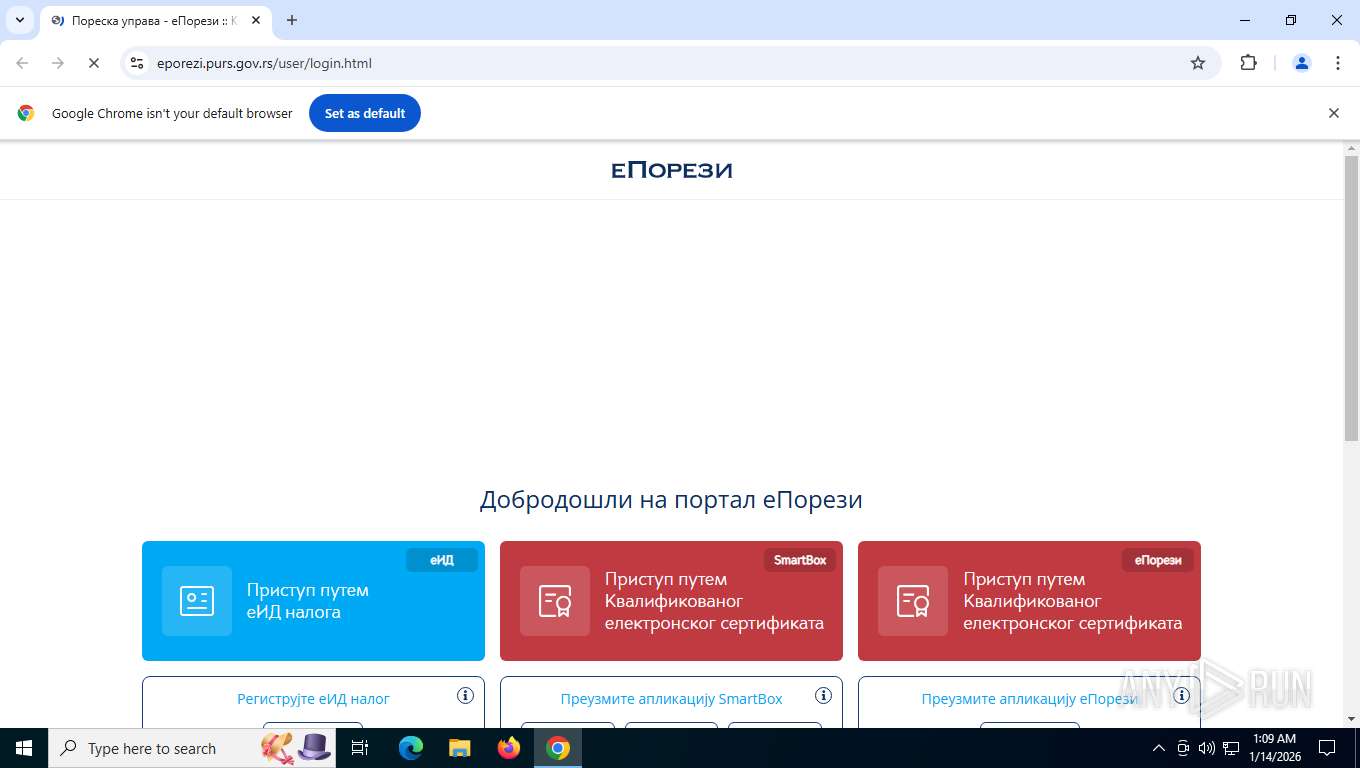
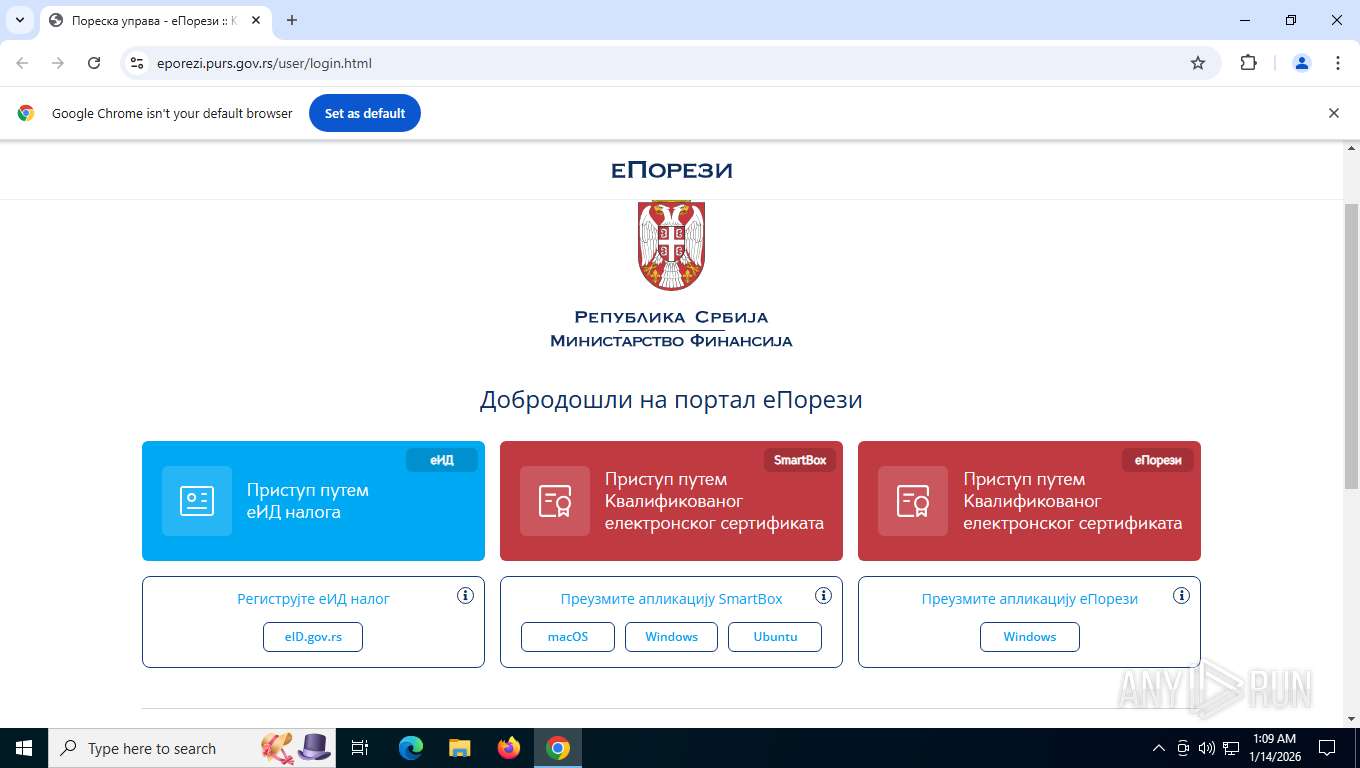
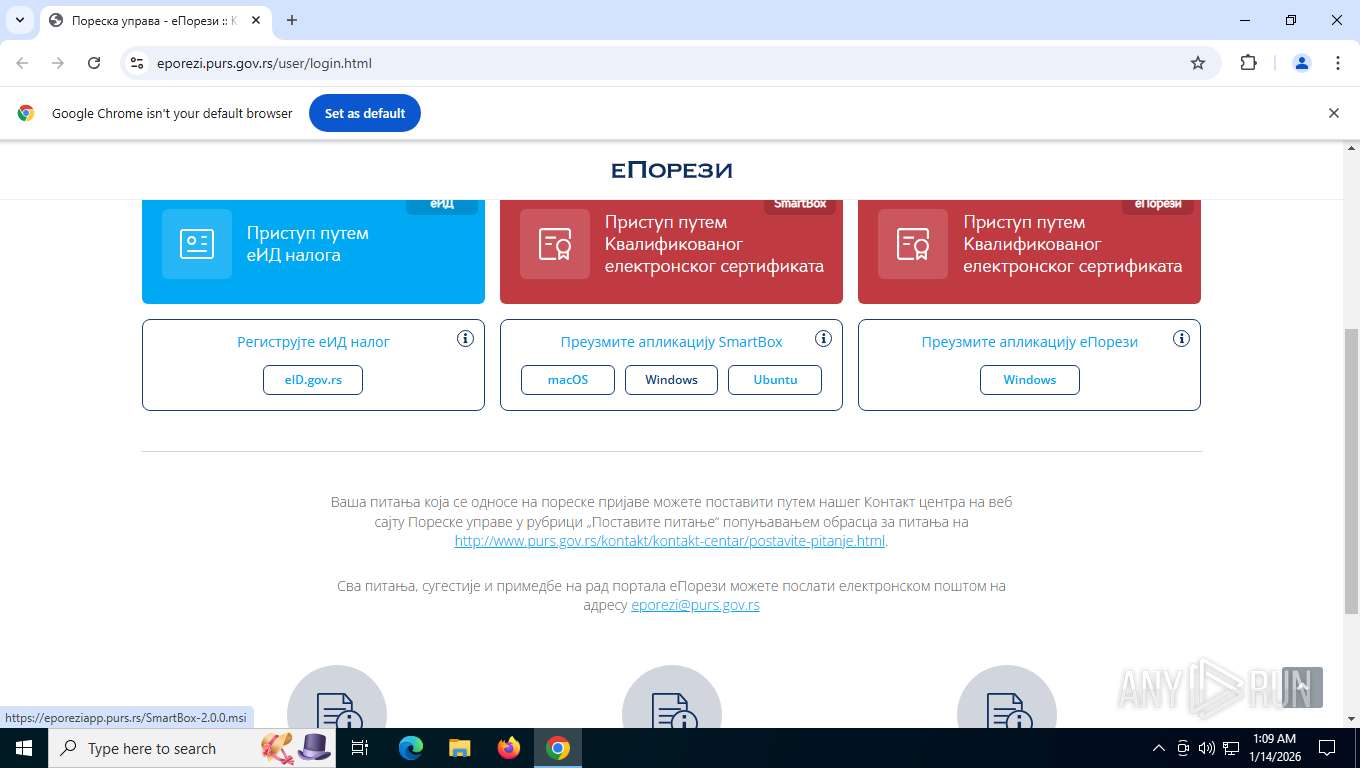
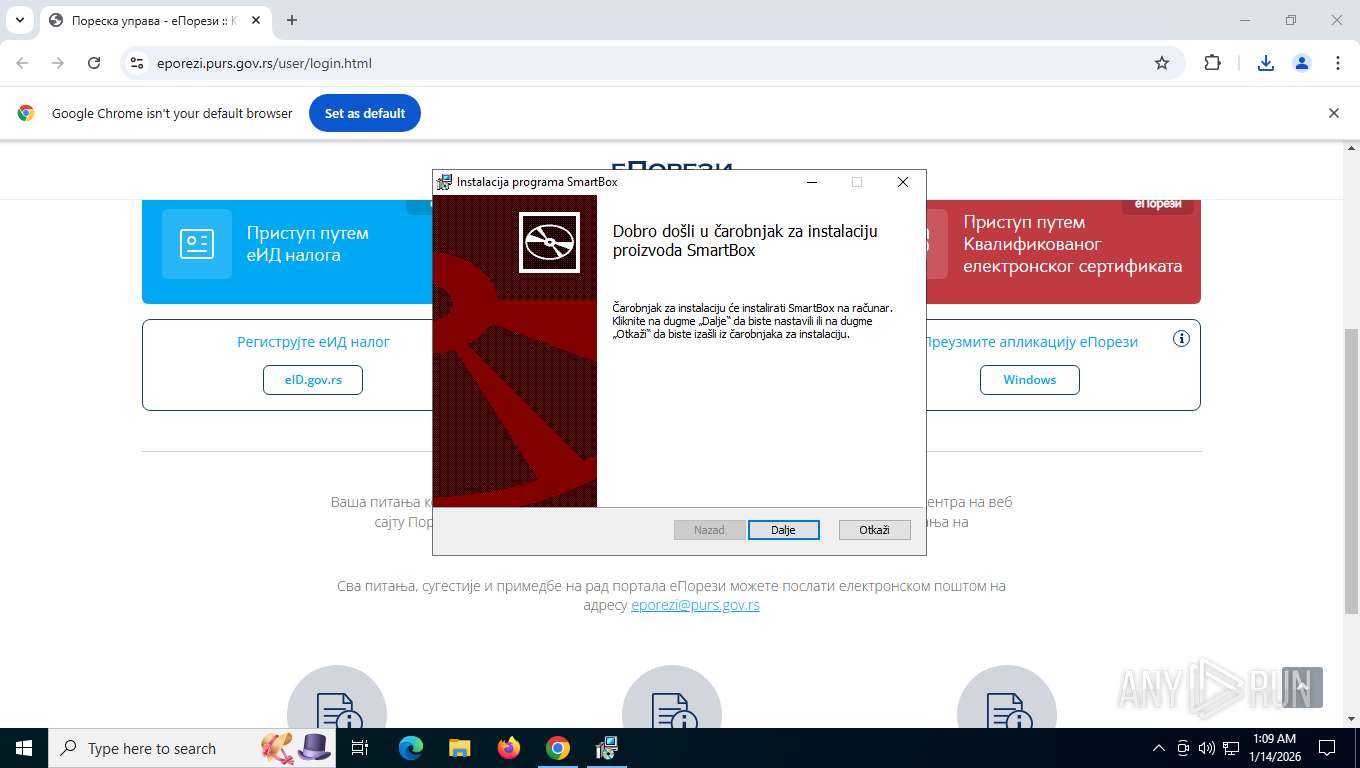
| URL: | https://eporezi.purs.gov.rs/user/login.html |
| Full analysis: | https://app.any.run/tasks/ca08faba-d6dc-40c8-a591-8106f75f9240 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2026, 06:09:16 |
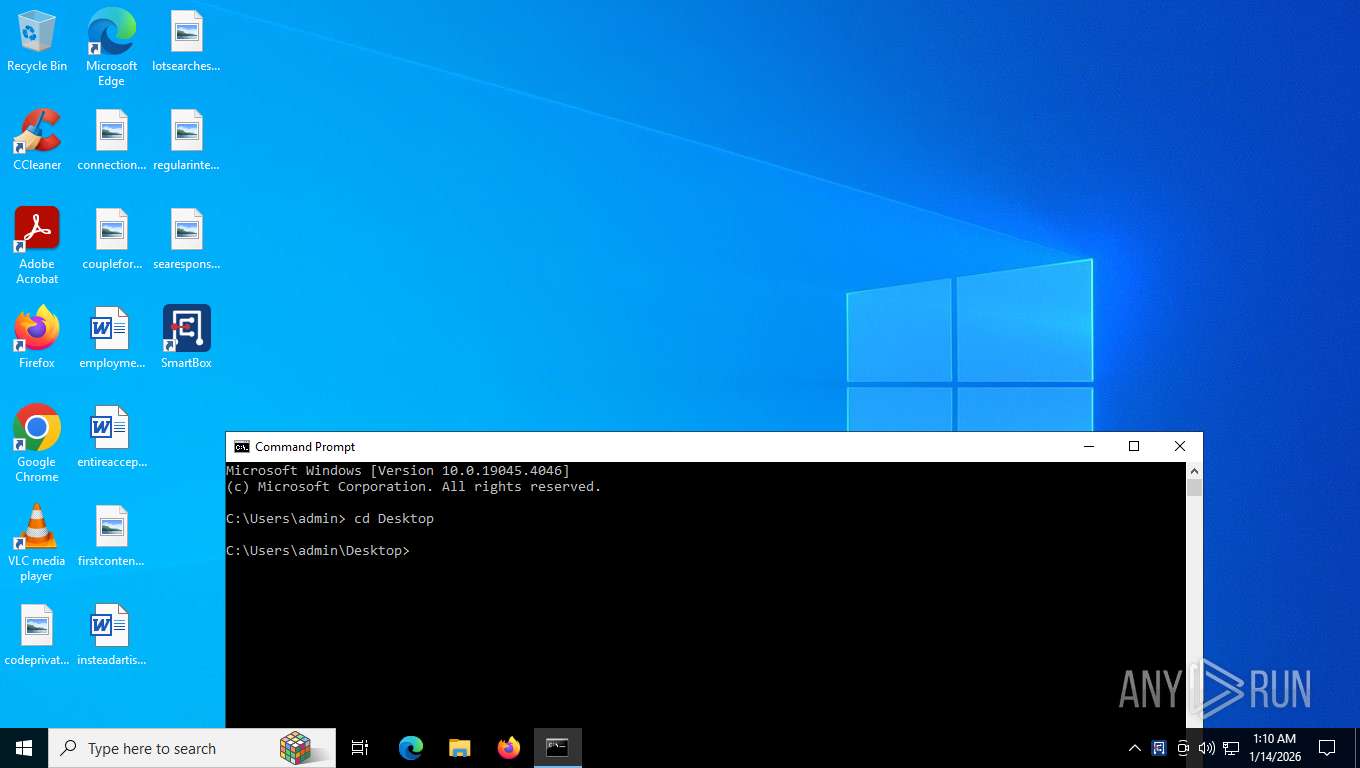
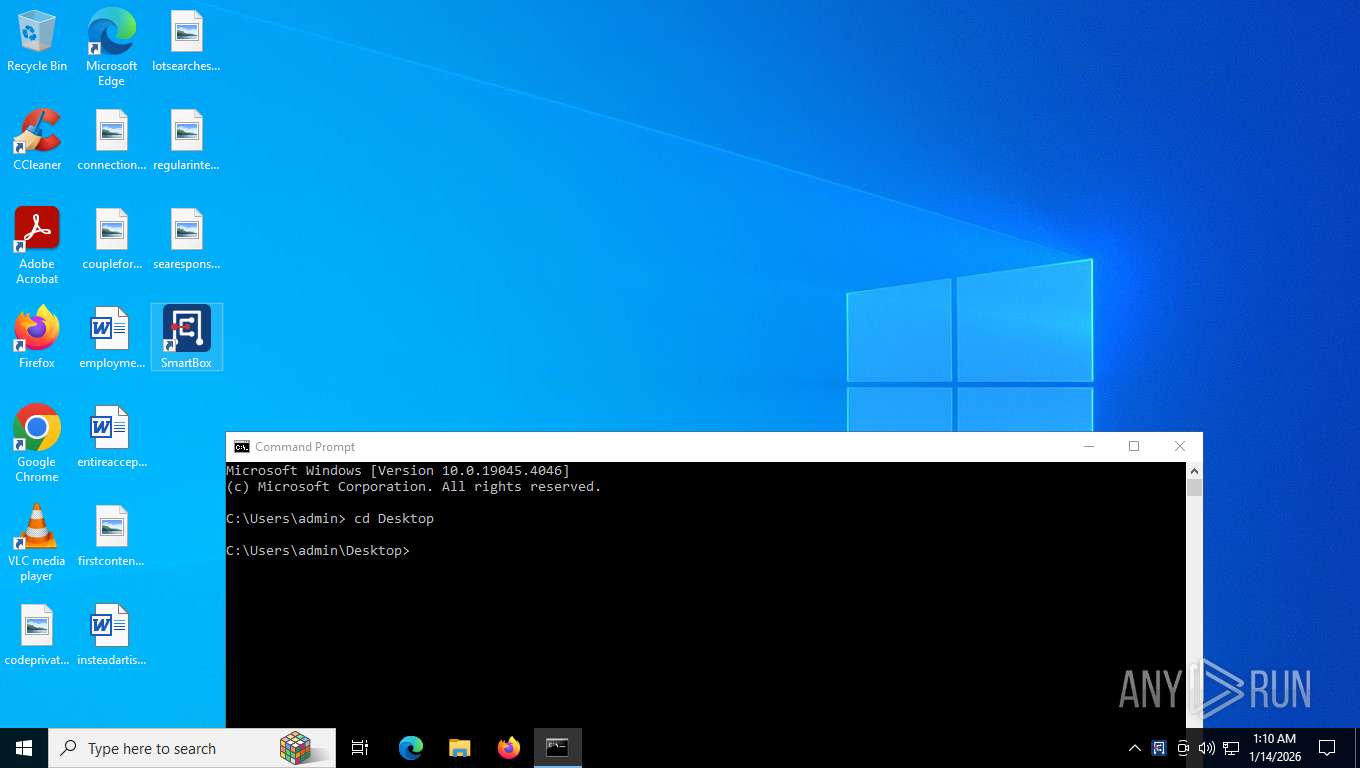
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
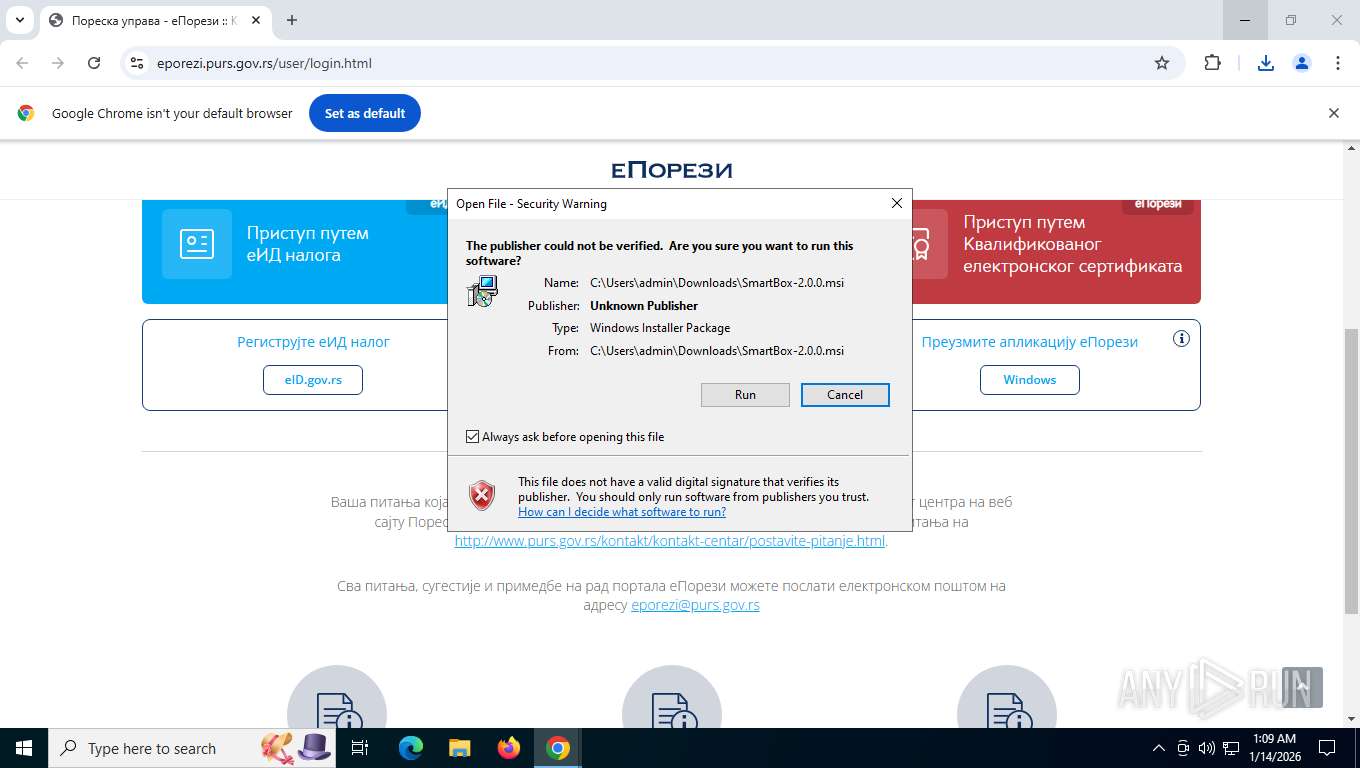
| MD5: | 4F03C89EDC2F9A9C7BAD01ABB1B089B3 |
| SHA1: | 1F1071F3650A7F184105EFB54084FDF232338BFF |
| SHA256: | EFBB44E895F97068159C163AEAAE82EE186243EB225A6EF38FECD562683723CF |
| SSDEEP: | 3:N8dVCW65D0:2d8DB0 |
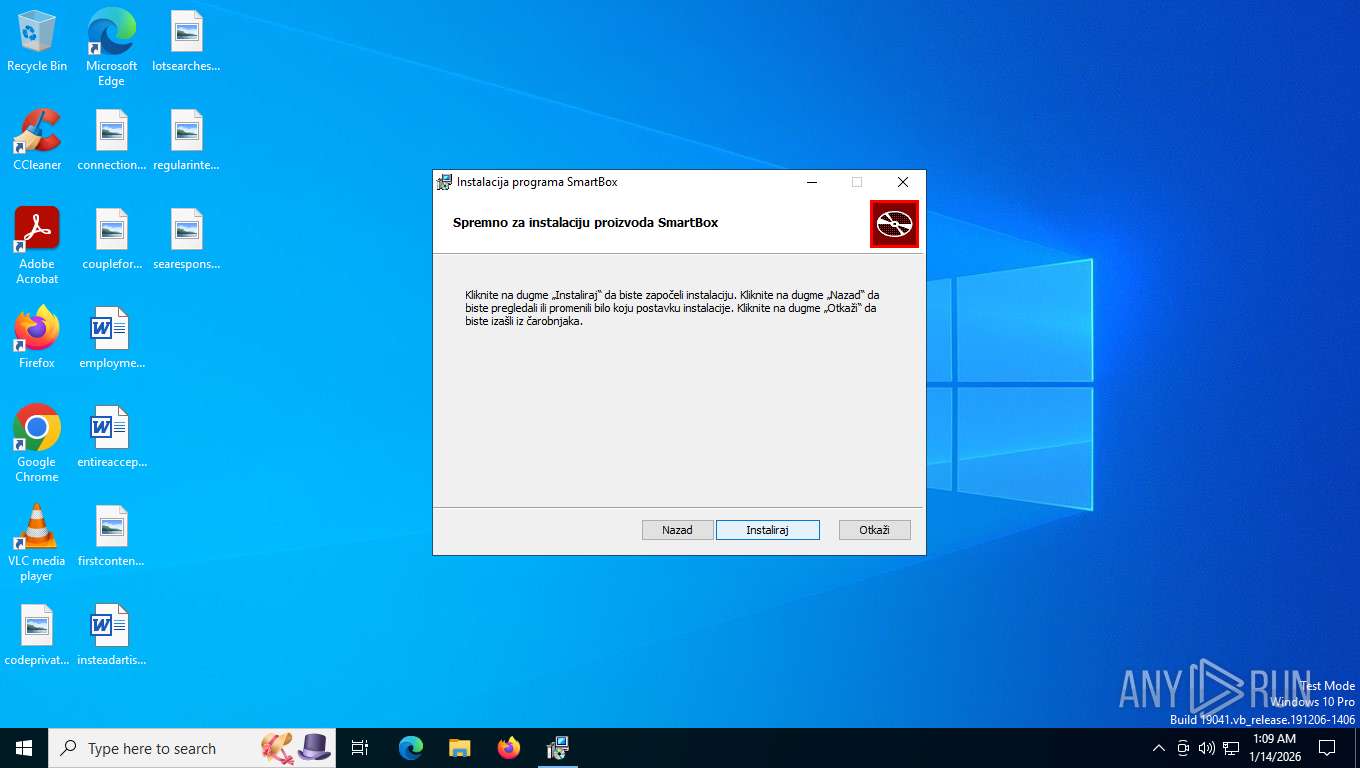
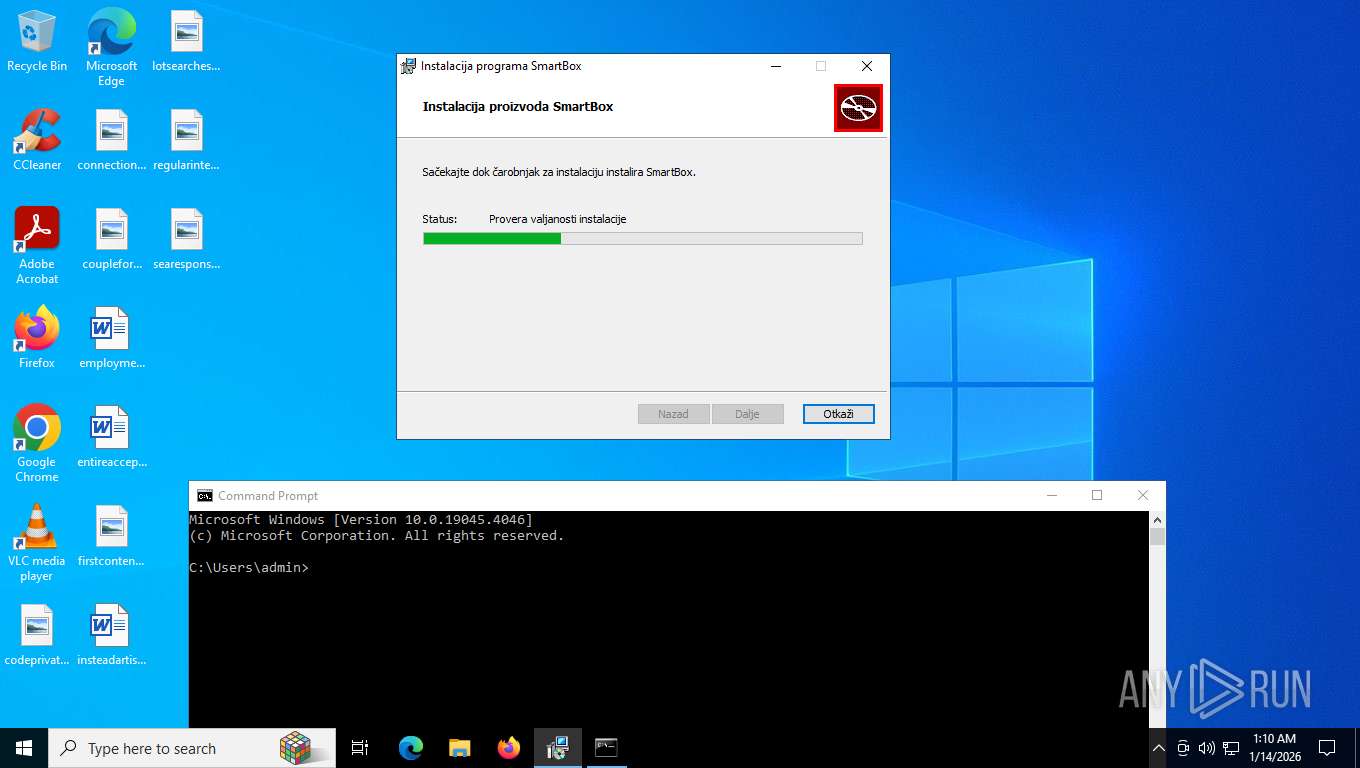
MALICIOUS
No malicious indicators.SUSPICIOUS
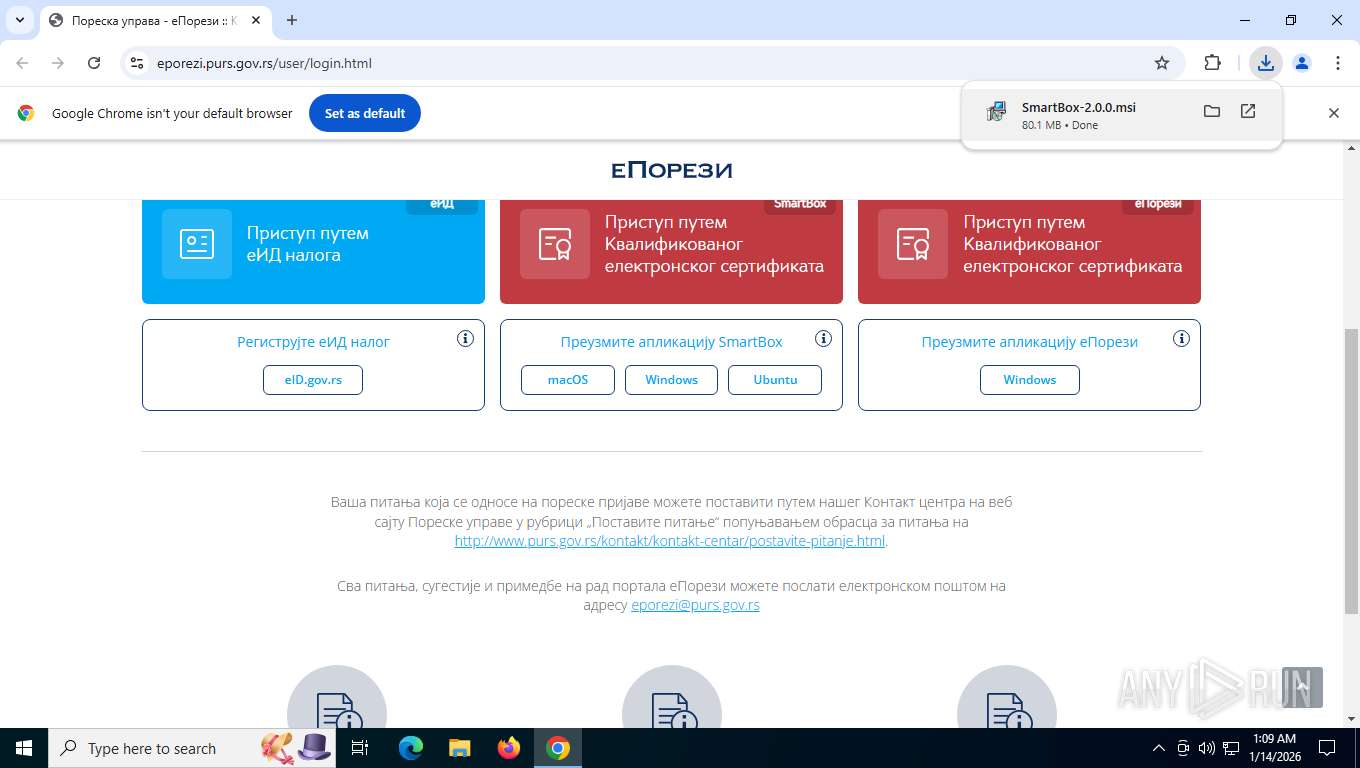
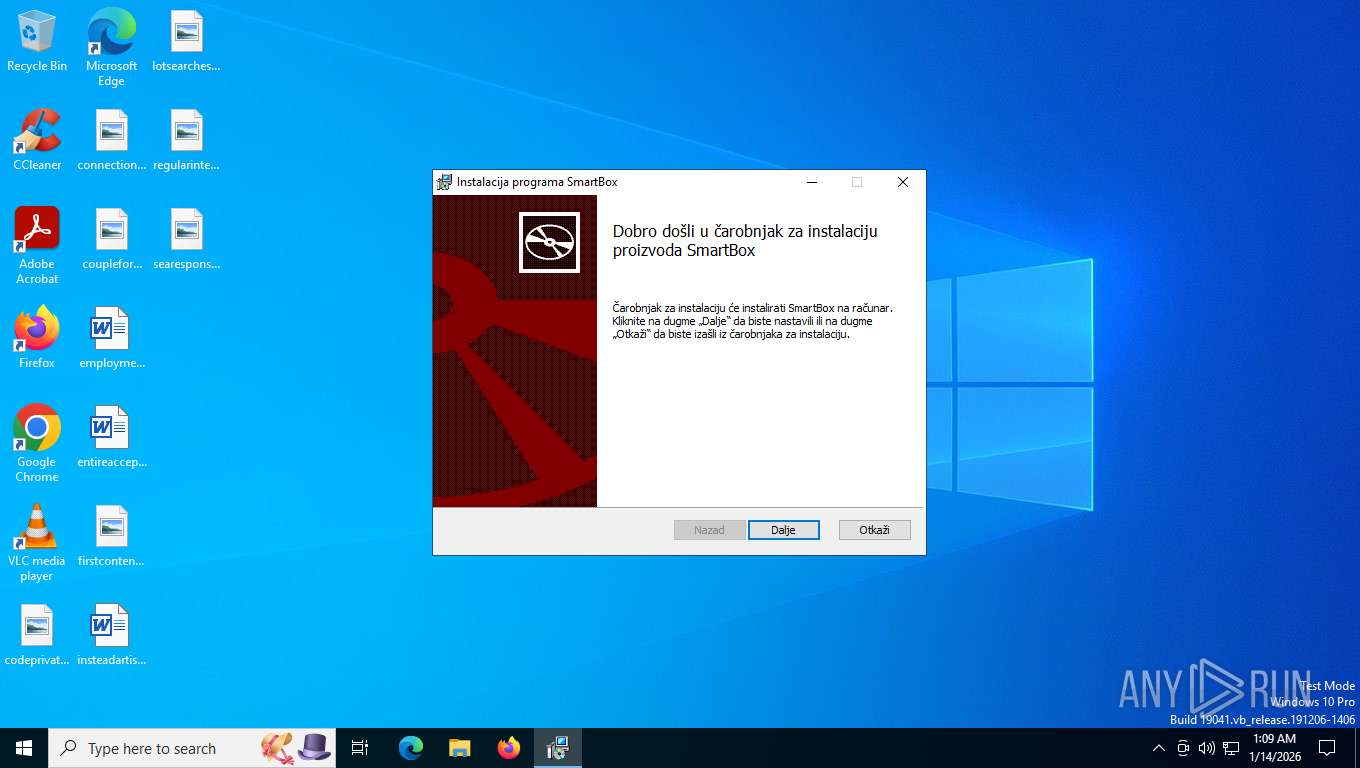
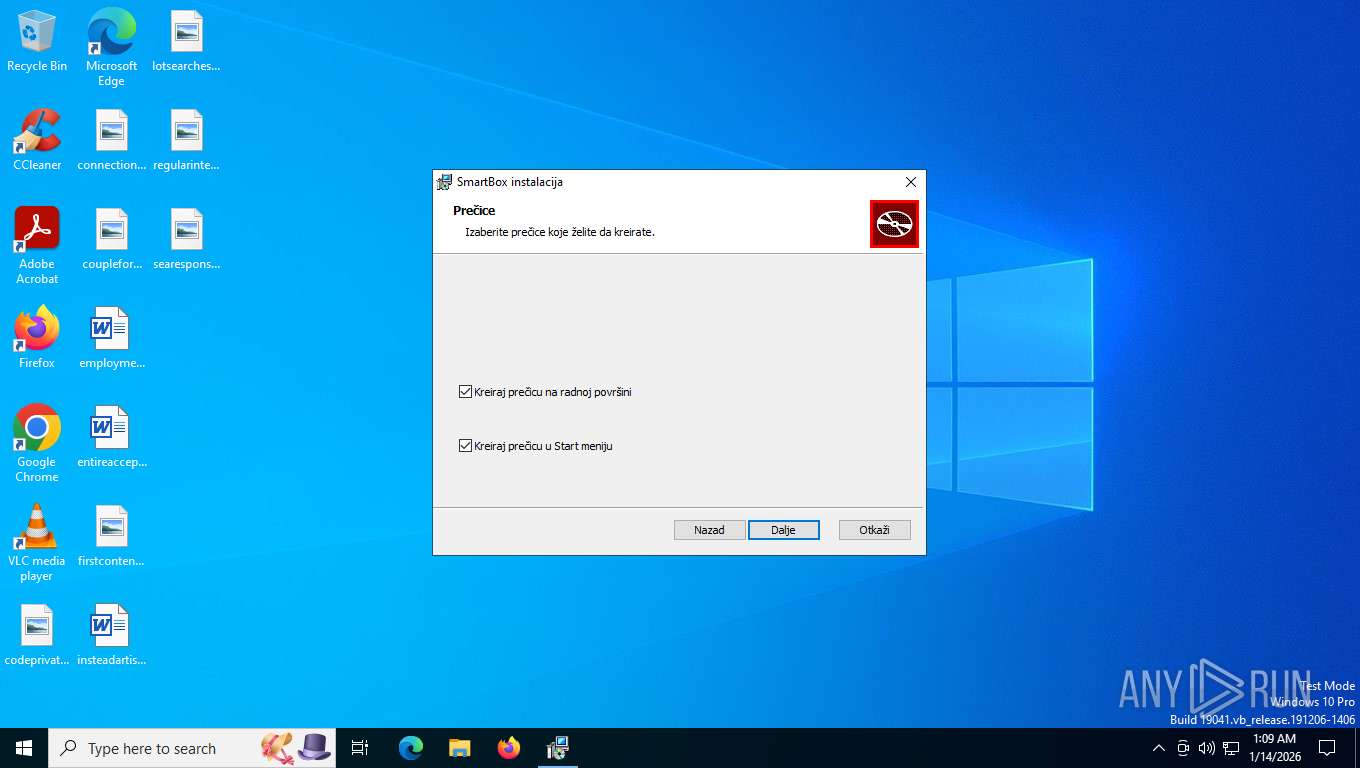
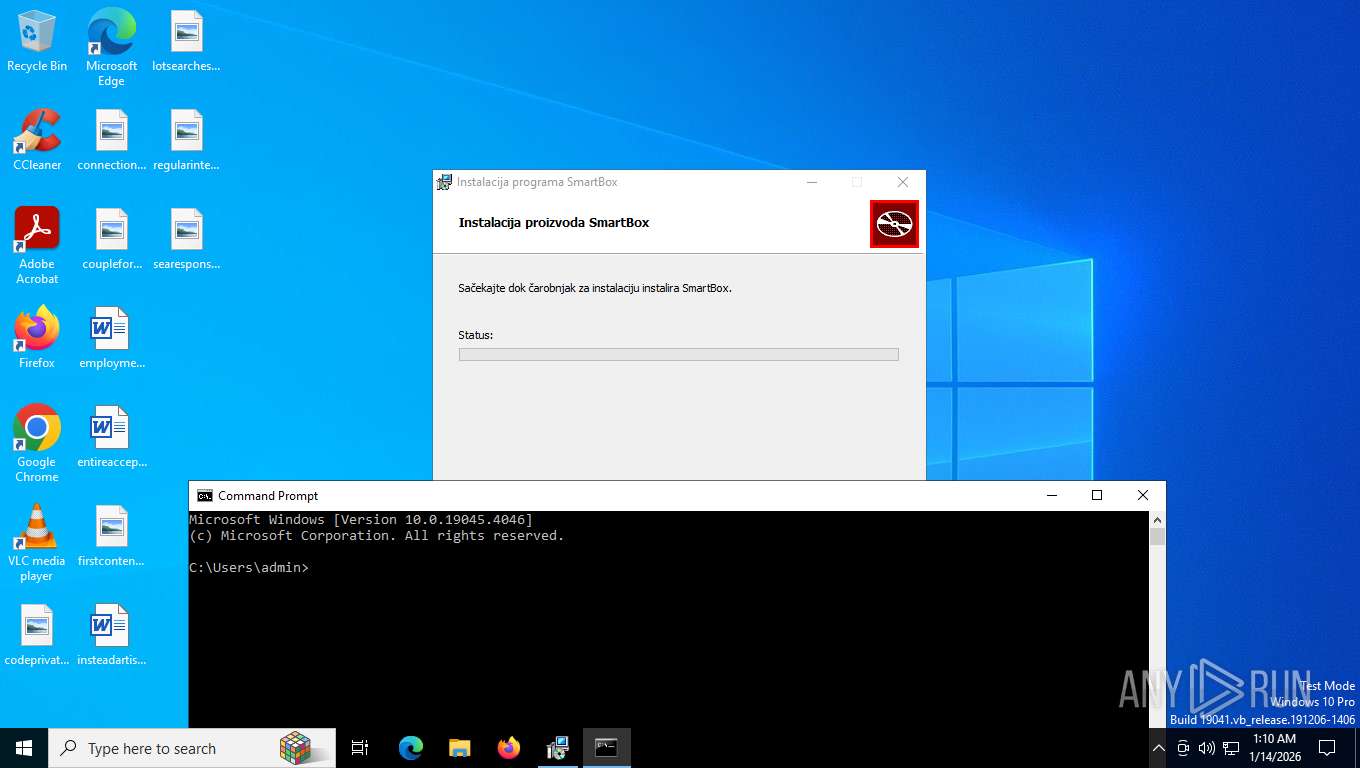
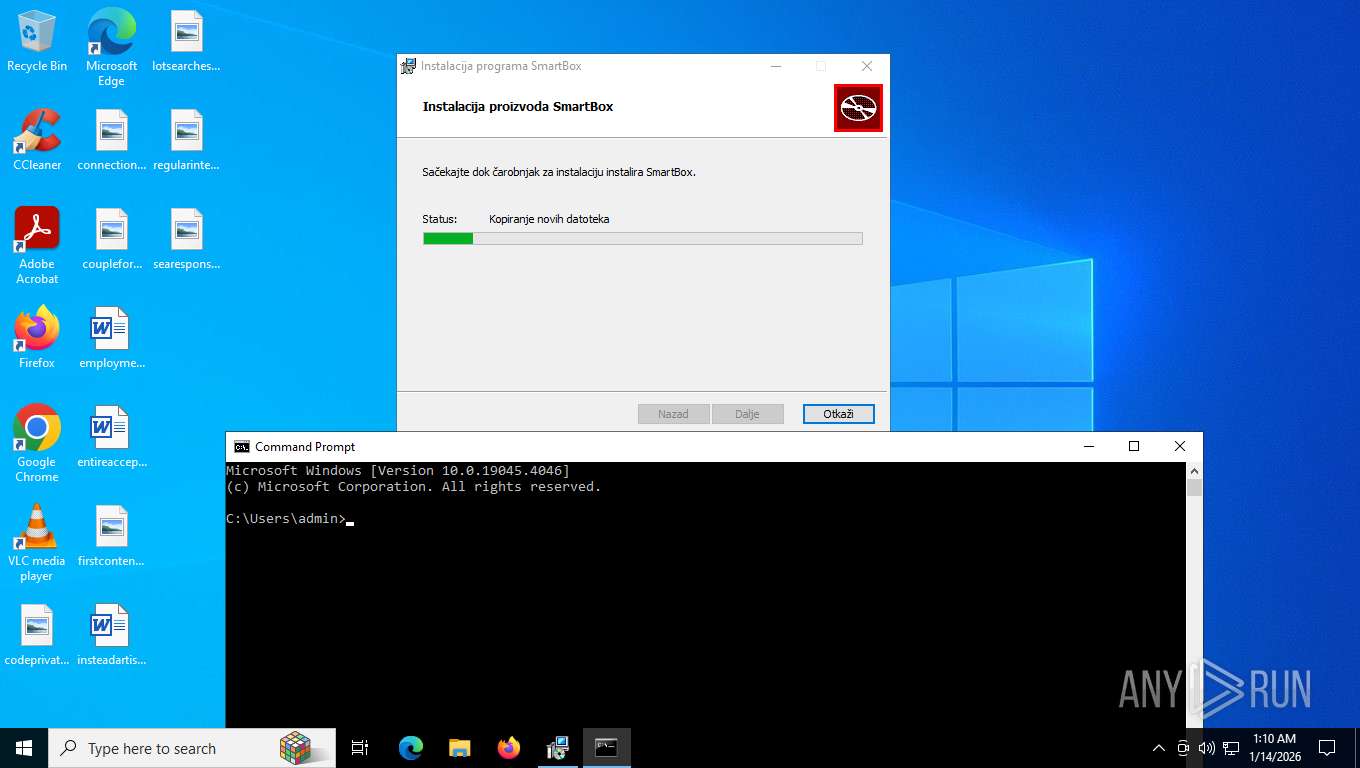
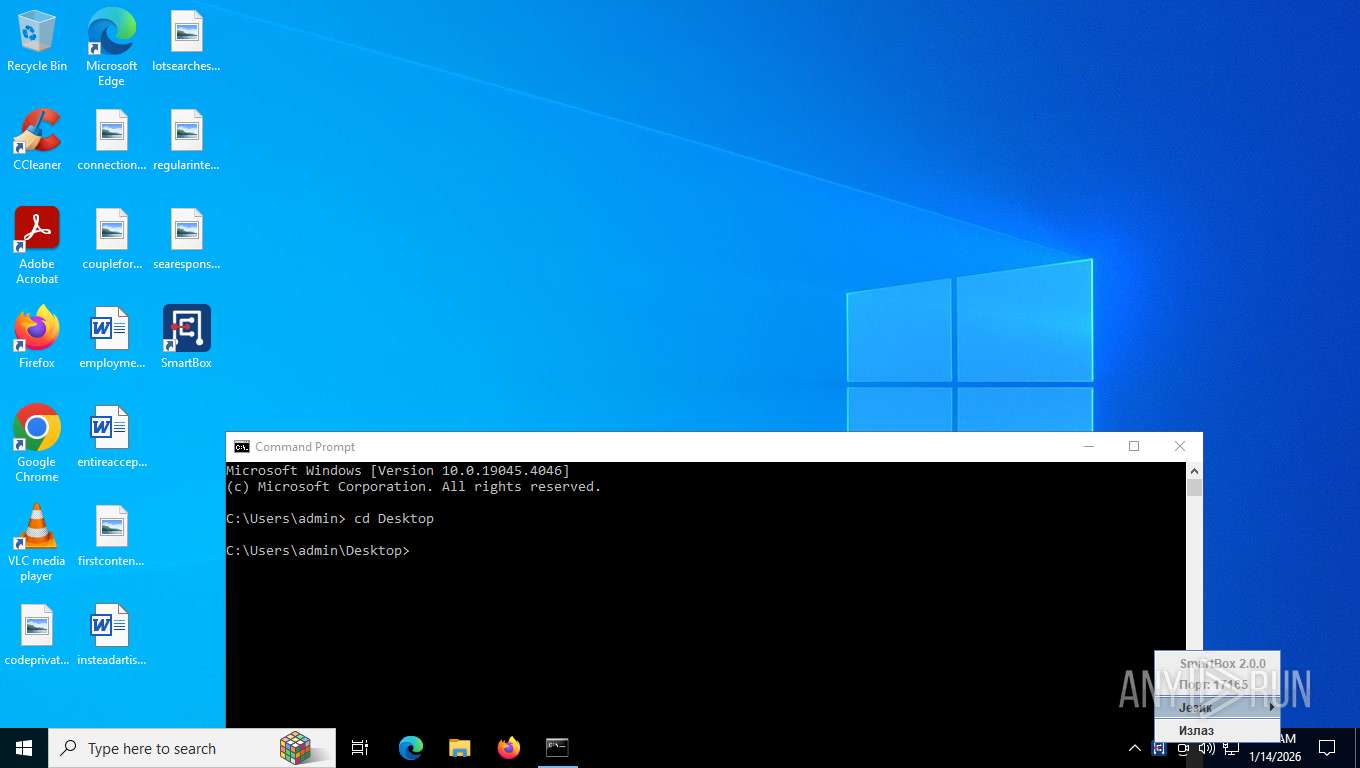
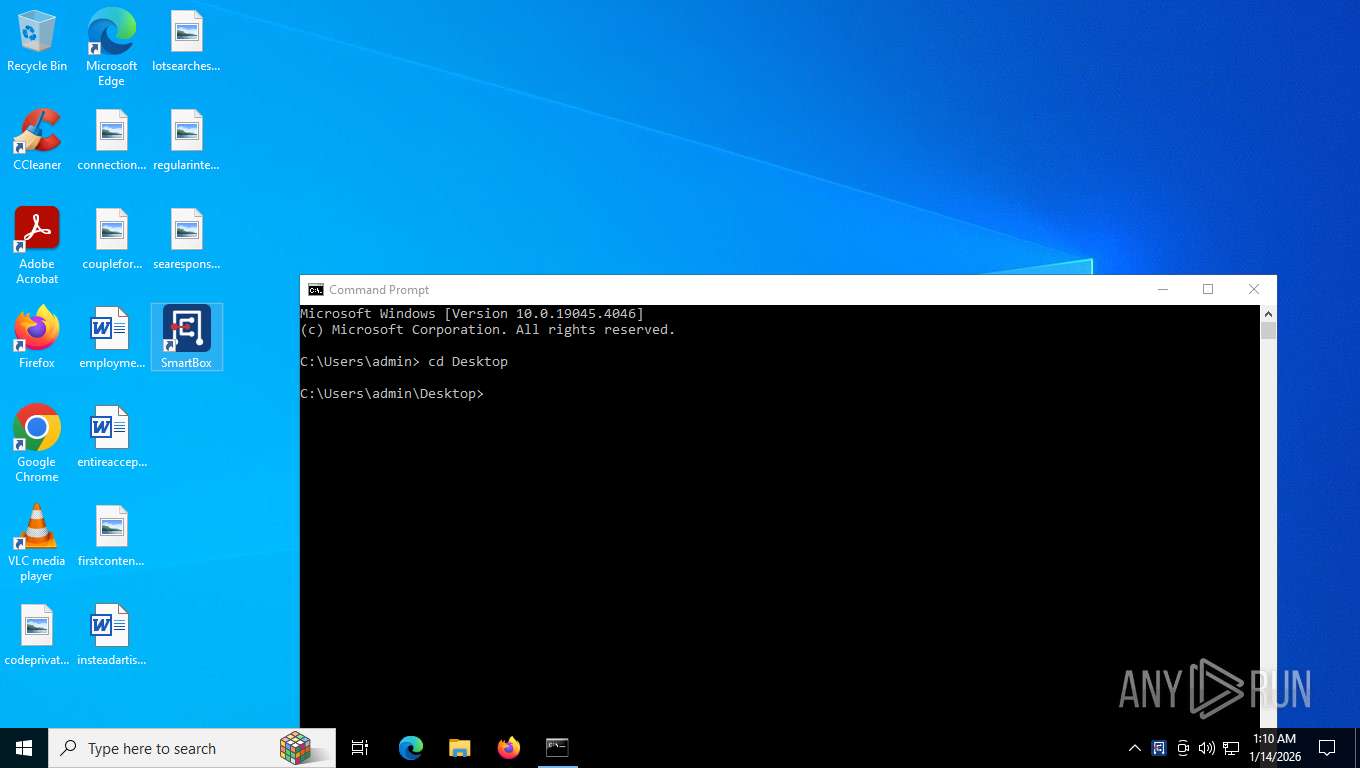
