| File name: | SunloginClient_9.8.1.exe |
| Full analysis: | https://app.any.run/tasks/18deaa99-cb36-4dfb-98f3-84b66fc473ee |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2018, 07:46:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2A25F8D0887ACFEFFC4FF6E1FFBF7A5B |
| SHA1: | C0D25E937D414EC064C8602798A00E88392245AD |
| SHA256: | F03FDFA43B4F681F93339C8CDE642FD772DE3977C7DB4DA0D5AA4B58B4A226CC |
| SSDEEP: | 98304:Oe/3A5rOdWTY6XaUfQAm1r/6z6QMDeg8PqQgCJYtdlCV5l0RTUN:OOAVlTvXLfQrRFeg8mCaZCVj0KN |
MALICIOUS
Changes the autorun value in the registry
- SunloginClient_9.8.1.exe (PID: 3144)
Application was dropped or rewritten from another process
- devcon.exe (PID: 3756)
SUSPICIOUS
Creates files in the Windows directory
- SunloginClient_9.8.1.exe (PID: 3132)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3792)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 3360)
- cmd.exe (PID: 3788)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 3292)
Creates files in the program directory
- SunloginClient_9.8.1.exe (PID: 3144)
Starts CMD.EXE for commands execution
- SunloginClient_9.8.1.exe (PID: 3144)
- cmd.exe (PID: 4040)
Application launched itself
- SunloginClient_9.8.1.exe (PID: 3132)
- cmd.exe (PID: 4040)
Executable content was dropped or overwritten
- SunloginClient_9.8.1.exe (PID: 3144)
Starts itself from another location
- SunloginClient_9.8.1.exe (PID: 3144)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:22 08:32:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4444160 |
| InitializedDataSize: | 135168 |
| UninitializedDataSize: | 11395072 |
| EntryPoint: | 0xf1b4c0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.8.1.15686 |
| ProductVersionNumber: | 9.8.1.15686 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Shanghai Best Oray Information Technology Co., Ltd. |
| FileDescription: | SunloginClient |
| FileVersion: | 9.8.1.15686 |
| InternalName: | SunloginClient |
| LegalCopyright: | Shanghai Best Oray Information Technology Co., Ltd. |
| OriginalFileName: | SunloginClient.exe |
| ProductName: | SunloginClient |
