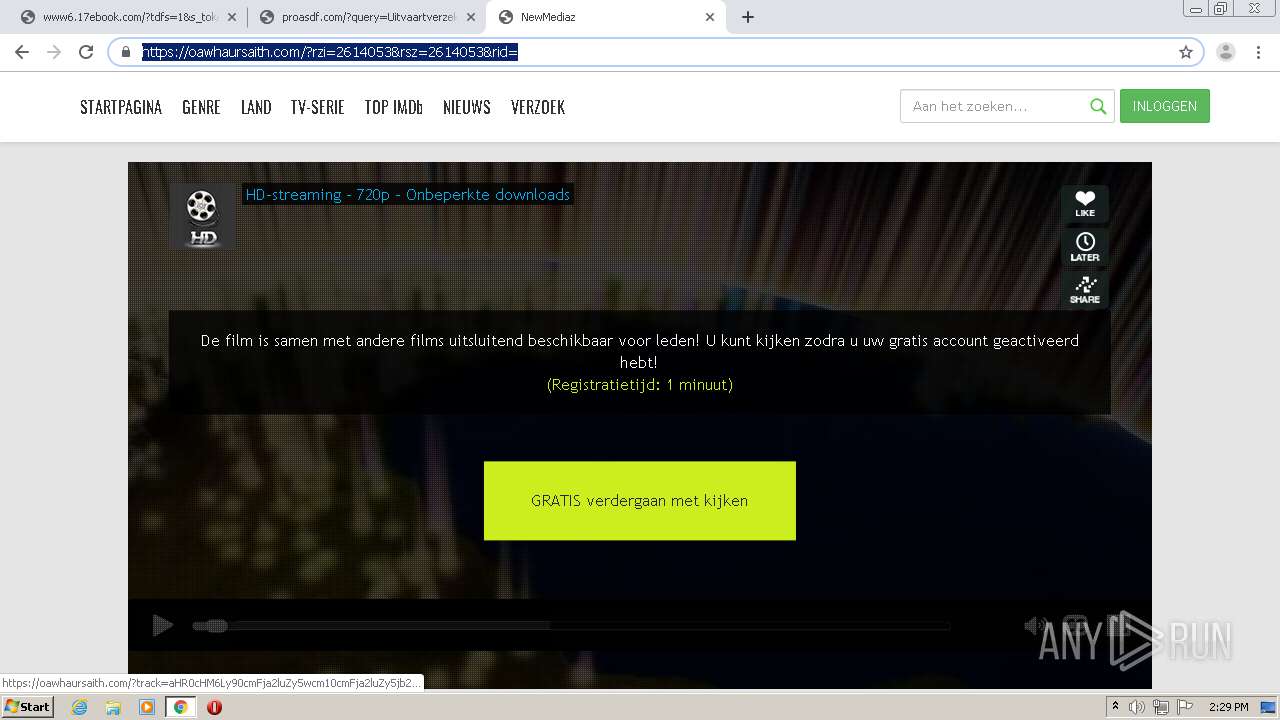
| URL: | http://www.17ebook.com |
| Full analysis: | https://app.any.run/tasks/424ad512-ccc2-4d0a-927b-dec65b23bdb4 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 13:27:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3919E33B9CD5A7B6FFC70BDF2233D5F3 |
| SHA1: | CEF788958C5030DA94A387FDA1A44AF1C8D29BAC |
| SHA256: | F0286E618C85B4AFA15AD92CE2A338F7D5343F4AEB7BD2ACCE9406BFD45CB079 |
| SSDEEP: | 3:N1KJS4r2:Cc4r2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
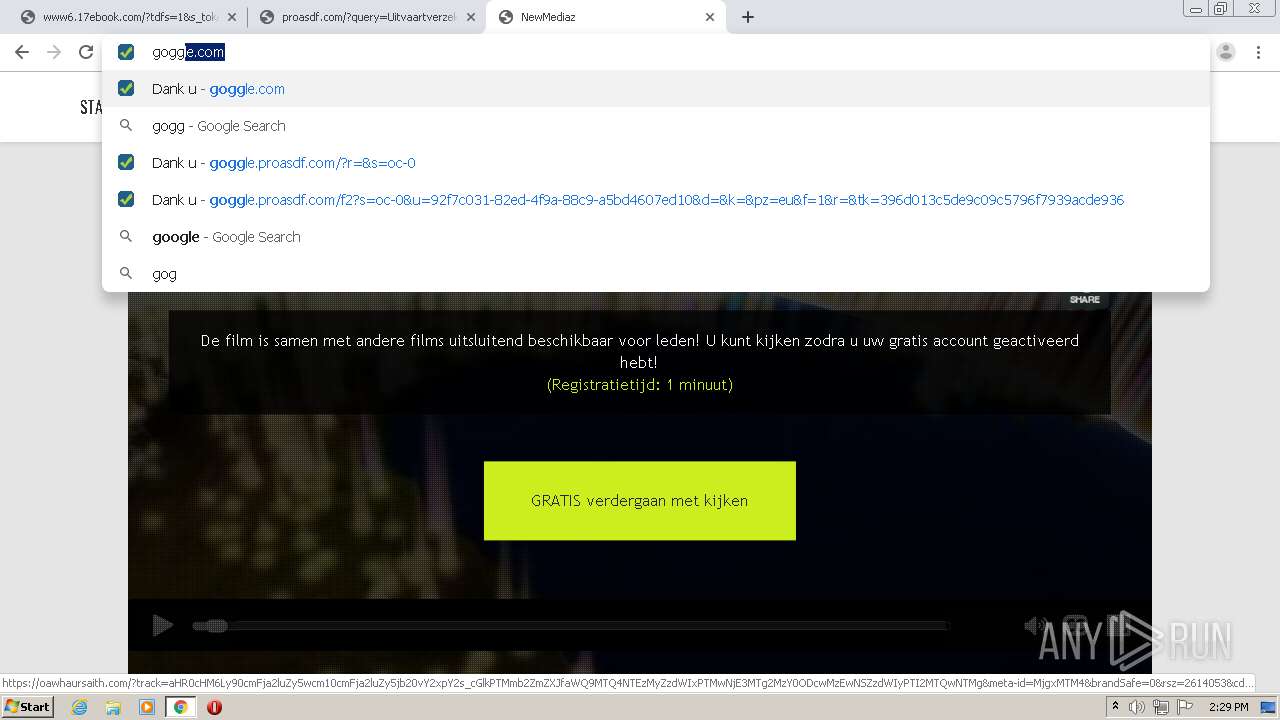
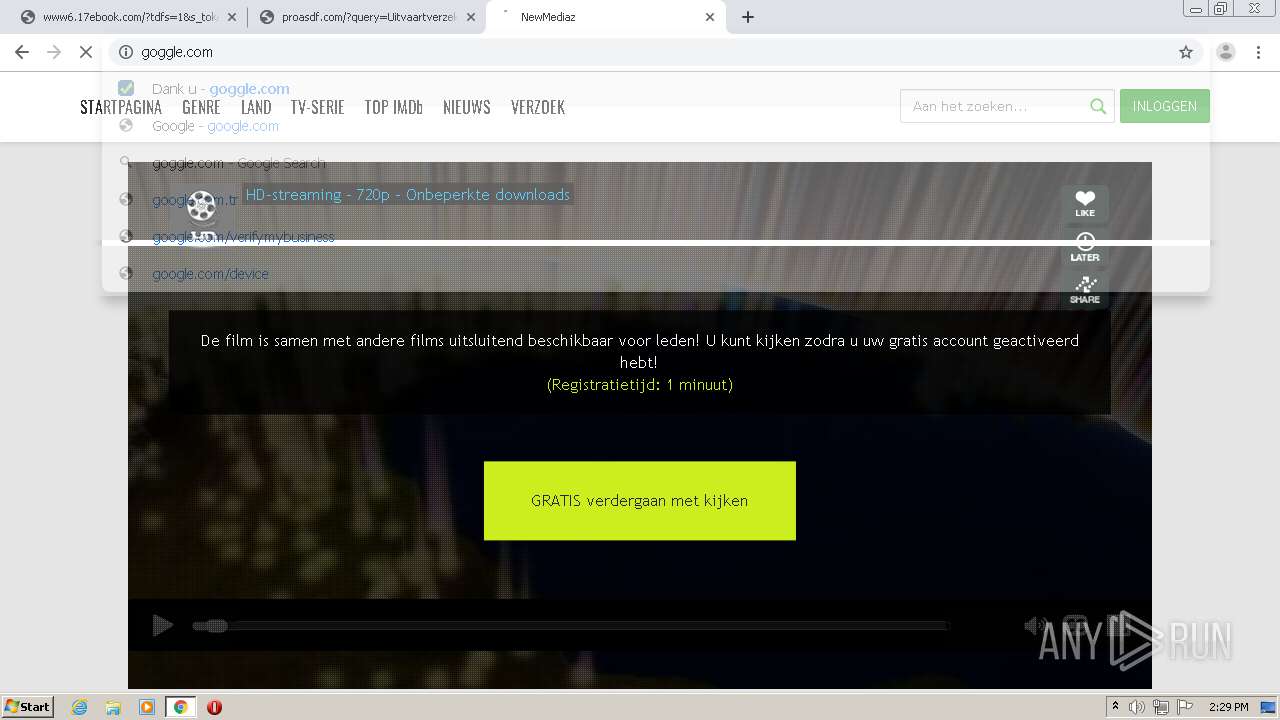
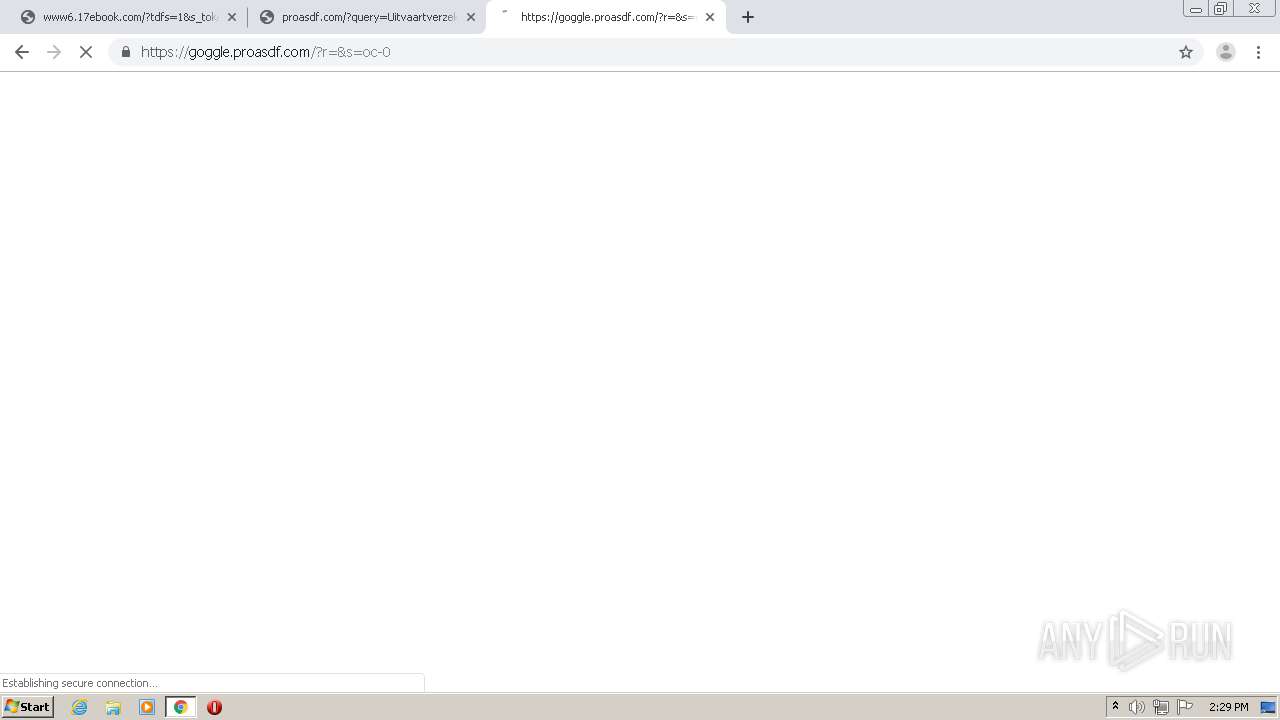
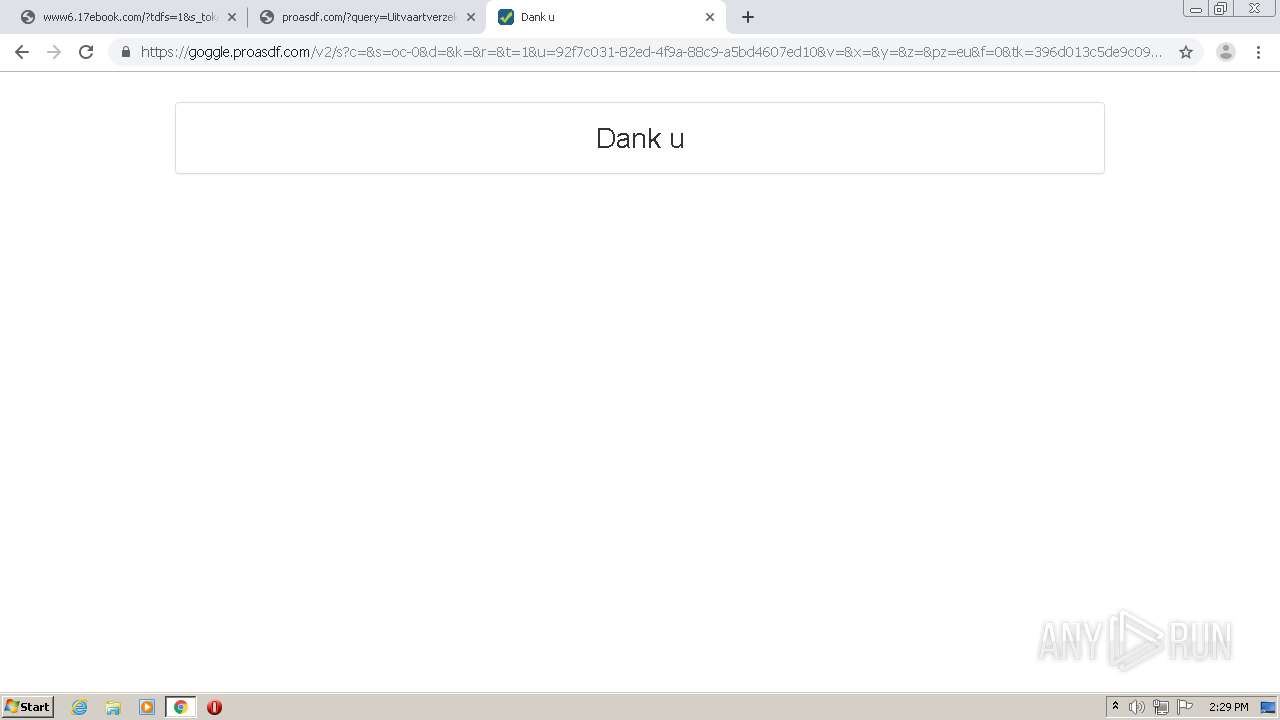
Modifies files in Chrome extension folder
- chrome.exe (PID: 620)
INFO
Reads the hosts file
- chrome.exe (PID: 620)
- chrome.exe (PID: 1652)
Application launched itself
- chrome.exe (PID: 620)
Reads settings of System Certificates
- chrome.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
57
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11888190477301879091 --mojo-platform-channel-handle=4164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8656239279800665827 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.17ebook.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17565995947647484085 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6563257670850243089 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4023688181104328052 --mojo-platform-channel-handle=4500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8342628300495481948 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=280038978155652827 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4111116364248166298 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11146273073875672101,13216643364405797548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10592860267858857099 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
823
Read events
700
Write events
118
Delete events
5
Modification events
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 620-13239034076541125 |
Value: 259 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
186
Text files
308
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B0FDD-26C.pma | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e391dc6e-2fcc-4126-b00d-5ab6f315024c.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF10759f.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF107580.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF107551.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF1075ce.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF107716.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
209
DNS requests
136
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
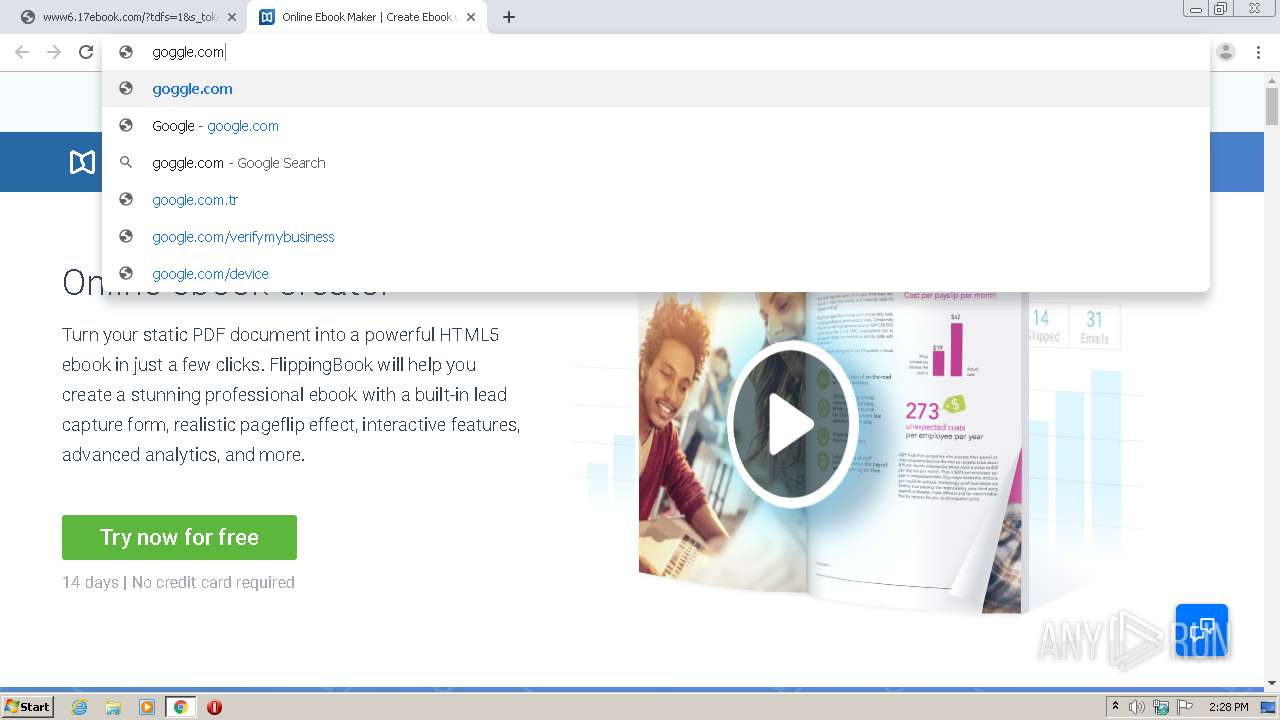
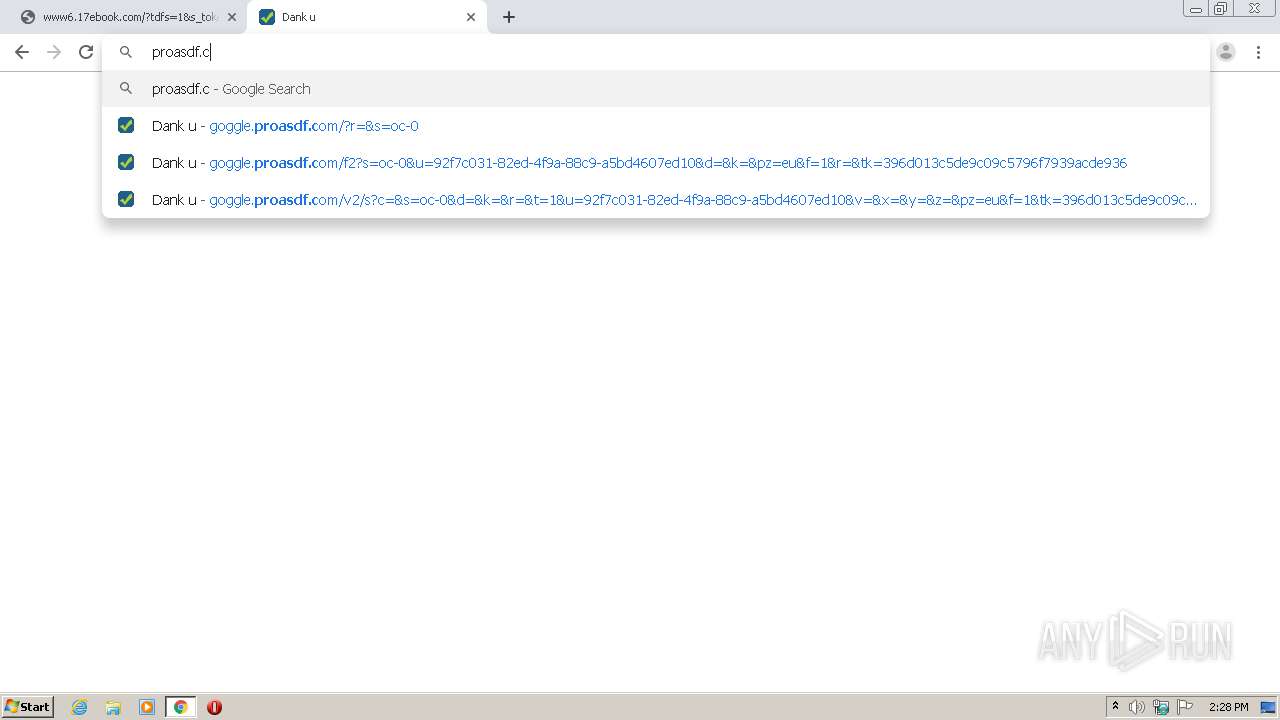
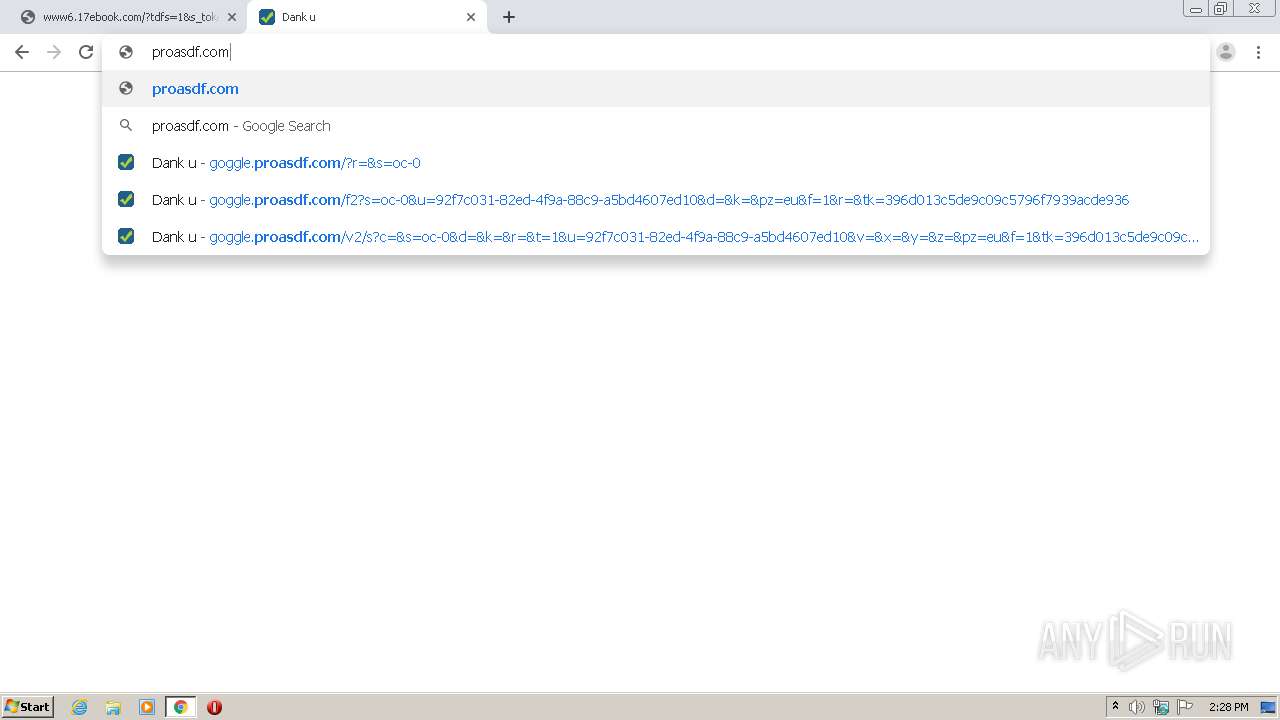
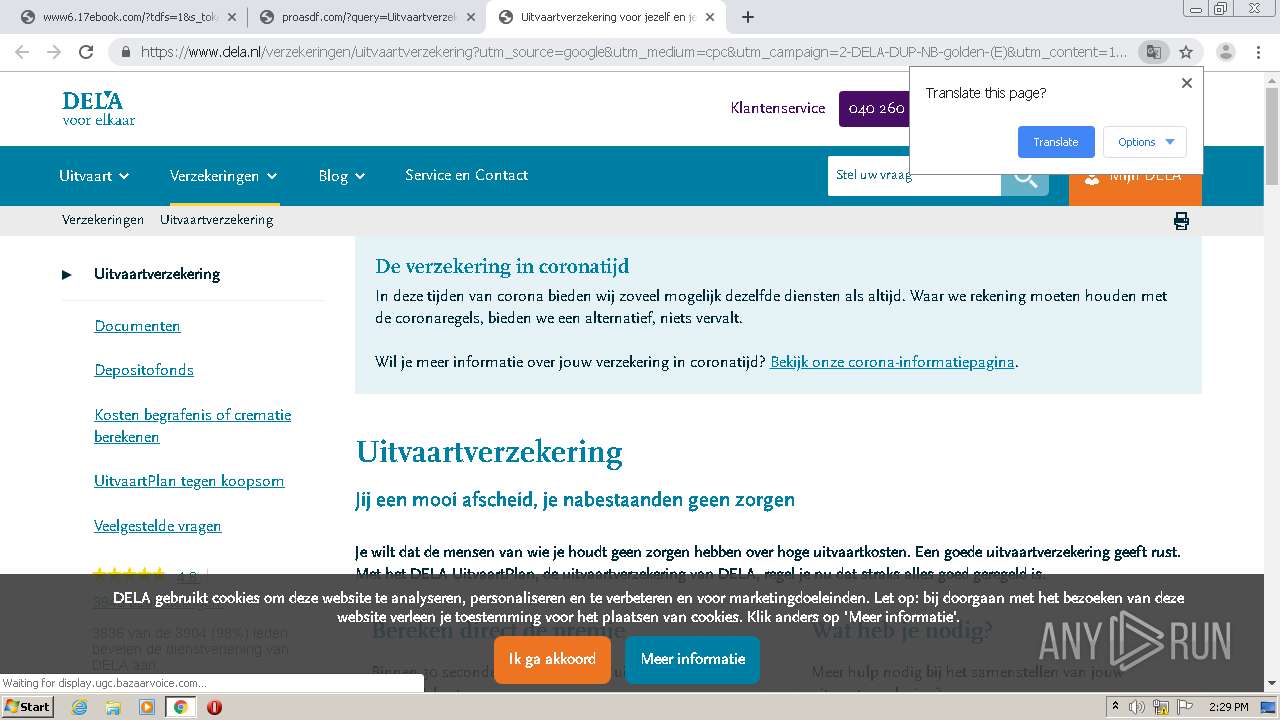
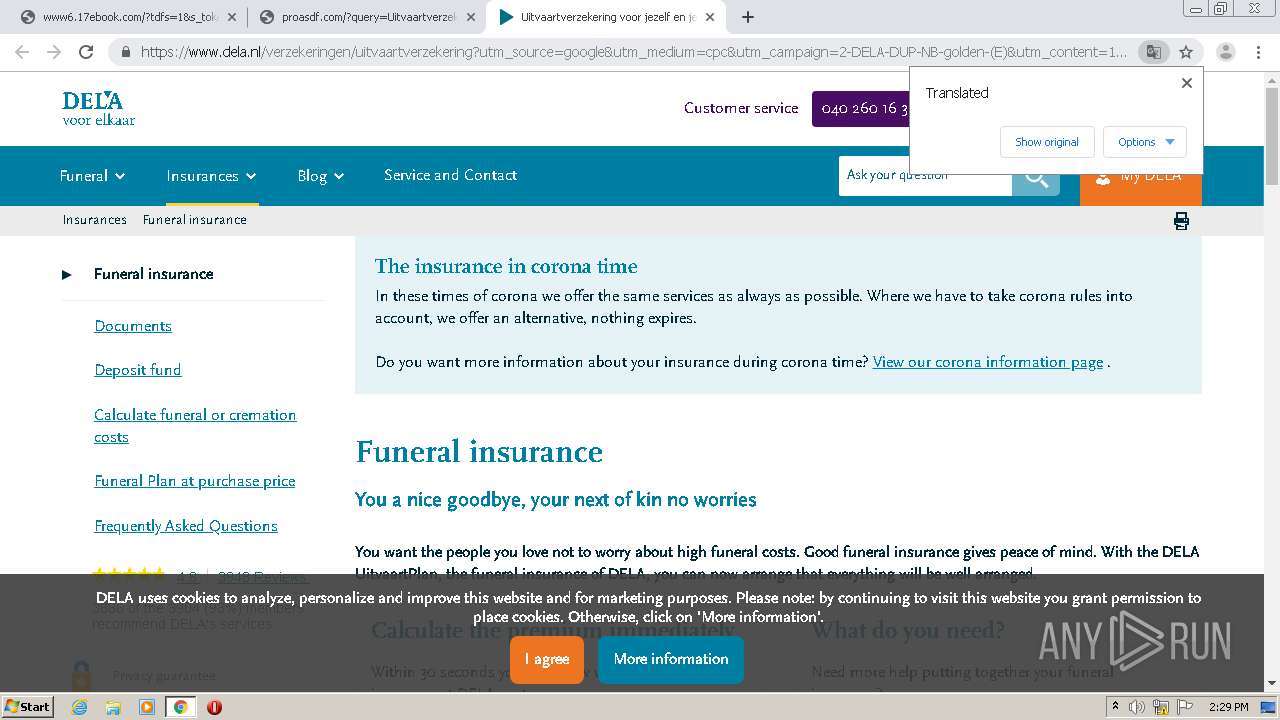
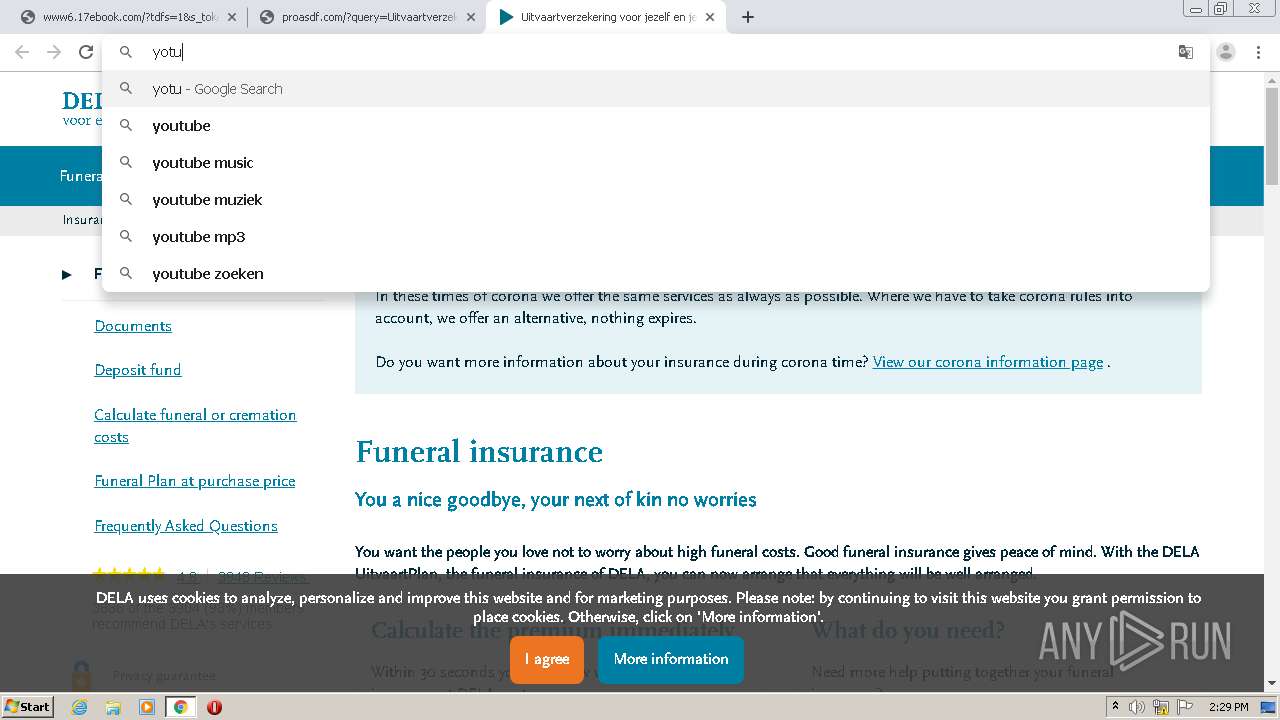
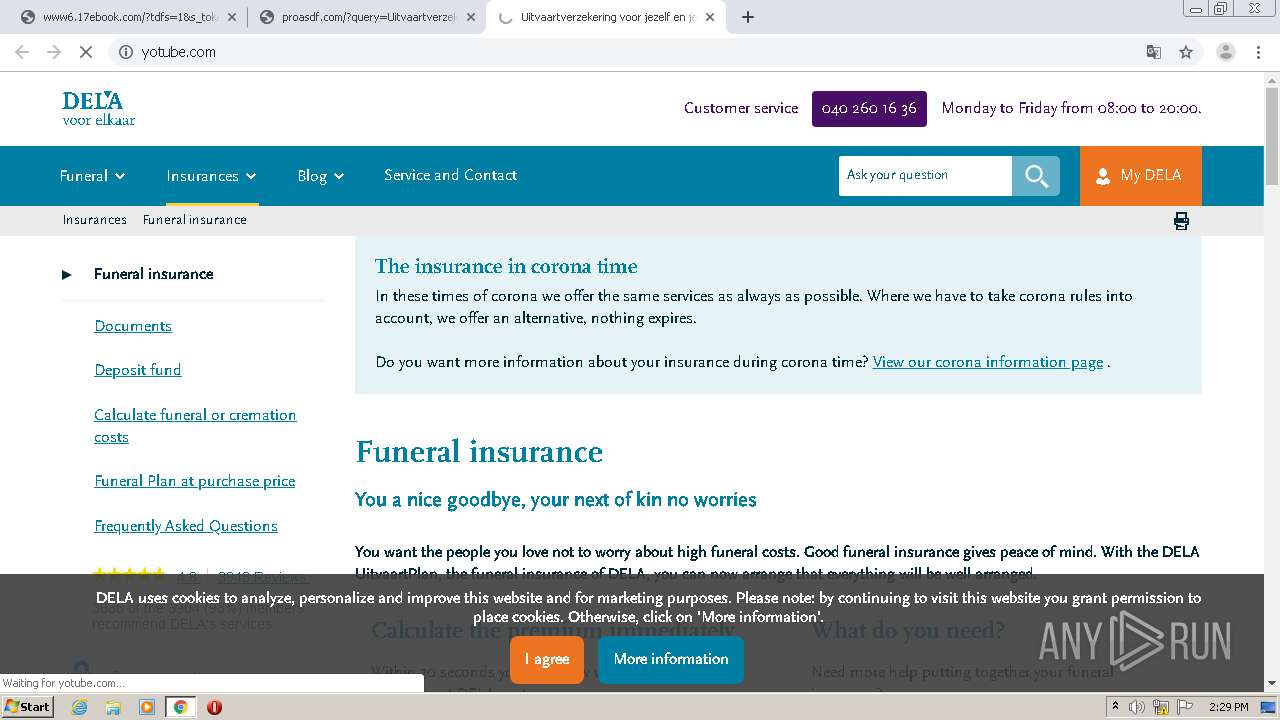
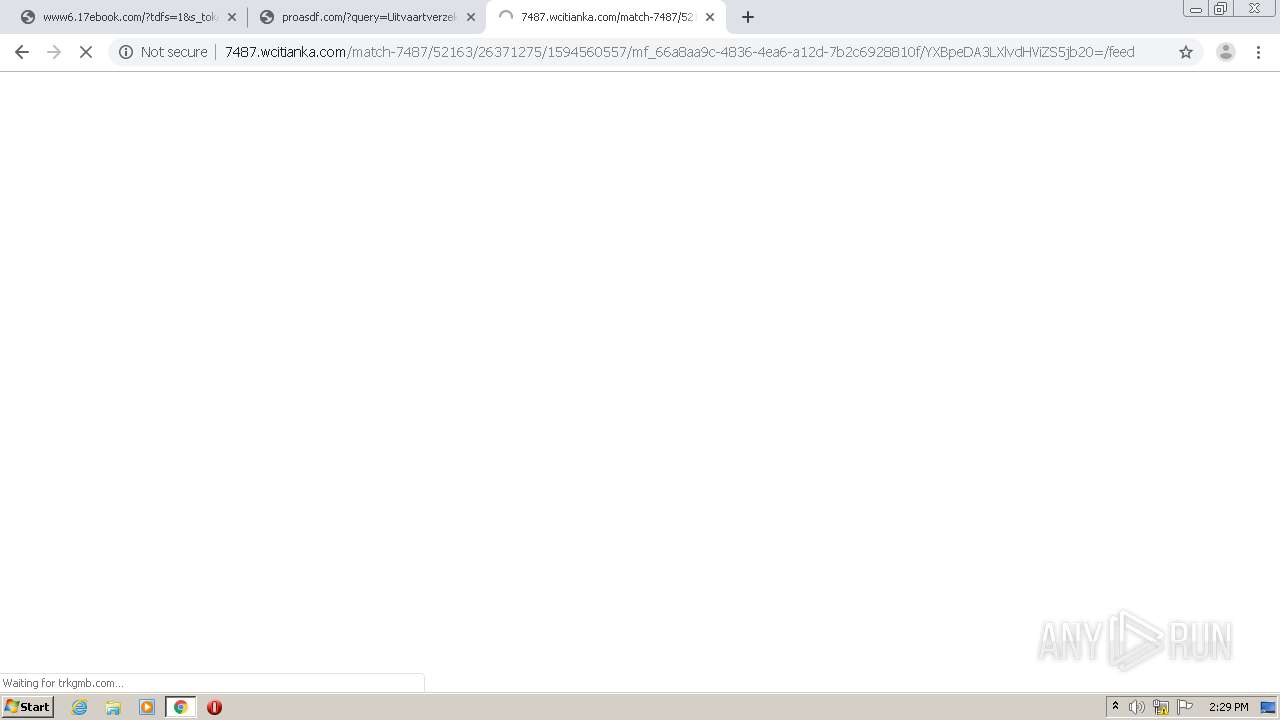
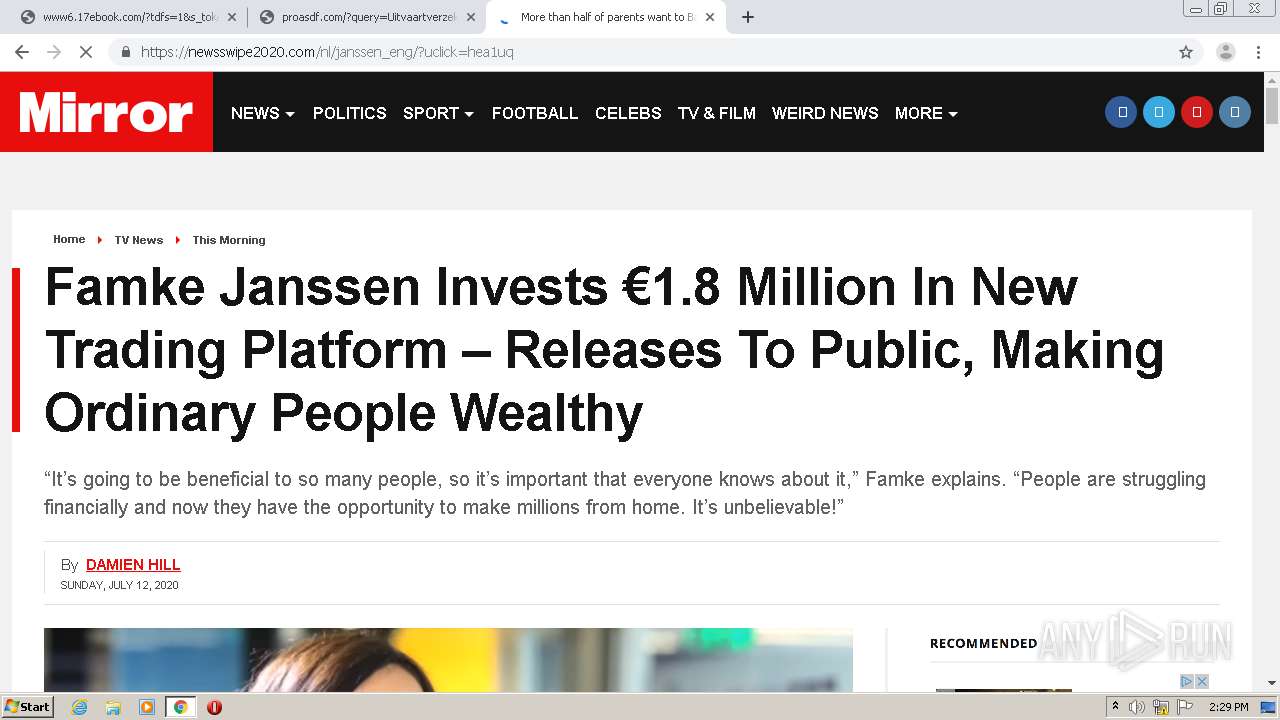
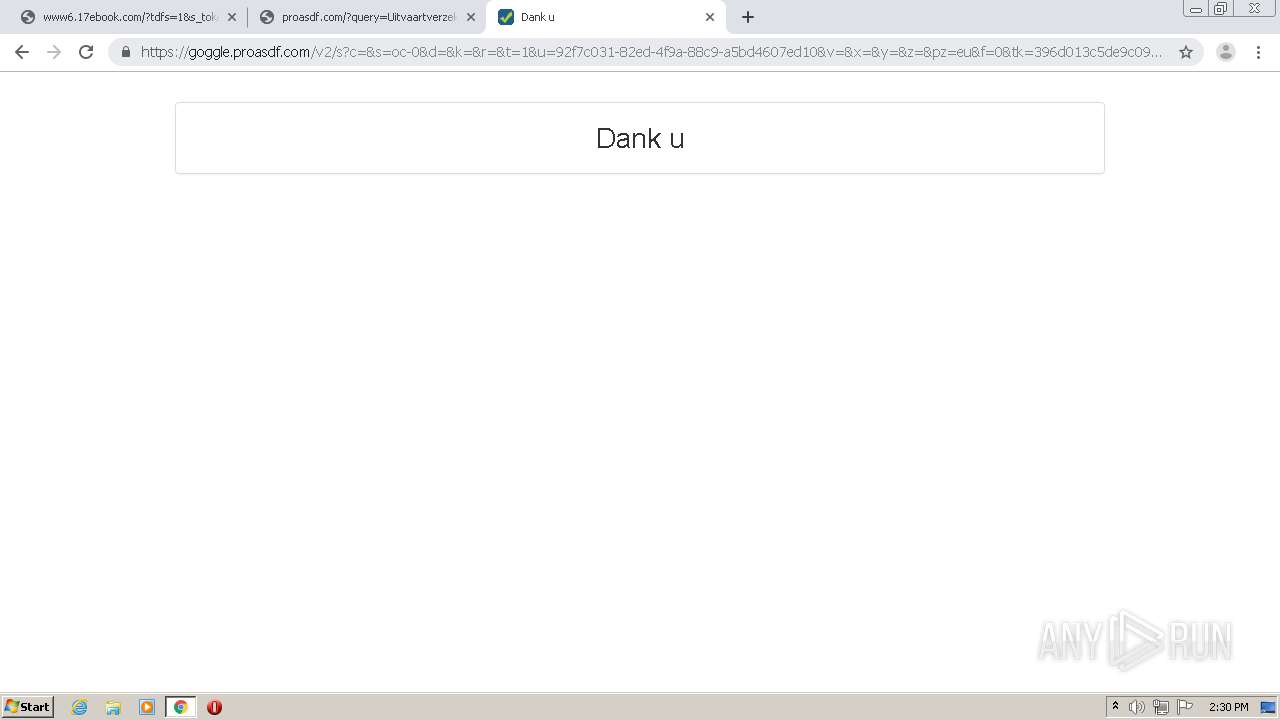
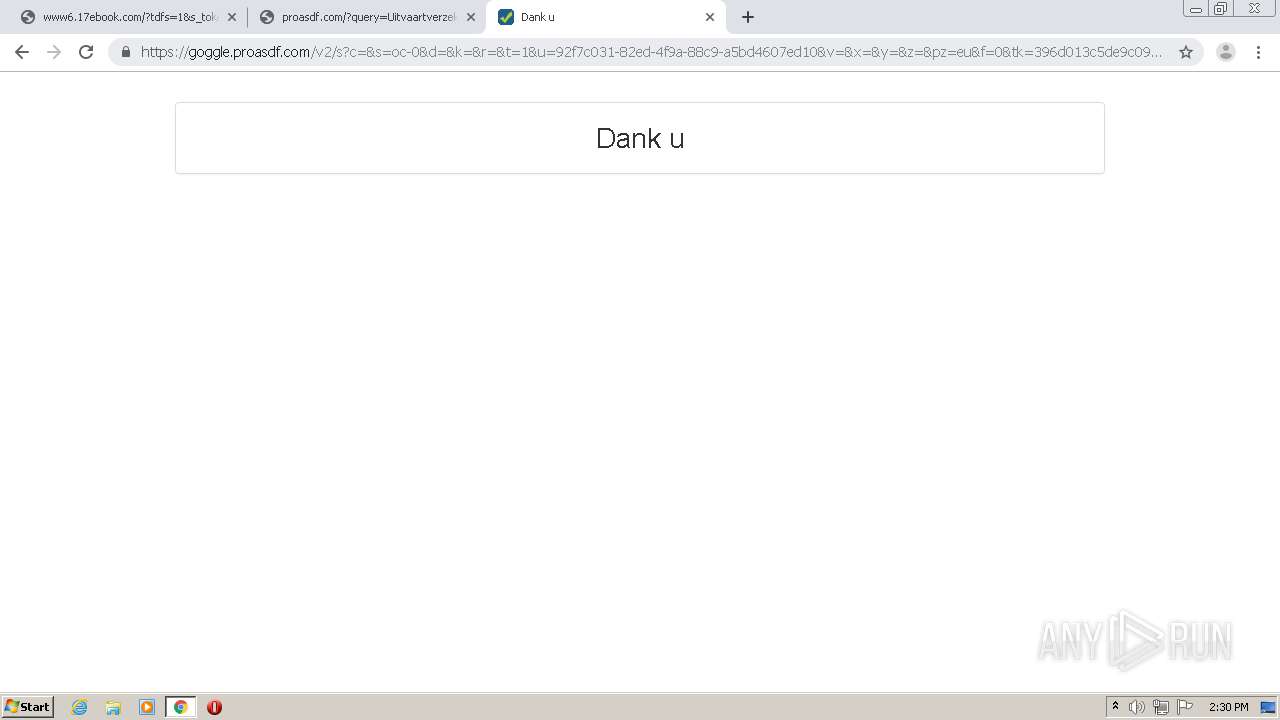
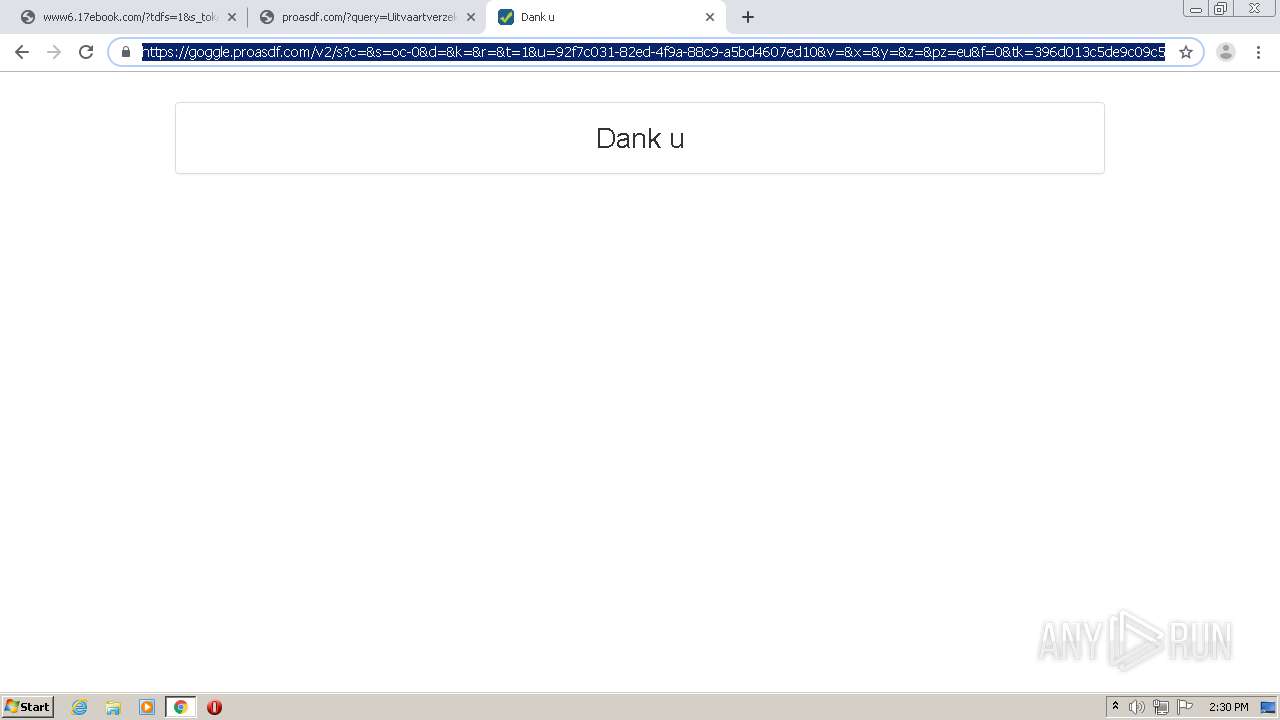
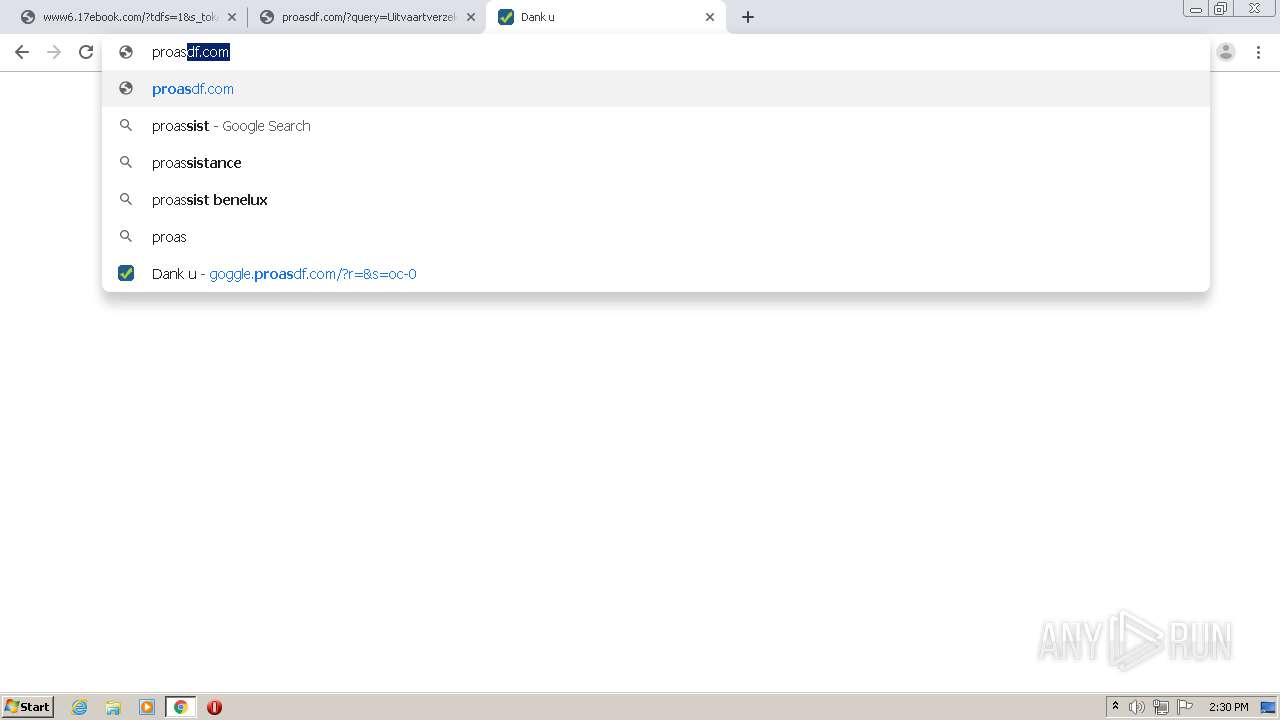
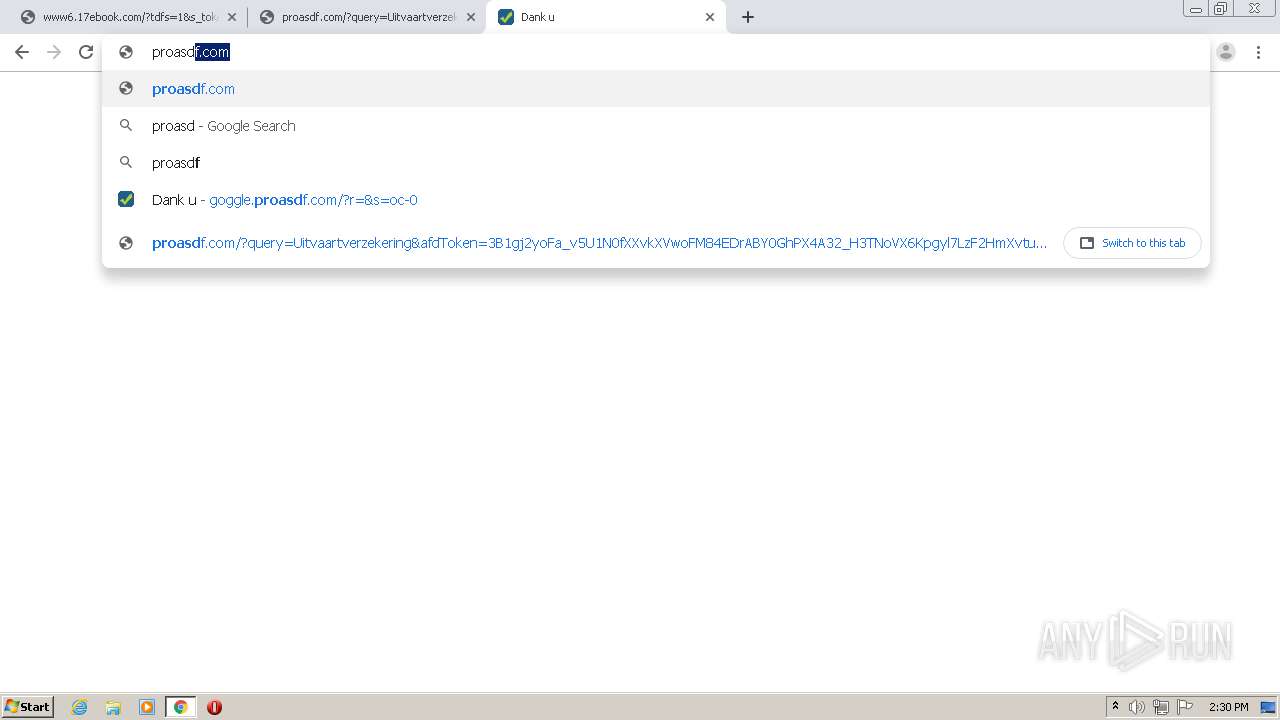
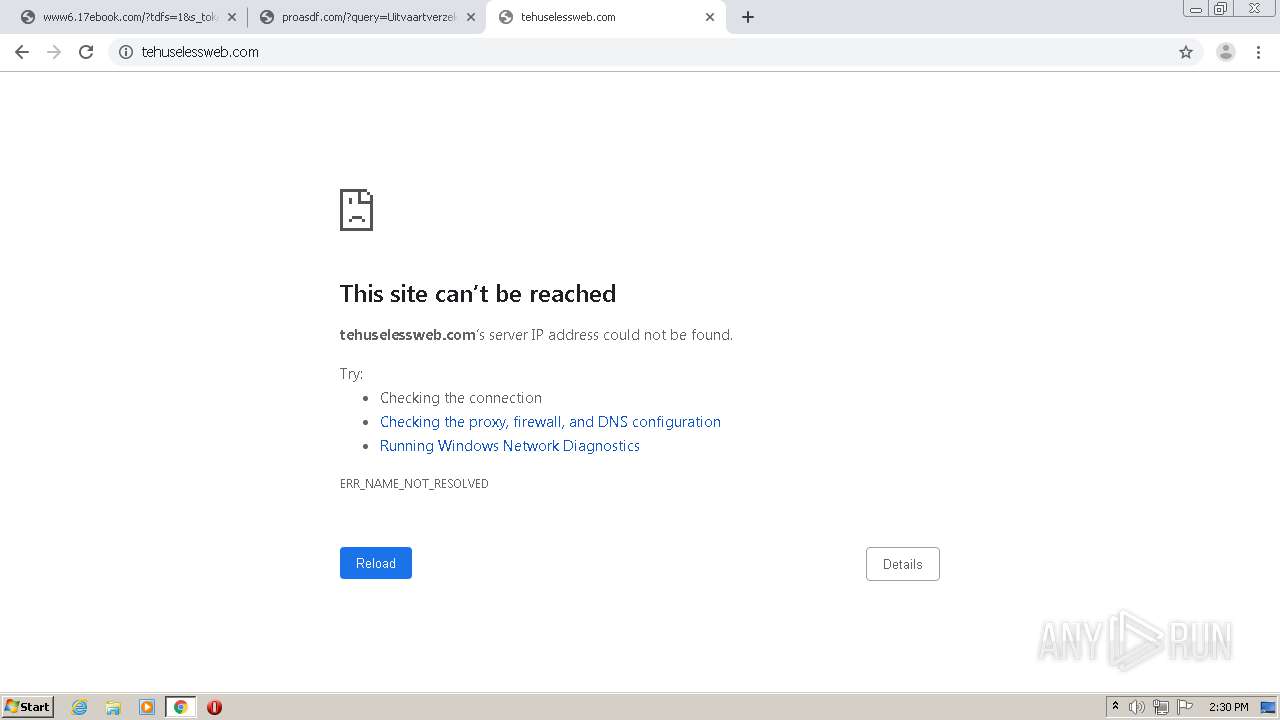
1652 | chrome.exe | GET | 302 | 45.55.44.56:80 | http://goggle.com/ | US | — | — | malicious |
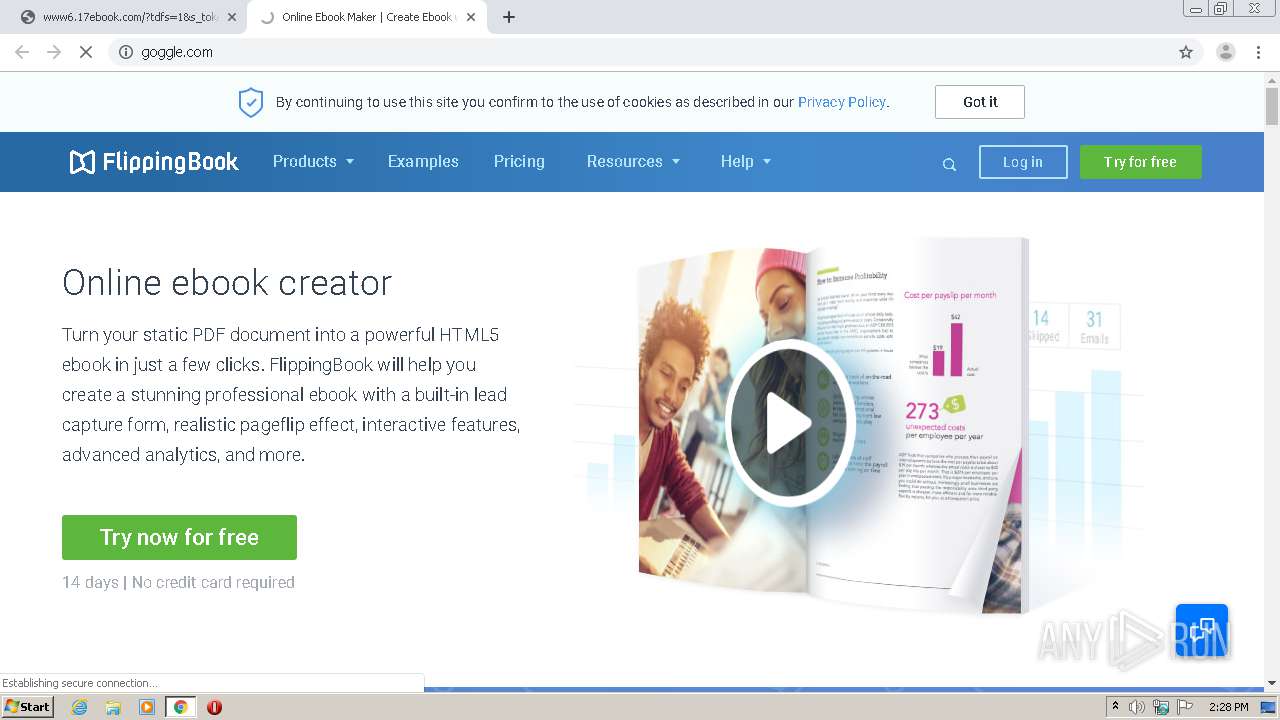
1652 | chrome.exe | GET | 200 | 96.126.123.244:80 | http://www.17ebook.com/ | US | html | 1.47 Kb | malicious |
1652 | chrome.exe | GET | 200 | 96.126.123.244:80 | http://www.17ebook.com/mtm/async/eyJ1cmkiOiIvIiwiYXJncyI6IiIsInJlZmVyZXIiOiIifQ:1juc1P:X8Scv-G8-3xGyo9hrLbSXulcRpY/1 | US | text | 203 b | malicious |
1652 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
1652 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEChOOcFLOG2InHKZ5YzQWlc%3D | US | der | 727 b | whitelisted |
1652 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
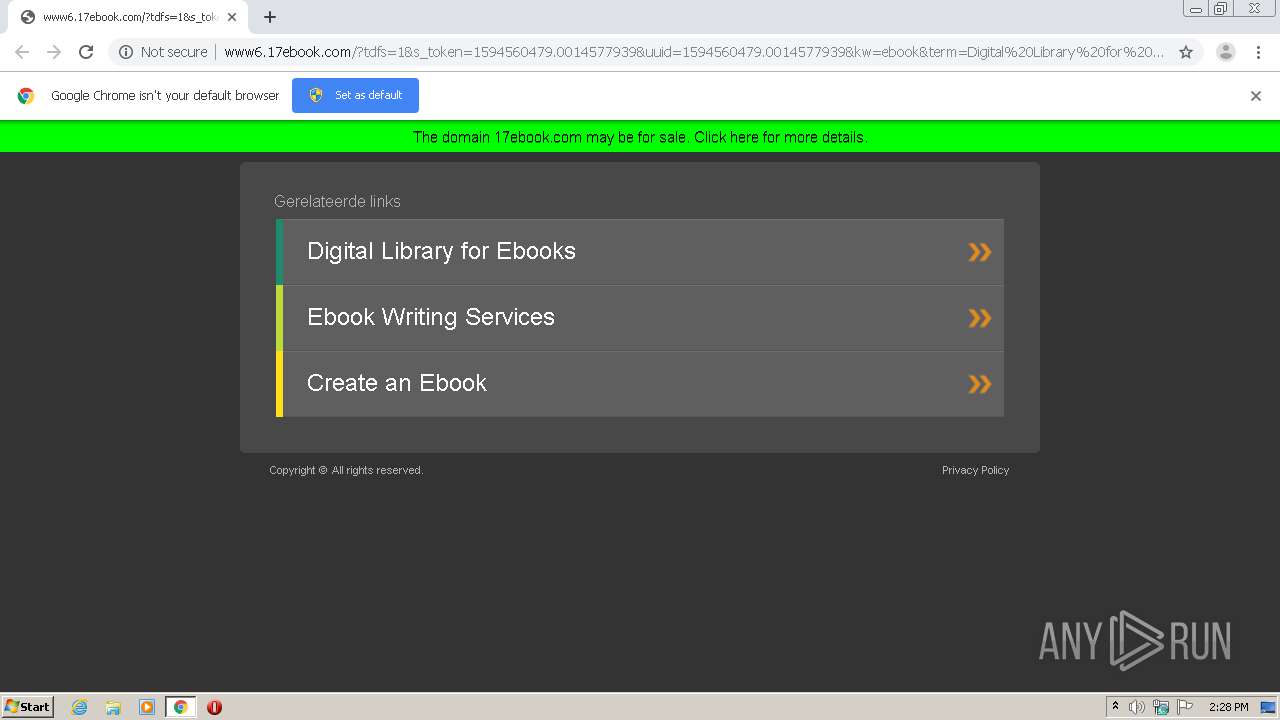
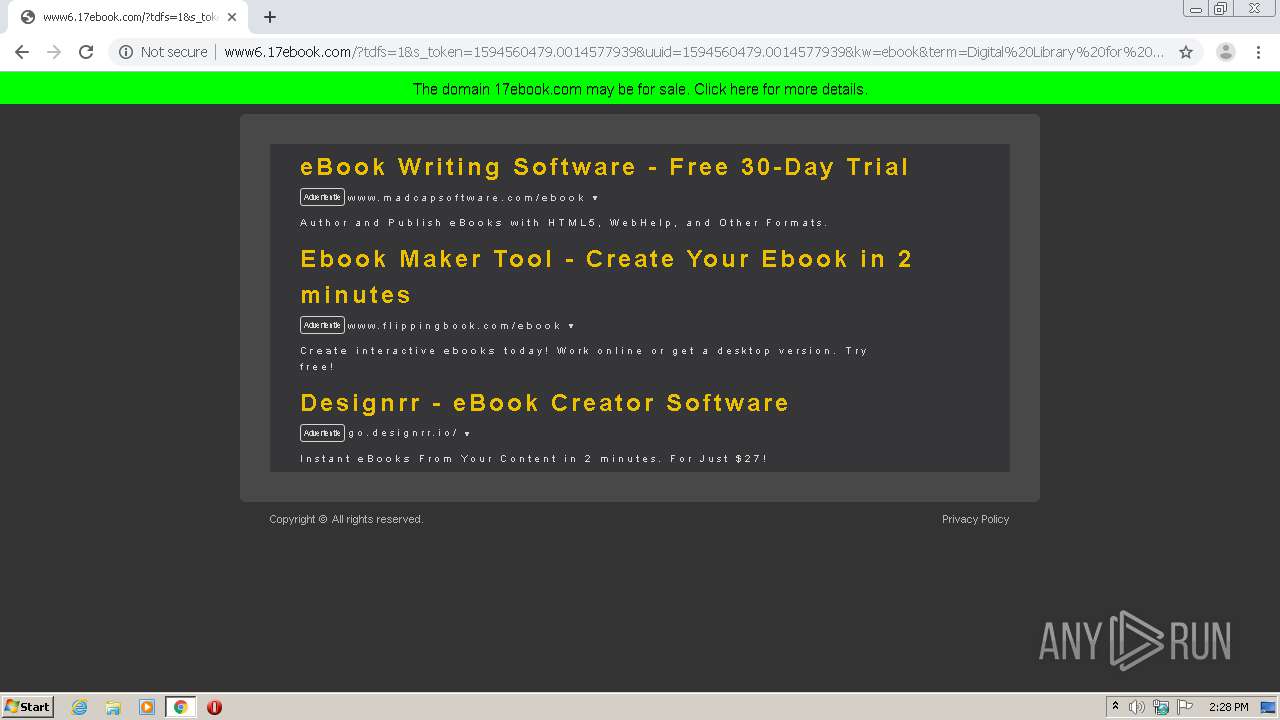
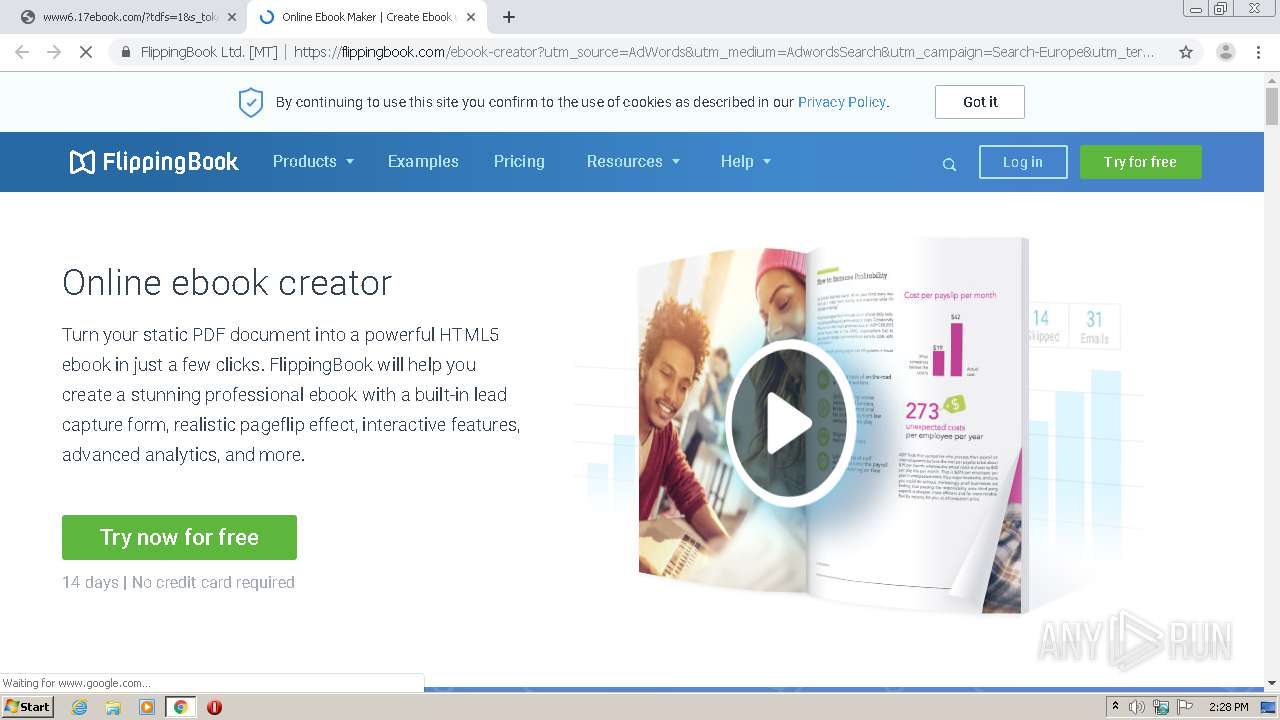
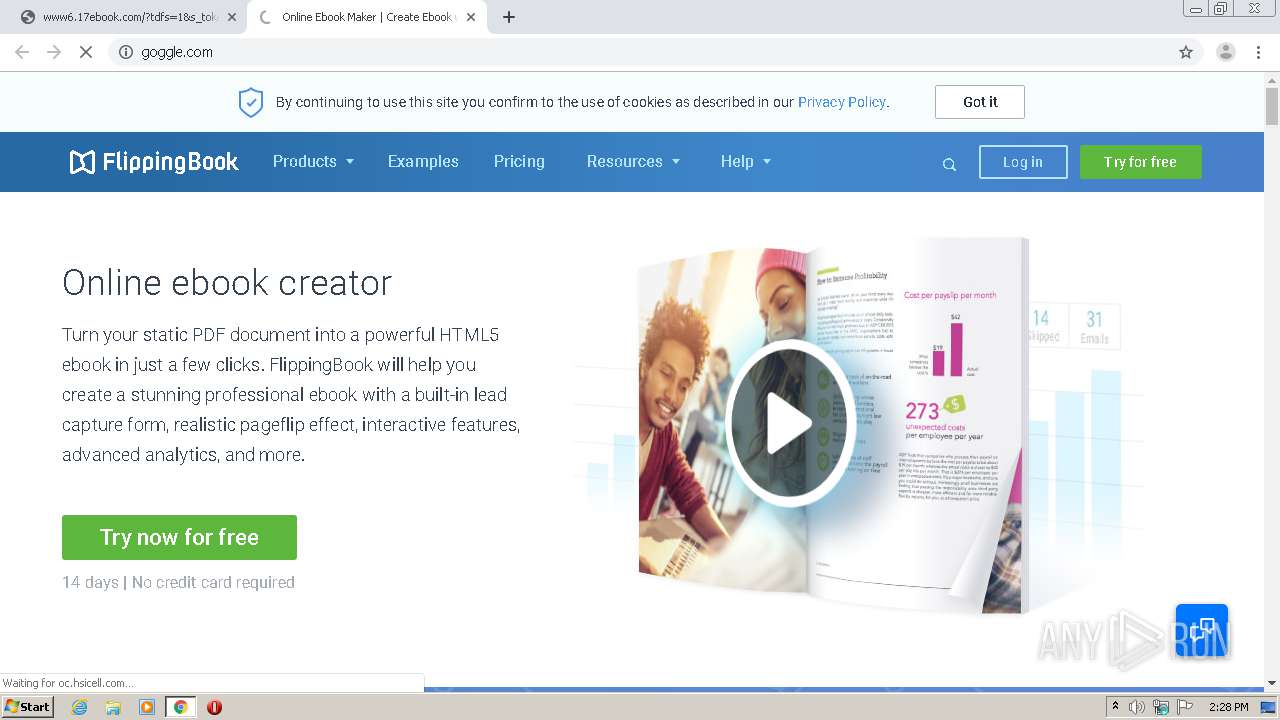
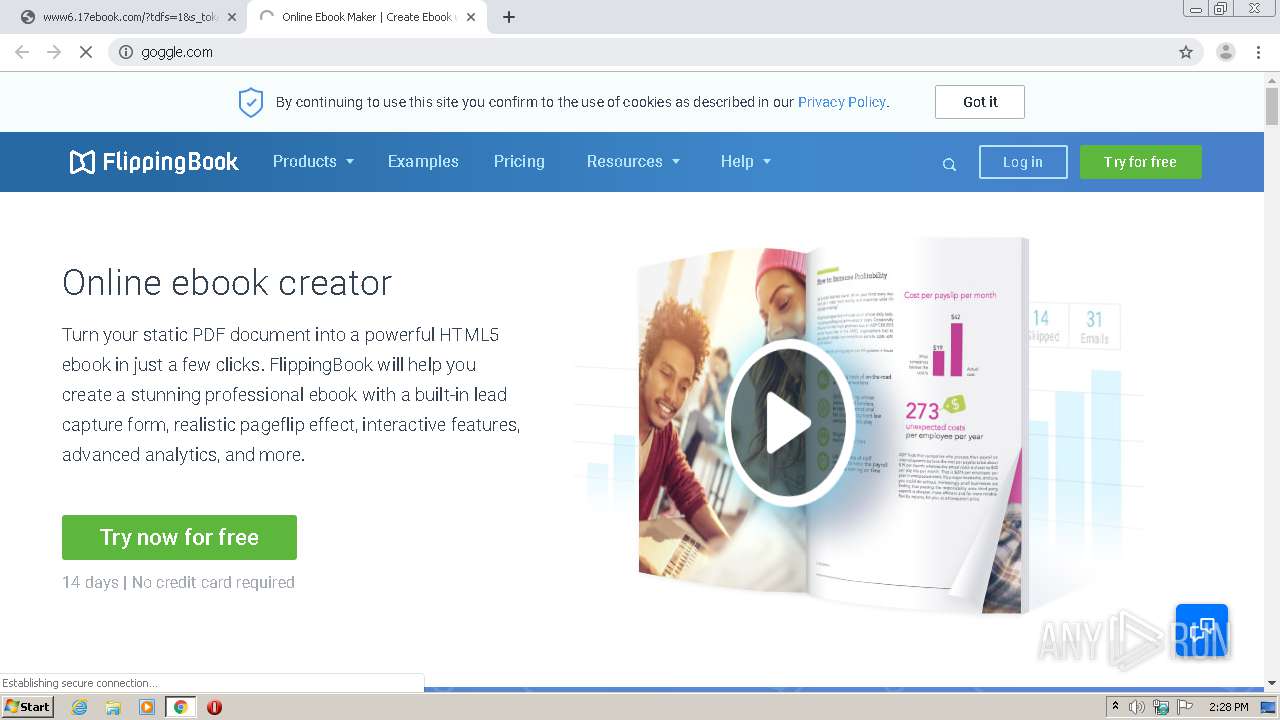
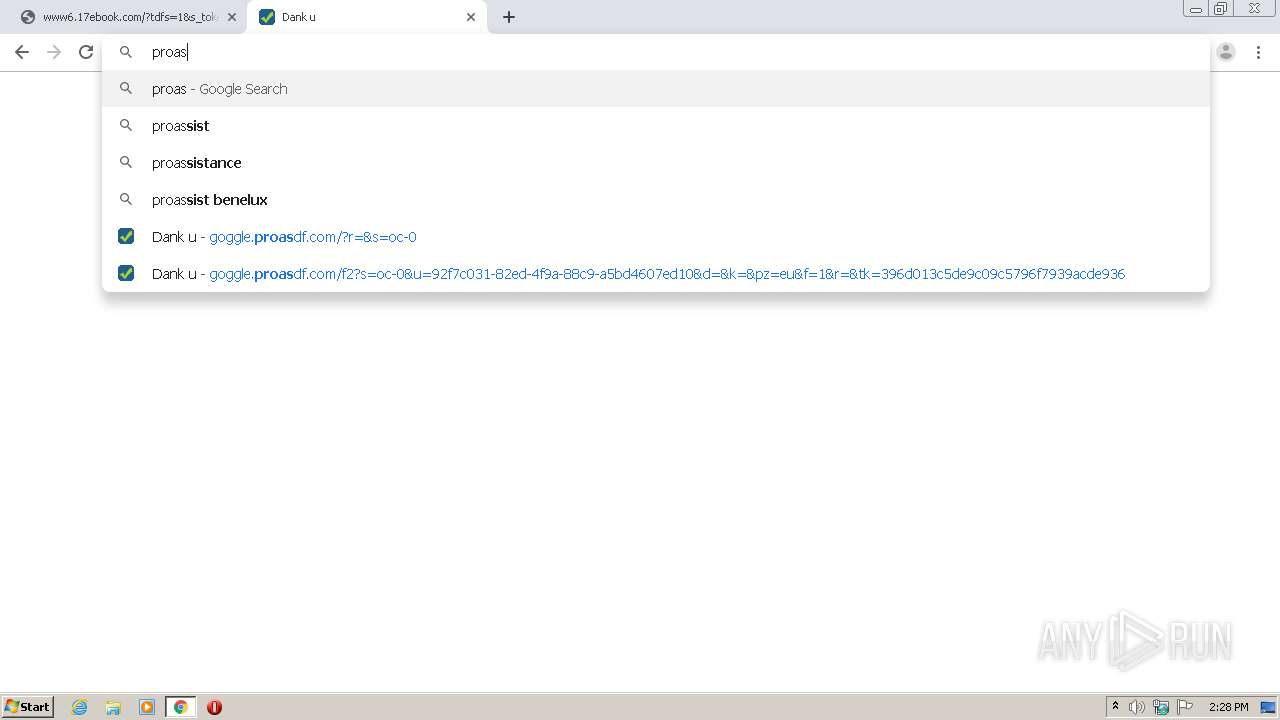
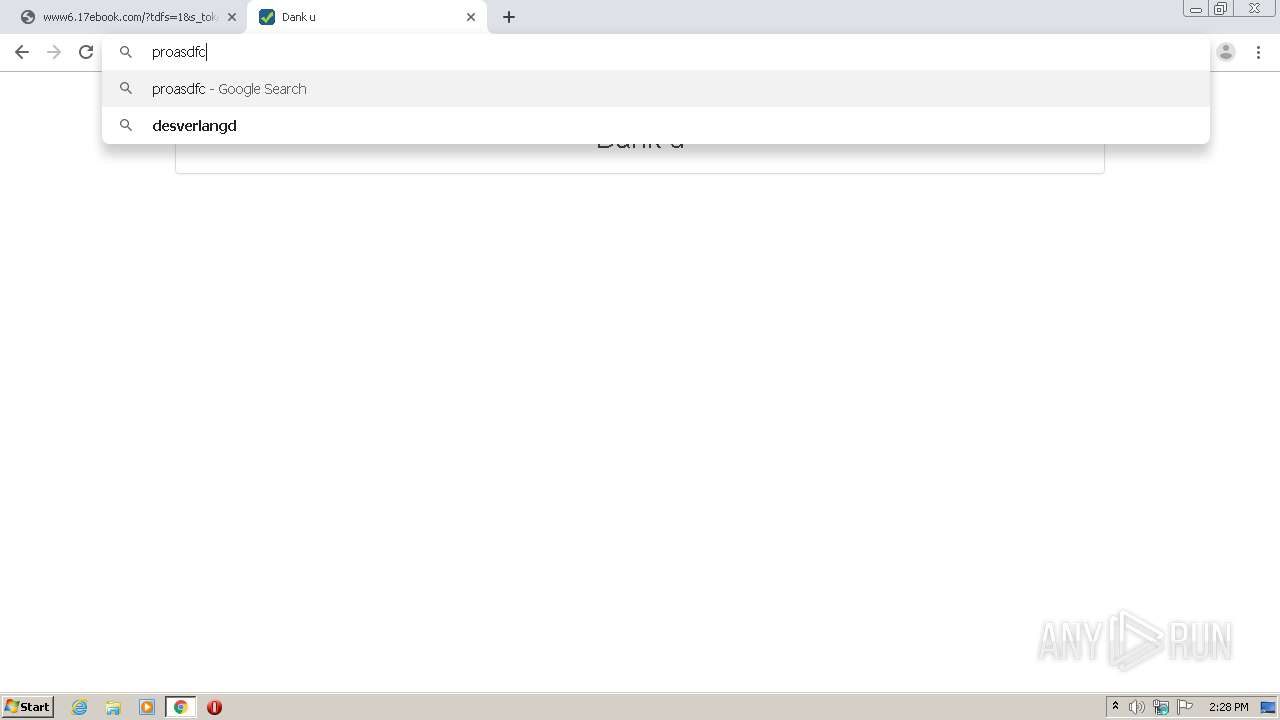
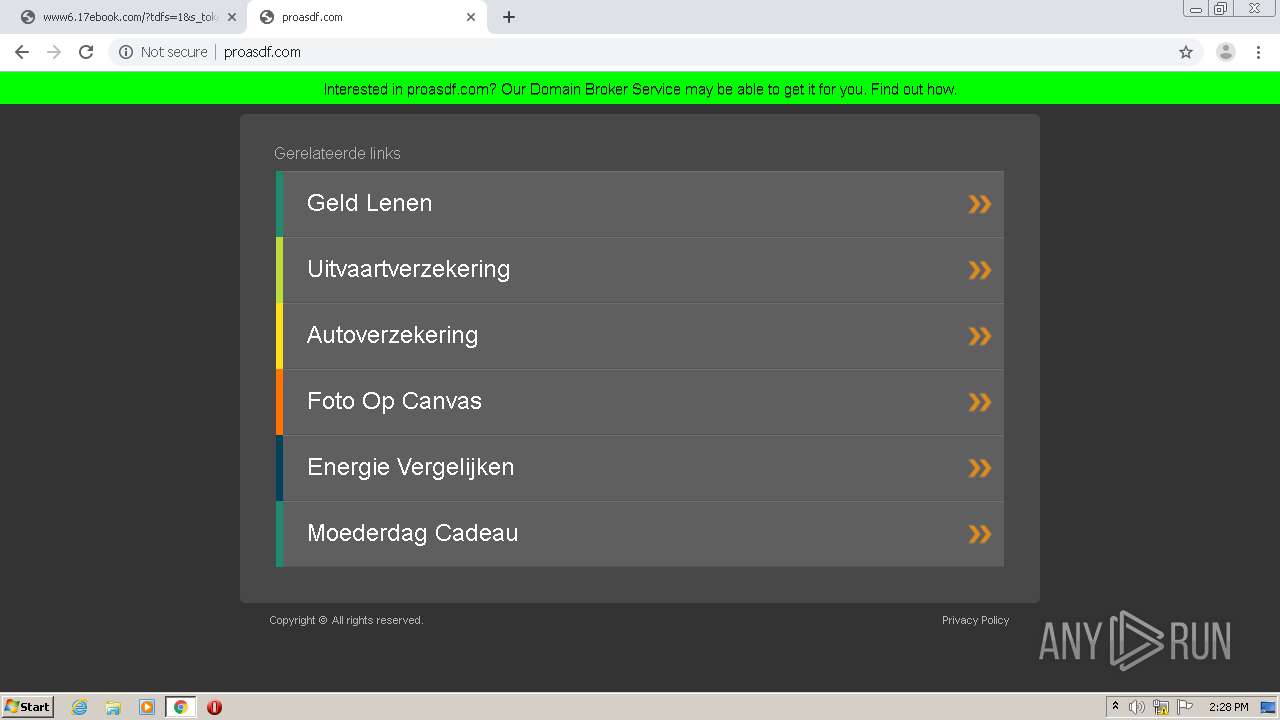
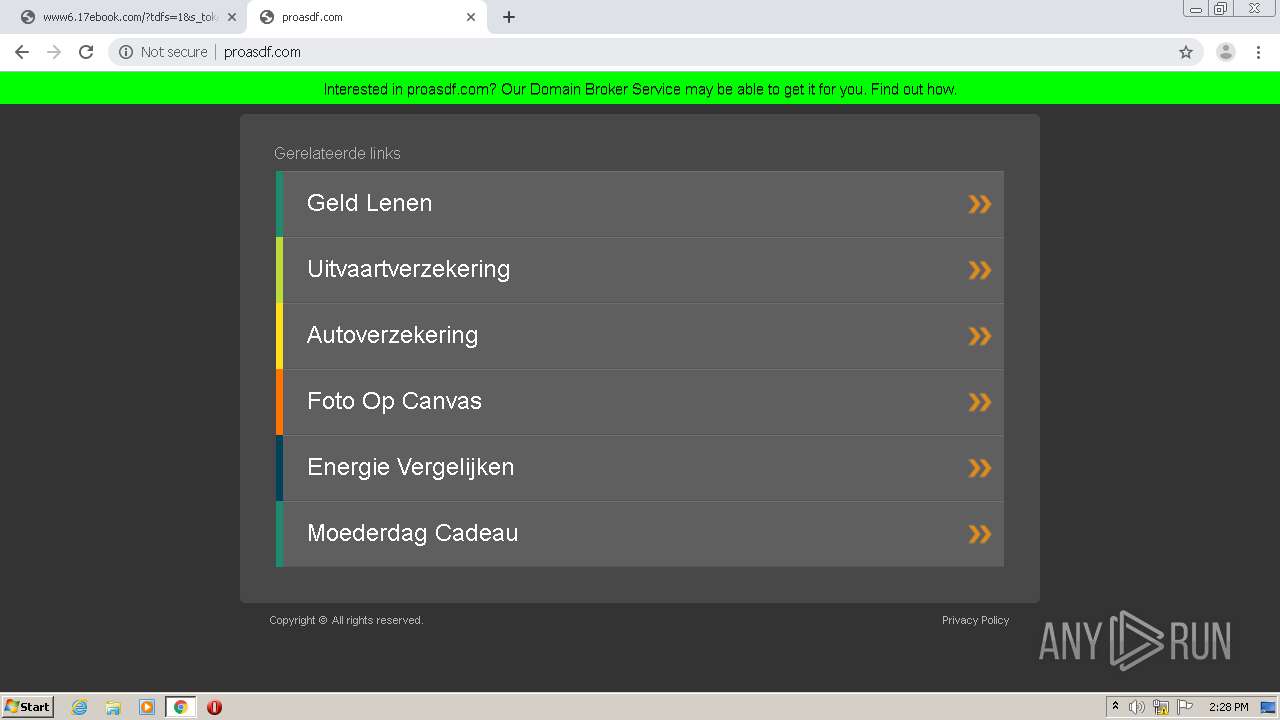
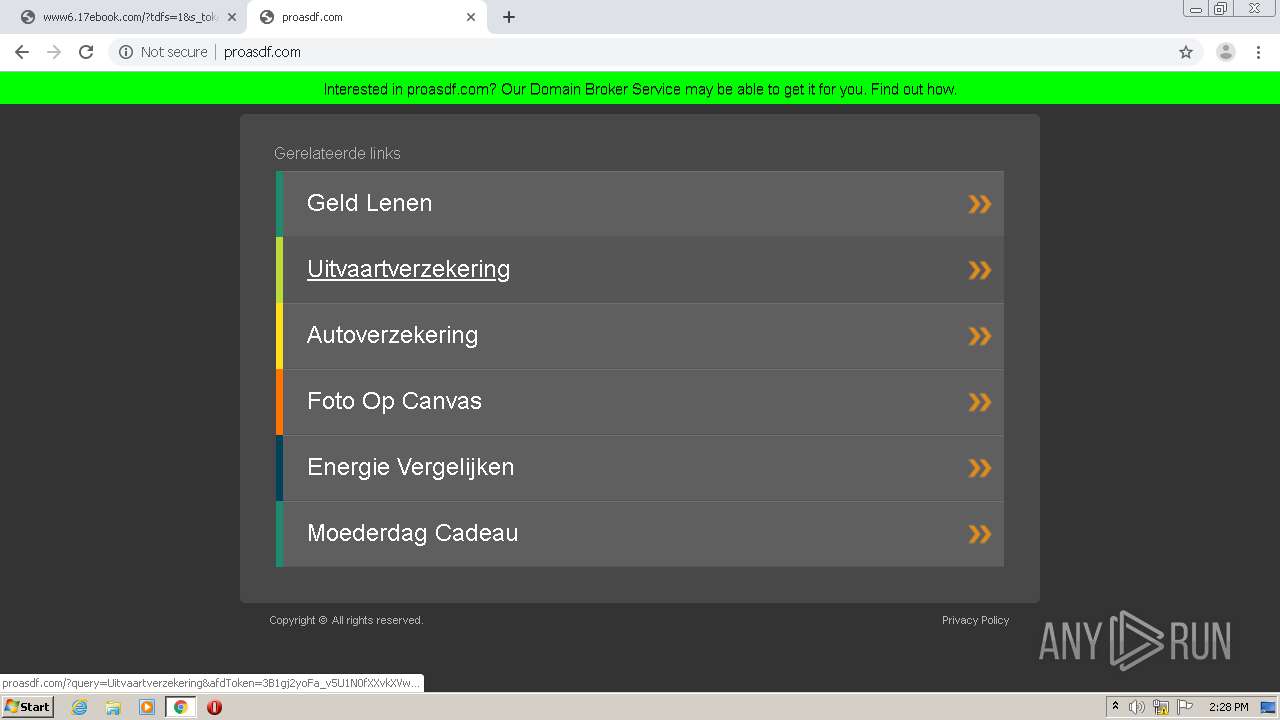
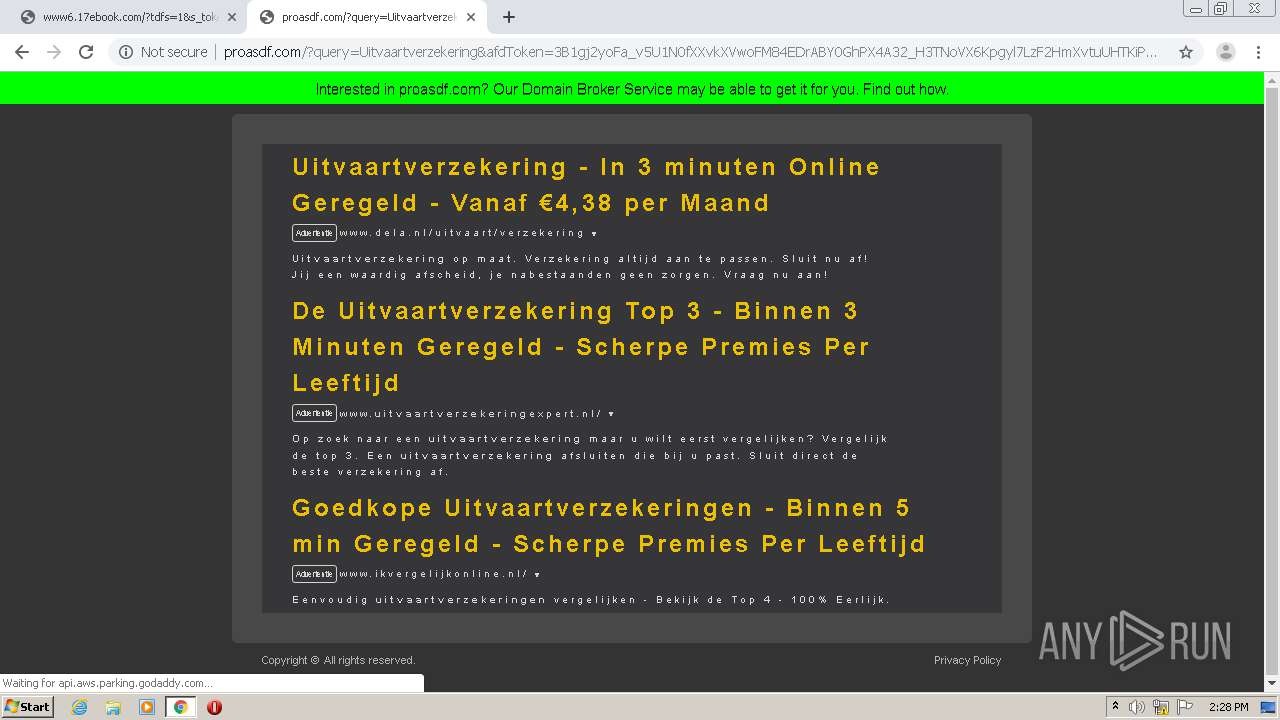
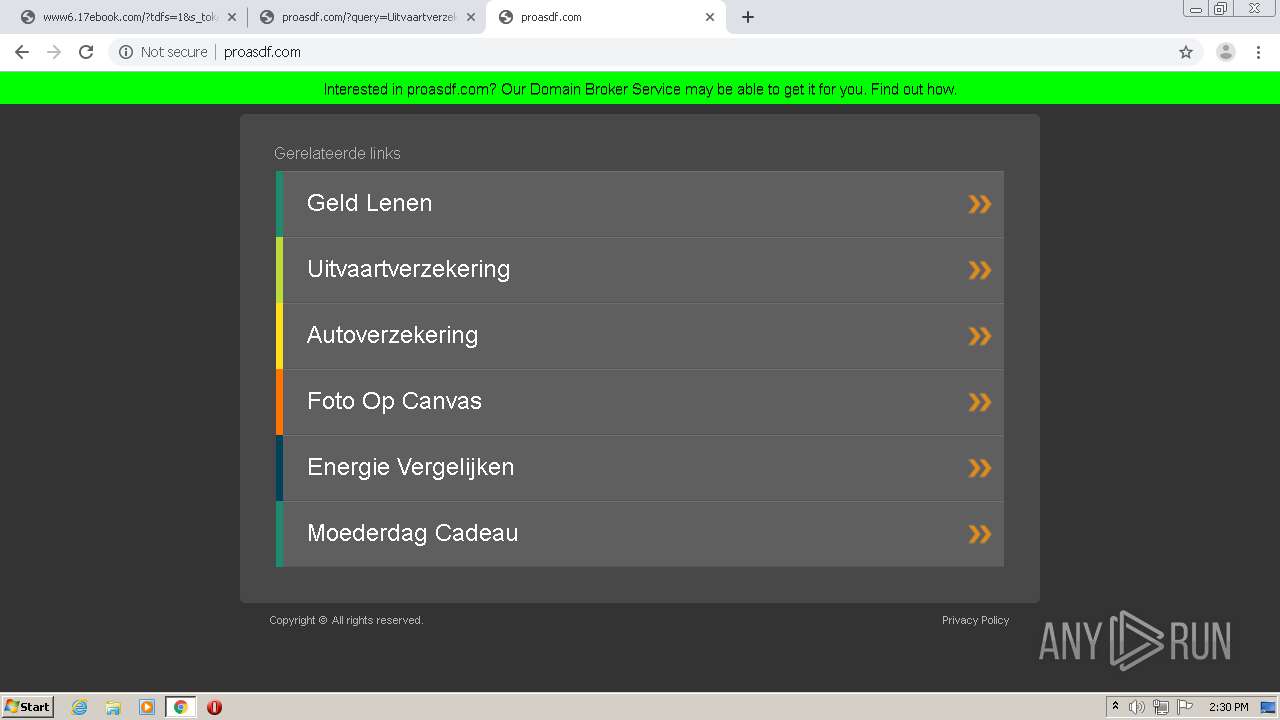
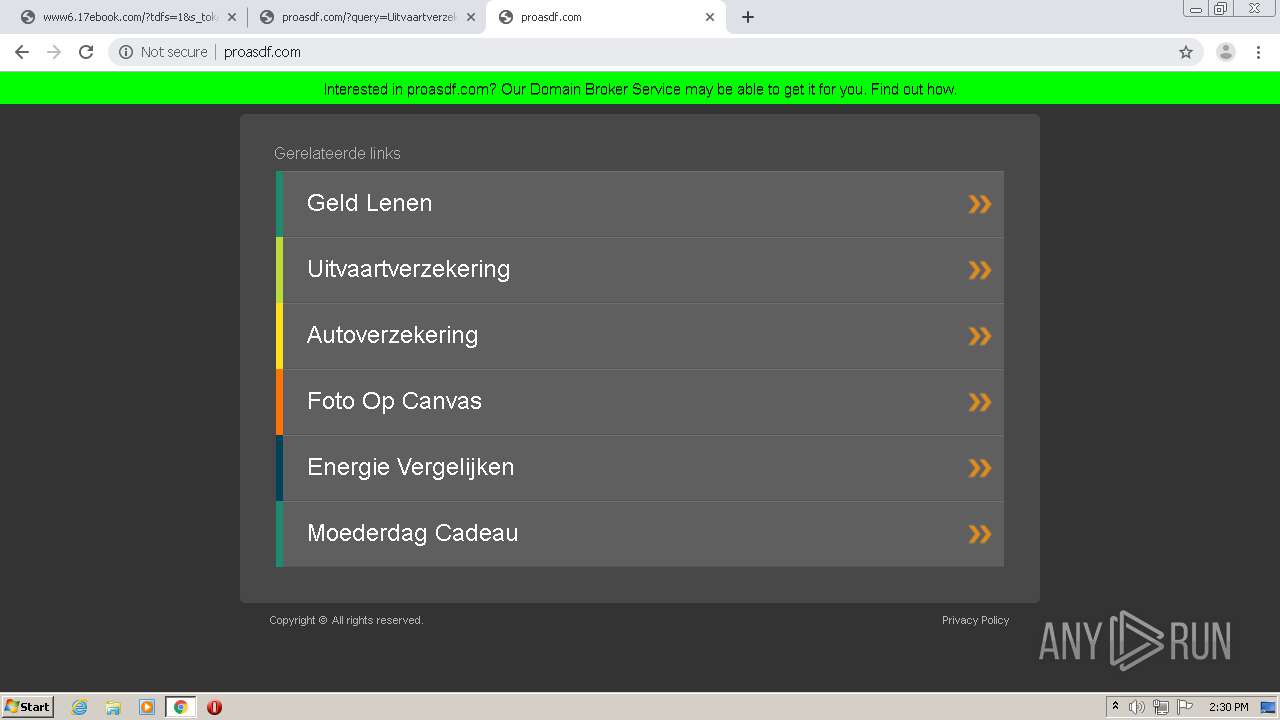
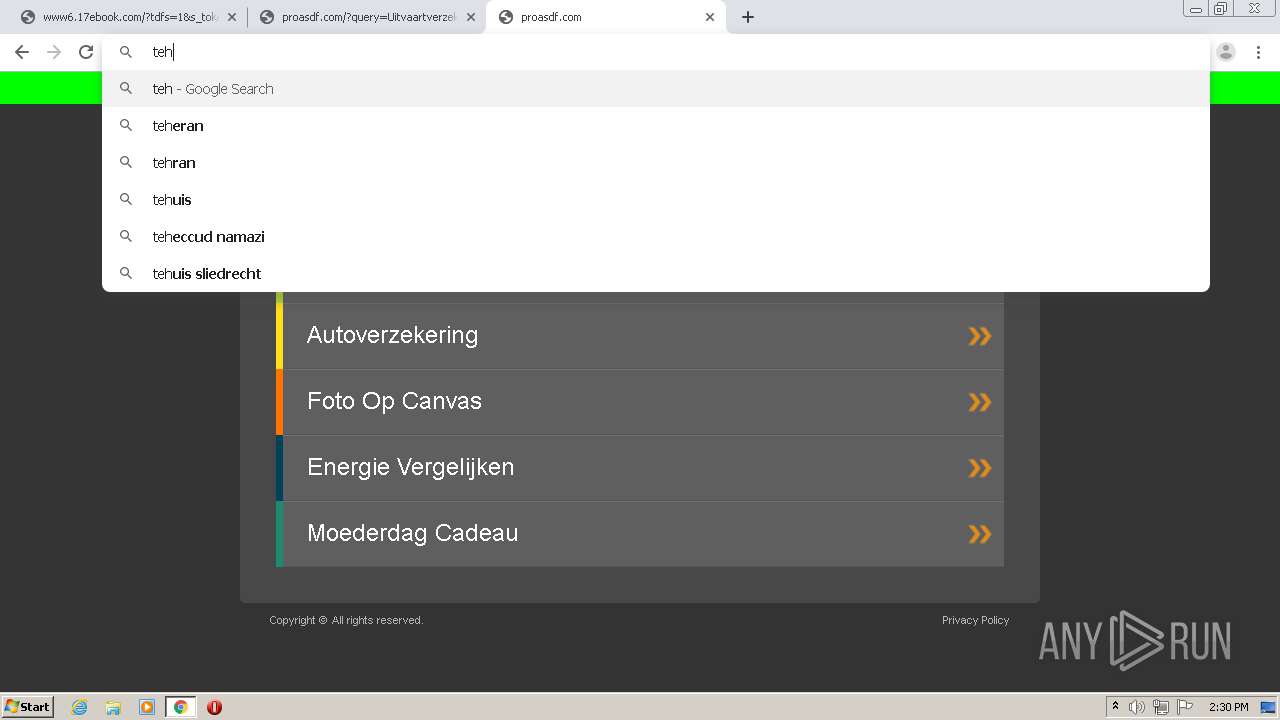
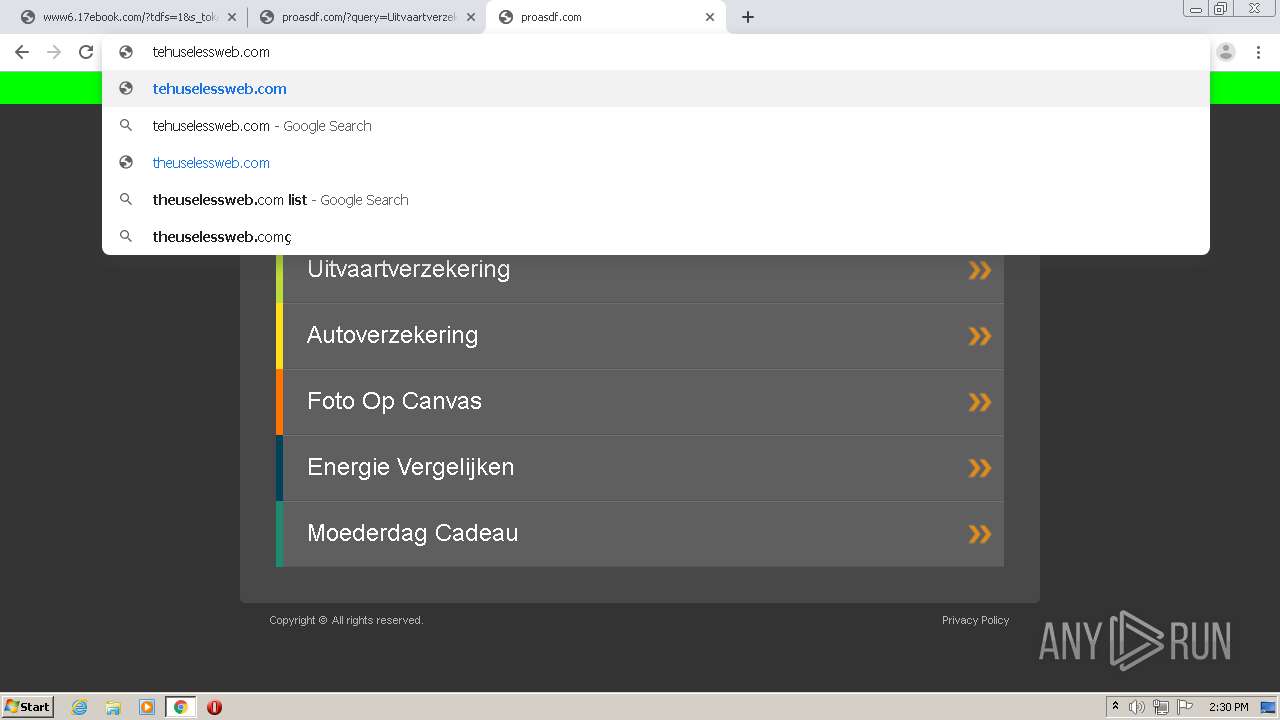
1652 | chrome.exe | GET | 200 | 35.186.238.101:80 | http://www6.17ebook.com/?tdfs=1&s_token=1594560479.0014577939&uuid=1594560479.0014577939&kw=ebook&term=Digital%20Library%20for%20Ebooks&term=Ebook%20Writing%20Services&term=Create%20an%20Ebook&backfill=0 | US | html | 800 b | whitelisted |
1652 | chrome.exe | GET | 302 | 45.55.120.157:80 | http://oc.hsicell.com/bid_oc | US | html | 287 b | whitelisted |
1652 | chrome.exe | GET | 200 | 74.125.8.140:80 | http://r6---sn-5hnednlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=45.86.201.12&mm=28&mn=sn-5hnednlk&ms=nvh&mt=1594560372&mv=m&mvi=6&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
1652 | chrome.exe | GET | 200 | 35.186.238.101:80 | http://www6.17ebook.com/?tdfs=1&s_token=1594560479.0014577939&uuid=1594560479.0014577939&kw=ebook&term=Digital%20Library%20for%20Ebooks&term=Ebook%20Writing%20Services&term=Create%20an%20Ebook&backfill=0&query=Create%20an%20Ebook&afdToken=3B1giTqGe9ie6hRT0fXXvgDqpqlM84EDrMITSmhPL1E9u_H3TJ8qO4qpgyl7L_M9hGXvxjQNLKjvzPti7vhEKjSCx3J0ZeLpS7N5xp-EUG4&pcsa=false | US | html | 800 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 96.126.123.244:80 | www.17ebook.com | Linode, LLC | US | malicious |
1652 | chrome.exe | 96.126.123.244:80 | www.17ebook.com | Linode, LLC | US | malicious |
1652 | chrome.exe | 35.186.238.101:80 | www6.17ebook.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 52.222.147.56:443 | d1hi41nc56pmug.cloudfront.net | Amazon.com, Inc. | US | unknown |
1652 | chrome.exe | 54.157.67.67:443 | api.aws.parking.godaddy.com | Amazon.com, Inc. | US | unknown |
1652 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.17ebook.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www6.17ebook.com |
| whitelisted |
www.google.com |
| malicious |
d1hi41nc56pmug.cloudfront.net |
| whitelisted |
api.aws.parking.godaddy.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
advexplore.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1652 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
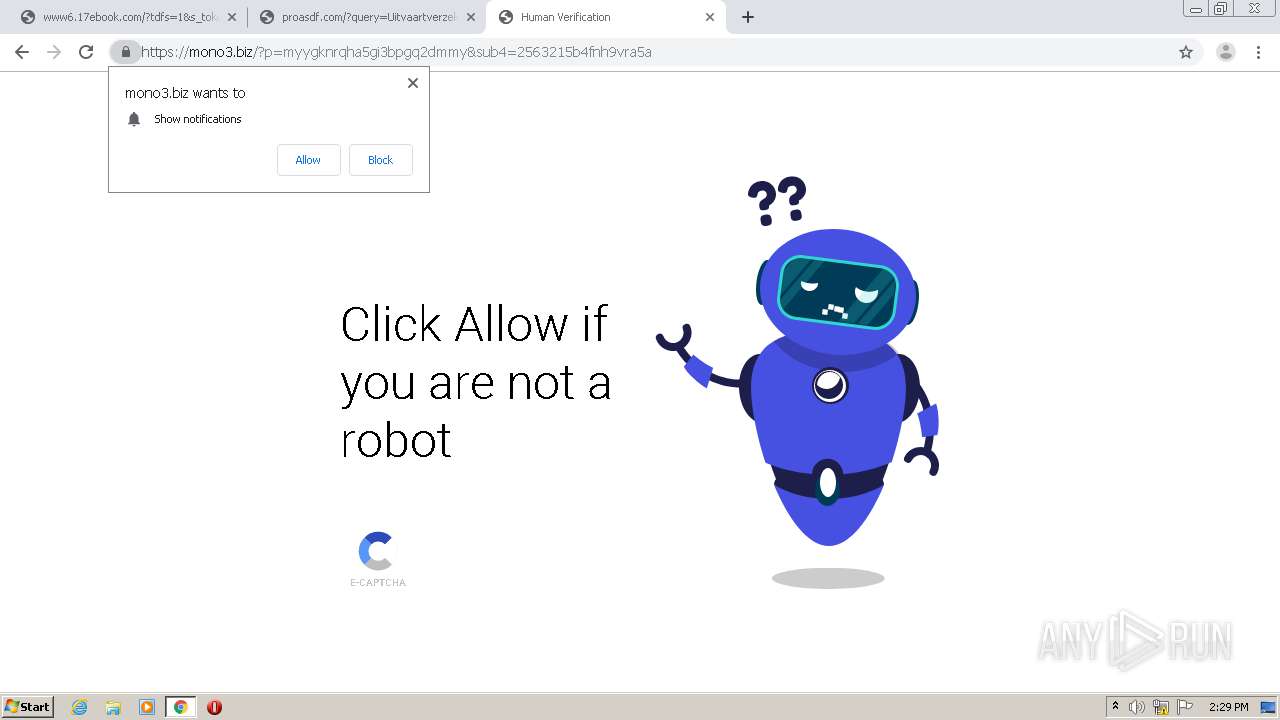
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1652 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1652 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |