| download: | CUENTA%20DE%20COBRO.tbz |
| Full analysis: | https://app.any.run/tasks/29f2af65-b01e-42d3-a61d-5f0e6dd4a6db |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 12:13:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
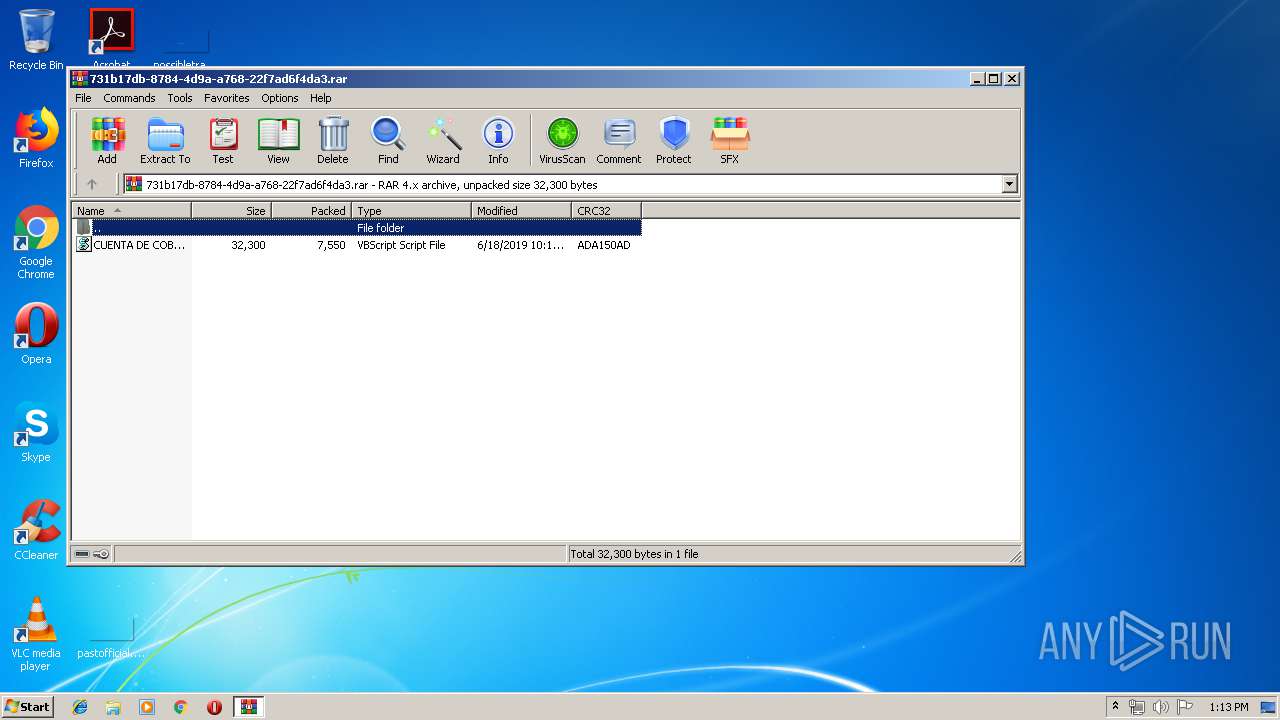
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | C6BBE5083F6C1A4CBA9A12EA75AF07C5 |
| SHA1: | 9BF72BD9A78B5737E8BD88B00D05CBD76A0019DA |
| SHA256: | EF9E23977E1CFD1517A4D9B3954DBB5C5F6BCE50BF9C4B9693C30FEB144F7733 |
| SSDEEP: | 192:TBe9O/tOayGHVtVPdUEUzoC0dZc8W7iTHMGr+neovGsbqcdfx:TBe9O/Aa5HVtVPjUzoC0TUiTHMGrCesD |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 3204)
- WScript.exe (PID: 2268)
- wscript.exe (PID: 3212)
Changes the autorun value in the registry
- WScript.exe (PID: 3204)
- wscript.exe (PID: 3212)
- WScript.exe (PID: 2268)
SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 2860)
- WScript.exe (PID: 3204)
- WScript.exe (PID: 2268)
Creates files in the user directory
- WScript.exe (PID: 3204)
Application launched itself
- WScript.exe (PID: 3204)
- WScript.exe (PID: 2268)
Reads Internet Cache Settings
- wscript.exe (PID: 3212)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 7595 |
|---|---|
| UncompressedSize: | 32300 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:06:18 10:13:15 |
| PackingMethod: | Normal |
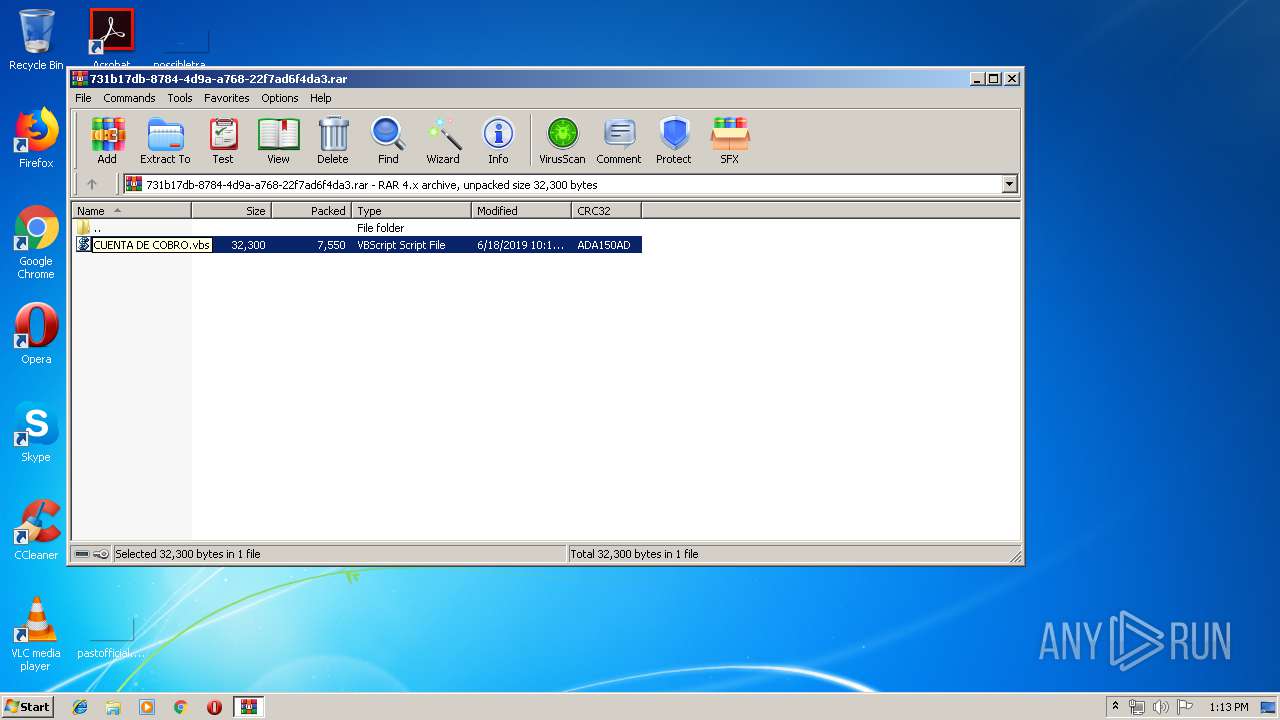
| ArchivedFileName: | CUENTA DE COBRO.vbs |
Total processes
37
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2268 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.46798\CUENTA DE COBRO.vbs" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2640 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\CUENTA DE COBRO.vbs" | C:\Windows\System32\wscript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\731b17db-8784-4d9a-a768-22f7ad6f4da3.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3204 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.41676\CUENTA DE COBRO.vbs" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3212 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\CUENTA DE COBRO.vbs" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
852
Read events
787
Write events
65
Delete events
0
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\731b17db-8784-4d9a-a768-22f7ad6f4da3.rar | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | WScript.exe | C:\Users\admin\AppData\Roaming\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
| 3212 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.41676\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
| 3204 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
| 2268 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.46798\CUENTA DE COBRO.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | wscript.exe | 186.82.243.168:1992 | bvs2019.duckdns.org | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bvs2019.duckdns.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |