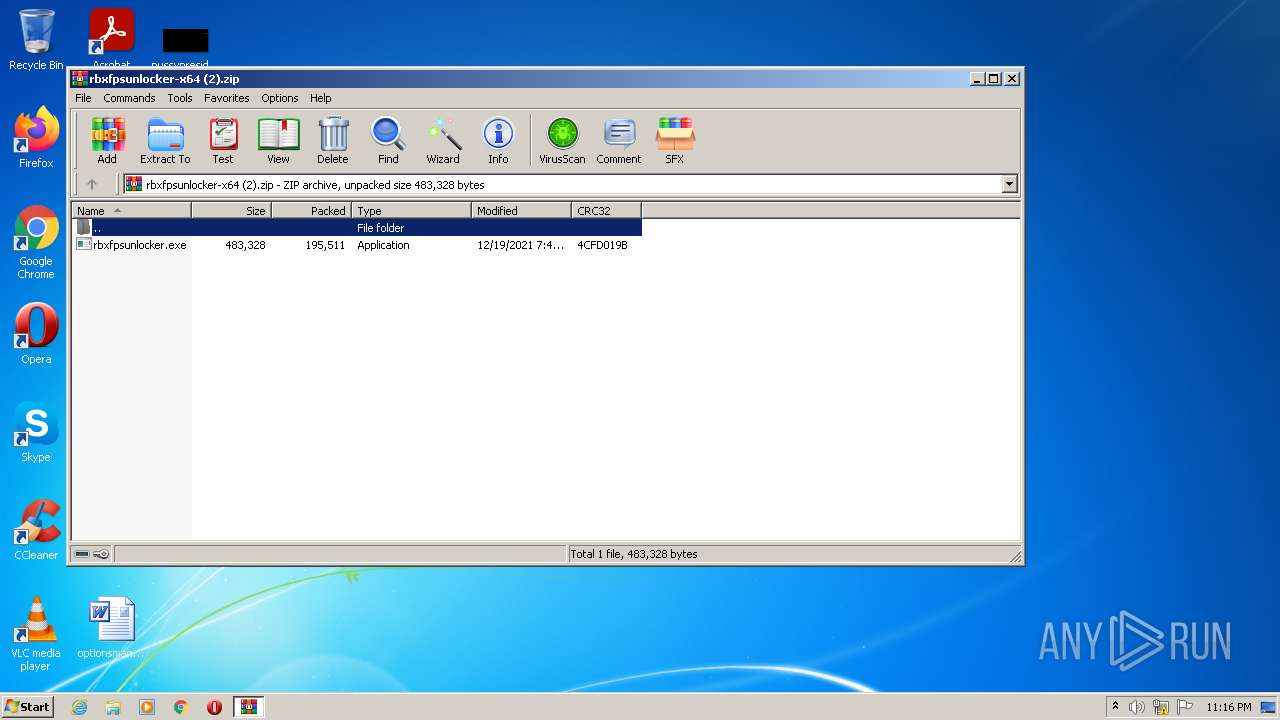
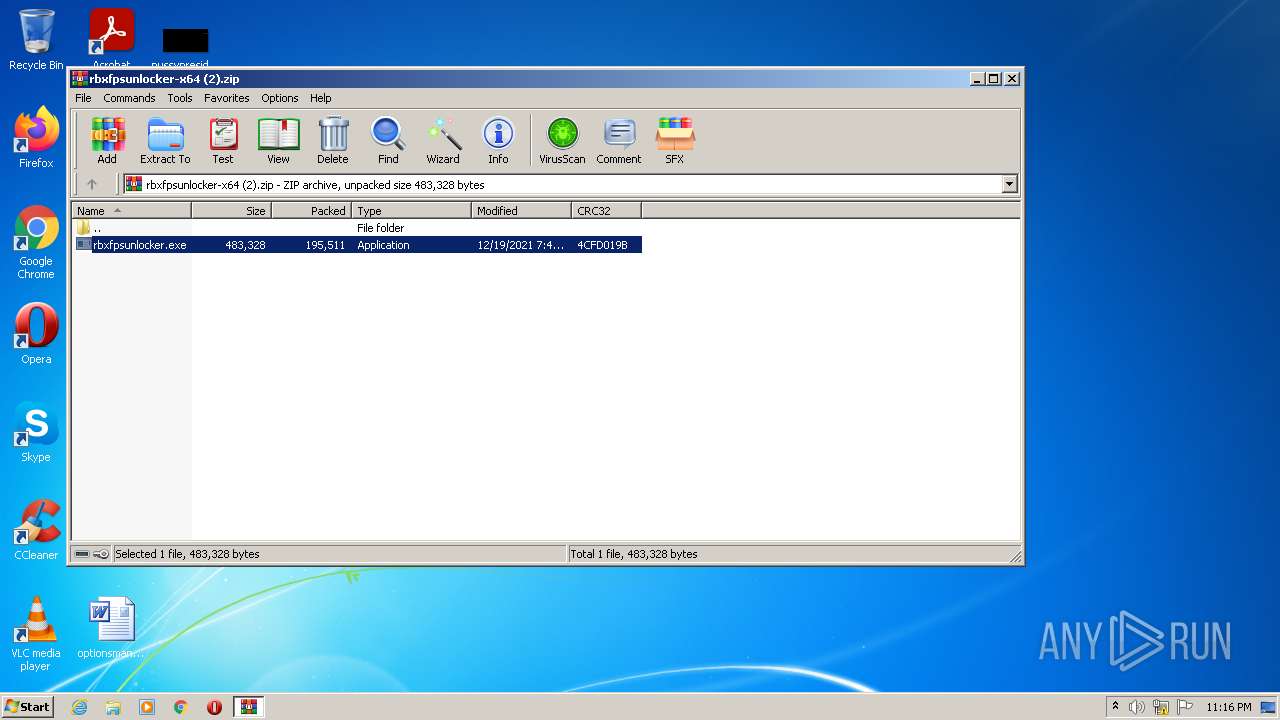
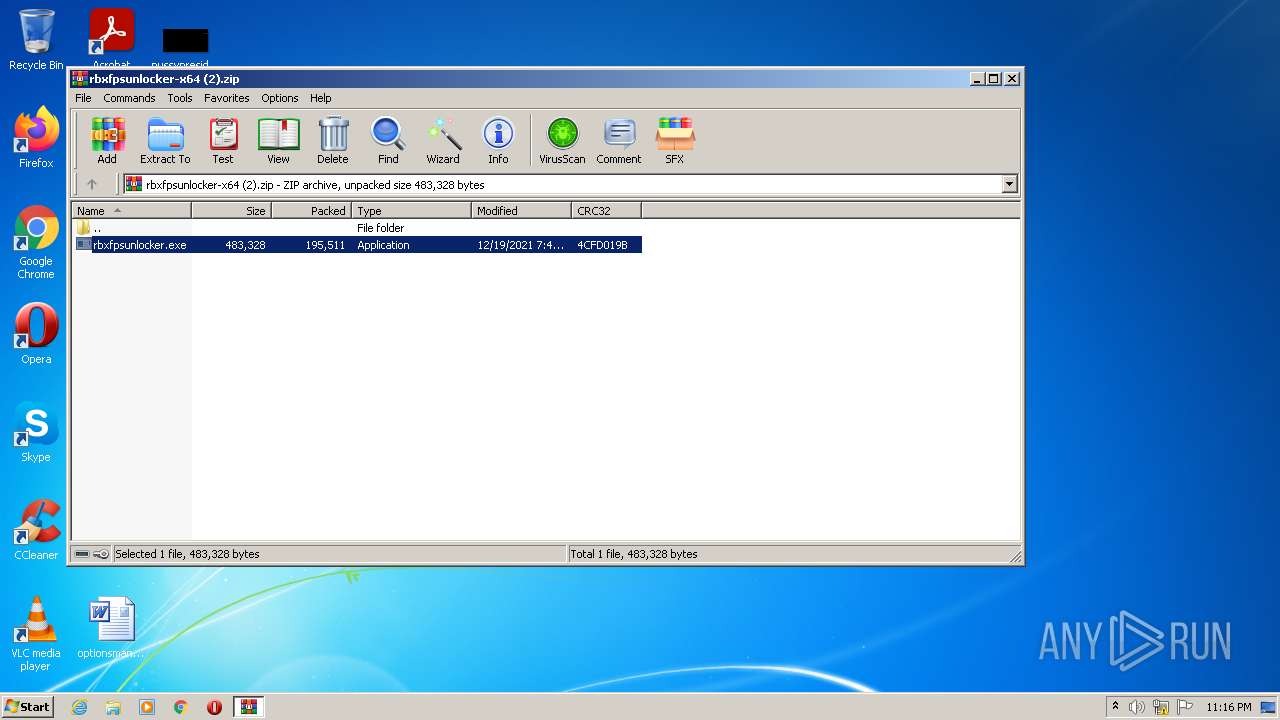
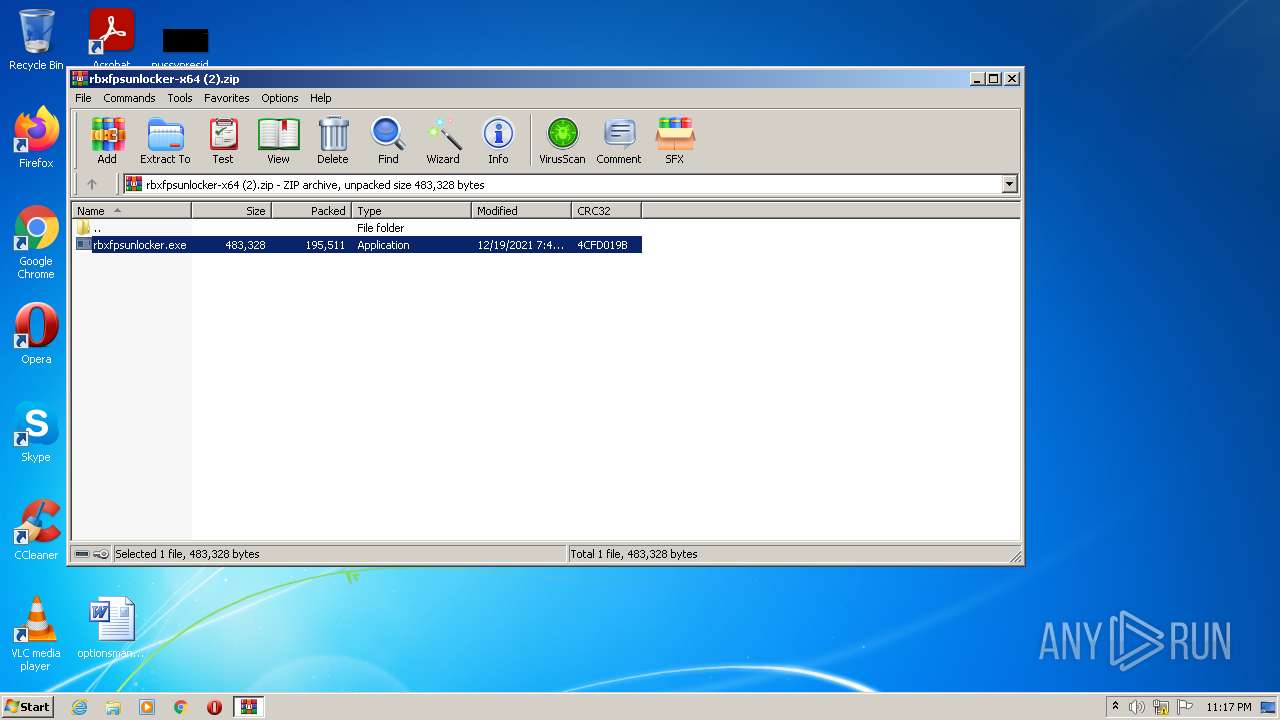
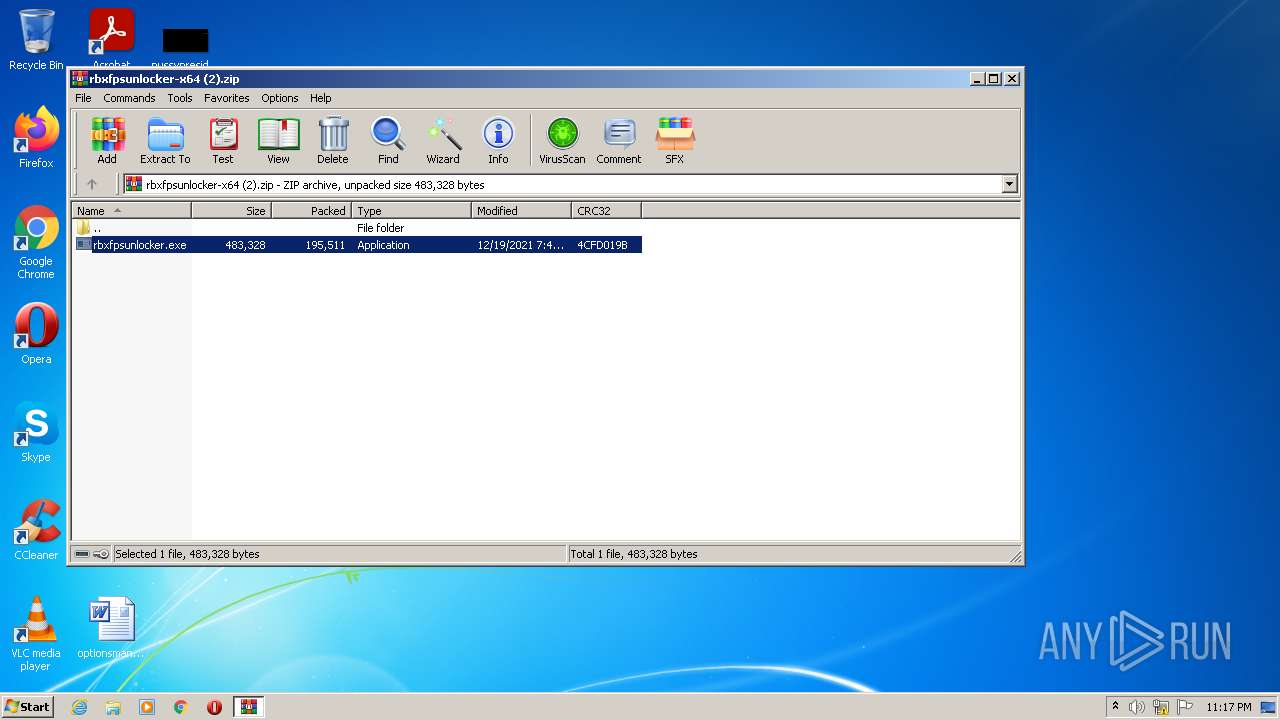
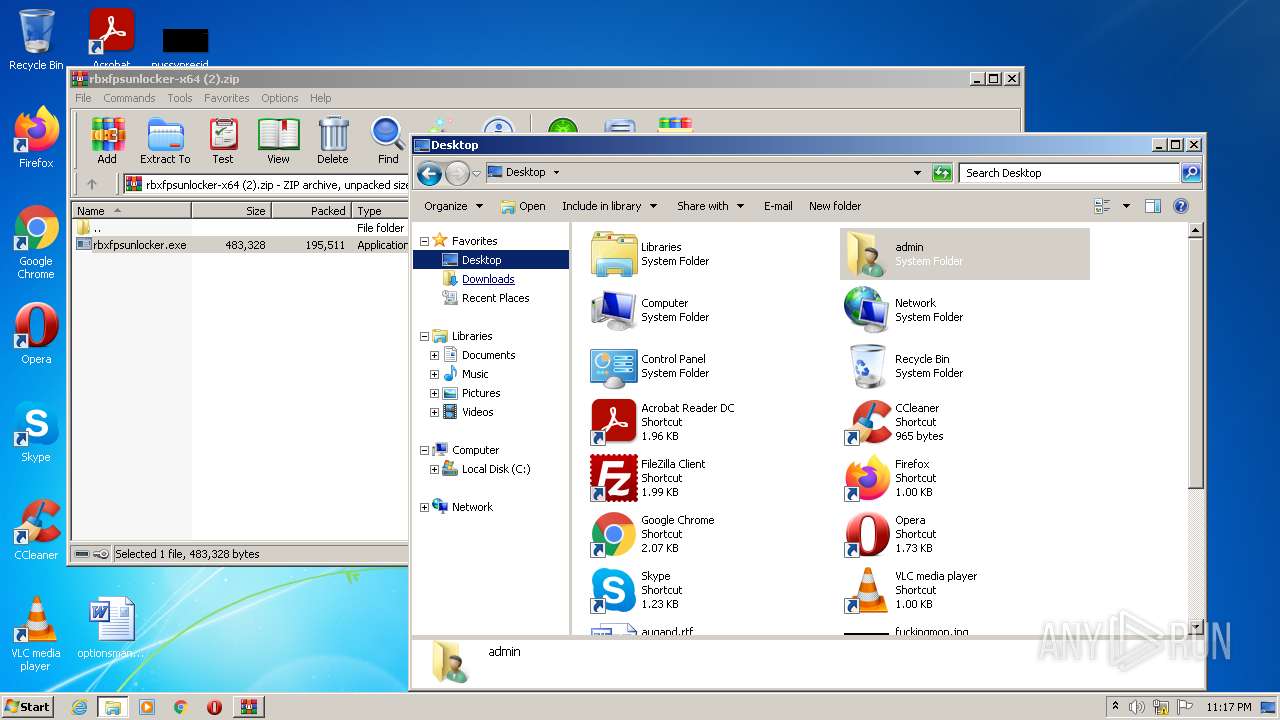
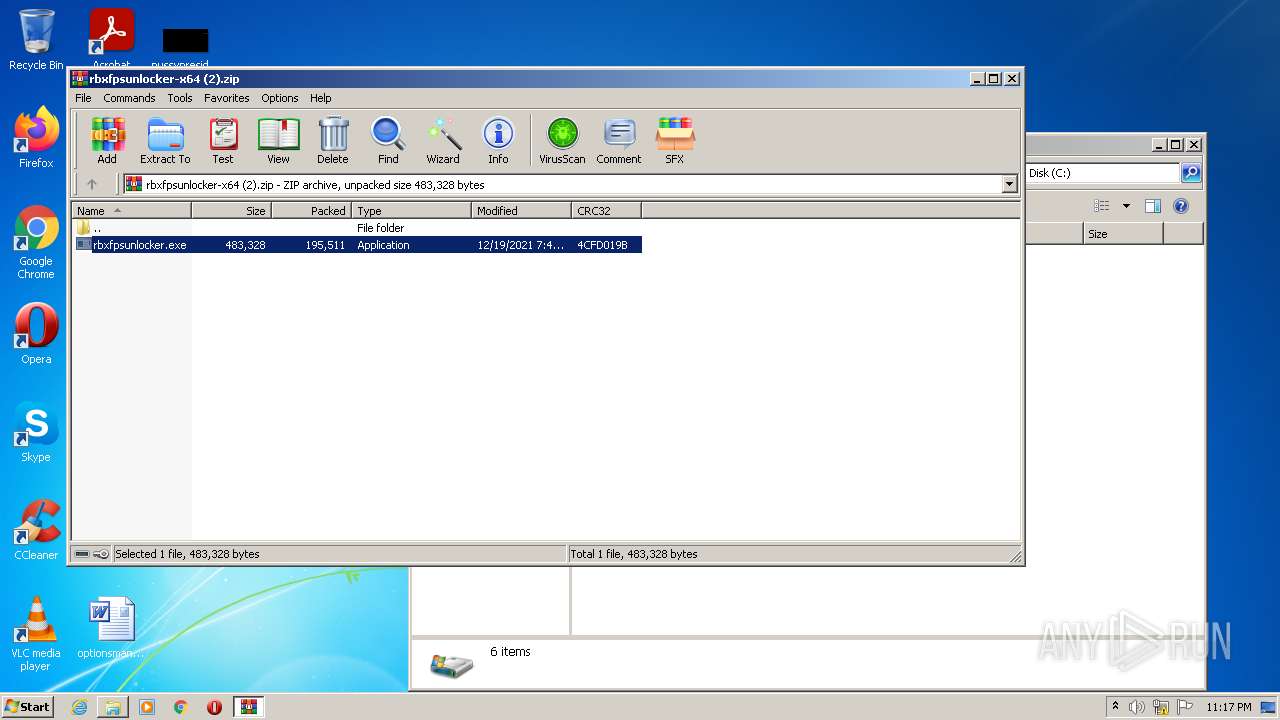
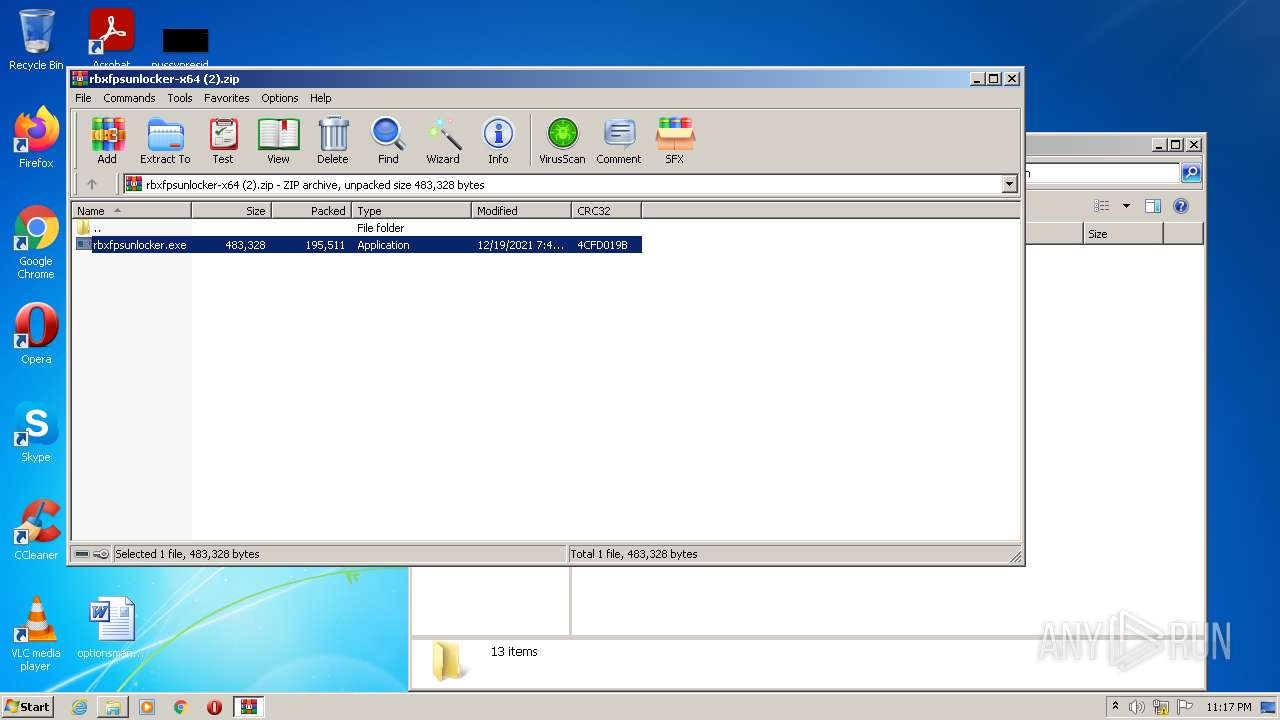
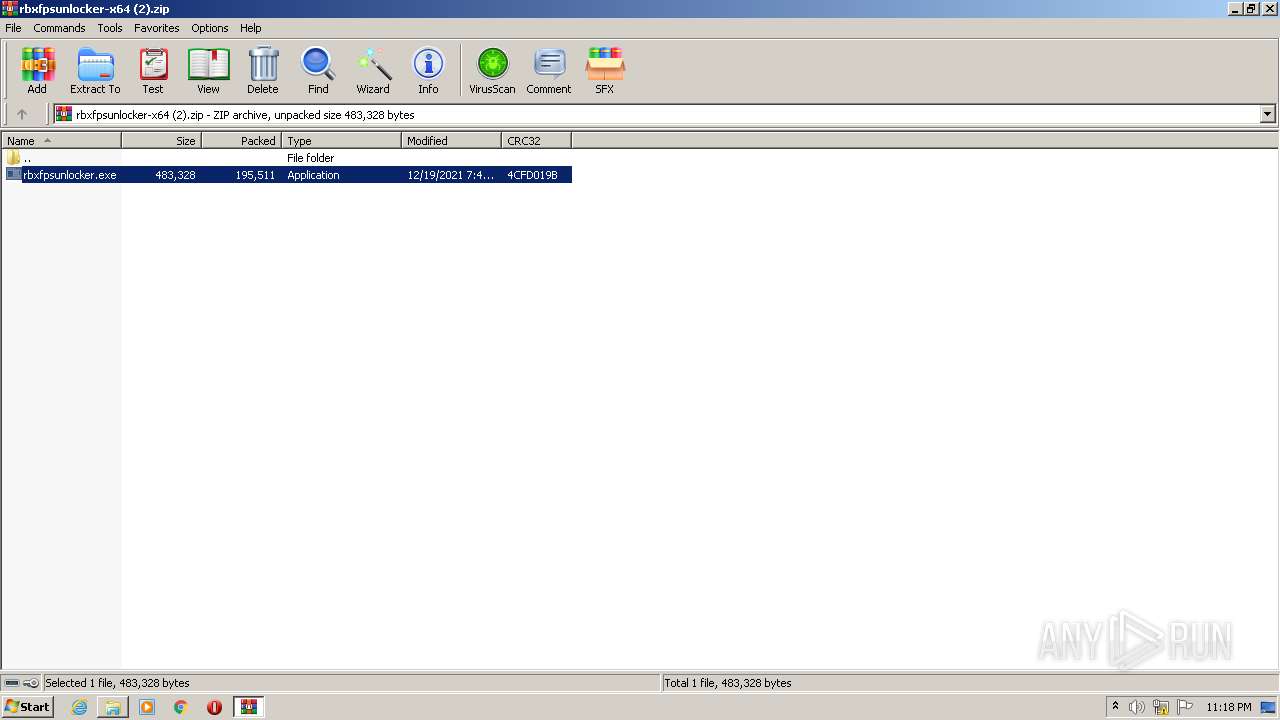
| File name: | rbxfpsunlocker-x64 (2).zip |
| Full analysis: | https://app.any.run/tasks/63db7197-e464-45f9-9fde-e6838cd548b0 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2022, 23:16:36 |
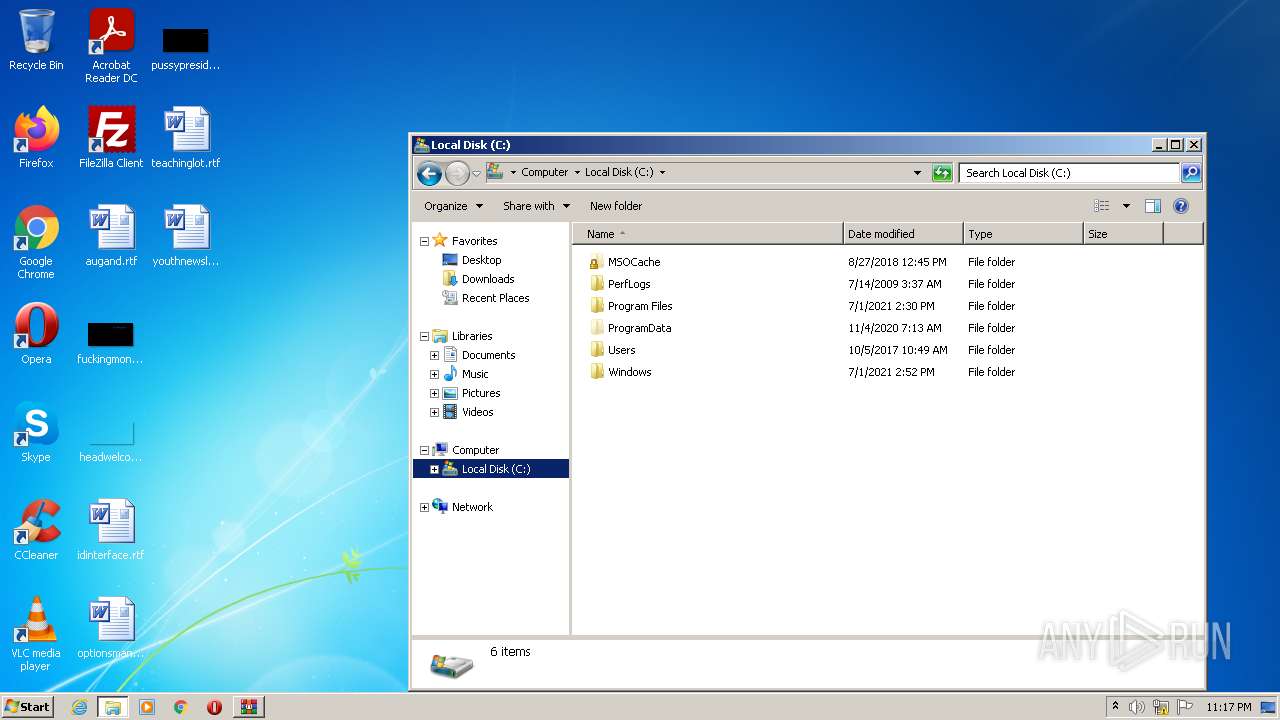
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 51E1FB4F11CD3B47FC70C56353CA9774 |
| SHA1: | 40F62BC532F045BDAE774FEA2EB120CEAD5D5791 |
| SHA256: | F0BAD3A2C8E84DC60066EF7E462ED2DA4C19F293EA2CA797859D751F5EBDDA63 |
| SSDEEP: | 3072:mkEZsCweSz62lJJyOo3SLun7IAathGxg9KFNBmA6yONgln87lifVh6emnTc8GnO4:CeCwei9lJJyIu7Fk4pnwl6yye59q5RN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3588)
