| File name: | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma |
| Full analysis: | https://app.any.run/tasks/66d70e91-7351-484c-b222-3907f1f92925 |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2023, 05:34:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D4726540EF9E6BFC0821650DB0E62DA3 |
| SHA1: | 8881BC14DA432189E8AE2494C54BB9DB5690B06B |
| SHA256: | F06EEC18F16BEBED895404D4D77863A2F157CF12695DF1B0710F865DC7A5BE4B |
| SSDEEP: | 3072:oaPFEQ/ZmQxAaZm6eHNW8V+IcTZ/tA2gr7EW2ZwPdxRT3qRnxQC6BK1/60zWsiKd:okkRu3fyqPRoAXW8 |
MALICIOUS
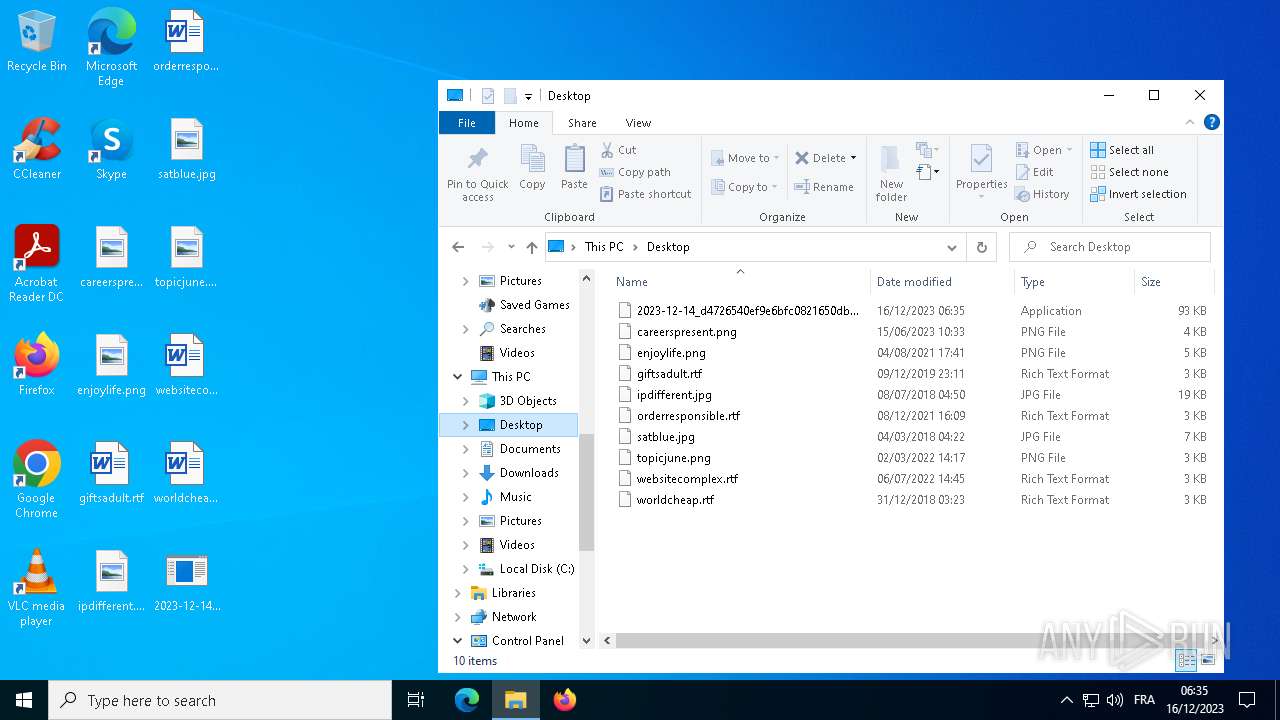
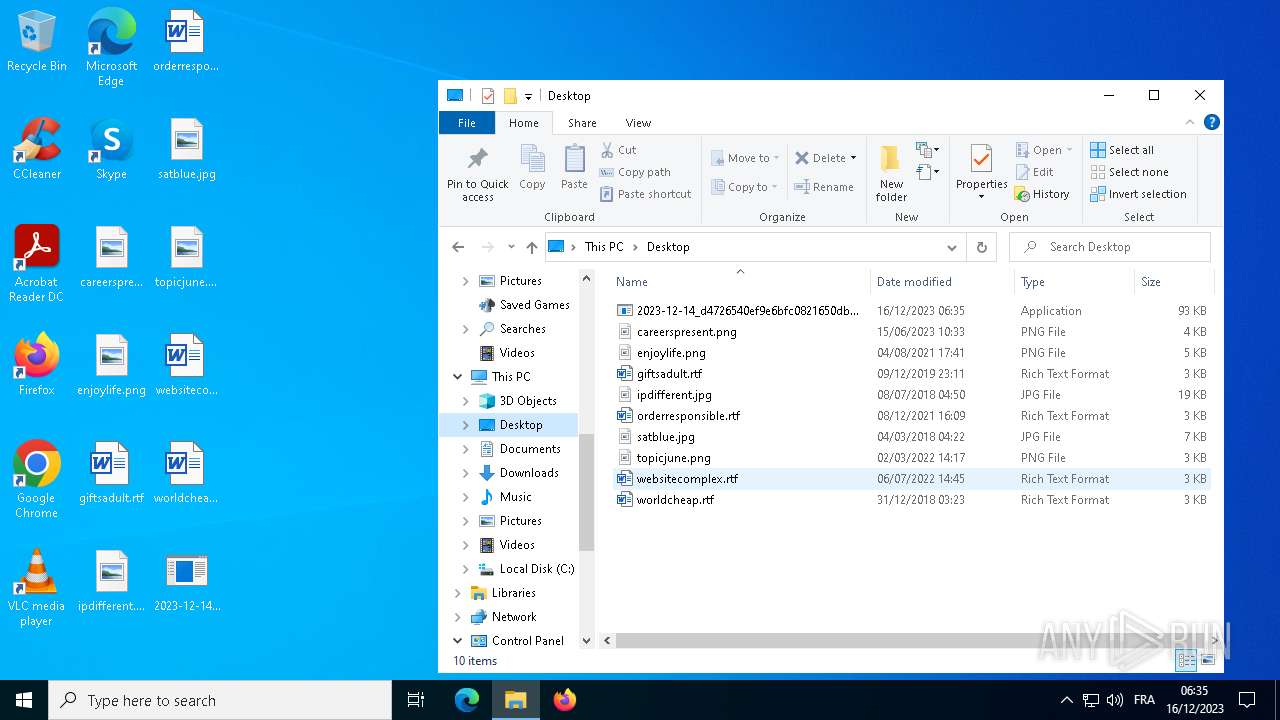
Create files in the Startup directory
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Deletes shadow copies
- cmd.exe (PID: 2320)
- cmd.exe (PID: 5220)
- cmd.exe (PID: 7020)
Drops the executable file immediately after the start
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Creates a writable file in the system directory
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Actions looks like stealing of personal data
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
SUSPICIOUS
Reads the date of Windows installation
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
Starts CMD.EXE for commands execution
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Application launched itself
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
Process drops legitimate windows executable
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Executes as Windows Service
- VSSVC.exe (PID: 6600)
The process creates files with name similar to system file names
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
INFO
Creates files or folders in the user directory
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
Checks supported languages
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
- mode.com (PID: 6288)
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
- mode.com (PID: 5584)
- mode.com (PID: 6216)
Reads the computer name
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3876)
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
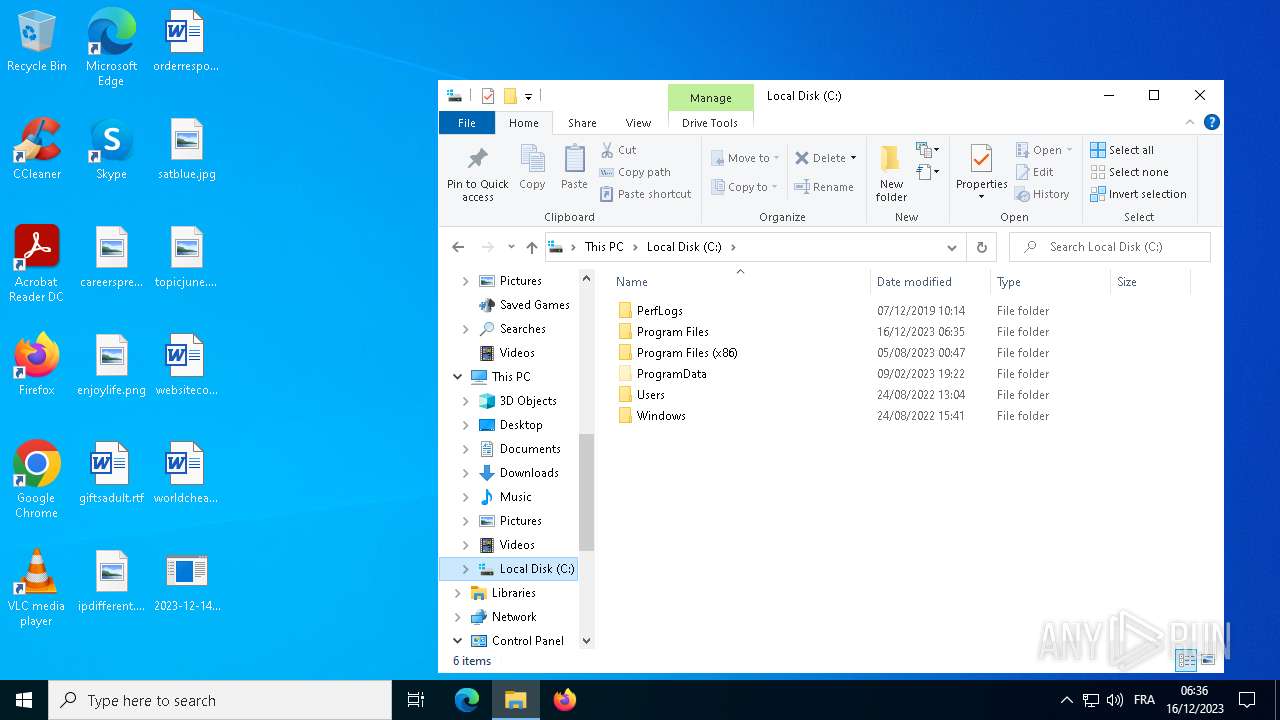
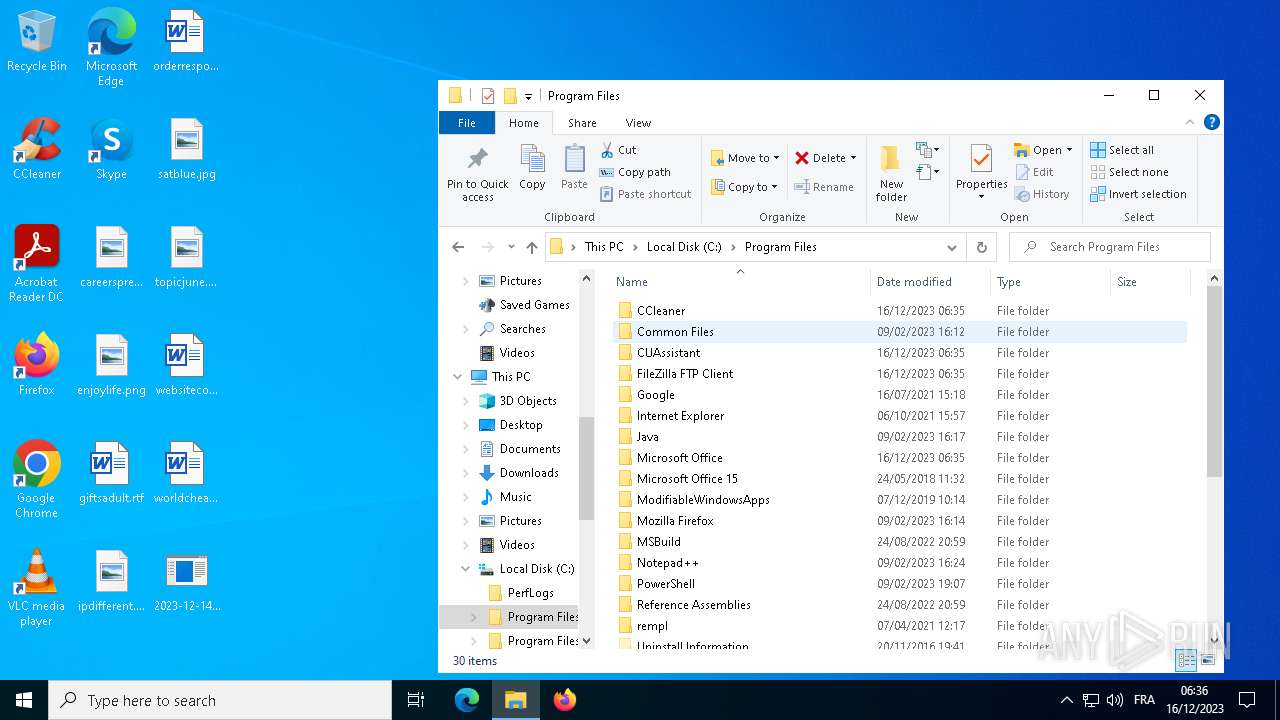
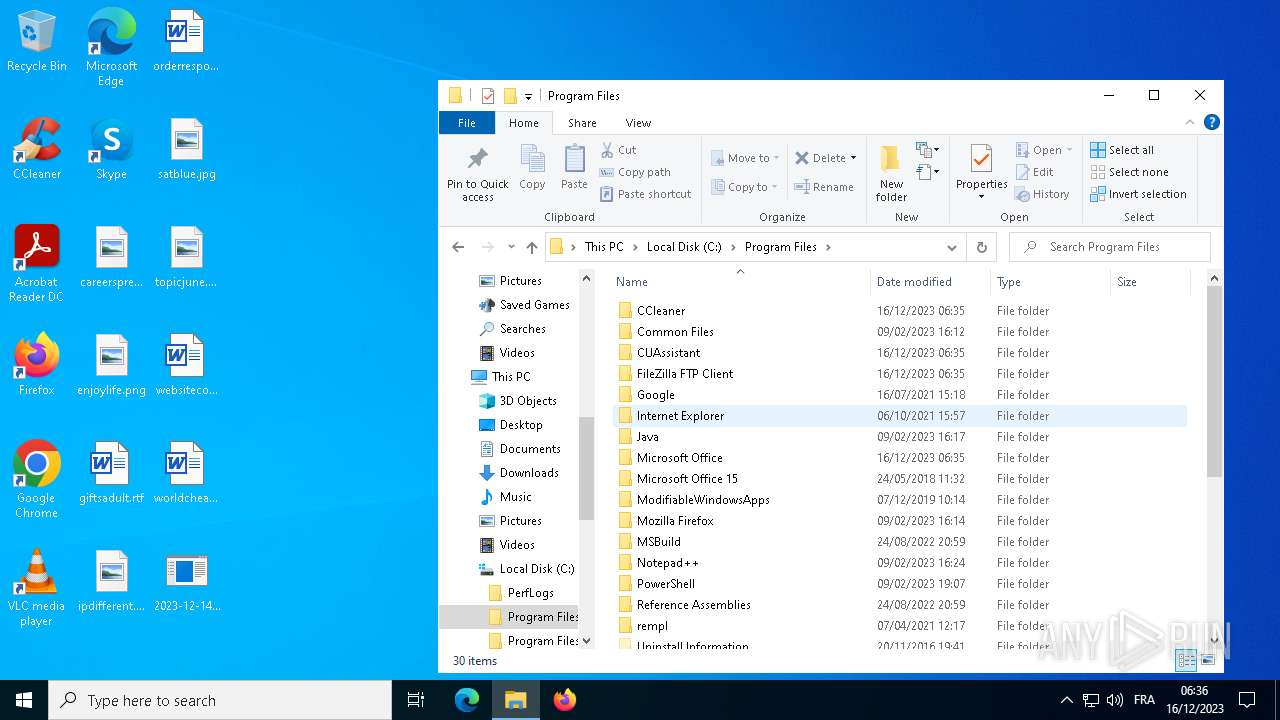
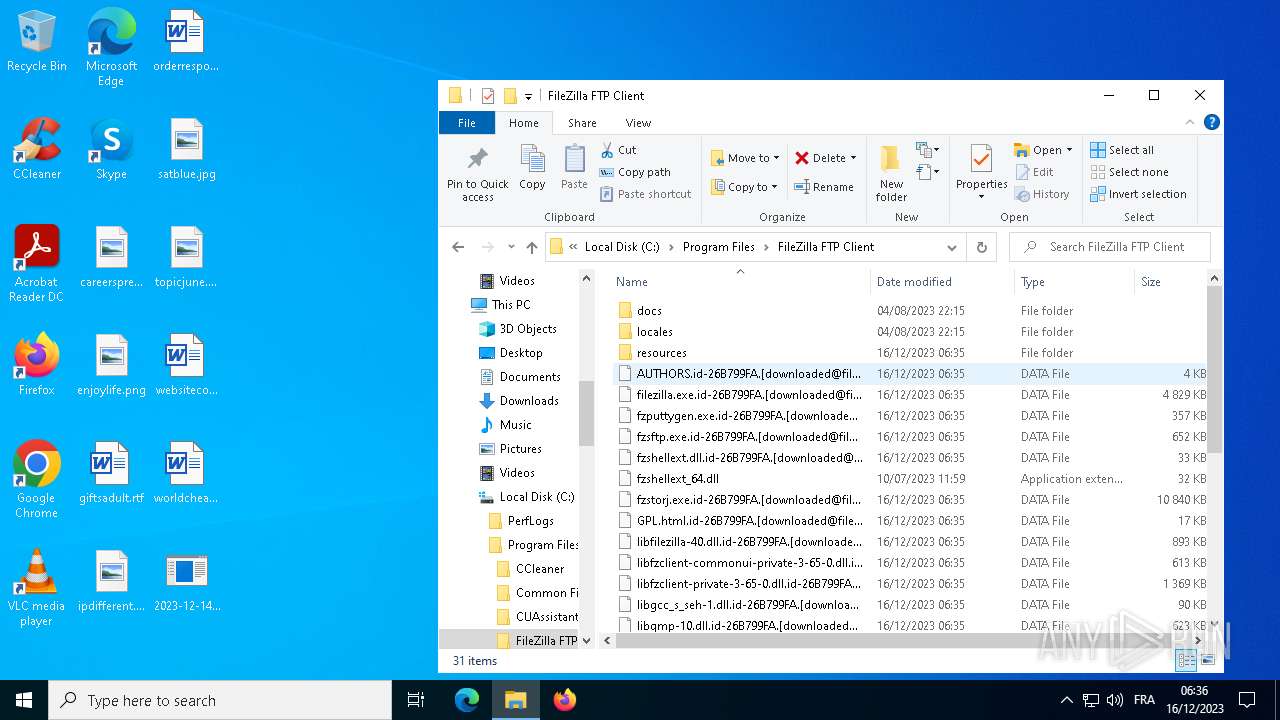
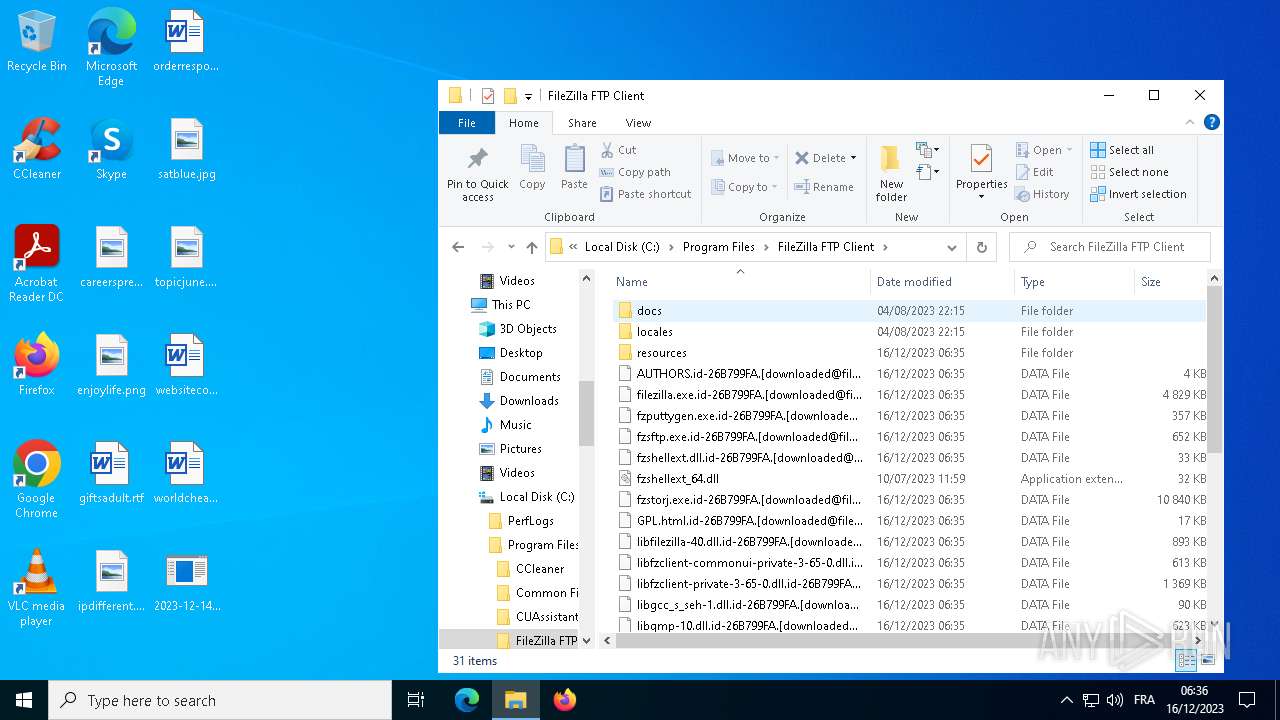
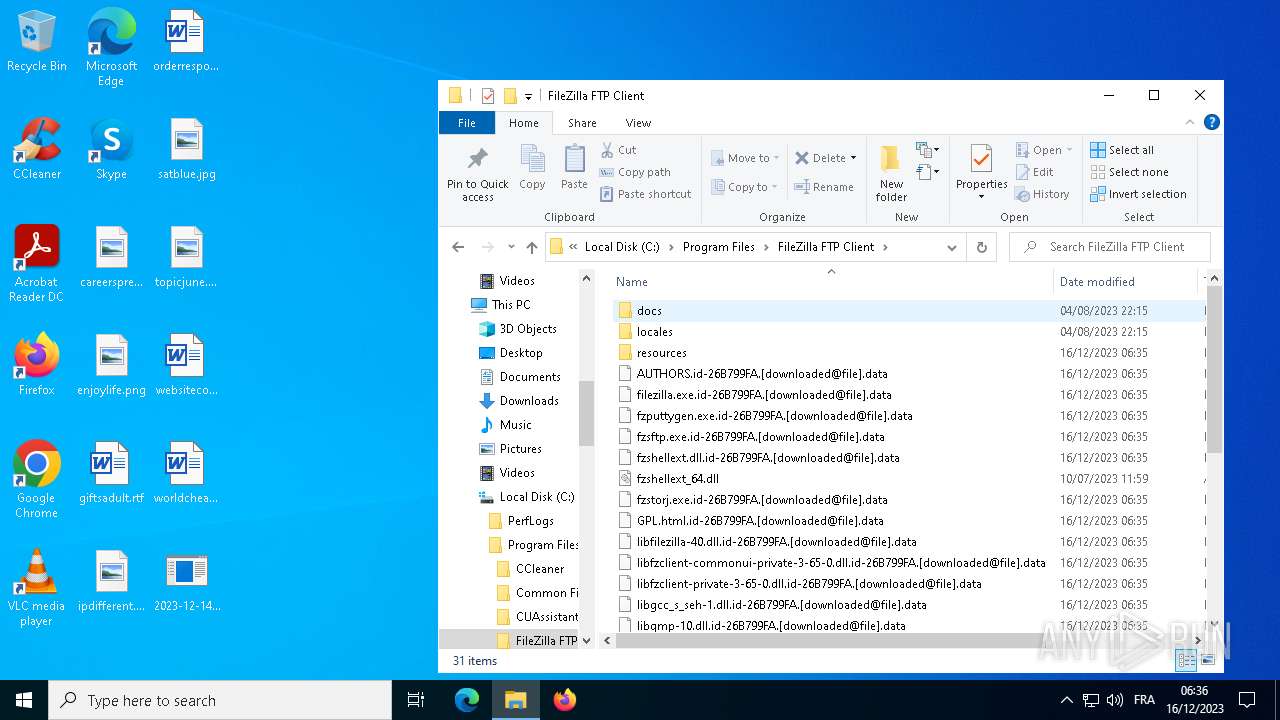
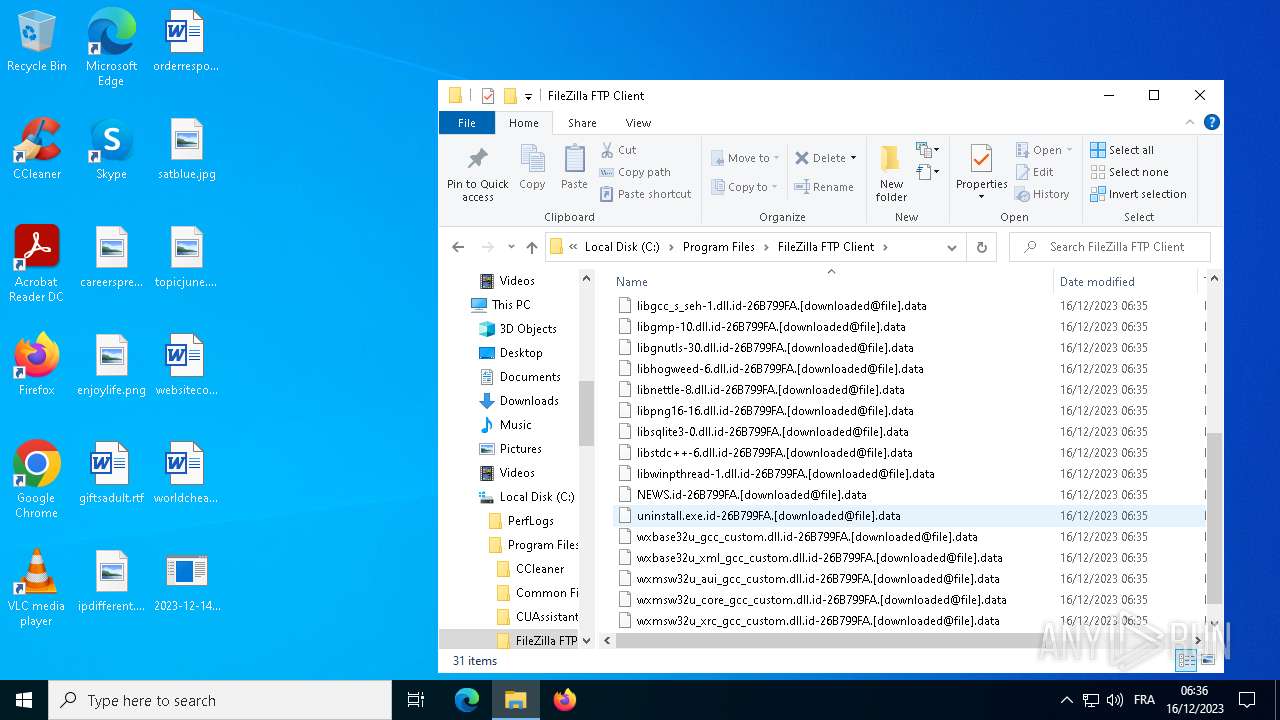
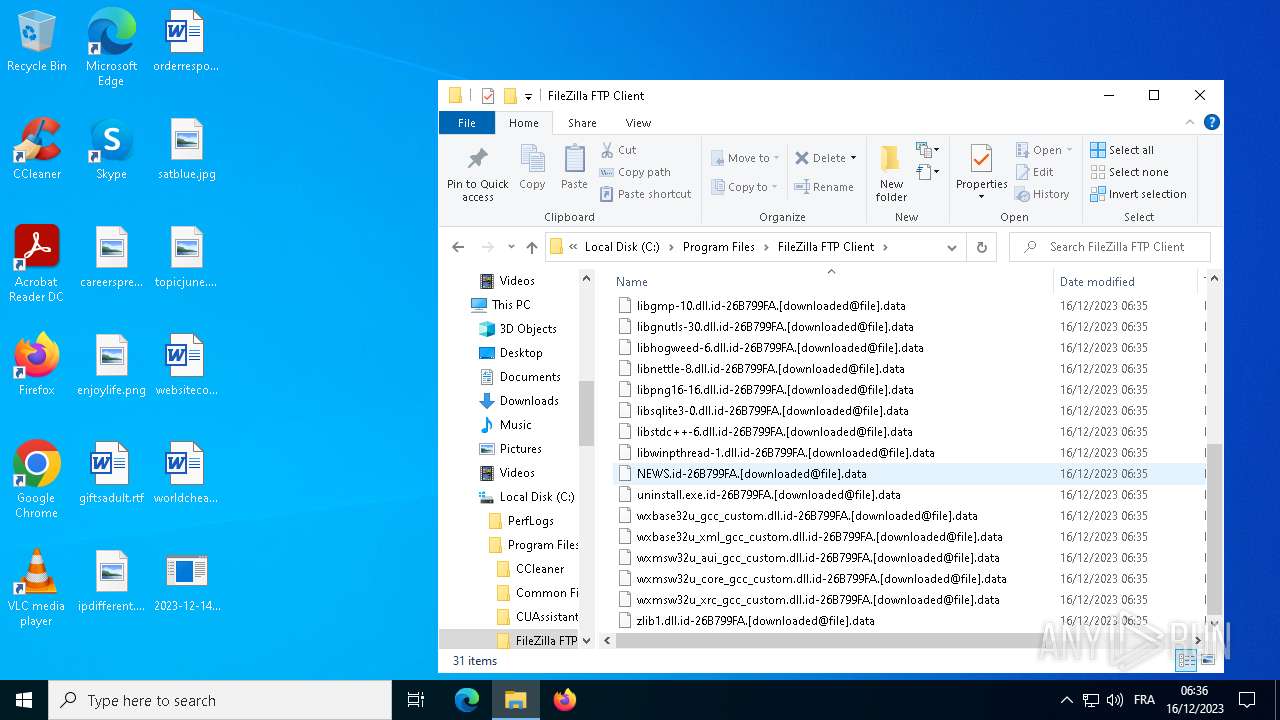
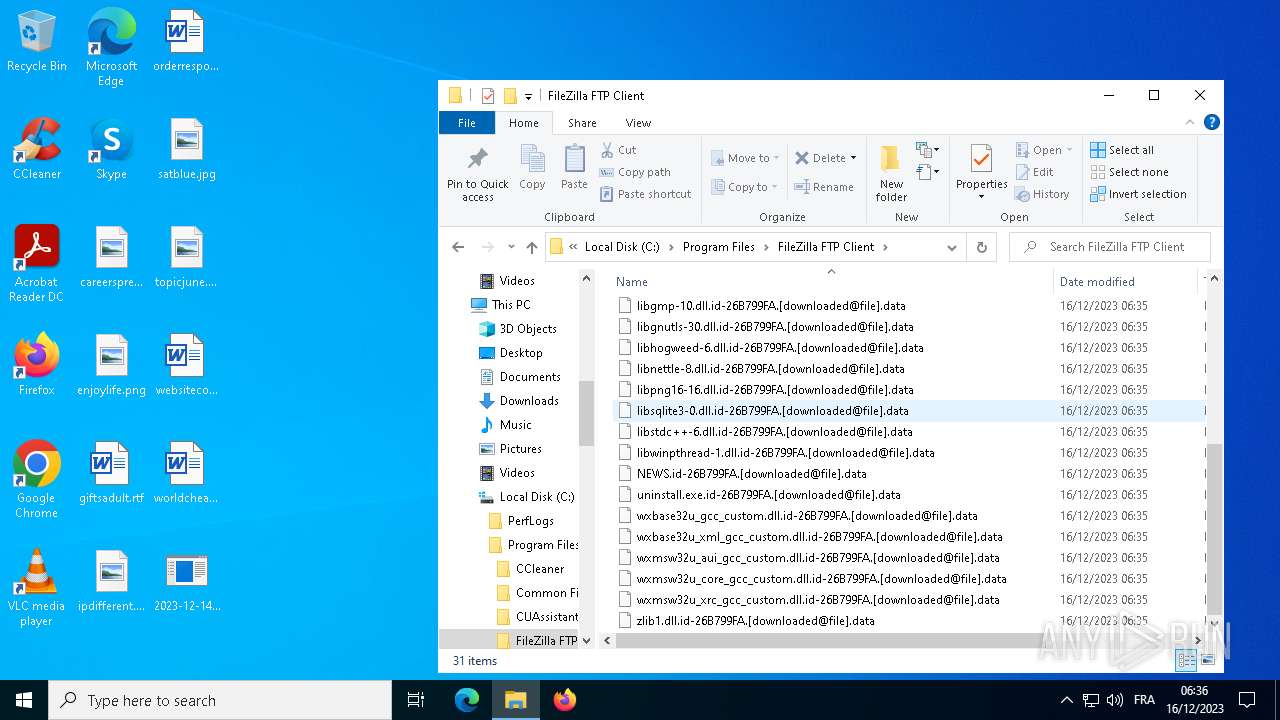
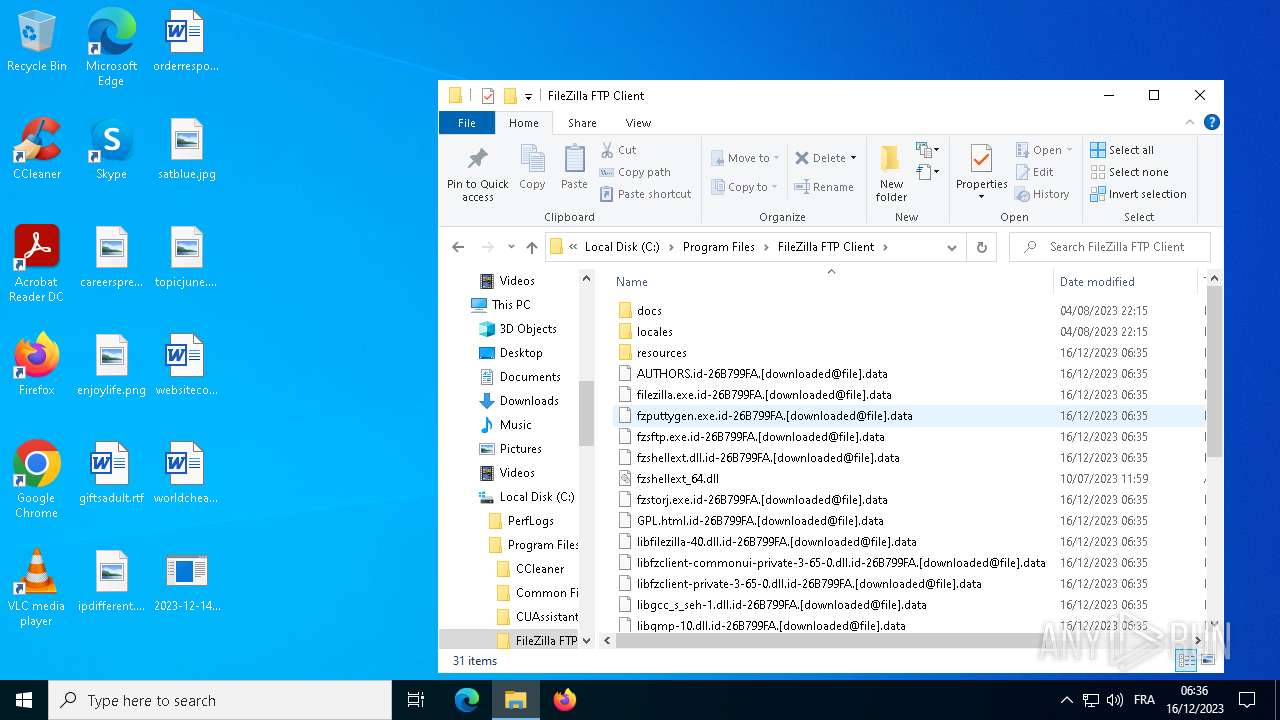
Creates files in the program directory
- 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:03:03 00:49:06+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 40448 |
| InitializedDataSize: | 54272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa9d0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
137
Monitored processes
15
Malicious processes
5
Suspicious processes
0
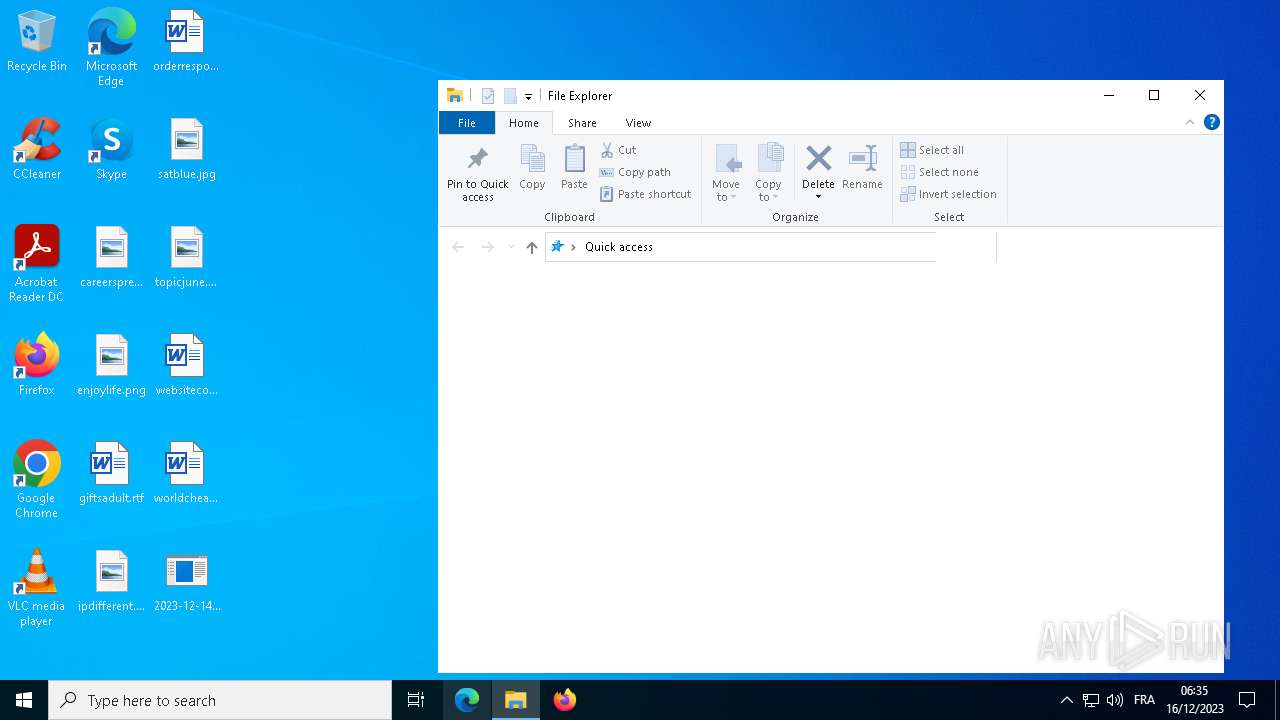
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1572 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3860 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3876 | "C:\Users\admin\Desktop\2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe" | C:\Users\admin\Desktop\2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\Desktop\2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe" -a | C:\Users\admin\Desktop\2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5220 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5584 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6216 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
839
Read events
831
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3876) 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3876) 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3876) 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3876) 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
223
Suspicious files
12 807
Text files
60
Unknown types
473
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\BOOTNXT | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\bootTel.dat | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\Common Files\Adobe\Acrobat\Setup\{AC76BA86-1033-1033-7760-BC15014EA700}\setup.ini | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\Common Files\Adobe\Acrobat\Setup\{AC76BA86-1033-1033-7760-BC15014EA700}\abcpy.ini | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\Common Files\DESIGNER\MSADDNDR.OLB | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\CUAssistant\CUAssistantTask.xml | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\CUAssistant\CUAssistantRebootTask.xml | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\CUAssistant\OkDone_80.png | — | |
MD5:— | SHA256:— | |||
| 3876 | 2023-12-14_d4726540ef9e6bfc0821650db0e62da3_crysis_dharma.exe | C:\Program Files\CUAssistant\RestartNowPower_80.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
2344 | svchost.exe | GET | 200 | 23.53.41.88:80 | http://crl.microsoft.com/pki/crl/products/MicWinPCA_2010-07-06.crl | DE | binary | 552 b | unknown |
2344 | svchost.exe | GET | 200 | 23.53.41.88:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.11 Kb | unknown |
2344 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | unknown |
2344 | svchost.exe | GET | 200 | 23.53.41.88:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | unknown |
7148 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | FR | binary | 418 b | unknown |
7148 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | FR | binary | 409 b | unknown |
2344 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | DE | binary | 1.05 Kb | unknown |
6796 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2832 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2832 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6796 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
6796 | backgroundTaskHost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
7148 | SIHClient.exe | 40.127.169.103:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7148 | SIHClient.exe | 2.18.97.123:80 | www.microsoft.com | Akamai International B.V. | FR | unknown |
7148 | SIHClient.exe | 13.85.23.206:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2344 | svchost.exe | 23.53.41.88:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |