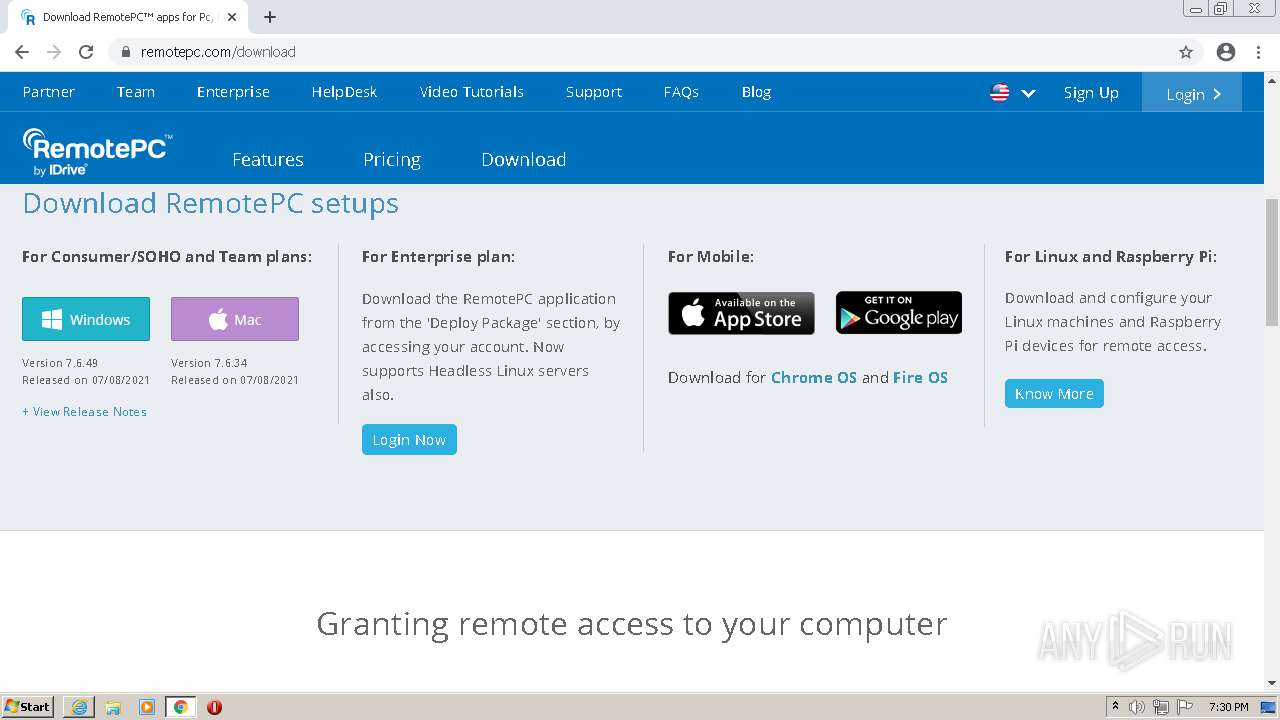
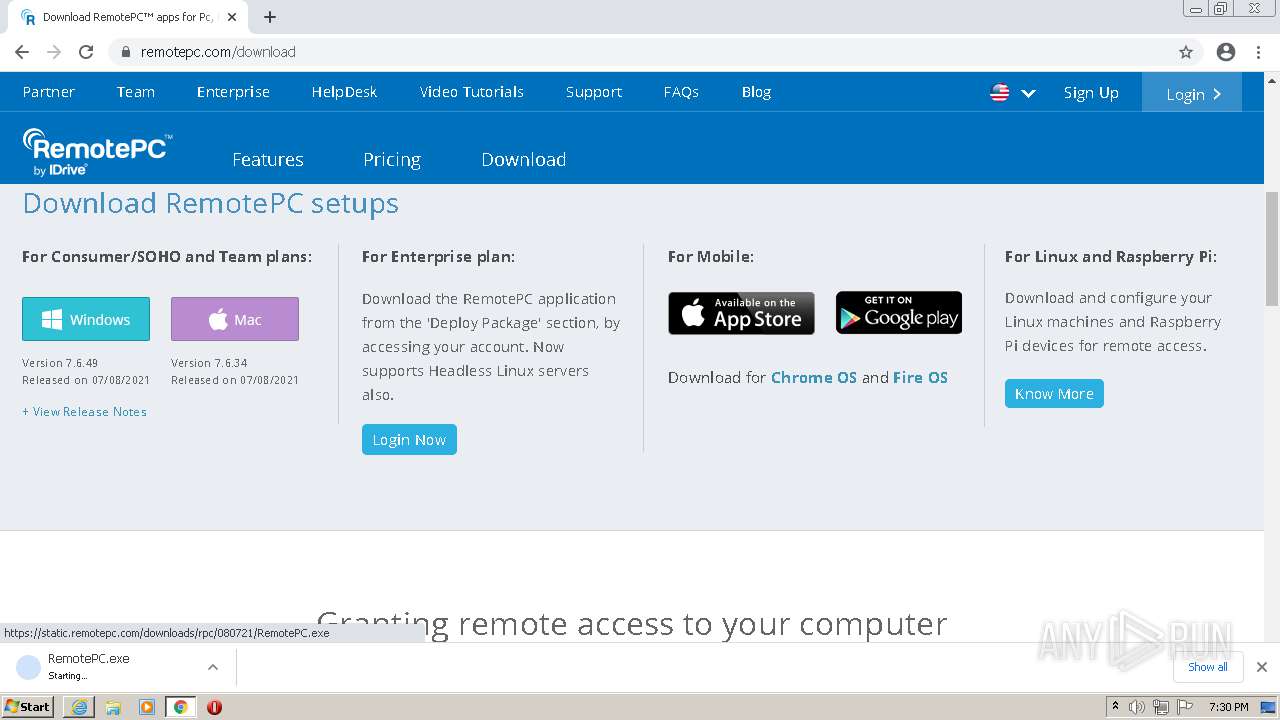
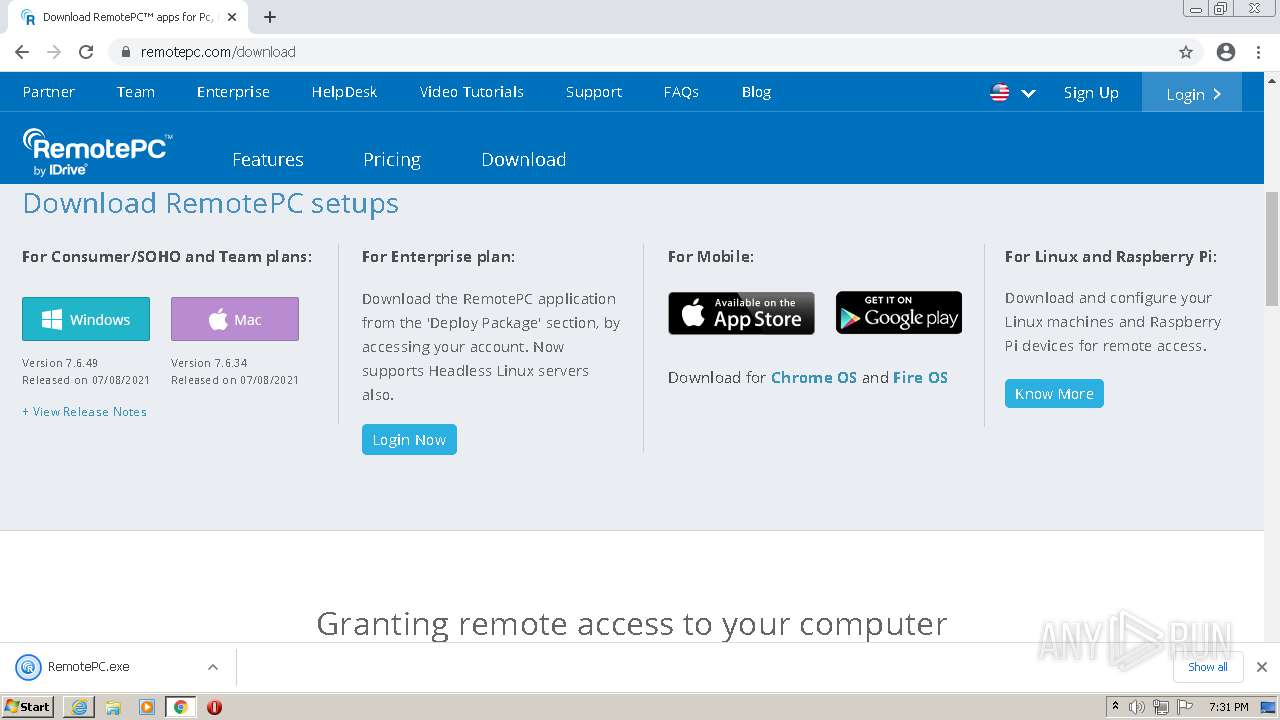
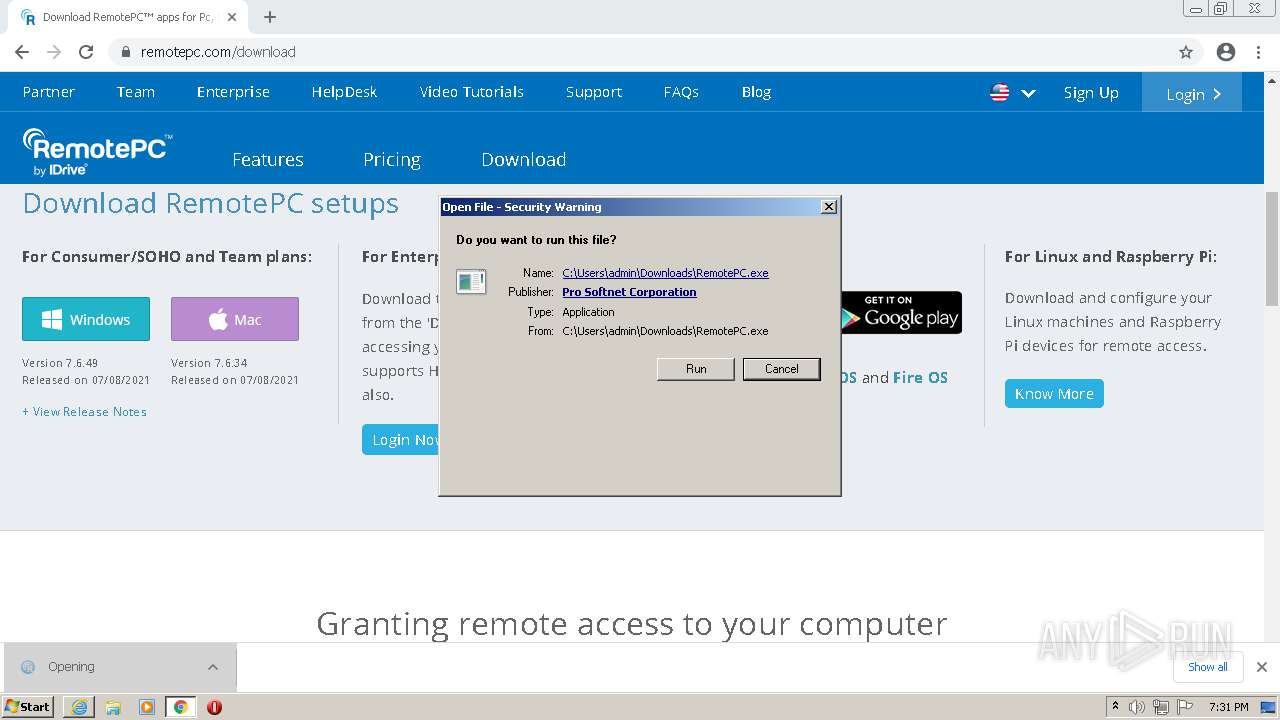
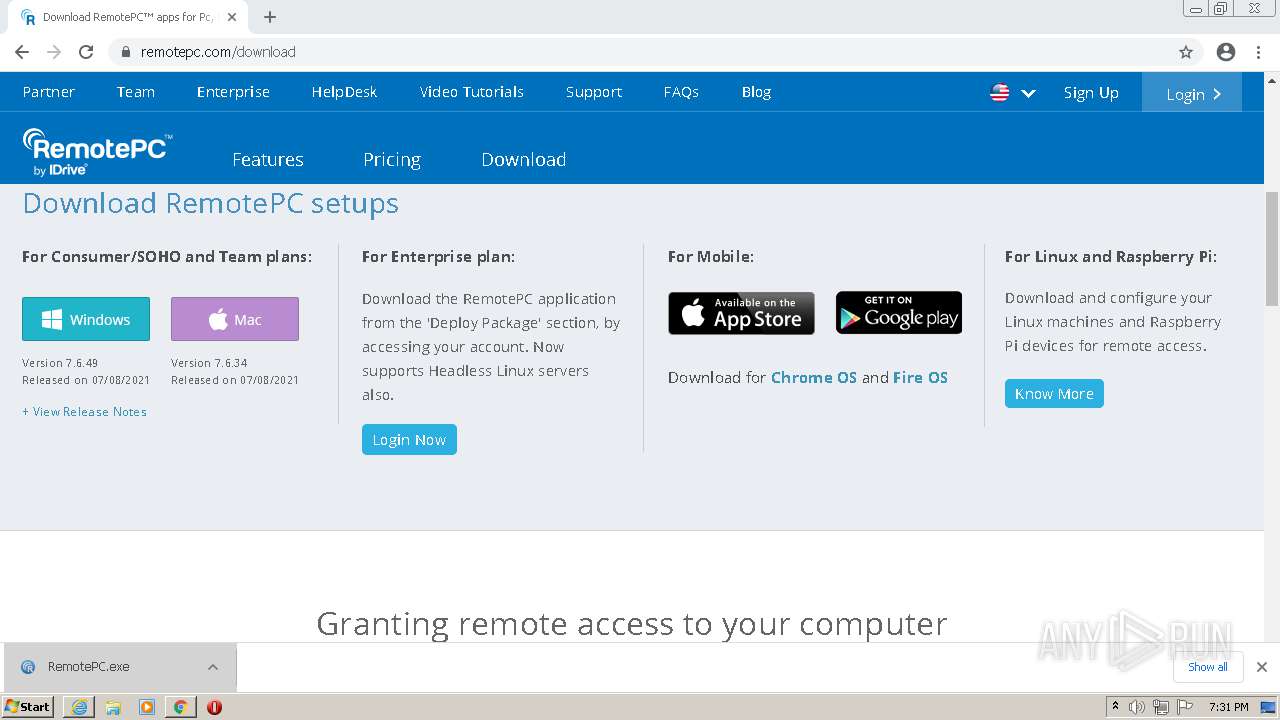
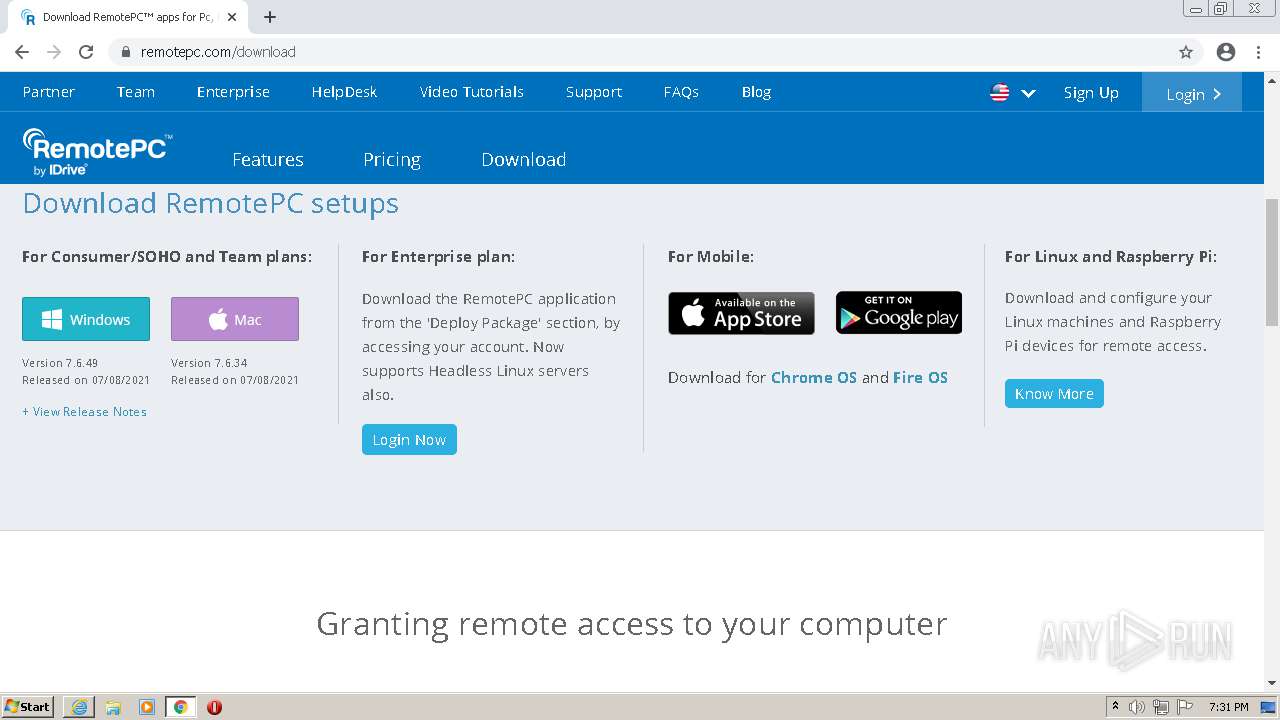
| URL: | https://www.remotepc.com/rpchd/helpdesk/sh/setup/download/v1/362764431 |
| Full analysis: | https://app.any.run/tasks/a036e93f-0f15-4fe2-a032-f2b49c4d6398 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2021, 18:28:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ABF04CF71123734A892155F1EF2E74D3 |
| SHA1: | DB0DC605303BEE644EEE37B349B125C808CE5F72 |
| SHA256: | EFA627CD3DA32F1EB3C18082DF4799526859EB5F2F0F54DDAB9B9687FB08BC14 |
| SSDEEP: | 3:N8DSLQ3i6IbFAWl0g8S9knOURTn:2OLQ3in6Wlg6URTn |
MALICIOUS
Application was dropped or rewritten from another process
- RemotePC.exe (PID: 3892)
- RemotePC.exe (PID: 1816)
- RPDUILaunch.exe (PID: 1676)
- PreUninstall.exe (PID: 1032)
- RPCFirewall.exe (PID: 1940)
- RemotePCLauncher.exe (PID: 1892)
- RemotePCLauncher.exe (PID: 672)
- RemotePCLauncher.exe (PID: 1924)
- RemotePCService.exe (PID: 1700)
- RemotePCLauncher.exe (PID: 3992)
- RemotePCLauncher.exe (PID: 2396)
- RPCPrinterDownloader.exe (PID: 4080)
- RemotePCUIU.exe (PID: 2064)
- RemotePCLauncher.exe (PID: 1244)
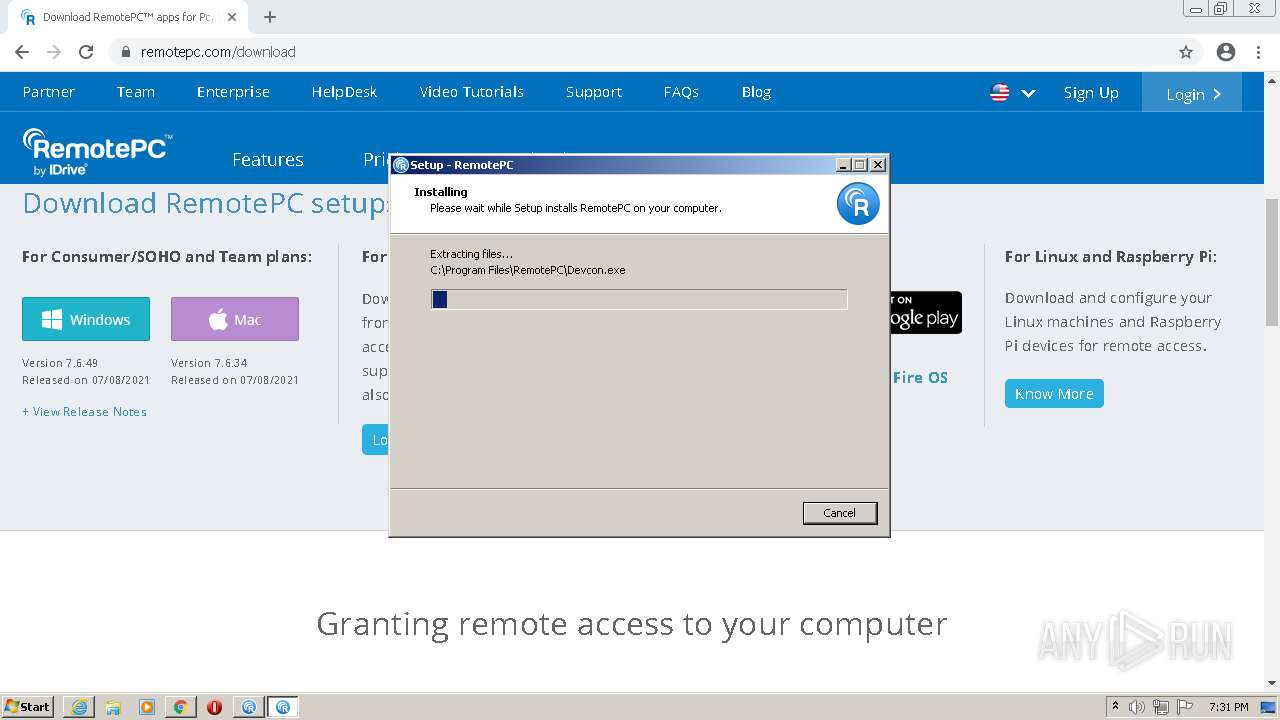
Drops executable file immediately after starts
- RemotePC.exe (PID: 3892)
- RemotePC.exe (PID: 1816)
- RemotePC.tmp (PID: 2728)
- RemotePC1.exe (PID: 2736)
- RemotePC1.tmp (PID: 2120)
- rundll32.exe (PID: 3676)
Loads the Task Scheduler COM API
- RPDUILaunch.exe (PID: 1676)
Loads dropped or rewritten executable
- RPDUILaunch.exe (PID: 1676)
- PreUninstall.exe (PID: 1032)
- RemotePCService.exe (PID: 1700)
- rundll32.exe (PID: 3676)
- wmiprvse.exe (PID: 1696)
- spoolsv.exe (PID: 3328)
- RemotePCUIU.exe (PID: 2064)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2192)
Reads the computer name
- wmiprvse.exe (PID: 1696)
- RemotePC.tmp (PID: 1244)
- RemotePC1.tmp (PID: 2120)
- RPDUILaunch.exe (PID: 1676)
- PreUninstall.exe (PID: 1032)
- RPCFirewall.exe (PID: 1940)
- RemotePCLauncher.exe (PID: 672)
- RemotePCLauncher.exe (PID: 1892)
- RemotePCService.exe (PID: 1700)
- RemotePCLauncher.exe (PID: 3992)
- RemotePCLauncher.exe (PID: 2396)
- RemotePCLauncher.exe (PID: 1924)
- RPCPrinterDownloader.exe (PID: 4080)
- RemotePCUIU.exe (PID: 2064)
- RemotePCLauncher.exe (PID: 1244)
Checks supported languages
- wmiprvse.exe (PID: 1696)
- RemotePC.exe (PID: 3892)
- RemotePC.tmp (PID: 1244)
- RemotePC.exe (PID: 1816)
- RemotePC.tmp (PID: 2728)
- RemotePC1.exe (PID: 2736)
- RemotePC1.tmp (PID: 2120)
- RPDUILaunch.exe (PID: 1676)
- PreUninstall.exe (PID: 1032)
- RPCFirewall.exe (PID: 1940)
- RemotePCLauncher.exe (PID: 672)
- RemotePCLauncher.exe (PID: 1892)
- RemotePCService.exe (PID: 1700)
- RemotePCLauncher.exe (PID: 1924)
- RemotePCLauncher.exe (PID: 3992)
- RPCPrinterDownloader.exe (PID: 4080)
- RemotePCLauncher.exe (PID: 2396)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2956)
- RemotePCUIU.exe (PID: 2064)
- RemotePCLauncher.exe (PID: 1244)
Reads Windows owner or organization settings
- wmiprvse.exe (PID: 1696)
- RemotePC.tmp (PID: 2728)
- RemotePC1.tmp (PID: 2120)
- msiexec.exe (PID: 2704)
Executable content was dropped or overwritten
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3740)
- RemotePC.exe (PID: 3892)
- RemotePC.exe (PID: 1816)