Checks supported languages
- WinRAR.exe (PID: 3588)
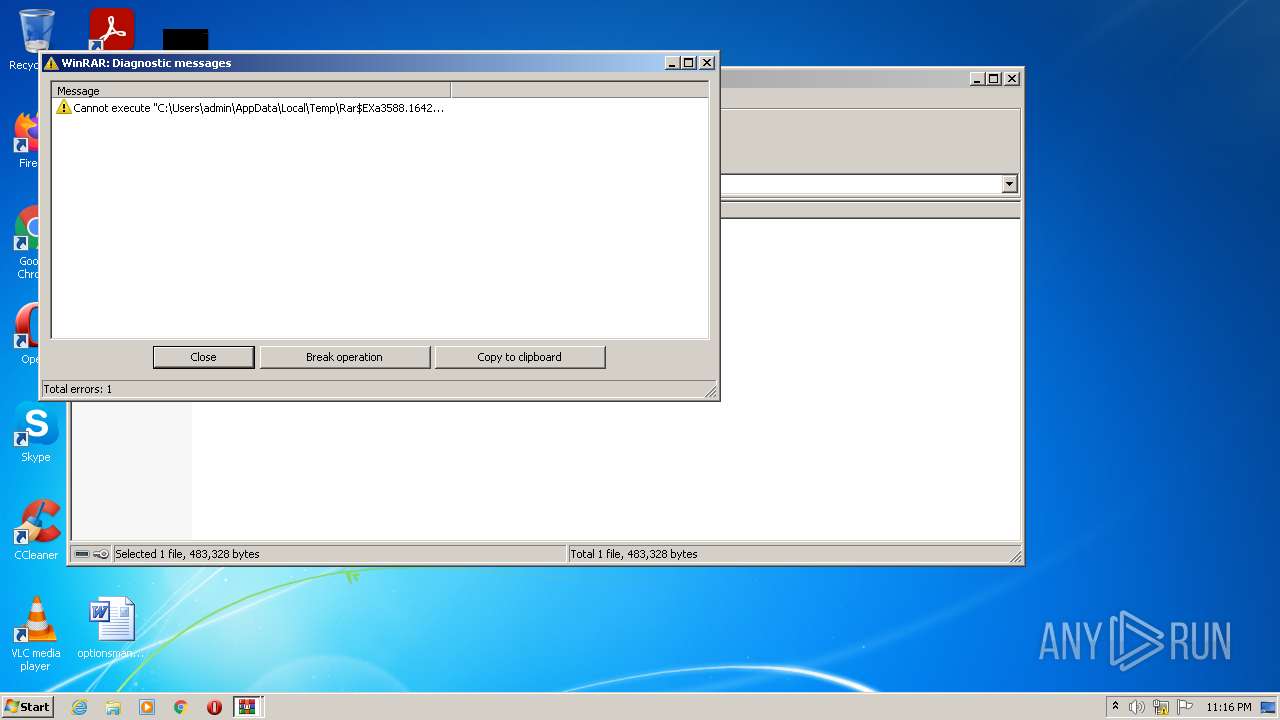
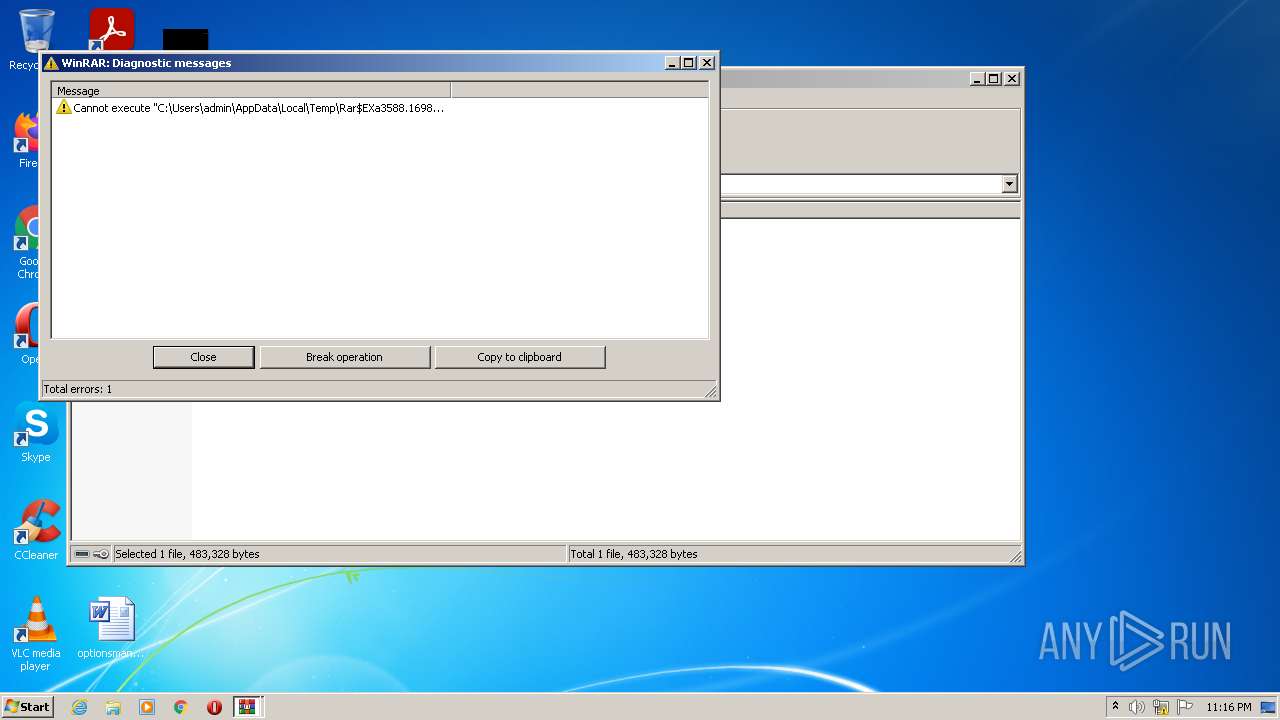
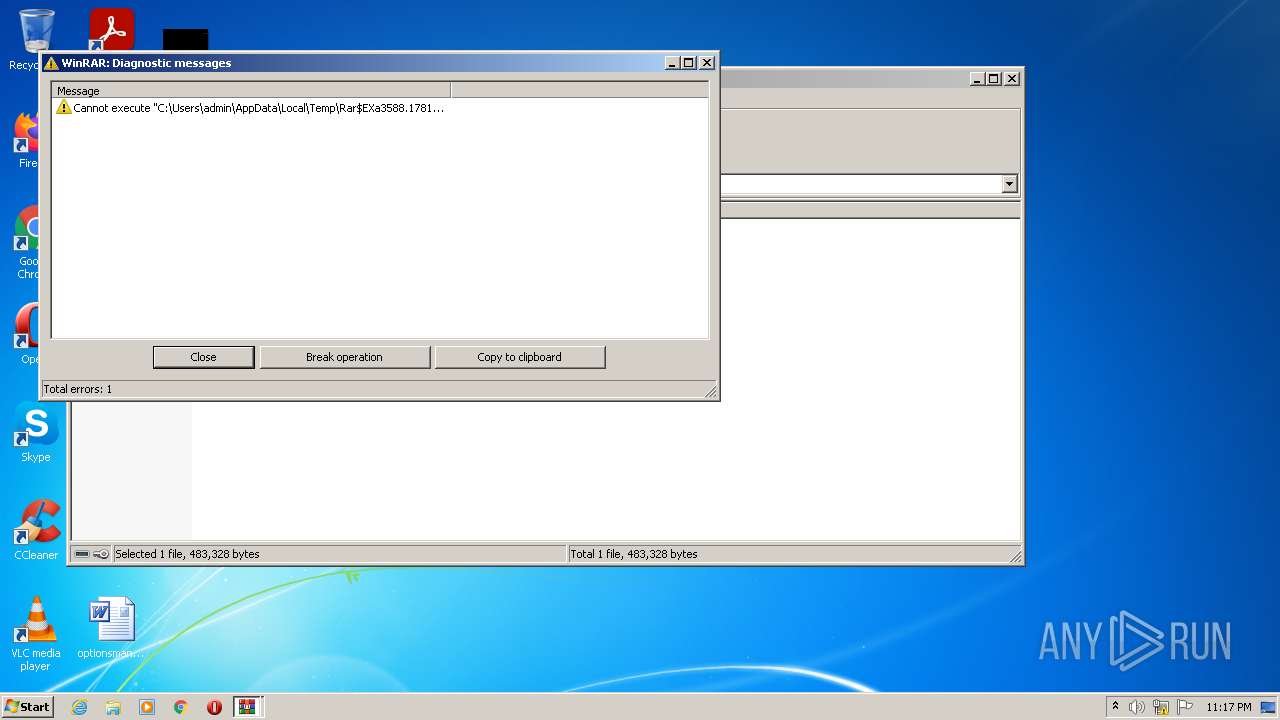
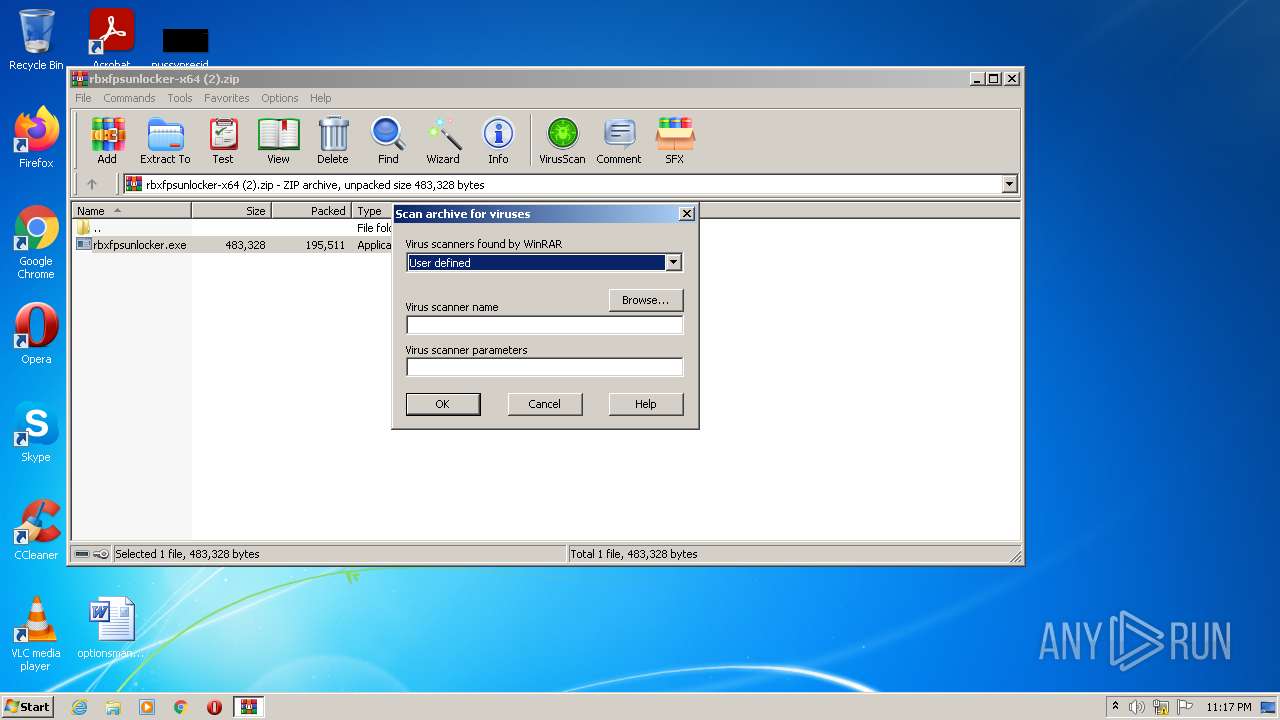
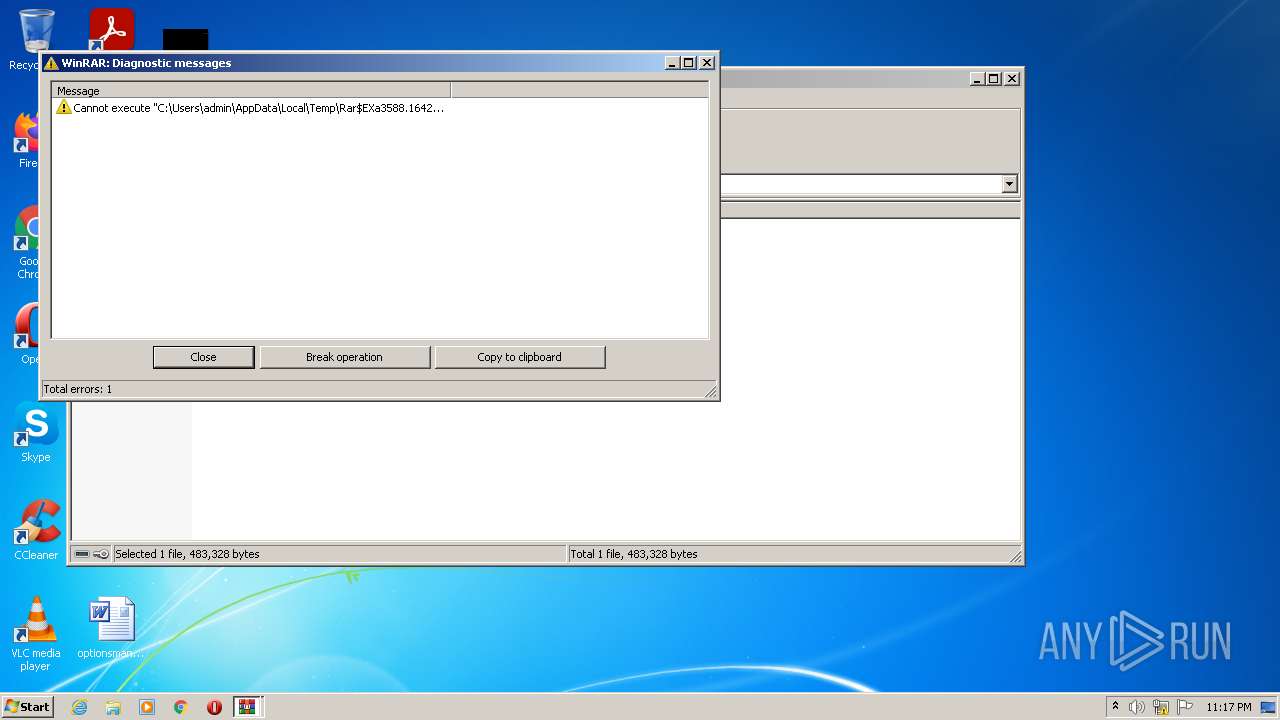
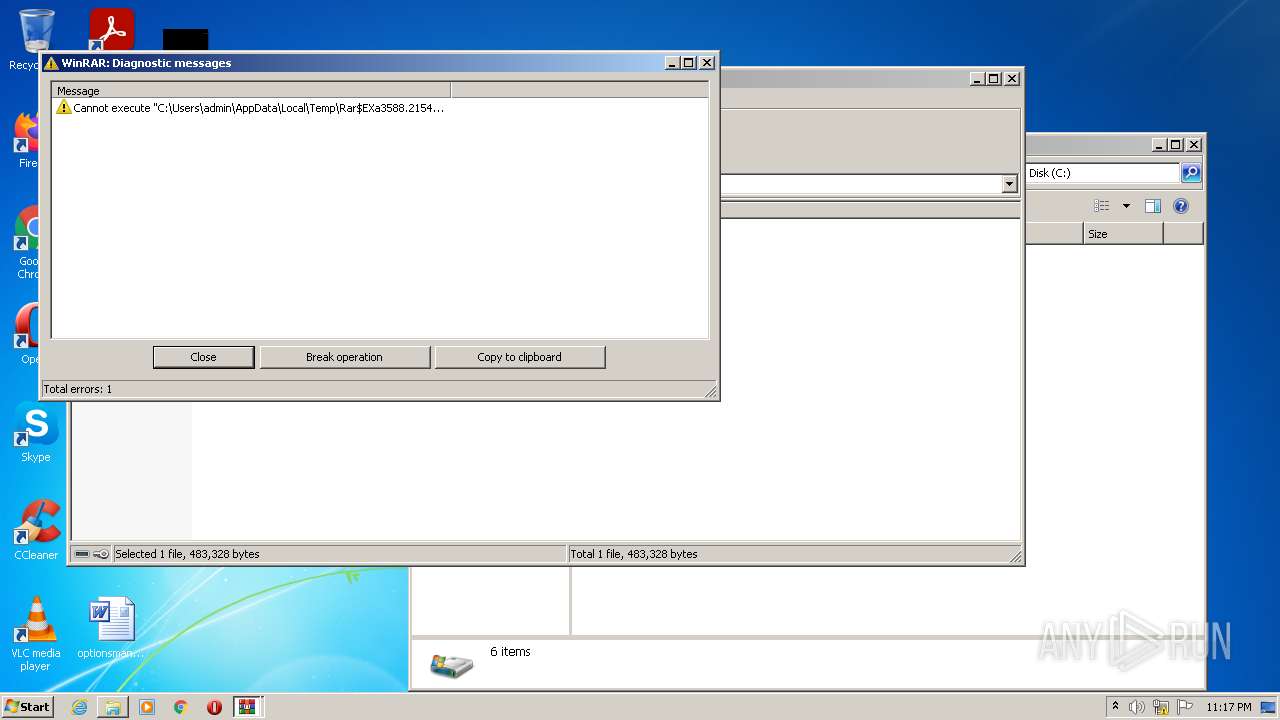
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3588)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3300)
INFO
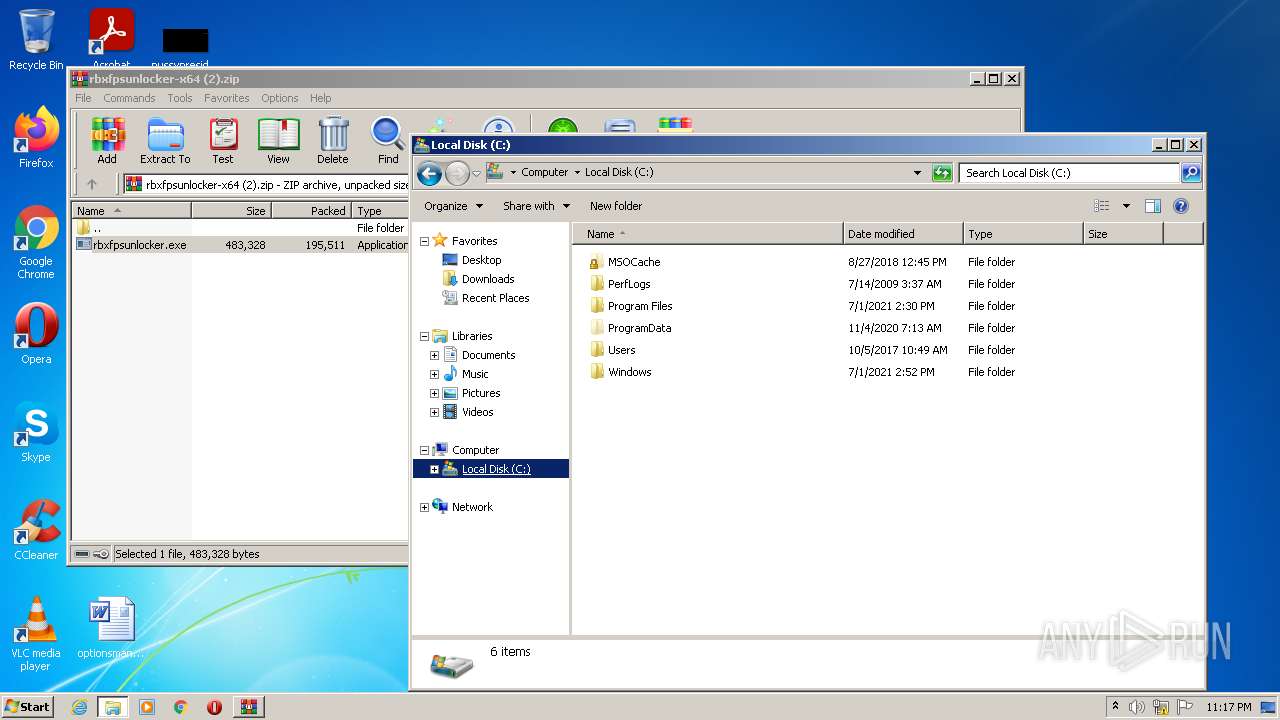
Manual execution by user
- explorer.exe (PID: 1028)
- chrome.exe (PID: 3300)
Application launched itself
- chrome.exe (PID: 3300)
Checks supported languages
- chrome.exe (PID: 1544)
- chrome.exe (PID: 1308)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 3496)
- explorer.exe (PID: 1028)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 2720)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 476)
- chrome.exe (PID: 884)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 588)
