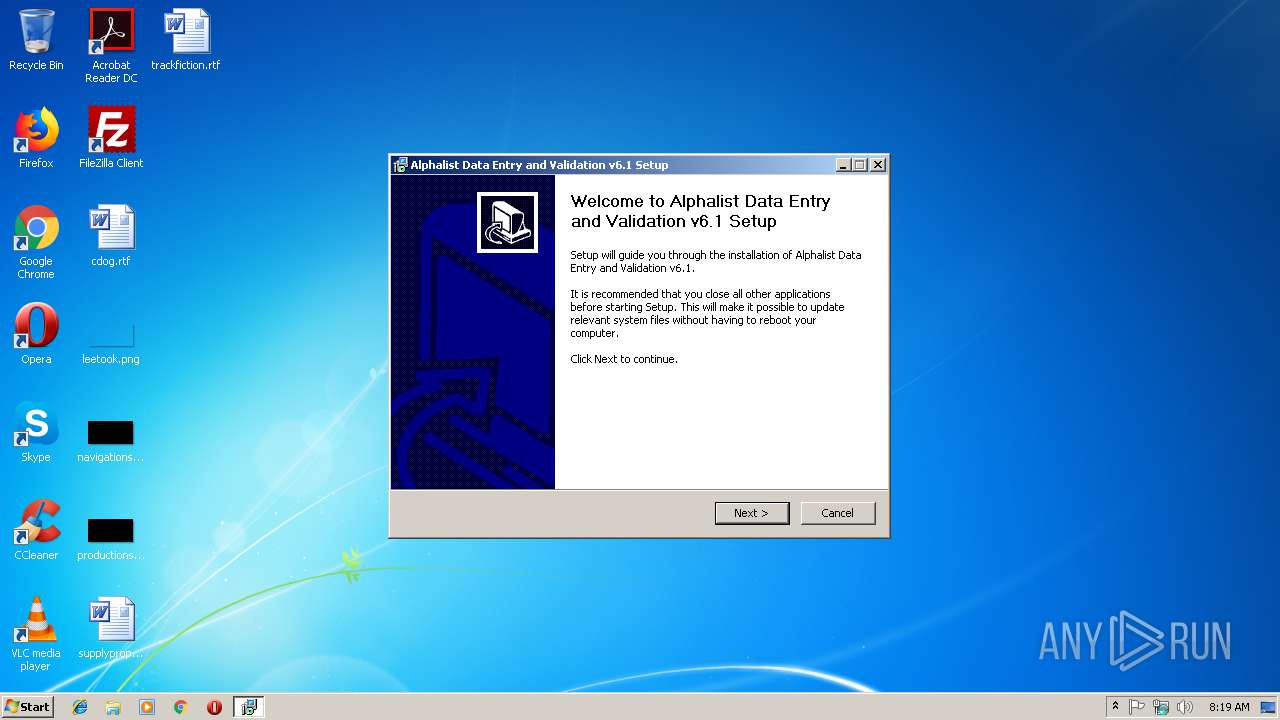
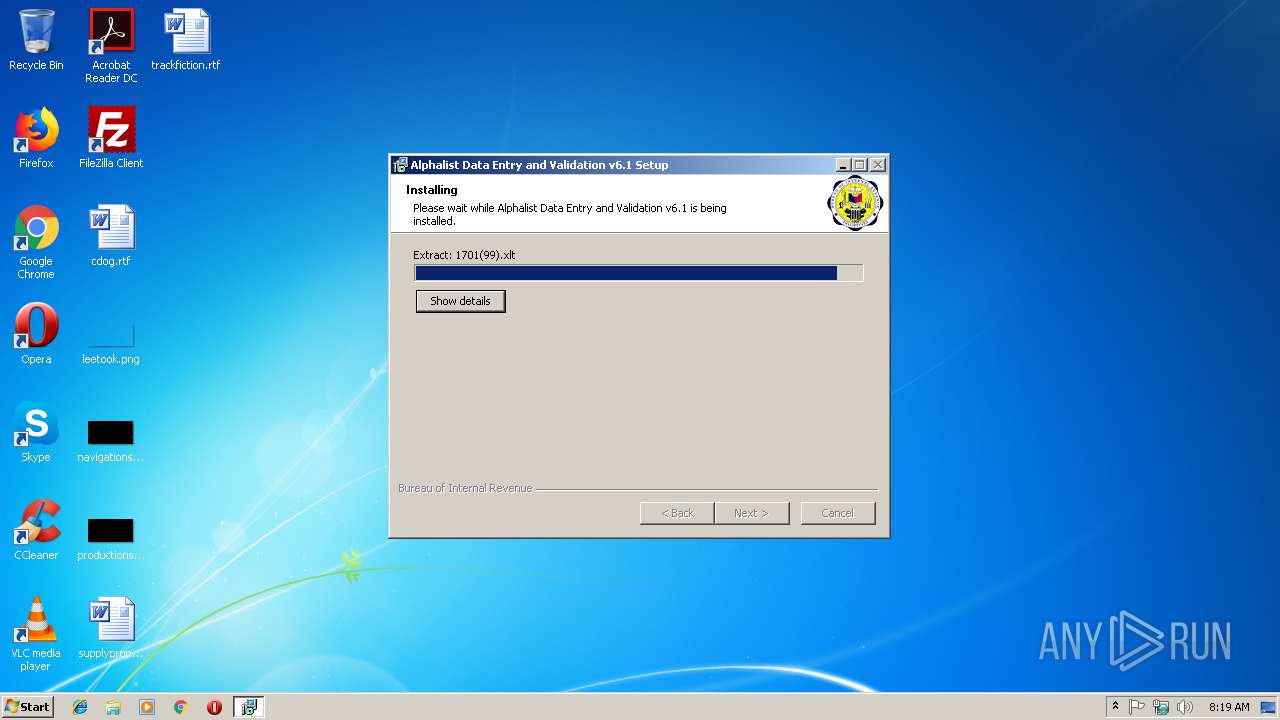
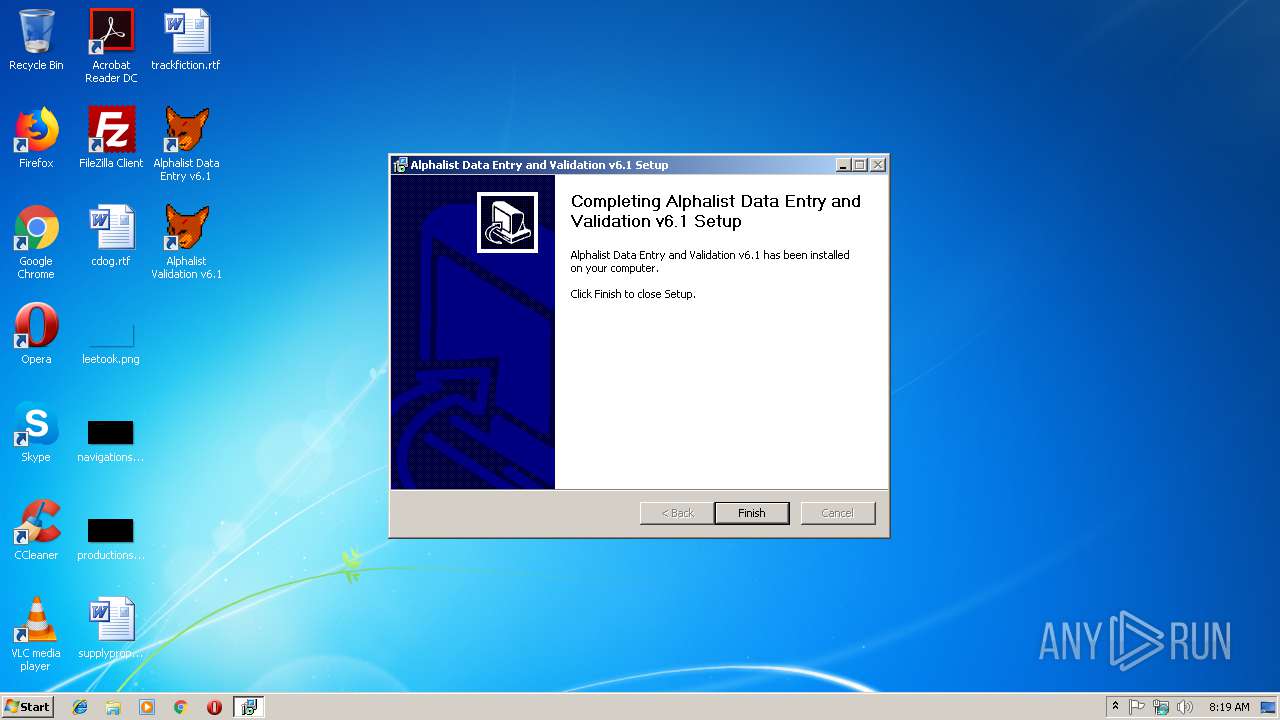
| File name: | Alphalist v6.1 Setup.exe |
| Full analysis: | https://app.any.run/tasks/8510d9d4-af24-44de-9590-b1e54c980a91 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 08:18:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BDF8EE8D5D8201D1799870FDB16CFB31 |
| SHA1: | D5991380DFA18335B003166B435CF1A581889916 |
| SHA256: | EFC5AF30E5354830D14E2BD9107FD621B29105800DE7F05D5CB574F740F65B54 |
| SSDEEP: | 196608:EJcJpYisOPbKt8a8stT3D1AJm+Q+MPgE9vg0RvvsGhfbfdKvsH/ebyz19OB:ESJKi5zha1j+QdxxUGpkvg6owB |
MALICIOUS
Loads dropped or rewritten executable
- Alphalist v6.1 Setup.exe (PID: 3880)
- Alphalist v6.1 Setup.exe (PID: 3472)
- val1604v61.exe (PID: 3688)
- bir1604v61.exe (PID: 3664)
- val1604v61.exe (PID: 3656)
Application was dropped or rewritten from another process
- val1604v61.exe (PID: 3688)
- bir1604v61.exe (PID: 3664)
- val1604v61.exe (PID: 3656)
SUSPICIOUS
Executable content was dropped or overwritten
- Alphalist v6.1 Setup.exe (PID: 3880)
- Alphalist v6.1 Setup.exe (PID: 3472)
Application launched itself
- Alphalist v6.1 Setup.exe (PID: 3880)
Creates files in the program directory
- Alphalist v6.1 Setup.exe (PID: 3472)
INFO
Dropped object may contain Bitcoin addresses
- Alphalist v6.1 Setup.exe (PID: 3472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31a3 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006071 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43434 |
.rdata | 0x00008000 | 0x00001352 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2373 |
.data | 0x0000A000 | 0x000254F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03725 |
.ndata | 0x00030000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00046000 | 0x000026E8 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39807 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2963 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.25755 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
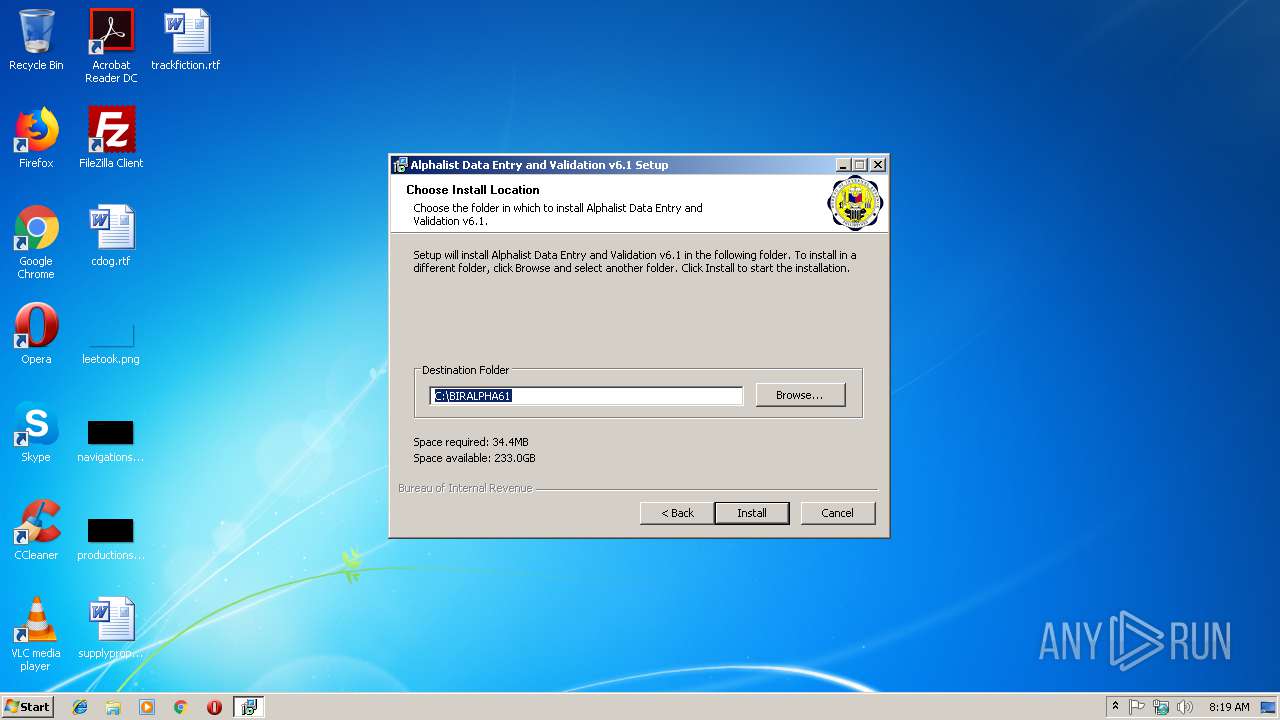
| 3472 | "C:\Users\admin\AppData\Local\Temp\Alphalist v6.1 Setup.exe" /UAC:20110 /NCRC | C:\Users\admin\AppData\Local\Temp\Alphalist v6.1 Setup.exe | Alphalist v6.1 Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1223 Modules
| |||||||||||||||
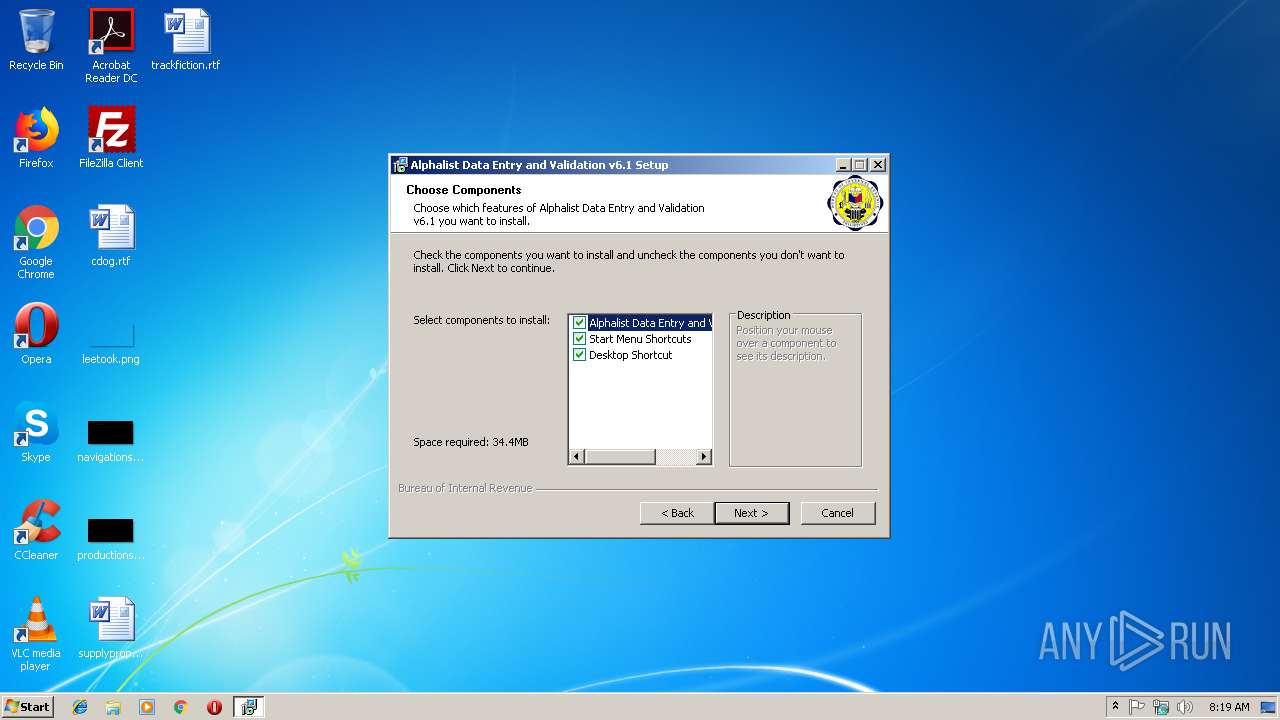
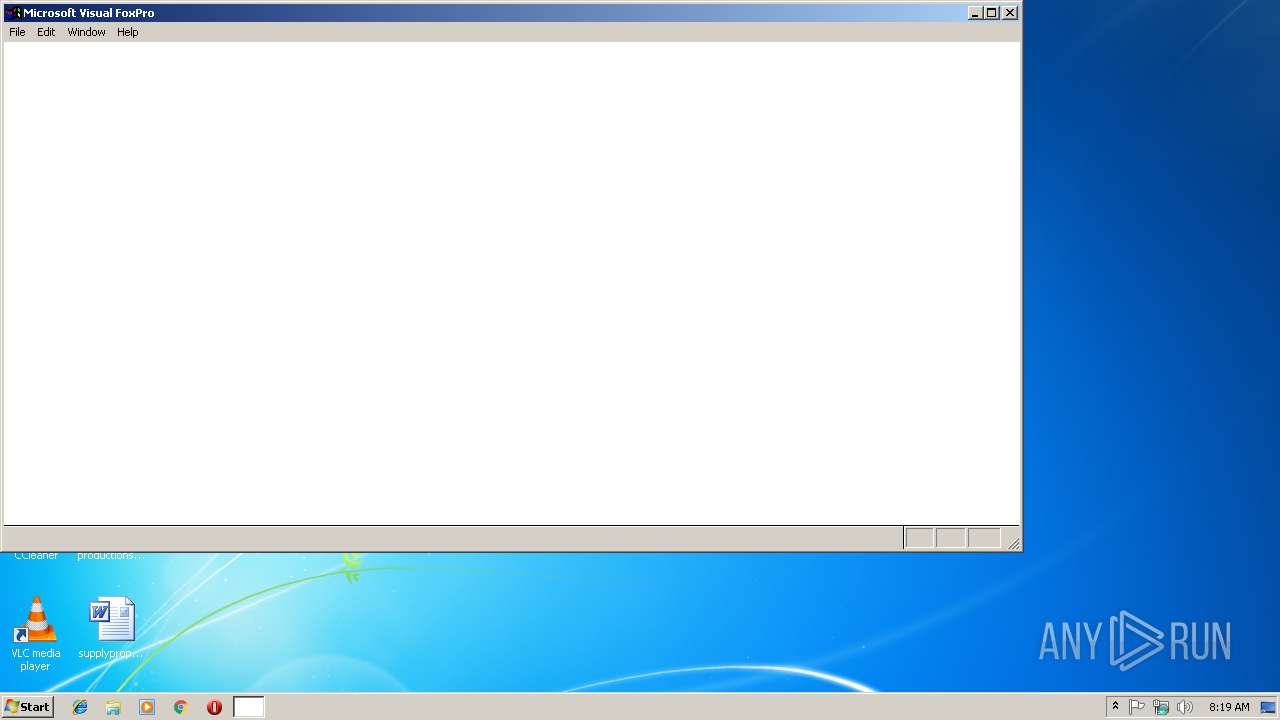
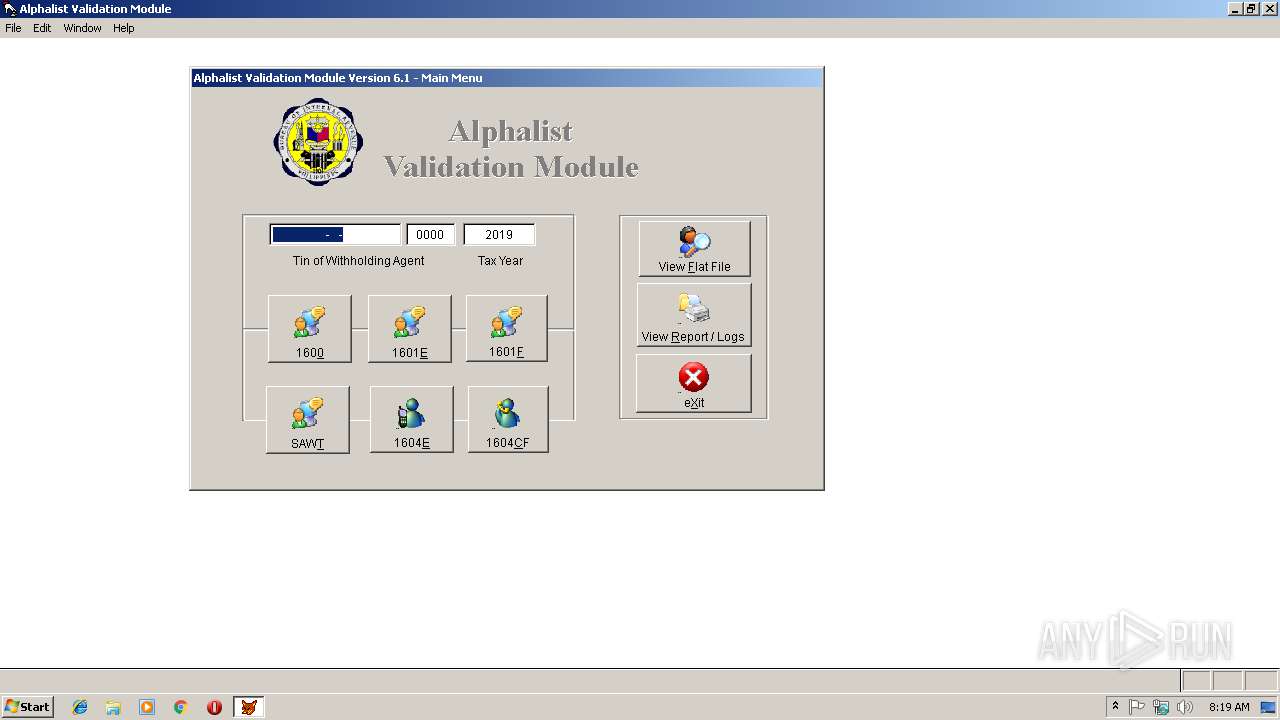
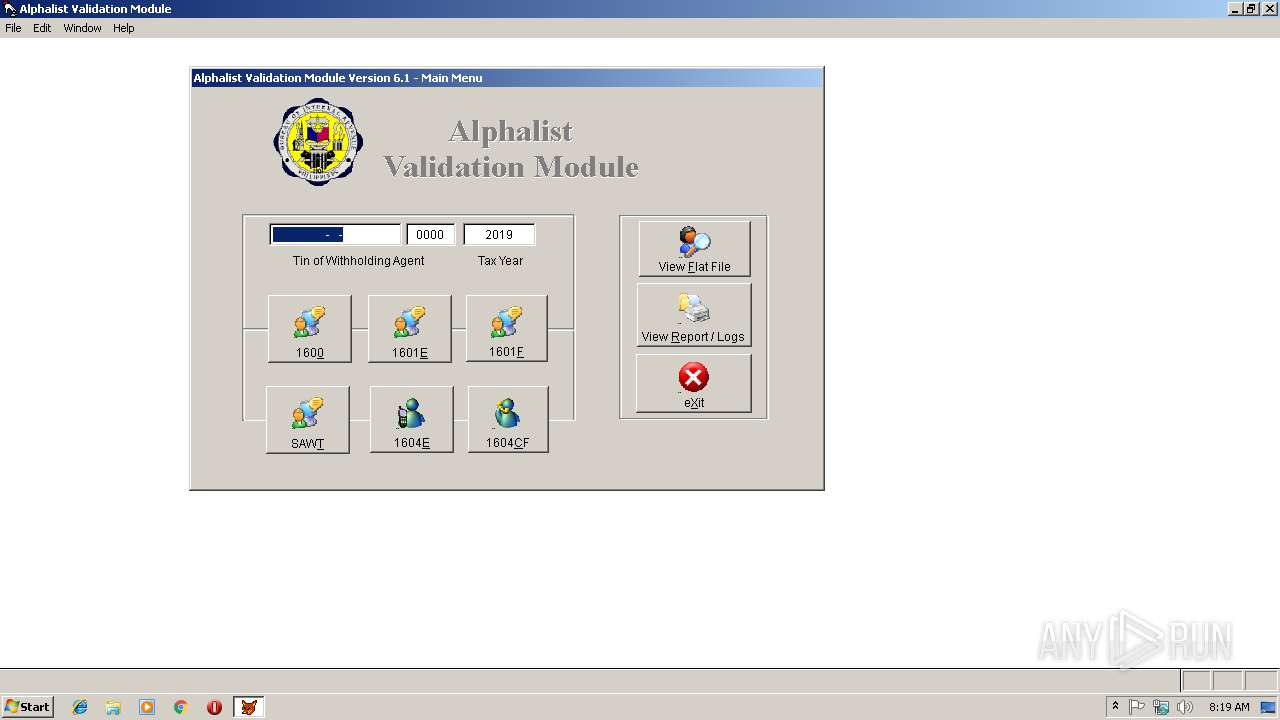
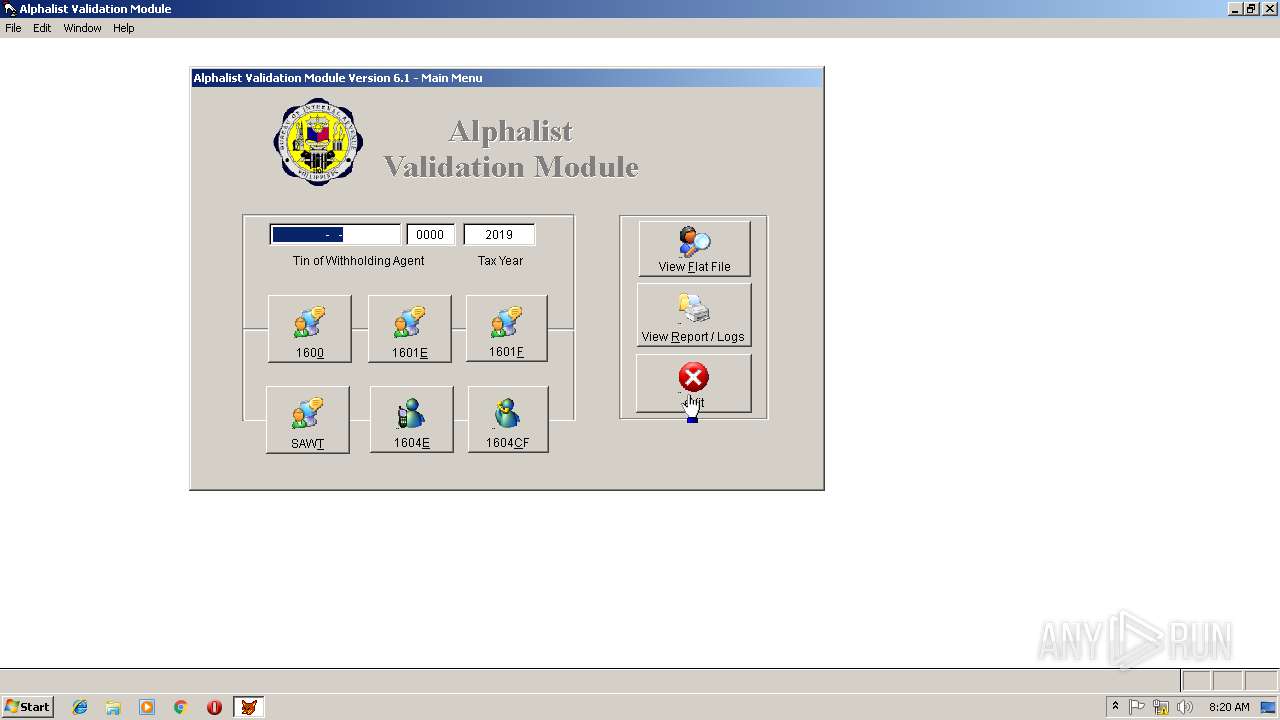
| 3656 | "C:\BIRALPHA61\val1604v61.exe" | C:\BIRALPHA61\val1604v61.exe | explorer.exe | ||||||||||||
User: admin Company: Bureau of Internal Revenue Integrity Level: MEDIUM Description: Alphalist Validation Module Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
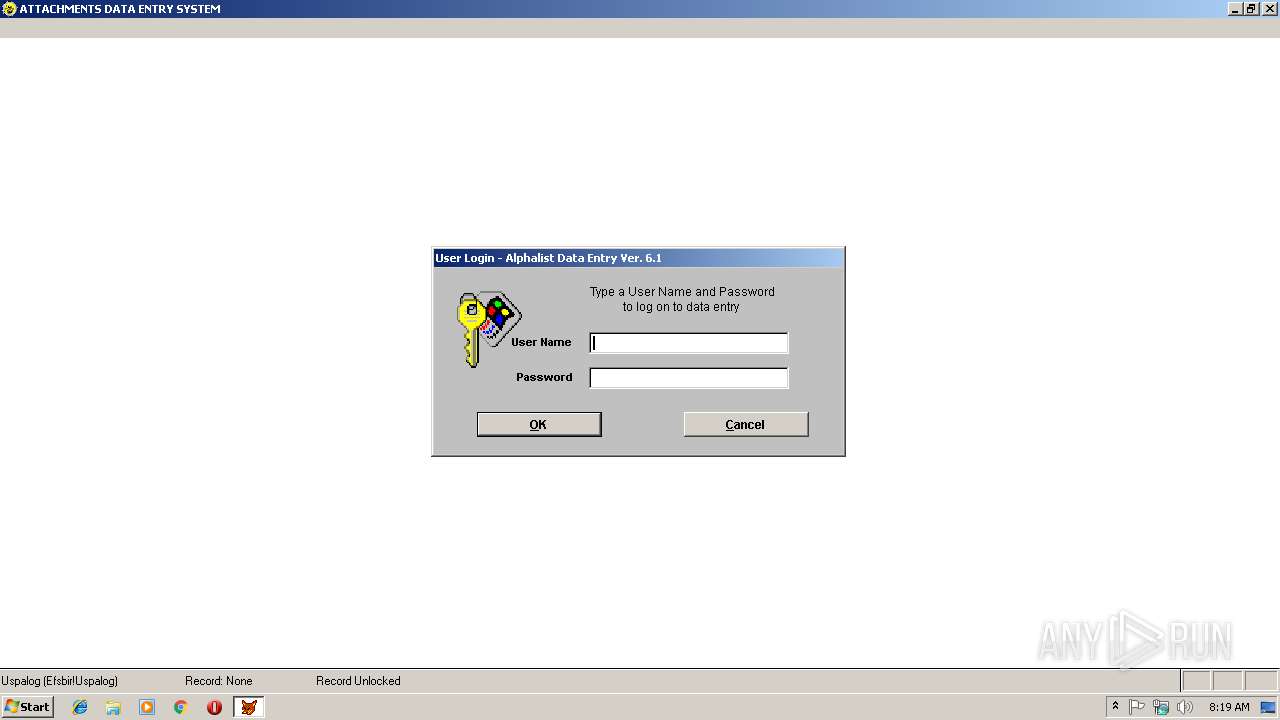
| 3664 | "C:\BIRALPHA61\bir1604v61.exe" | C:\BIRALPHA61\bir1604v61.exe | explorer.exe | ||||||||||||
User: admin Company: Bureau of Internal Revenue Integrity Level: MEDIUM Description: Alphalist Data Entry System Exit code: 0 Version: 5.0.0 Modules
| |||||||||||||||
| 3688 | "C:\BIRALPHA61\val1604v61.exe" | C:\BIRALPHA61\val1604v61.exe | explorer.exe | ||||||||||||
User: admin Company: Bureau of Internal Revenue Integrity Level: MEDIUM Description: Alphalist Validation Module Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\Alphalist v6.1 Setup.exe" | C:\Users\admin\AppData\Local\Temp\Alphalist v6.1 Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1223 Modules
| |||||||||||||||
Total events
1 167
Read events
1 127
Write events
39
Delete events
1
Modification events
| (PID) Process: | (3472) Alphalist v6.1 Setup.exe | Key: | HKEY_CURRENT_USER\Software\BIRALPHA6 |
| Operation: | write | Name: | |
Value: C:\BIRALPHA61 | |||
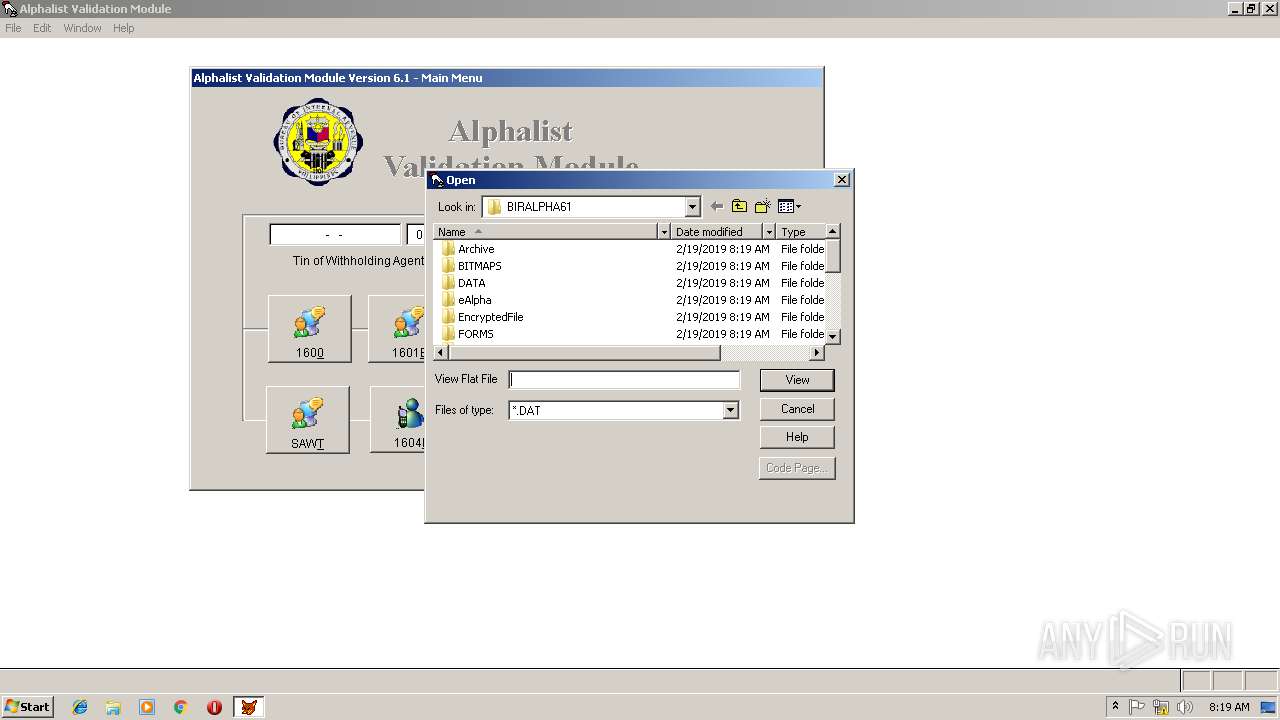
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C0042004900520041004C00500048004100360031005C00760061006C0031003600300034007600360031002E00650078006500000063003A005C0062006900720061006C00700068006100360031000000 | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000020000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | 5 |
Value: 5A00310000000000534E6B421000424952414C507E310000420008000400EFBE534E6A42534E6B422A0000005DDF000000000300000000000000000000000000000042004900520041004C0050004800410036003100000018000000 | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000100000000000000020000000400000003000000FFFFFFFF | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\5 |
| Operation: | write | Name: | NodeSlot |
Value: 95 | |||
| (PID) Process: | (3656) val1604v61.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\5 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
Executable files
10
Suspicious files
59
Text files
59
Unknown types
294
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\4_ICO_3.ICO | image | |
MD5:3B88B2ED9833F61C43F1E53A10690155 | SHA256:D69E45A04B52FCA45641F6C1398590590F56BACF6AB228D0C14CB4DD9492BE10 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\bir1604v61.exe | executable | |
MD5:— | SHA256:— | |||
| 3880 | Alphalist v6.1 Setup.exe | C:\Users\admin\AppData\Local\Temp\nsr9B6C.tmp\UAC.dll | executable | |
MD5:4814167AA1C7EC892E84907094646FAA | SHA256:32DD7269ABF5A0E5DB888E307D9DF313E87CEF4F1B597965A9D8E00934658822 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\Users\admin\AppData\Local\Temp\nsoA119.tmp\nsDialogs.dll | executable | |
MD5:B3070CF20DB659FDFB3CB2ED38130E8D | SHA256:F2C1409FAF2952C1C91F4B5495158EF5C7D1A1DB6EEA4A18F163574BD52FCAD0 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\VFP6RENU.DLL | executable | |
MD5:67C5FD2305AF277134E00C76F3E5BCE5 | SHA256:FB89F70273870D5BAA75BE62F2905A0A87453C915D5173F2231DA37783441B3B | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\VALID.ICO | image | |
MD5:BD14D1A6DB2006DFC25ECB9D17708F74 | SHA256:6FA76C15B12B1E9FA9F1DC1310E688ECA34D32A39B33AE9C97E1F3482944C1E2 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\FOXUSER.DBF | dbf | |
MD5:0A3CAA434E222D2EBA7C4ECE47594EB8 | SHA256:BD1787D74E3B512990BA3058328384018E2470FDD50F201F702D28B84057E3A9 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\birrlf.mnt | atn | |
MD5:A34E051E70D9683380D92EEDE26F101C | SHA256:D3989B4FDC14D970CB975277F79A61F2A3BC1F2B501EF0849EAA2FCF13EF61E3 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\Uninstall.exe | executable | |
MD5:6000C55D39024F55EADE61D81225AF08 | SHA256:0C3D904DBDD2B936D95E0E558CA281675BCE5B6ACC45D3B3BA3AD54EDE821F73 | |||
| 3472 | Alphalist v6.1 Setup.exe | C:\BIRALPHA61\appwiz.vct | sct | |
MD5:B428112CB091BB896A7975E9B7284F33 | SHA256:120CBC50E970E88263877379DF303C95ED20BD98D426CD7EE8F0CA3B7601E2F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|
val1604v61.exe | Invalid parameter passed to C runtime function.
|