- RemotePC.tmp (PID: 2728)
- RemotePC1.exe (PID: 2736)
- RemotePC1.tmp (PID: 2120)
- PreUninstall.exe (PID: 1032)
- msiexec.exe (PID: 2704)
- rundll32.exe (PID: 3676)
- spoolsv.exe (PID: 3328)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2280)
Drops a file with too old compile date
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3740)
- RemotePC.exe (PID: 3892)
- RemotePC.exe (PID: 1816)
- RemotePC.tmp (PID: 2728)
- RemotePC1.exe (PID: 2736)
- RemotePC1.tmp (PID: 2120)
Reads the Windows organization settings
- RemotePC.tmp (PID: 2728)
- RemotePC1.tmp (PID: 2120)
- msiexec.exe (PID: 2704)
Drops a file that was compiled in debug mode
- RemotePC.tmp (PID: 2728)
- RemotePC1.tmp (PID: 2120)
- PreUninstall.exe (PID: 1032)
- msiexec.exe (PID: 2704)
- rundll32.exe (PID: 3676)
- spoolsv.exe (PID: 3328)
Drops a file with a compile date too recent
- RemotePC1.tmp (PID: 2120)
- msiexec.exe (PID: 2704)
- rundll32.exe (PID: 3676)
Creates a directory in Program Files
- RemotePC1.tmp (PID: 2120)
- msiexec.exe (PID: 2704)
Creates files in the user directory
- RemotePC1.tmp (PID: 2120)
- RemotePCLauncher.exe (PID: 672)
Creates files in the program directory
- RPDUILaunch.exe (PID: 1676)
- PreUninstall.exe (PID: 1032)
- RPCPrinterDownloader.exe (PID: 4080)
- msiexec.exe (PID: 2704)
- RemotePCUIU.exe (PID: 2064)
Creates/Modifies COM task schedule object
- regedit.exe (PID: 3756)
Executed as Windows Service
- msiexec.exe (PID: 2704)
- RemotePCService.exe (PID: 1700)
- spoolsv.exe (PID: 3328)
- spoolsv.exe (PID: 3132)
Starts SC.EXE for service management
- RemotePC1.tmp (PID: 2120)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2956)
Creates files in the Windows directory
- RemotePCService.exe (PID: 1700)
- wmiprvse.exe (PID: 1696)
- RPCPrinterDownloader.exe (PID: 4080)
- msiexec.exe (PID: 2704)
- rundll32.exe (PID: 3676)
- spoolsv.exe (PID: 3328)
Reads Environment values
- RPCPrinterDownloader.exe (PID: 4080)
- RemotePCUIU.exe (PID: 2064)
Changes default file association
- RemotePCLauncher.exe (PID: 672)
Starts CMD.EXE for commands execution
- RPCPrinterDownloader.exe (PID: 4080)
Executed via COM
- rundll32.exe (PID: 2088)
Starts Microsoft Installer
- RPCPrinterDownloader.exe (PID: 4080)
Application launched itself
- msiexec.exe (PID: 2704)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3332)
Creates a software uninstall entry
- msiexec.exe (PID: 2704)
Removes files from Windows directory
- spoolsv.exe (PID: 3328)
INFO
Reads the computer name
- iexplore.exe (PID: 2192)
- iexplore.exe (PID: 1108)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3476)
- msiexec.exe (PID: 2704)
- msiexec.exe (PID: 2732)
- msiexec.exe (PID: 3500)
- msiexec.exe (PID: 3104)
- sc.exe (PID: 3792)
- sc.exe (PID: 1928)
- sc.exe (PID: 2996)
- msiexec.exe (PID: 2488)
- chrome.exe (PID: 3724)
- msiexec.exe (PID: 3232)
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 2576)
- sc.exe (PID: 3264)
- sc.exe (PID: 3336)
- spoolsv.exe (PID: 3132)
- sc.exe (PID: 1180)
- sc.exe (PID: 3028)
- spoolsv.exe (PID: 3328)
- msiexec.exe (PID: 1248)
- MsiExec.exe (PID: 3332)
- rundll32.exe (PID: 3676)
- WISPTIS.EXE (PID: 1412)
Checks supported languages
- iexplore.exe (PID: 2192)
- iexplore.exe (PID: 1108)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 888)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 532)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3476)
- msiexec.exe (PID: 2732)
- msiexec.exe (PID: 2704)
- msiexec.exe (PID: 3104)
- msiexec.exe (PID: 3500)
- regedit.exe (PID: 3756)
- sc.exe (PID: 1928)
- sc.exe (PID: 3792)
- sc.exe (PID: 2996)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3724)
- msiexec.exe (PID: 2488)
- msiexec.exe (PID: 3232)
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 2576)
- msiexec.exe (PID: 3816)
- sc.exe (PID: 3264)
- rundll32.exe (PID: 2088)
- spoolsv.exe (PID: 3132)
- sc.exe (PID: 3028)
- sc.exe (PID: 1180)
- spoolsv.exe (PID: 3328)
- msiexec.exe (PID: 1248)
- sc.exe (PID: 3336)
- MsiExec.exe (PID: 3332)
- rundll32.exe (PID: 3676)
- WISPTIS.EXE (PID: 1412)
- chrome.exe (PID: 2772)
Changes internet zones settings
- iexplore.exe (PID: 1108)
Application launched itself
- iexplore.exe (PID: 1108)
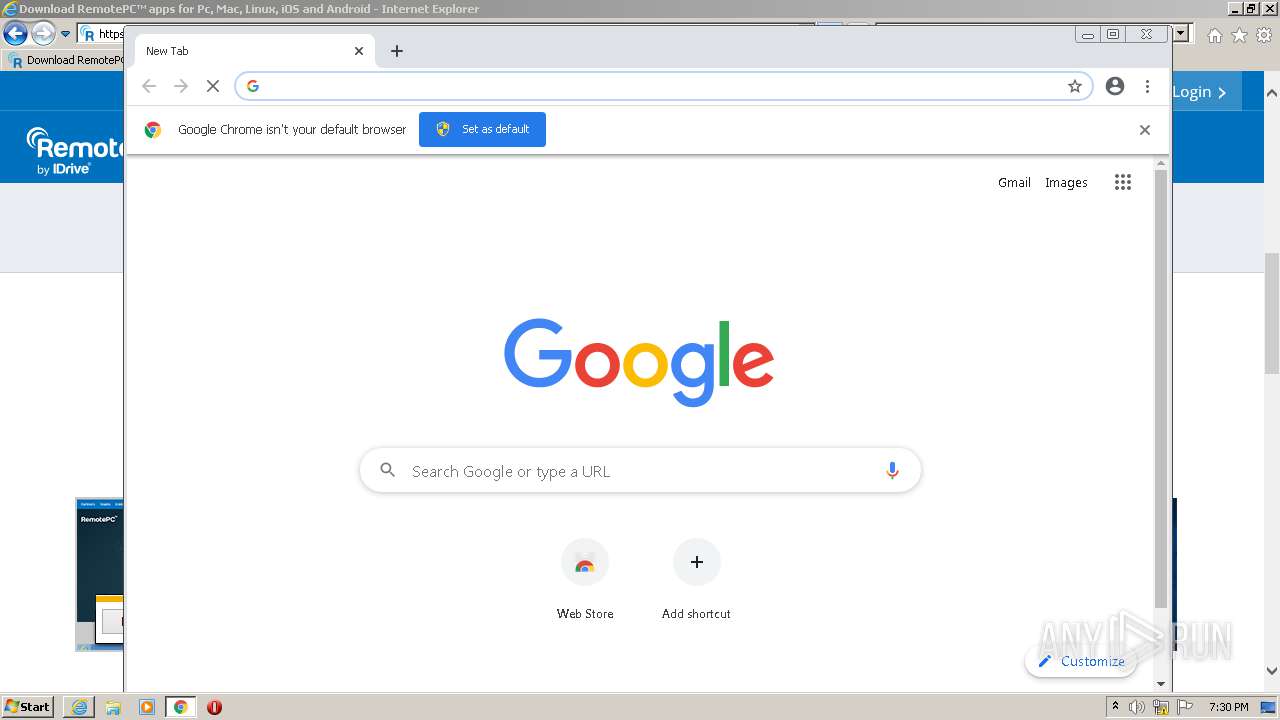
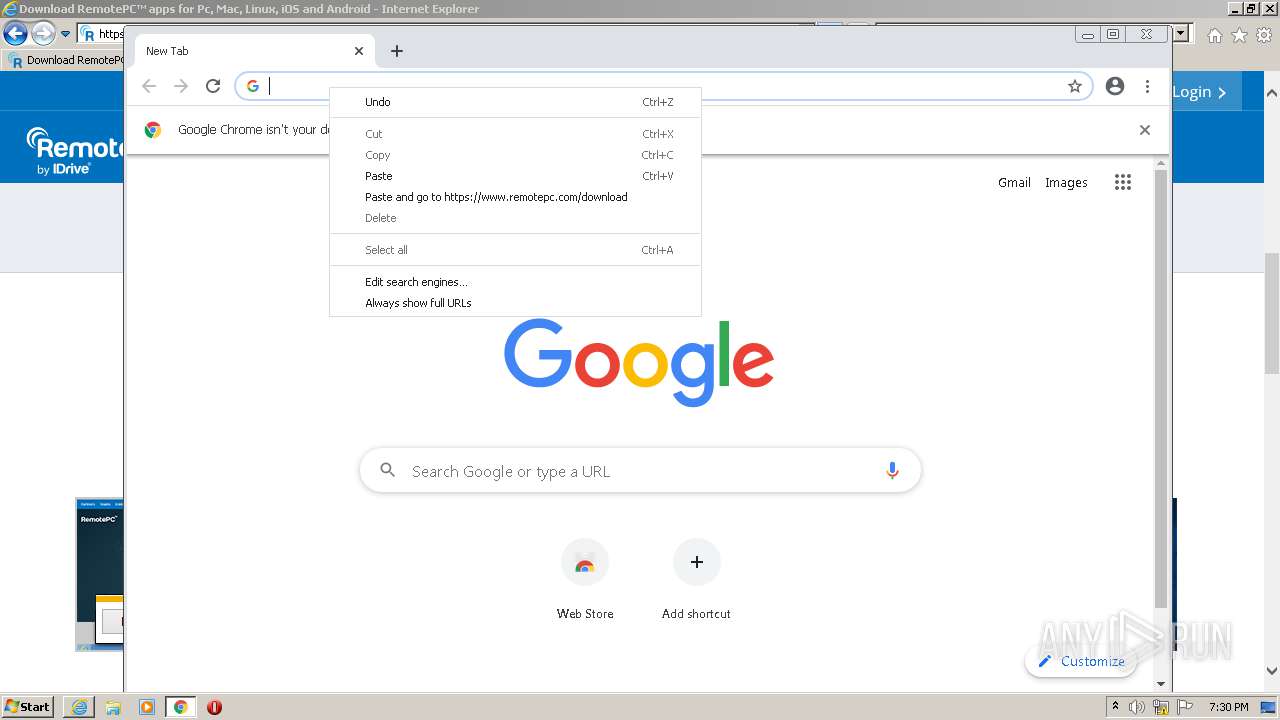
- chrome.exe (PID: 2280)
Reads settings of System Certificates
- iexplore.exe (PID: 2192)
- iexplore.exe (PID: 1108)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 2280)
- RPDUILaunch.exe (PID: 1676)
- RPCPrinterDownloader.exe (PID: 4080)
- RemotePCUIU.exe (PID: 2064)
Reads internet explorer settings
- iexplore.exe (PID: 2192)
Checks Windows Trust Settings
- iexplore.exe (PID: 2192)
- iexplore.exe (PID: 1108)
- chrome.exe (PID: 2280)
Creates files in the user directory
- iexplore.exe (PID: 2192)
- iexplore.exe (PID: 1108)
Changes settings of System certificates
- iexplore.exe (PID: 1108)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1108)
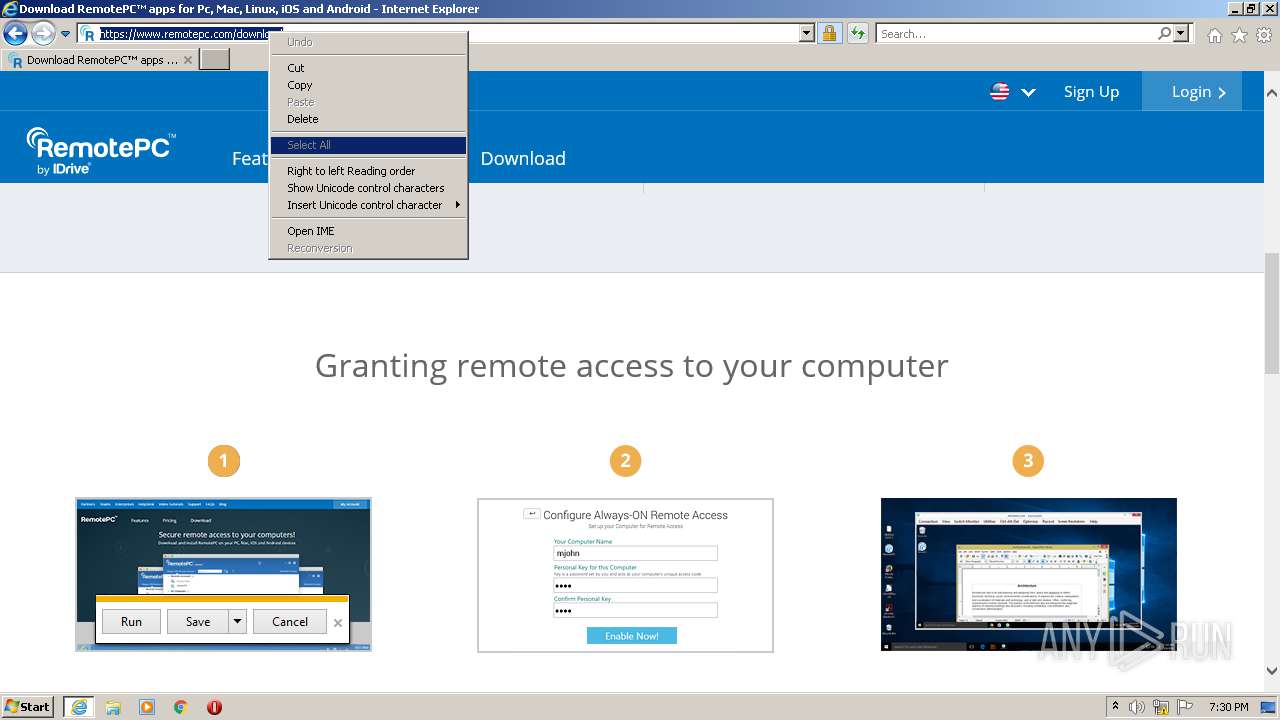
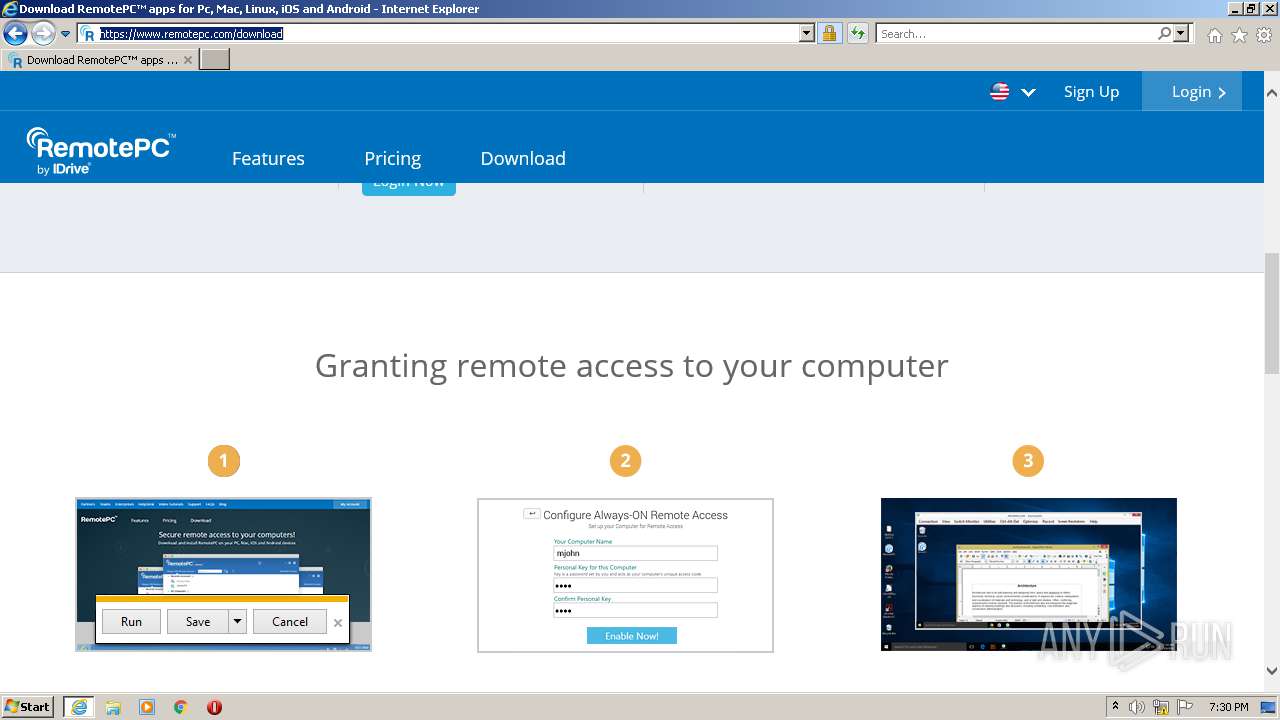
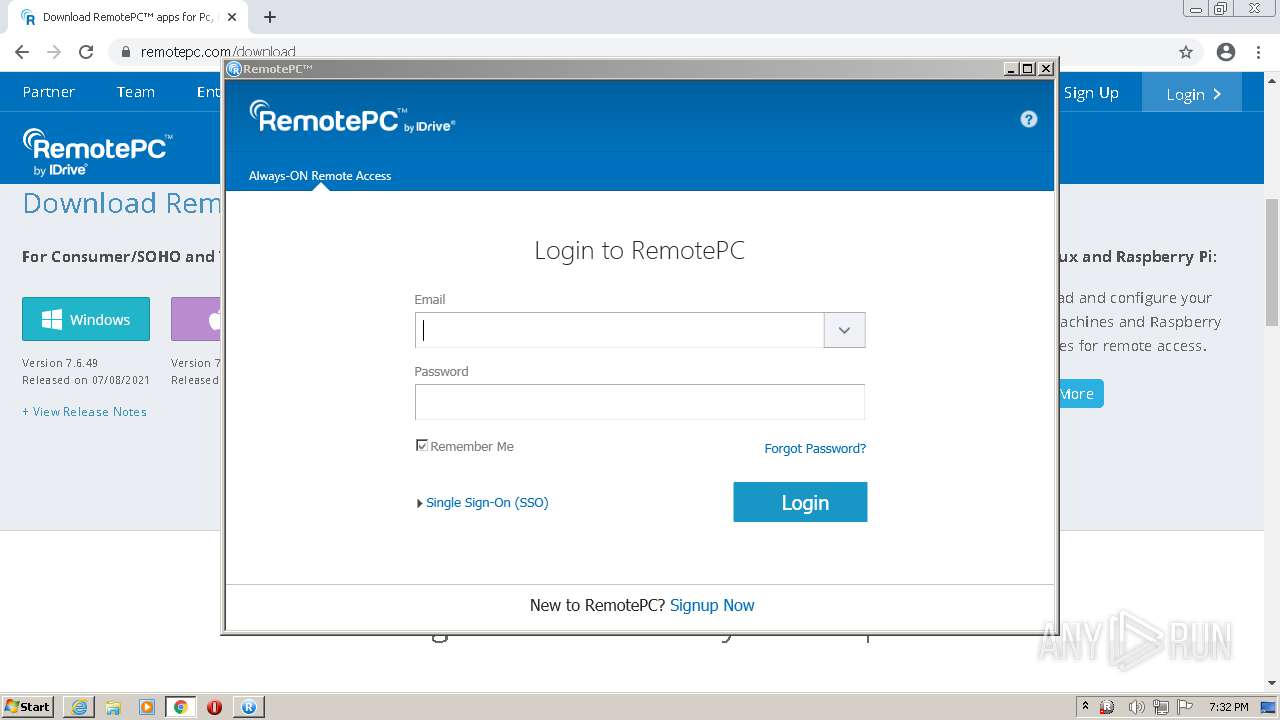
Manual execution by user
- chrome.exe (PID: 2280)
Reads the hosts file
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3740)
Application was dropped or rewritten from another process
- RemotePC.tmp (PID: 2728)
- RemotePC.tmp (PID: 1244)
- RemotePC1.tmp (PID: 2120)
- RemotePC1.exe (PID: 2736)
Loads dropped or rewritten executable
- RemotePC.tmp (PID: 2728)
- RemotePC1.tmp (PID: 2120)
Reads the date of Windows installation
- chrome.exe (PID: 3476)
Creates files in the program directory
- RemotePC1.tmp (PID: 2120)
Dropped object may contain Bitcoin addresses
- RemotePC1.tmp (PID: 2120)
Creates a software uninstall entry
- RemotePC1.tmp (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
78
Malicious processes
14
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,6905697528828953862,7569804877410584651,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\RemotePC\RemotePCLauncher.exe" 1 | C:\Program Files\RemotePC\RemotePCLauncher.exe | — | RemotePC1.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: RemotePC Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,6905697528828953862,7569804877410584651,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,6905697528828953862,7569804877410584651,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3356 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\RemotePC\PreUninstall.exe" 1 | C:\Program Files\RemotePC\PreUninstall.exe | RemotePC1.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: PreUninstall Exit code: 0 Version: 7.5.1.0 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.remotepc.com/rpchd/helpdesk/sh/setup/download/v1/362764431" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1180 | sc stop Spooler" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\AppData\Local\Temp\is-4IJ2N.tmp\RemotePC.tmp" /SL5="$40214,26483932,228352,C:\Users\admin\Downloads\RemotePC.exe" | C:\Users\admin\AppData\Local\Temp\is-4IJ2N.tmp\RemotePC.tmp | — | RemotePC.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\RemotePC\RemotePCLauncher.exe" 4 | C:\Program Files\RemotePC\RemotePCLauncher.exe | — | RemotePCUIU.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RemotePC Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1248 | "C:\Windows\System32\msiexec.exe" /qn /i "C:\ProgramData\RemotePC\PrinterSetup\Printer.msi" | C:\Windows\System32\msiexec.exe | — | RPCPrinterDownloader.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
62 428
Read events
61 213
Write events
1 180
Delete events
35
Modification events
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30898599 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30898599 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
280
Suspicious files
80
Text files
332
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\remotepc-responsive[1].css | text | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_EAFF2B43AD3DF231A512225A0F3E02E6 | binary | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\css[1].css | text | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\remotepc-structure[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
127
DNS requests
82
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFS9lWfFTtEyCgAAAADoPas%3D | US | der | 471 b | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCUbcaWZY6KcQoAAAAA6EIk | US | der | 472 b | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDaqCx0Uw5IKBQAAAACH9mE%3D | US | der | 471 b | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECxnvN4MUipXCgAAAADoMbo%3D | US | der | 471 b | whitelisted |
1108 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2Bk7JzdJrHjAoAAAAA6DGx | US | der | 472 b | whitelisted |
1108 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEPADVwzSh7mAwAAAADMUdQ%3D | US | der | 471 b | whitelisted |
2192 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | iexplore.exe | 172.67.37.123:443 | www.remotepc.com | — | US | unknown |
2192 | iexplore.exe | 67.27.159.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2192 | iexplore.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2192 | iexplore.exe | 93.184.220.29:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2192 | iexplore.exe | 142.250.185.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1108 | iexplore.exe | 93.184.220.29:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | iexplore.exe | 104.22.40.86:80 | www.remotepc.com | Cloudflare Inc | US | unknown |
1108 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2192 | iexplore.exe | 104.22.41.86:443 | www.remotepc.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.remotepc.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
static.remotepc.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
spoolsv.exe | dll main |
spoolsv.exe | RemotePC Printer Initialization |
spoolsv.exe | InitializePrintMonitor2 |
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Port monitor successfully installed.
|
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Printer drivers copied or already exist.
|
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Redirection port added.
|
spoolsv.exe | open port |