Application launched itself
- msiexec.exe (PID: 8172)
- SmartBox.exe (PID: 3656)
- SmartBox.exe (PID: 1840)
- SmartBox.exe (PID: 7852)
- SmartBox.exe (PID: 1156)
- SmartBox.exe (PID: 32)
- SmartBox.exe (PID: 7300)
- SmartBox.exe (PID: 7828)
- SmartBox.exe (PID: 6916)
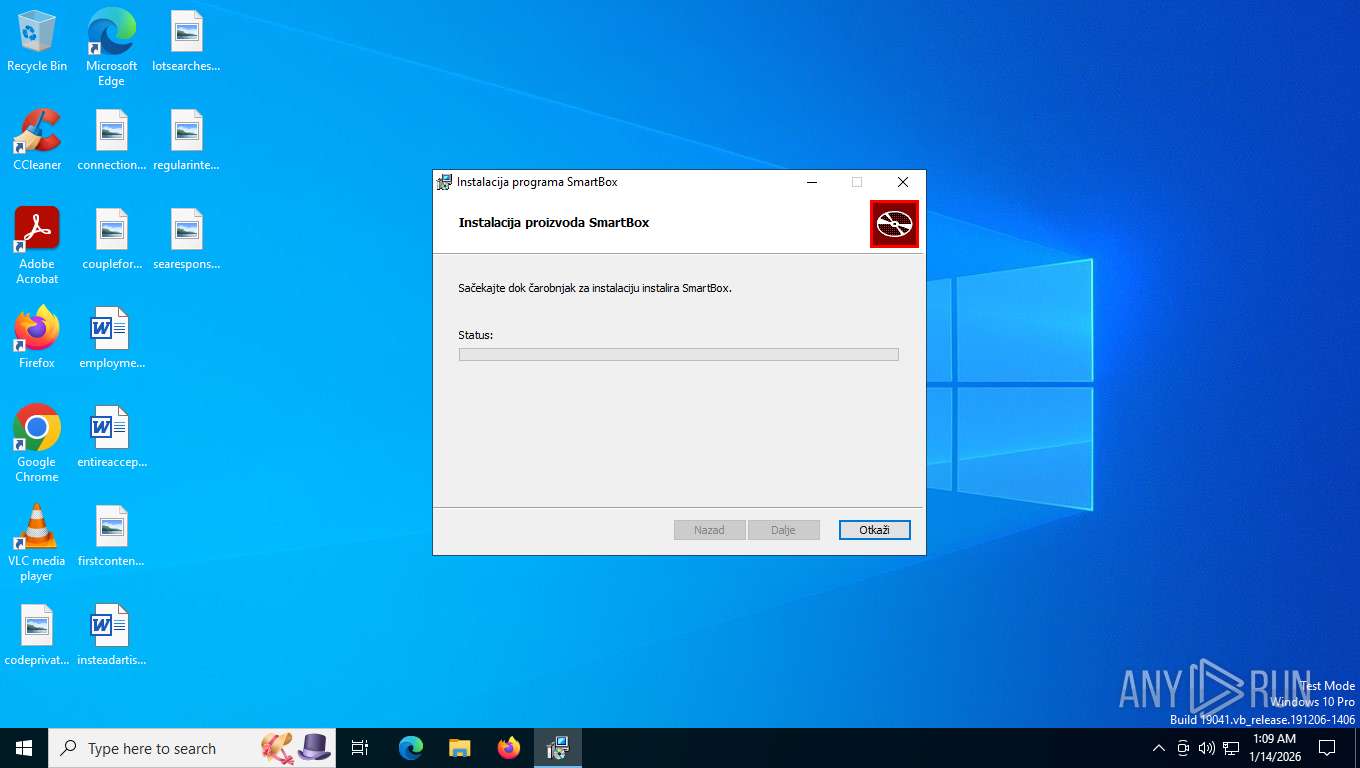
Executes as Windows Service
- VSSVC.exe (PID: 7212)
The process drops C-runtime libraries
- msiexec.exe (PID: 8172)
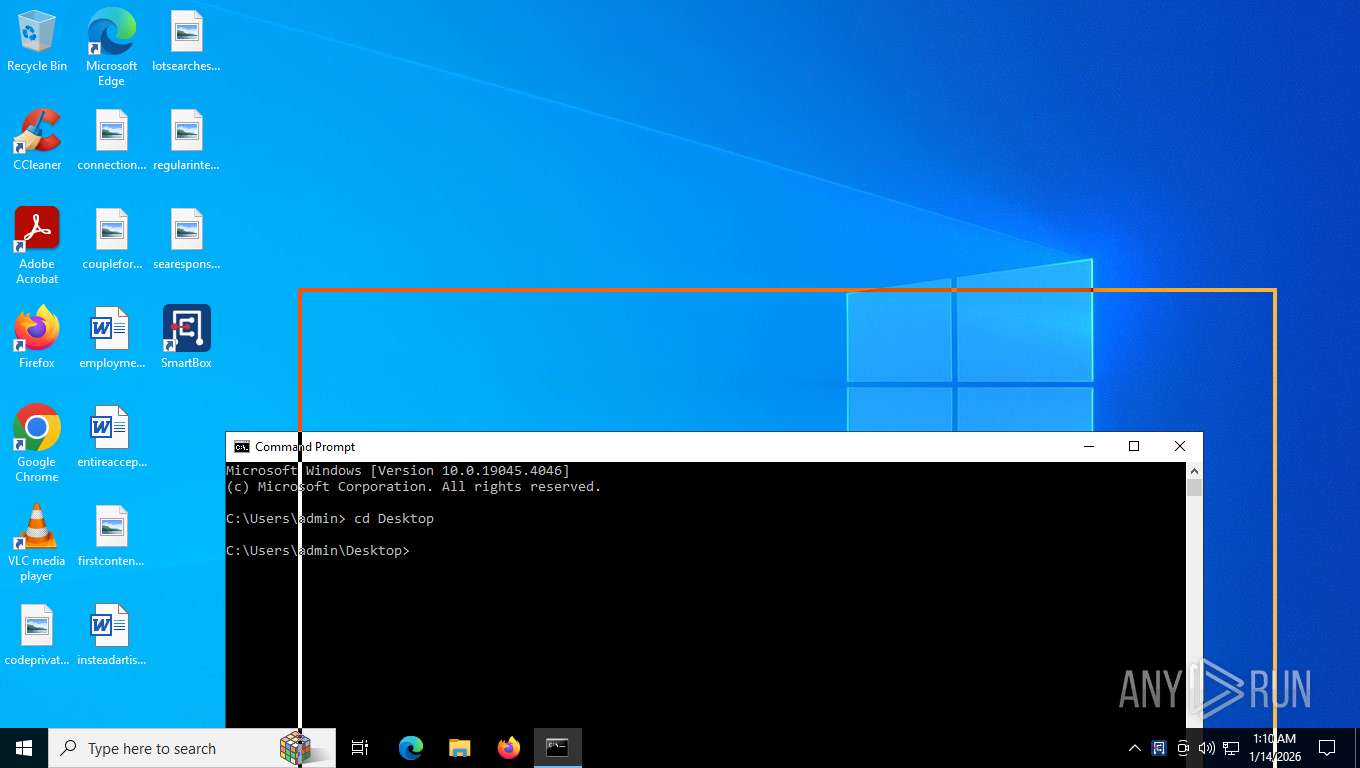
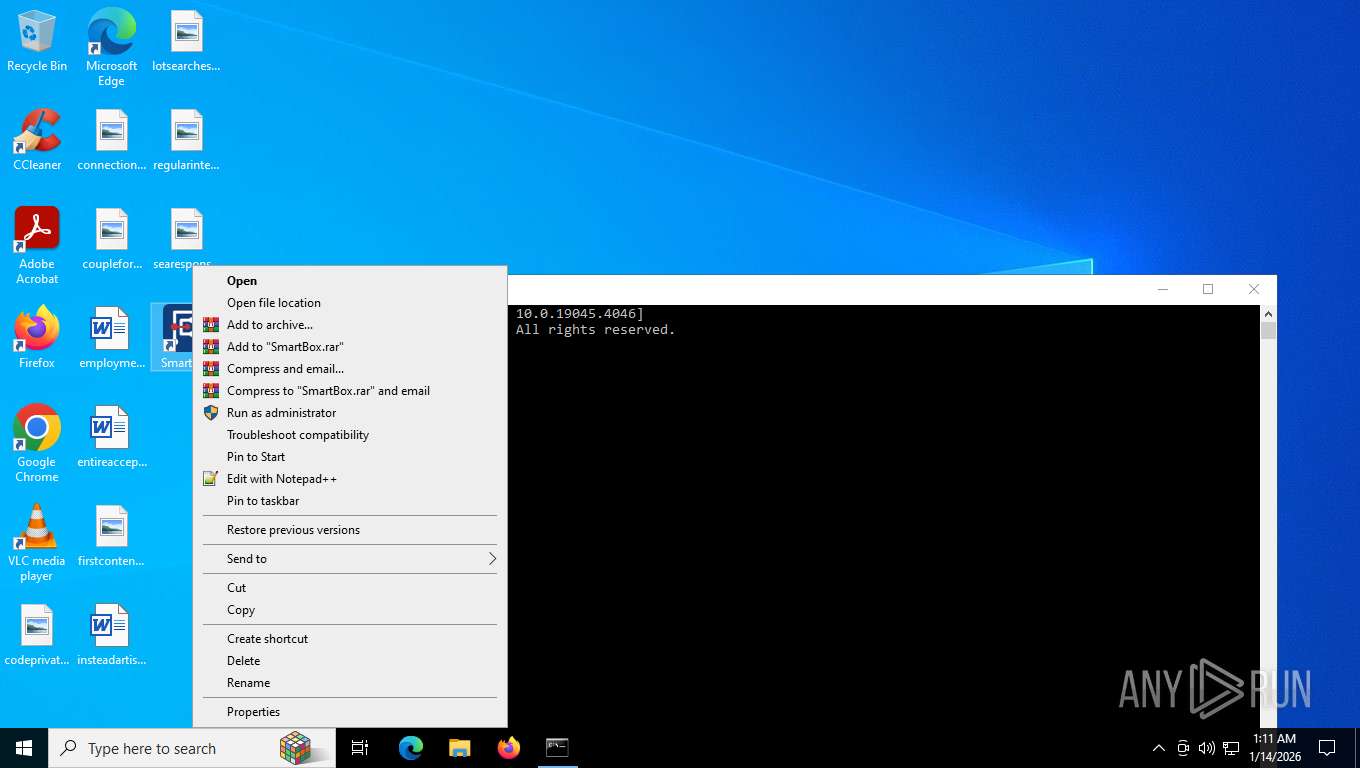
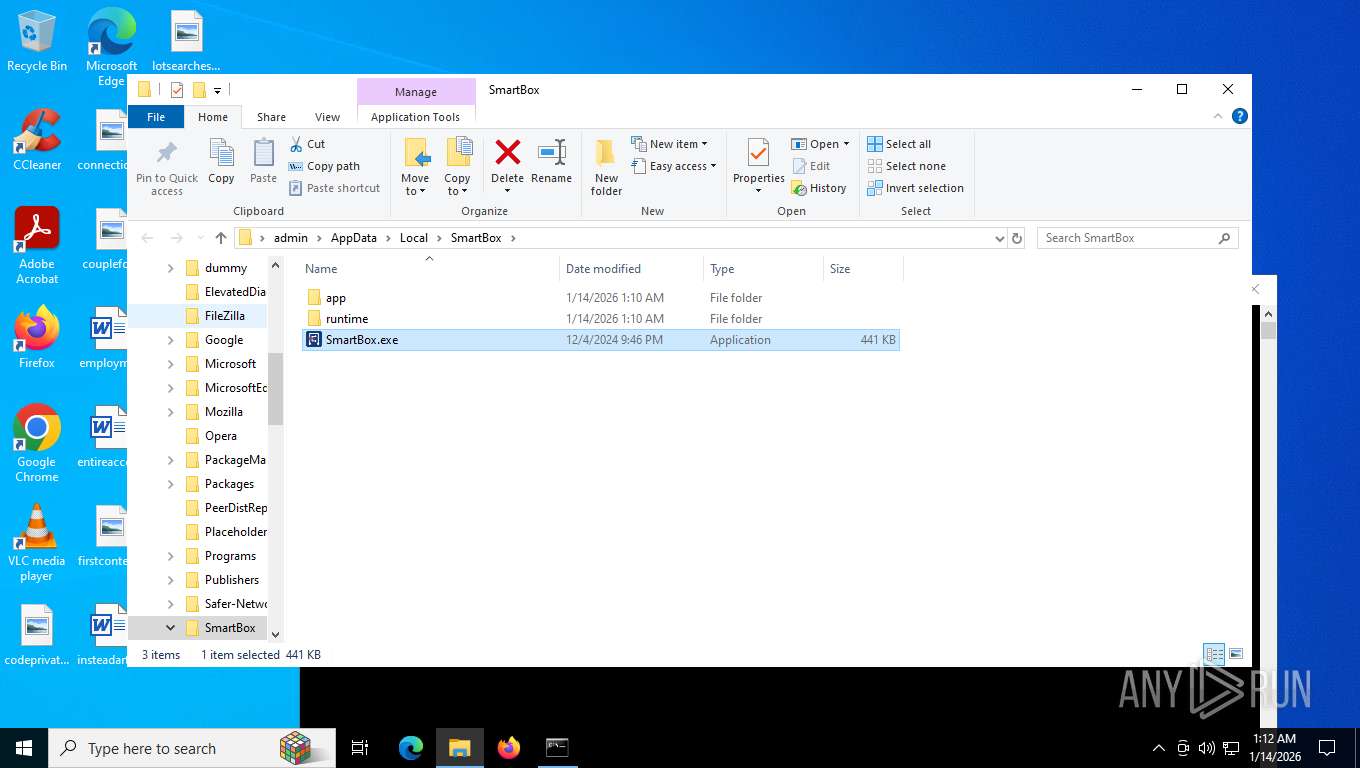
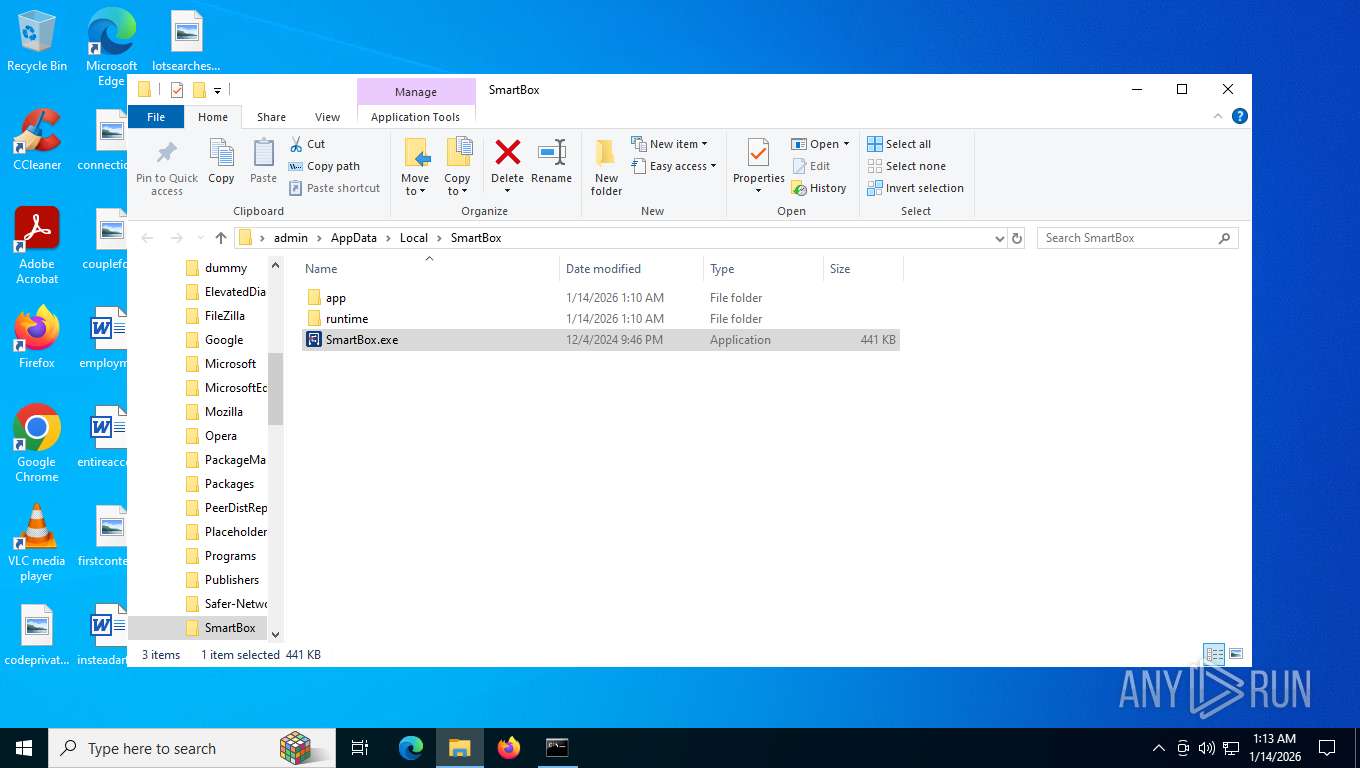
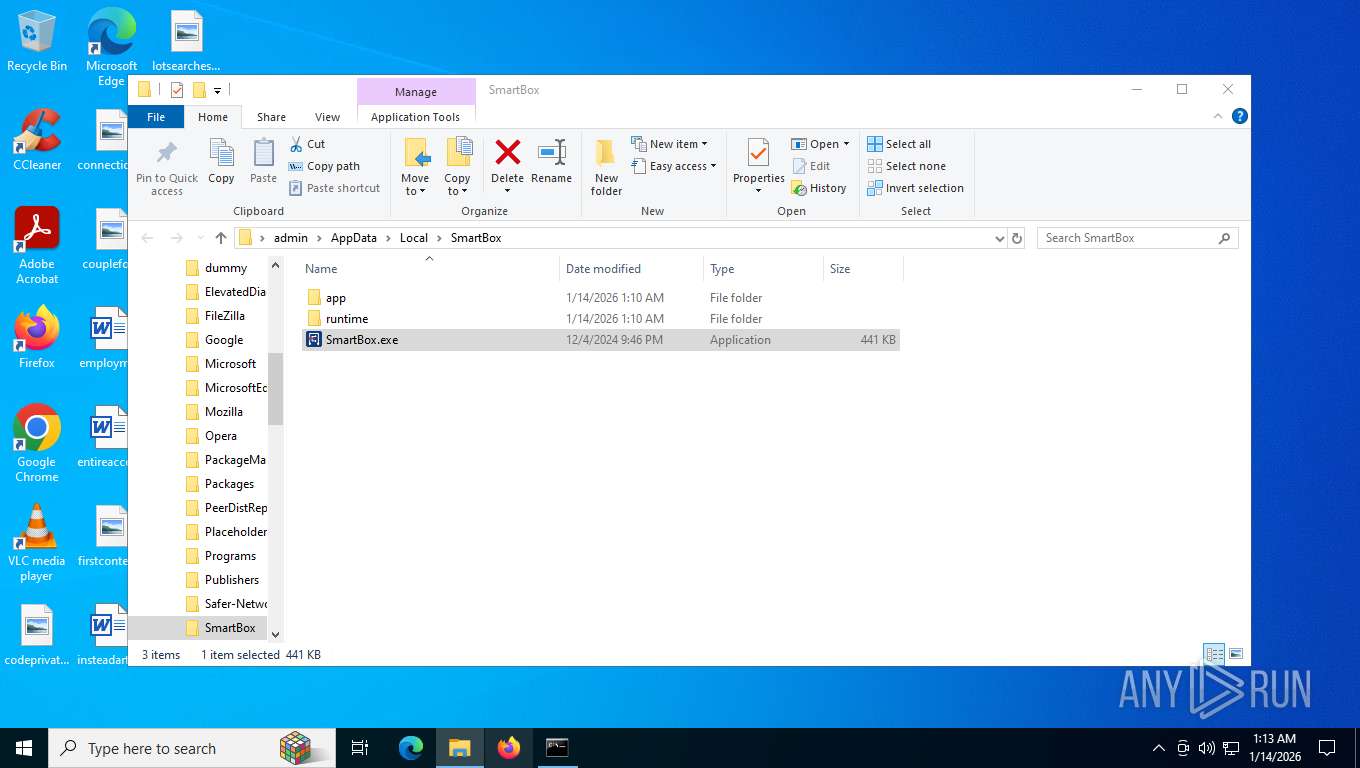
Executable content was dropped or overwritten
- SmartBox.exe (PID: 6272)
Process drops legitimate windows executable
- msiexec.exe (PID: 8172)
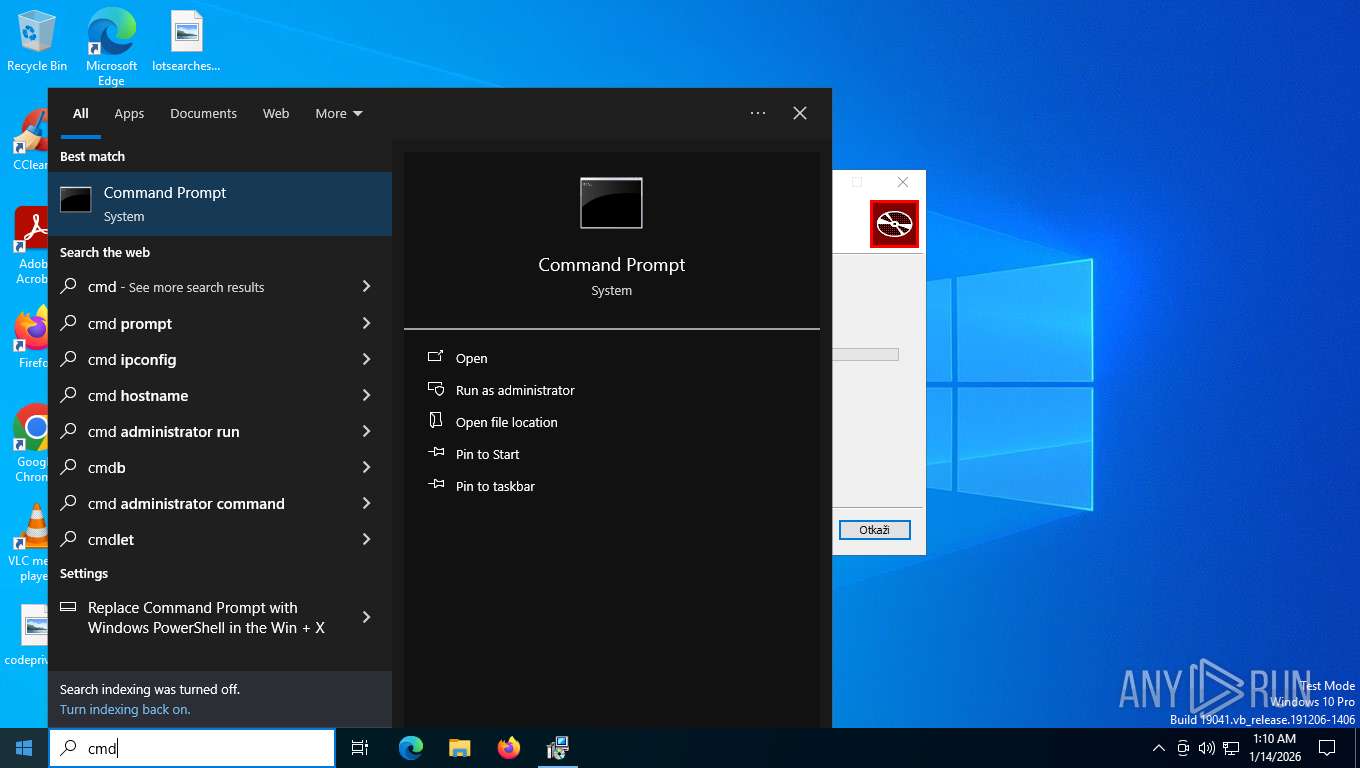
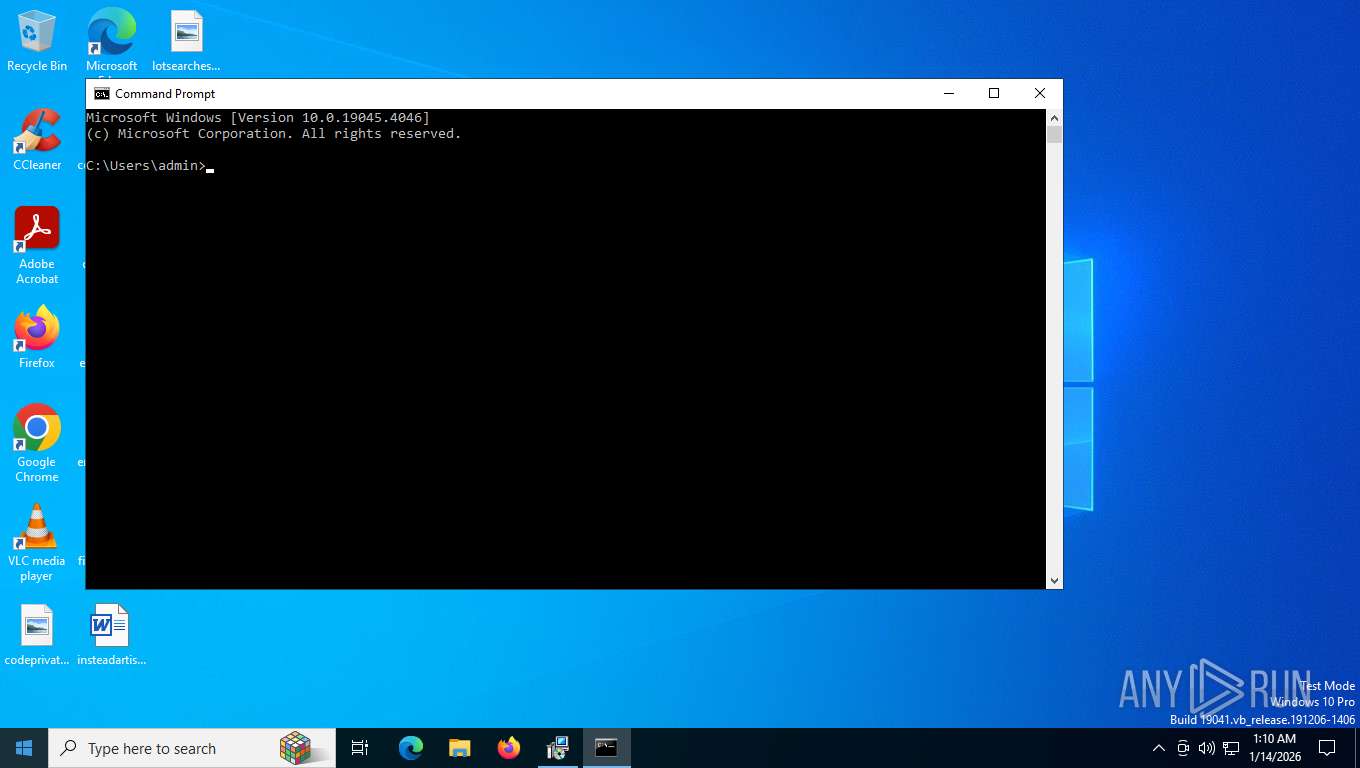
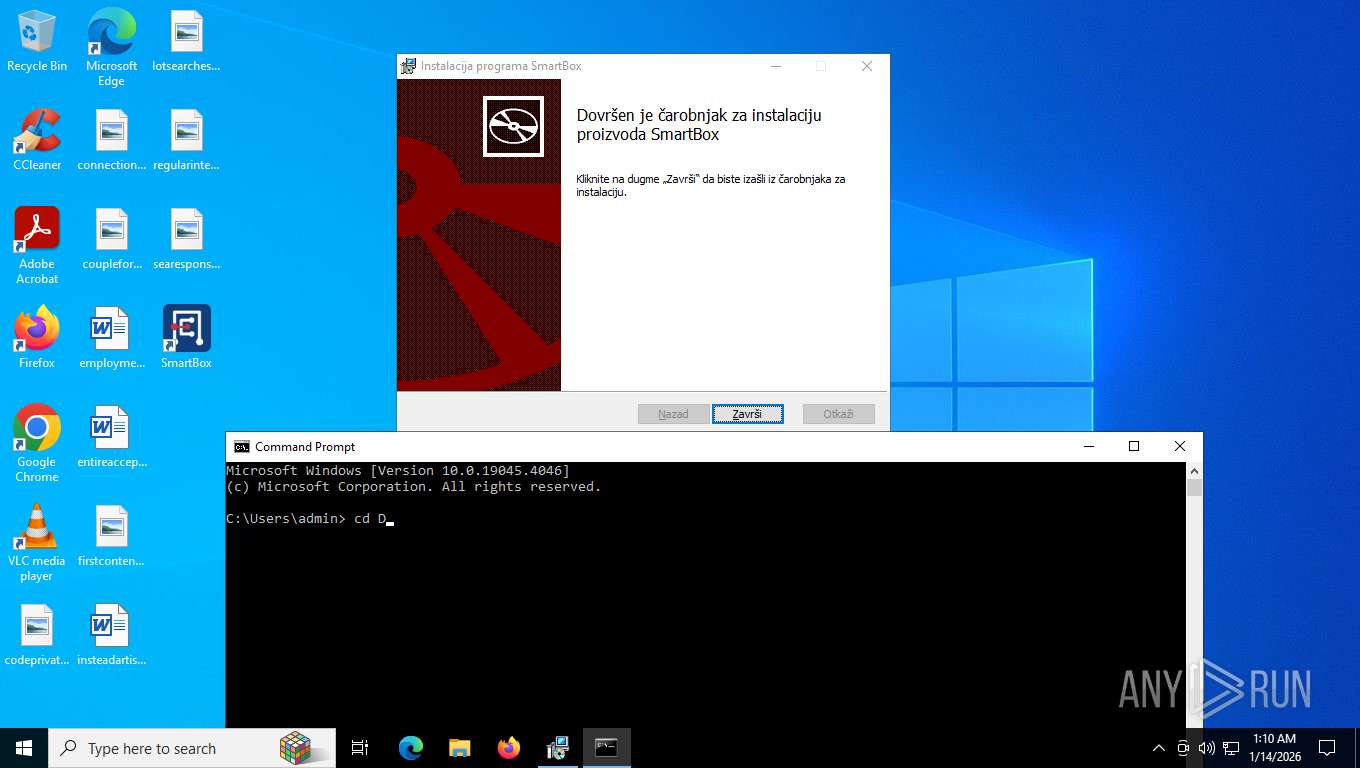
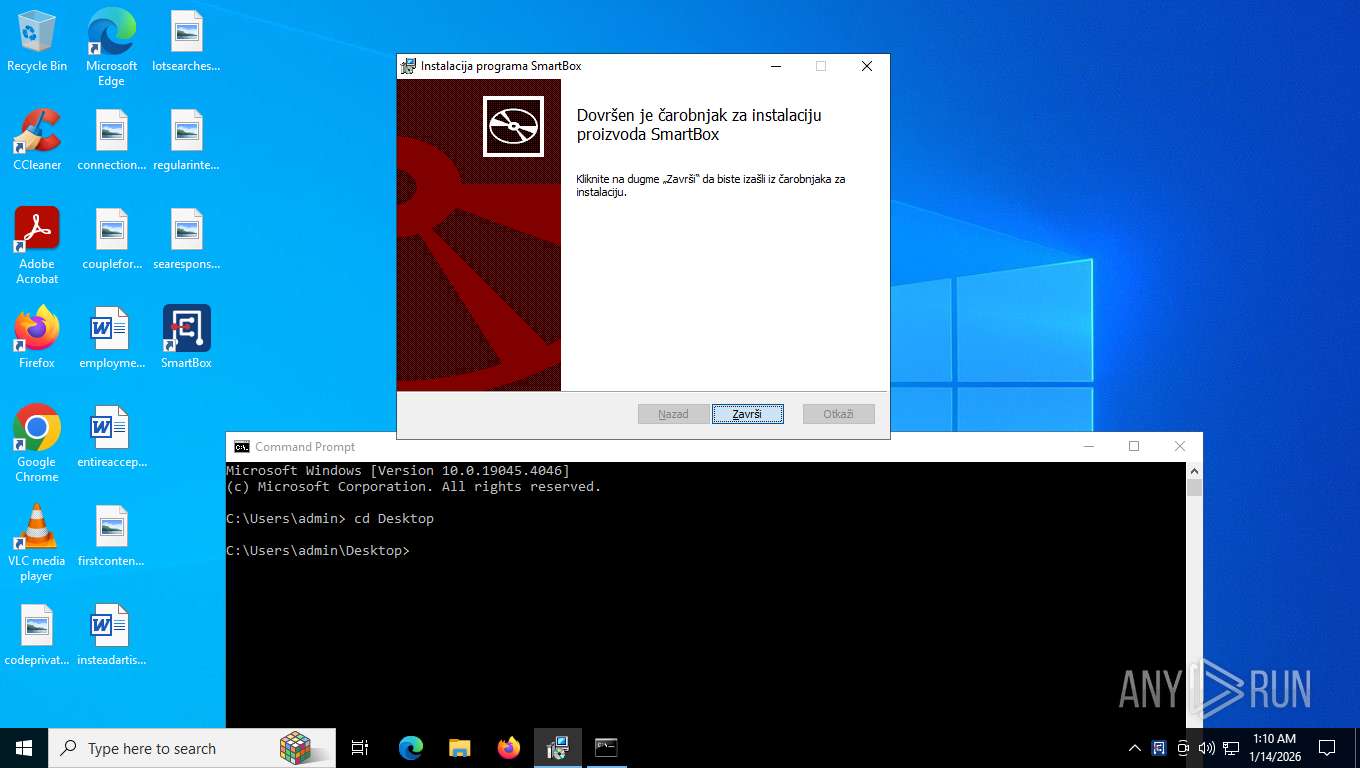
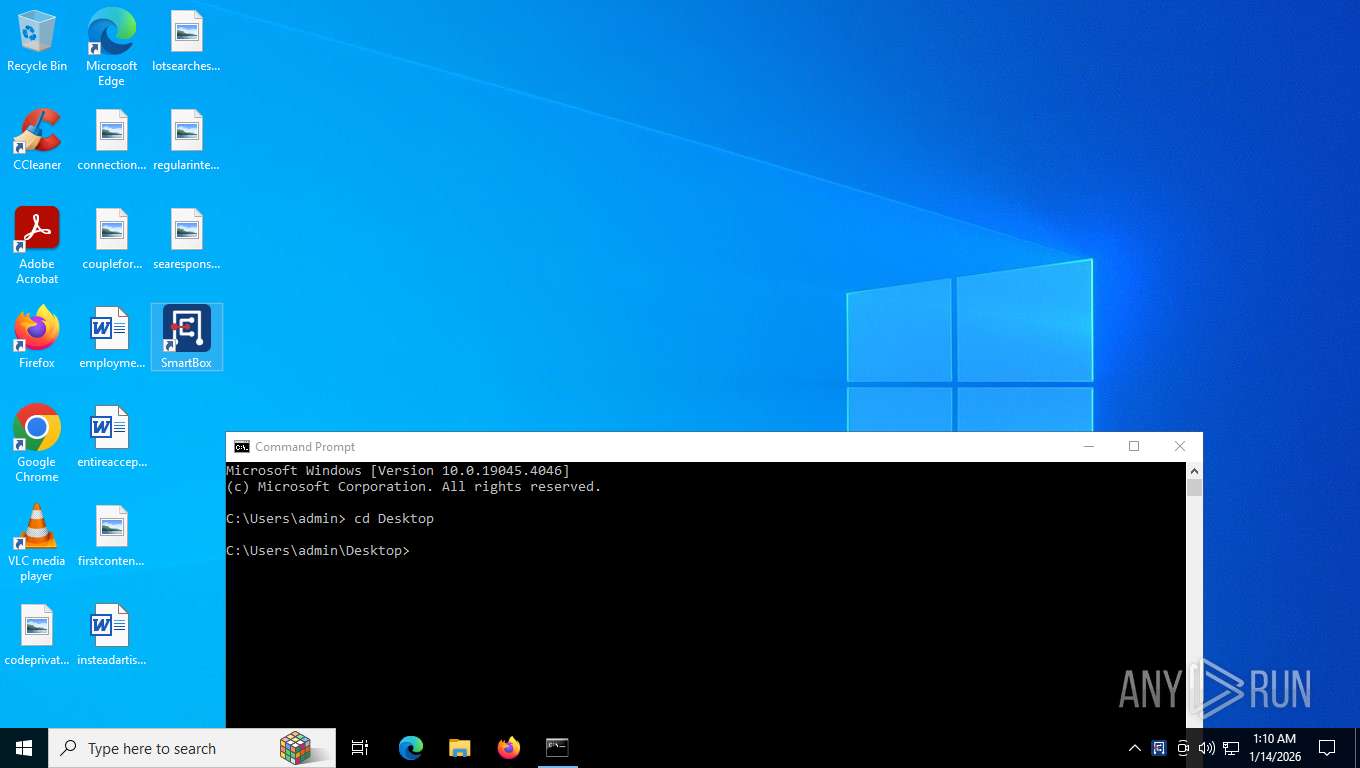
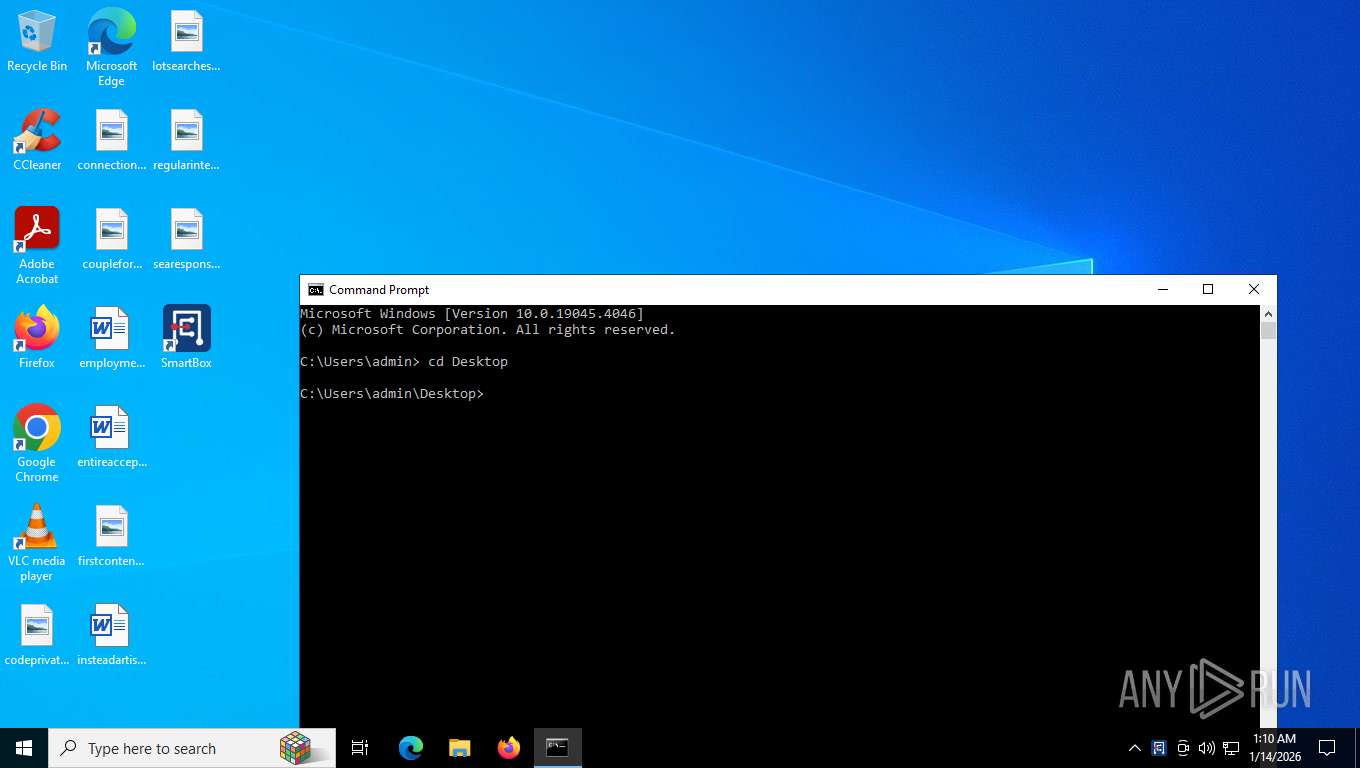
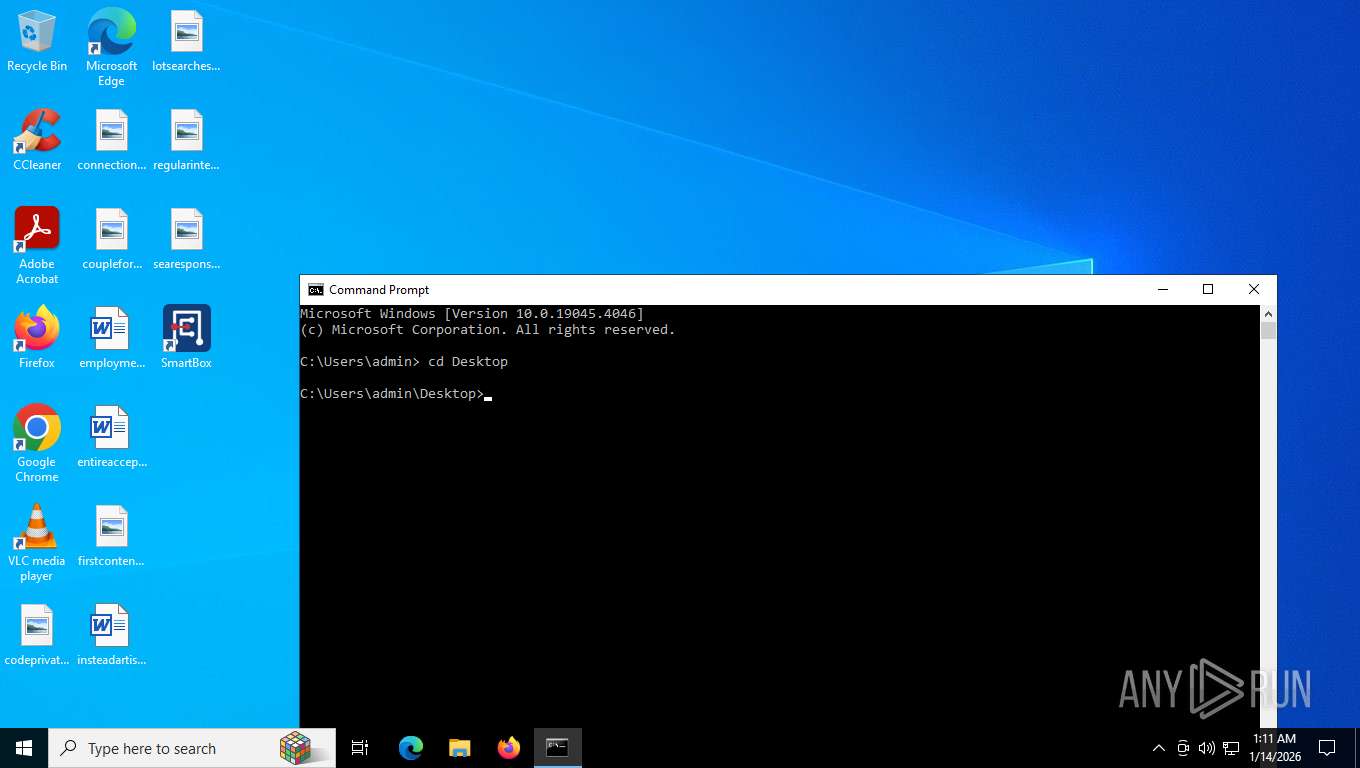
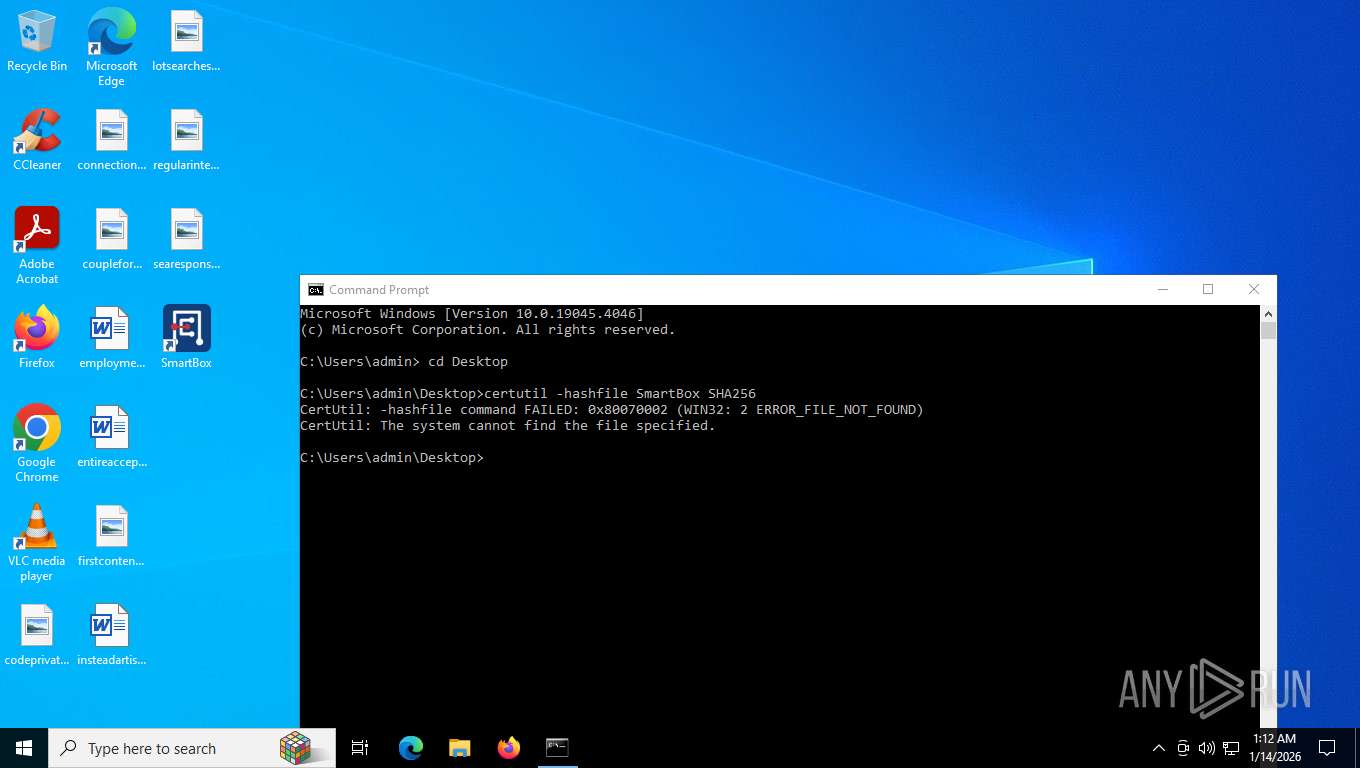
Starts CMD.EXE for commands execution
- SmartBox.exe (PID: 6272)
Checks for Java to be installed
- SmartBox.exe (PID: 6272)
INFO
Reads the computer name
- msiexec.exe (PID: 8172)
- msiexec.exe (PID: 7920)
- msiexec.exe (PID: 7828)
- msiexec.exe (PID: 7808)
- SmartBox.exe (PID: 6272)
- TextInputHost.exe (PID: 1872)
Checks supported languages
- msiexec.exe (PID: 8172)
- msiexec.exe (PID: 7920)
- msiexec.exe (PID: 7828)
- TextInputHost.exe (PID: 1872)
- msiexec.exe (PID: 7808)
- SmartBox.exe (PID: 1840)
- SmartBox.exe (PID: 3656)
- SmartBox.exe (PID: 6272)
- SmartBox.exe (PID: 1456)
- SmartBox.exe (PID: 7852)
- SmartBox.exe (PID: 7024)
- SmartBox.exe (PID: 6916)
- SmartBox.exe (PID: 7948)
- SmartBox.exe (PID: 1156)
- SmartBox.exe (PID: 4620)
- SmartBox.exe (PID: 6208)
- SmartBox.exe (PID: 7828)
- SmartBox.exe (PID: 7300)
- SmartBox.exe (PID: 8048)
- SmartBox.exe (PID: 5772)
- SmartBox.exe (PID: 32)
The sample compiled with english language support
- msiexec.exe (PID: 8172)
- msiexec.exe (PID: 7172)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8172)
- msiexec.exe (PID: 7172)
Create files in a temporary directory
- SmartBox.exe (PID: 6272)
- SmartBox.exe (PID: 1456)
- SmartBox.exe (PID: 7024)
- SmartBox.exe (PID: 7948)
- SmartBox.exe (PID: 4620)
- SmartBox.exe (PID: 6208)
