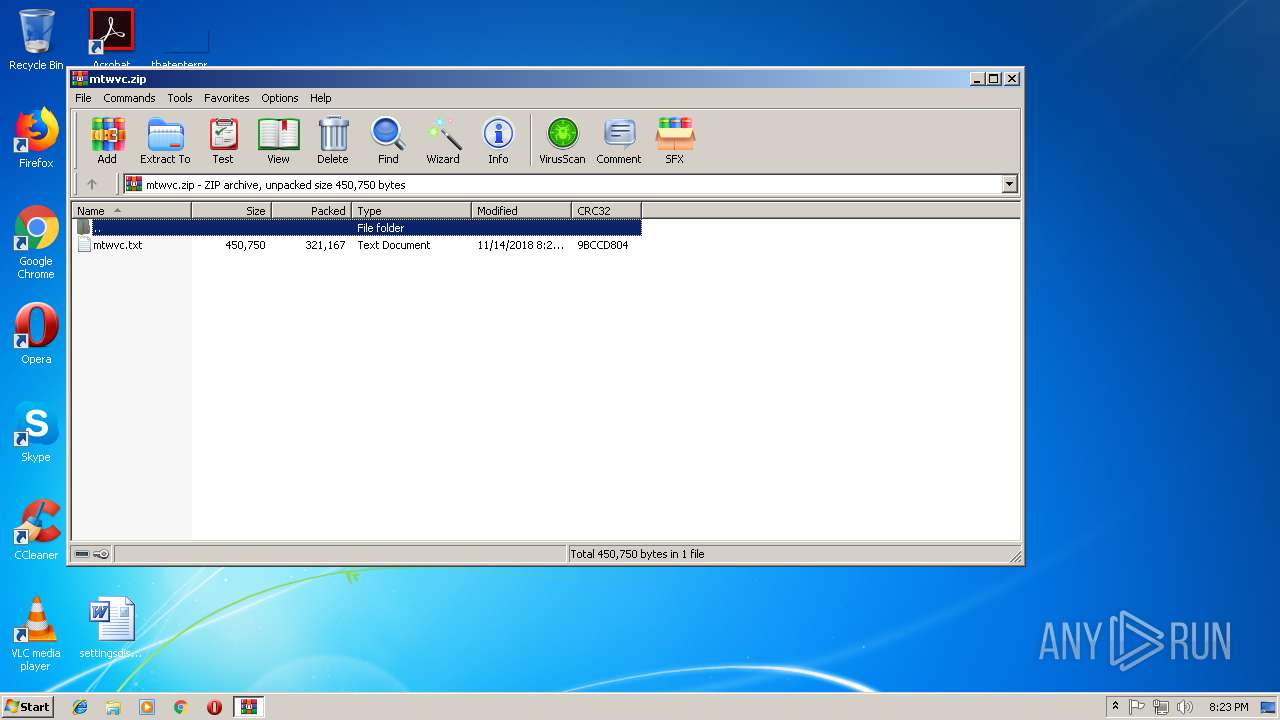
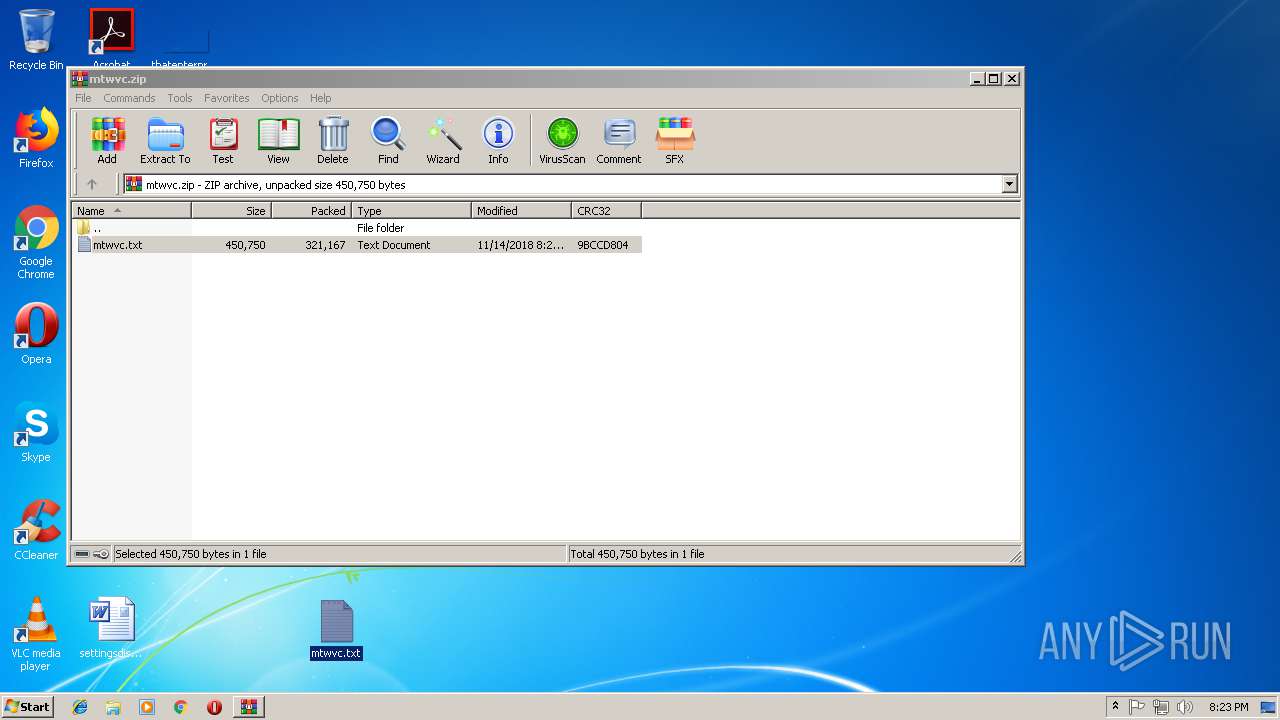
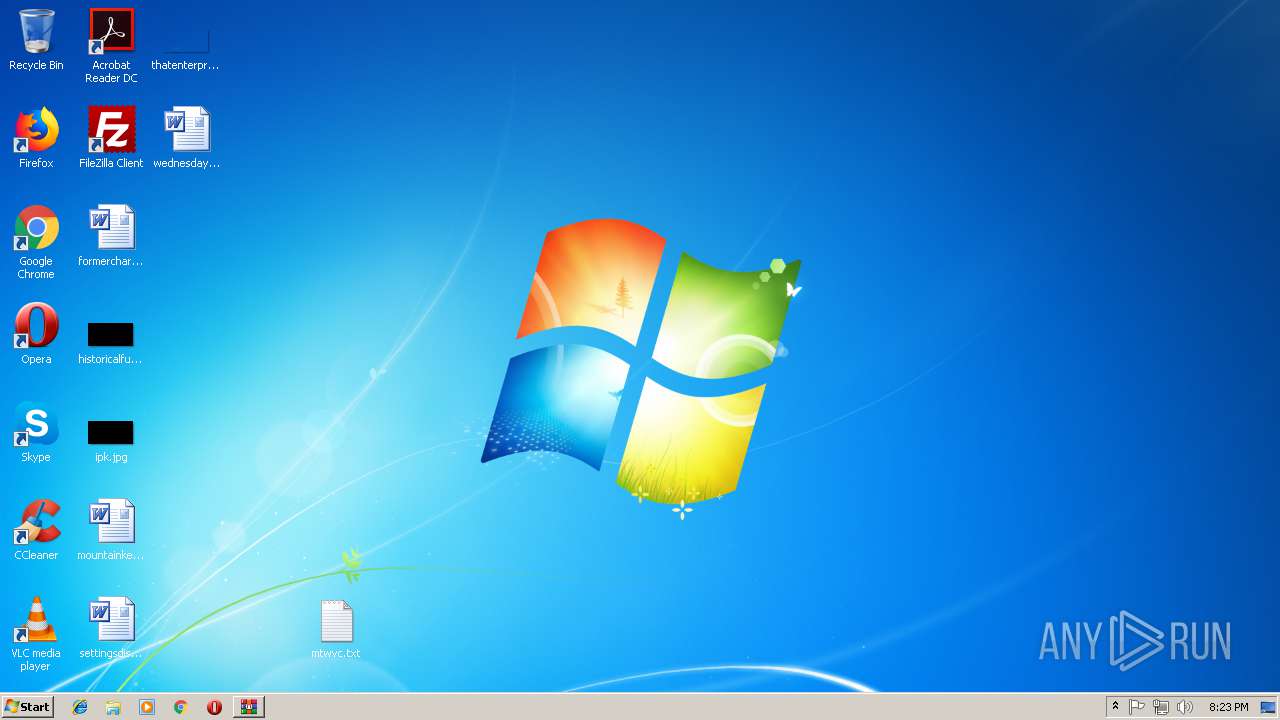
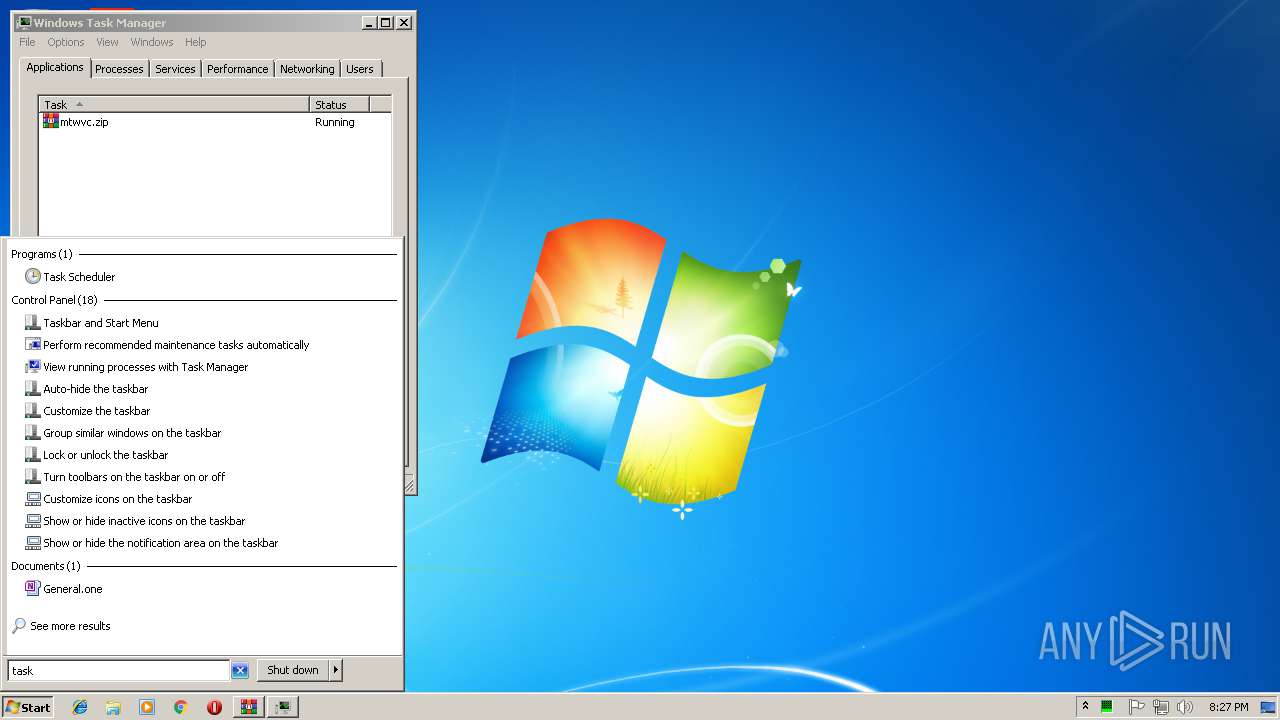
| File name: | mtwvc.zip |
| Full analysis: | https://app.any.run/tasks/e27bf5b6-673c-434d-b108-81108d37d444 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 20:22:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 86F4733FB5A4BEF3DAE7418CF6B8B40A |
| SHA1: | D02660F42B196E47B8A25E9F0BD67DBE4EA5FD2A |
| SHA256: | F0697C7AA4BE9C511E0AF32AF7D31D2E80445FC243885DBF39FA1734816D8854 |
| SSDEEP: | 6144:pXFz/r0zt9hdNBHT2UYnRCI/kd1GS94Cpbe1AnnZcIYVEooj82HpXMs:j7MlTJYRC8krGS94AeCnZIVEjHcs |
MALICIOUS
Stops/Deletes Windows Defender service
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 3336)
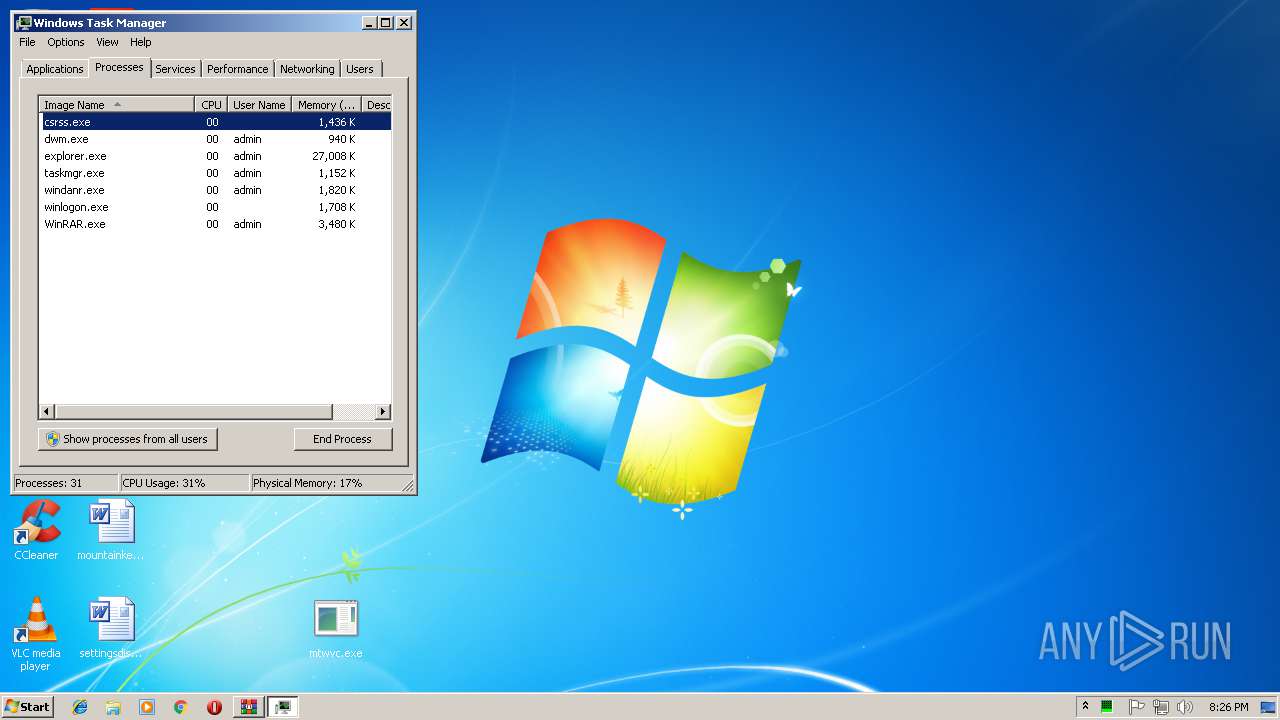
Application was dropped or rewritten from another process
- mtwvc.exe (PID: 2724)
- mtwvc.exe (PID: 1720)
- mtwvc.exe (PID: 1820)
- mtwvc.exe (PID: 3984)
- mtwvc.exe (PID: 340)
Known privilege escalation attack
- DllHost.exe (PID: 3320)
- DllHost.exe (PID: 2452)
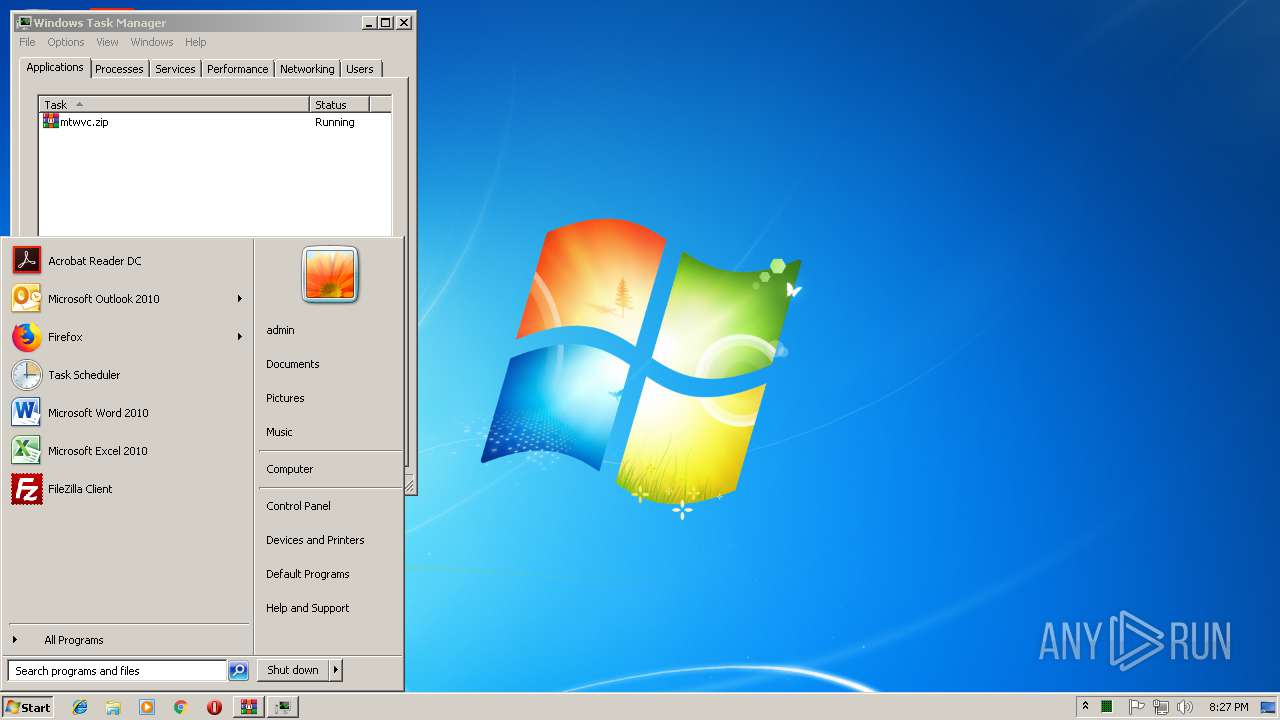
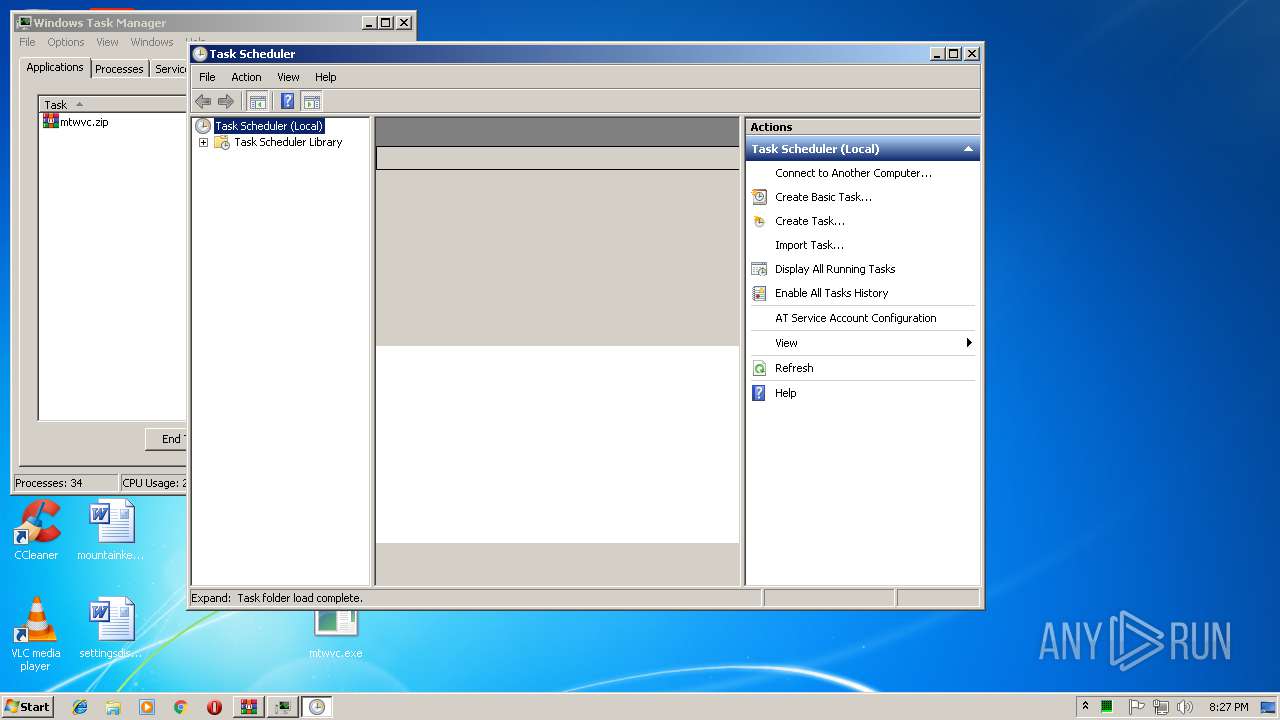
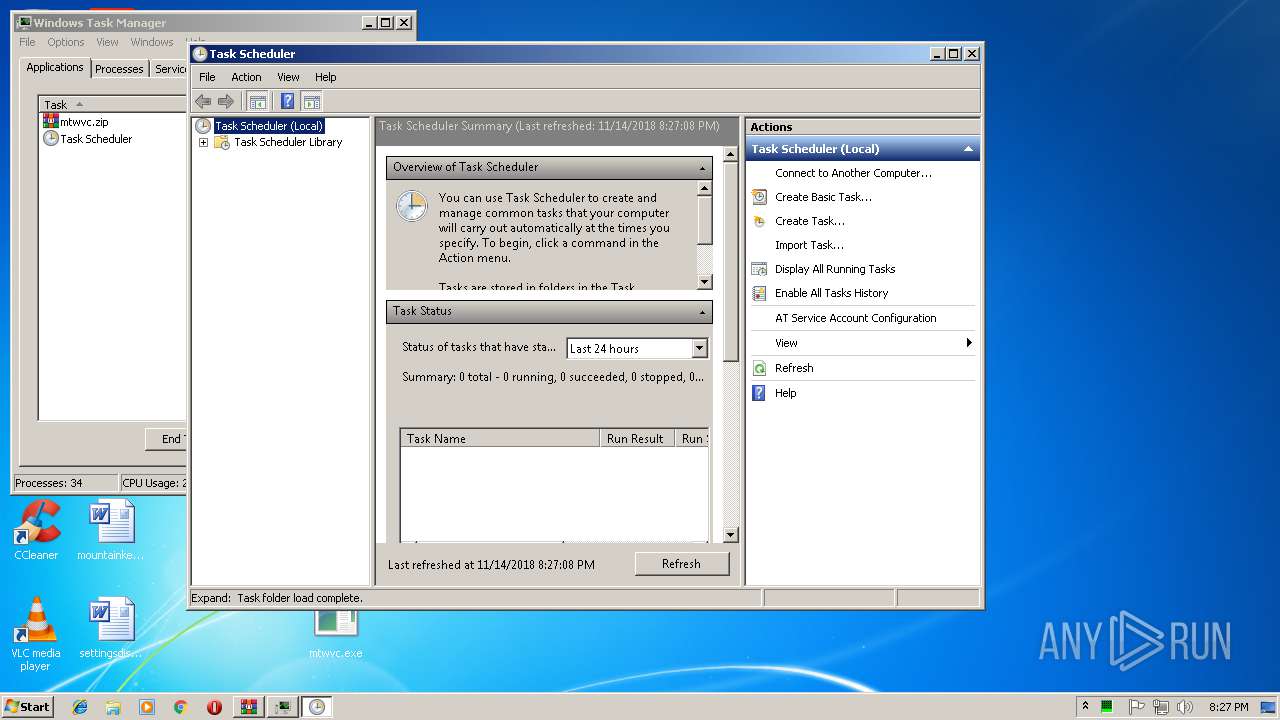
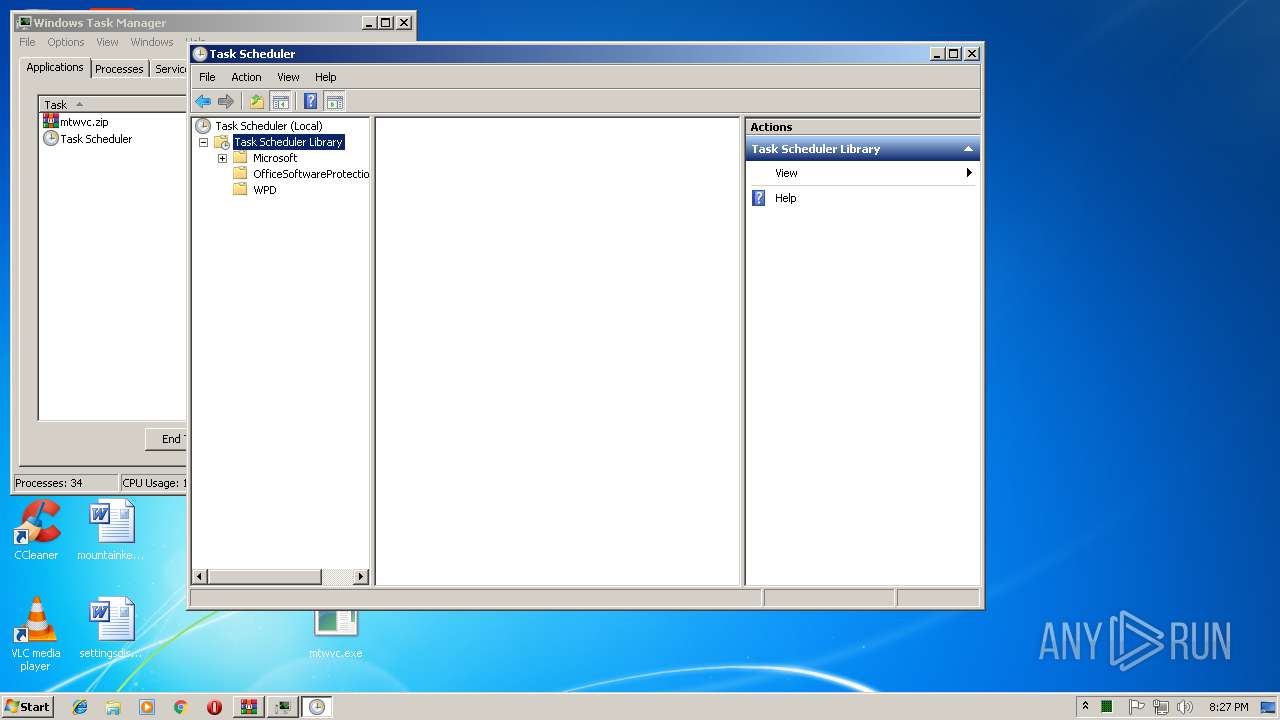
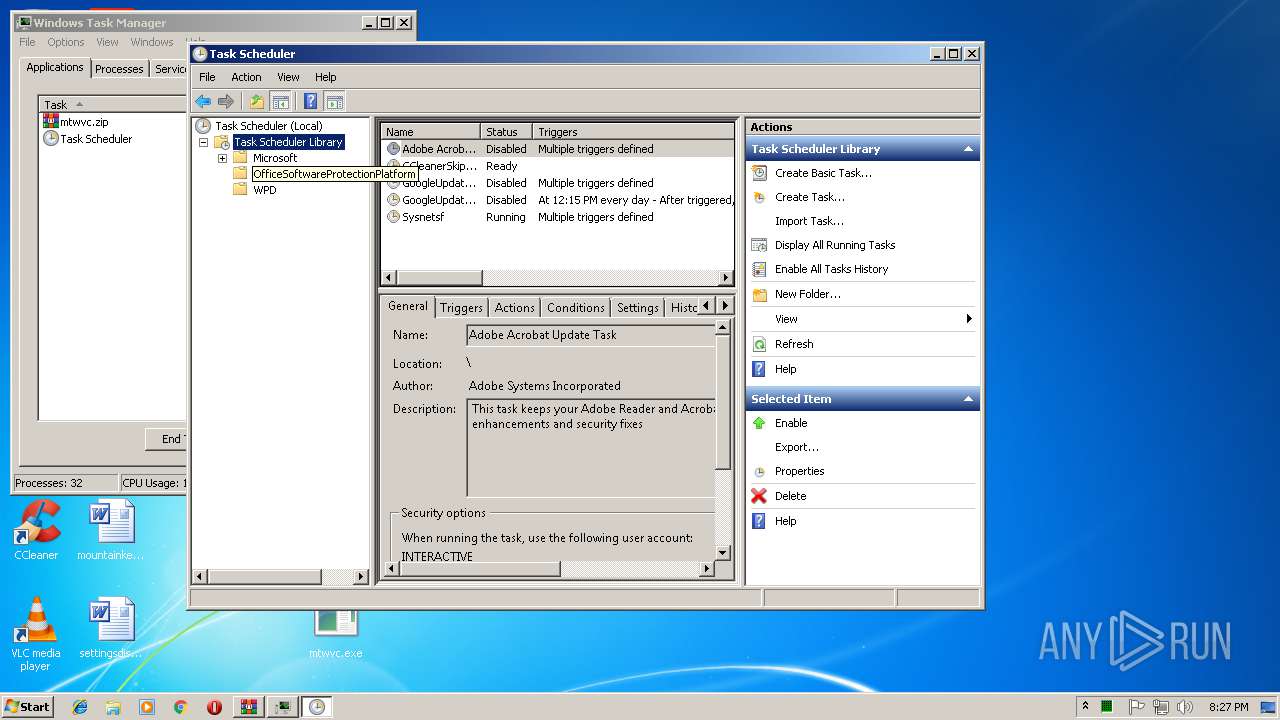
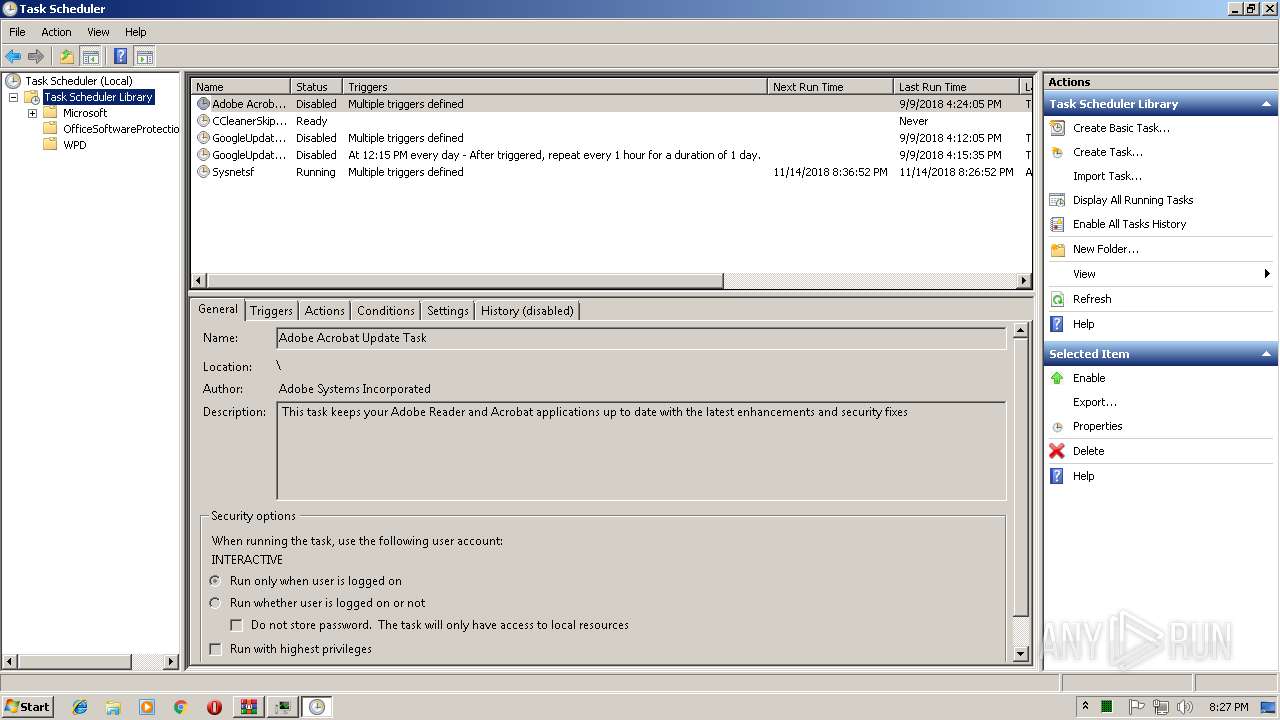
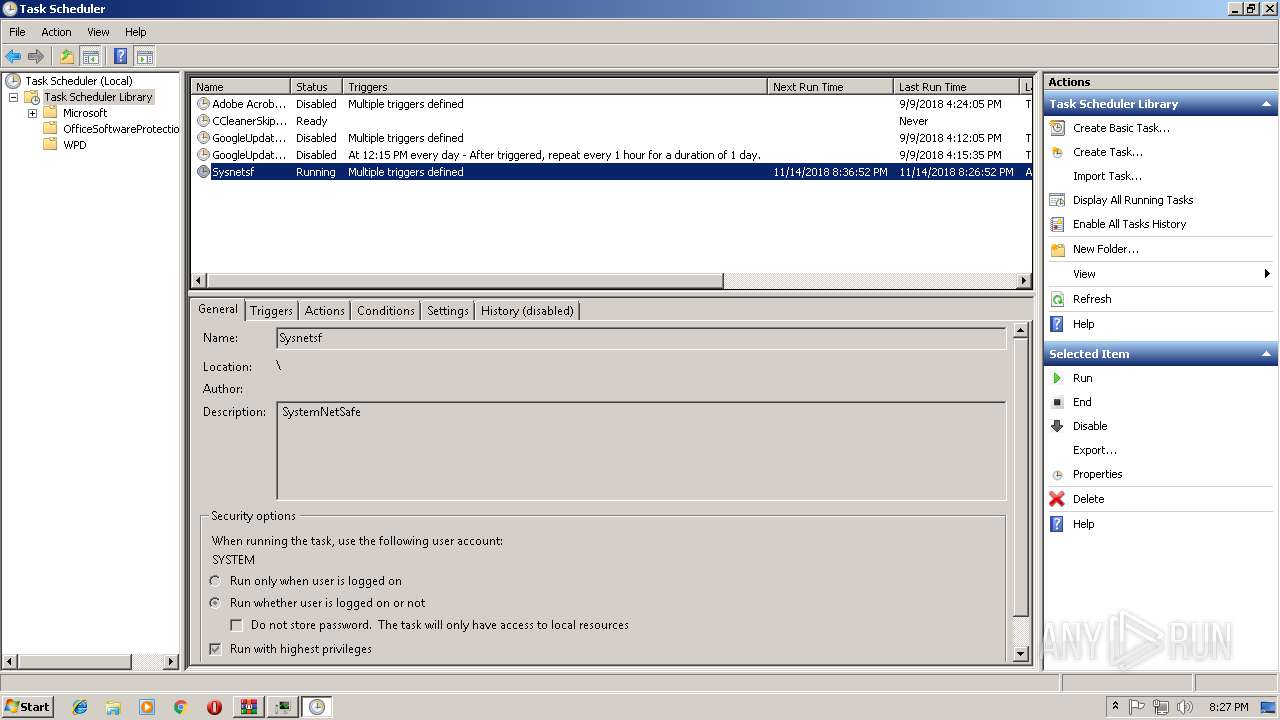
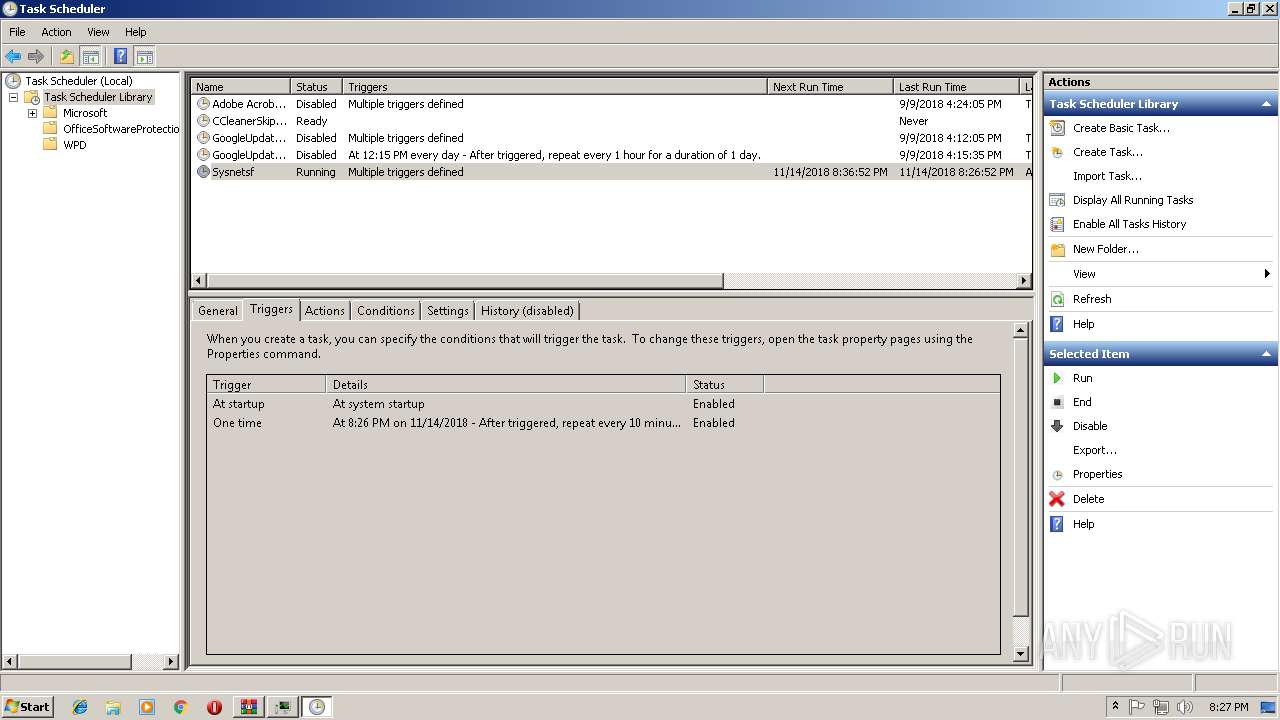
Loads the Task Scheduler COM API
- mtwvc.exe (PID: 1720)
- mtwvc.exe (PID: 3984)
- mmc.exe (PID: 2624)
- mtwvc.exe (PID: 340)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3084)
- mtwvc.exe (PID: 2724)
- powershell.exe (PID: 1796)
- mtwvc.exe (PID: 340)
Executes PowerShell scripts
- cmd.exe (PID: 3576)
- cmd.exe (PID: 2740)
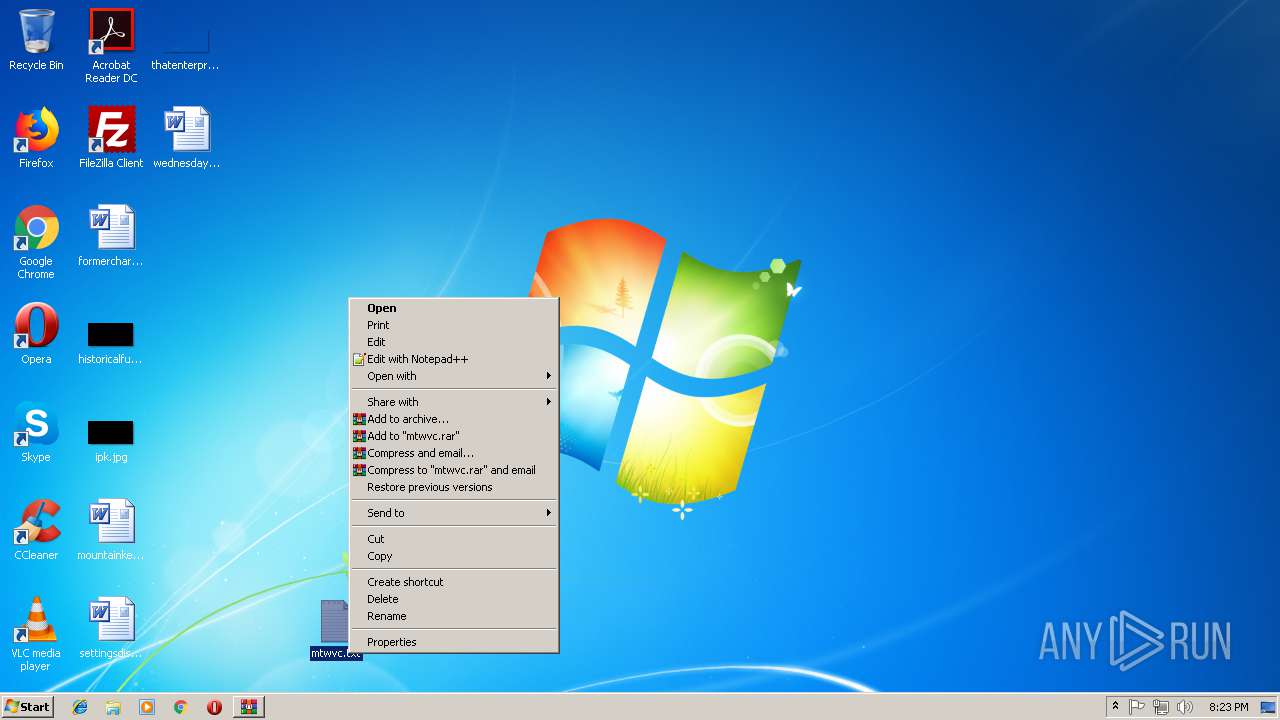
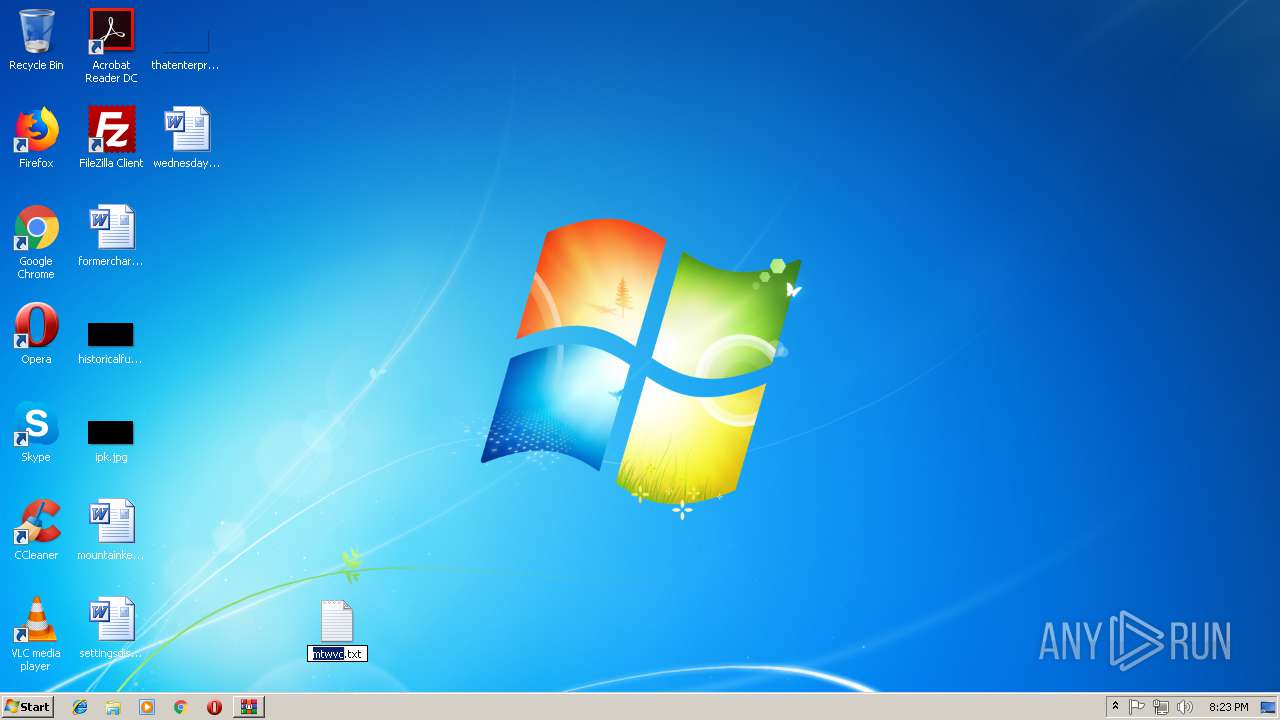
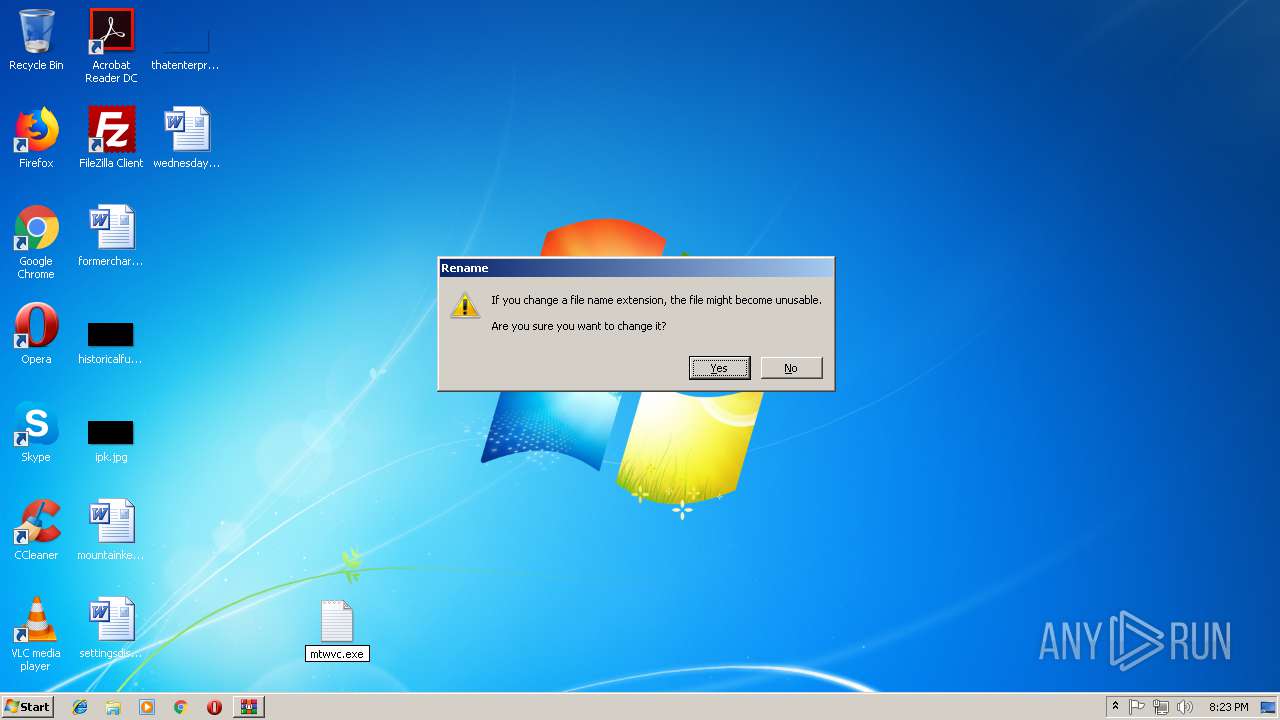
Executable content was dropped or overwritten
- mtwvc.exe (PID: 2724)
- mtwvc.exe (PID: 1820)
Starts CMD.EXE for commands execution
- mtwvc.exe (PID: 2724)
- mtwvc.exe (PID: 1720)
Checks for external IP
- mtwvc.exe (PID: 340)