- chrome.exe (PID: 592)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 120)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 980)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 2068)
Reads the hosts file
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3300)
Reads the computer name
- chrome.exe (PID: 1544)
- explorer.exe (PID: 1028)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 120)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3496)
Reads settings of System Certificates
- chrome.exe (PID: 1544)
Reads the date of Windows installation
- chrome.exe (PID: 120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
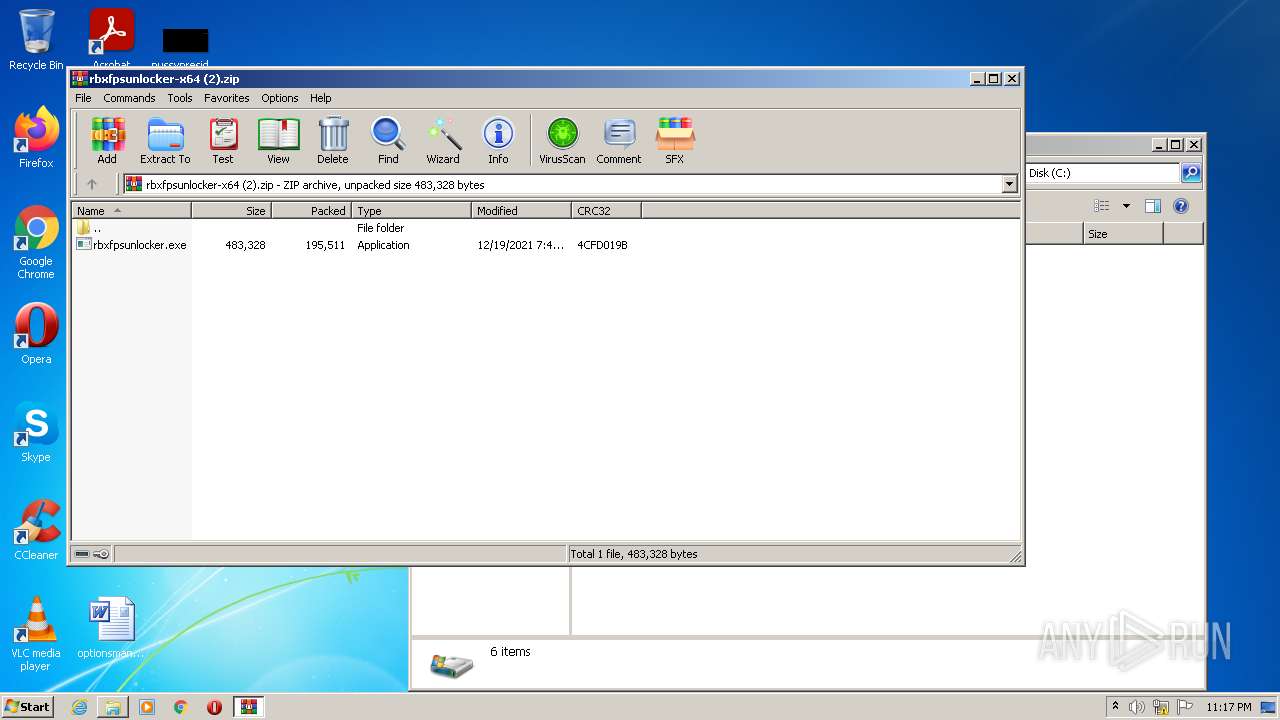
ZIP
| ZipFileName: | rbxfpsunlocker.exe |
|---|---|
| ZipUncompressedSize: | 483328 |
| ZipCompressedSize: | 195511 |
| ZipCRC: | 0x4cfd019b |
| ZipModifyDate: | 2021:12:19 01:48:07 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