- SmartBox.exe (PID: 8048)
- SmartBox.exe (PID: 5772)
Application launched itself
- chrome.exe (PID: 7556)
- firefox.exe (PID: 7180)
- firefox.exe (PID: 2480)
Reads CPU info
- SmartBox.exe (PID: 6272)
- SmartBox.exe (PID: 1456)
- SmartBox.exe (PID: 7024)
- SmartBox.exe (PID: 4620)
- SmartBox.exe (PID: 7948)
- SmartBox.exe (PID: 6208)
- SmartBox.exe (PID: 8048)
- SmartBox.exe (PID: 5772)
Reads the machine GUID from the registry
- SmartBox.exe (PID: 6272)
Manages system restore points
- SrTasks.exe (PID: 8092)
Creates files or folders in the user directory
- SmartBox.exe (PID: 6272)
Manual execution by a user
- SmartBox.exe (PID: 3656)
- mspaint.exe (PID: 7380)
- SmartBox.exe (PID: 7852)
- cmd.exe (PID: 7312)
- SmartBox.exe (PID: 32)
- SmartBox.exe (PID: 6916)
- SmartBox.exe (PID: 1156)
- SmartBox.exe (PID: 7300)
- SmartBox.exe (PID: 7828)
- firefox.exe (PID: 7180)
Process checks computer location settings
- SmartBox.exe (PID: 6272)
Checks operating system version
- SmartBox.exe (PID: 6272)
Checks proxy server information
- slui.exe (PID: 5612)
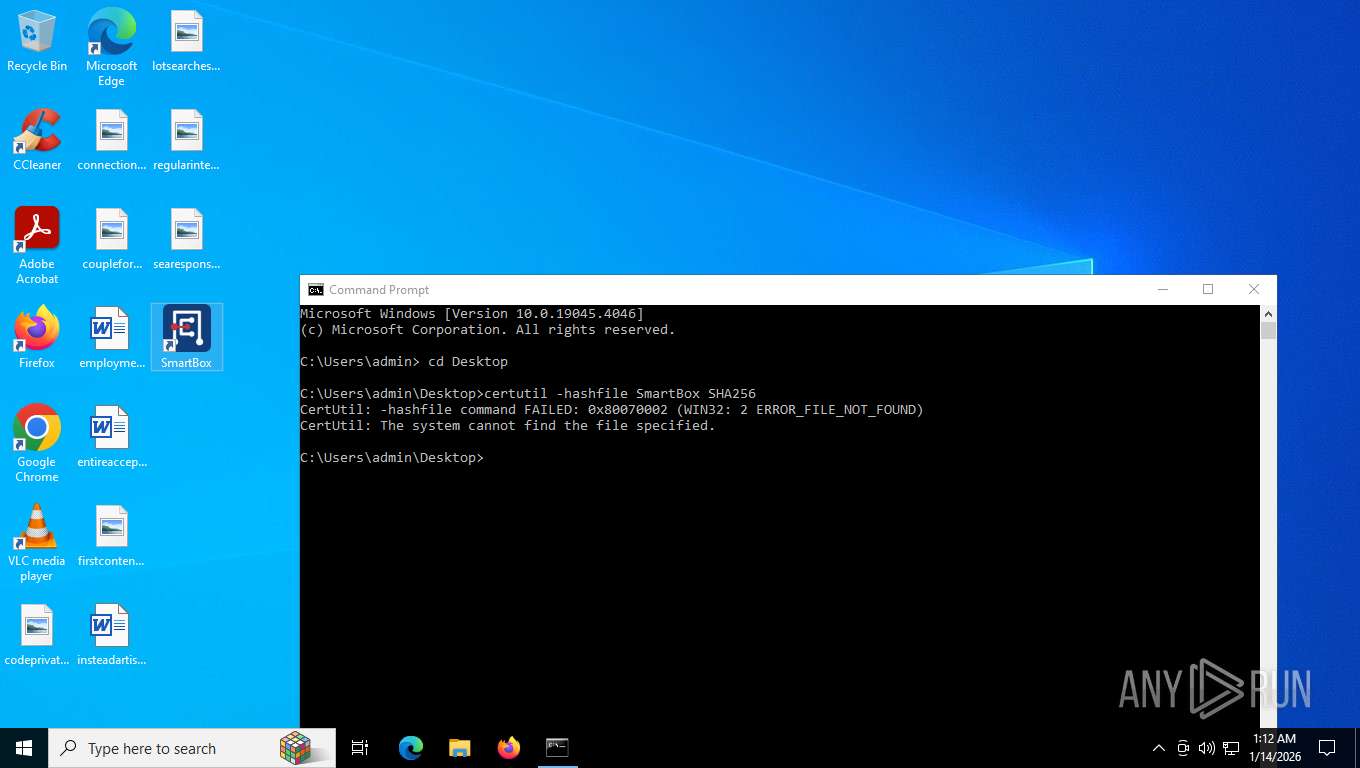
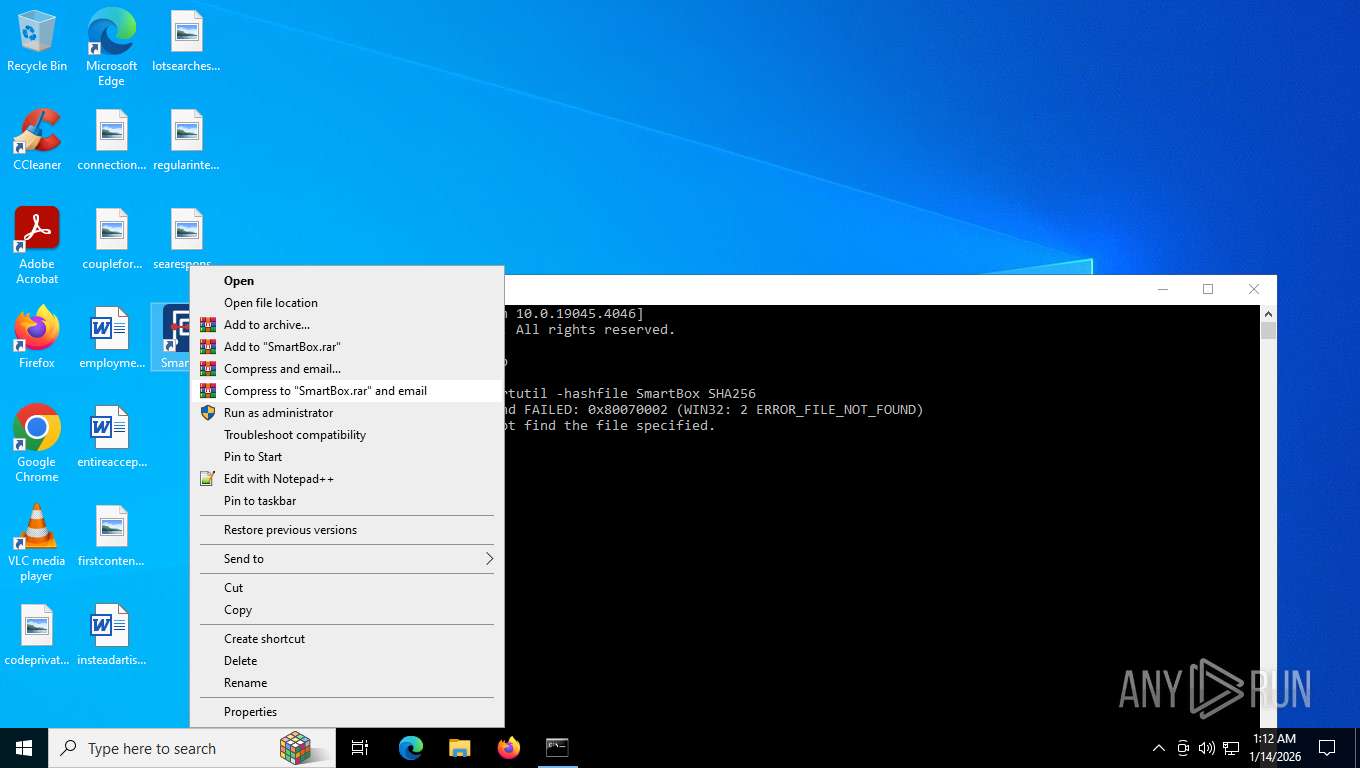
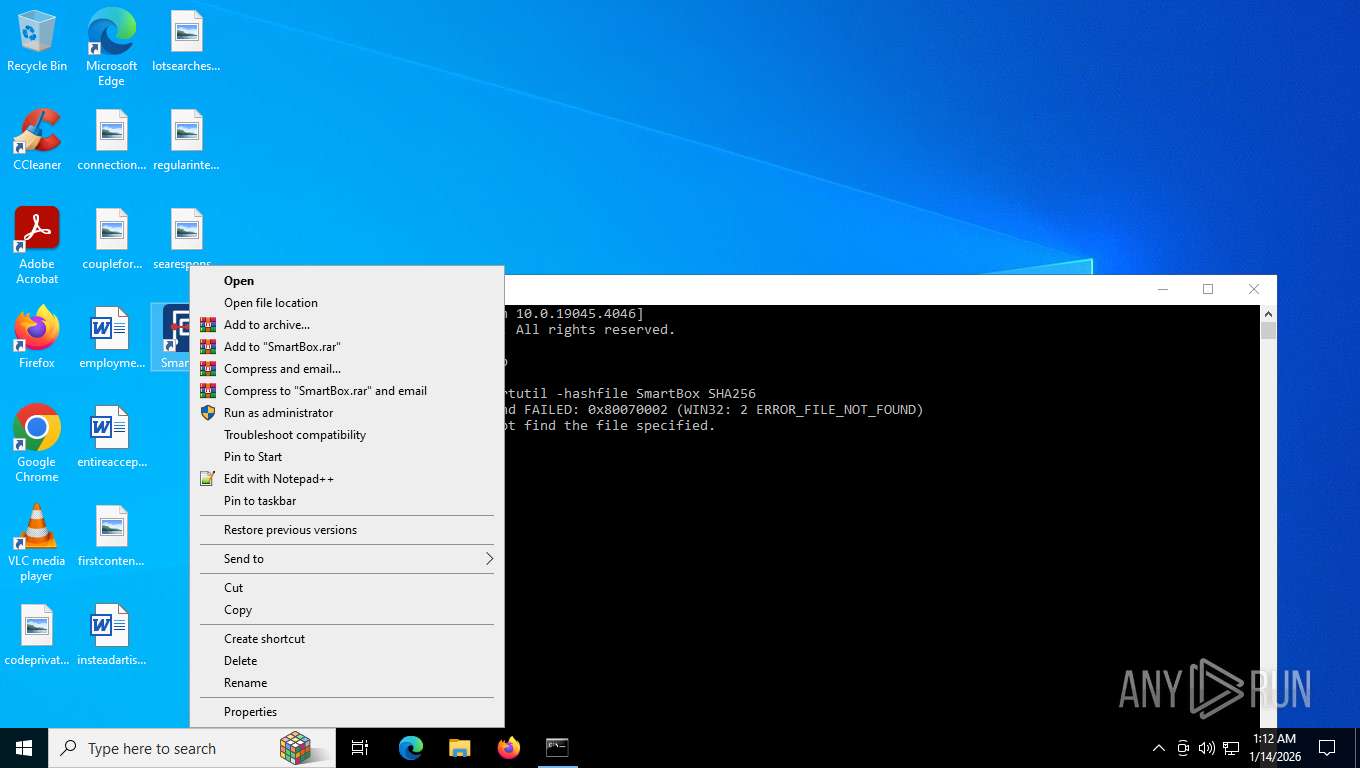
