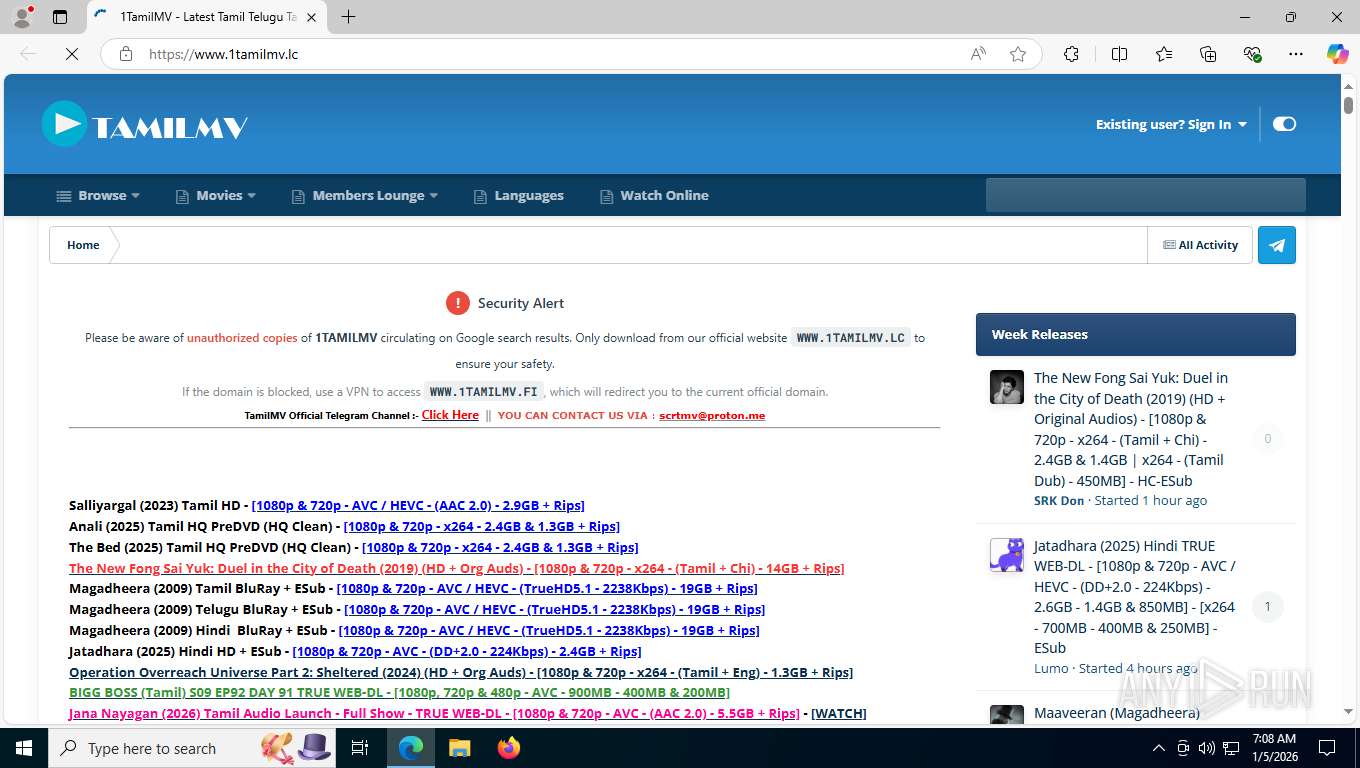
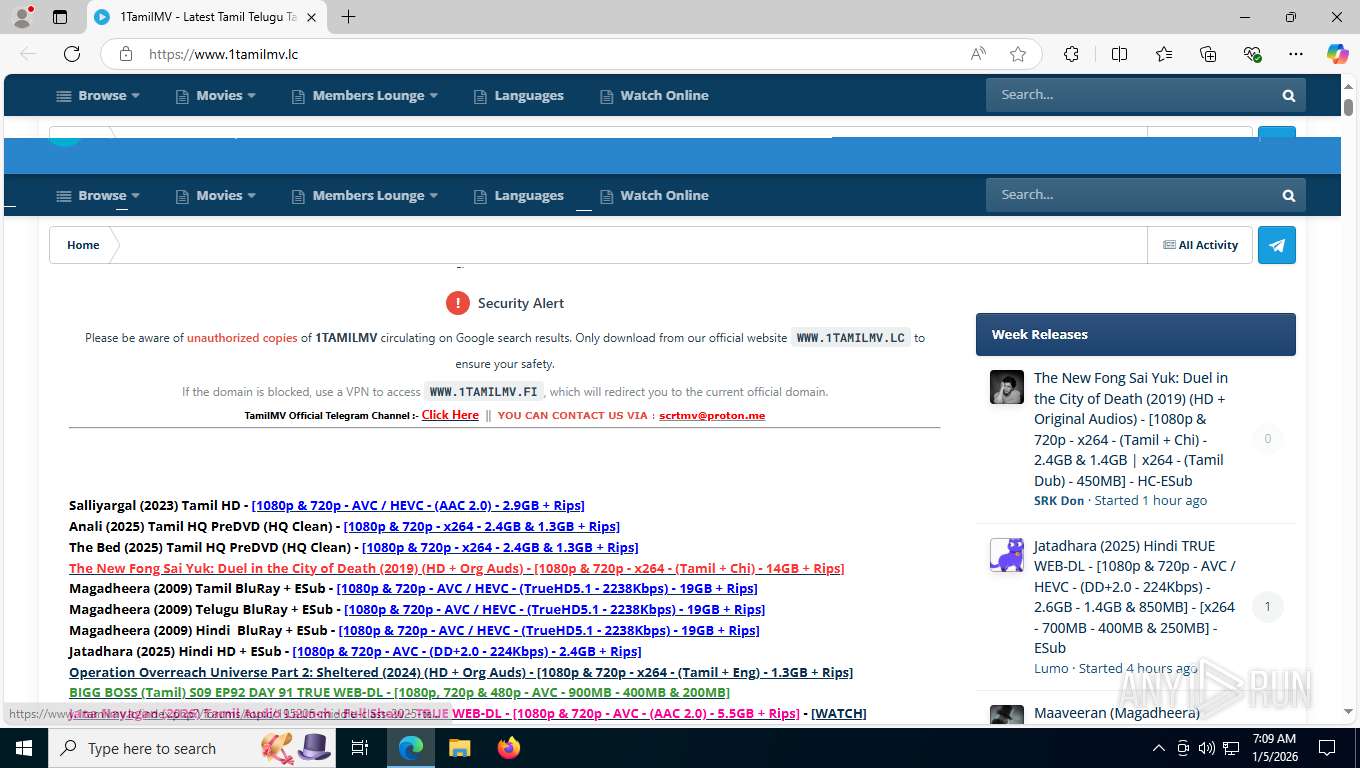
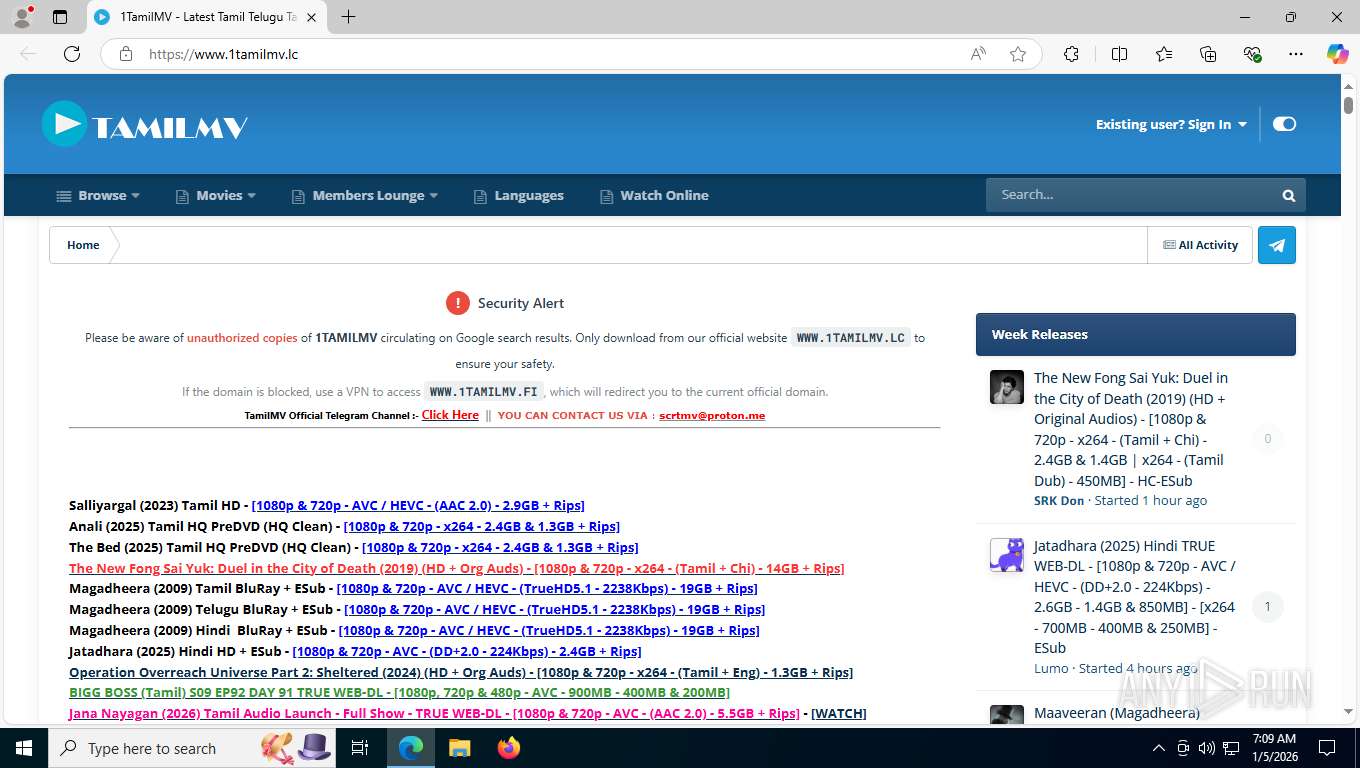
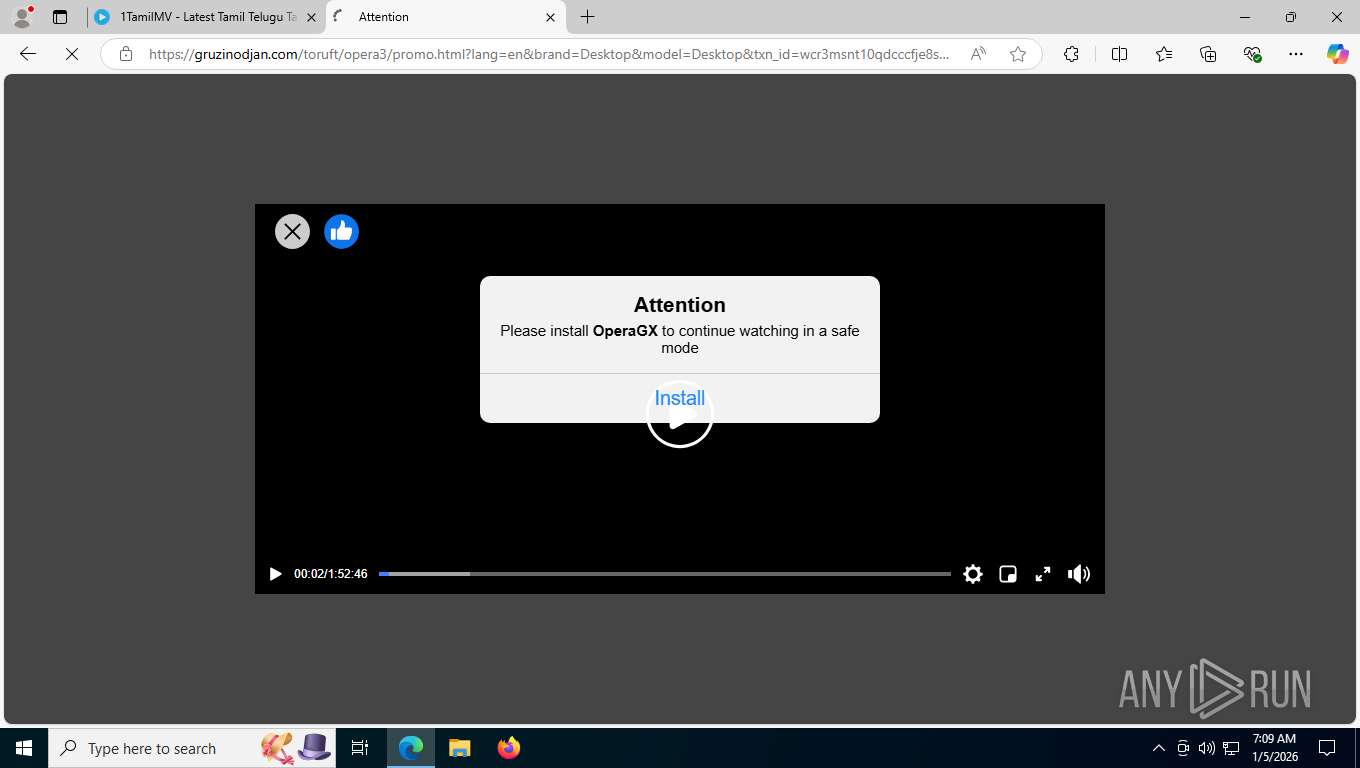
| URL: | https://www.1tamilmv.lc/ |
| Full analysis: | https://app.any.run/tasks/200fa143-bd5e-40e8-819c-91c85955fdf9 |
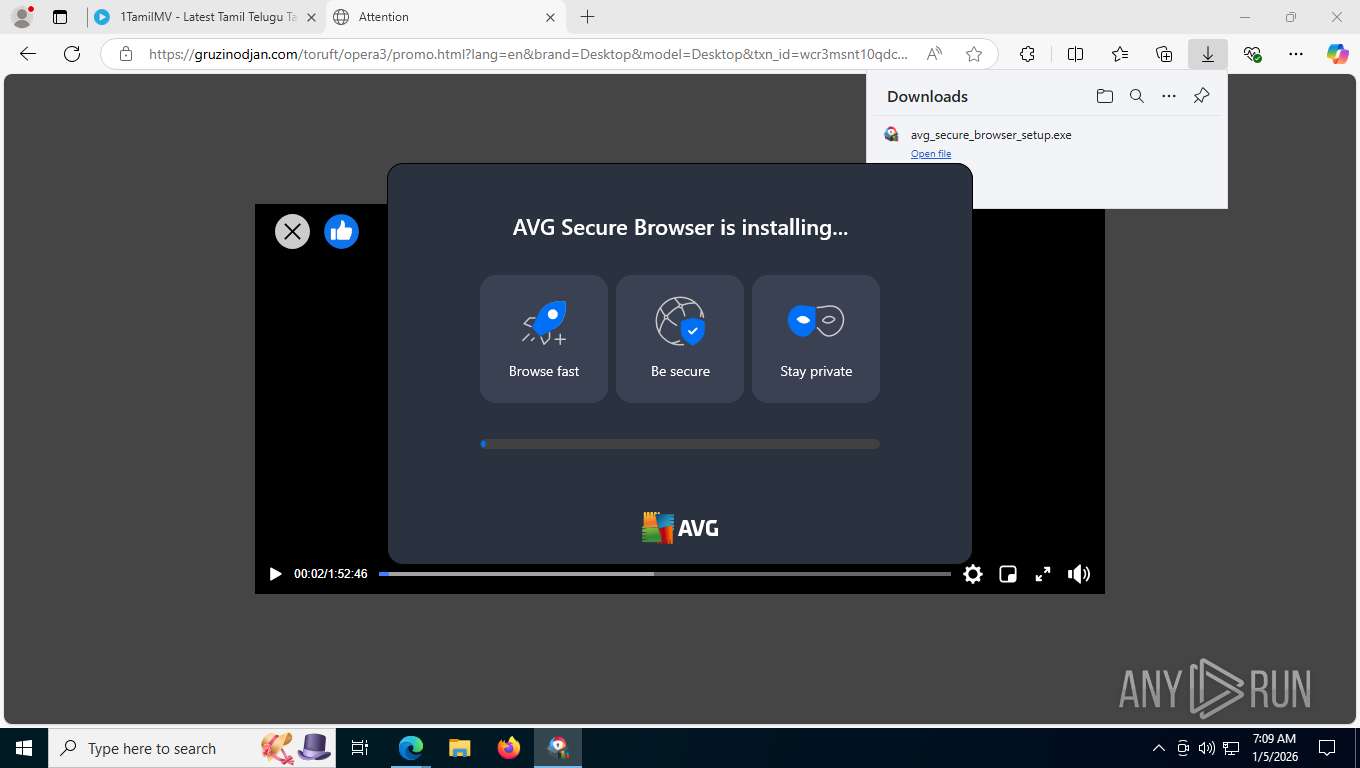
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 05, 2026, 12:08:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51A1DCB30D1DB8E6193B27F1A2B82E45 |
| SHA1: | 6C8DE7FA7CC15E7AD56063F668B0A43BE2CCA85D |
| SHA256: | F07125A79F851EA27AADC1B094655F1BB105F3EE21439B5E45EAFAF0543F255A |
| SSDEEP: | 3:N8DSLWJd:2OLW3 |
MALICIOUS
Actions looks like stealing of personal data
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowser.exe (PID: 8904)
Changes the autorun value in the registry
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowser.exe (PID: 8228)
SUSPICIOUS
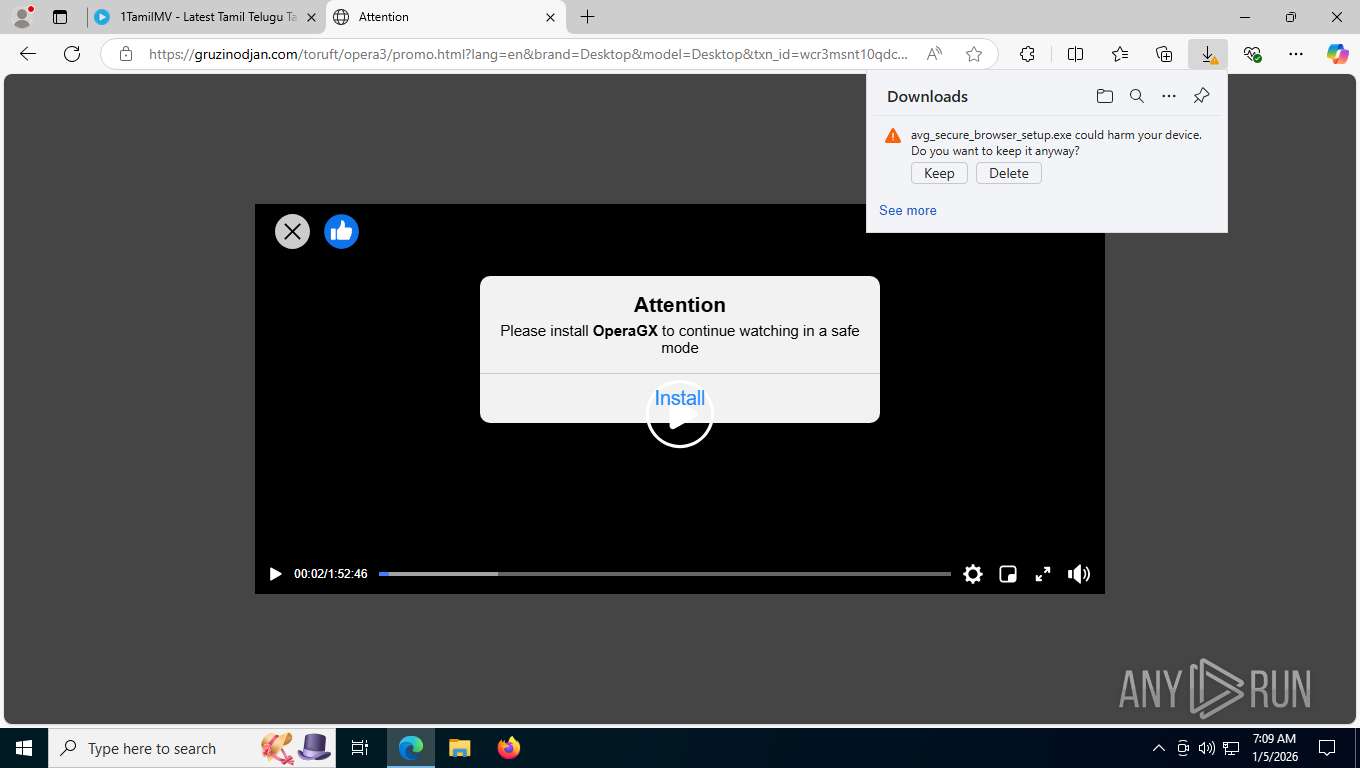
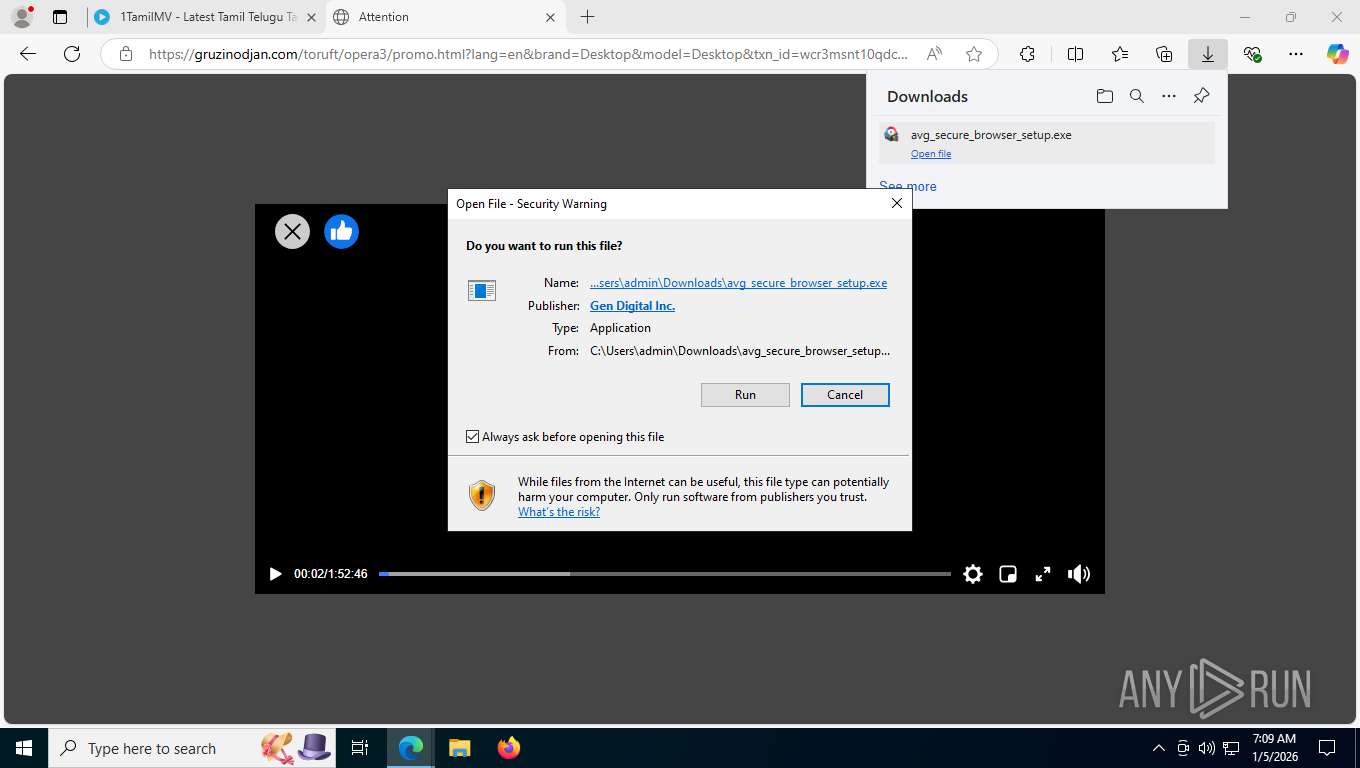
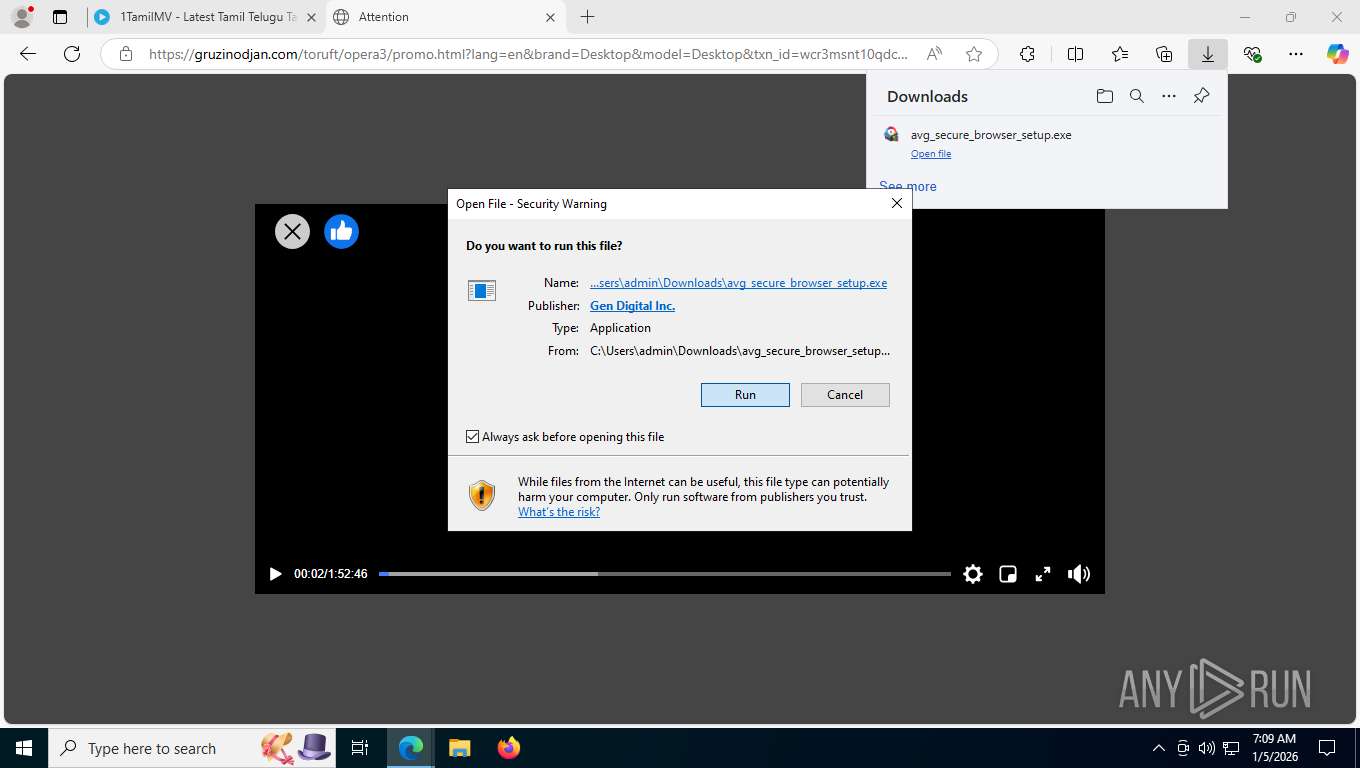
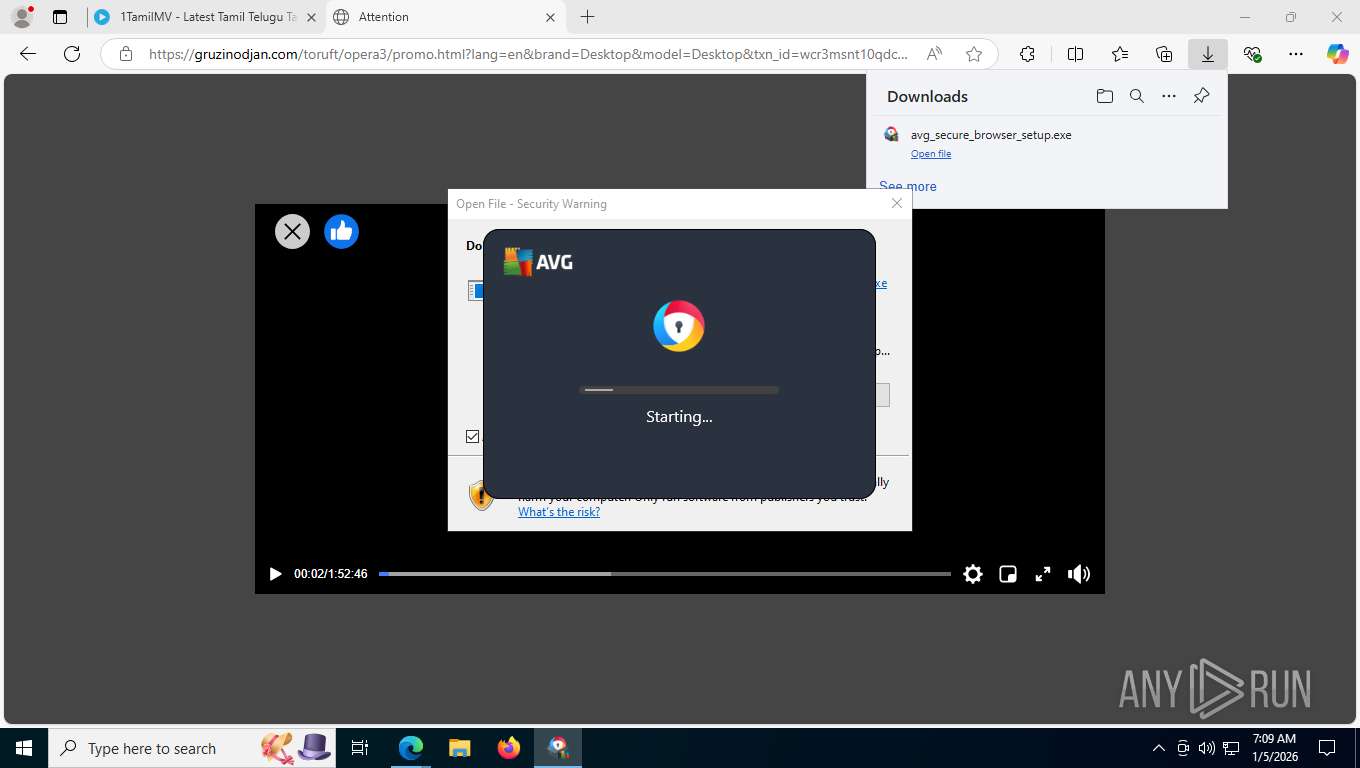
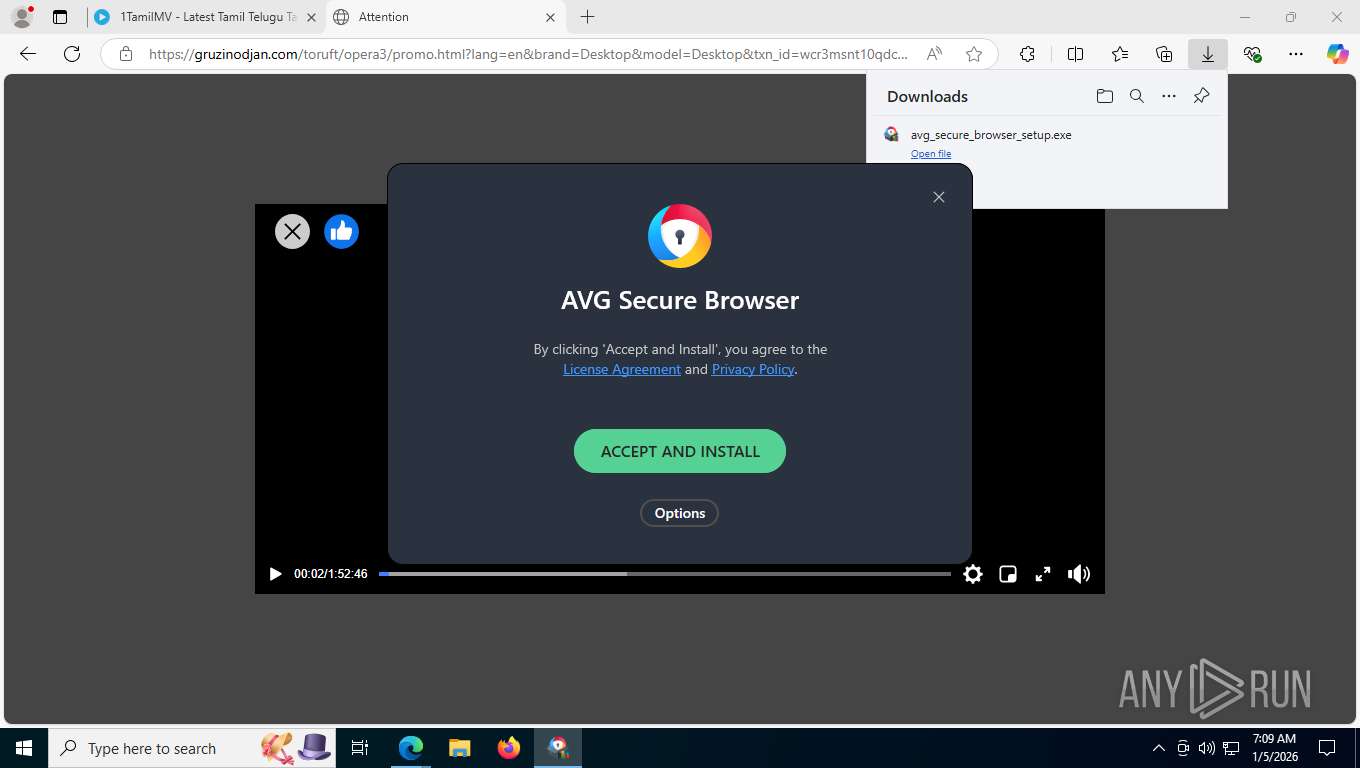
Executable content was dropped or overwritten
- avg_secure_browser_setup.exe (PID: 6460)
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserInstaller.exe (PID: 4404)
- setup.exe (PID: 1952)
- AVGBrowserInstaller.exe (PID: 6188)
The process verifies whether the antivirus software is installed
- AVGBrowserInstaller.exe (PID: 6188)
Reads security settings of Internet Explorer
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdate.exe (PID: 2452)
Starts itself from another location
- AVGBrowserUpdate.exe (PID: 2452)
Creates/Modifies COM task schedule object
- AVGBrowserUpdate.exe (PID: 6592)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 2900)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 2612)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 7476)
- AVGBrowserUpdate.exe (PID: 2452)
Application launched itself
- setup.exe (PID: 1952)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Process drops legitimate windows executable
- setup.exe (PID: 1952)
Searches for installed software
- setup.exe (PID: 1952)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Reads the BIOS version
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
INFO
Connects to unusual port
- msedge.exe (PID: 8040)
Checks supported languages
- identity_helper.exe (PID: 8256)
- avg_secure_browser_setup.exe (PID: 6460)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 2900)
- AVGBrowserUpdate.exe (PID: 6592)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 2612)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 7476)
- AVGBrowserUpdate.exe (PID: 7904)
- AVGBrowserUpdate.exe (PID: 8760)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowserInstaller.exe (PID: 4404)
- setup.exe (PID: 1952)
- setup.exe (PID: 7120)
- AVGBrowserCrashHandler.exe (PID: 6580)
- AVGBrowserCrashHandler64.exe (PID: 3104)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 8244)
- AVGBrowser.exe (PID: 3304)
- AVGBrowser.exe (PID: 8328)
- AVGBrowser.exe (PID: 5044)
- AVGBrowser.exe (PID: 8904)
- AVGBrowser.exe (PID: 6916)
- AVGBrowser.exe (PID: 6536)
- AVGBrowser.exe (PID: 7960)
- AVGBrowser.exe (PID: 9256)
- AVGBrowser.exe (PID: 9392)
- AVGBrowser.exe (PID: 9556)
- AVGBrowser.exe (PID: 9568)
- AVGBrowser.exe (PID: 9372)
- AVGBrowser.exe (PID: 9672)
- AVGBrowser.exe (PID: 9840)
- AVGBrowser.exe (PID: 9940)
- AVGBrowser.exe (PID: 9984)
- AVGBrowser.exe (PID: 10024)
- AVGBrowser.exe (PID: 10032)
- AVGBrowser.exe (PID: 10072)
- AVGBrowser.exe (PID: 10092)
- AVGBrowser.exe (PID: 10192)
- AVGBrowser.exe (PID: 8780)
- AVGBrowser.exe (PID: 4680)
- AVGBrowser.exe (PID: 9628)
- AVGBrowser.exe (PID: 5900)
- AVGBrowser.exe (PID: 9312)
- AVGBrowser.exe (PID: 9352)
- AVGBrowser.exe (PID: 8616)
- AVGBrowser.exe (PID: 5696)
- AVGBrowser.exe (PID: 9220)
- AVGBrowser.exe (PID: 9336)
- AVGBrowser.exe (PID: 7532)
Reads the computer name
- identity_helper.exe (PID: 8256)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserUpdate.exe (PID: 6592)
- AVGBrowserUpdate.exe (PID: 7904)
- AVGBrowserUpdate.exe (PID: 8760)
- AVGBrowserInstaller.exe (PID: 4404)
- setup.exe (PID: 1952)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 3304)
- AVGBrowser.exe (PID: 8328)
- AVGBrowser.exe (PID: 8904)
- AVGBrowser.exe (PID: 9372)
- AVGBrowser.exe (PID: 9568)
- AVGBrowser.exe (PID: 9556)
Reads Environment values
- identity_helper.exe (PID: 8256)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Launching a file from the Downloads directory
- msedge.exe (PID: 7816)
Application launched itself
- msedge.exe (PID: 7816)
Create files in a temporary directory
- avg_secure_browser_setup.exe (PID: 6460)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Executable content was dropped or overwritten
- msedge.exe (PID: 8040)
- msedge.exe (PID: 7816)
The sample compiled with english language support
- avg_secure_browser_setup.exe (PID: 6460)
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserInstaller.exe (PID: 4404)
- setup.exe (PID: 1952)
Process checks whether UAC notifications are on
- AVGBrowserInstaller.exe (PID: 6188)
Checks proxy server information
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdate.exe (PID: 7904)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Process checks computer location settings
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 6916)
- AVGBrowser.exe (PID: 6536)
- AVGBrowser.exe (PID: 7960)
- AVGBrowser.exe (PID: 9372)
- AVGBrowser.exe (PID: 9672)
- AVGBrowser.exe (PID: 5900)
- AVGBrowser.exe (PID: 9312)
- AVGBrowser.exe (PID: 7532)
- AVGBrowser.exe (PID: 9352)
Reads the machine GUID from the registry
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
The sample compiled with slovak language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with arabic language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
- setup.exe (PID: 1952)
The sample compiled with bulgarian language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with czech language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with french language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with german language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with Italian language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with Indonesian language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with korean language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with japanese language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with polish language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with portuguese language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with russian language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with swedish language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
The sample compiled with chinese language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
Creates files or folders in the user directory
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowserUpdate.exe (PID: 4472)
- AVGBrowserInstaller.exe (PID: 4404)
- setup.exe (PID: 1952)
- setup.exe (PID: 7120)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 8328)
- AVGBrowser.exe (PID: 9372)
- AVGBrowser.exe (PID: 9392)
- AVGBrowser.exe (PID: 9568)
The sample compiled with turkish language support
- AVGBrowserUpdateSetup.exe (PID: 6900)
- AVGBrowserUpdate.exe (PID: 2452)
Launching a file from a Registry key
- AVGBrowserUpdate.exe (PID: 2452)
- AVGBrowser.exe (PID: 8228)
Creates a software uninstall entry
- setup.exe (PID: 1952)
- AVGBrowserInstaller.exe (PID: 6188)
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Reads CPU info
- AVGBrowser.exe (PID: 8228)
- AVGBrowser.exe (PID: 9372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
234
Monitored processes
86
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=9112,i,8351791794054919284,17257179963460539078,262144 --variations-seed-version --mojo-platform-channel-handle=9196 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3640,i,8351791794054919284,17257179963460539078,262144 --variations-seed-version --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\AppData\Local\AVG\Browser\Update\Install\{CEC96228-AE14-4F5D-8B9C-88868B1339E6}\CR_E9FD0.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\AVG\Browser\Update\Install\{CEC96228-AE14-4F5D-8B9C-88868B1339E6}\CR_E9FD0.tmp\SECURE.PACKED.7Z" --chrome --do-not-launch-chrome --hide-browser-override --show-developer-mode --suppress-first-run-bubbles --default-search-id=3 --default-search=bing.com --adblock-mode-default=0 --no-create-user-shortcuts --make-chrome-default --force-default-win10 --auto-import-data=msedge --import-cookies | C:\Users\admin\AppData\Local\AVG\Browser\Update\Install\{CEC96228-AE14-4F5D-8B9C-88868B1339E6}\CR_E9FD0.tmp\setup.exe | AVGBrowserInstaller.exe | ||||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: MEDIUM Description: AVG Secure Browser Installer Exit code: 0 Version: 143.0.33371.147 Modules
| |||||||||||||||
| 2452 | C:\Users\admin\AppData\Local\Temp\GUM514E.tmp\AVGBrowserUpdate.exe /silent /install "bundlename=AVG Secure Browser&appguid={48F69C39-1356-4A7B-A899-70E3539D4982}&appname=AVG Secure Browser&needsadmin=false&lang=en&brand=9274&installargs= --no-create-user-shortcuts --make-chrome-default --force-default-win10 --auto-import-data%3Dmsedge --import-cookies" | C:\Users\admin\AppData\Local\Temp\GUM514E.tmp\AVGBrowserUpdate.exe | AVGBrowserUpdateSetup.exe | ||||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: MEDIUM Description: AVG Browser Exit code: 0 Version: 1.8.1996.6 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserUpdateComRegisterShell64.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: MEDIUM Description: AVG Browser Com Register Shell 64 Exit code: 0 Version: 1.8.1996.6 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserUpdateComRegisterShell64.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: MEDIUM Description: AVG Browser Com Register Shell 64 Exit code: 0 Version: 1.8.1996.6 Modules
| |||||||||||||||
| 2912 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1352,i,8351791794054919284,17257179963460539078,262144 --variations-seed-version --mojo-platform-channel-handle=7280 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserCrashHandler64.exe" | C:\Users\admin\AppData\Local\AVG\Browser\Update\1.8.1996.6\AVGBrowserCrashHandler64.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: MEDIUM Description: AVG Browser Crash Handler Exit code: 0 Version: 1.8.1996.6 Modules
| |||||||||||||||
| 3304 | "C:\Users\admin\AppData\Local\AVG\Browser\Application\AVGBrowser.exe" --type=gpu-process --force-high-res-timeticks=disabled --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --metrics-shmem-handle=1984,i,8210537842711715309,12177001660804317835,262144 --field-trial-handle=2084,i,14402676498910694237,4200999897219863257,262144 --variations-seed-version --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=2080 /prefetch:2 | C:\Users\admin\AppData\Local\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 143.0.33371.147 Modules
| |||||||||||||||
Total events
10 979
Read events
9 965
Write events
953
Delete events
61
Modification events
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser |
| Operation: | write | Name: | user_id |
Value: 364ba00896e344b8af90a46c6a5da731 | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser |
| Operation: | write | Name: | user_timestamp |
Value: 1767614958 | |||
| (PID) Process: | (2452) AVGBrowserUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser\Update |
| Operation: | write | Name: | devmode |
Value: 0 | |||
| (PID) Process: | (2452) AVGBrowserUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser\Update |
| Operation: | write | Name: | endpoint |
Value: update.avgbrowser.com | |||
| (PID) Process: | (2452) AVGBrowserUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser\Update |
| Operation: | write | Name: | hostprefix |
Value: | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser |
| Operation: | write | Name: | BankMode |
Value: 1 | |||
| (PID) Process: | (6188) AVGBrowserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AVG\Browser\Update |
| Operation: | write | Name: | MachineId |
Value: 00000000000000000000000000000000E67CAB79AE400BF62D27B6F892308F1E | |||
Executable files
177
Suspicious files
294
Text files
753
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdfc8.TMP | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdfd7.TMP | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdfd7.TMP | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfdfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
182
TCP/UDP connections
156
DNS requests
160
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/ | US | html | 128 Kb | unknown |
8040 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
8040 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
8040 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:HqVj7YTSx_QVy8WMDtx_Q_c8uIh5z5PYnJ6K-XCwiY0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/applications/core/interface/font/fontawesome-webfont.woff2?v=4.7.0 | US | binary | 75.3 Kb | unknown |
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/uploads/css_built_32/341e4a57816af3ba440d891ca87450ff_framework.css?v=2ee4c756441766835470 | US | text | 128 Kb | unknown |
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/uploads/css_built_32/97c0a48072ce601c9764cb6b00a6588a_page.css?v=2ee4c756441766835470 | US | text | 316 b | unknown |
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/uploads/css_built_32/5a0da001ccc2200dc5625c3f3934497d_core_responsive.css?v=2ee4c756441766835470 | US | text | 4.95 Kb | unknown |
8040 | msedge.exe | GET | 200 | 104.21.87.218:443 | https://www.1tamilmv.lc/uploads/css_built_32/90eb5adf50a8c640f633d47fd7eb1778_core.css?v=2ee4c756441766835470 | US | text | 26.5 Kb | unknown |
8040 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1784 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5436 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8040 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8040 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8040 | msedge.exe | 104.21.87.218:443 | www.1tamilmv.lc | CLOUDFLARENET | US | whitelisted |
8040 | msedge.exe | 142.250.184.200:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
8040 | msedge.exe | 142.250.185.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.1tamilmv.lc |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
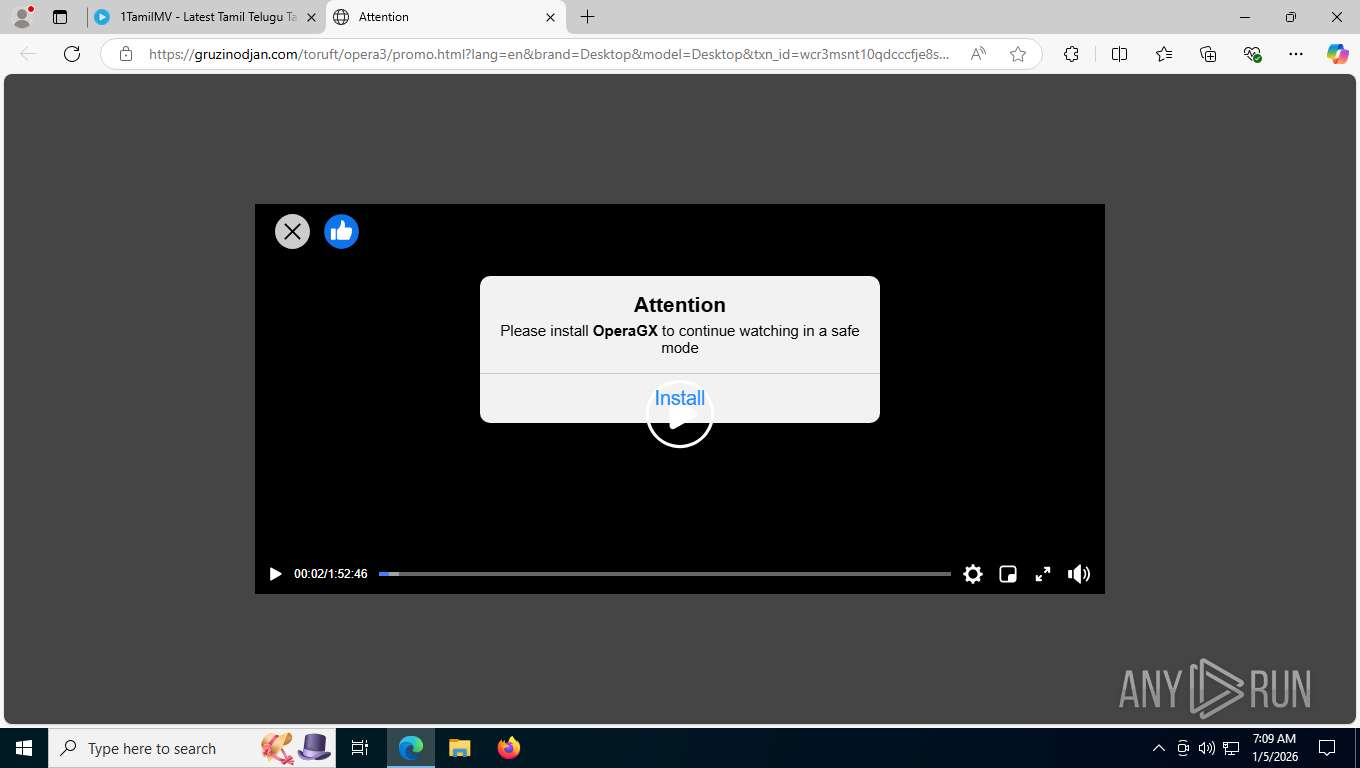
8040 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ghabovethec .info) |
8040 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ukankingwithea .com) |
— | — | Attempted Information Leak | SUSPICIOUS [ANY.RUN] FingerprintJS Usage Observed in HTTP response |
