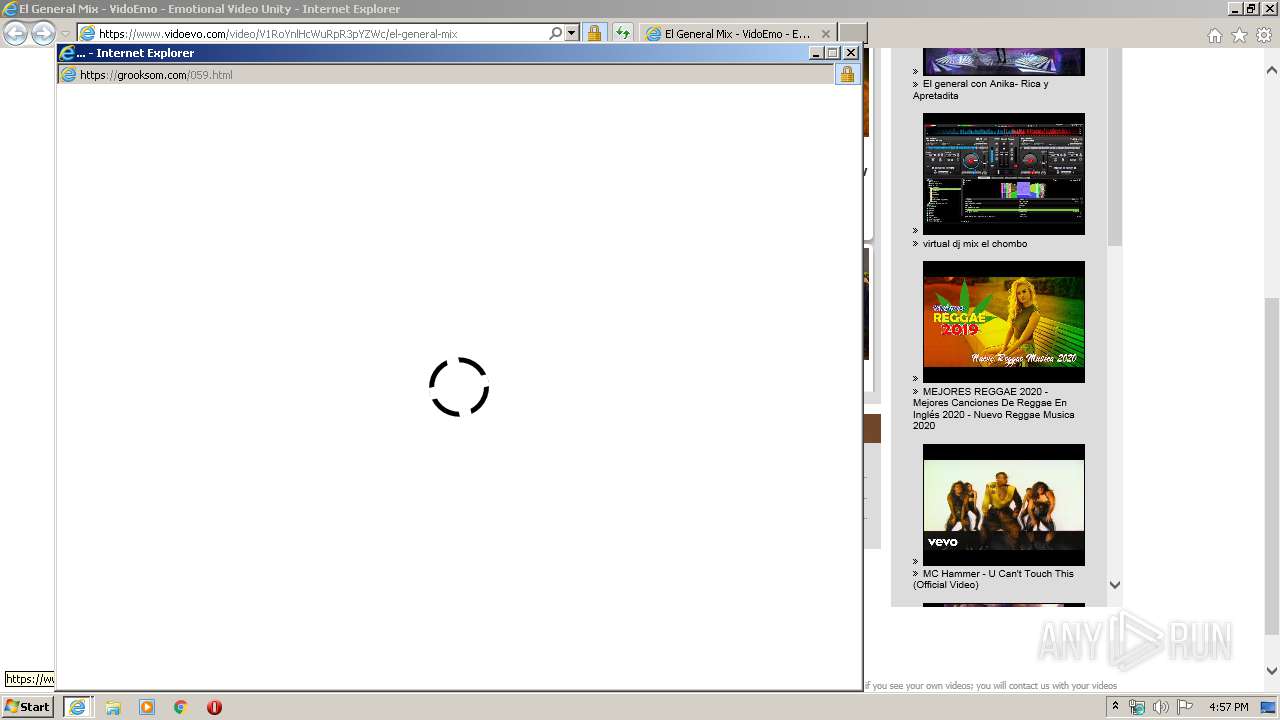
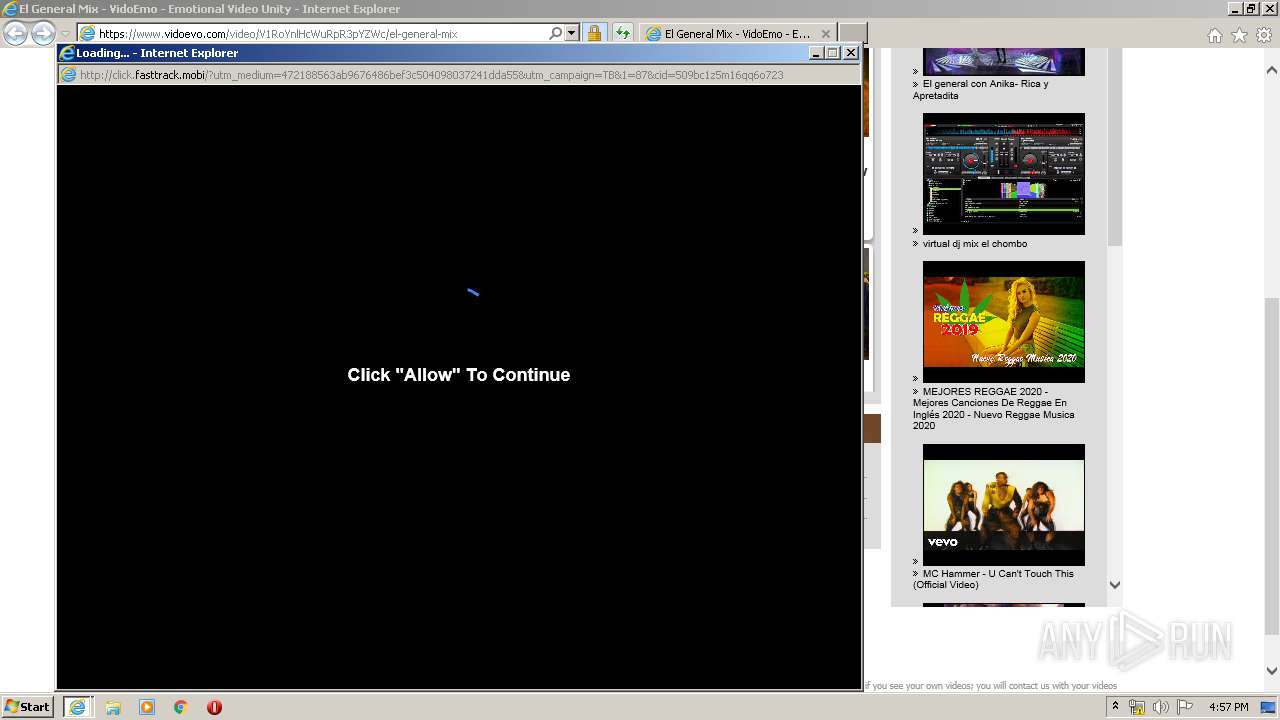
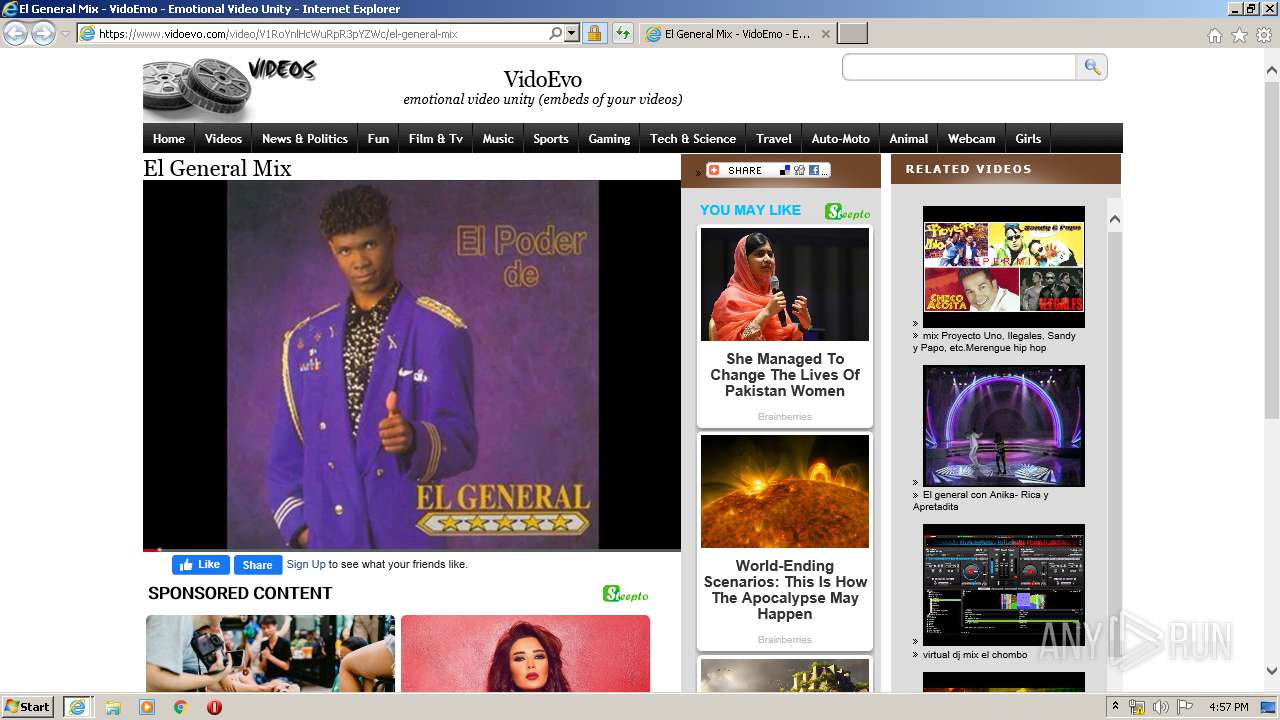
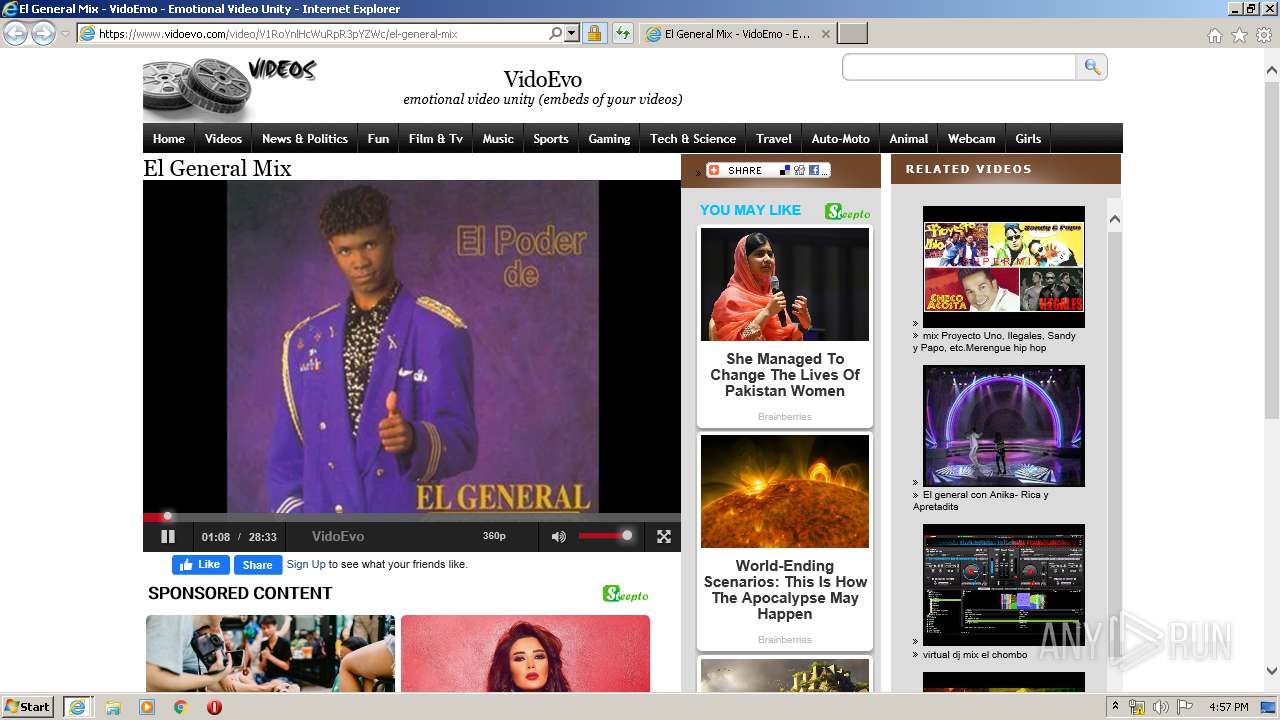
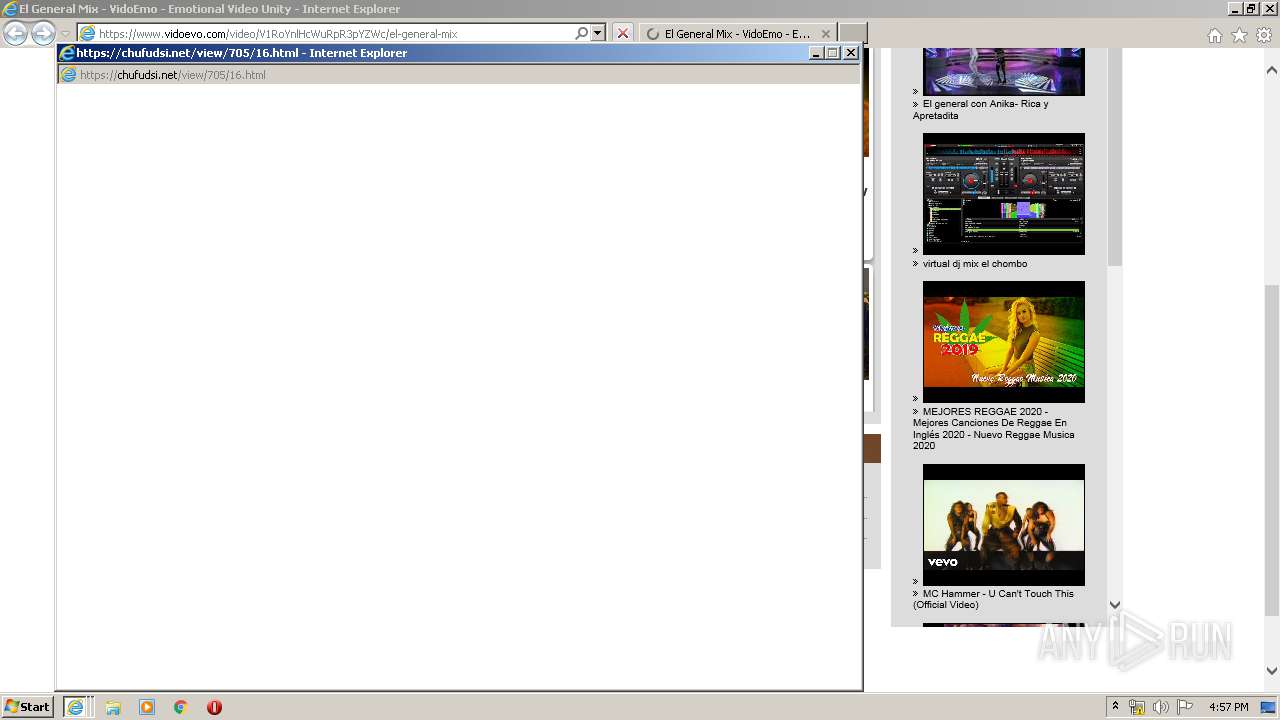
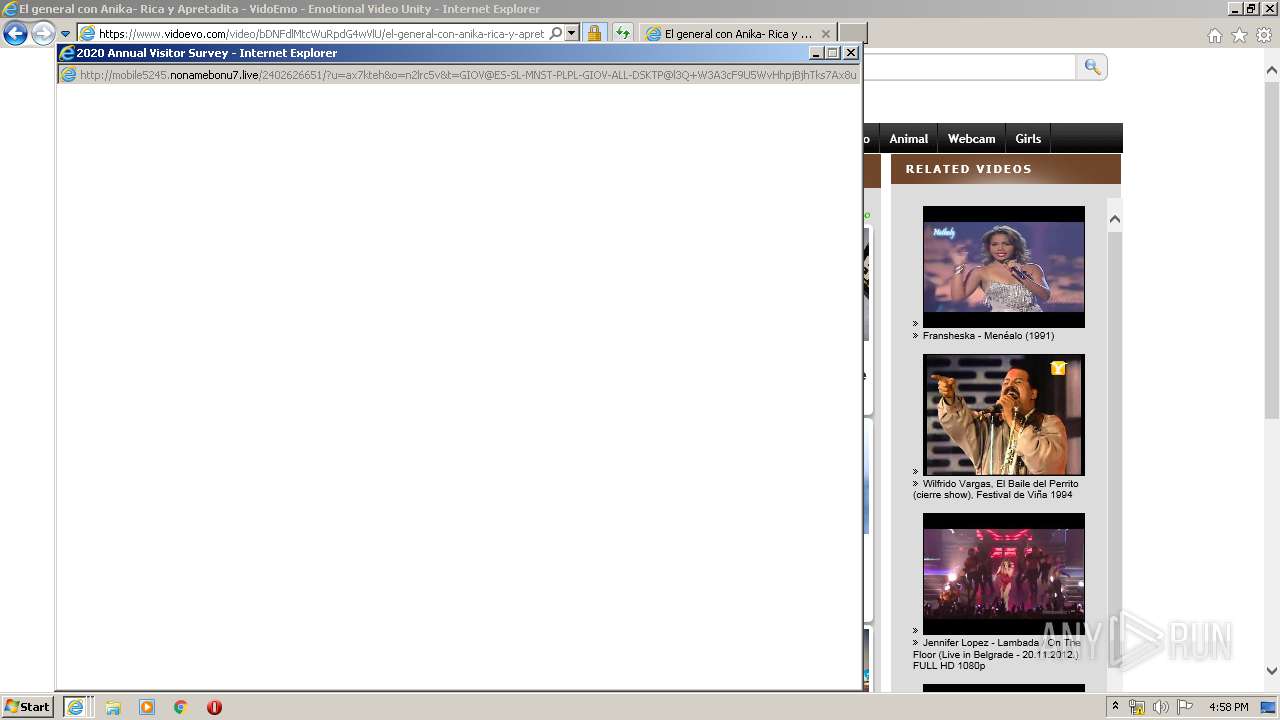
| URL: | https://www.vidoevo.com/video/V1RoYnlHcWuRpR3pYZWc/el-general-mix |
| Full analysis: | https://app.any.run/tasks/df702dac-a270-45ff-a259-1611ea78061b |
| Verdict: | No threats detected |
| Analysis date: | January 22, 2020, 16:55:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7EF38D541A602A4F07CE121C9E66FA61 |
| SHA1: | 832F9C3F6E7FE06BC095D63FEB74A5E384D35028 |
| SHA256: | F019C8884ECB7B2320191CE8579A000550A6086EC2CA6DC27320B1DC84C06505 |
| SSDEEP: | 3:N8DSLABKtyGJKK69X4yvu9n:2OLAA8Jvu9n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 2372)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 2076)
Reads Internet Cache Settings
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2160)
Creates files in the user directory
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 2076)
Changes internet zones settings
- iexplore.exe (PID: 2072)
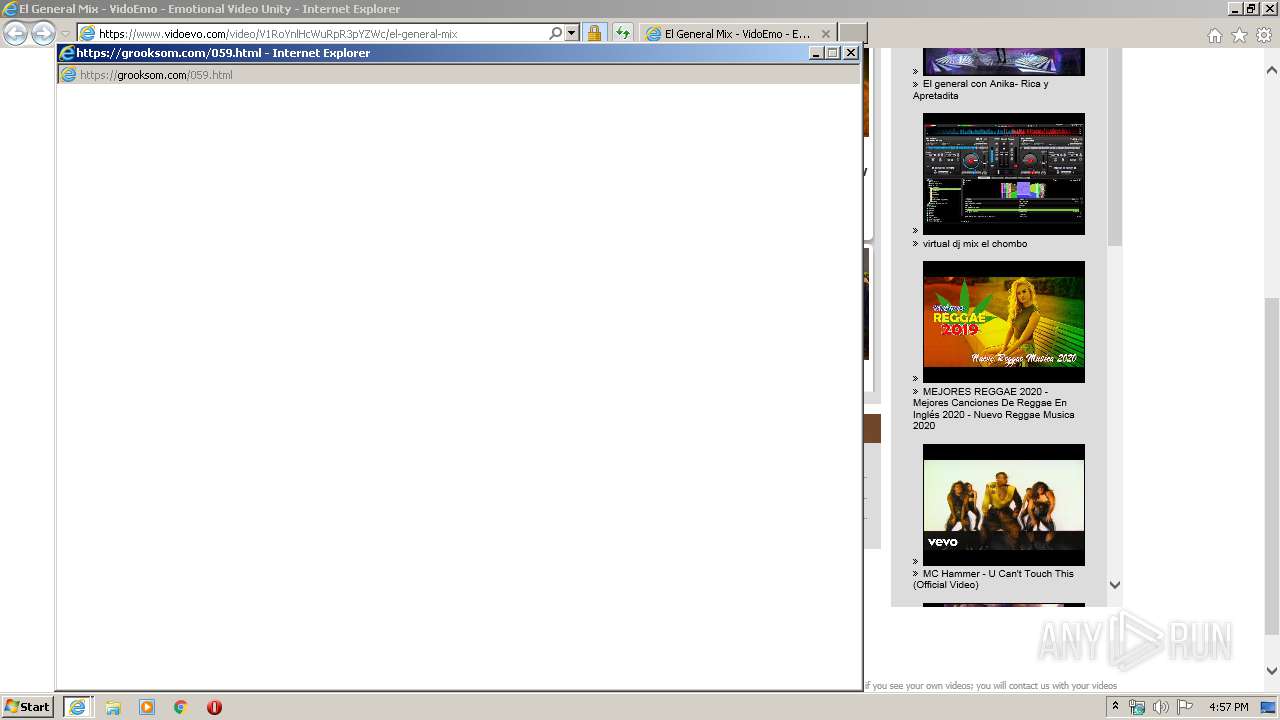
Application launched itself
- iexplore.exe (PID: 2072)
Reads internet explorer settings
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 2160)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2072)
Changes settings of System certificates
- iexplore.exe (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2072 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.vidoevo.com/video/V1RoYnlHcWuRpR3pYZWc/el-general-mix" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2072 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2072 CREDAT:4003098 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2072 CREDAT:791857 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 631
Read events
767
Write events
859
Delete events
5
Modification events
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3939328524 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30789956 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A0000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
149
Text files
420
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab79B6.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar79B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1161MORM.txt | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\el-general-mix[1].htm | html | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\default[1].css | text | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\main[1].js | text | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\load[1].htm | text | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_77982F76455B0F98176BAD53B06DE37B | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
99
TCP/UDP connections
261
DNS requests
87
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.62 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAkRQiJ2RmHfAgAAAABSqWE%3D | US | der | 471 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.66 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAeXhvdrjnvIccwlWly2%2FQg%3D | US | der | 471 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
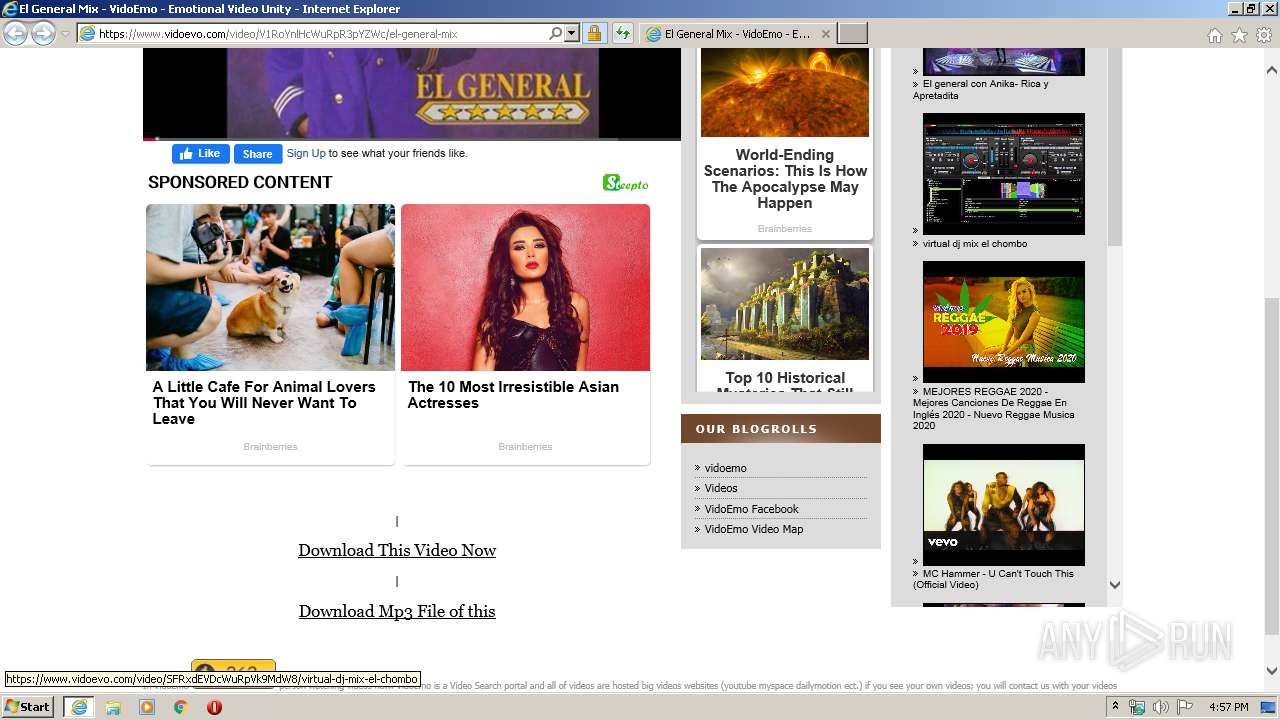
2076 | iexplore.exe | 104.26.7.223:443 | www.vidoevo.com | Cloudflare Inc | US | suspicious |
2076 | iexplore.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2076 | iexplore.exe | 2.21.36.164:443 | s7.addthis.com | GTT Communications Inc. | FR | suspicious |
2076 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
2076 | iexplore.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2076 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
2076 | iexplore.exe | 92.122.255.233:443 | z.moatads.com | GTT Communications Inc. | — | suspicious |
2076 | iexplore.exe | 188.42.162.187:443 | go.oclaserver.com | Webzilla B.V. | NL | unknown |
2076 | iexplore.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.vidoevo.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
videothumb.vidoevo.com |
| suspicious |
s7.addthis.com |
| whitelisted |
whos.amung.us |
| whitelisted |
mc.yandex.ru |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
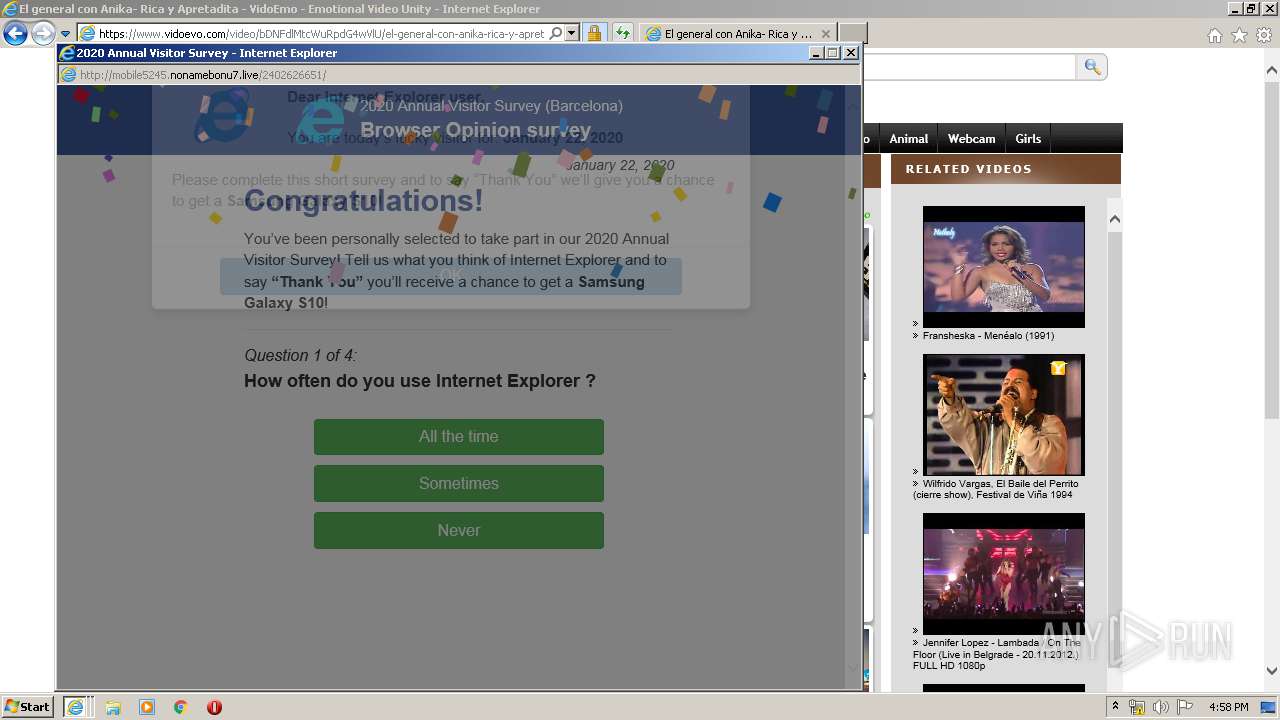
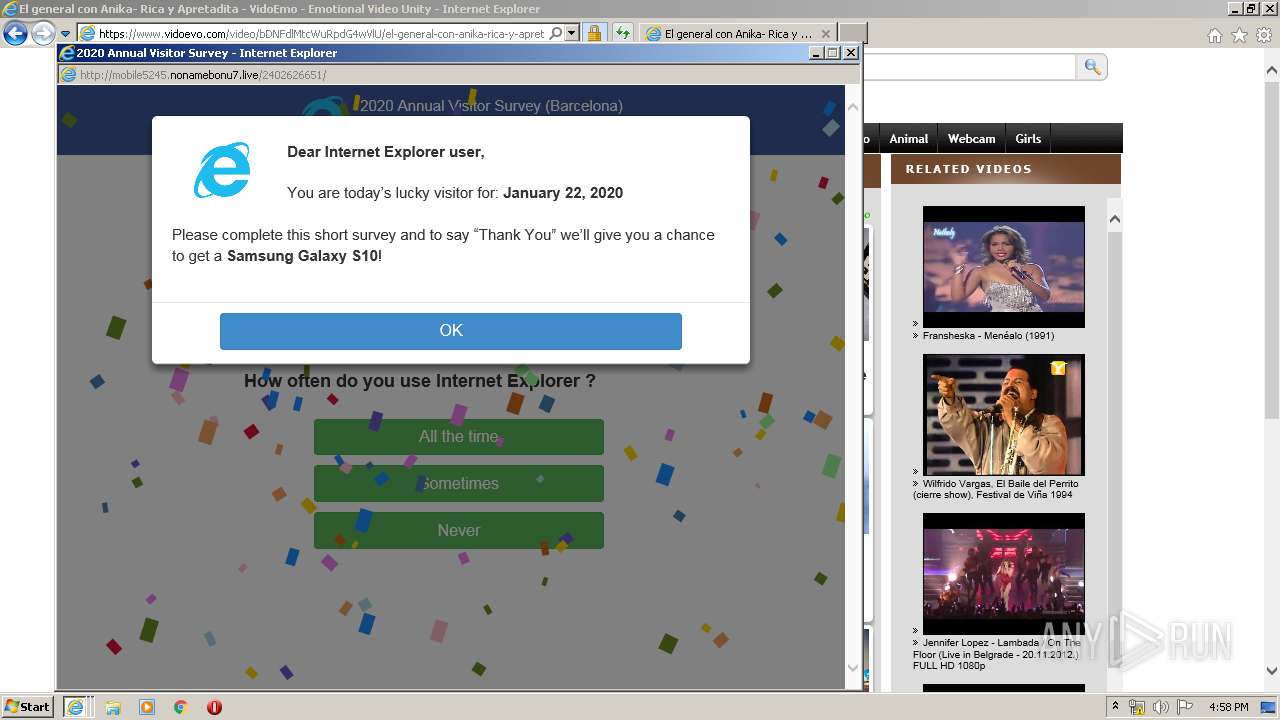
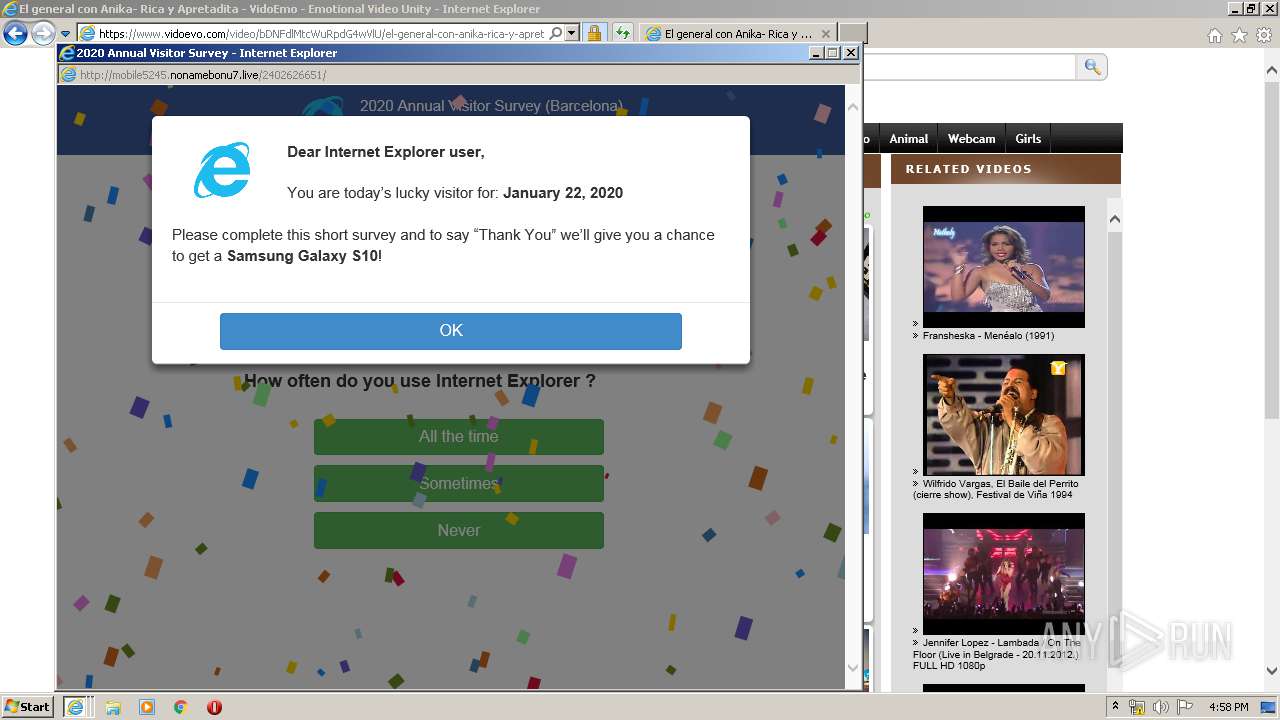
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1 ETPRO signatures available at the full report