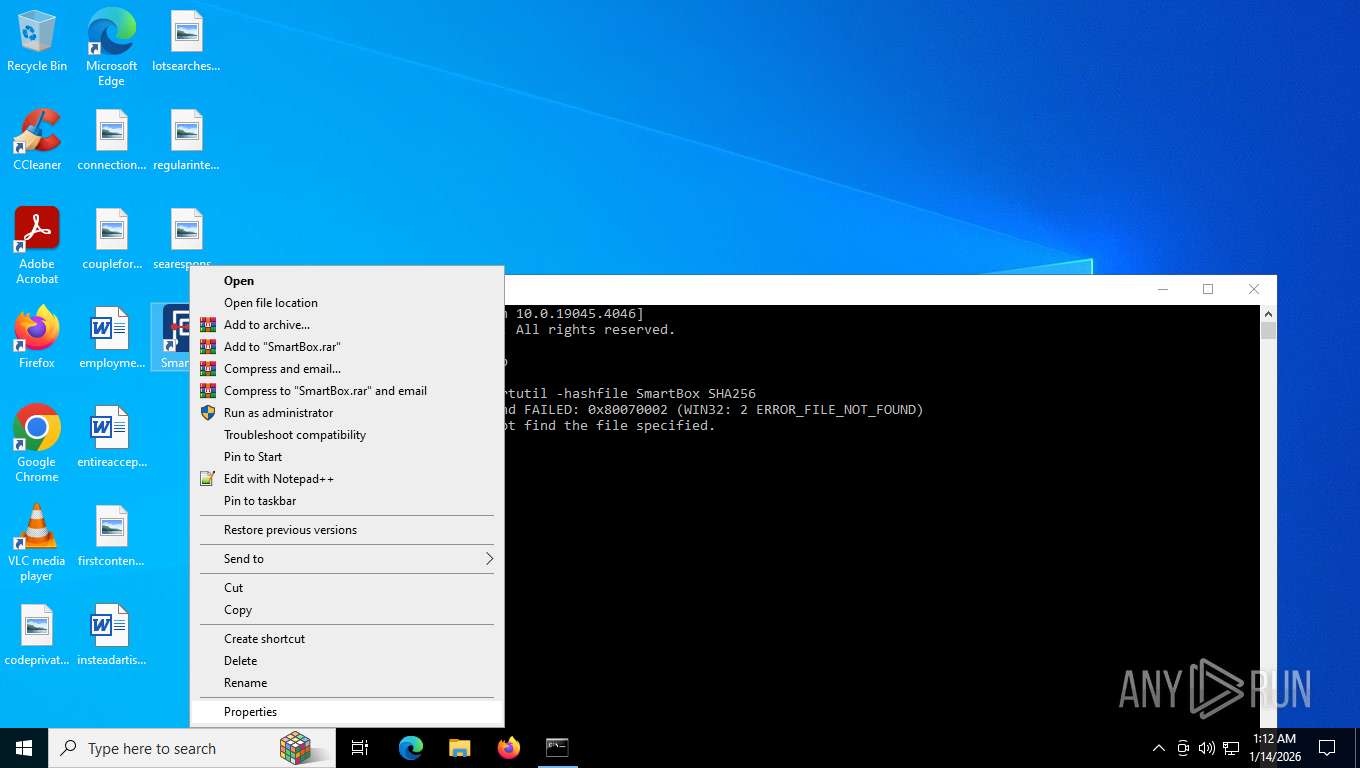
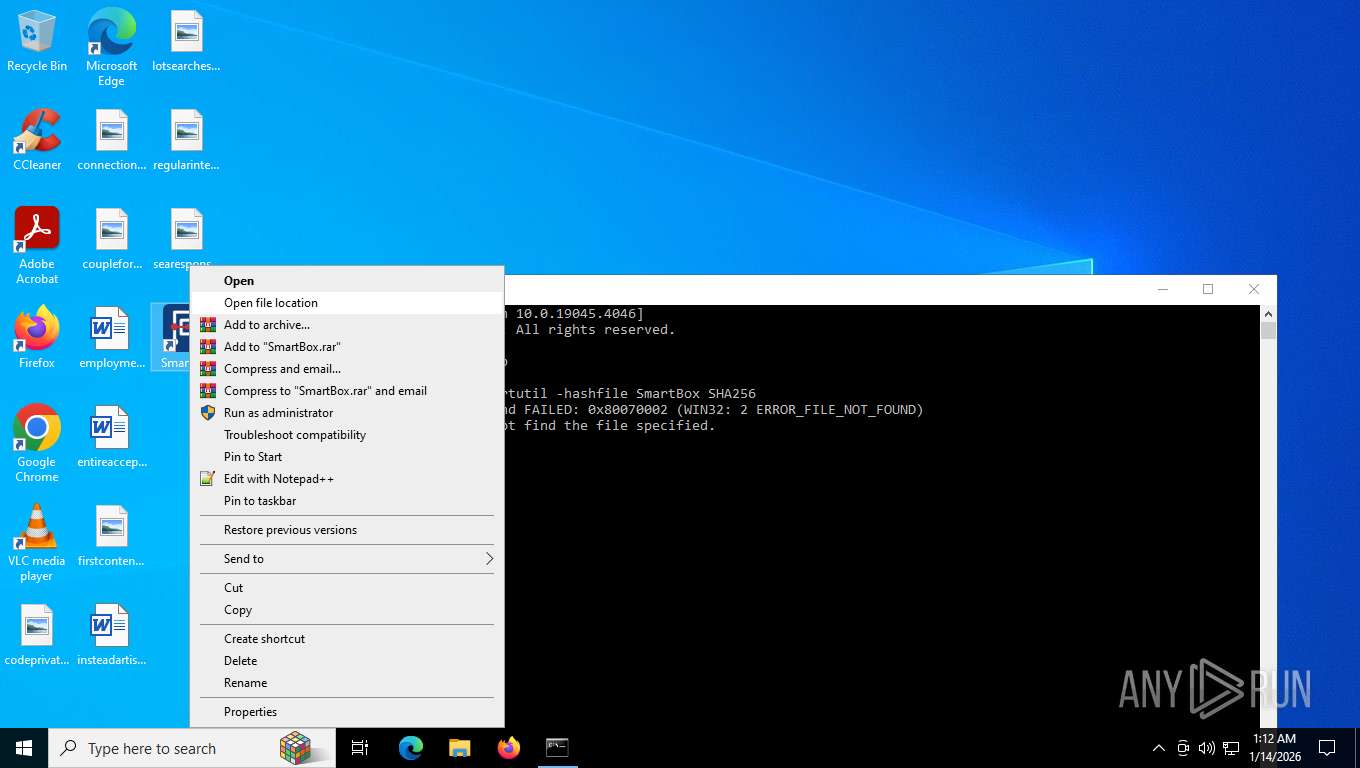
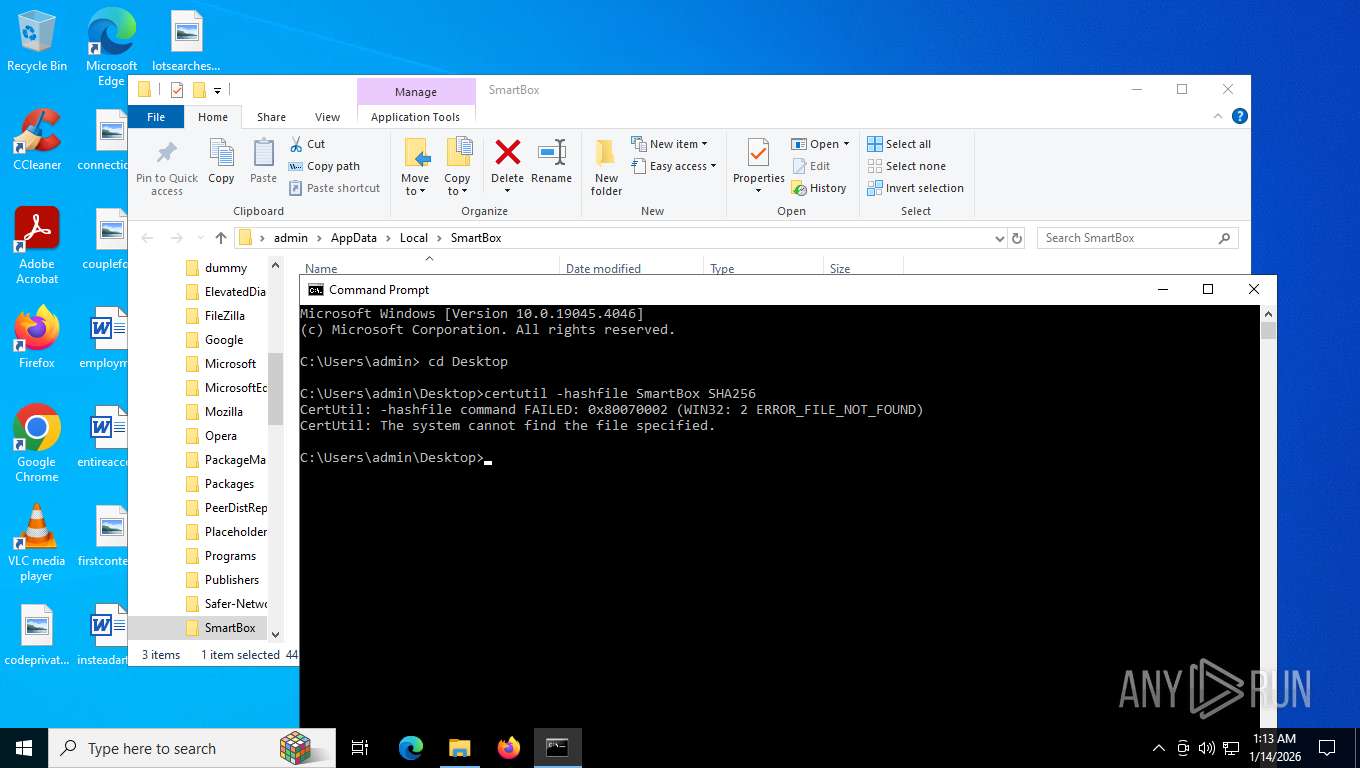
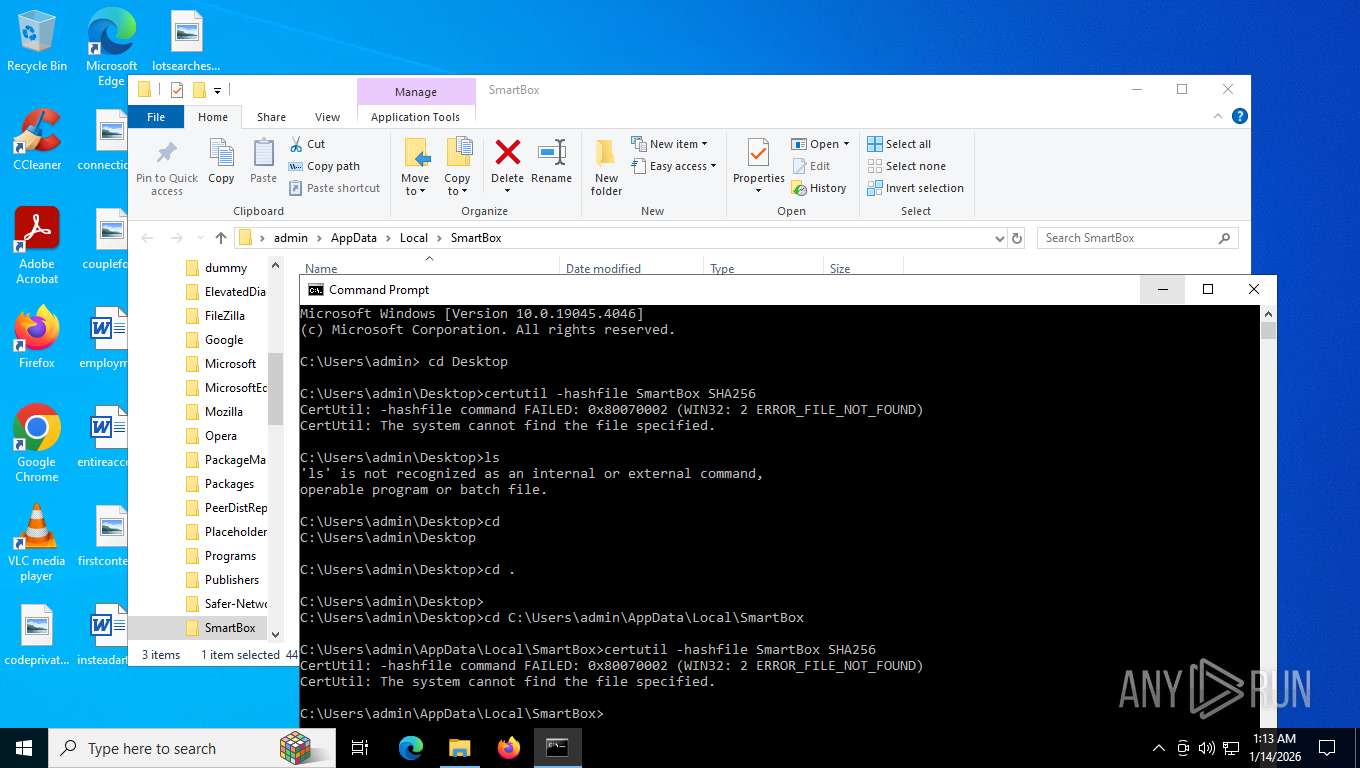
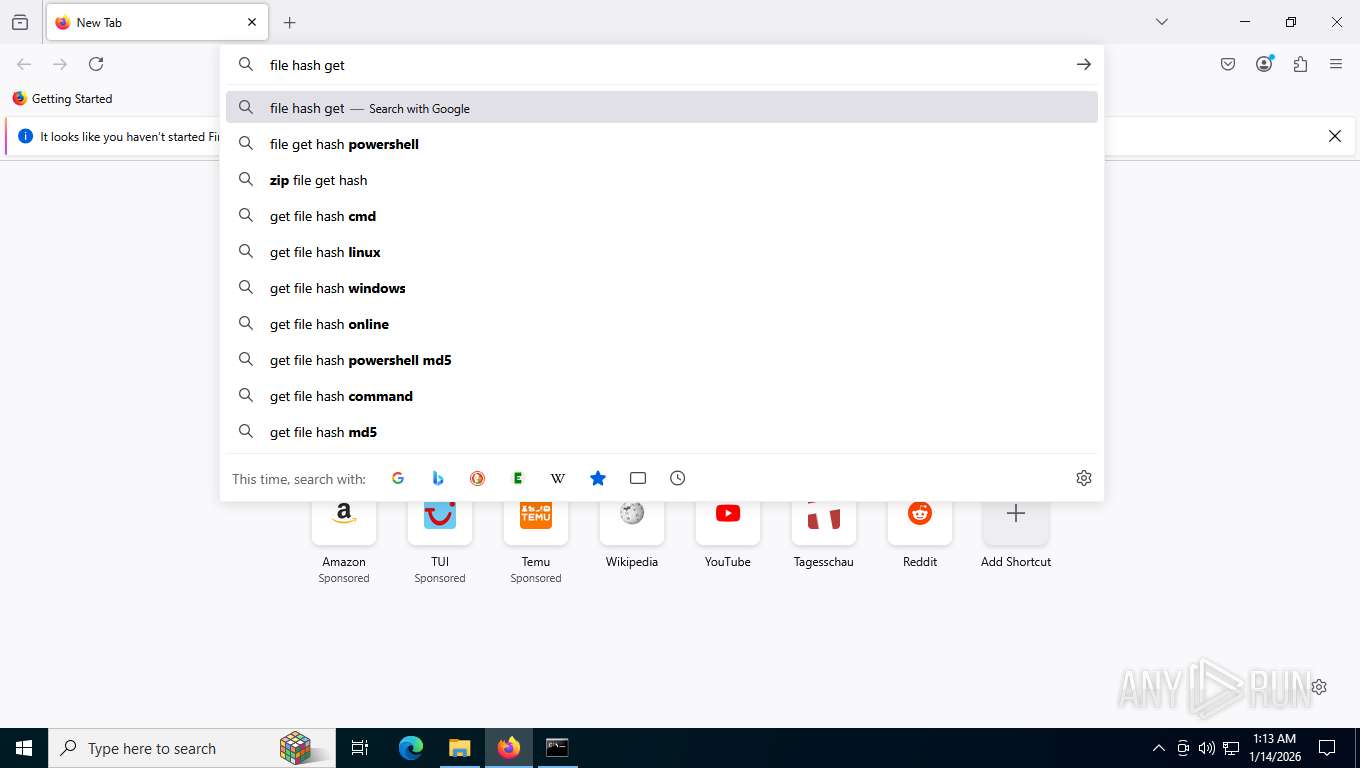
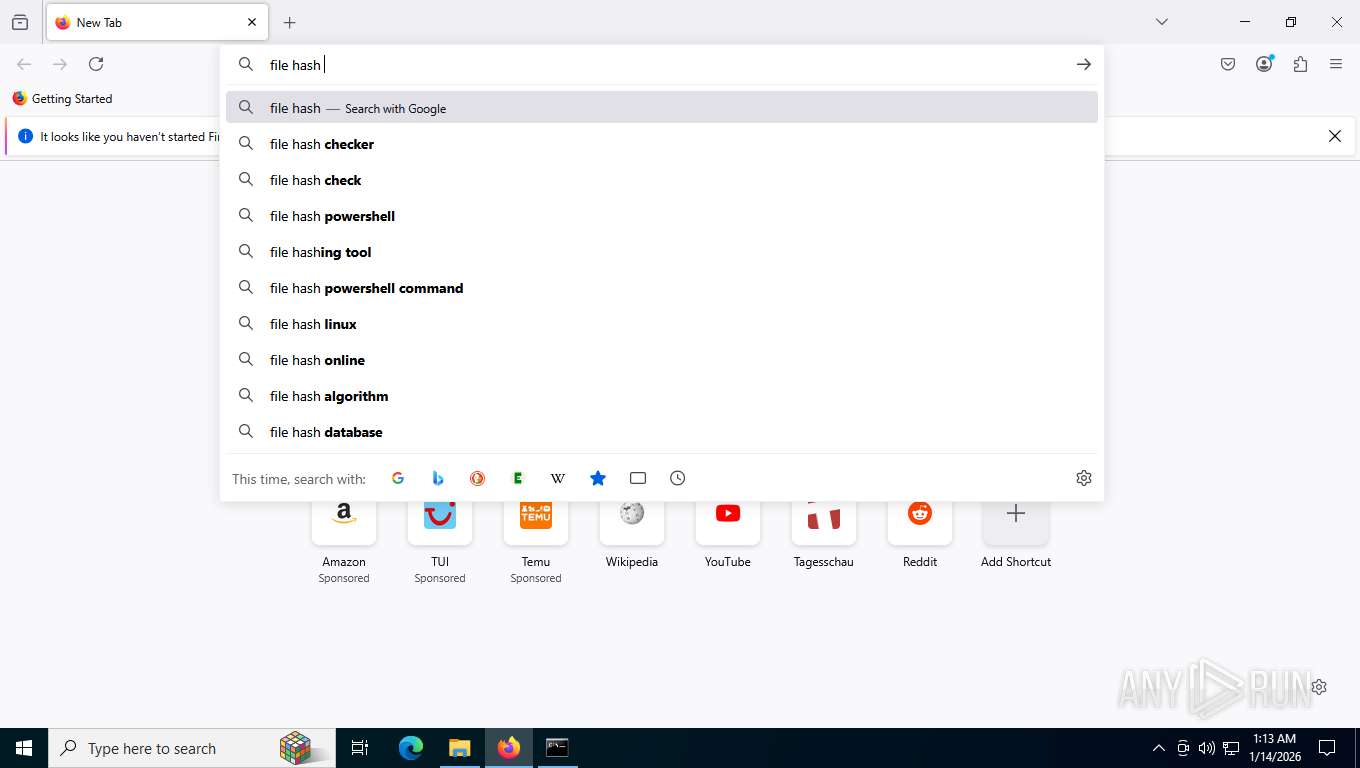
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 3056)
- certutil.exe (PID: 7408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
58
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe" | C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2260 -prefsLen 36580 -prefMapHandle 2264 -prefMapSize 273045 -ipcHandle 2272 -initialChannelId {7d636995-5c05-43ca-b51e-16feddf56a41} -parentPid 2480 -crashReporter "\\.\pipe\gecko-crash-server-pipe.2480" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 2 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe" | C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4412,i,8519956840053299697,13593838128784985381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1456 | C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe | C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe | — | SmartBox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe" | C:\Users\admin\AppData\Local\SmartBox\SmartBox.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1872 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=5044,i,8519956840053299697,13593838128784985381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
Total events
8 486
Read events
8 298
Write events
178
Delete events
10
Modification events
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000008D68EA671C85DC01EC1F000068140000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000001B06E8671C85DC01EC1F000068140000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000007D9F42681C85DC01EC1F000068140000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000007D9F42681C85DC01EC1F000068140000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A0E449681C85DC01EC1F000068140000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000002DC568681C85DC01EC1F000068140000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007D276B681C85DC01EC1F00008C1C0000E80300000100000000000000000000003EB0463A7D864049B85AF038C84FF7F300000000000000000000000000000000 | |||
| (PID) Process: | (7212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000907579681C85DC012C1C000038190000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000907579681C85DC012C1C0000341C0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
130
Suspicious files
408
Text files
383
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfde41.TMP | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfde41.TMP | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFfde41.TMP | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFfde60.TMP | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFfde51.TMP | — | |
MD5:— | SHA256:— | |||
| 7556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
558
TCP/UDP connections
142
DNS requests
161
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/img/eid.svg | unknown | image | 2.08 Kb | unknown |
7816 | chrome.exe | GET | 200 | 142.250.185.206:80 | http://clients2.google.com/time/1/current?cup2key=8:eKamuEJ3mJaM4GmF_FK71dYmBeB4FPRhgljLJCKbPH0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7816 | chrome.exe | POST | 200 | 173.194.76.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7816 | chrome.exe | GET | 200 | 172.217.23.106:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/user/login.html | unknown | html | 50.0 Kb | unknown |
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/css/plugins/item1.css | unknown | text | 10.2 Kb | unknown |
7816 | chrome.exe | GET | 200 | 172.67.142.245:443 | https://use.fontawesome.com/releases/v5.3.1/css/all.css | unknown | text | 47.5 Kb | unknown |
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/css/collector.css | unknown | text | 1.33 Kb | unknown |
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/resources/js/customScript.js | unknown | text | 18.9 Kb | unknown |
7816 | chrome.exe | GET | 200 | 195.178.50.151:443 | https://eporezi.purs.gov.rs/css/layoutNew.css | unknown | text | 188 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1984 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7816 | chrome.exe | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7816 | chrome.exe | 142.250.185.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
7816 | chrome.exe | 195.178.50.151:443 | eporezi.purs.gov.rs | TELEKOM-AS | RS | unknown |
7816 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7816 | chrome.exe | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
eporezi.purs.gov.rs |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |