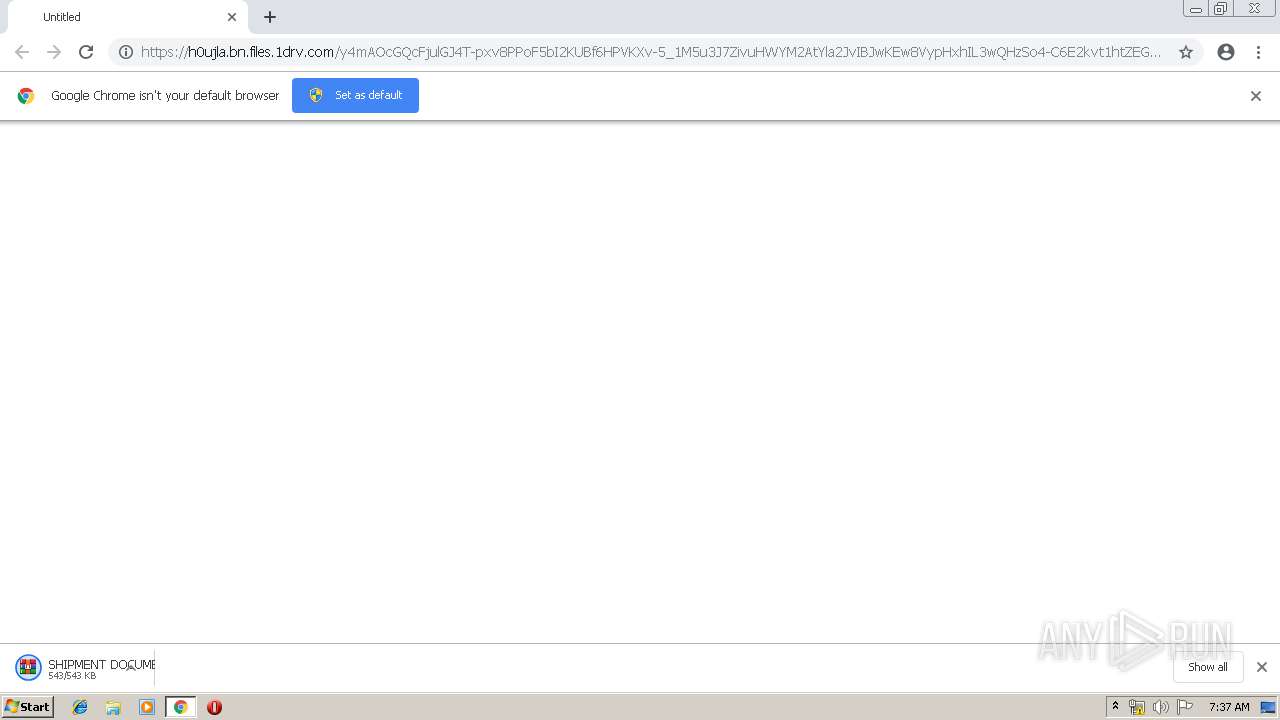
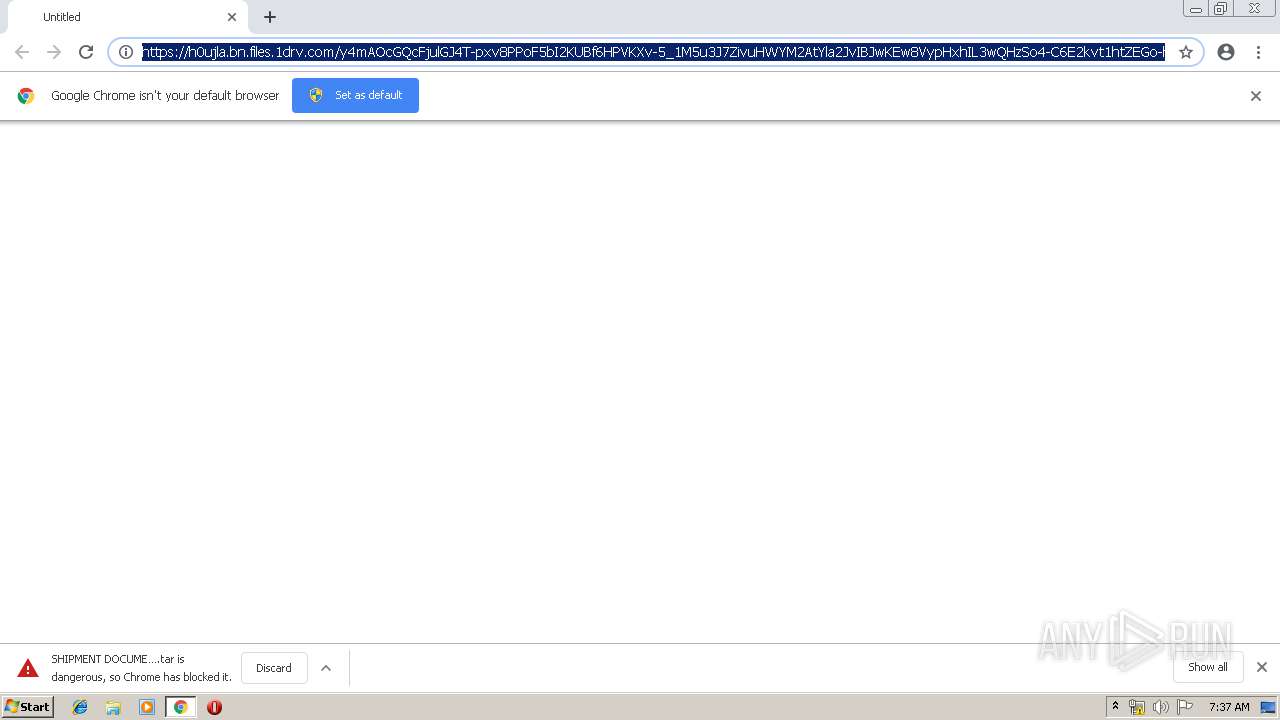
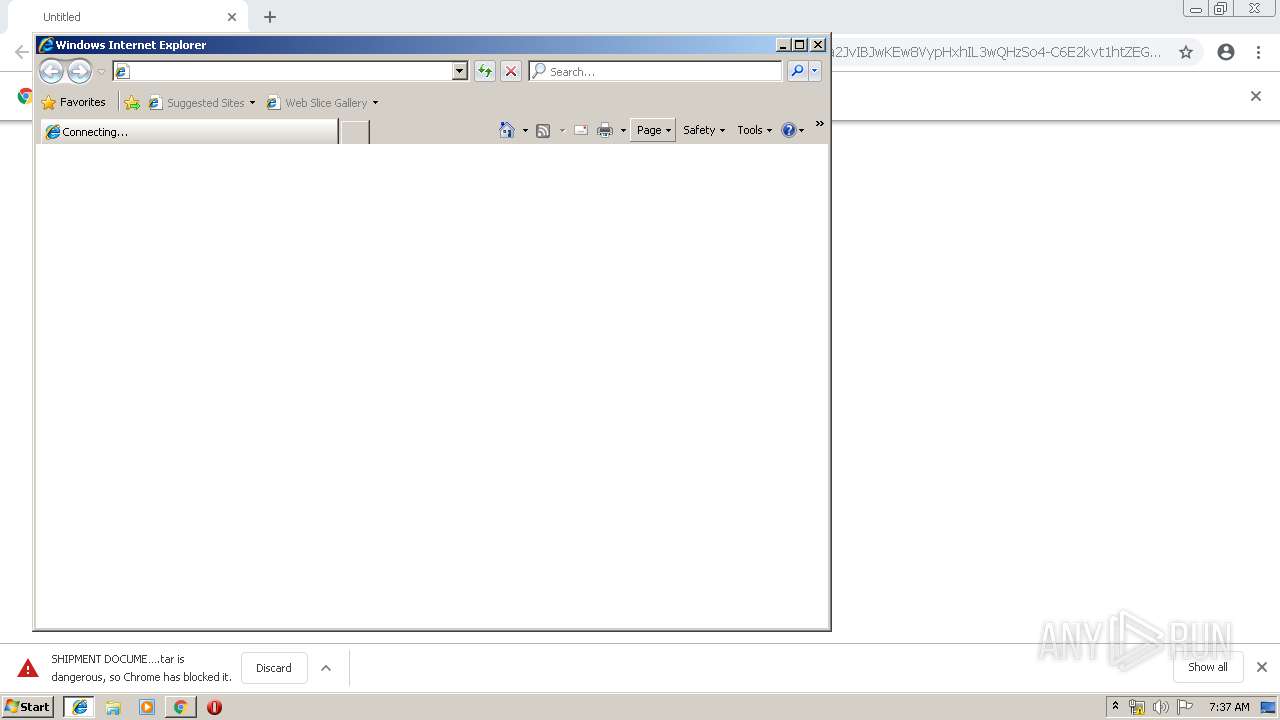
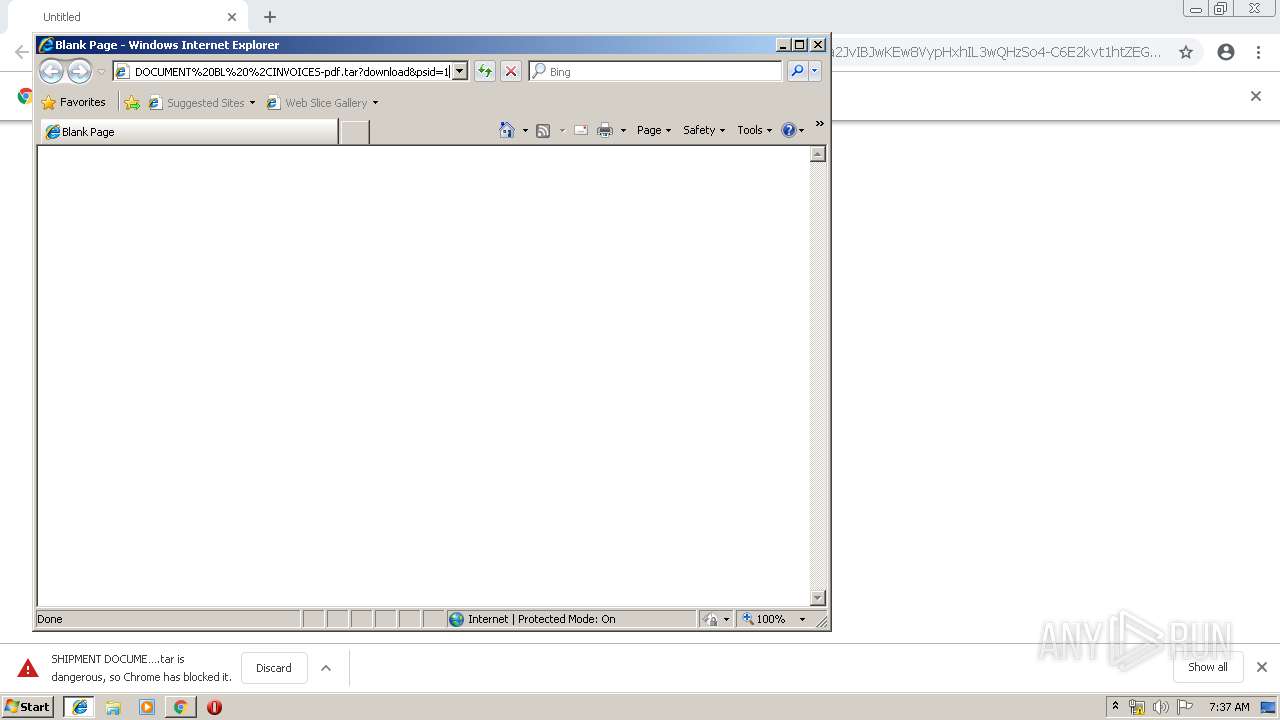
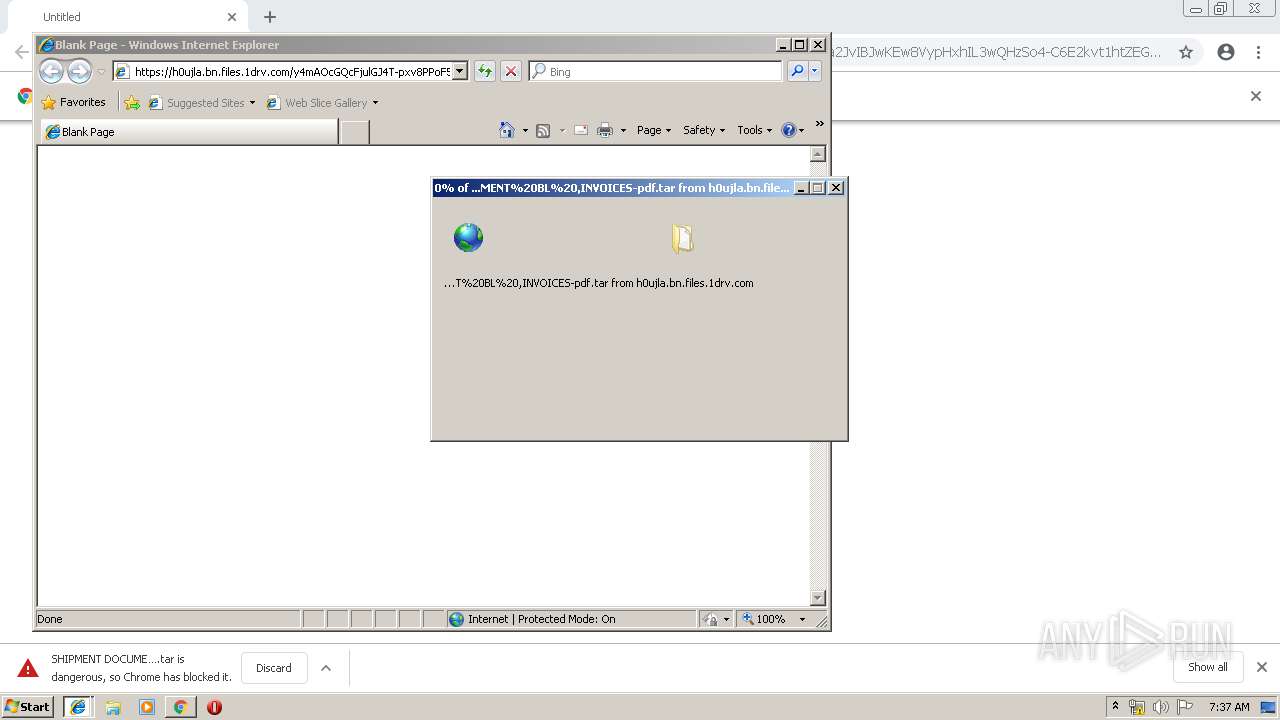
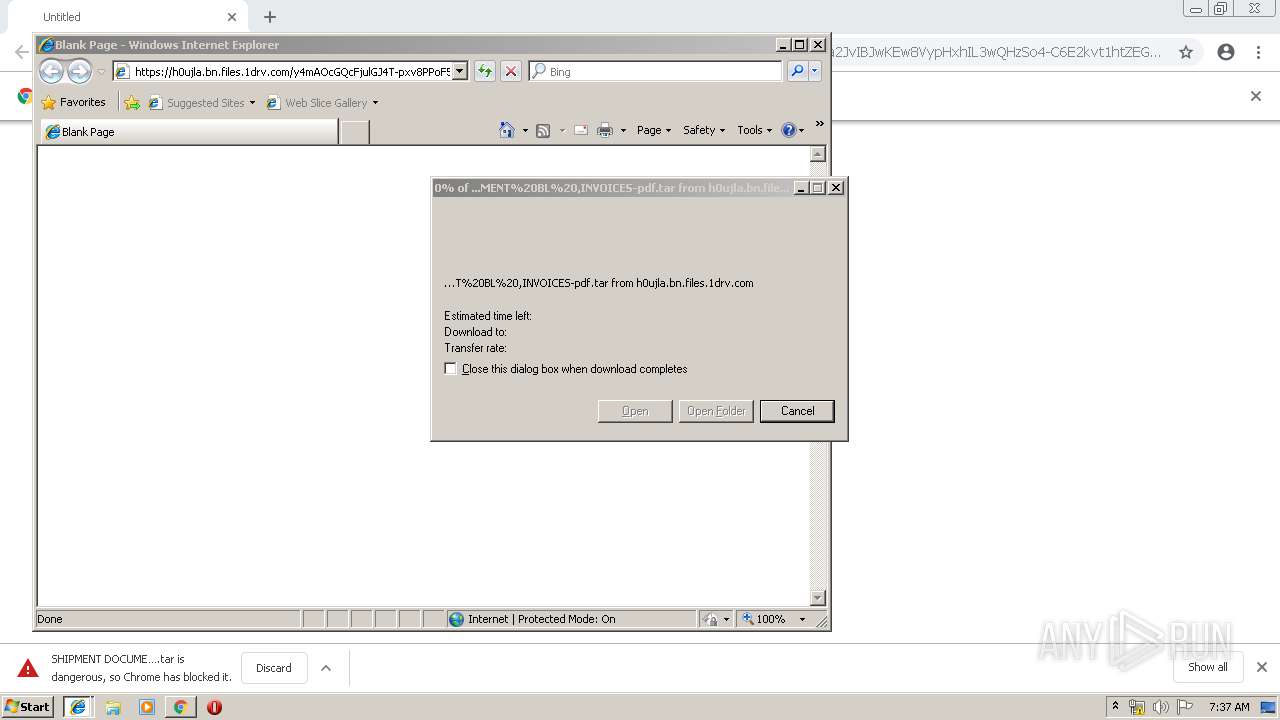
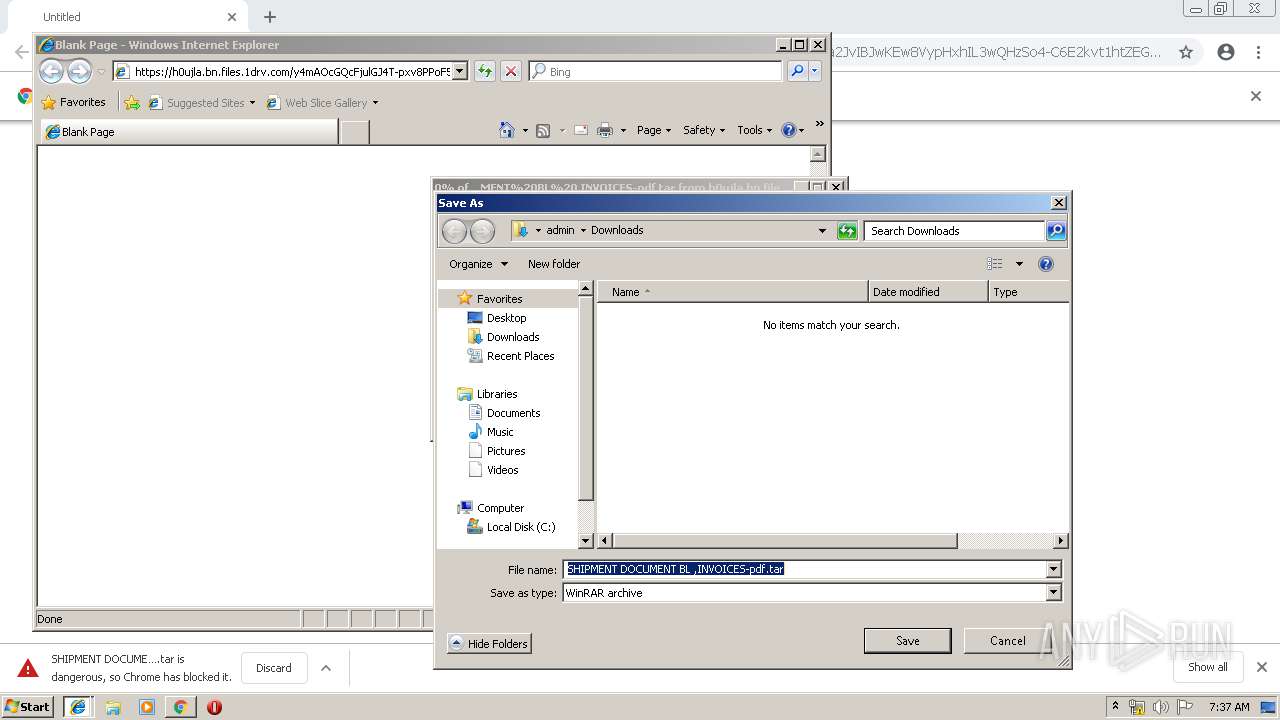
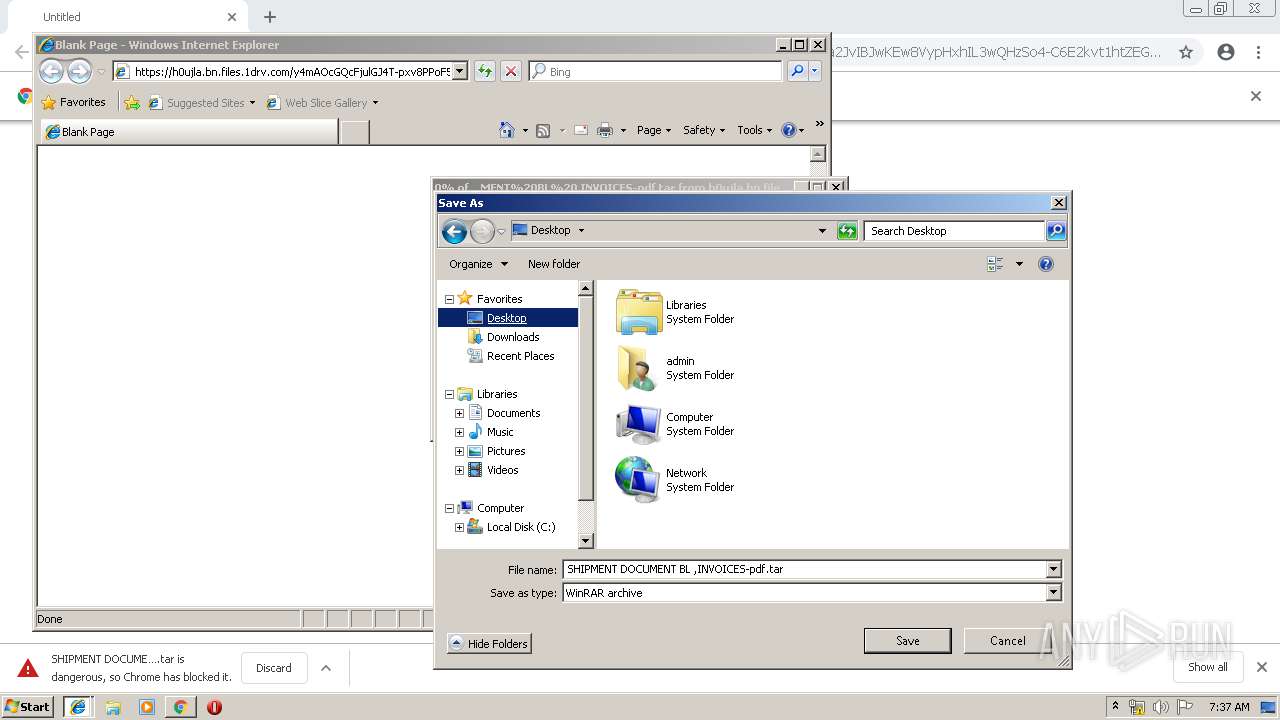
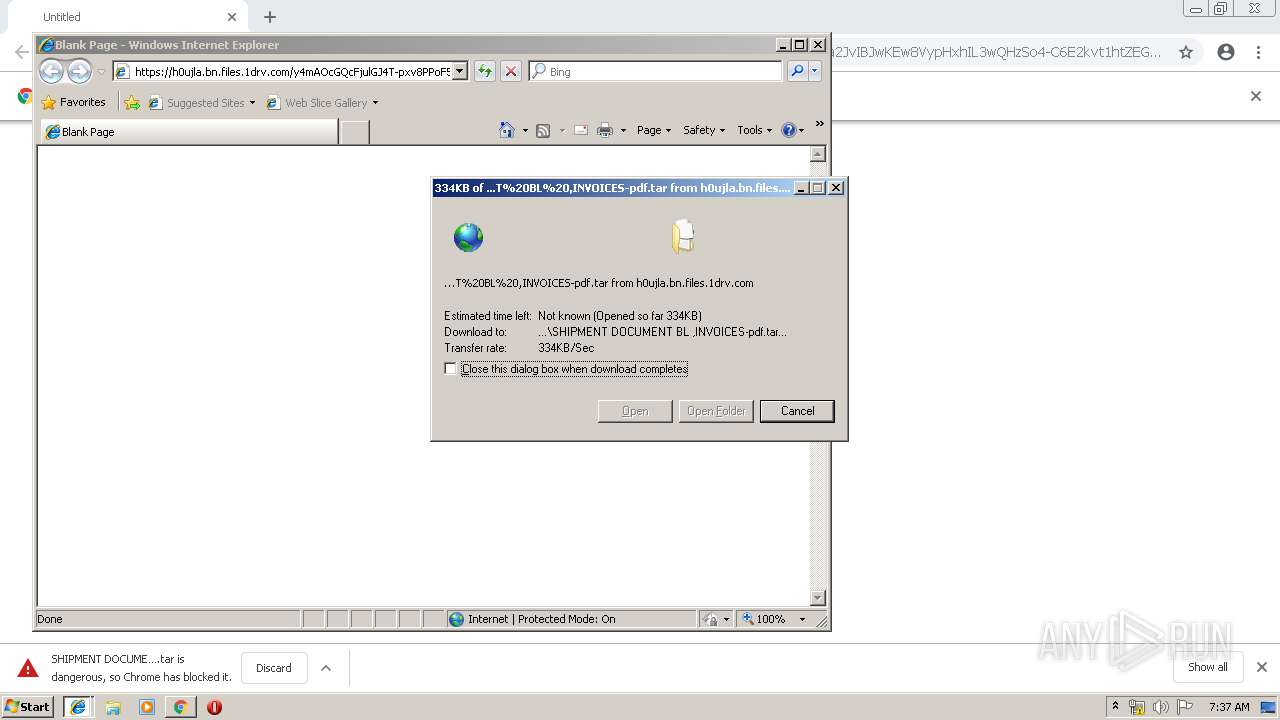
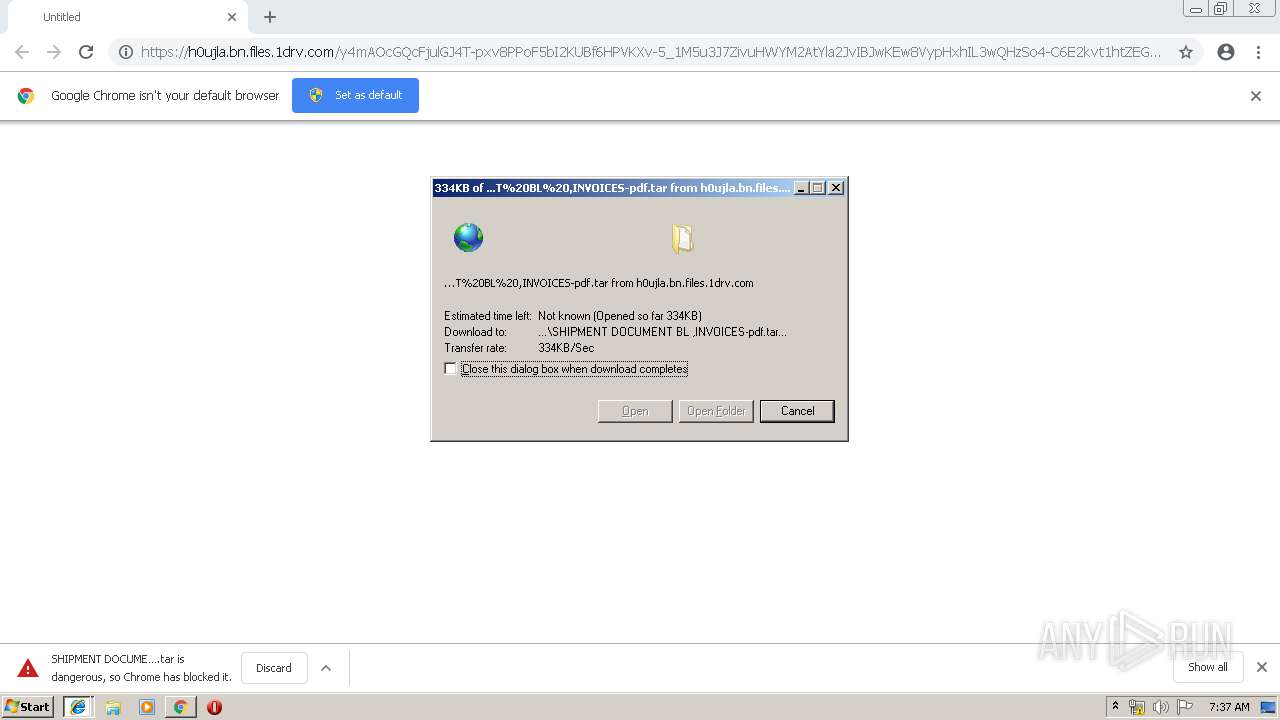
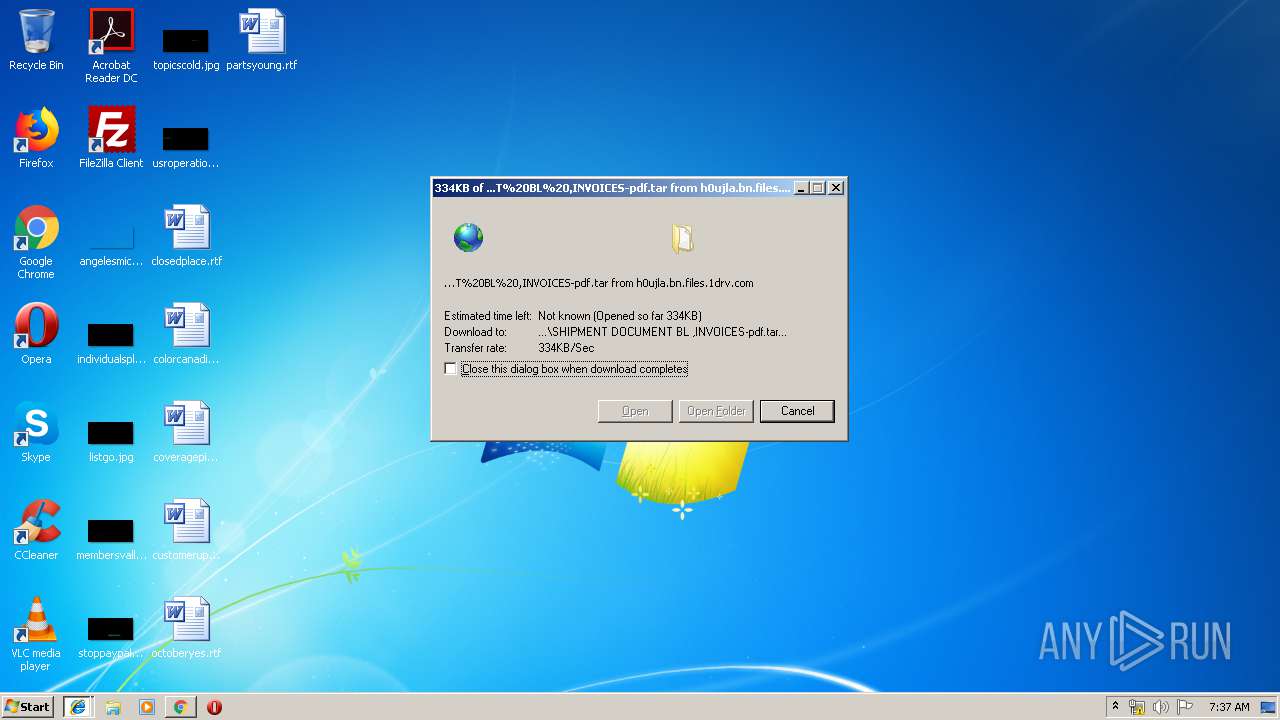
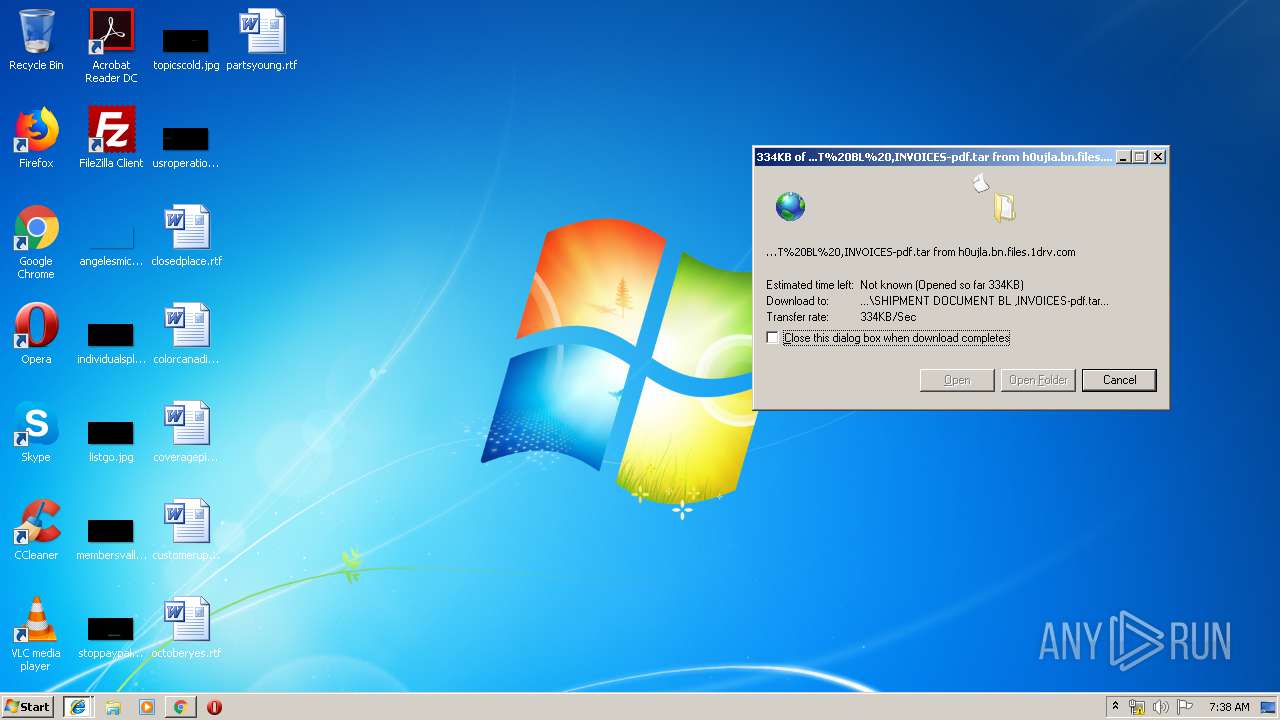
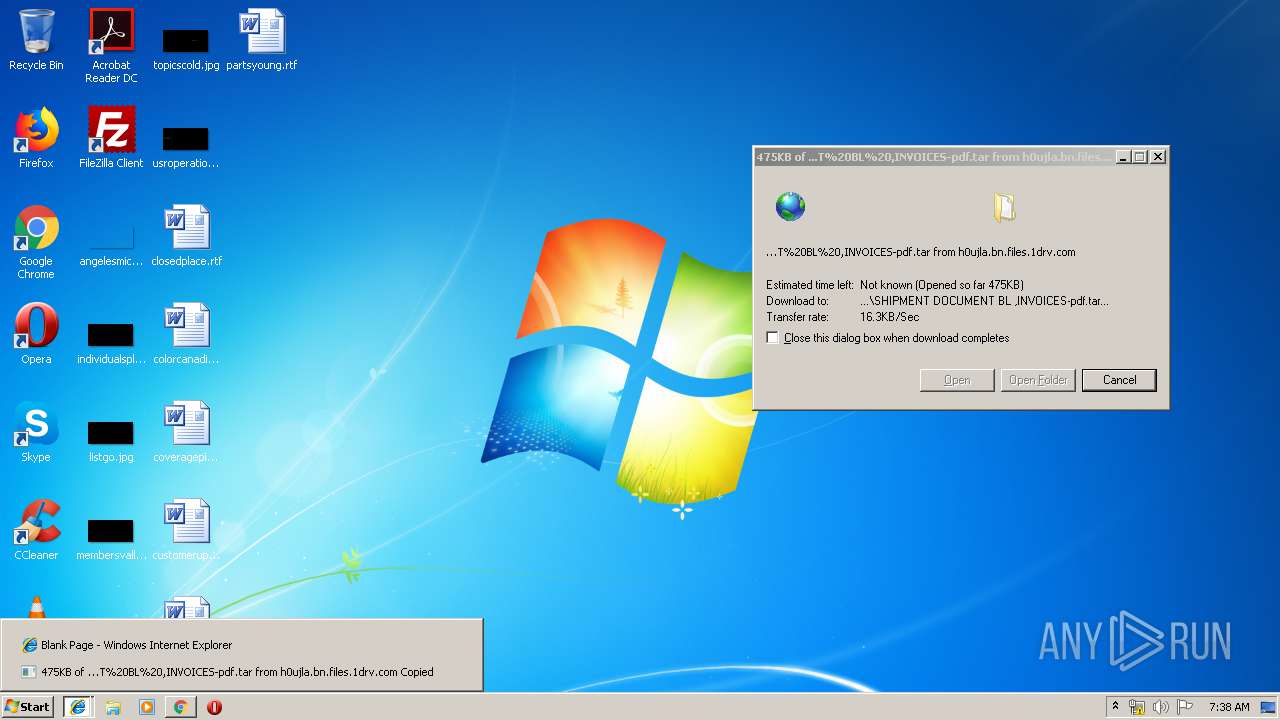
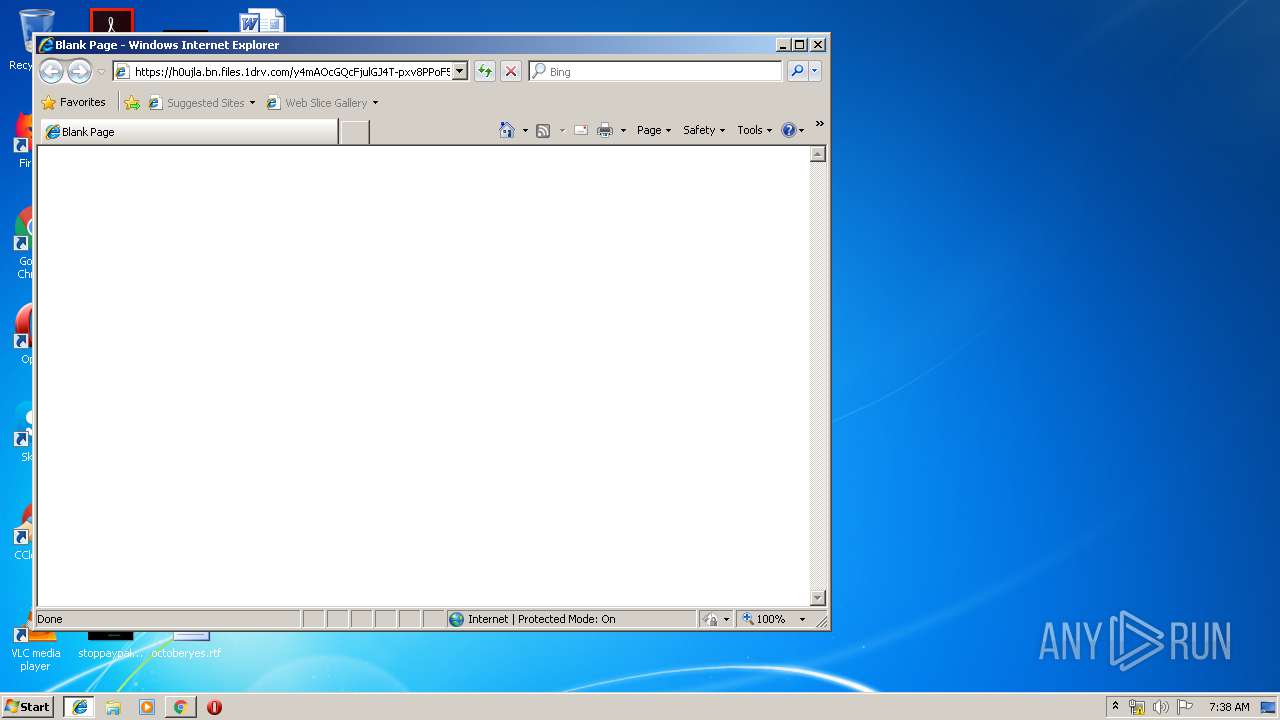
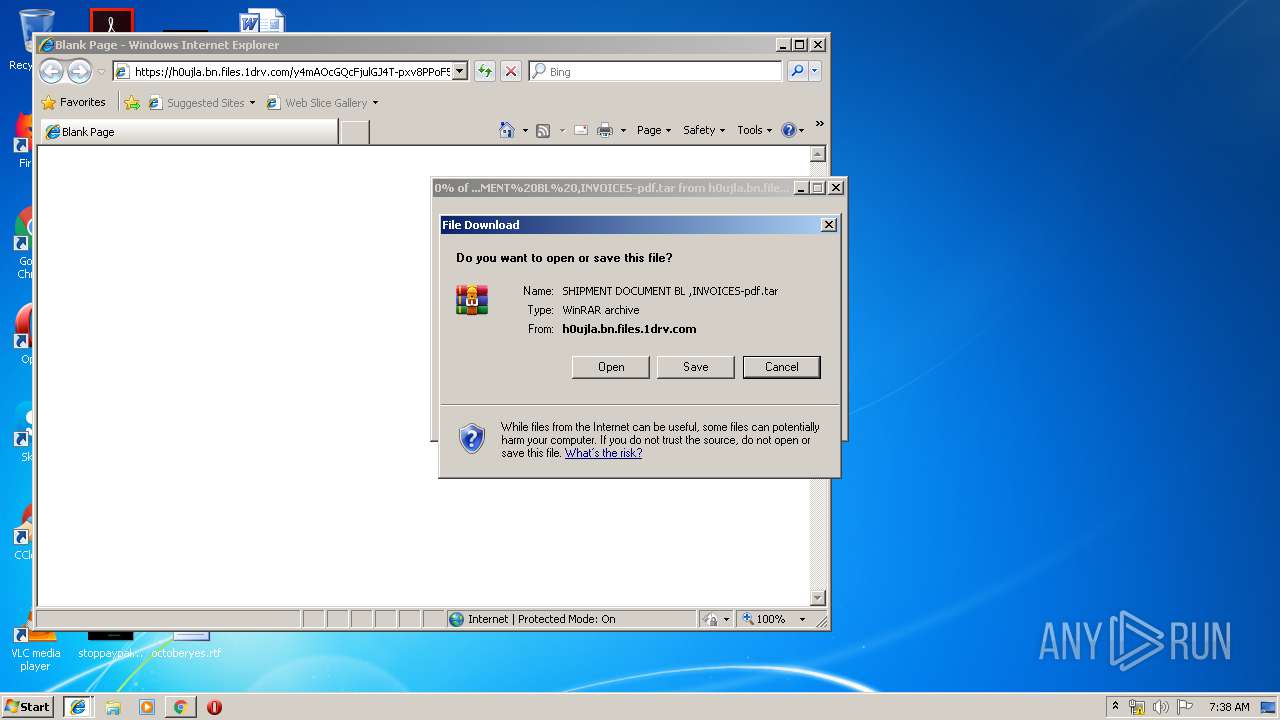
| URL: | https://h0ujla.bn.files.1drv.com/y4mAOcGQcFjulGJ4T-pxv8PPoF5bI2KUBf6HPVKXv-5_1M5u3J7ZivuHWYM2AtYla2JvIBJwKEw8VypHxhIL3wQHzSo4-C6E2kvt1htZEGo-h9_PptdI5J_FkIt3B9K7O-VXgQ_1xuc9lVlwujBT9v8SidtUWs6Ya8-Ek7cSWgBe_rjIAl8c64FLXSmuzX63haT9DQT3CR5gVL9QGEP-Uckew/SHIPMENT%20DOCUMENT%20BL%20%2CINVOICES-pdf.tar?download&psid=1 |
| Full analysis: | https://app.any.run/tasks/c1f1a21b-4ca5-4772-bd1d-5432a24e6030 |
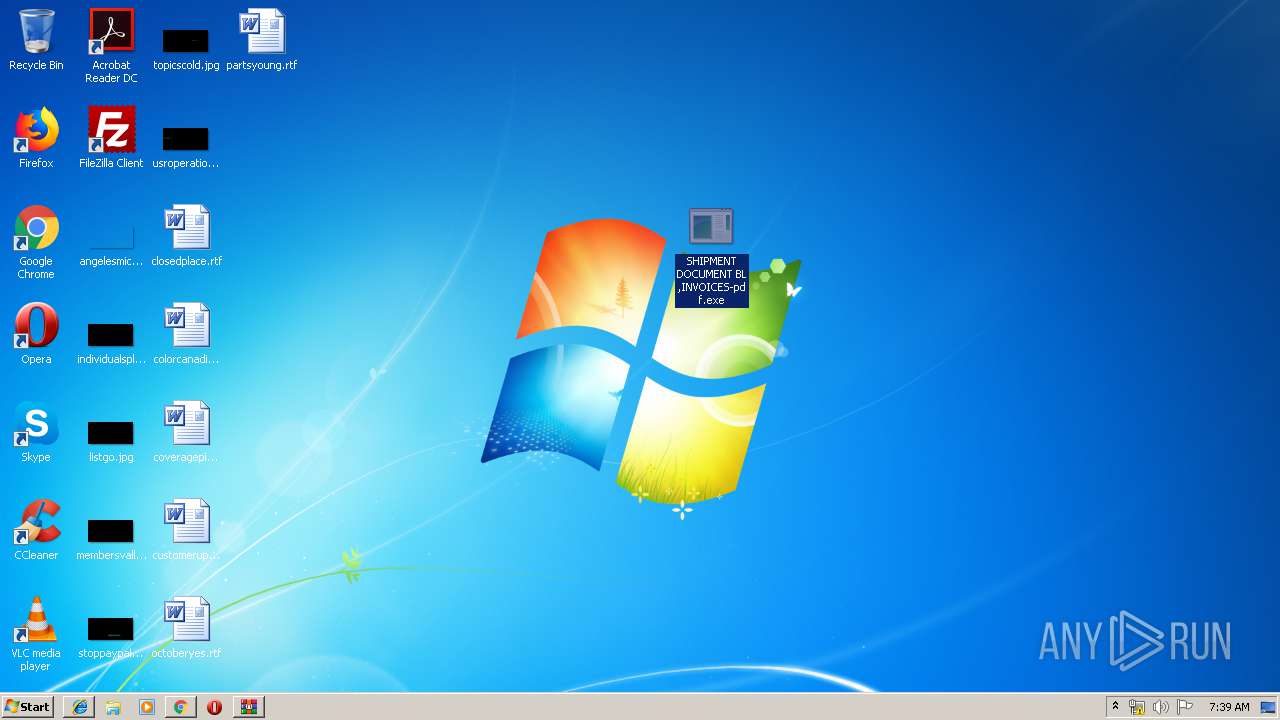
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 06:36:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F910BF80D8F9C996DABF5A799D224223 |
| SHA1: | A3C095675C5FF7DB030E7589C3EFE36BAF7068EC |
| SHA256: | EFC13F882C187E1DC716F8A3CDDE69E06641866A381E8A72C2FD30B3C5E45E7D |
| SSDEEP: | 6:2dX8j3Aj/3HdUJTpywWNkBNRLOK3V9za2BOLSWAQCKjoirzg28Jv9n:25q3Az3dU9py+D3V9F4uWAQCio8g28N9 |
MALICIOUS
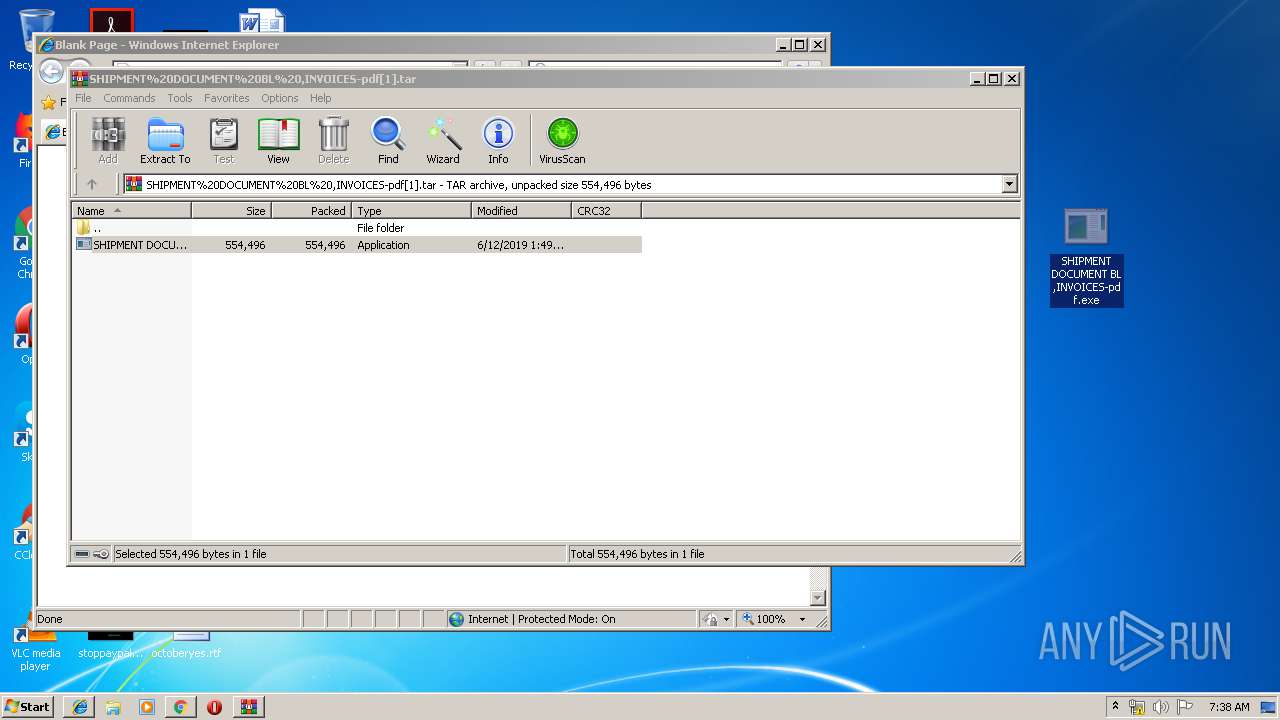
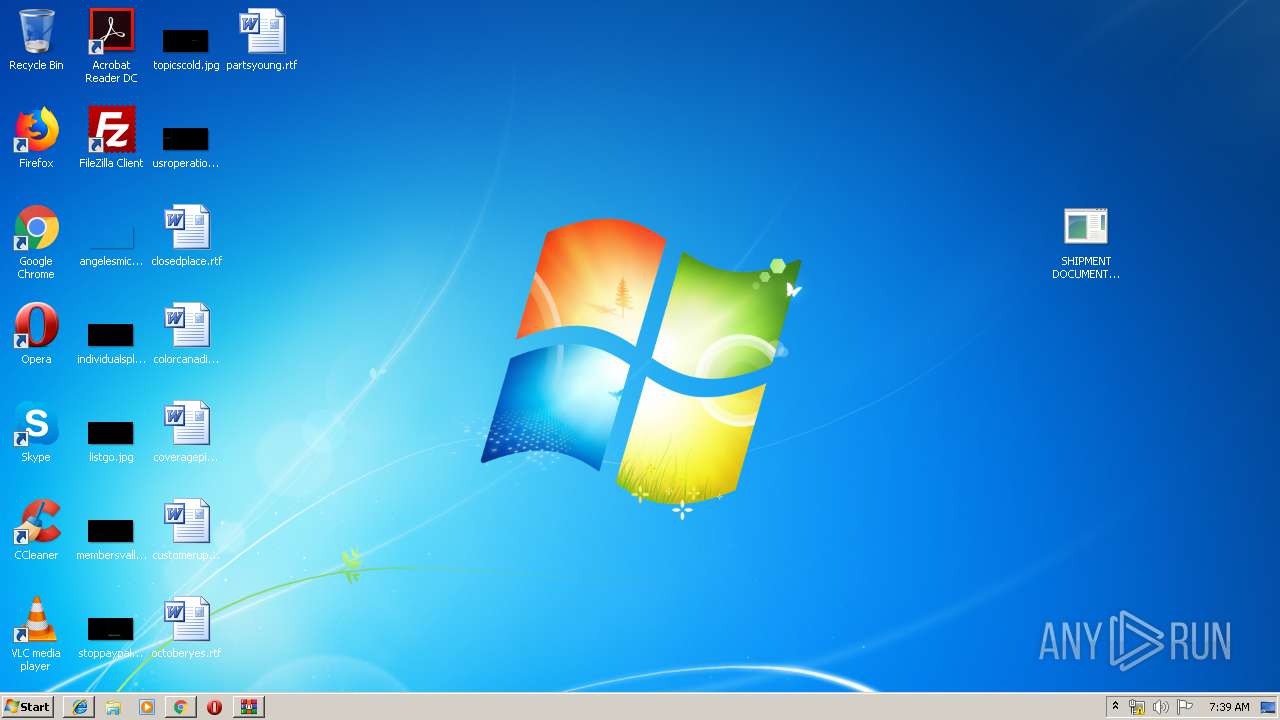
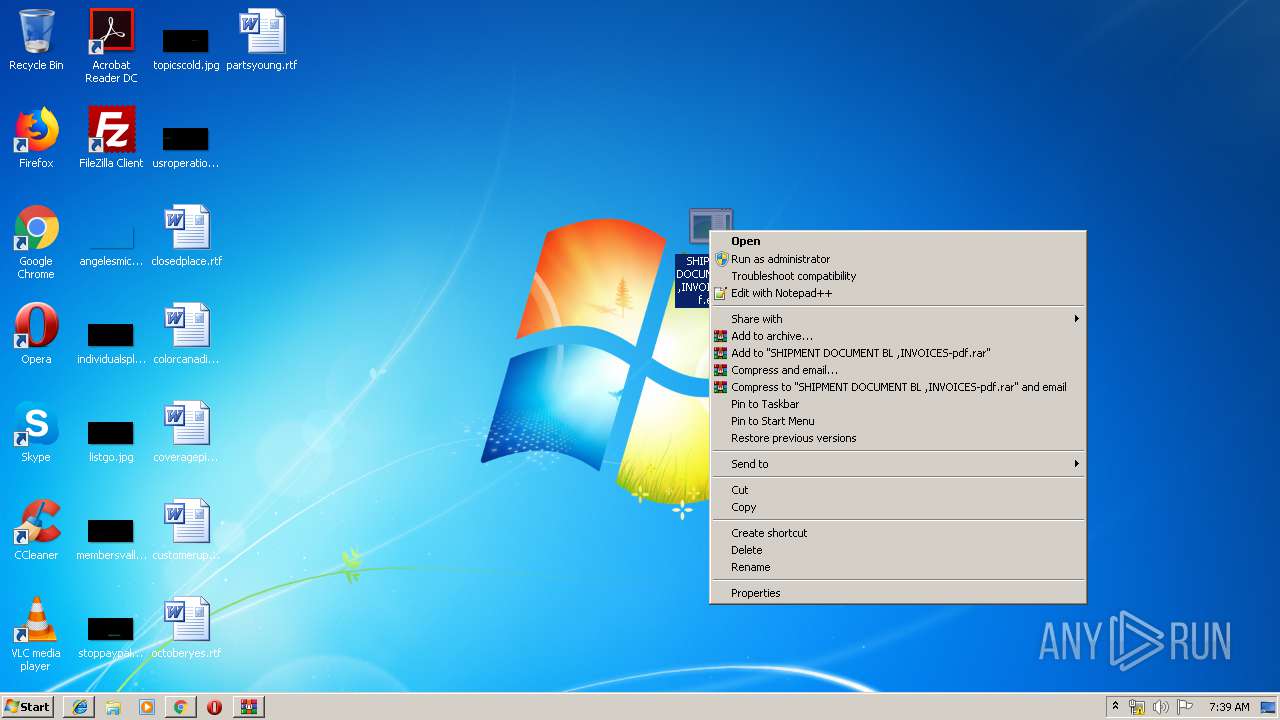
Application was dropped or rewritten from another process
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 2084)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 3912)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 1008)
Actions looks like stealing of personal data
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 1008)
SUSPICIOUS
Starts CMD.EXE for commands execution
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 2084)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 3912)
Reads Windows Product ID
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 1008)
Application launched itself
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 2084)
Reads Environment values
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 1008)
INFO
Application launched itself
- iexplore.exe (PID: 3064)
- chrome.exe (PID: 3276)
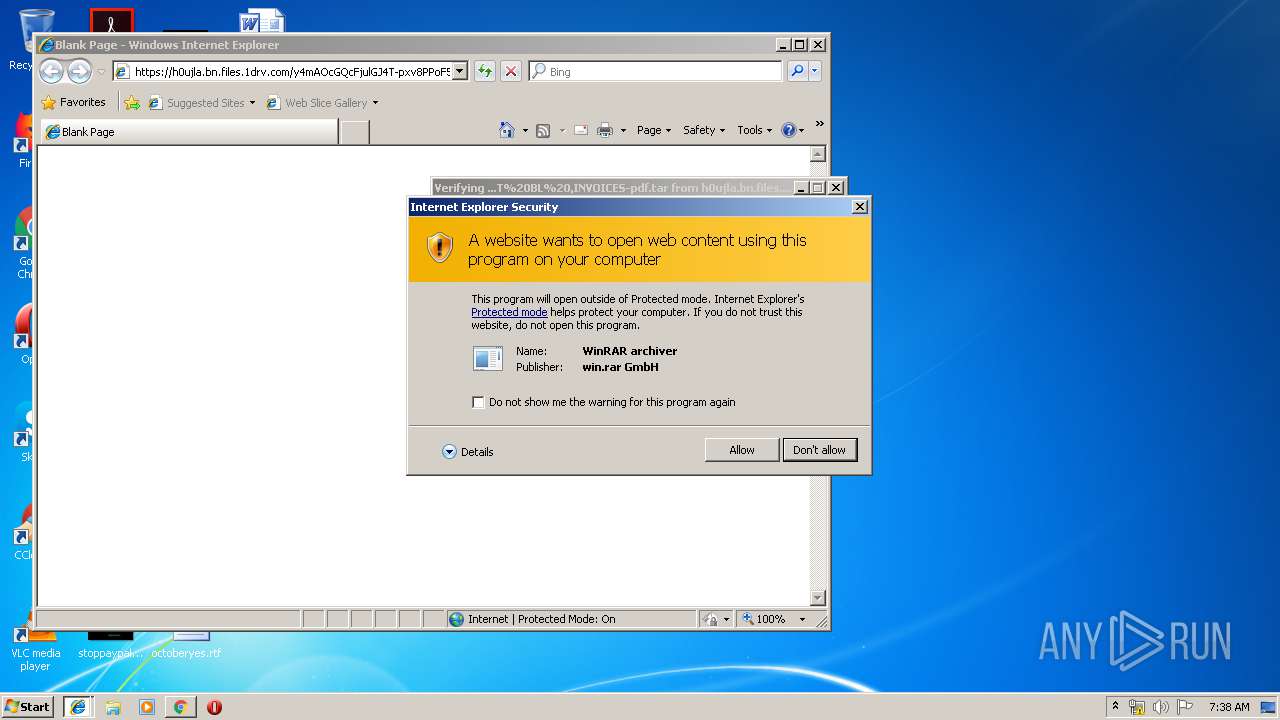
Changes internet zones settings
- iexplore.exe (PID: 3064)
Manual execution by user
- iexplore.exe (PID: 3064)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 2084)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 3912)
Reads internet explorer settings
- iexplore.exe (PID: 1080)
Reads Internet Cache Settings
- iexplore.exe (PID: 1080)
- iexplore.exe (PID: 3064)
Creates files in the user directory
- iexplore.exe (PID: 1080)
Reads settings of System Certificates
- iexplore.exe (PID: 3064)
- SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe (PID: 1008)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3064)
Changes settings of System certificates
- iexplore.exe (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
20
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=927289249614774528 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=927289249614774528 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4134483467442619566 --mojo-platform-channel-handle=2344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2229209592257445739 --mojo-platform-channel-handle=932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
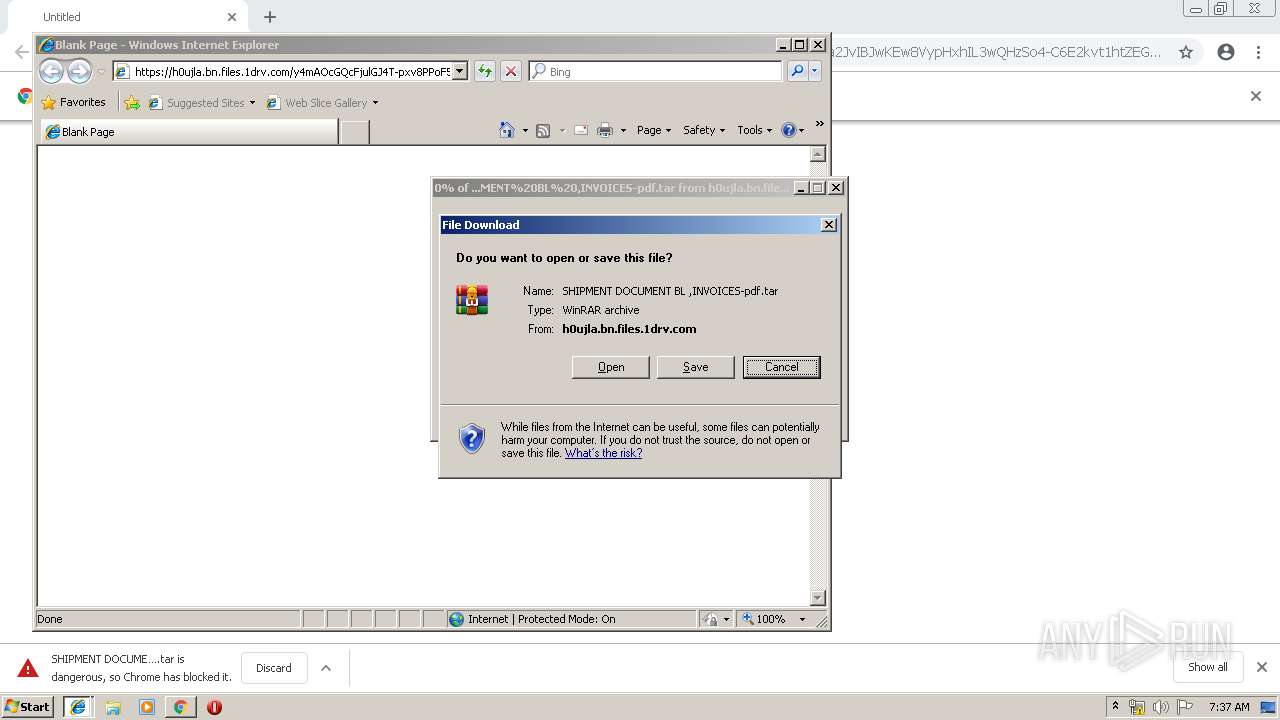
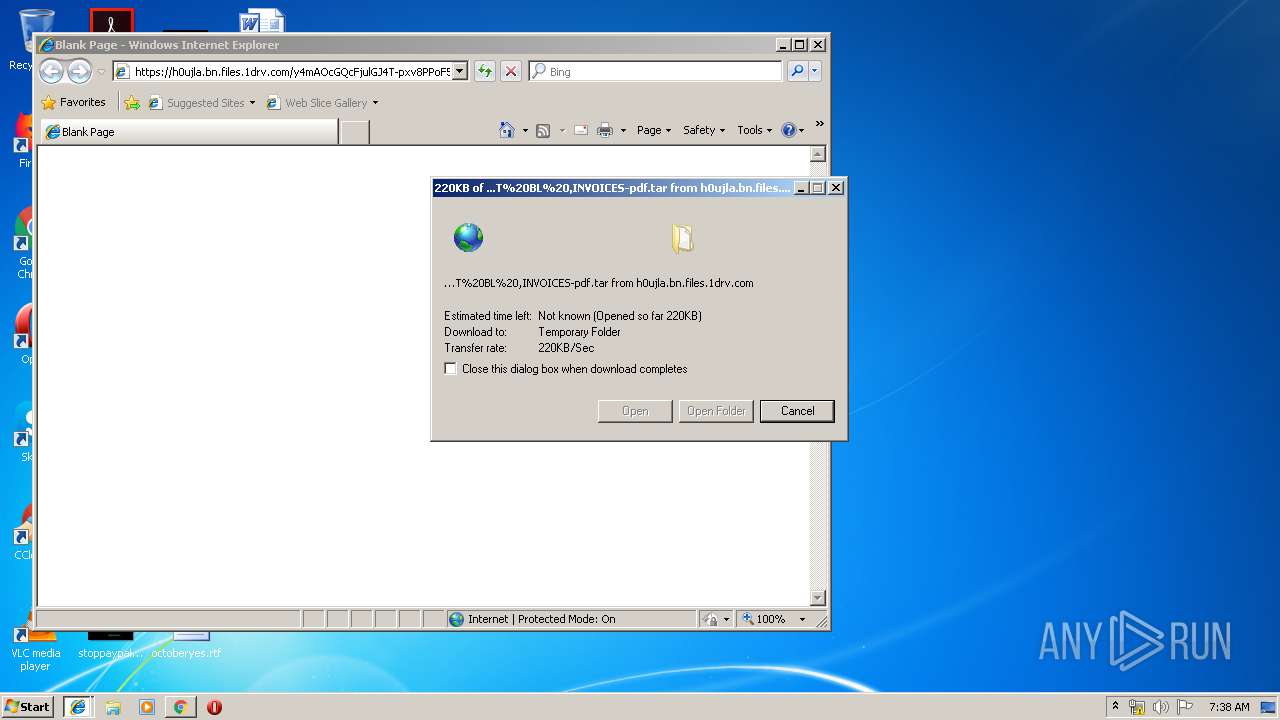
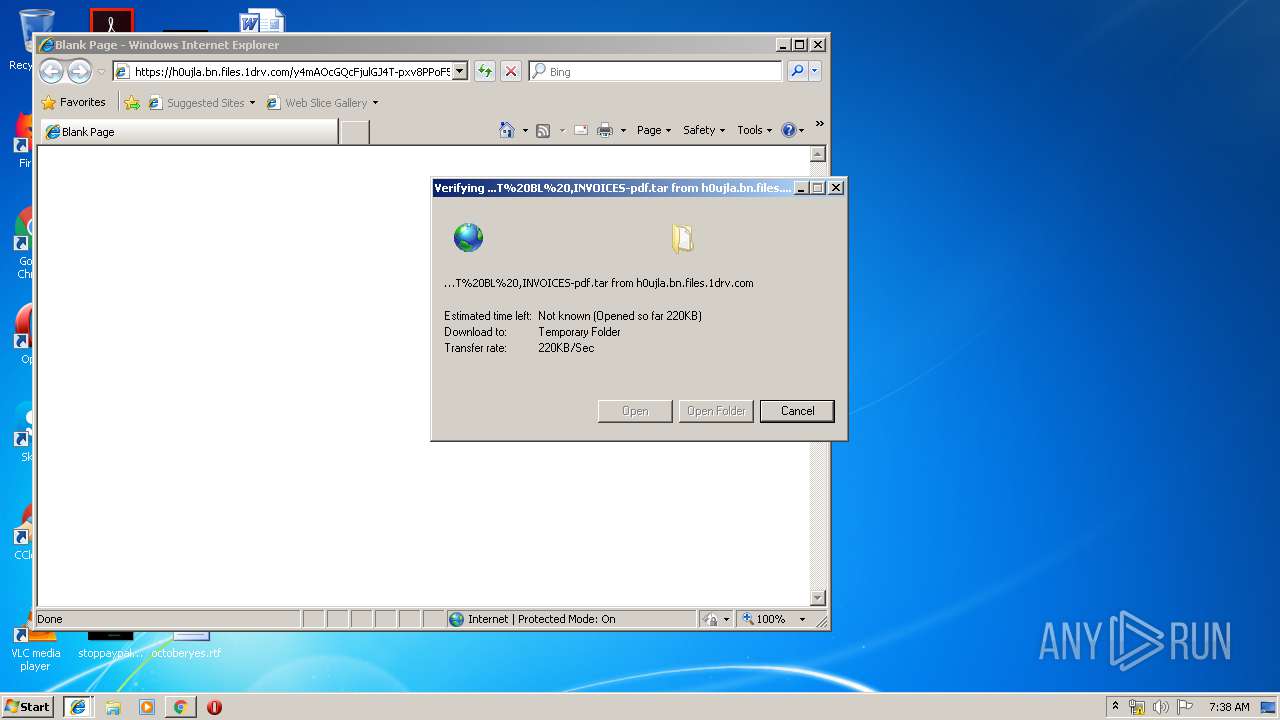
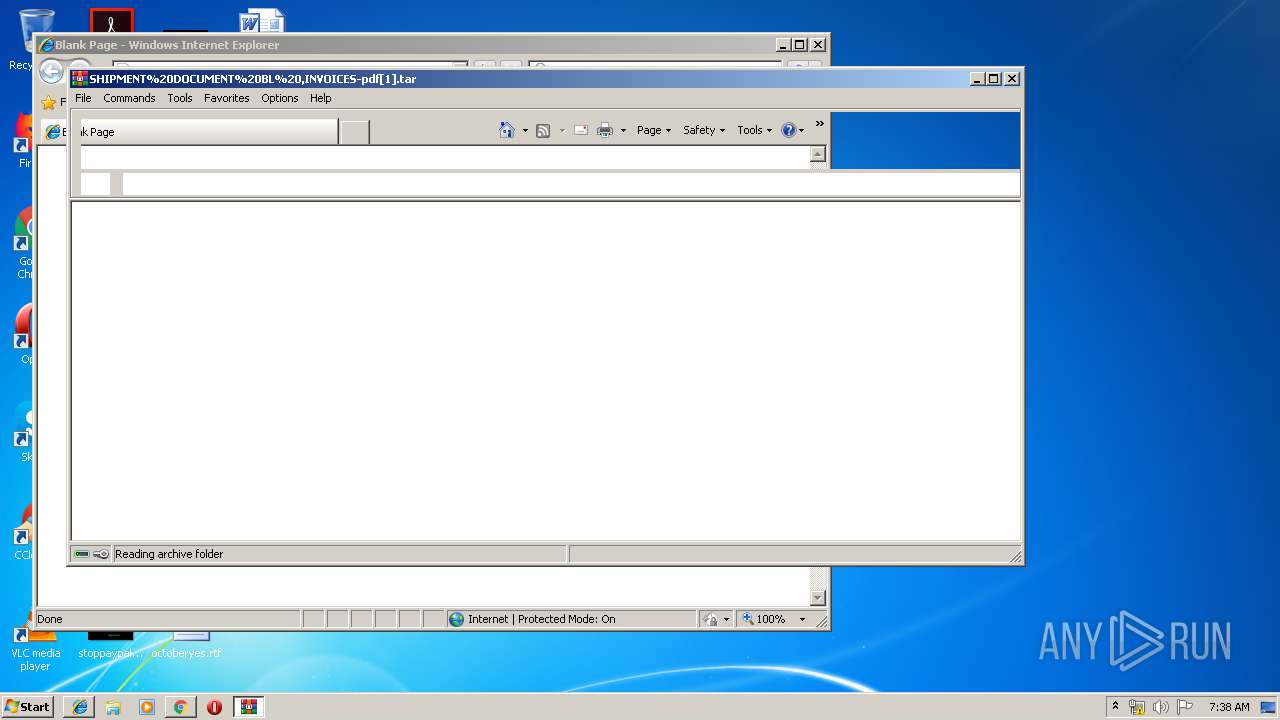
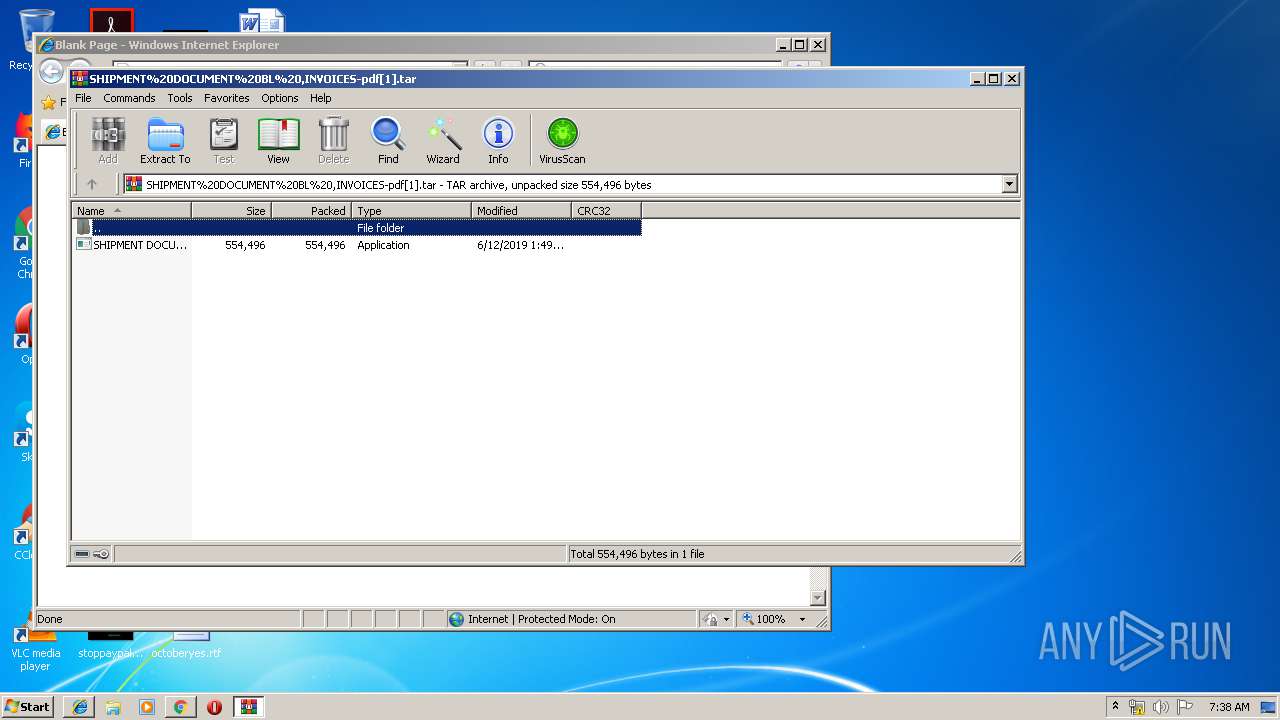
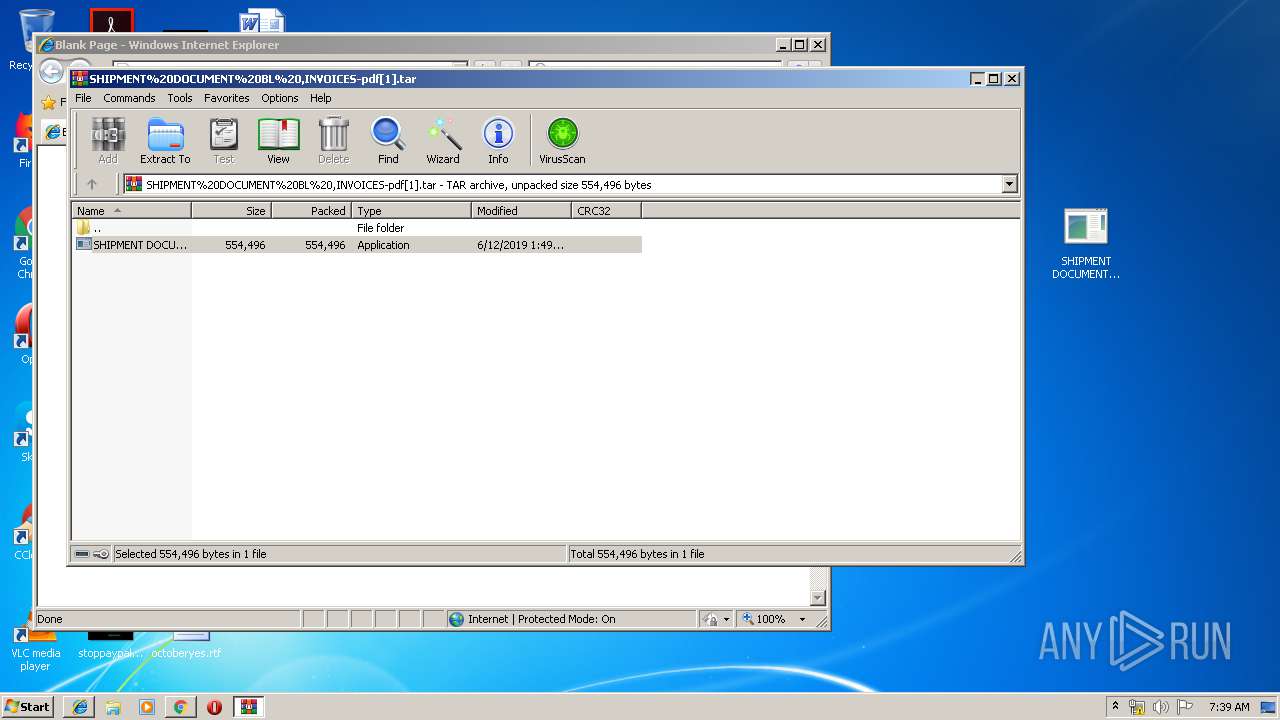
| 856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AA6QAAUC\SHIPMENT%20DOCUMENT%20BL%20,INVOICES-pdf[1].tar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\Desktop\SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe" | C:\Users\admin\Desktop\SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe | SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe | ||||||||||||
User: admin Company: ejasuyoqefakij Integrity Level: MEDIUM Description: ucetadaxoj Exit code: 0 Version: 1.1.1.2 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3064 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11512753656242486938 --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\Desktop\SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe" | C:\Users\admin\Desktop\SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe | — | explorer.exe | |||||||||||
User: admin Company: ejasuyoqefakij Integrity Level: MEDIUM Description: ucetadaxoj Exit code: 0 Version: 1.1.1.2 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3951898115158110506 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 182
Read events
1 959
Write events
215
Delete events
8
Modification events
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3276-13204795034935625 |
Value: 259 | |||
| (PID) Process: | (3276) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
65
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c1a2eefa-3fde-41cf-b3d9-571036810192.tmp | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
16
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3064 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 13.107.42.12:443 | h0ujla.bn.files.1drv.com | Microsoft Corporation | US | suspicious |
3276 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.22.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
1008 | SHIPMENT DOCUMENT BL ,INVOICES-pdf.exe | 199.193.7.228:587 | smtp.privateemail.com | Namecheap, Inc. | US | unknown |
3064 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
h0ujla.bn.files.1drv.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
smtp.privateemail.com |
| malicious |