Removes files from Windows directory
- mtwvc.exe (PID: 340)
Creates files in the program directory
- mtwvc.exe (PID: 340)
Connects to unusual port
- mtwvc.exe (PID: 340)
Creates files in the Windows directory
- mtwvc.exe (PID: 340)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:14 08:23:15 |
| ZipCRC: | 0x9bccd804 |
| ZipCompressedSize: | 321167 |
| ZipUncompressedSize: | 450750 |
| ZipFileName: | mtwvc.txt |
Total processes
68
Monitored processes
23
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | C:\Users\admin\AppData\Roaming\vsvsid\mtwvc.exe | C:\Users\admin\AppData\Roaming\vsvsid\mtwvc.exe | taskeng.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Developed using the Dev-C++ IDE Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1548 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1720 | "C:\Users\admin\AppData\Roaming\vsvsid\mtwvc.exe" | C:\Users\admin\AppData\Roaming\vsvsid\mtwvc.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Developed using the Dev-C++ IDE Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1796 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\Desktop\mtwvc.exe" | C:\Users\admin\Desktop\mtwvc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Developed using the Dev-C++ IDE Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2340 | /c sc stop WinDefend | C:\Windows\system32\cmd.exe | — | mtwvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2356 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | mtwvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\Desktop\mtwvc.exe" | C:\Users\admin\Desktop\mtwvc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Developed using the Dev-C++ IDE Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 776
Read events
1 635
Write events
141
Delete events
0
Modification events
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mtwvc.zip | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2724) mtwvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3084) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
19
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3556.49809\mtwvc.txt | — | |
MD5:— | SHA256:— | |||
| 3084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X64YWZG92V31C6B410O6.temp | — | |
MD5:— | SHA256:— | |||
| 1796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B7MVPGX2VNNT00KWYUK0.temp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Cab688A.tmp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Tar688B.tmp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Cab689C.tmp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Tar689D.tmp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Cab7D7E.tmp | — | |
MD5:— | SHA256:— | |||
| 340 | mtwvc.exe | C:\Windows\TEMP\Tar7D7F.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
340 | mtwvc.exe | GET | 200 | 37.120.182.208:80 | http://ip.anysrc.net/plain/clientip | DE | text | 11 b | shared |
340 | mtwvc.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 54.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
340 | mtwvc.exe | 37.120.182.208:80 | ip.anysrc.net | netcup GmbH | DE | suspicious |
340 | mtwvc.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
340 | mtwvc.exe | 24.119.69.70:449 | — | Cable One, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip.anysrc.net |
| shared |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
340 | mtwvc.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|