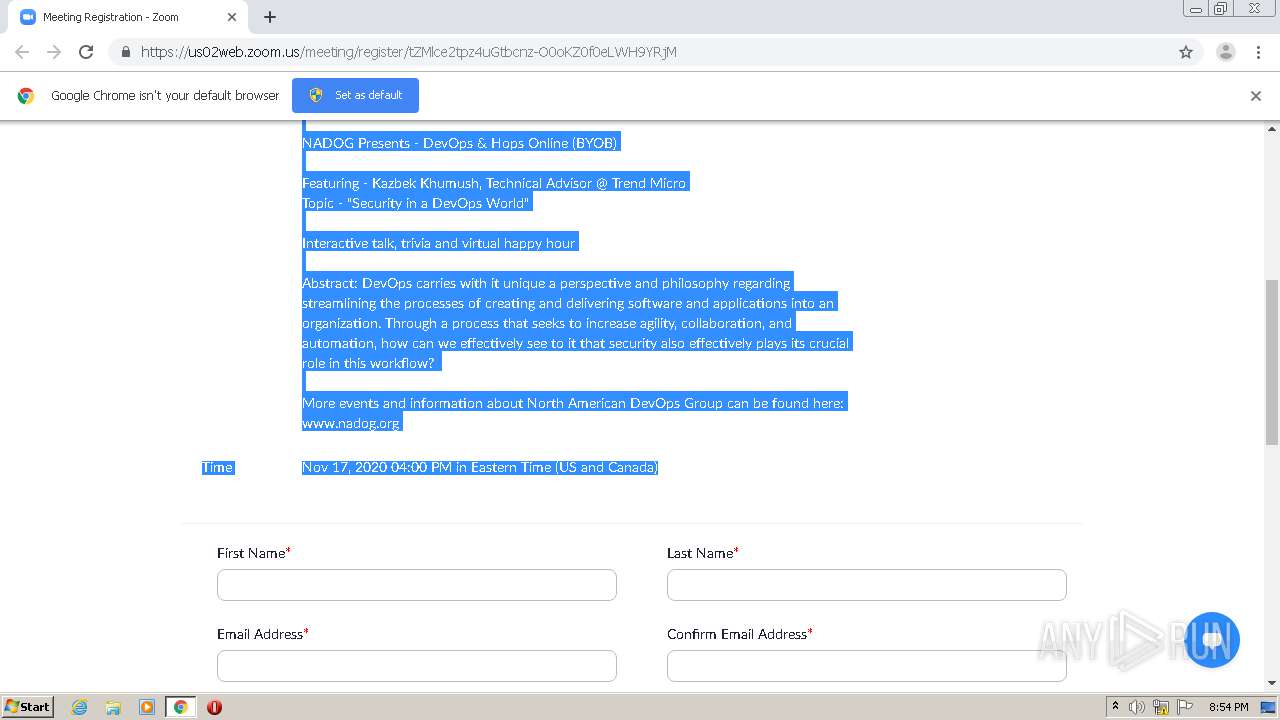
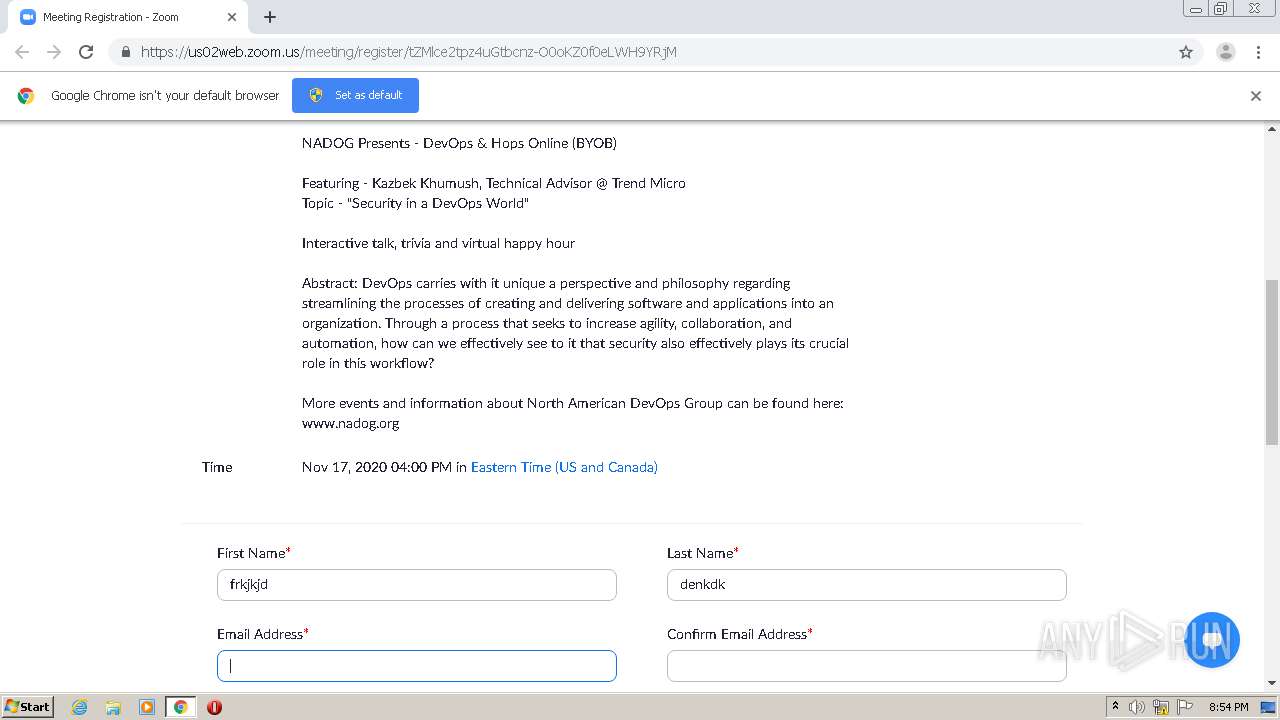
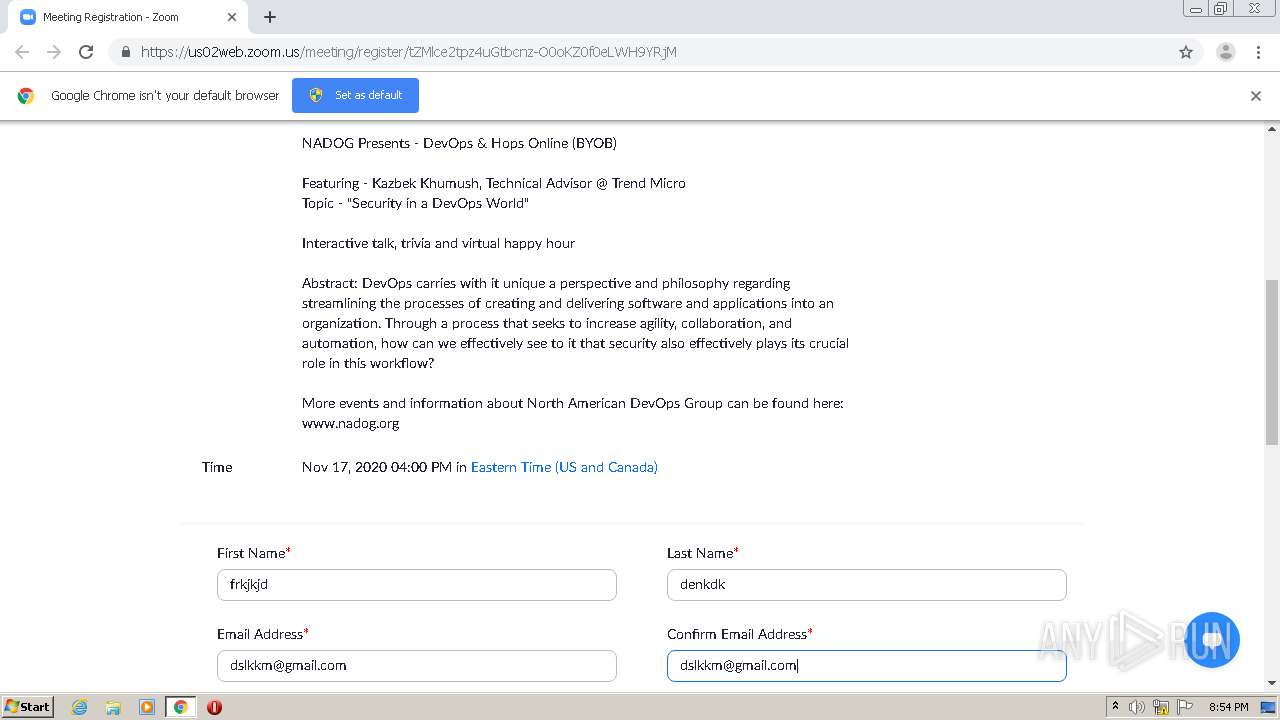
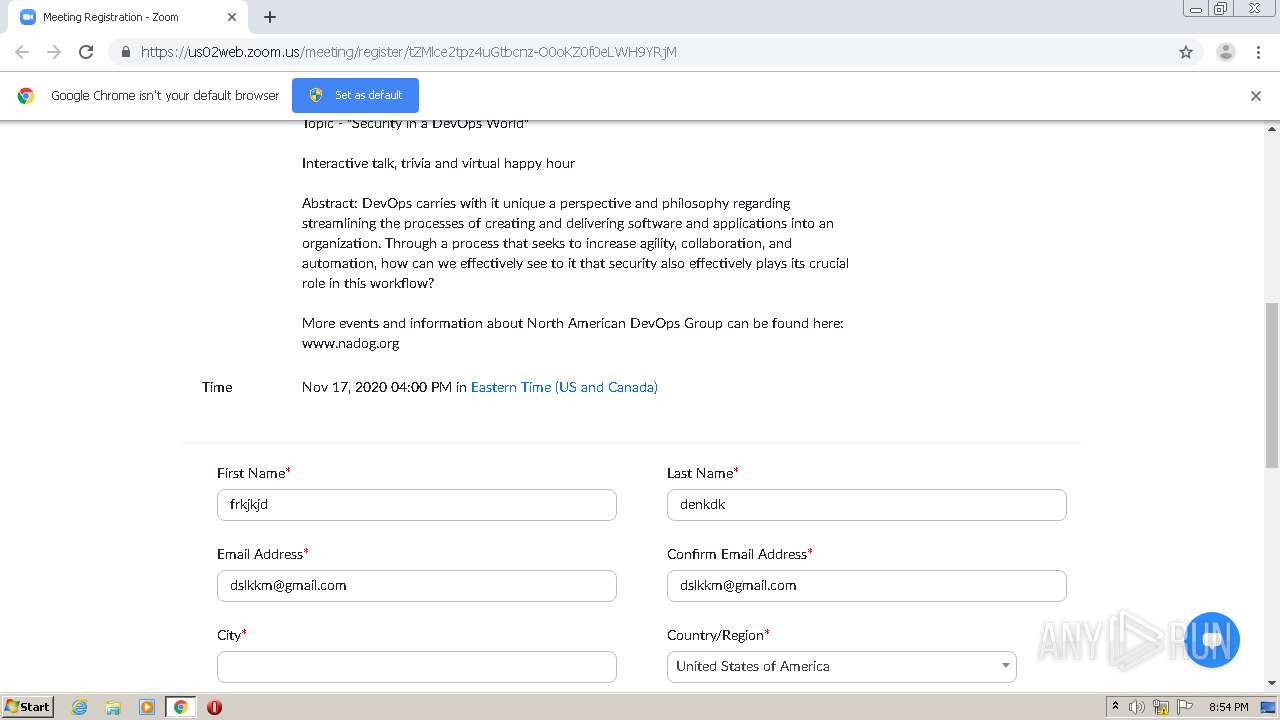
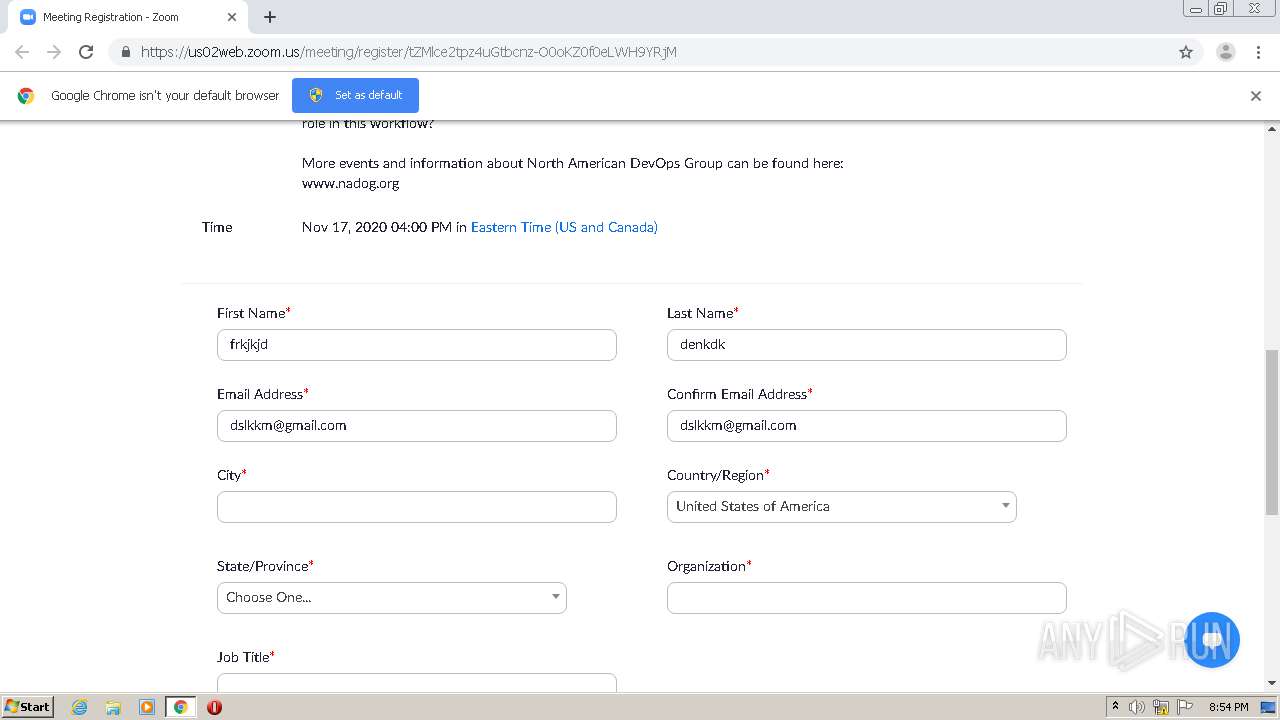
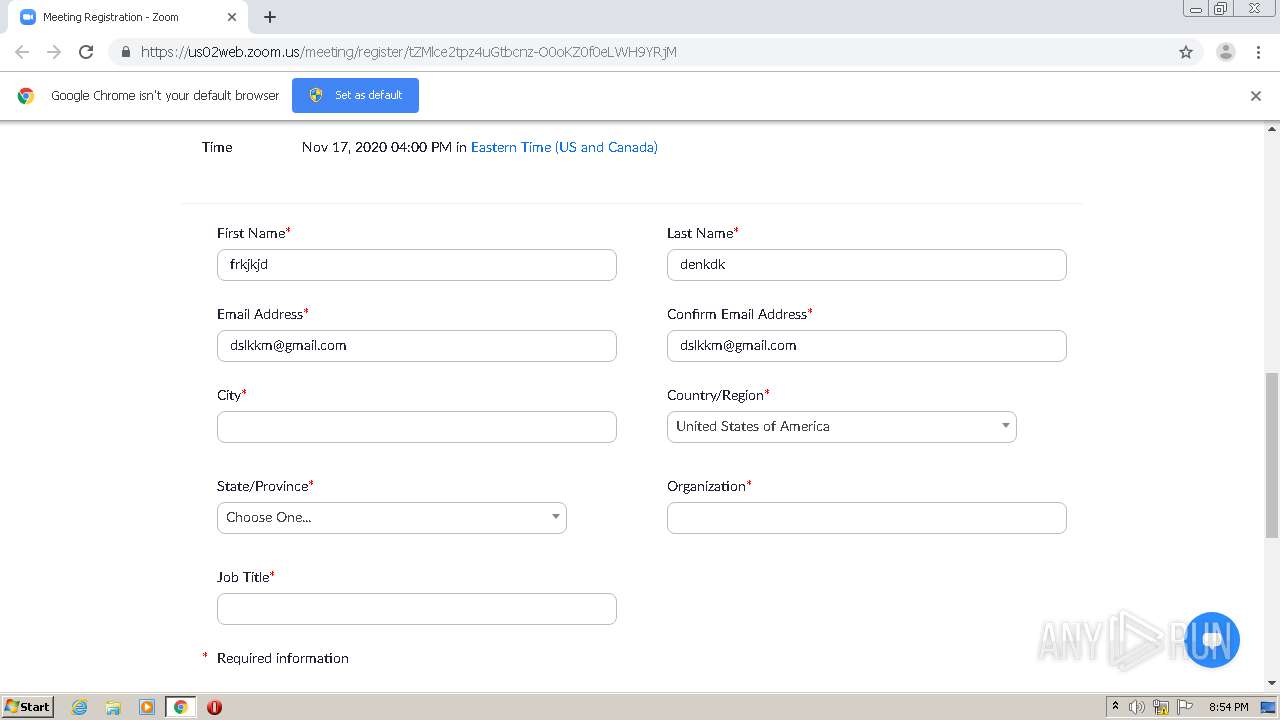
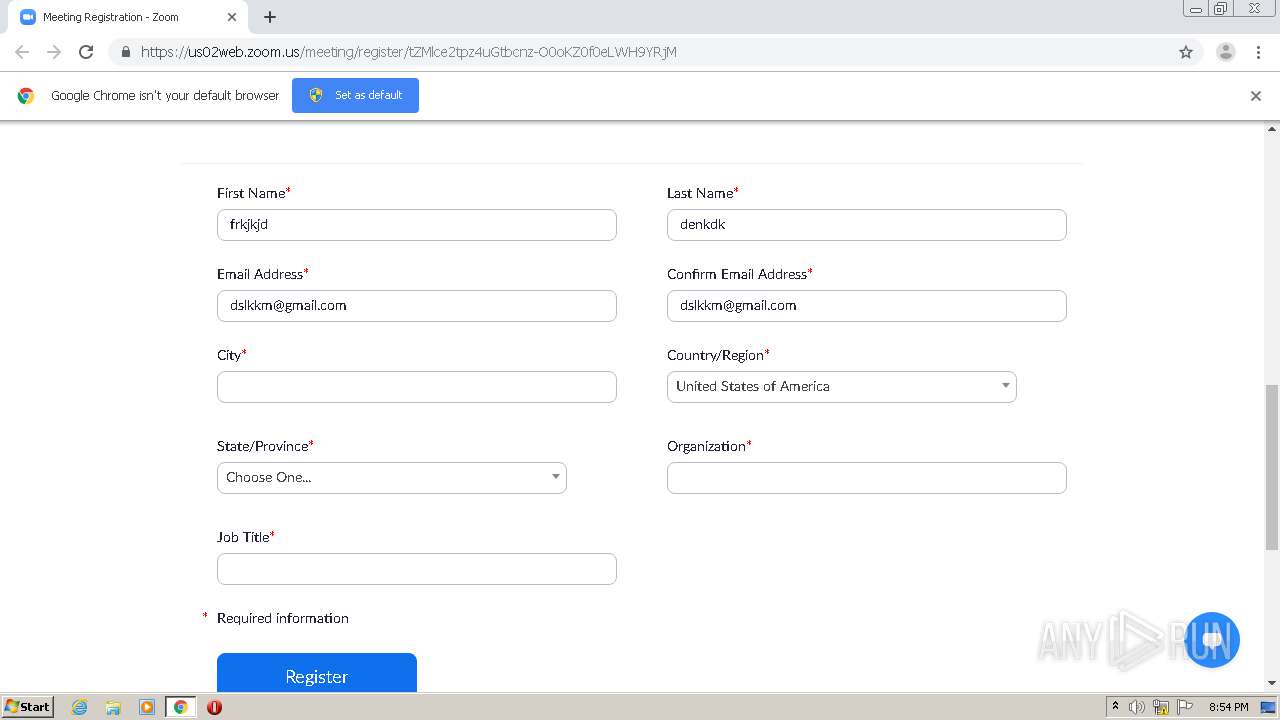
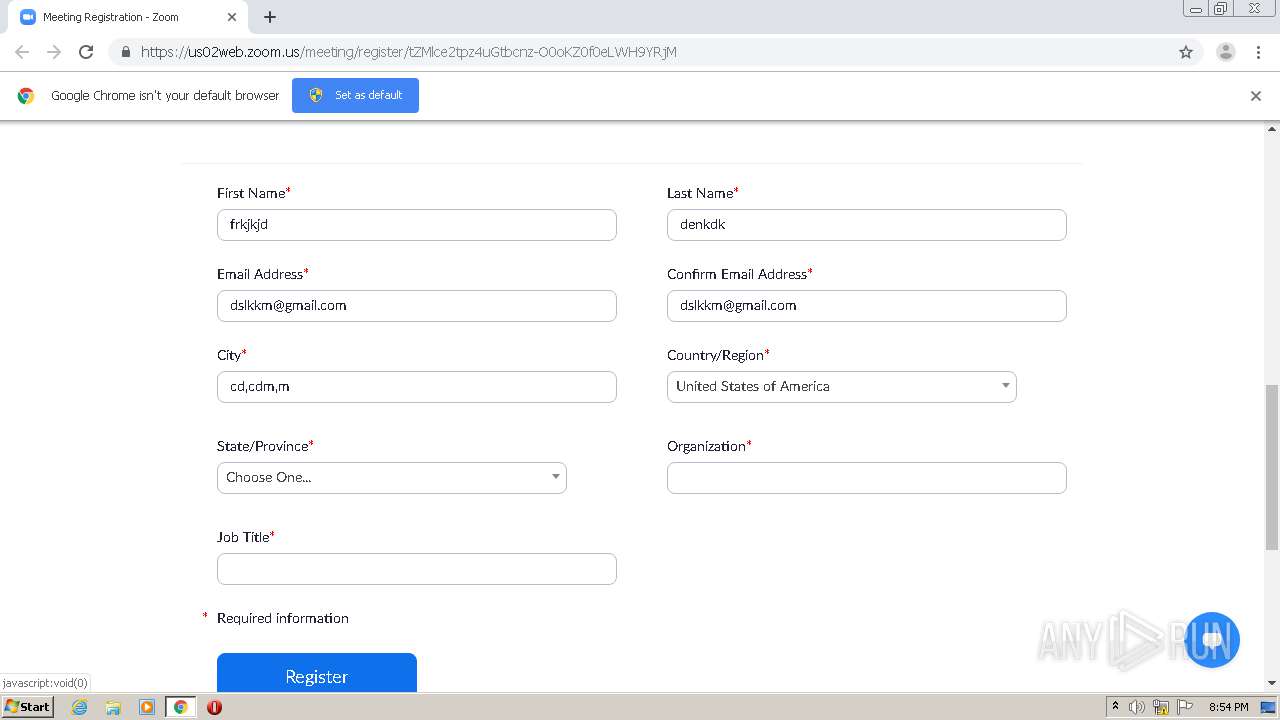
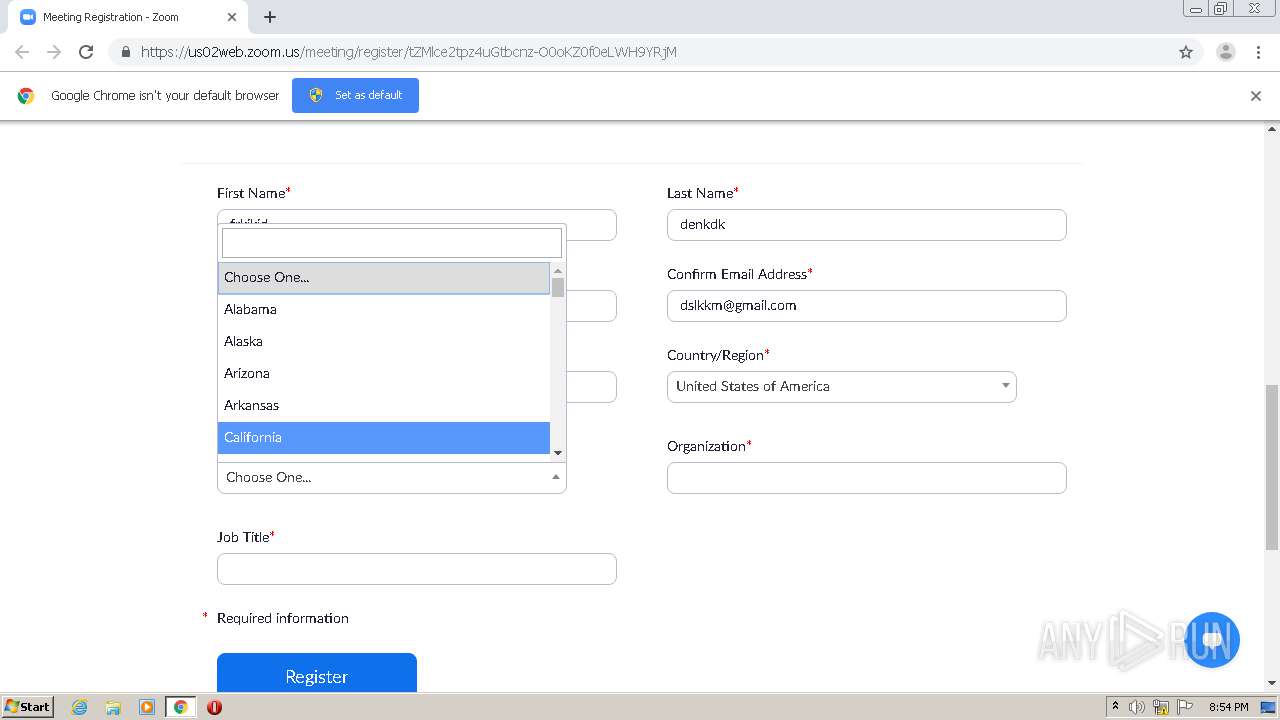
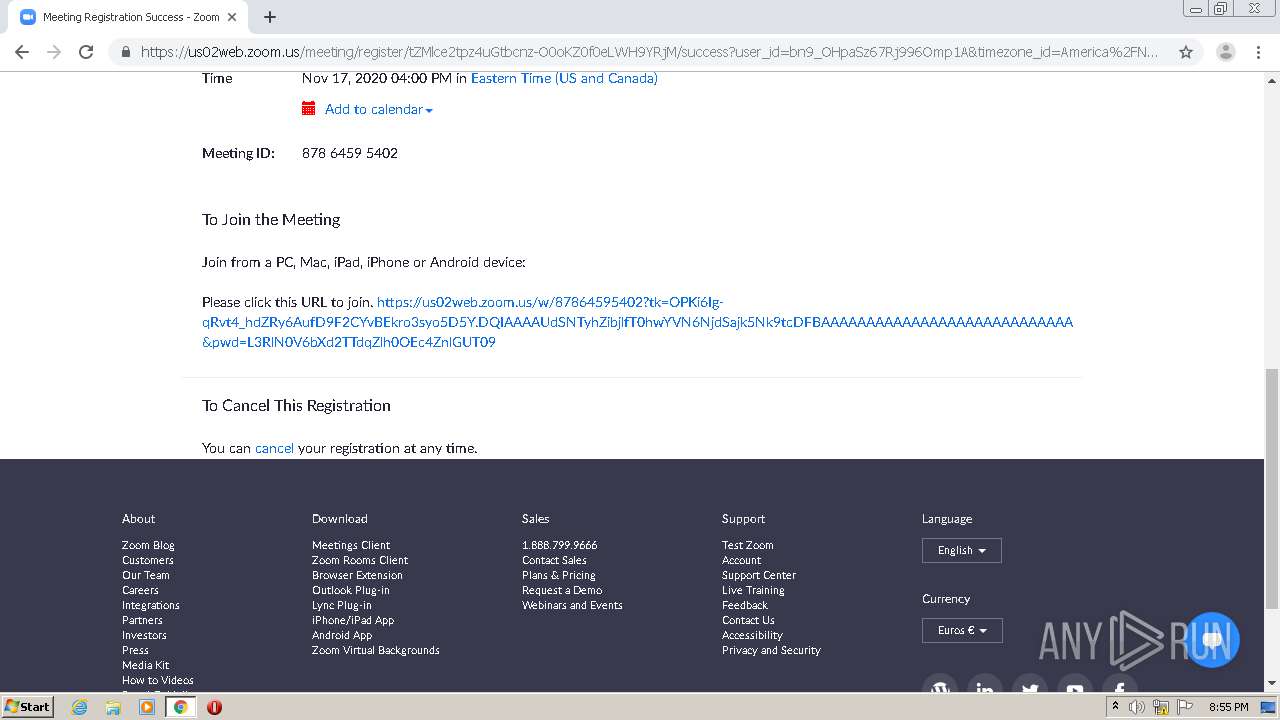
| URL: | https://us02web.zoom.us/meeting/register/tZMlce2tpz4uGtbcnz-O0oKZ0f0eLWH9YRjM |
| Full analysis: | https://app.any.run/tasks/4da8012a-9698-4faf-9fa8-a8a9eab62c94 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2020, 20:53:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CF1DF0793380E1EC1EF17536A5D93133 |
| SHA1: | 83EF91DAD1543E1CA948AAD73F438CD290B94DCC |
| SHA256: | EFE9603AC299A5DDB67DAD9DC447E19A6CECFD2CE04B766C7947A40DAA8CAA27 |
| SSDEEP: | 3:N8eoiKILQNiqC3KpABVNRqggG5n:2eop9fC3PjDD5 |
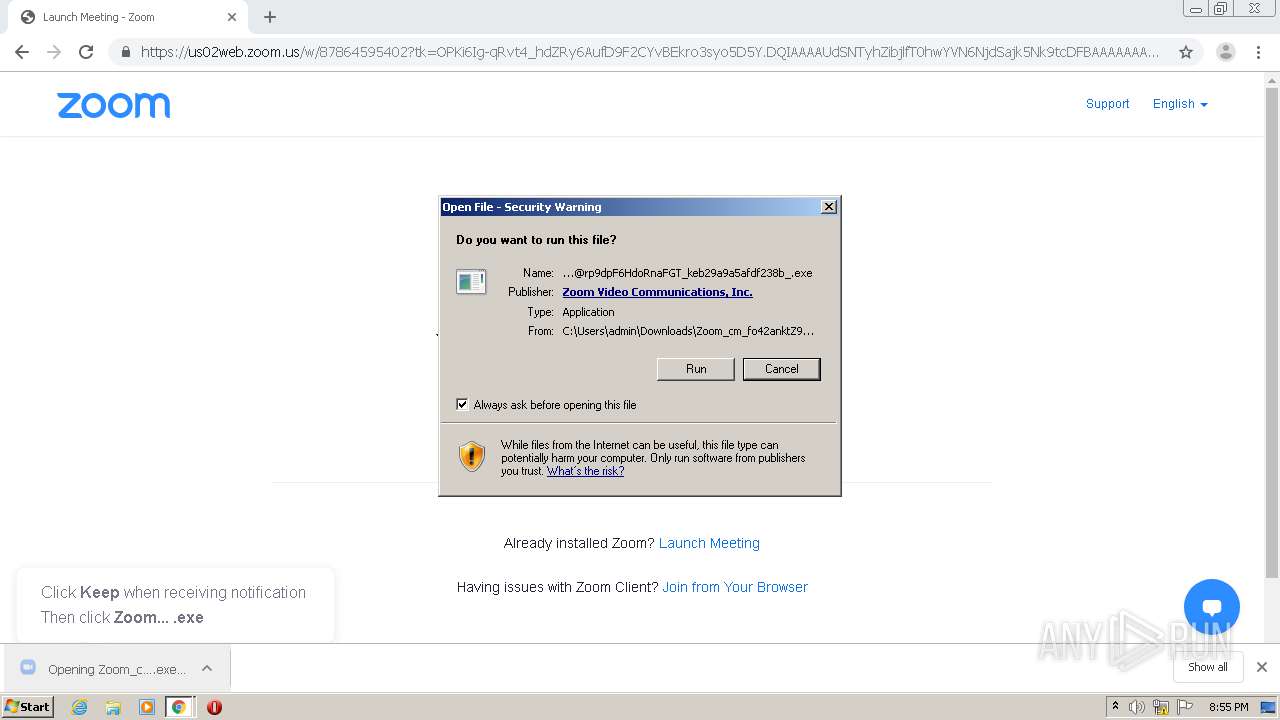
MALICIOUS
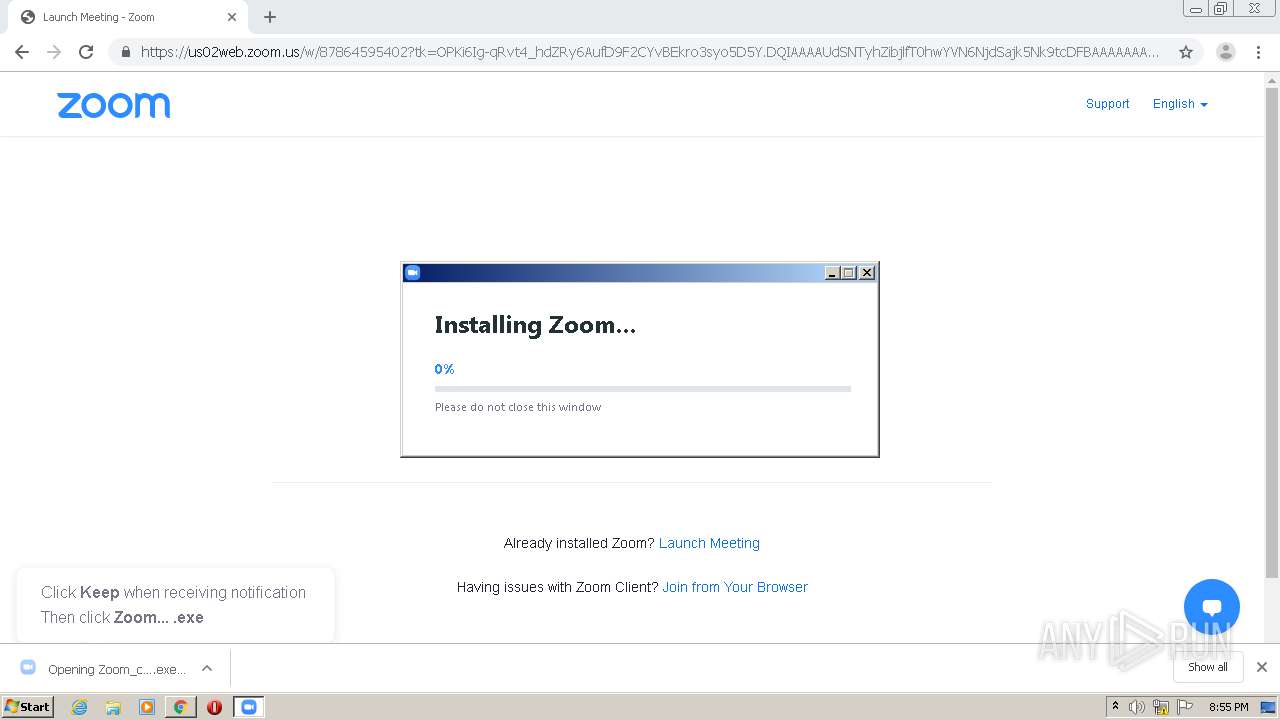
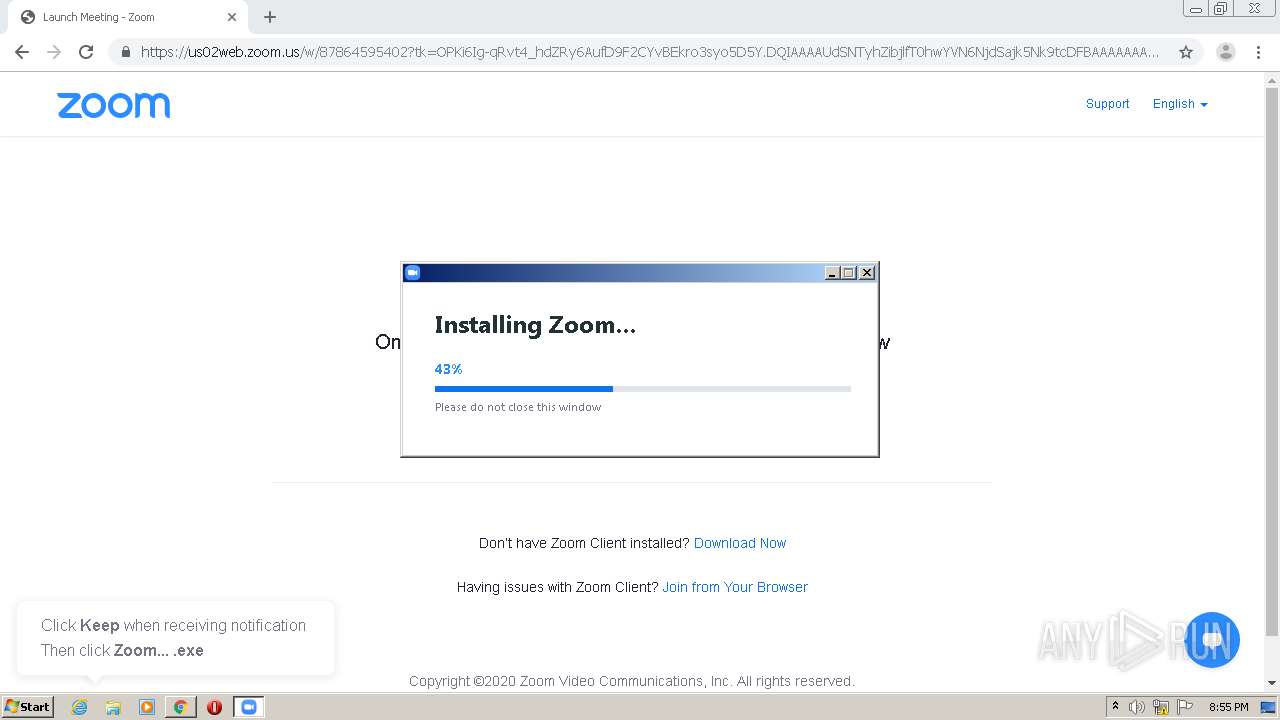
Application was dropped or rewritten from another process
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
- Installer.exe (PID: 3732)
- Installer.exe (PID: 2012)
- zm4249.tmp (PID: 3432)
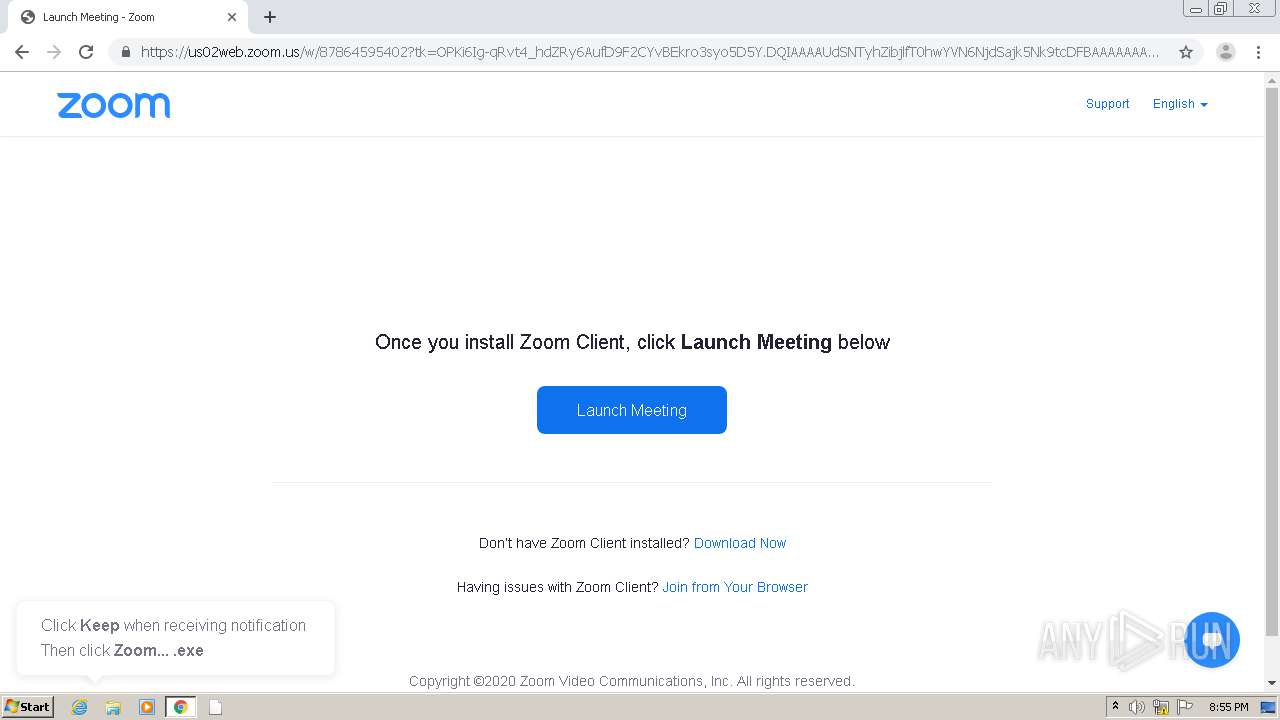
- Zoom.exe (PID: 3204)
- Zoom.exe (PID: 956)
- Zoom.exe (PID: 2852)
- Zoom.exe (PID: 676)
Changes settings of System certificates
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Loads dropped or rewritten executable
- Installer.exe (PID: 2012)
- Zoom.exe (PID: 676)
- Zoom.exe (PID: 956)
- Zoom.exe (PID: 3204)
- Zoom.exe (PID: 2852)
SUSPICIOUS
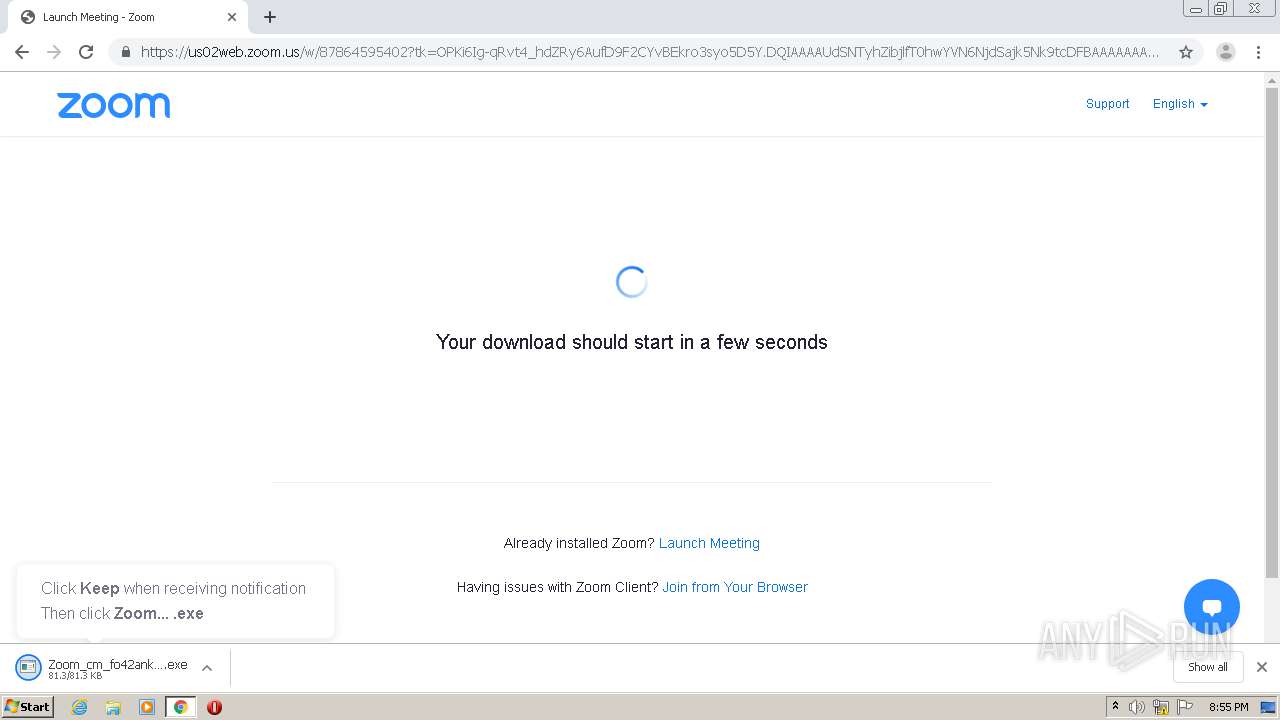
Executable content was dropped or overwritten
- chrome.exe (PID: 2560)
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
- Installer.exe (PID: 2012)
Reads Internet Cache Settings
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Creates files in the user directory
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
- Zoom.exe (PID: 956)
- Zoom.exe (PID: 676)
- Installer.exe (PID: 2012)
- Zoom.exe (PID: 2852)
Adds / modifies Windows certificates
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Application launched itself
- Installer.exe (PID: 2012)
- Zoom.exe (PID: 956)
Creates a software uninstall entry
- Installer.exe (PID: 2012)
Starts itself from another location
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Starts application with an unusual extension
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 2012)
Modifies the open verb of a shell class
- Installer.exe (PID: 2012)
INFO
Reads the hosts file
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1092)
Application launched itself
- chrome.exe (PID: 2560)
Reads settings of System Certificates
- chrome.exe (PID: 2560)
- Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe (PID: 3160)
Reads Internet Cache Settings
- chrome.exe (PID: 2560)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
24
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe --action=join --runaszvideo=TRUE | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,4,58891,1115 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=764739435456965912 --mojo-platform-channel-handle=1068 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" "--url=zoommtg://win.launch?h.domain=us02web.zoom.us&h.path=join&confid=dXNzPUZGaFRzQUV3TVNGSzgxbTRmMEgwNDBjdExrODhHdzBVSldIUWh5YnU1c2JVRFFJZnhHQ1JVNzlYUm94SkFYOHhCaXJIWjZXUnVWaGpwazBnWkpmZThmNkFfS3MuVHF3ckpHWnVLd1hMaHpVQyZ0aWQ9ZDZhOGY2YWE3NTA3NDdiZTk5Mjg0OTYwNjAwMzE0MTE%3D&mcv=0.92.11227.0929&stype=0&zc=0&tk=OPKi6Ig-qRvt4_hdZRy6AufD9F2CYvBEkro3syo5D5Y.DQIAAAAUdSNTyhZibjlfT0hwYVN6NjdSajk5Nk9tcDFBAAAAAAAAAAAAAAAAAAAAAAAAAAAA&browser=chrome&action=join&confno=87864595402&pwd=L3RlN0V6bXd2TTdqZlh0OEc4ZnlGUT09" | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,4,58891,1115 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15618412224052519274 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2020644579886916849 --mojo-platform-channel-handle=2400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16624580848056229410 --mojo-platform-channel-handle=1452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7401096364706873679 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10180700544525727073 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10755418267529914698,12775901546742594942,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15621465758721622439 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2012 | "C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe" ZInstaller --conf.mode=silent --ipc_wnd=131438 | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe | Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Installer Exit code: 0 Version: 5,4,58891,1115 Modules
| |||||||||||||||
Total events
2 348
Read events
2 143
Write events
197
Delete events
8
Modification events
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2632) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2560-13250033622939875 |
Value: 259 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
155
Suspicious files
83
Text files
140
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FB2E6D7-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e6e5918d-ae07-43cd-bd8c-a7c90f12089a.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1282f3.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1282f3.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF128610.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
40
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3160 | Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe | GET | 200 | 23.46.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3160 | Zoom_cm_fo42anktZ9vvrZo4_mhzipfPVlkXPeHj+vgbXP5nOIA-v8fBl4+SOW@rp9dpF6HdoRnaFGT_keb29a9a5afdf238b_.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1092 | chrome.exe | 99.86.2.87:443 | us02st1.zoom.us | AT&T Services, Inc. | US | malicious |
1092 | chrome.exe | 99.86.2.98:443 | us02st1.zoom.us | AT&T Services, Inc. | US | suspicious |
1092 | chrome.exe | 216.58.198.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1092 | chrome.exe | 143.204.201.84:443 | static.ada.support | — | US | malicious |
1092 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1092 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
1092 | chrome.exe | 143.204.201.29:443 | rollout.ada.support | — | US | unknown |
1092 | chrome.exe | 143.204.201.108:443 | zoom.ada.support | — | US | malicious |
1092 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1092 | chrome.exe | 13.224.195.211:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
us02web.zoom.us |
| whitelisted |
accounts.google.com |
| shared |
us02st1.zoom.us |
| shared |
us02st3.zoom.us |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
us02st2.zoom.us |
| shared |
static.ada.support |
| whitelisted |
clients1.google.com |
| whitelisted |
rollout.ada.support |
| shared |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | |
Installer.exe | [CZoomProductPathHelper::RecursiveRemoveDirA] Path is: |