| ProductVersion: | 9.8.1.15686 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Oct-2018 06:32:43 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000178 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Oct-2018 06:32:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00ADE000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00ADF000 | 0x0043D000 | 0x0043C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92701 |
.rsrc | 0x00F1C000 | 0x00021000 | 0x00020200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70431 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
HID.DLL |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
NETAPI32.dll |
Total processes
58
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=tcp enable=yes profile=private | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | netsh advfirewall firewall delete rule name="SunloginClient" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | TASKKILL /PID 0 /PID 0 /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" --mod=install --cmd=driver_mirror | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe | SunloginClient_9.8.1.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: HIGH Description: SunloginClient Exit code: 0 Version: 9.8.1.15686 Modules
| |||||||||||||||
| 2268 | netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=public | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=tcp enable=yes profile=private | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3048 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\SunloginClient_9.8.1.exe" | C:\Users\admin\AppData\Local\Temp\SunloginClient_9.8.1.exe | explorer.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: MEDIUM Description: SunloginClient Exit code: 4294967295 Version: 9.8.1.15686 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\SunloginClient_9.8.1.exe" --mod=install | C:\Users\admin\AppData\Local\Temp\SunloginClient_9.8.1.exe | SunloginClient_9.8.1.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: HIGH Description: SunloginClient Exit code: 0 Version: 9.8.1.15686 Modules
| |||||||||||||||
| 3148 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=tcp enable=yes profile=domain | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
969
Read events
648
Write events
321
Delete events
0
Modification events
| (PID) Process: | (3132) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Oray\SunLogin\SunloginClient |
| Operation: | write | Name: | 9.8.1.15686_IsRunSeted |
Value: 1 | |||
| (PID) Process: | (3132) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3132) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3144) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3144) SunloginClient_9.8.1.exe | Key: | HKEY_CURRENT_USER\Software\Oray\SunLogin\SunloginClient |
| Operation: | write | Name: | 9.8.1.15686_IsInstalling |
Value: 1 | |||
| (PID) Process: | (3144) SunloginClient_9.8.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SunloginClient |
Value: "C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" --cmd=autorun | |||
| (PID) Process: | (1904) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1904) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (1904) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
Executable files
18
Suspicious files
5
Text files
9
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient_Test.zip | compressed | |
MD5:— | SHA256:— | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\scad.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\DpmsMonitor\devcon.exe | executable | |
MD5:DEA7C7A2F6A968C4A574DF6BD22B8E97 | SHA256:7FD75AECF247D44D483C6480BEAE370E9E6D5569BC1B504047279C053EAB62C9 | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\DpmsMonitor64\devcon.exe | executable | |
MD5:55F91028015F6B1A9D7B78AE35B002C2 | SHA256:9EB065C70CED8980C33E06CF64BA6F78E5CACEA1263F97EEFAF6D323D7964F41 | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\DpmsMonitor\oraydpms.inf | binary | |
MD5:E83920982575A11EFC8A5520887535EA | SHA256:EC07226BD82CD2F89BAE5B36BBCE088C29C4A89F25E6E82AF8877EE1823AE9A9 | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\Mirror64\OrayMir.sys | executable | |
MD5:8A61A25D7748F902EC39976F3A4CCF55 | SHA256:65EF006E05E84940D6EF9AF40F08916850C9DFB9085E46EBCA71CE51599A74DD | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\Mirror64\OrayMir.dll | executable | |
MD5:D275259C36EB1EE4F8EAAA9D2306D5C2 | SHA256:96DC4482F0D4F04D760EFCCB42941161FE8F16F4F347716BAF361F7320C4BE3E | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\DpmsMonitor\oraydpmsx86.cat | cat | |
MD5:A6F9DFFA6DC0257349DE76355A22D87E | SHA256:8A4504DBCBEB53421314A6F4E15C1994CEFE0C8FC881EB5A2C9D70A3596E5817 | |||
| 3144 | SunloginClient_9.8.1.exe | C:\Program Files\Oray\SunLogin\SunloginClient\driver\Print\oray.gpd | text | |
MD5:099014165BE15C5833535A3129BD2308 | SHA256:8E3120D35FA97E78D6CD029216D647E6DA1824E05814800877546225EDDB32F2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | SunloginClient_9.8.1.exe | 172.217.168.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3144 | SunloginClient_9.8.1.exe | 222.73.7.11:443 | client.oray.net | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
client.oray.net |
| unknown |
Threats
Process | Message |
|---|---|
SunloginClient_9.8.1.exe | 2018-12-10 07:47:17.480 = Debug = [monitor]PRIMARY, left=0, top=0
|
SunloginClient_9.8.1.exe | 2018-12-10 07:47:17.480 - Info - config path: C:/Users/admin/AppData/Roaming/Oray/SunloginClient
|
SunloginClient_9.8.1.exe | 2018-12-10 07:47:17.527 - Info - config path: C:/Users/admin/AppData/Roaming/Oray/SunloginClient
|
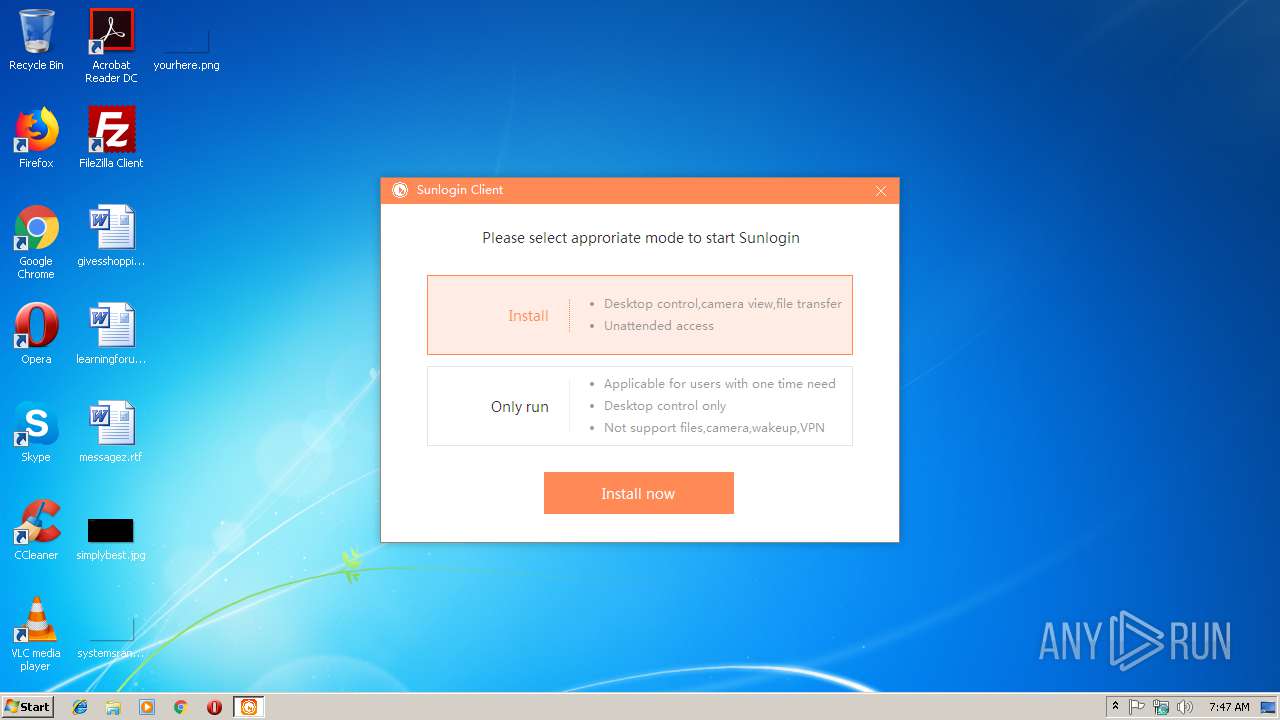
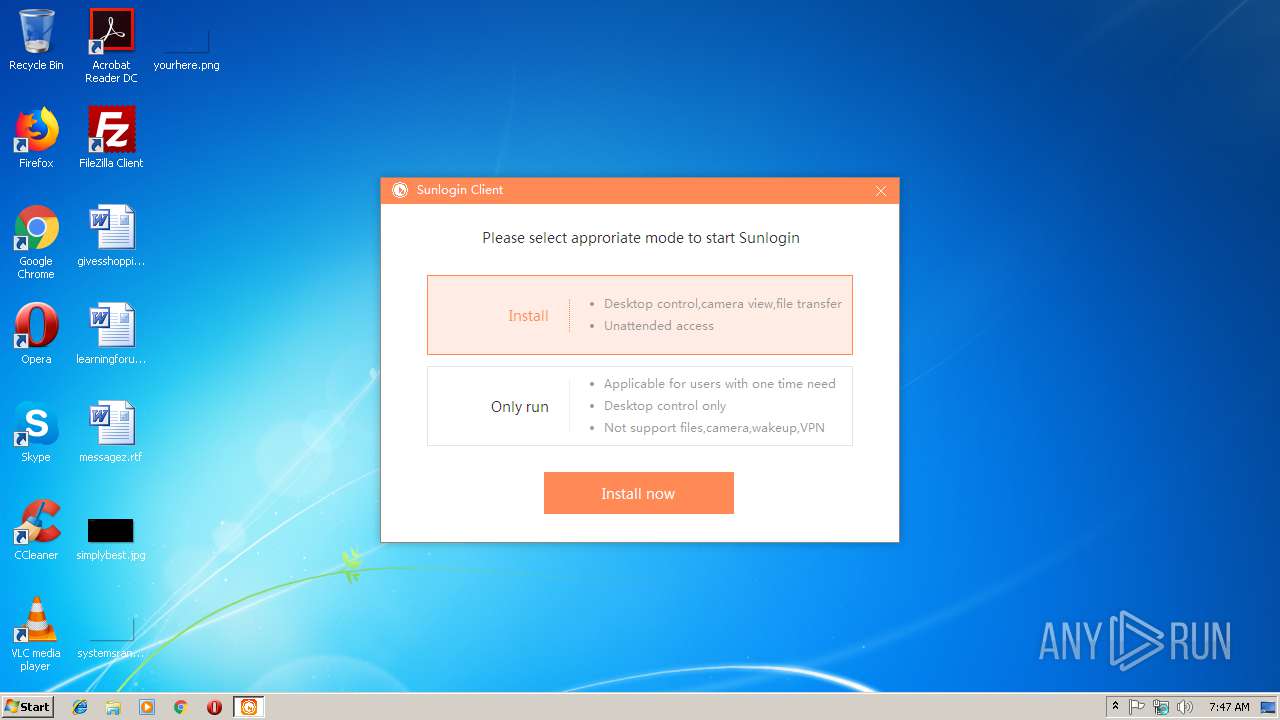
SunloginClient_9.8.1.exe | [dlg_bootselector.xml] - start boot selector
|
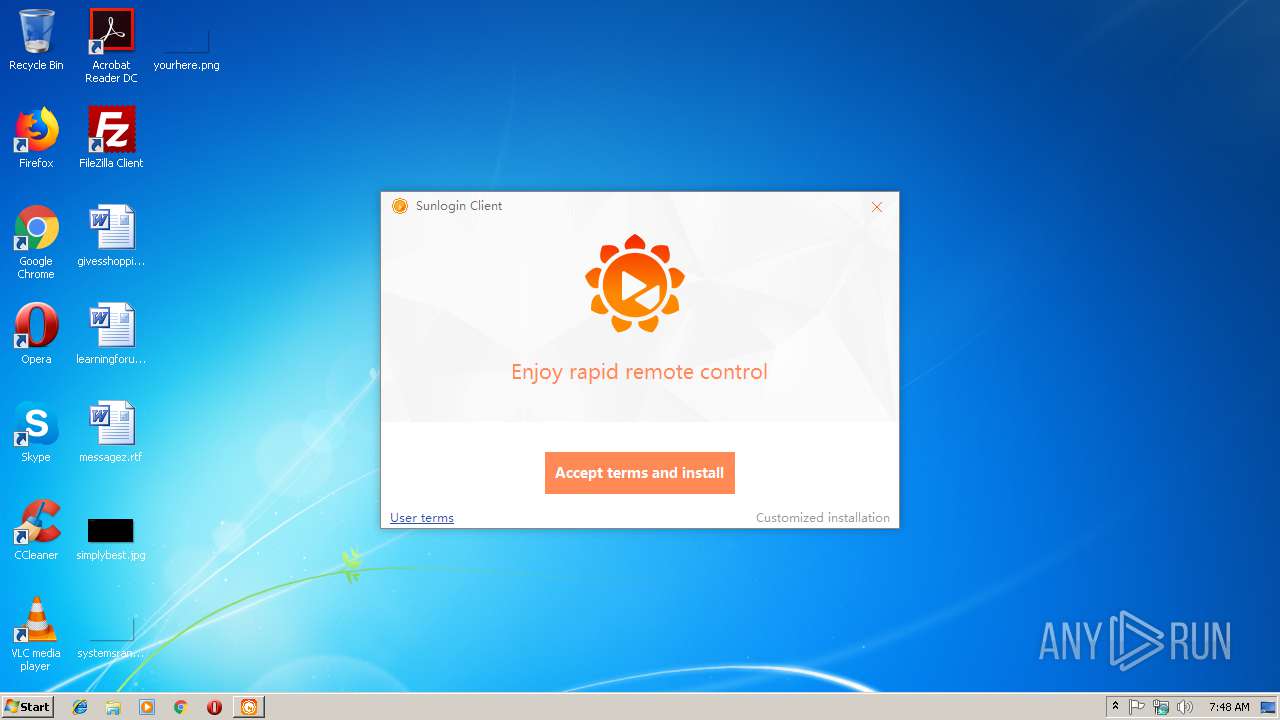
SunloginClient_9.8.1.exe | 2018-12-10 07:48:05.152 - Info - [Install] Create new you write info
|
SunloginClient_9.8.1.exe | 2018-12-10 07:48:06.527 - Info - [STOP SERVICE] send bef |
SunloginClient_9.8.1.exe | 2018-12-10 07:48:06.527 - Info - [STOP SERVICE] send before
|
SunloginClient_9.8.1.exe | 2018-12-10 07:48:06.527 - Info - [STOP SERVICE] send after
|
SunloginClient_9.8.1.exe | 2018-12-10 07:48:06.527 - Info - program is exit
|
SunloginClient_9.8.1.exe | 2018-12-10 07:48:06.699 = Debug = [monitor]PRIMARY, left=0, top=0
|