— | — | Attempted Information Leak | SUSPICIOUS [ANY.RUN] FingerprintJS Usage Observed in HTTP response |
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
9568 | AVGBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
9568 | AVGBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
Process | Message |
|---|---|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:167) ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:168) Jinx logging started
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:169) ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:171)
build date: Nov 25 2025
build number: 1733
build time: 19:34:52
build timestamp: Nov 25 2025 19:34:52
company: Gen Digital Inc.
copyright: (C) 2017-2025 Gen Digital Inc.
description: Secure Browser Installer
file name: AVGBrowserInstaller.exe
file version: 9.3.2.1733
git commit: d88e2deed6ef3bceaa97f4975153f45fa68d8cd9
internal name: jinx-installer
product name: Secure Browser Installer
product version: 9.3.2.1733
target system: windows
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:181) Operating system: Windows Enterprise x64 10.0.19045.4046 SP0
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:184) Process is not elevated.
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:190) Process owner: DESKTOP-JGLLJLD\admin (logon=true, admin=true)
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <2:Info> (4bbd888238eee7c1\src\jinx\Logging.cpp:106)
Command line: "C:\Users\admin\AppData\Local\Temp\nso41FD.tmp\AVGBrowserInstaller.exe" "C:\Users\admin\Downloads\avg_secure_browser_setup.exe"
User dotfile was used: false
Global dotfile was used: false
Execution arguments:
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <1:Debug> (4bbd888238eee7c1\src\jinx\VmDetect.cpp:203) Starting VM Detection system
|
AVGBrowserInstaller.exe | 2026-01-05T07:09:17 [installer] {0000182c:00002208} <1:Debug> (4bbd888238eee7c1\src\jinx\TagData.cpp:457) TagData: Extracting from "C:\Users\admin\Downloads\avg_secure_browser_setup.exe" using start marker '<##TAGDATA##>' and end marker '</##TAGDATA##>'
|