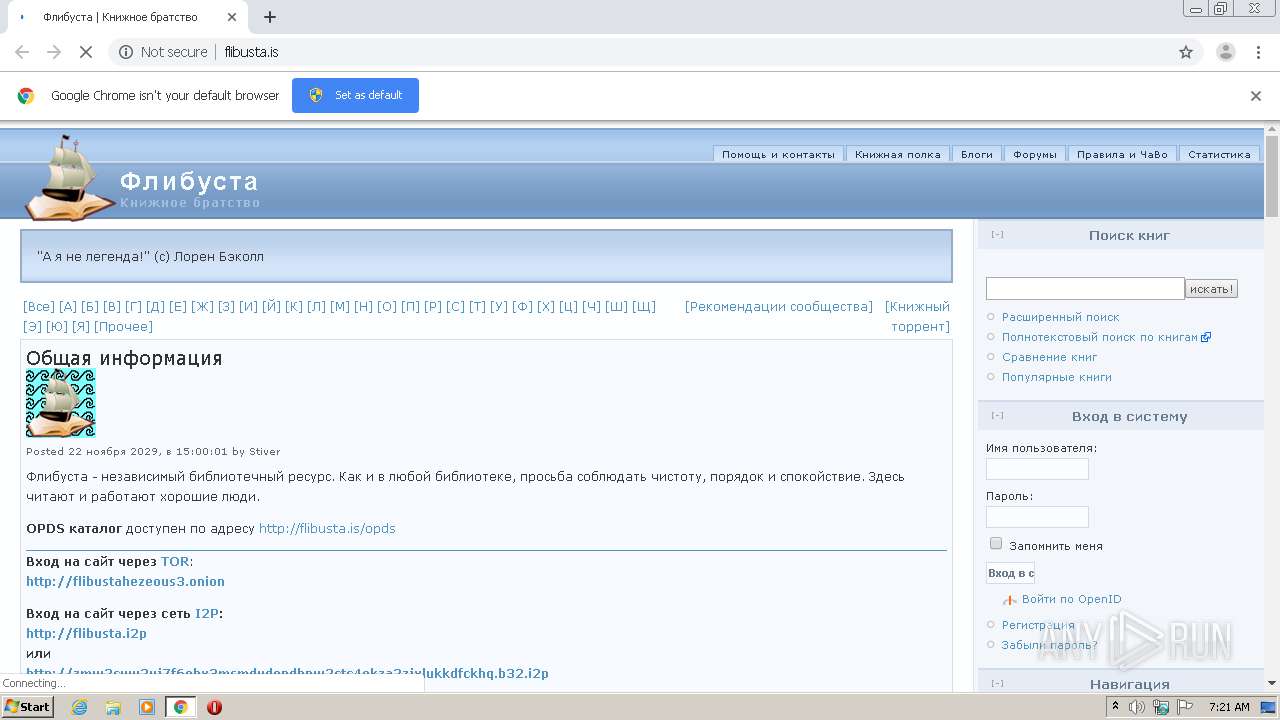
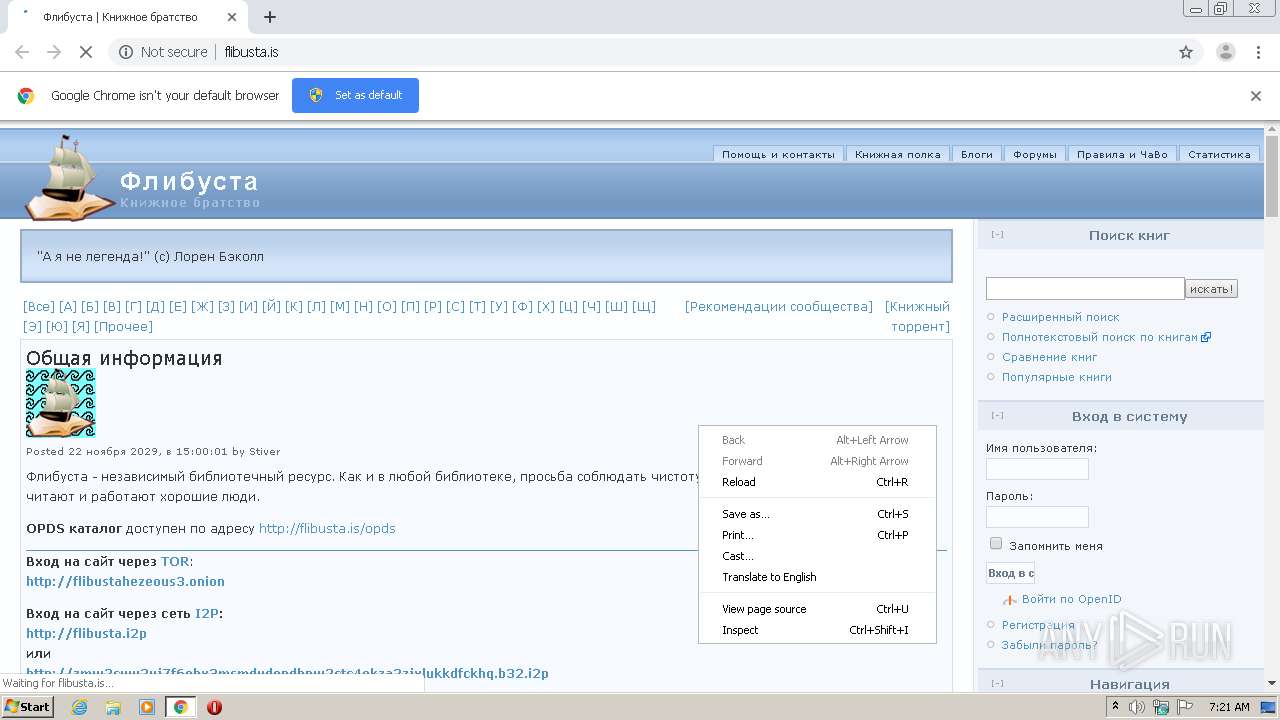
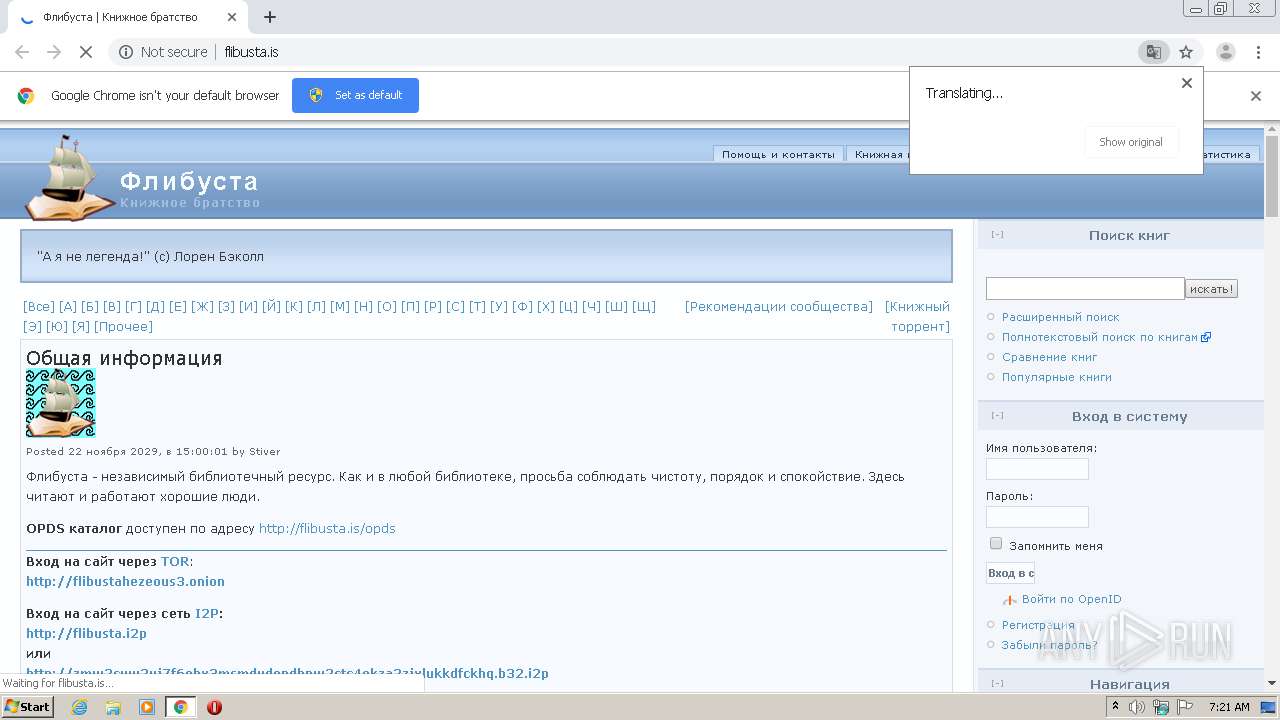
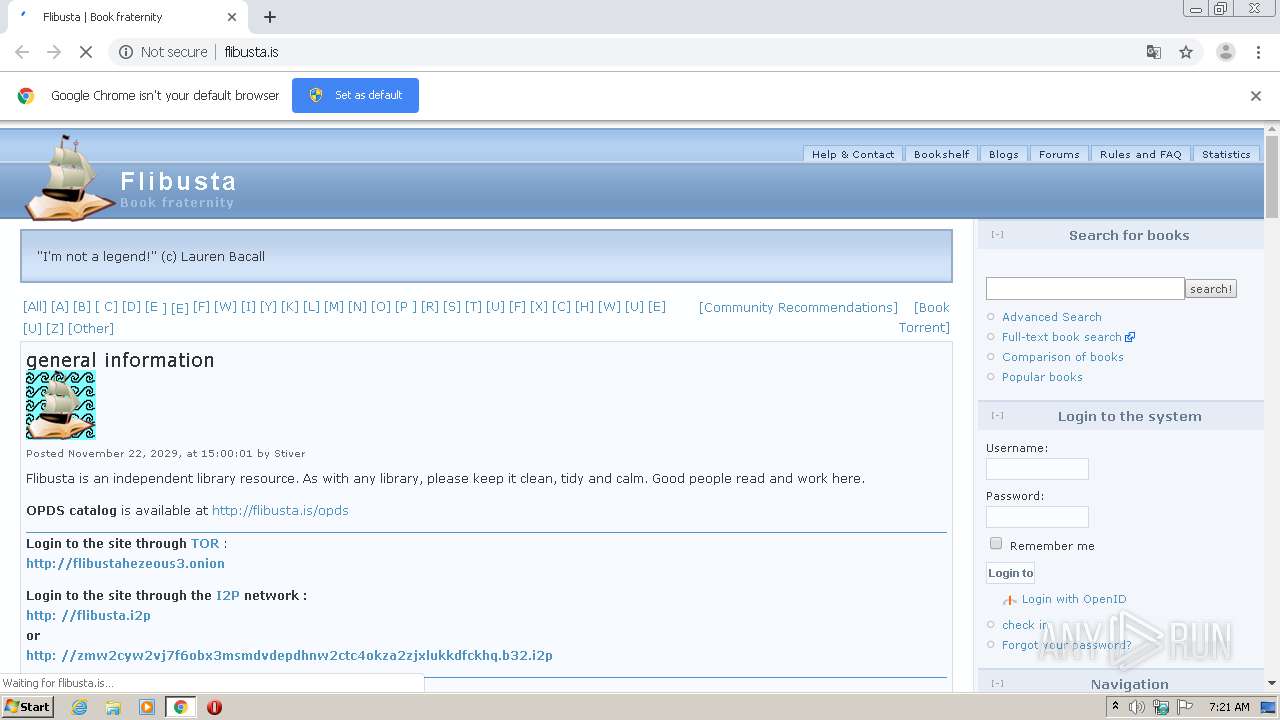
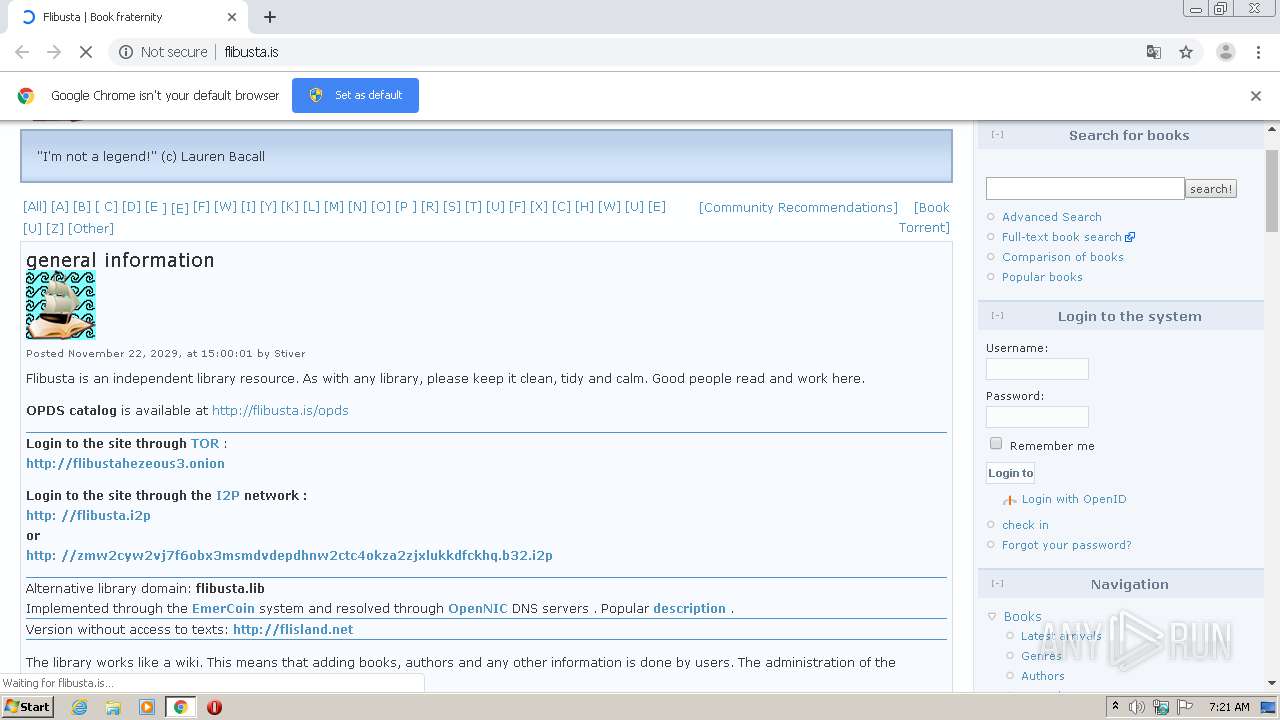
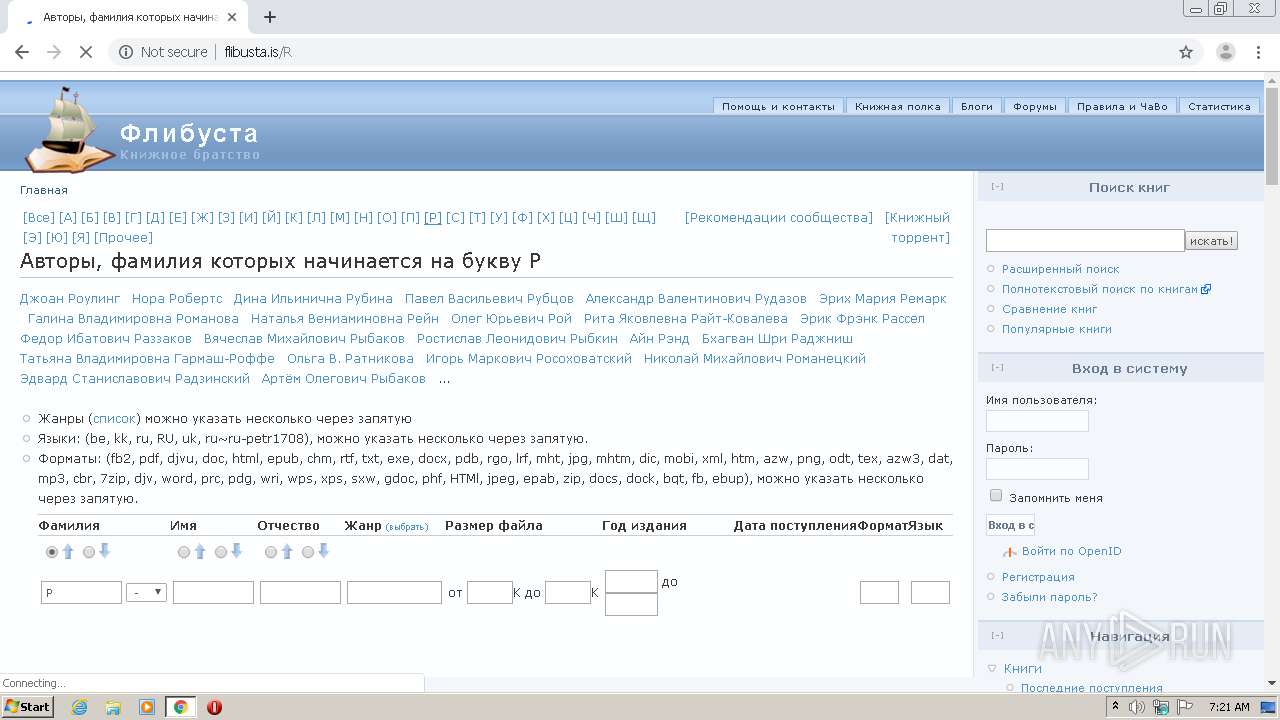
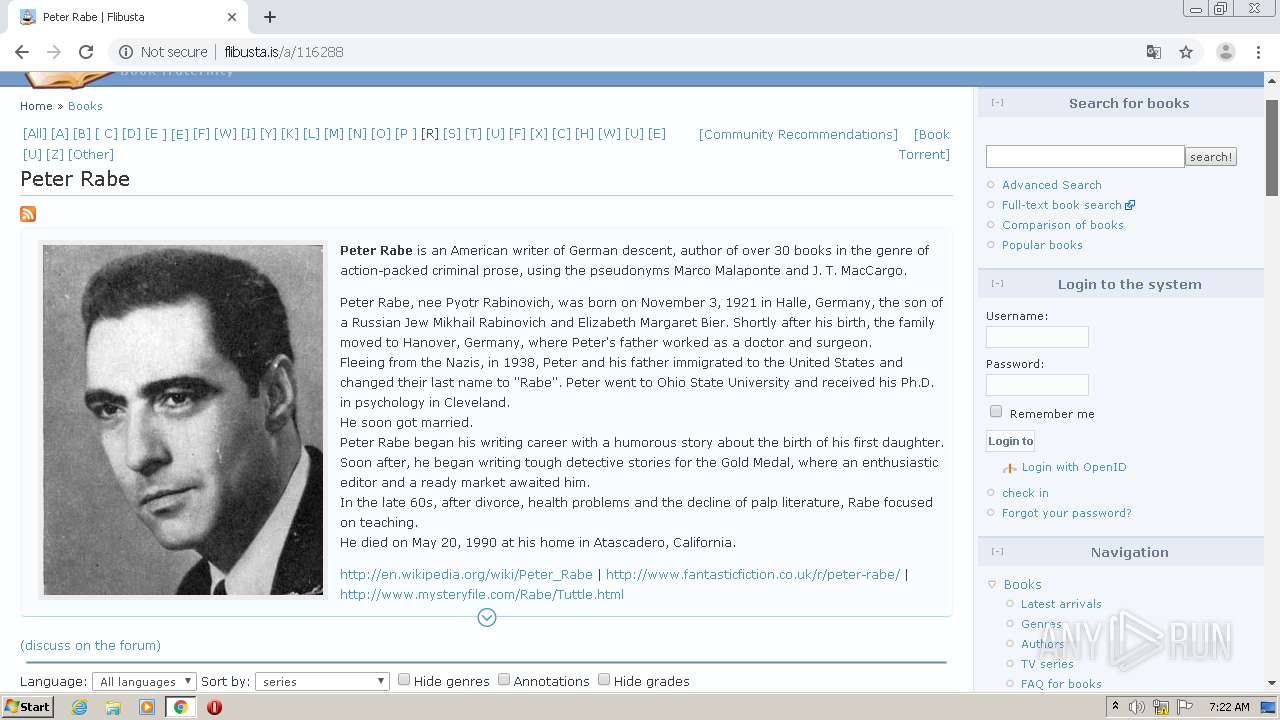
| URL: | http://flibusta.is/ |
| Full analysis: | https://app.any.run/tasks/f8ba04ed-bf15-4ea5-b429-fb60a6139438 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2021, 06:20:44 |
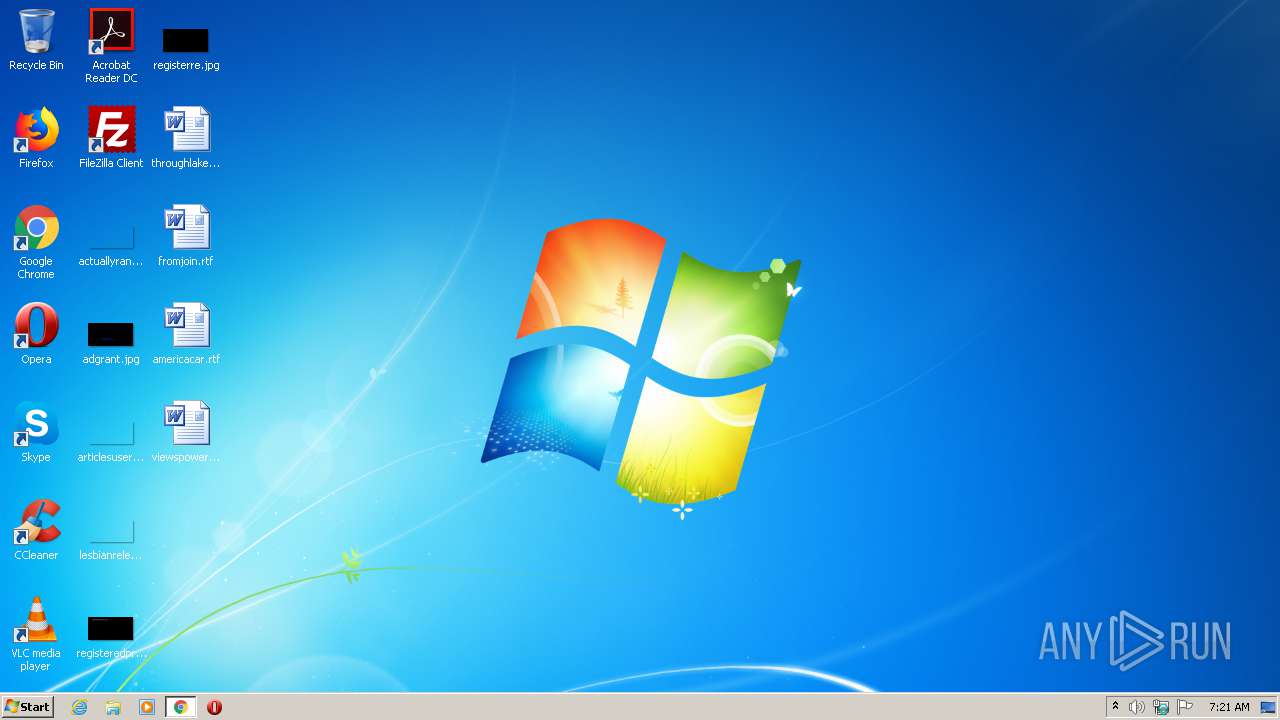
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 84916213A7DE5863175C4F356B3E70FE |
| SHA1: | 88B4220A620E7D63A3D6E8C219125CC6711A48D5 |
| SHA256: | F0372C85B465474DB4BB93A7B20662B5F0AB254214D4B71C581CEB900EE5EC51 |
| SSDEEP: | 3:N1KYEW4Nn:CYlu |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 4036)
- chrome.exe (PID: 1816)
Application launched itself
- chrome.exe (PID: 1816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1804 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10095606919698713708 --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://flibusta.is/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17088454711017691322 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12451092343588089177 --mojo-platform-channel-handle=3332 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12731736776780399510 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c1ea9d0,0x6c1ea9e0,0x6c1ea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9175233955203486330 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1195204084968349691 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 4036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,3733084790482977771,6811322895244145900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2108075984602719403 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
589
Read events
526
Write events
60
Delete events
3
Modification events
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1816-13265446862007625 |
Value: 259 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
14
Text files
73
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-609E16CE-718.pma | — | |
MD5:— | SHA256:— | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3c379865-838a-4387-b946-fc61cbba3398.tmp | — | |
MD5:— | SHA256:— | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFe7b85.TMP | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:F1220A80653B6B89B42DFD1B2E8155C3 | SHA256:36BBBC13CC1901CF269B4CE36E2EE08946806DFA58474AE88287CA8E9DA9725D | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFe7be2.TMP | text | |
MD5:F1220A80653B6B89B42DFD1B2E8155C3 | SHA256:36BBBC13CC1901CF269B4CE36E2EE08946806DFA58474AE88287CA8E9DA9725D | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe7d1b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
43
DNS requests
33
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
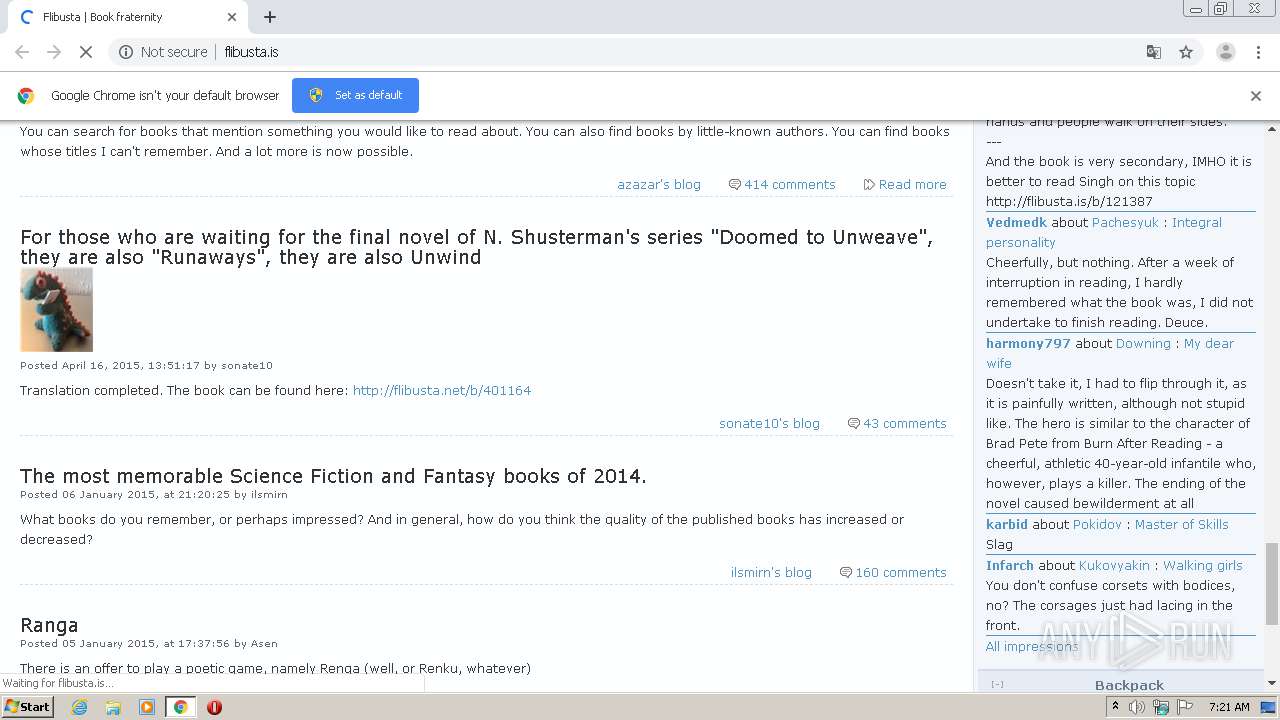
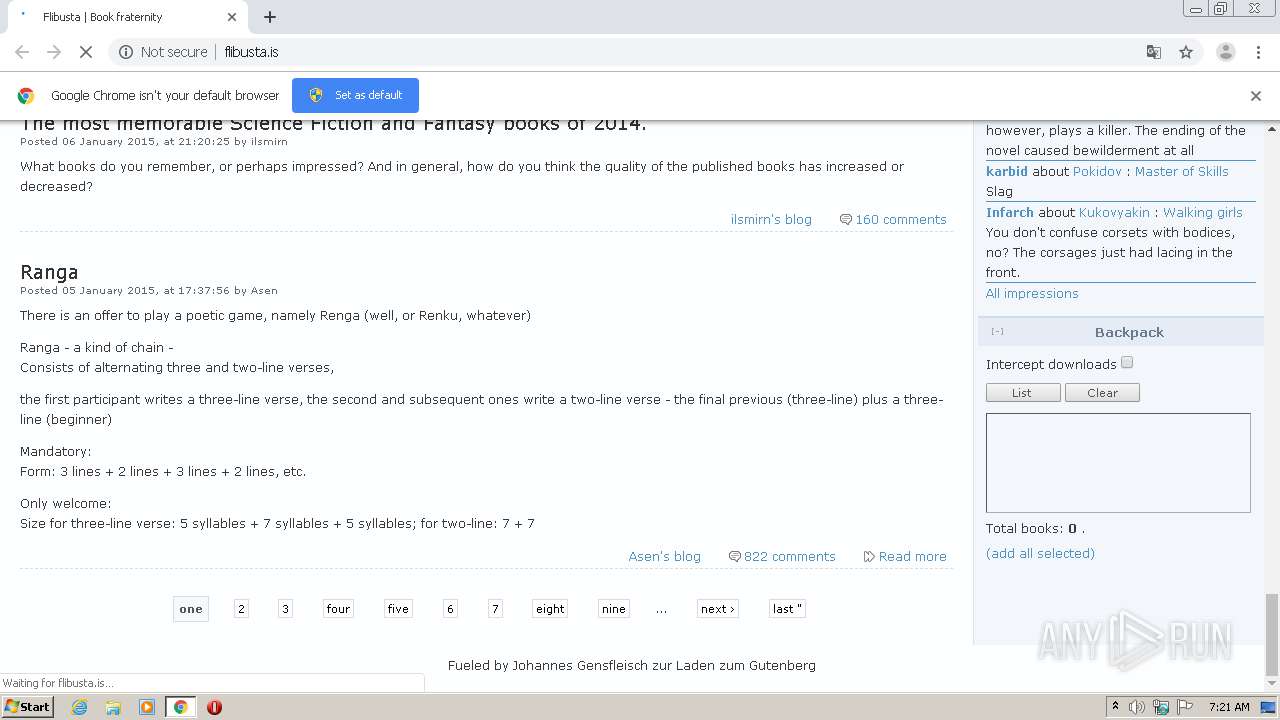
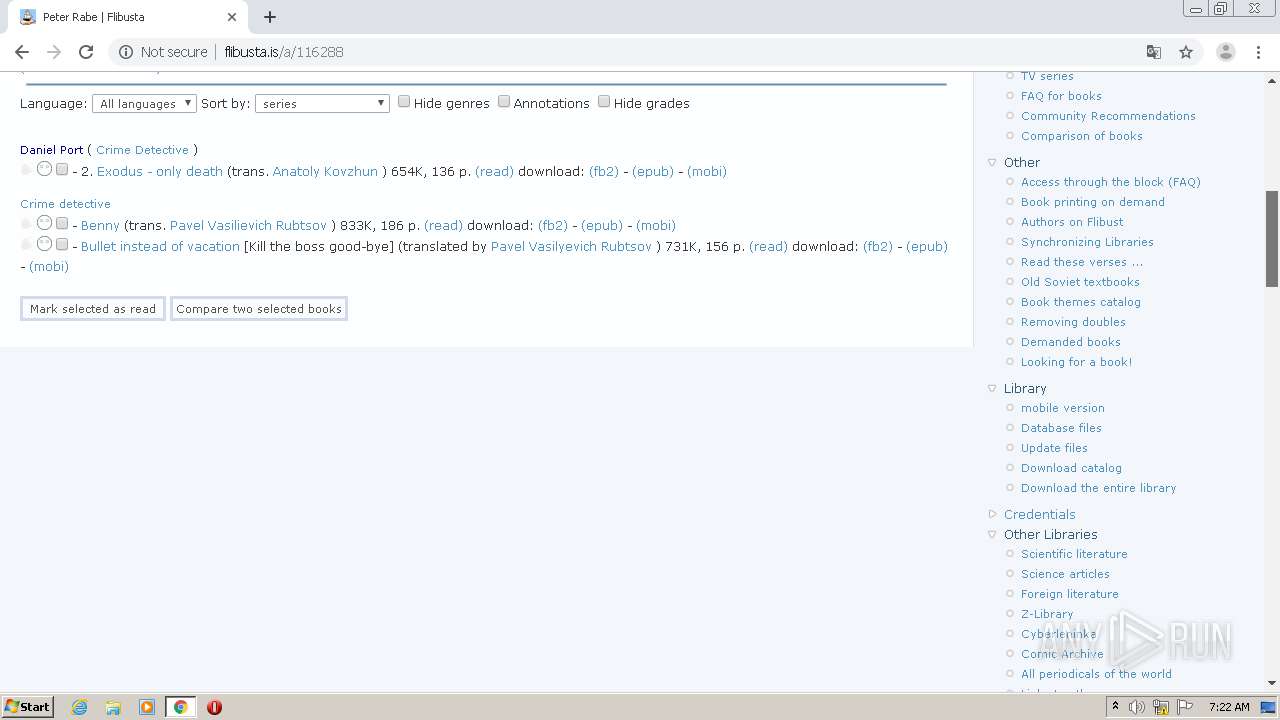
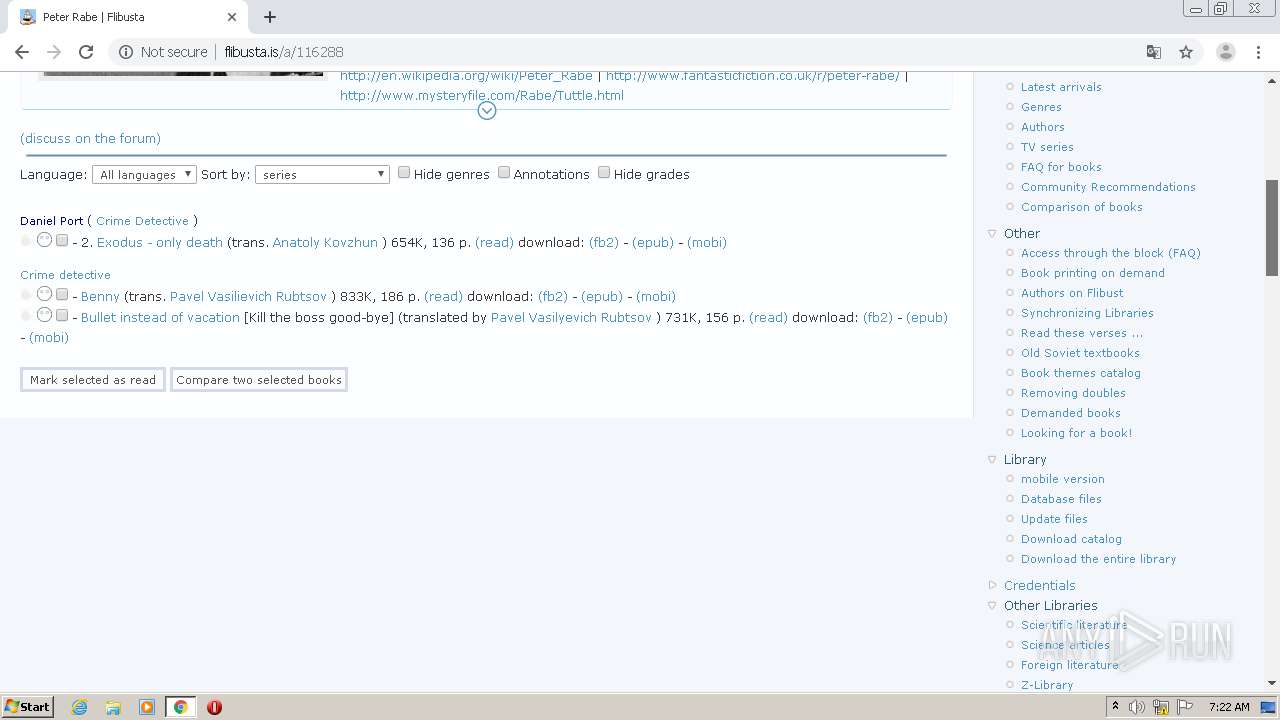
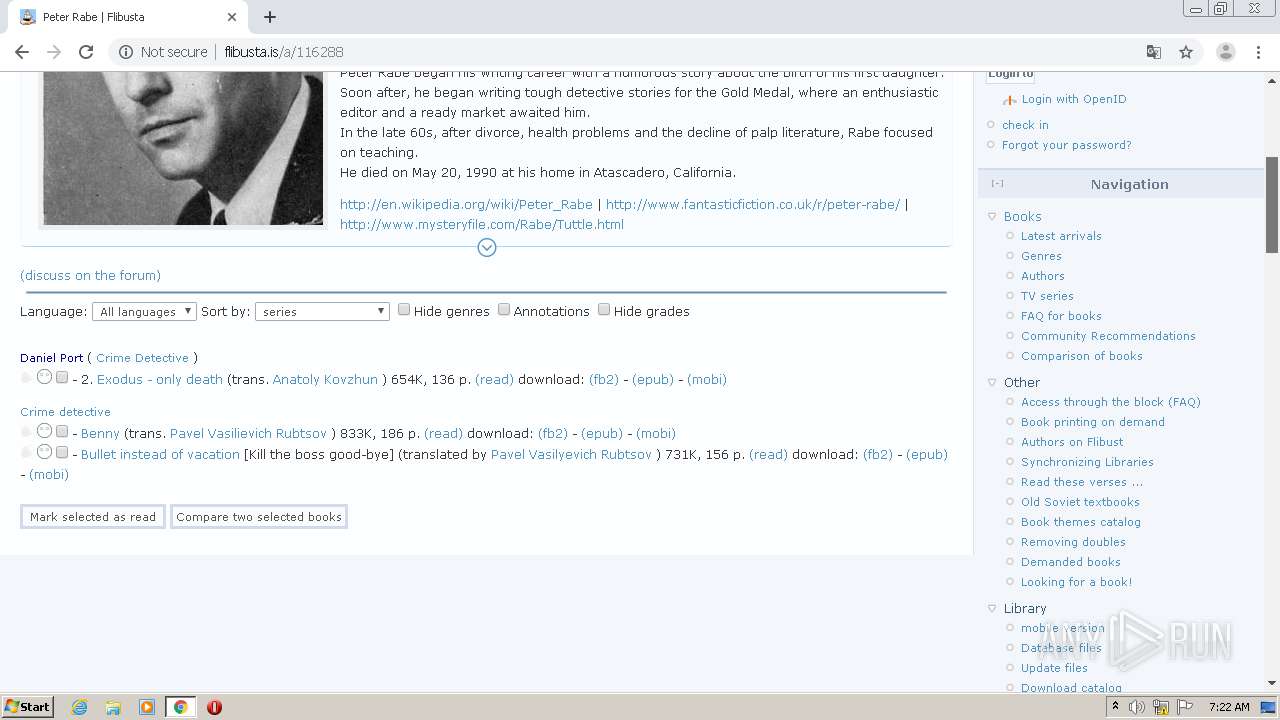
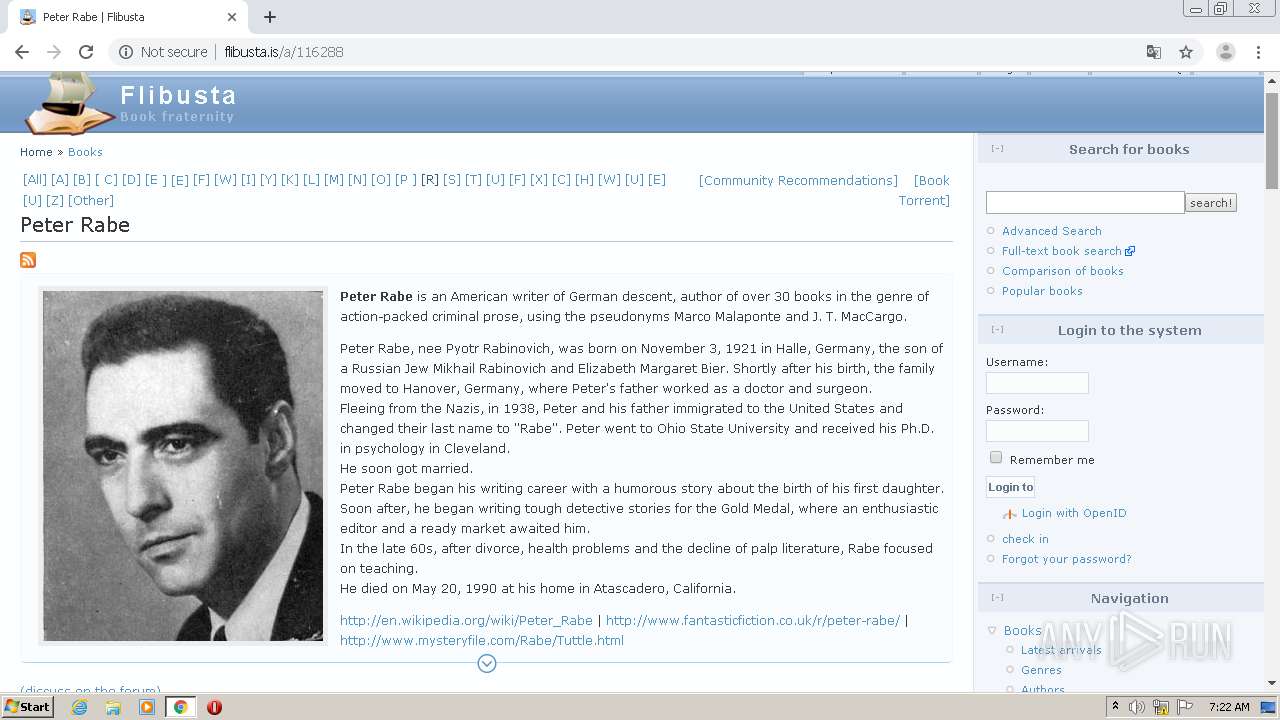
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/css/css_541b6da58ae4dff17f932324504056f9.css | CH | text | 7.33 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-4.png | CH | image | 12.4 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/ | CH | html | 13.7 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-124185.gif | CH | image | 4.39 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-37400.jpg | CH | image | 3.43 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/bluebreeze_logo.png | CH | image | 12.8 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/js/js_65bd89c41ff1e065c43cc27e23c28553.js | CH | text | 48.0 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-7176.jpg | CH | image | 2.48 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-8052.jpg | CH | image | 18.4 Kb | whitelisted |
4036 | chrome.exe | GET | 200 | 81.17.19.227:80 | http://flibusta.is/sites/default/files/pictures/picture-2215.jpg | CH | image | 3.83 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4036 | chrome.exe | 142.250.185.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4036 | chrome.exe | 142.250.185.234:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
4036 | chrome.exe | 81.17.19.227:80 | flibusta.is | Private Layer INC | CH | unknown |
4036 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 81.17.19.227:80 | flibusta.is | Private Layer INC | CH | unknown |
4036 | chrome.exe | 142.250.185.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
4036 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4036 | chrome.exe | 142.250.185.174:80 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
flibusta.is |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
booktracker.org |
| whitelisted |
cyberleninka.ru |
| whitelisted |
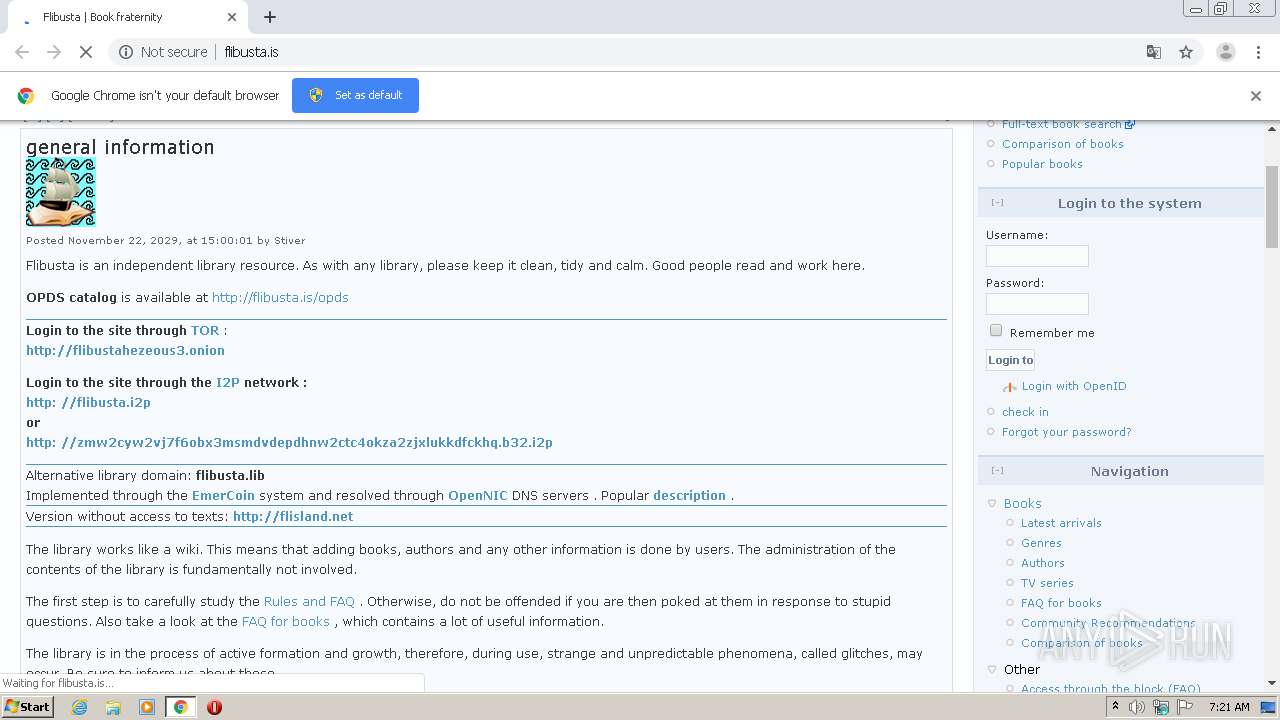
emercoin.com |
| malicious |
fbsearch.ru |
| malicious |
flibusta.i2p |
| unknown |
flibustahezeous3.onion |
| unknown |
flisland.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for Invisible Internet Project Domain (I2P) |
1040 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1040 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
1040 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for Invisible Internet Project Domain (I2P) |