77
Monitored processes
40
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1028 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f1dd988,0x6f1dd998,0x6f1dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,14684139267181514454,14909138511001685755,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
19 977
Read events
19 749
Write events
219
Delete events
9
Modification events
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\rbxfpsunlocker-x64 (2).zip | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
6
Suspicious files
241
Text files
141
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-622D2A30-CE4.pma | — | |
MD5:— | SHA256:— | |||
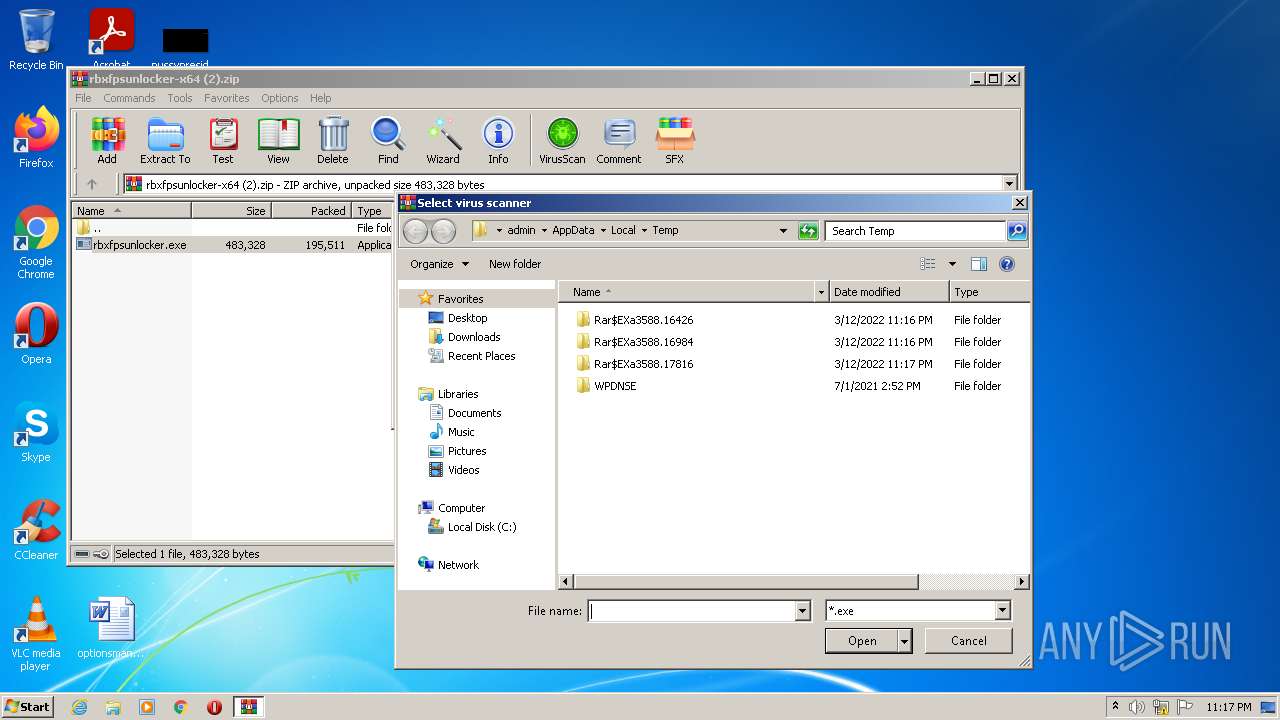
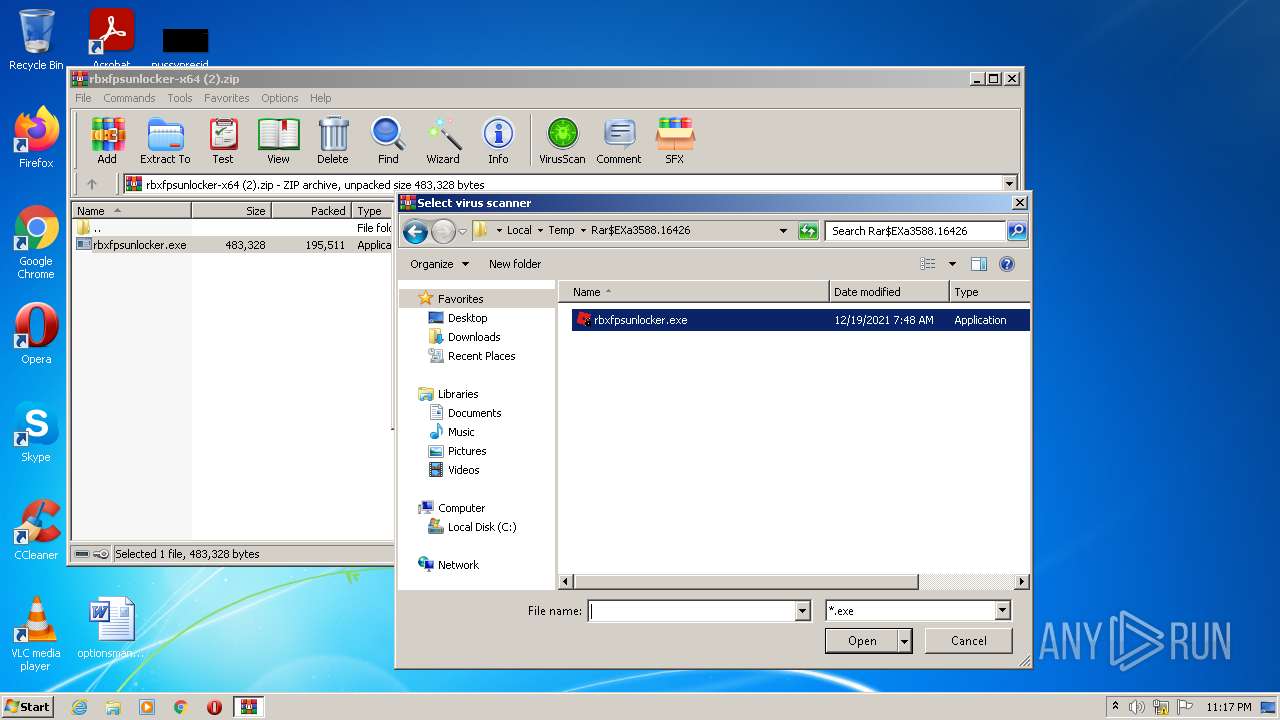
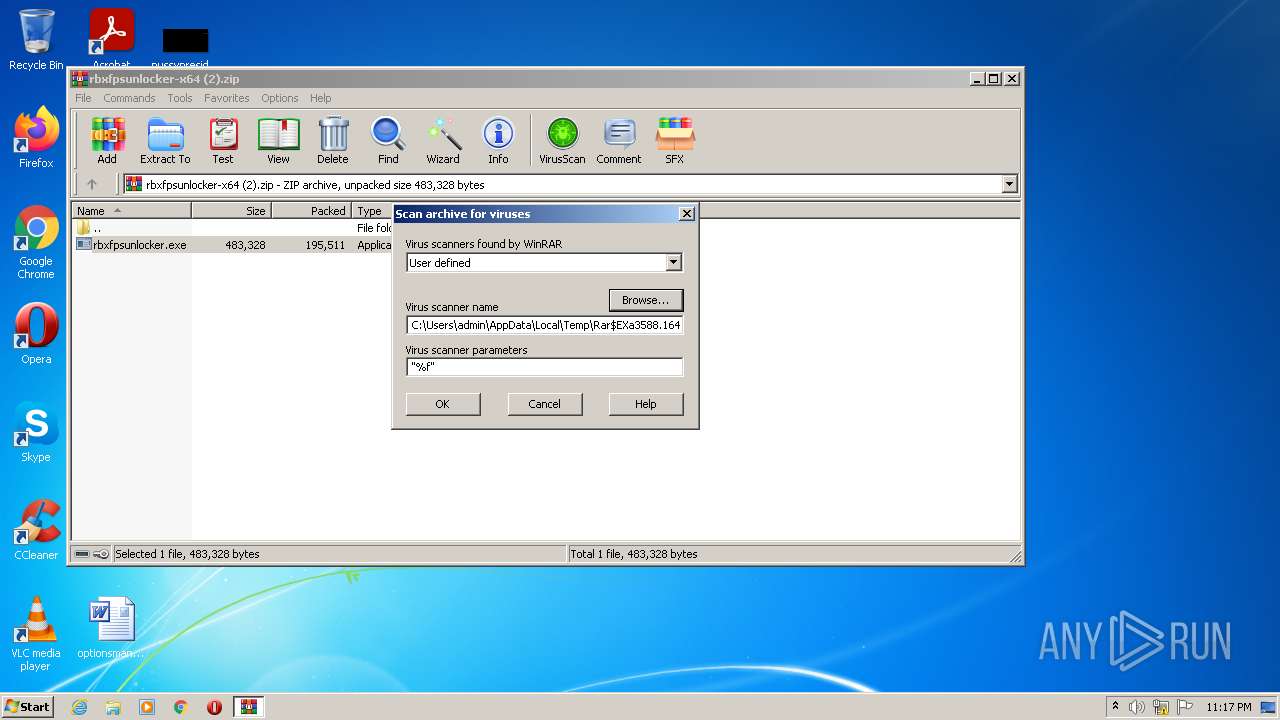
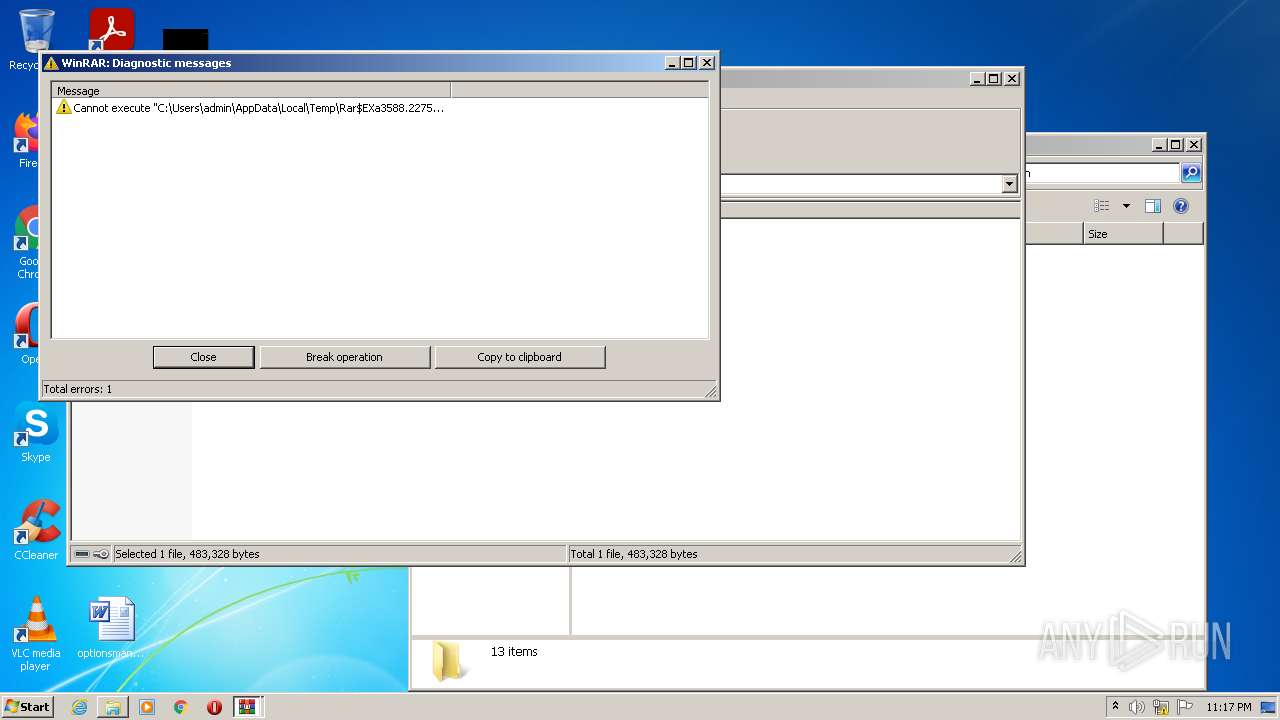
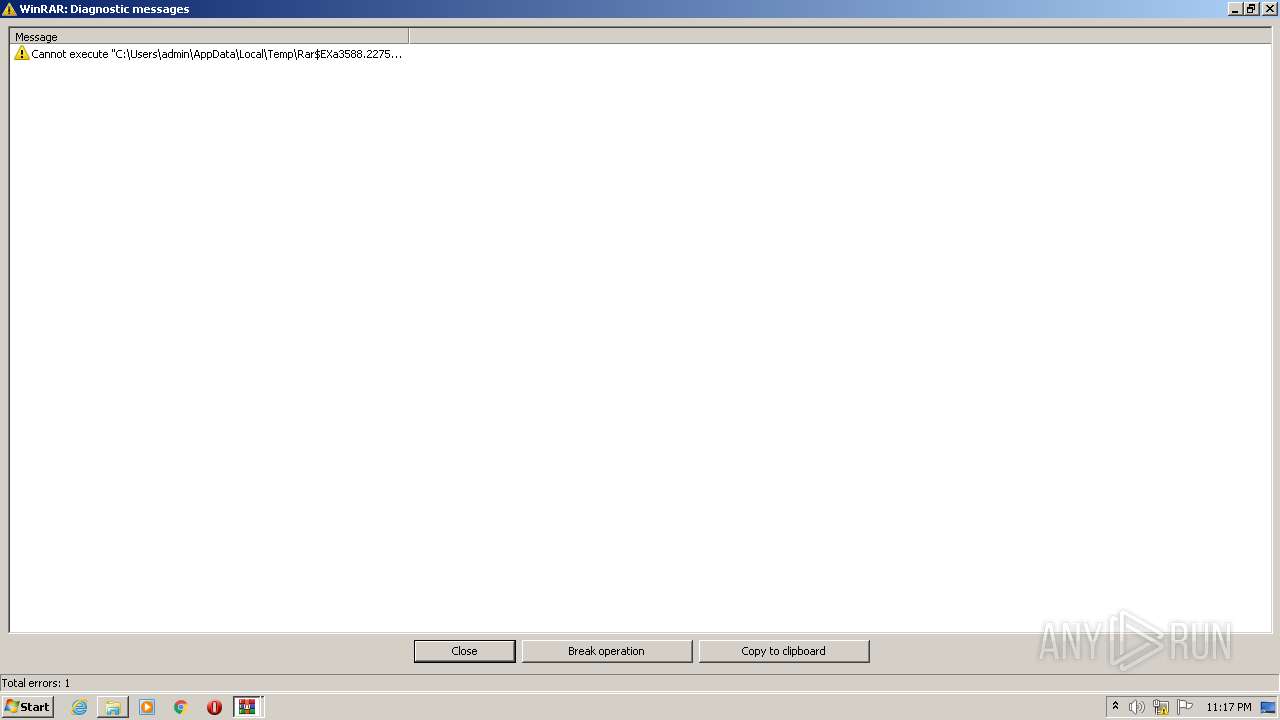
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3588.19310\rbxfpsunlocker-x64 (2).zip\rbxfpsunlocker.exe | executable | |
MD5:70F5AA0E8F8A69BDC3BCEDBF01A14BEC | SHA256:BC16C090DA0F70D81984C2DDCDF23369B0F9CC2D45BF62502A8211E77338C469 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3588.16984\rbxfpsunlocker.exe | executable | |
MD5:70F5AA0E8F8A69BDC3BCEDBF01A14BEC | SHA256:BC16C090DA0F70D81984C2DDCDF23369B0F9CC2D45BF62502A8211E77338C469 | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3588.17816\rbxfpsunlocker.exe | executable | |
MD5:70F5AA0E8F8A69BDC3BCEDBF01A14BEC | SHA256:BC16C090DA0F70D81984C2DDCDF23369B0F9CC2D45BF62502A8211E77338C469 | |||
| 1260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3588.22753\rbxfpsunlocker.exe | executable | |
MD5:70F5AA0E8F8A69BDC3BCEDBF01A14BEC | SHA256:BC16C090DA0F70D81984C2DDCDF23369B0F9CC2D45BF62502A8211E77338C469 | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF141da8.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF141e73.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
51
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ack7ut75hqoo5tco66getjgytyrq_2782/jflookgnkcckhobaglndicnbbgbonegd_2782_all_adtj3mouf5ugodspfqd56gujxgeq.crx3 | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 200 | 74.125.100.230:80 | http://r1---sn-5hne6nzd.gvt1.com/edgedl/release2/chrome_component/ack7ut75hqoo5tco66getjgytyrq_2782/jflookgnkcckhobaglndicnbbgbonegd_2782_all_adtj3mouf5ugodspfqd56gujxgeq.crx3?cms_redirect=yes&mh=GT&mip=157.97.122.3&mm=28&mn=sn-5hne6nzd&ms=nvh&mt=1647126742&mv=m&mvi=1&pl=24&rmhost=r4---sn-5hne6nzd.gvt1.com&shardbypass=sd&smhost=r2---sn-5hne6nsk.gvt1.com | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 200 | 74.125.100.187:80 | http://r5---sn-5hnedn7z.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=157.97.122.3&mm=28&mn=sn-5hnedn7z&ms=nvh&mt=1647126742&mv=m&mvi=5&pl=24&rmhost=r3---sn-5hnedn7z.gvt1.com&shardbypass=sd&smhost=r2---sn-5hnekn7l.gvt1.com | US | — | — | whitelisted |
872 | svchost.exe | HEAD | 200 | 209.85.226.41:80 | http://r4---sn-5hnekn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=8_&mip=157.97.122.3&mm=28&mn=sn-5hnekn7d&ms=nvh&mt=1647126742&mv=m&mvi=4&pl=24&rmhost=r2---sn-5hnekn7d.gvt1.com&shardbypass=sd&smhost=r2---sn-5hnekn7z.gvt1.com | US | — | — | whitelisted |
872 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | html | 592 b | whitelisted |
1544 | chrome.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
872 | svchost.exe | GET | 206 | 74.125.100.230:80 | http://r1---sn-5hne6nzd.gvt1.com/edgedl/release2/chrome_component/ack7ut75hqoo5tco66getjgytyrq_2782/jflookgnkcckhobaglndicnbbgbonegd_2782_all_adtj3mouf5ugodspfqd56gujxgeq.crx3?cms_redirect=yes&mh=GT&mip=157.97.122.3&mm=28&mn=sn-5hne6nzd&ms=nvh&mt=1647126742&mv=m&mvi=1&pl=24&rmhost=r4---sn-5hne6nzd.gvt1.com&shardbypass=sd&smhost=r2---sn-5hne6nsk.gvt1.com | US | binary | 9.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1544 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1544 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
1544 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
1544 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1544 | chrome.exe | 142.250.186.65:443 | lh5.googleusercontent.com | Google Inc. | US | whitelisted |
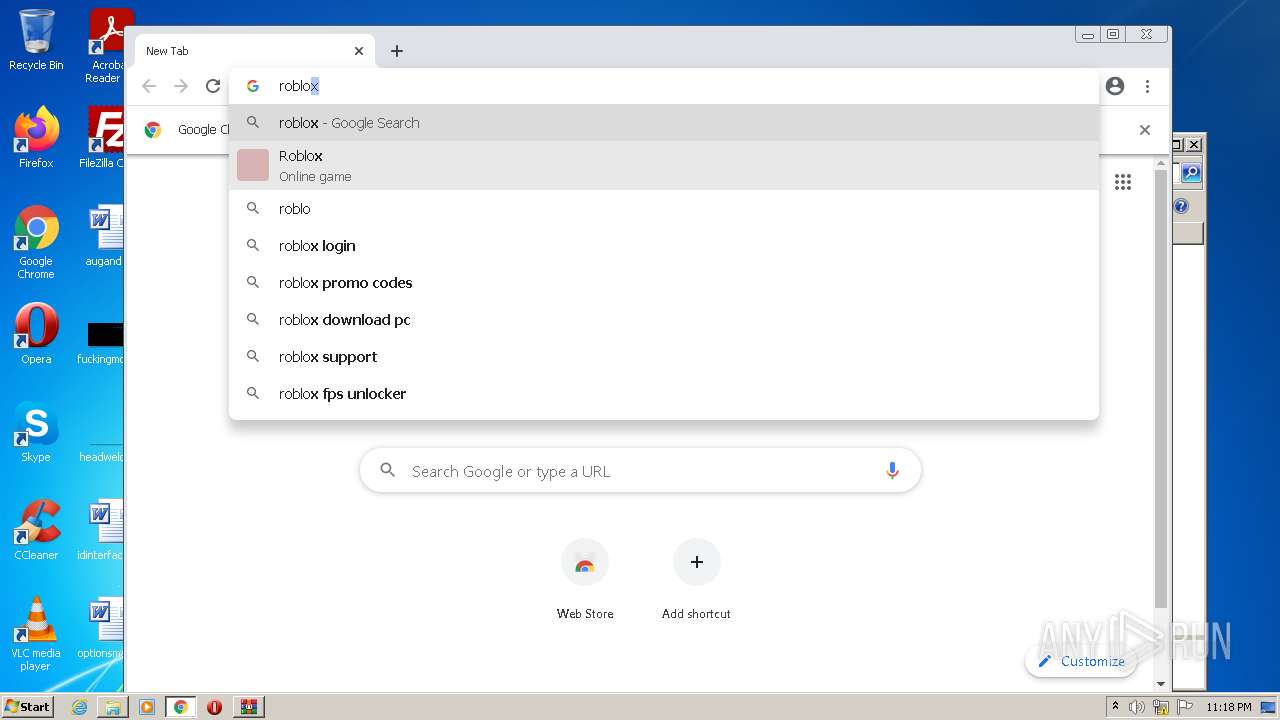
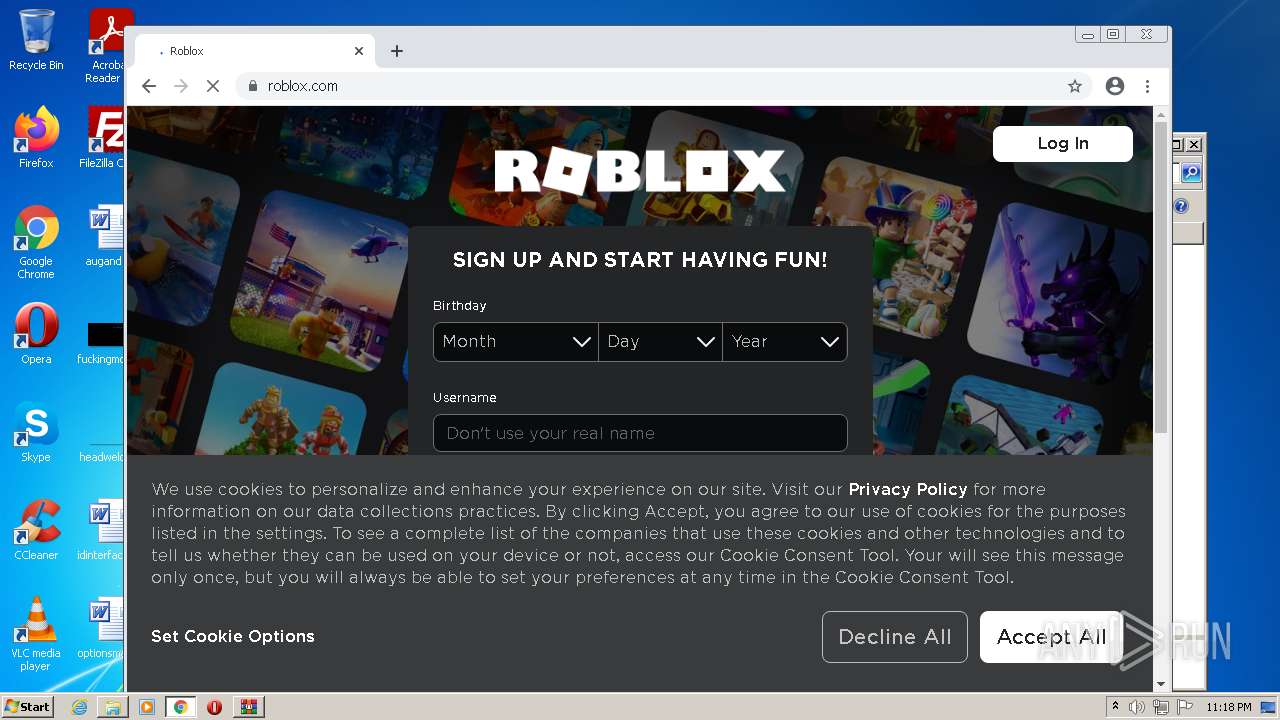
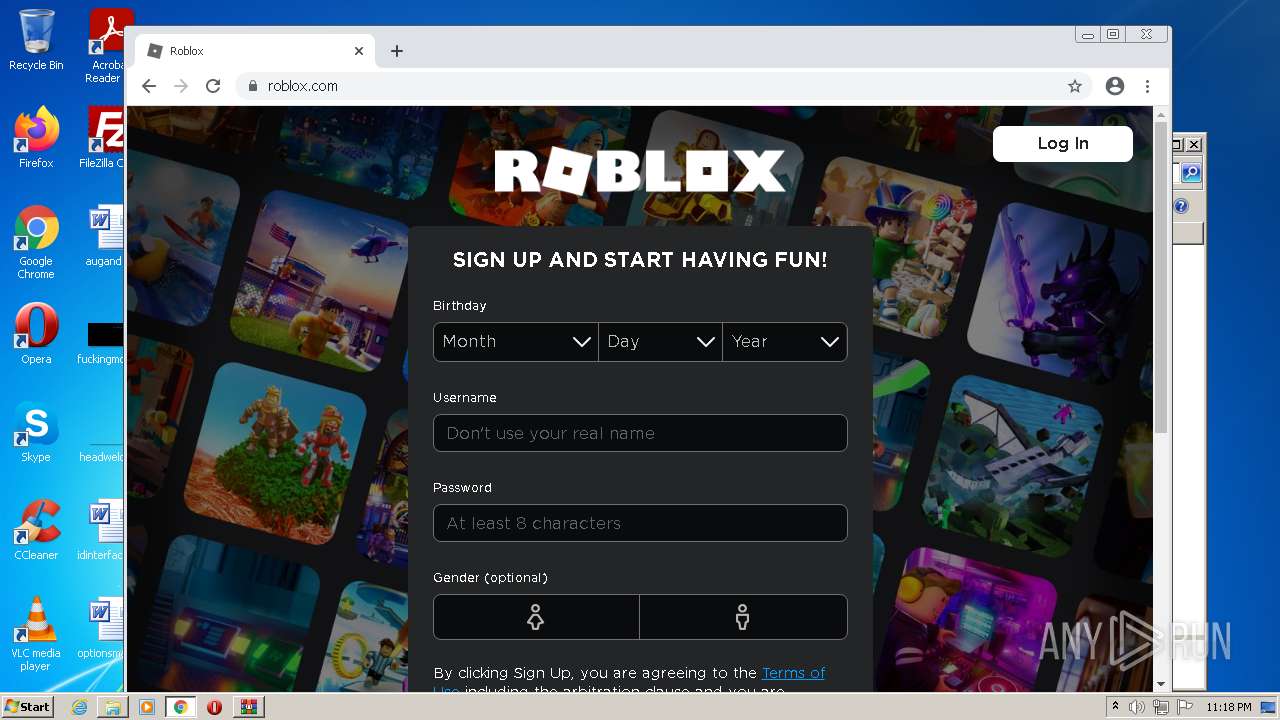
1544 | chrome.exe | 205.234.175.102:443 | css.rbxcdn.com | CacheNetworks, Inc. | US | suspicious |
1544 | chrome.exe | 128.116.123.3:443 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
1544 | chrome.exe | 205.185.216.10:443 | static.rbxcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1544 | chrome.exe | 142.250.185.98:443 | adservice.google.com | Google Inc. | US | shared |
1544 | chrome.exe | 104.18.25.64:443 | roblox-api.arkoselabs.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |