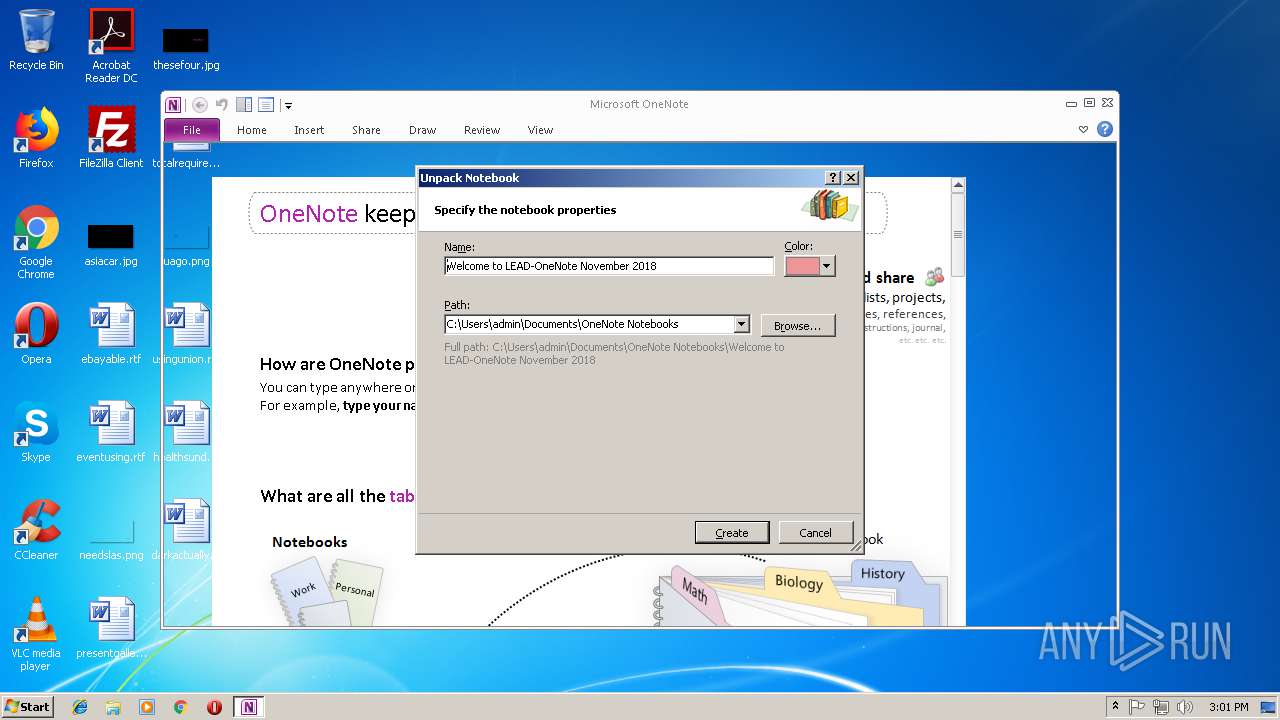
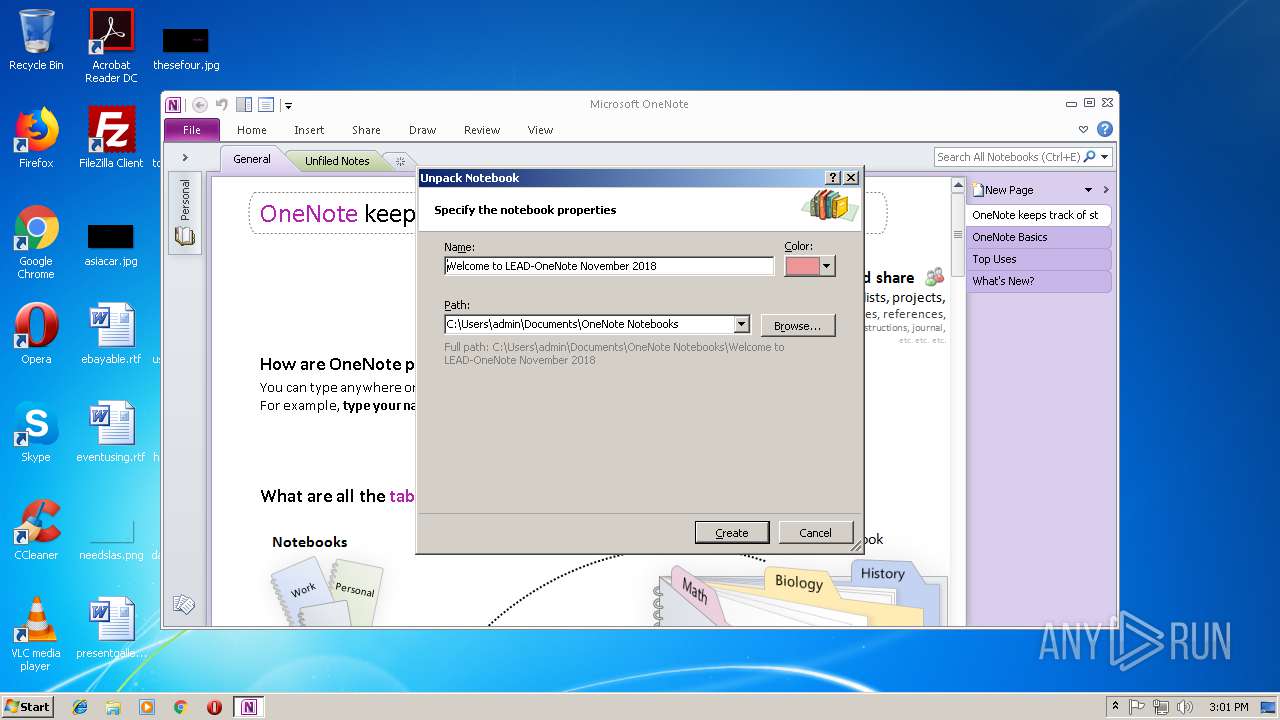
| File name: | Welcome to LEAD-OneNote November 2018.onepkg |
| Full analysis: | https://app.any.run/tasks/5a68bc5e-f526-4c7c-b204-8ff0db586c93 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 15:00:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, 12018417 bytes, 6 files |
| MD5: | C5F5DBB04D92BABE1C4E31BDCC0488A5 |
| SHA1: | 5884FD6A66ECC1FC7CE8B739D604F812DAE9F8ED |
| SHA256: | EFE47A7B5DBC857278BE2E06EA1E0BFA46CD02DC07EF832DA7BE1B8A6B0F8942 |
| SSDEEP: | 196608:3bGfht1S6tEY2ZSh8ZC/MgDDHJoTvMFwZARIpM1+ObfQFWdl4U:36fn1ZEY2ZShhMGiTAwIz1JfQk/ |
MALICIOUS
Unusual execution from Microsoft Office
- ONENOTE.EXE (PID: 3204)
Writes to a start menu file
- ONENOTE.EXE (PID: 3204)
SUSPICIOUS
Starts Microsoft Office Application
- ONENOTE.EXE (PID: 3204)
Reads internet explorer settings
- ONENOTE.EXE (PID: 3204)
Unusual connect from Microsoft Office
- ONENOTE.EXE (PID: 3204)
INFO
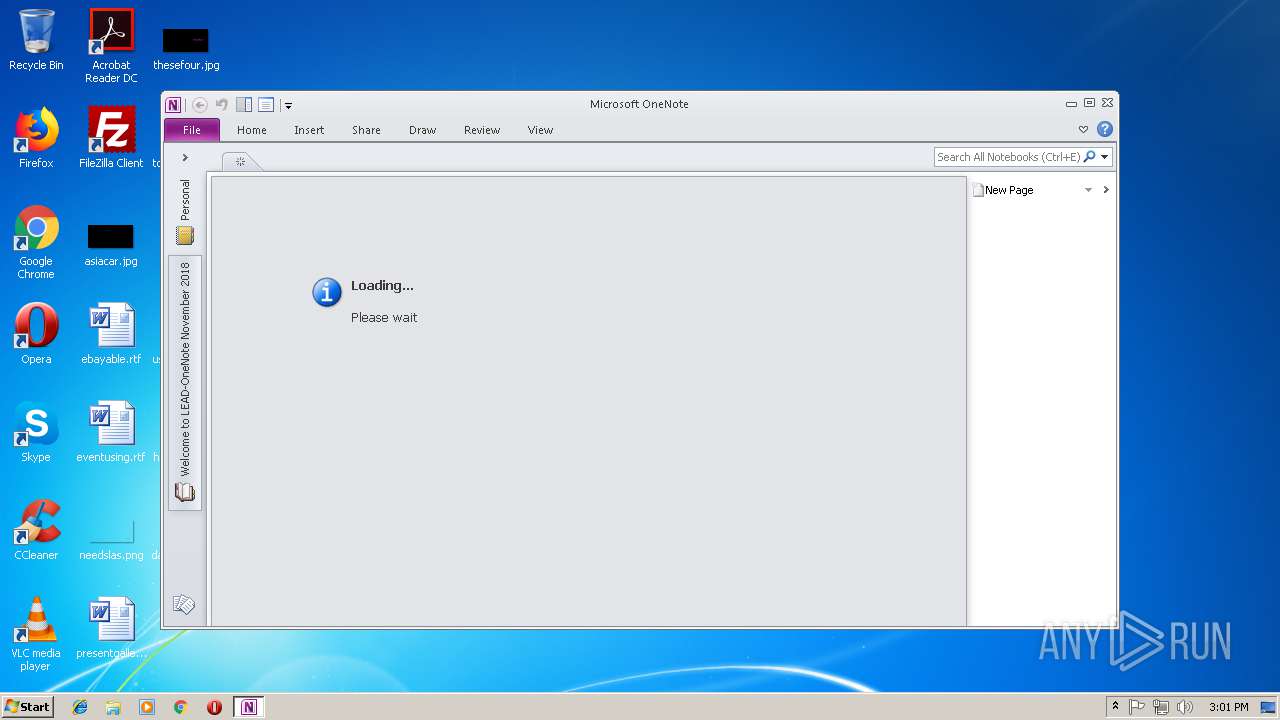
Creates files in the user directory
- ONENOTE.EXE (PID: 3204)
- iexplore.exe (PID: 3184)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 3204)
Changes internet zones settings
- iexplore.exe (PID: 3484)
Reads Internet Cache Settings
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 2164)
Application launched itself
- iexplore.exe (PID: 3484)
Reads internet explorer settings
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .onepkg | | | Microsoft OneNote Package (63.6) |
|---|---|---|
| .cab | | | Microsoft Cabinet Archive (36.3) |
Total processes
38
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2060 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:6402 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | /tsr | C:\Program Files\Microsoft Office\Office14\ONENOTEM.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Quick Launcher Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE" "C:\Users\admin\AppData\Local\Temp\Welcome to LEAD-OneNote November 2018.onepkg" | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 401
Read events
1 292
Write events
104
Delete events
5
Modification events
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\OneNote\Resiliency\StartupItems |
| Operation: | write | Name: | *bk |
Value: 2A626B00840C0000010000000000000000000000 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\OneNote |
| Operation: | write | Name: | OneNoteMTTT |
Value: 840C0000823B840DF47CD40100000000 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\OneNote\Resiliency\StartupItems |
| Operation: | write | Name: | ibk |
Value: 69626B00840C0000020003400000000000000000 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\OneNote\OpenNotebooks |
| Operation: | write | Name: | 1 |
Value: OneNote Notebooks\Personal | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | OneNoteFiles |
Value: 1299120135 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (3204) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\Licensing |
| Operation: | write | Name: | 62F8C897D3594D8F9659CF1E9E3E6B74 |
Value: 01000000270000007B39303134303030302D303033442D303030302D303030302D3030303030303046463143457D005A0000004F00660066006900630065002000310034002C0020004F0066006600690063006500500072006F00660065007300730069006F006E0061006C002D00520065007400610069006C002000650064006900740069006F006E000000 | |||
Executable files
0
Suspicious files
18
Text files
37
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\CVRAE9A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\Documents\OneNote Notebooks\Welcome to LEAD-OneNote November 2018\C. Support Materials.one | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\Documents\OneNote Notebooks\Welcome to LEAD-OneNote November 2018\D. Support Materials (Advisors).one | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{F40D573E-8184-43AB-A44C-1C02E6F14920} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{204A4472-C337-4E03-9E90-6817D7018AF8} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{E9ABD9F4-306E-4F69-A0AB-6F598ED52EB1} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{6B199286-6CA8-4576-A769-8FB1BB768734} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{024F00B6-5D49-4CE2-85E6-CAEA57687645} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{27BD4F7F-EE91-42BA-91C6-32E140F4FDB6} | — | |
MD5:— | SHA256:— | |||
| 3204 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{8602FCFF-6F28-474B-B60A-E9D4772B60D8} | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | ONENOTE.EXE | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
3204 | ONENOTE.EXE | GET | 200 | 54.192.63.95:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3484 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3204 | ONENOTE.EXE | GET | 200 | 143.204.98.76:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3204 | ONENOTE.EXE | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 54.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | ONENOTE.EXE | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
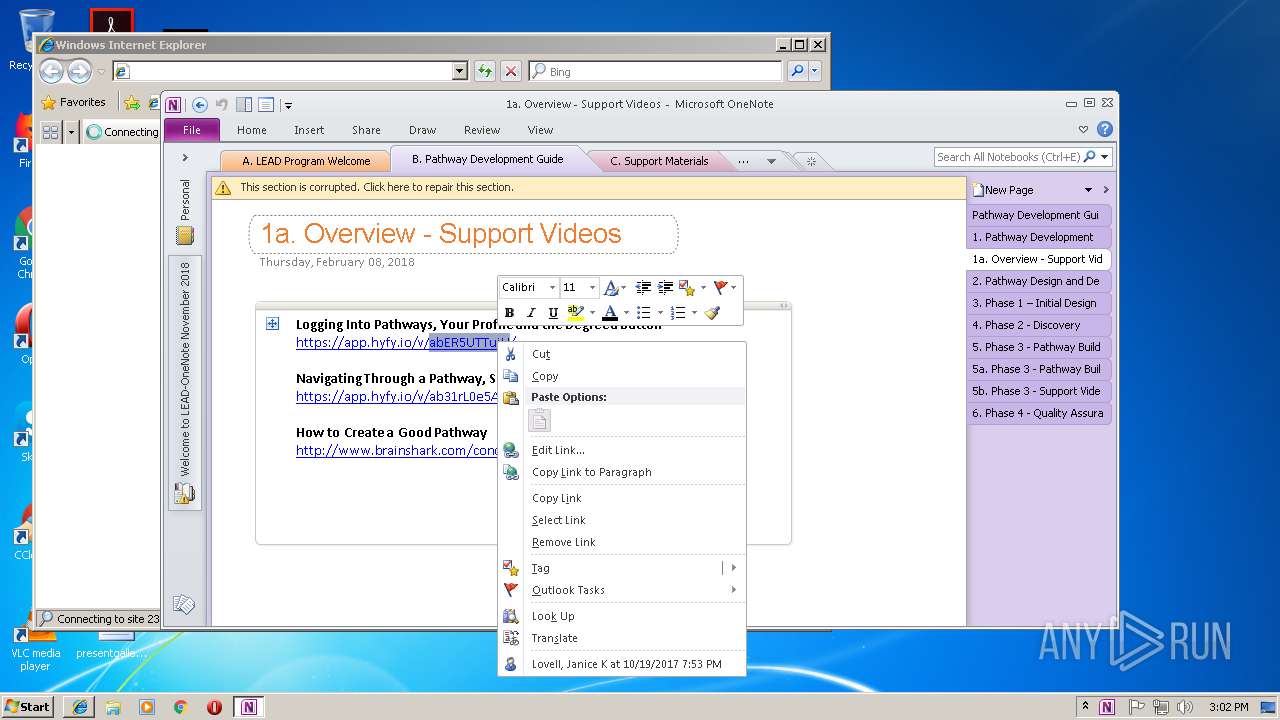
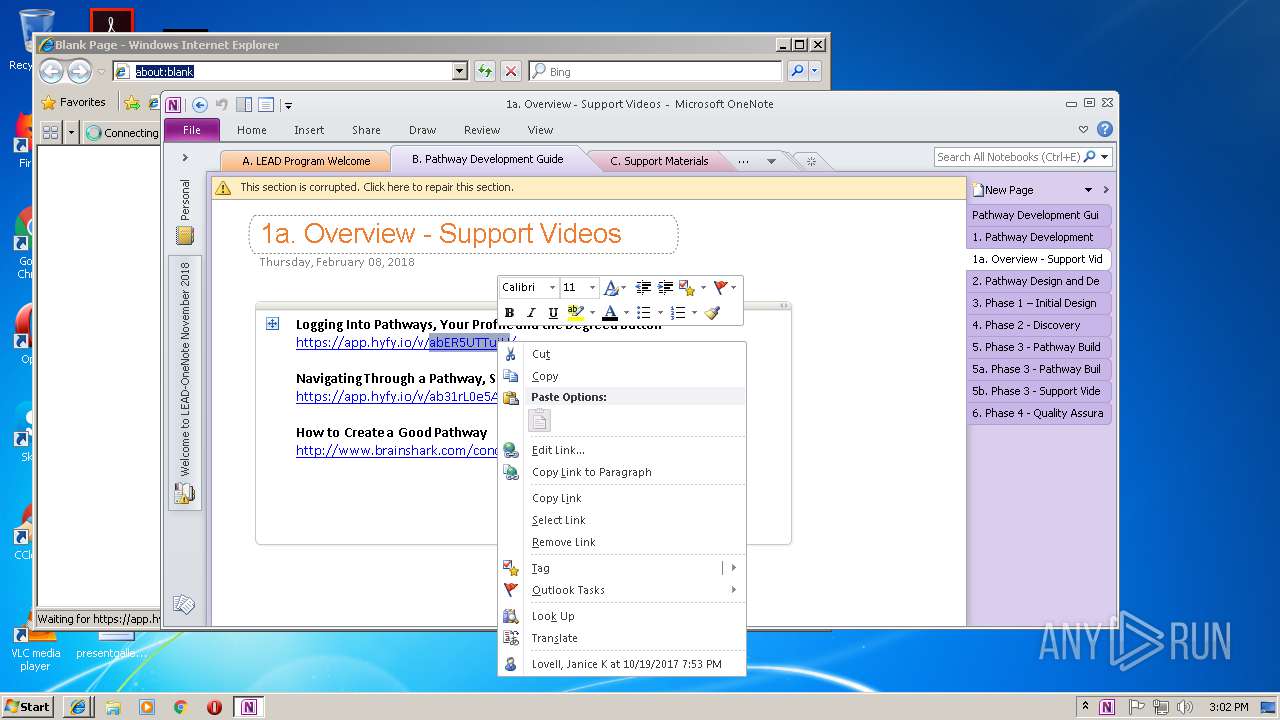
3184 | iexplore.exe | 23.20.182.69:443 | app.hyfy.io | Amazon.com, Inc. | US | unknown |
3484 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3204 | ONENOTE.EXE | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2164 | iexplore.exe | 23.20.182.69:443 | app.hyfy.io | Amazon.com, Inc. | US | unknown |
— | — | 23.20.182.69:443 | app.hyfy.io | Amazon.com, Inc. | US | unknown |
3204 | ONENOTE.EXE | 23.20.182.69:443 | app.hyfy.io | Amazon.com, Inc. | US | unknown |
3204 | ONENOTE.EXE | 54.192.63.95:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
3204 | ONENOTE.EXE | 143.204.98.76:80 | x.ss2.us | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.hyfy.io |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.bing.com |
| whitelisted |