| File name: | startwtk.exe |
| Full analysis: | https://app.any.run/tasks/b27d1af0-0c2c-45c7-a37a-992bf6625af8 |
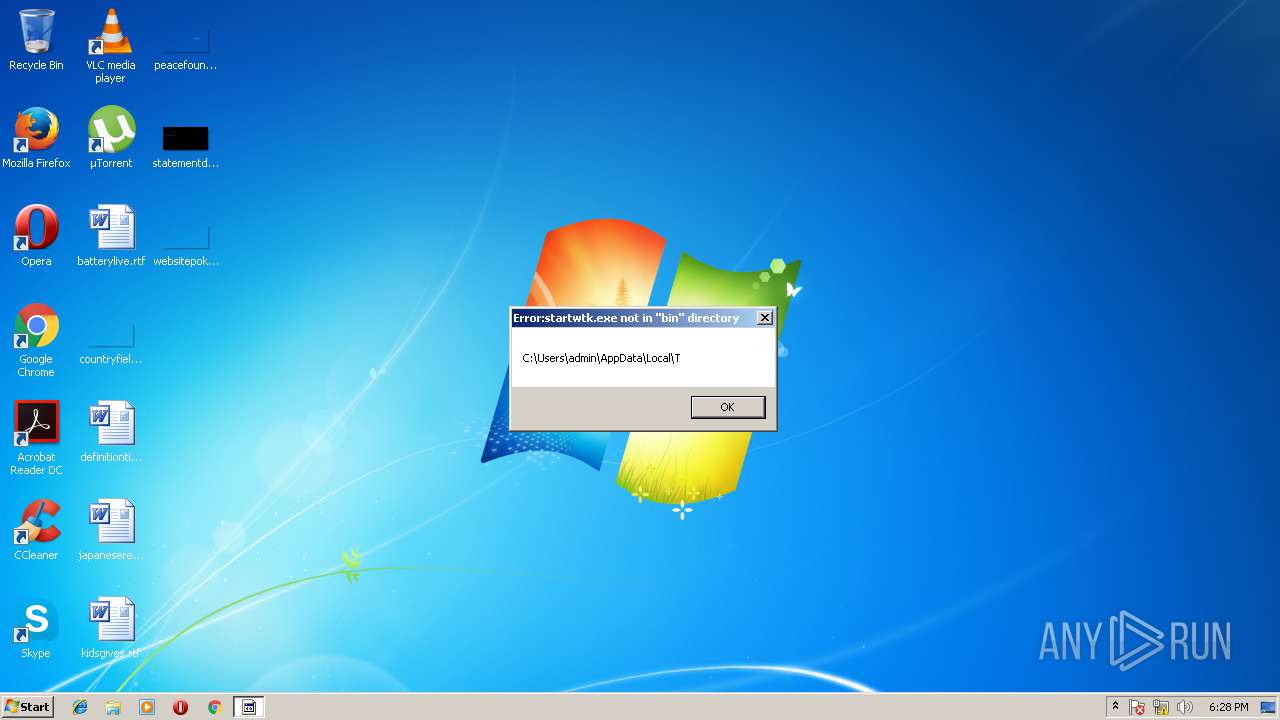
| Verdict: | No threats detected |
| Analysis date: | March 08, 2018, 18:28:06 |
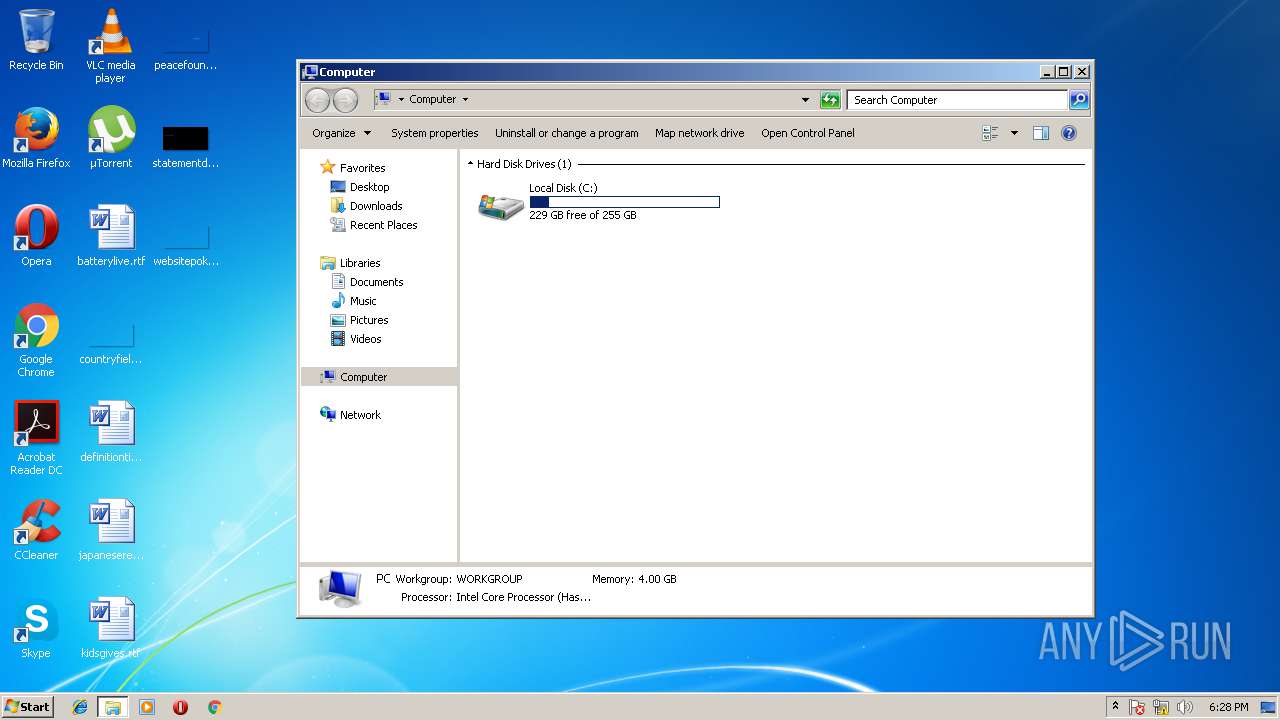
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB397E7EA662CBF8D51043485F0BA590 |
| SHA1: | 0641018B59E0D9581D2642B467C7949134DC3209 |
| SHA256: | F02EFA2715CB1015D3E7AD07D98DD319B45AA405B942D2DFDB1FDA1830F0EF3A |
| SSDEEP: | 768:4eIpRssBG7MJthhwaA8Co/UURIpycYSn+APU6VgZo5c/07qMEnGsGi3aOCRCx:uO4JtD9A89/UUiHn+Ac6VCeviGsGx |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Borland C++ (43.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (21.8) |
| .exe | | | Win32 Executable (generic) (14.9) |
| .exe | | | Win16/32 Executable Delphi generic (6.8) |
| .exe | | | Generic Win/DOS Executable (6.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:13 00:23:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 43520 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Nov-2022 23:23:32 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 12-Nov-2022 23:23:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000B000 | 0x0000AA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52784 |
DATA | 0x0000C000 | 0x00004000 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.92915 |
.tls | 0x00010000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00011000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.11837 |
.idata | 0x00012000 | 0x00001000 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93116 |
.edata | 0x00013000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.41434 |
.reloc | 0x00014000 | 0x00001000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.57034 |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
___CPPdebugHook | 1 | 0x0000C06F |
__GetExceptDLLinfo | 2 | 0x00001046 |
__DebuggerHookData | 3 | 0x0000C3B8 |
@__lockDebuggerData$qv | 4 | 0x00002160 |
@__unlockDebuggerData$qv | 5 | 0x00002188 |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 984 | C:\Windows\system32\DllHost.exe /Processid:{7007ACD1-3202-11D1-AAD2-00805FC1270E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\startwtk.exe" | C:\Users\admin\AppData\Local\Temp\startwtk.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
145
Read events
122
Write events
23
Delete events
0
Modification events
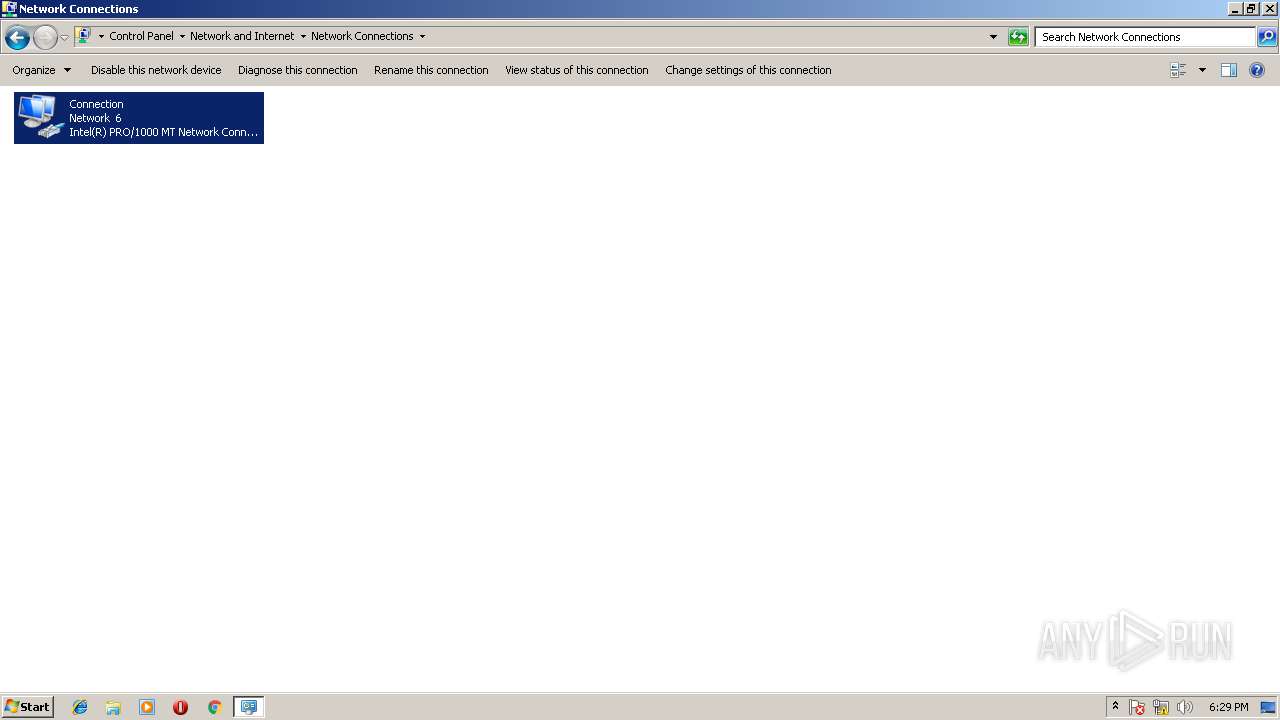
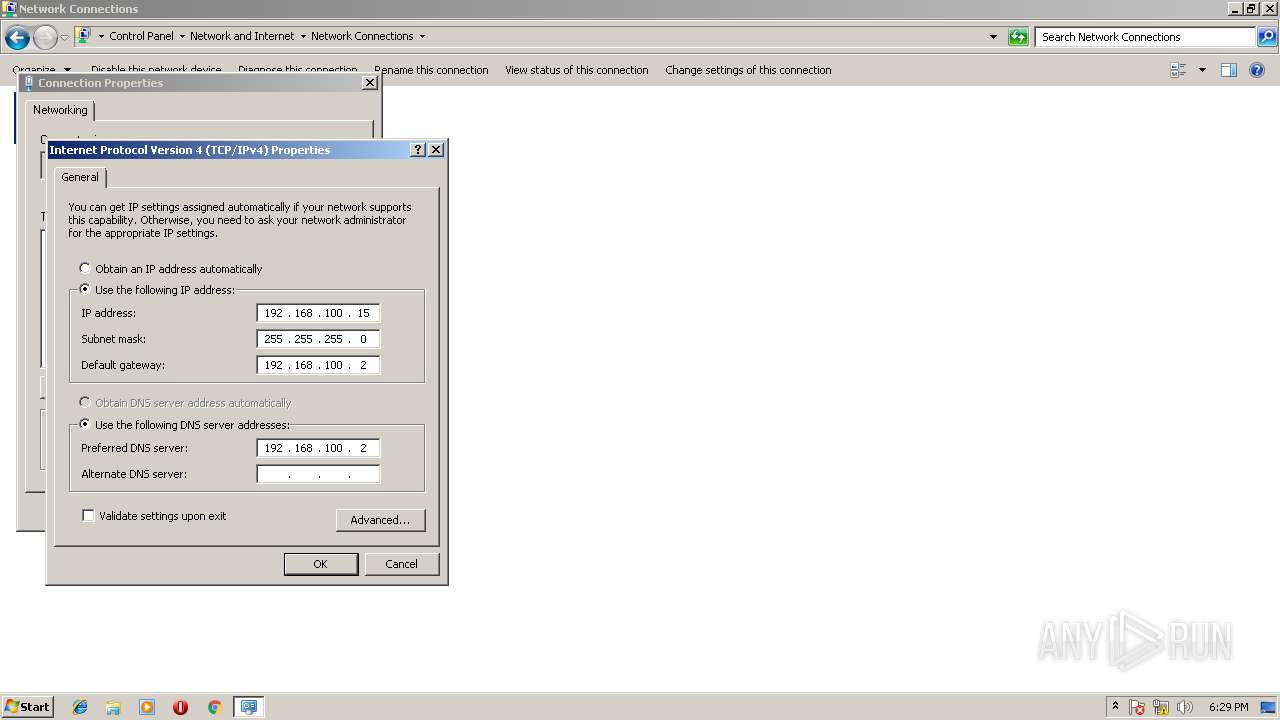
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NetCfgLockHolder |
| Operation: | write | Name: | |
Value: Local Network Connection Properties | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
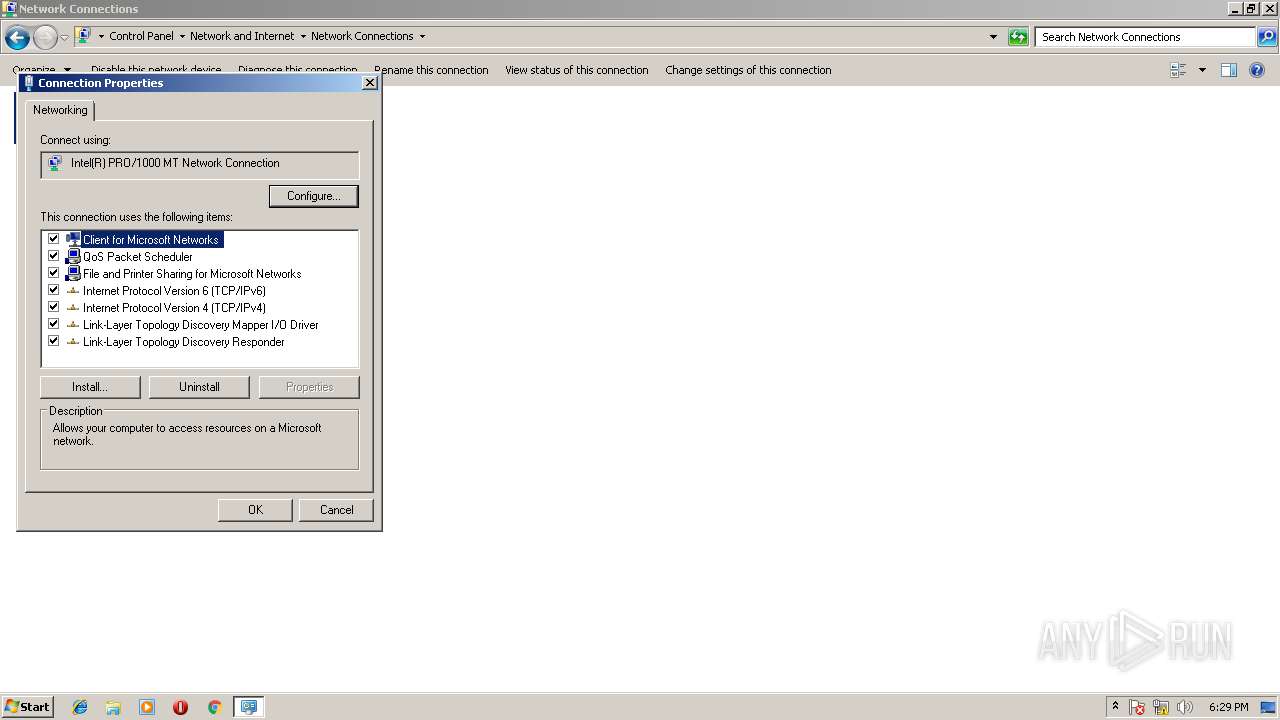
| Operation: | write | Name: | @netcfgx.dll,-50002 |
Value: Allows your computer to access resources on a Microsoft network. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\drivers\pacer.sys,-100 |
Value: Quality of Service Packet Scheduler. This component provides network traffic control, including rate-of-flow and prioritization services. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @netcfgx.dll,-50003 |
Value: Allows other computers to access resources on your computer using a Microsoft network. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @tcpipcfg.dll,-50002 |
Value: TCP/IP version 6. The latest version of the internet protocol that provides communication across diverse interconnected networks. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tcpipcfg.dll,-50001 |
Value: Transmission Control Protocol/Internet Protocol. The default wide area network protocol that provides communication across diverse interconnected networks. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\lltdres.dll,-4 |
Value: Used to discover and locate other PCs, devices, and network infrastructure components on the network. Also used to determine network bandwidth. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\lltdres.dll,-3 |
Value: Allows this PC to be discovered and located on the network. | |||
| (PID) Process: | (984) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\rascfg.dll,-32010 |
Value: Provides the abilitiy to connect a host to a Remote Access Concentrator that supports RFC2516. | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
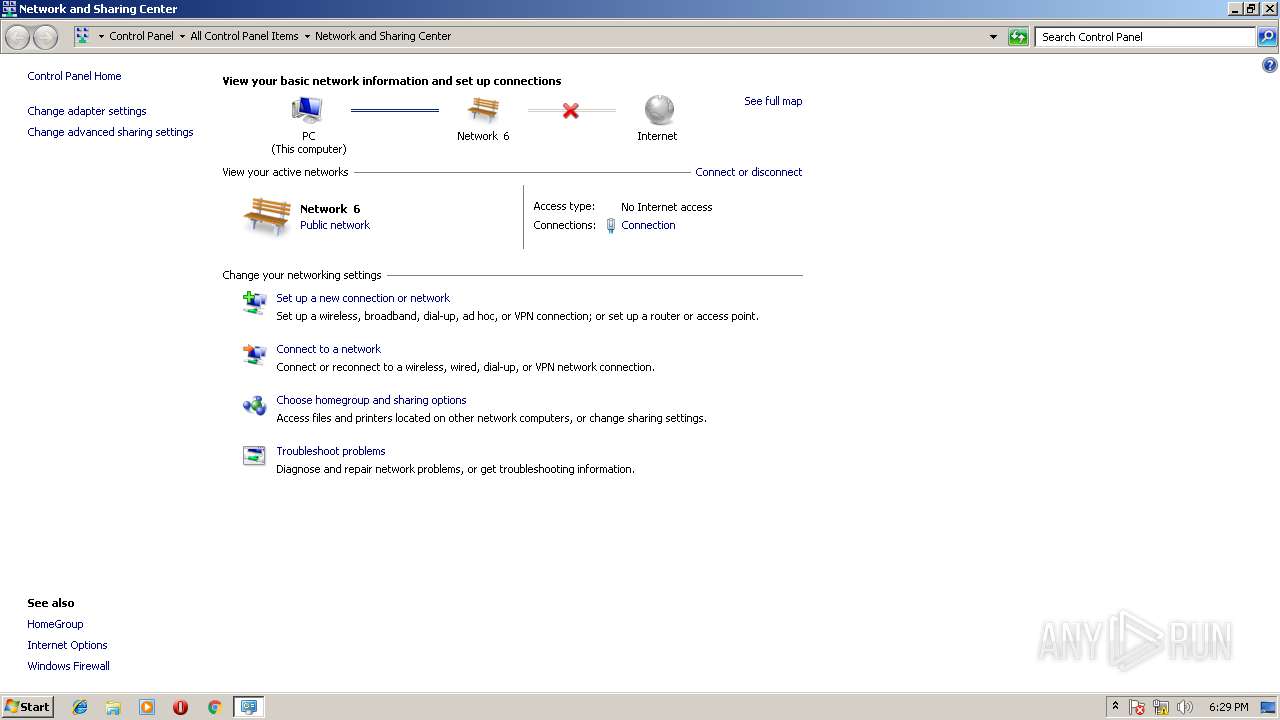
HTTP(S) requests
0
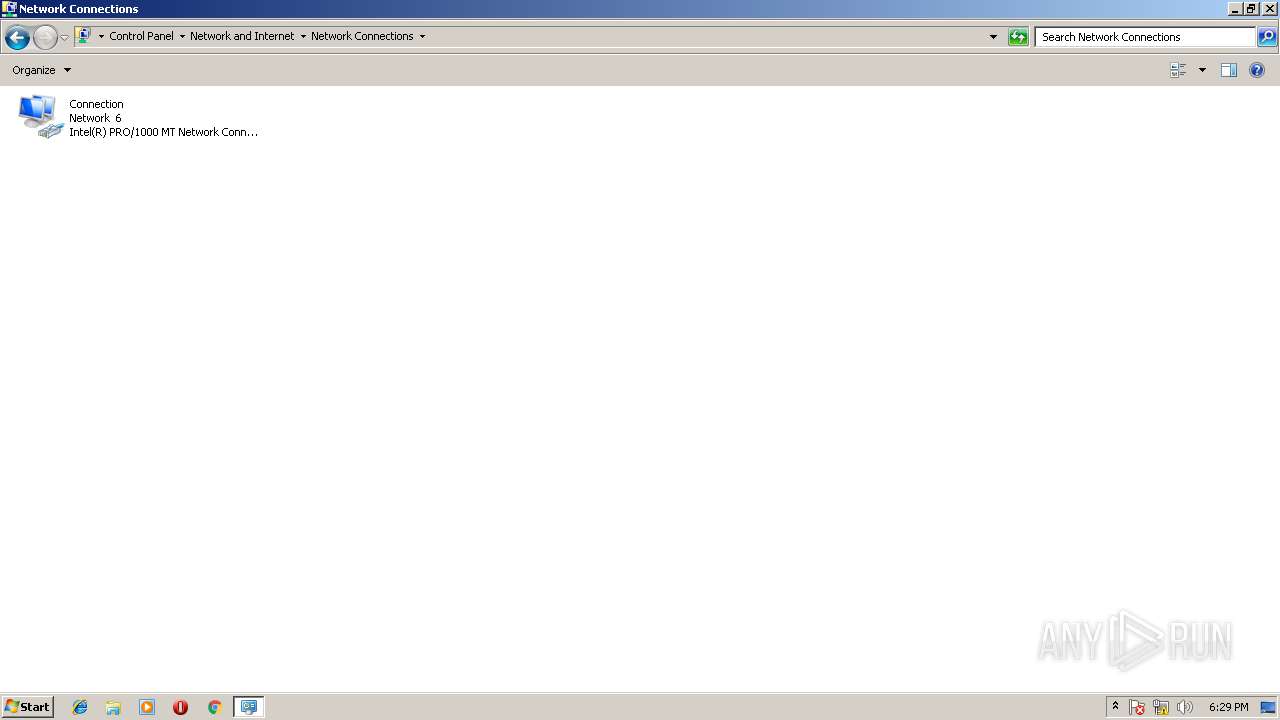
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.22.110:80 | — | Google Inc. | US | whitelisted |