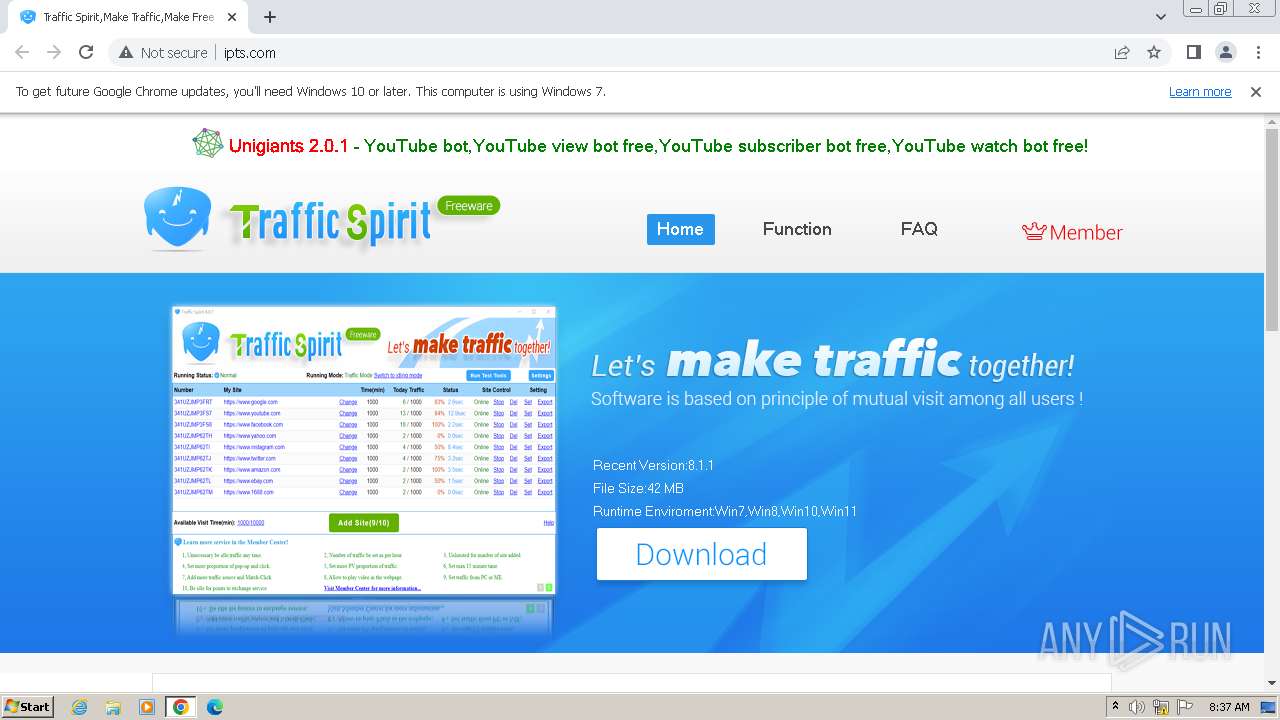
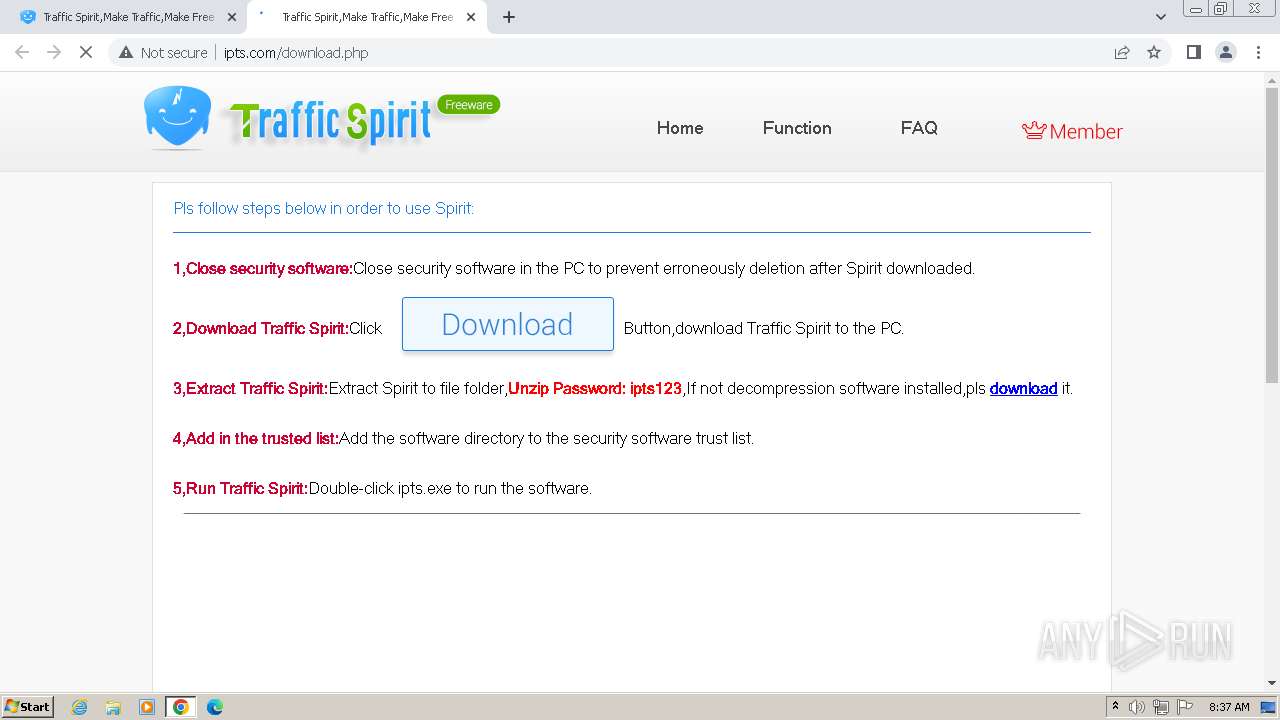
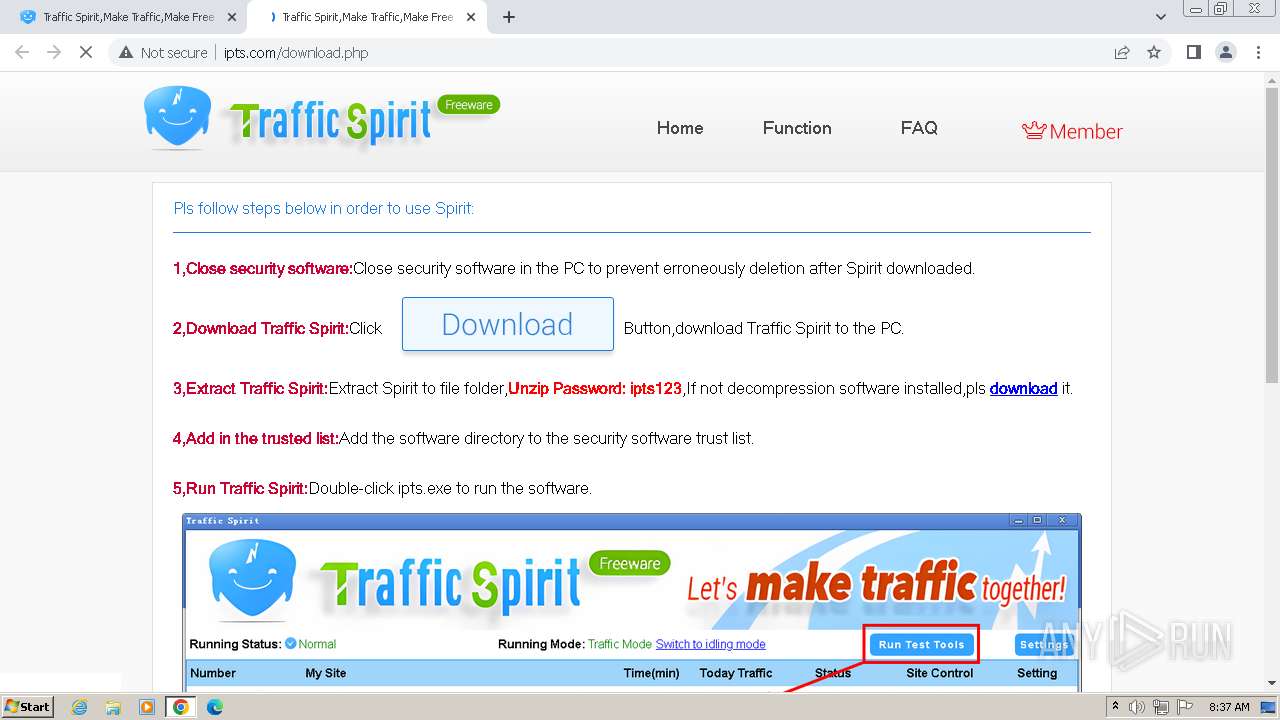
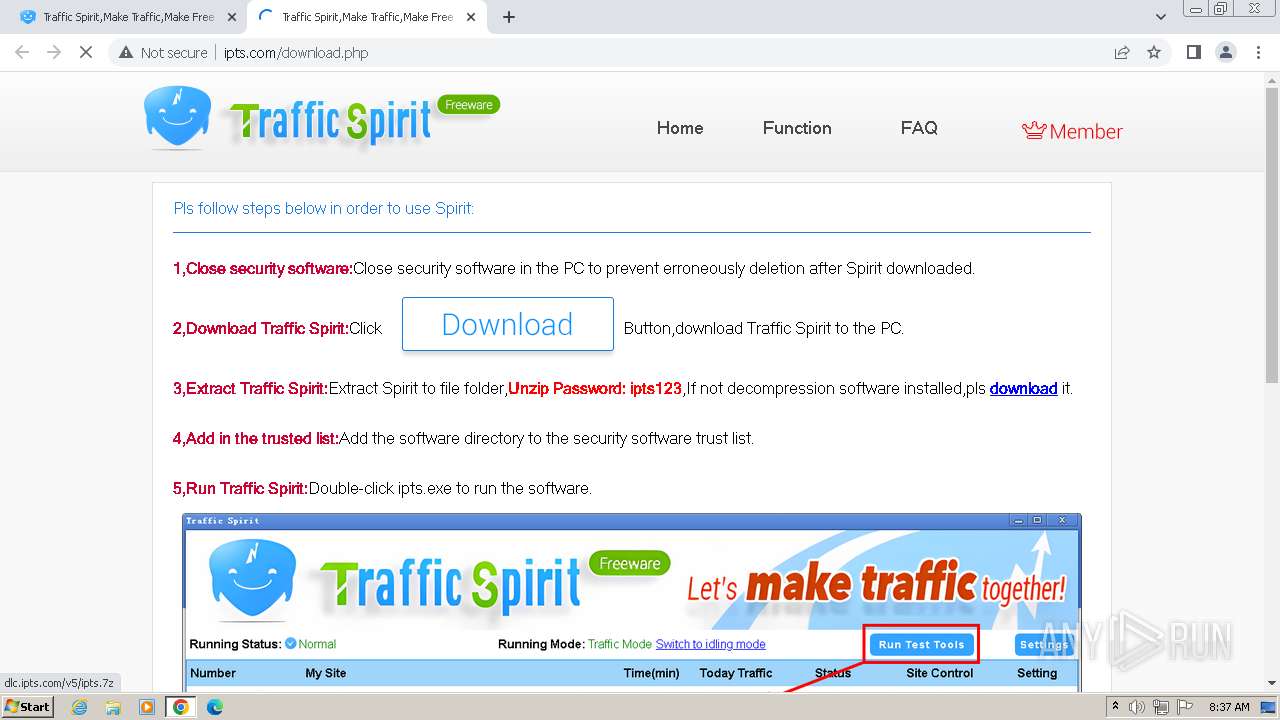
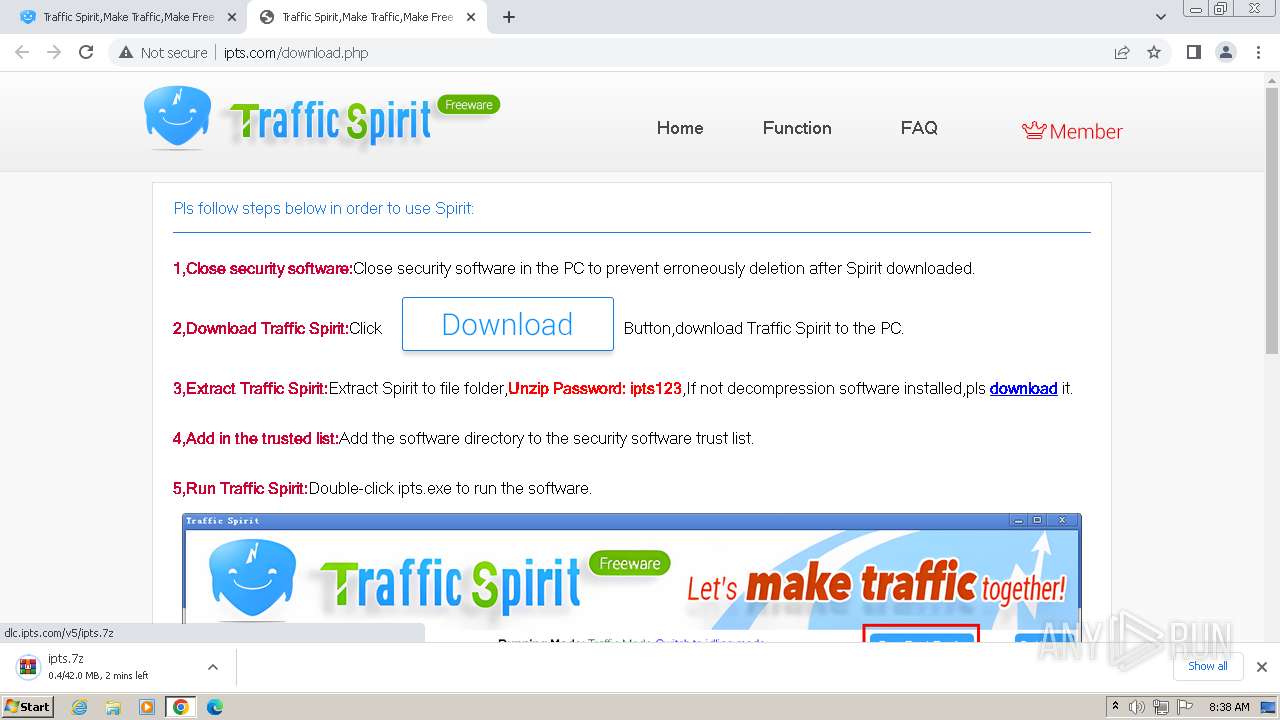
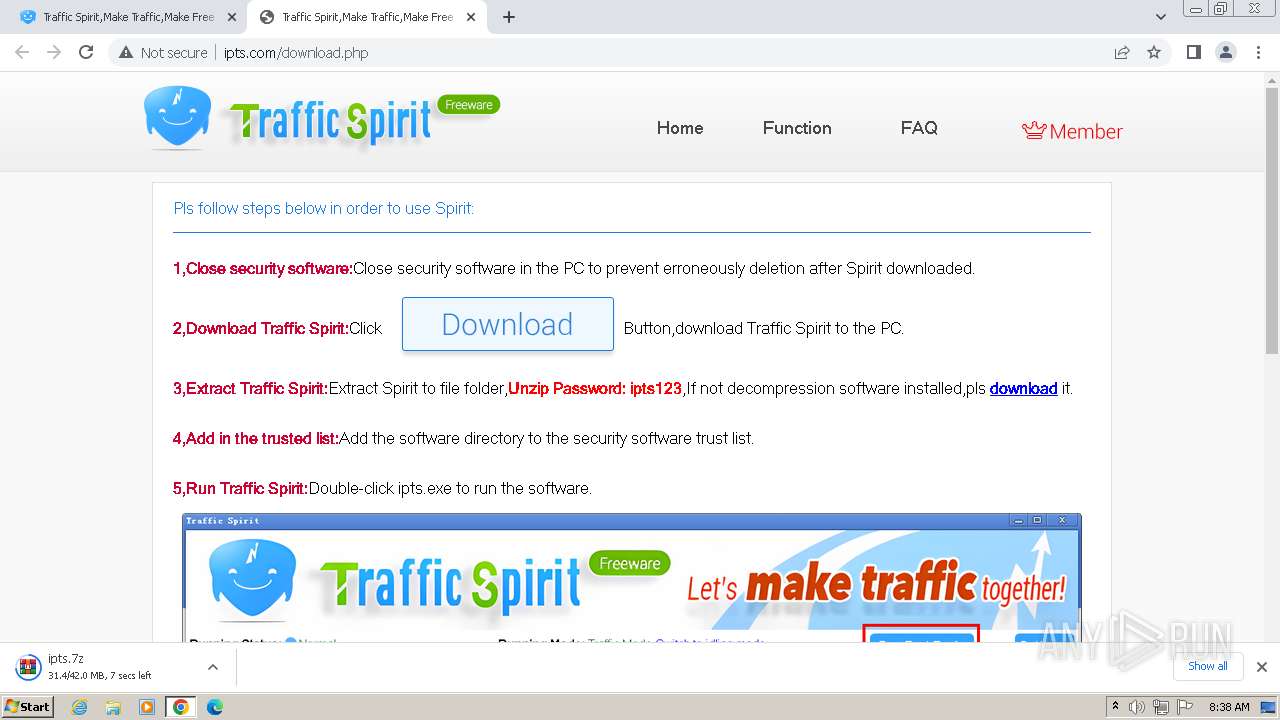
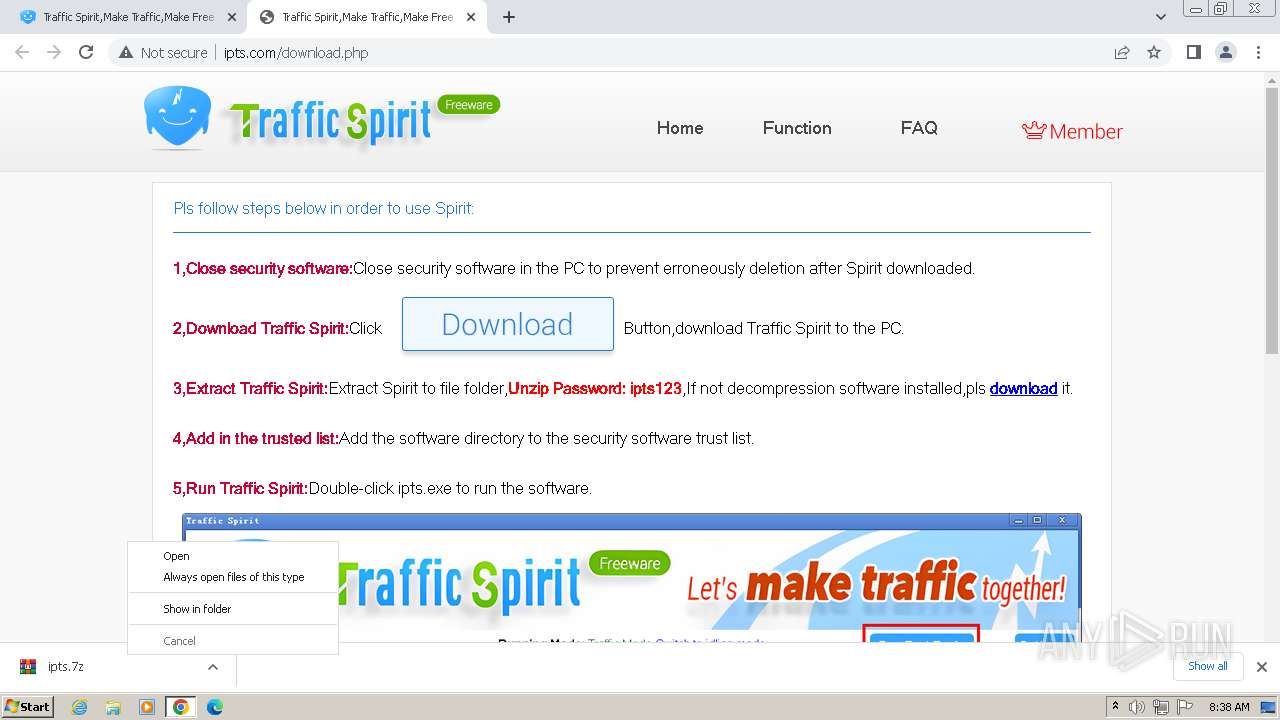
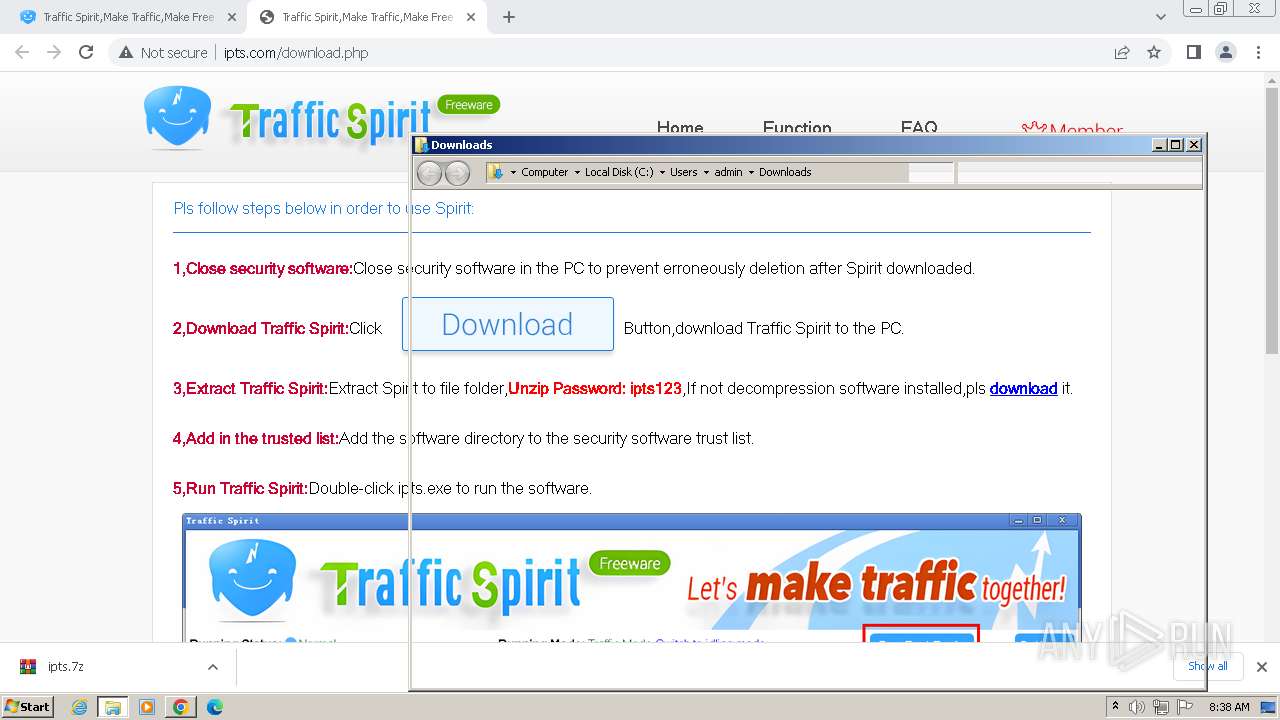
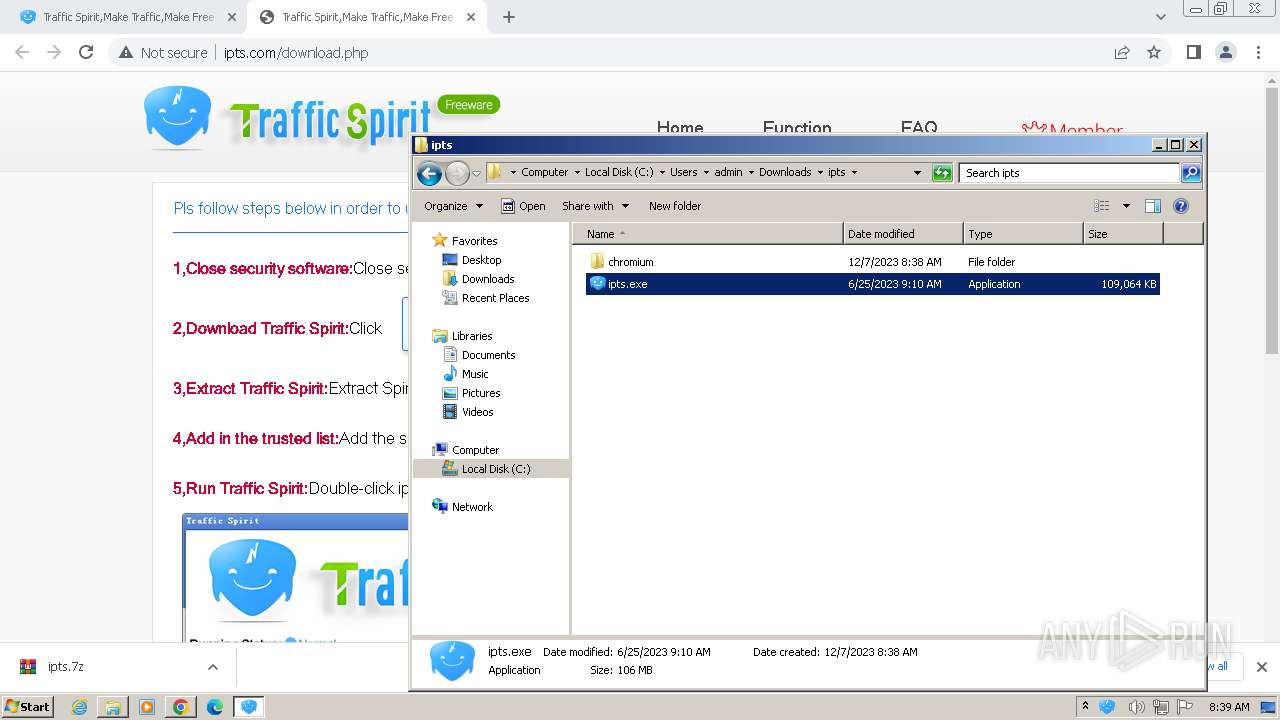
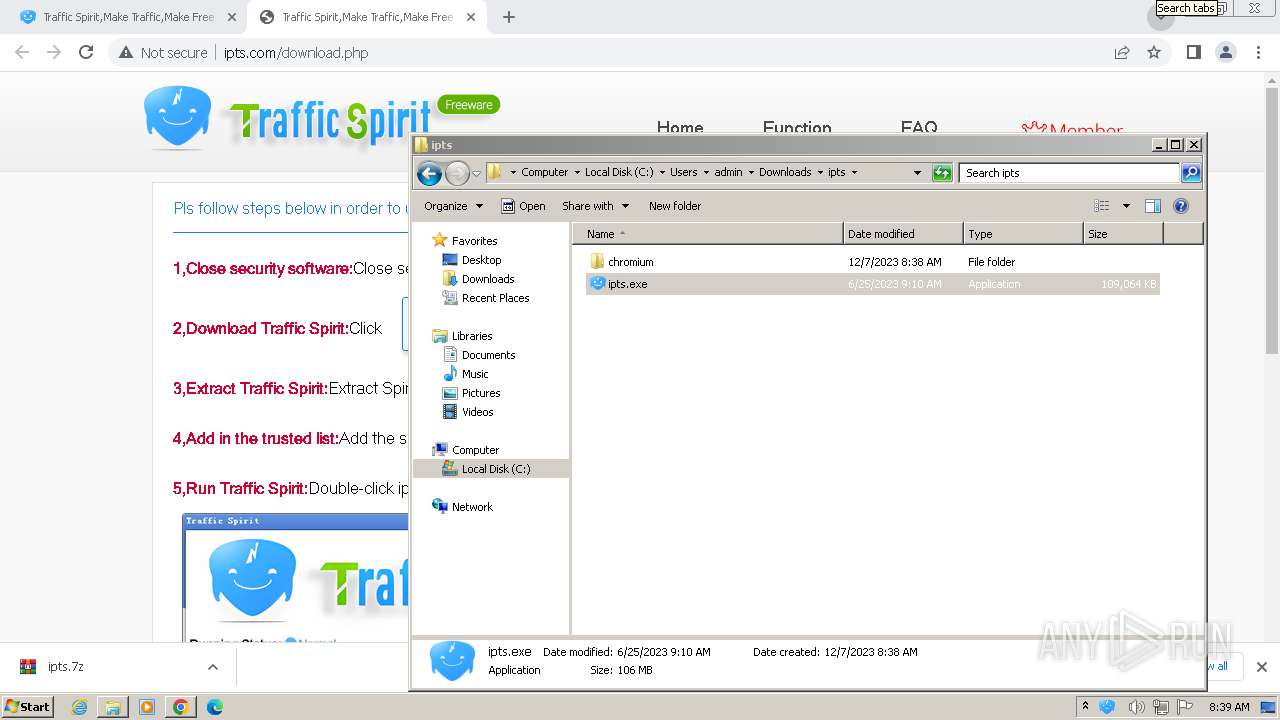
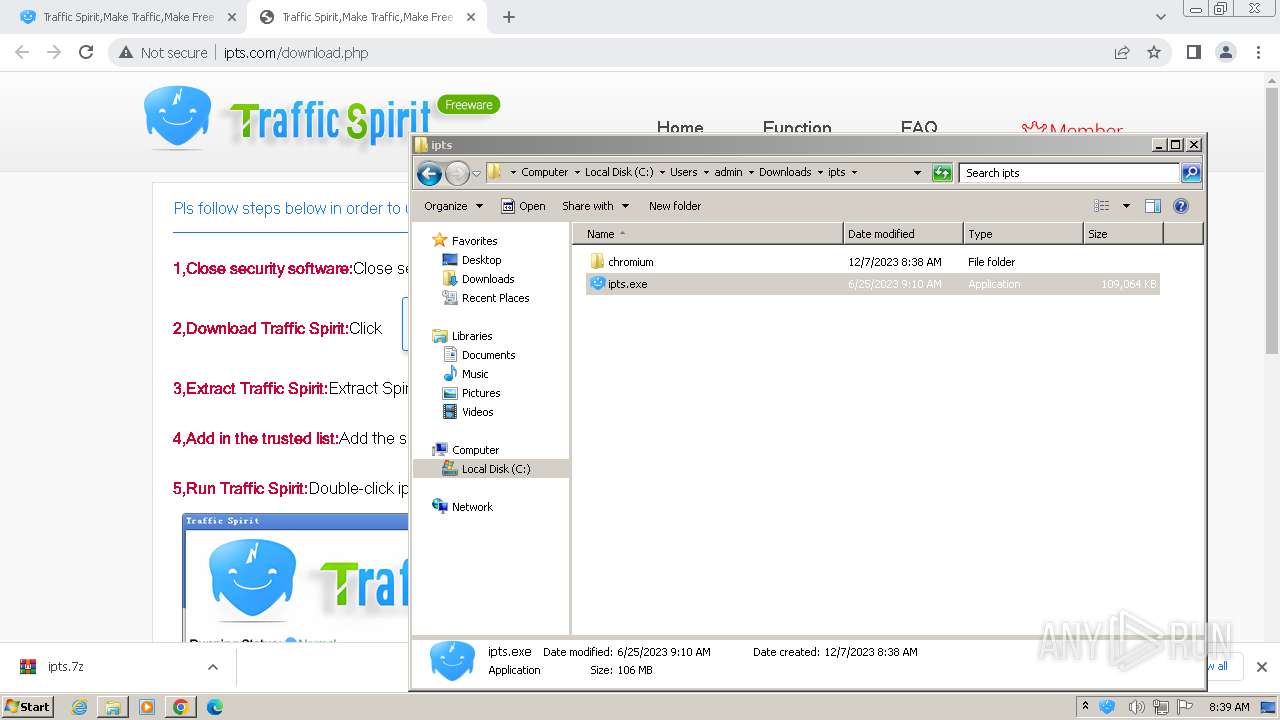
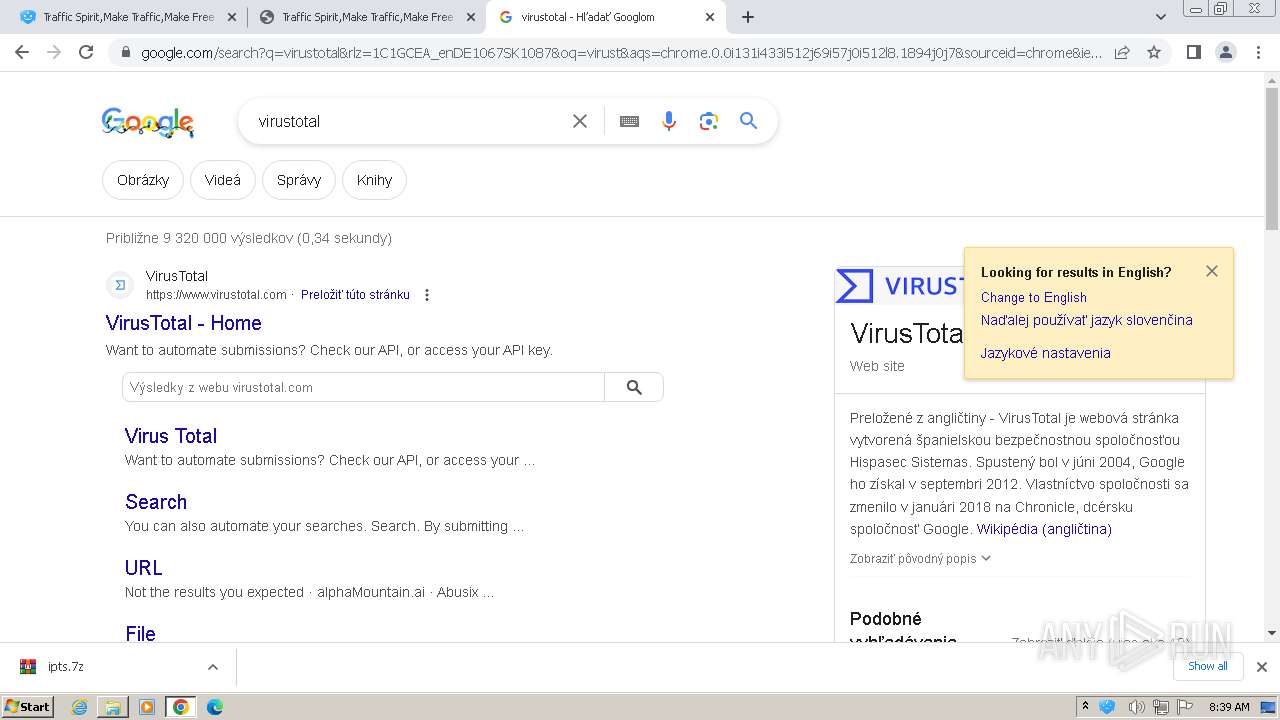
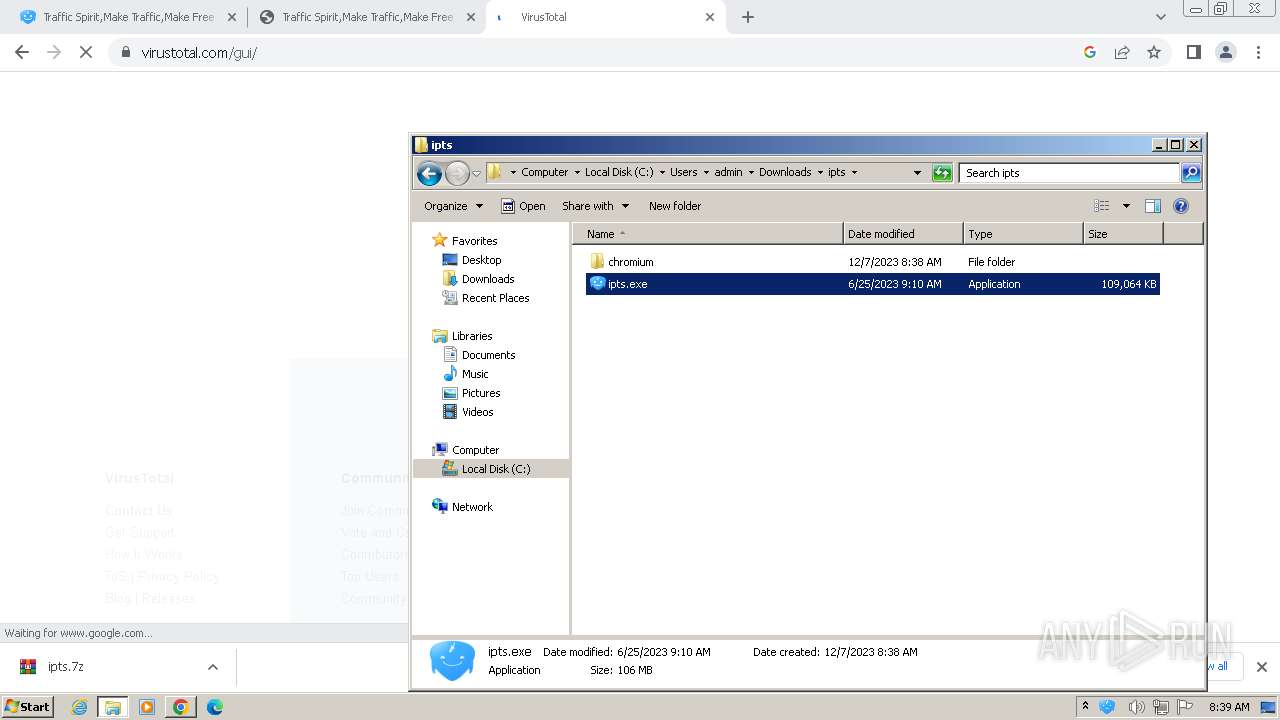
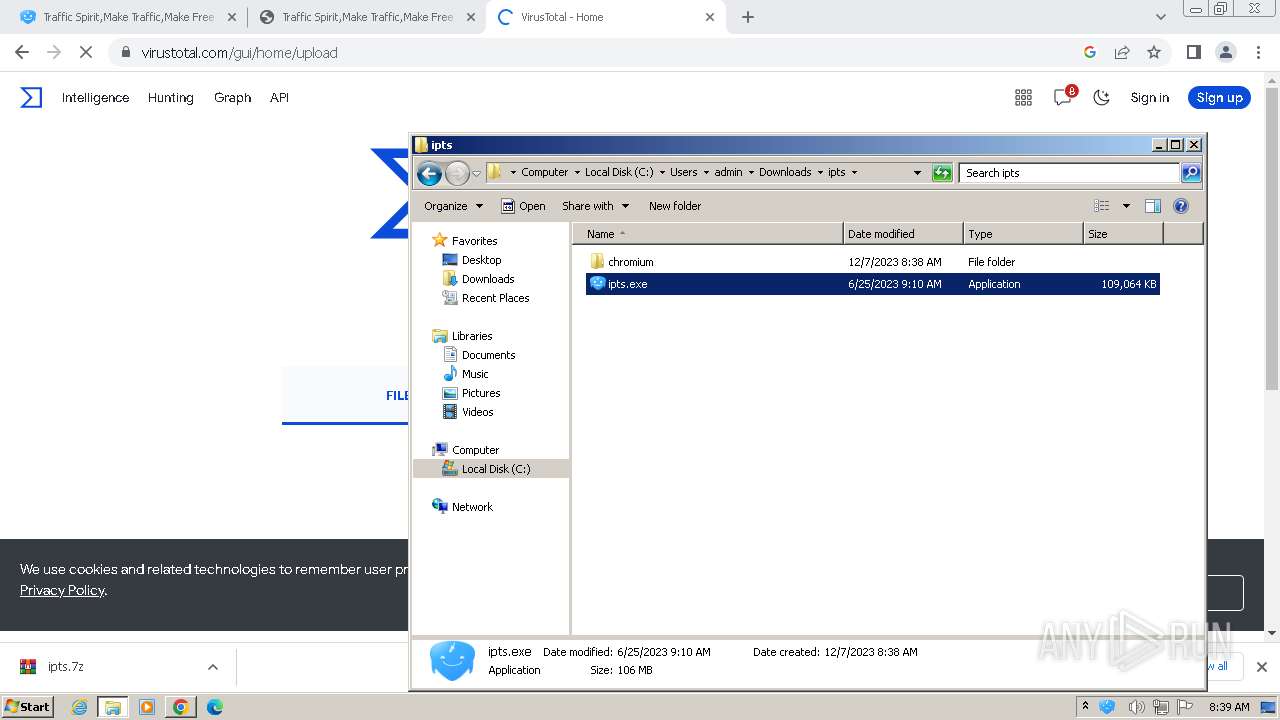
| URL: | http://www.ipts.com/ |
| Full analysis: | https://app.any.run/tasks/cbc1f97c-6263-4361-b02f-e9d7e232f4e3 |
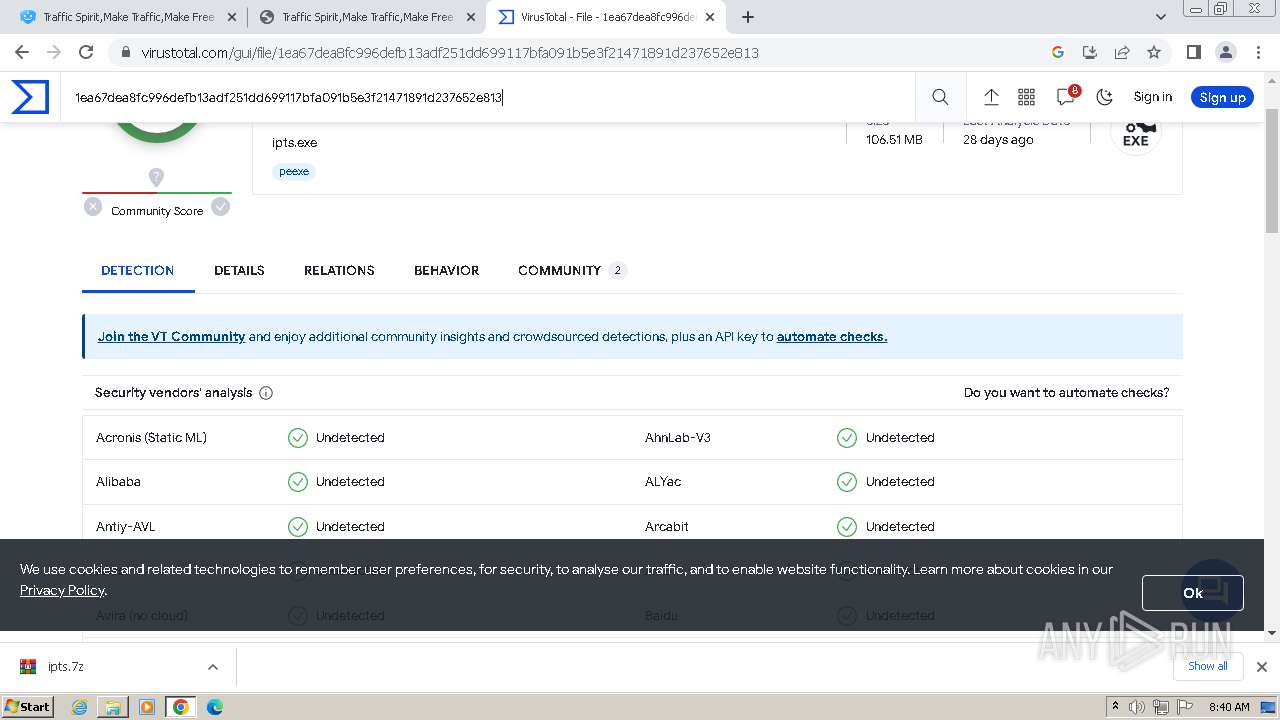
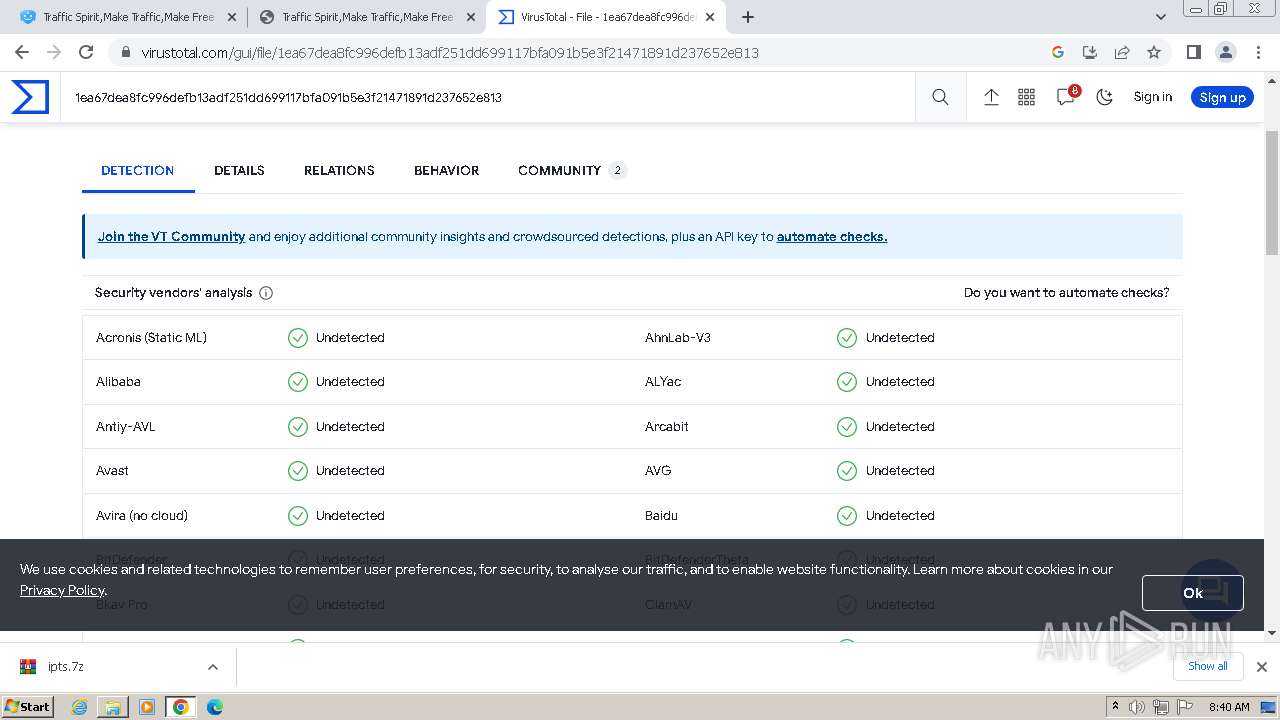
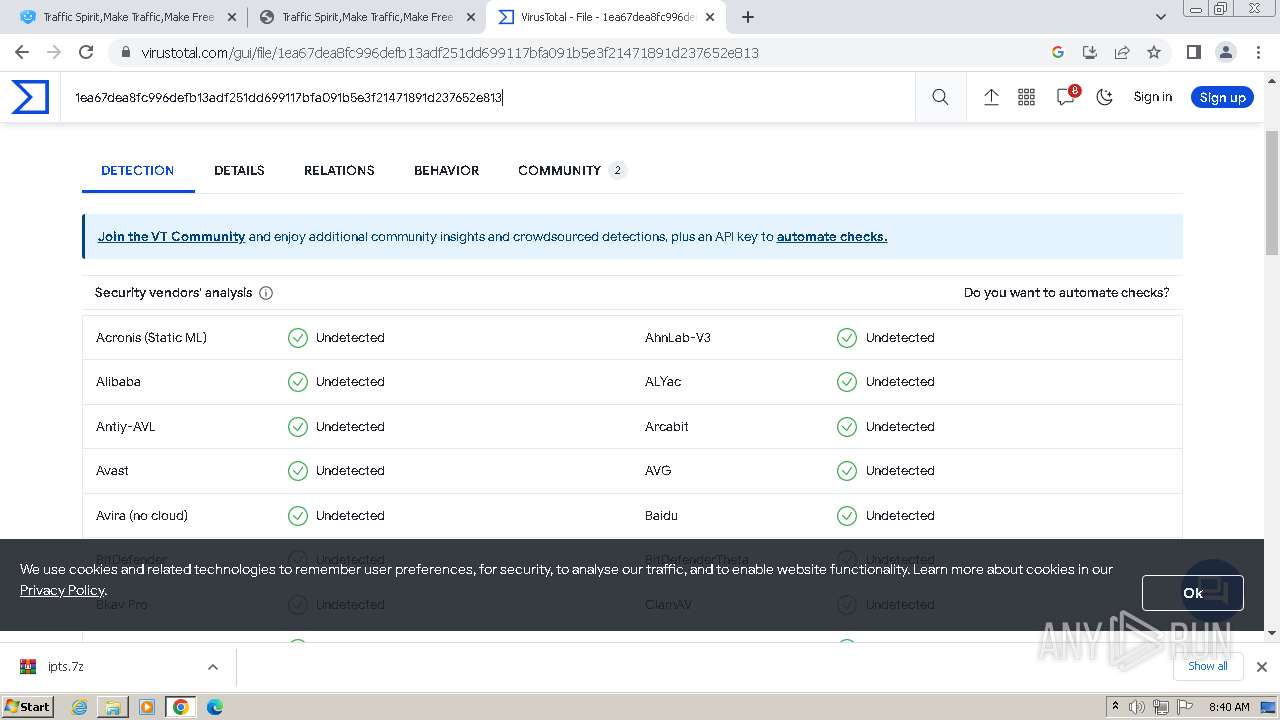
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2023, 08:37:26 |
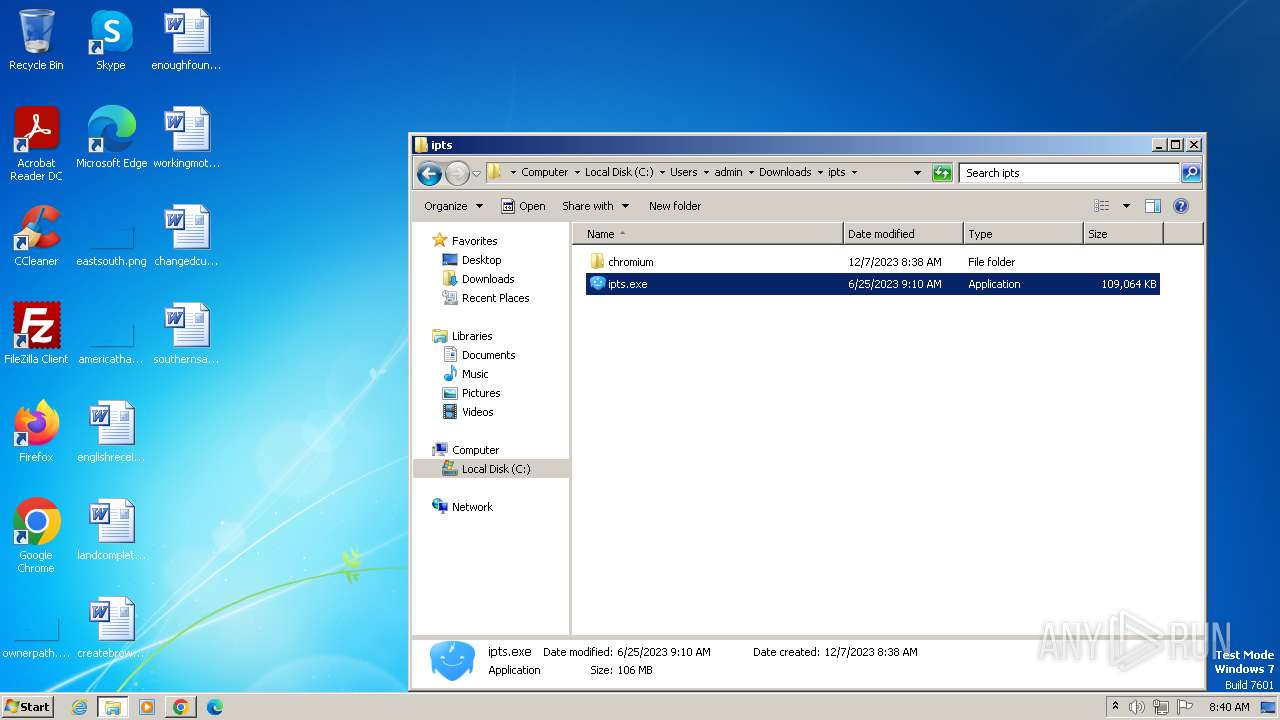
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
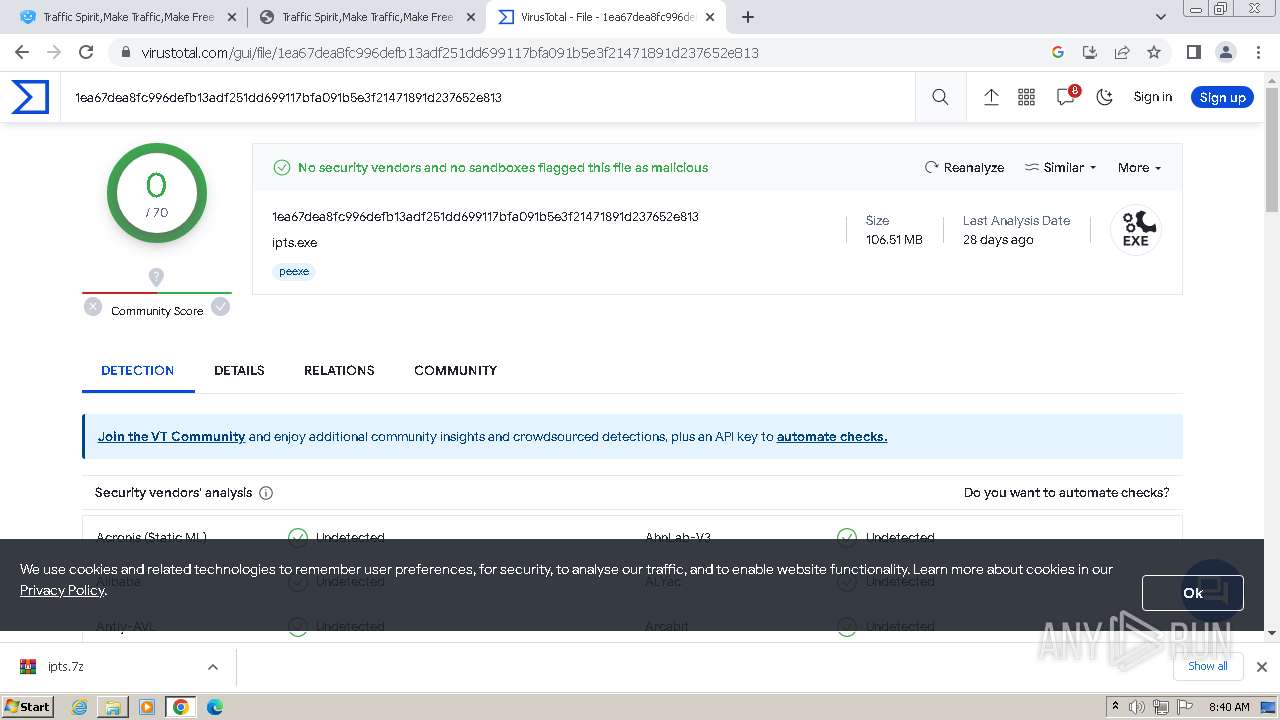
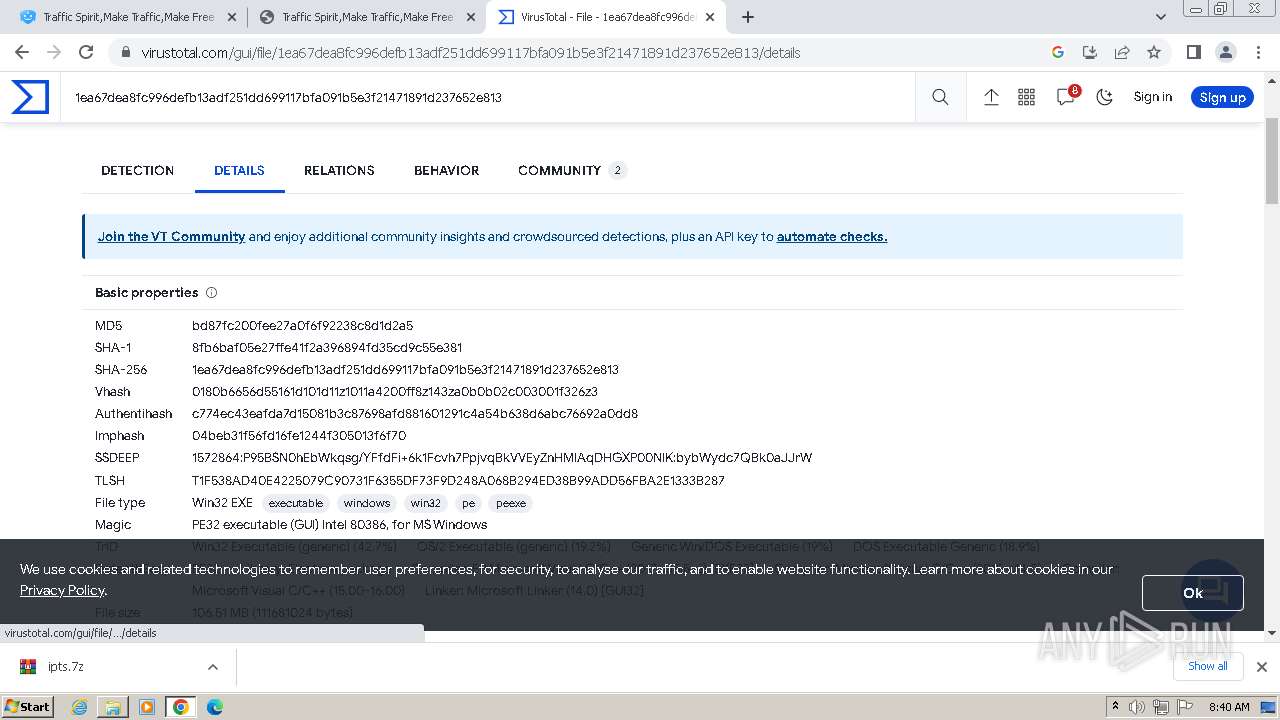
| MD5: | 0E72A6EA889827BFA1E618E6B46AE8FD |
| SHA1: | DF9A6D6D6DB1EB6581A57E3598DCA830110093E4 |
| SHA256: | EF87EDB74ACAFBFF0B327D864081CC7EC133497FA174A957AC53453EA58FF7C9 |
| SSDEEP: | 3:N1KJS4rLdIKn:Cc4rLd3 |
MALICIOUS
Actions looks like stealing of personal data
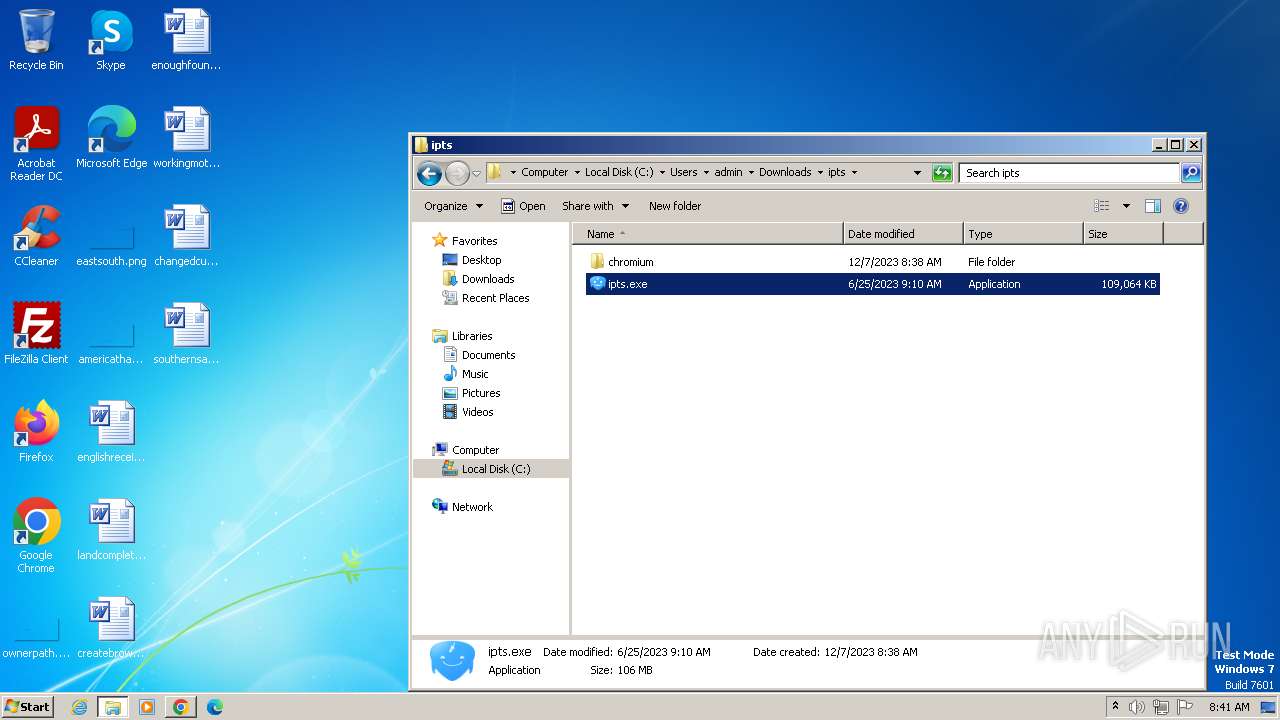
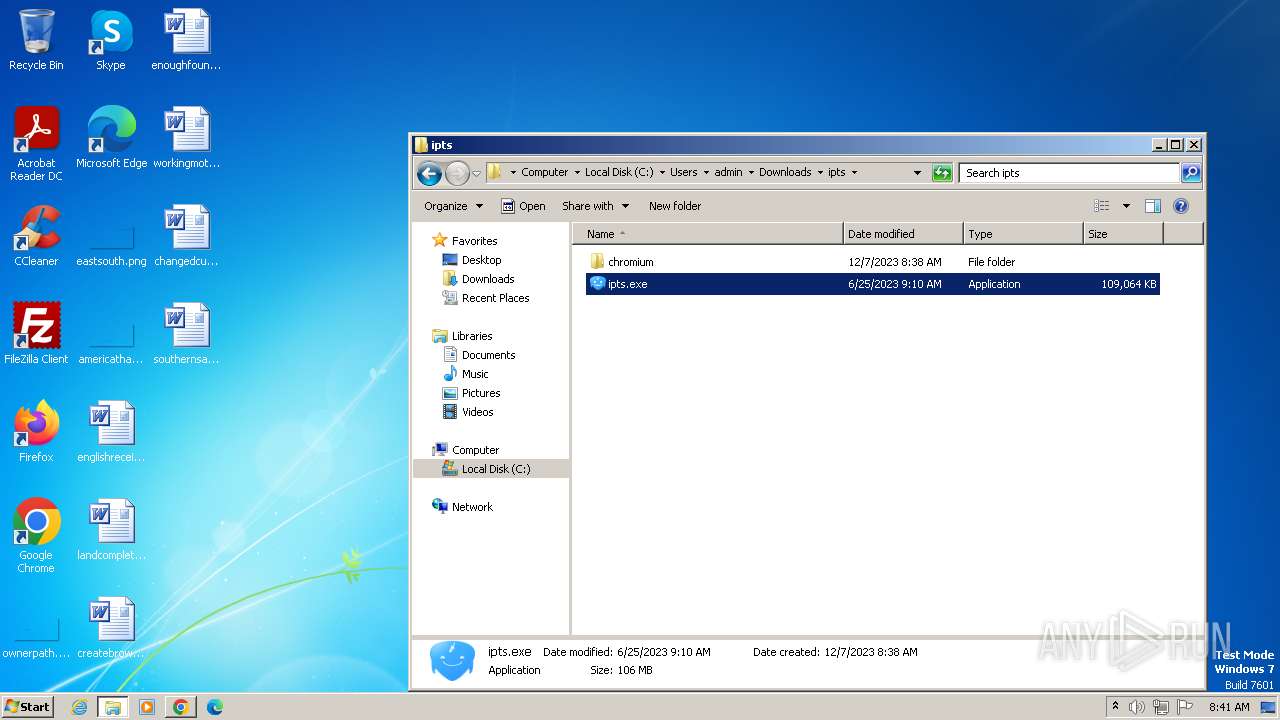
- WinRAR.exe (PID: 2552)
- ipts.exe (PID: 2624)
- ipts.exe (PID: 2152)
- ipts.exe (PID: 3752)
- ipts.exe (PID: 3792)
- ipts.exe (PID: 3220)
- ipts.exe (PID: 1356)
- ipts.exe (PID: 2468)
- ipts.exe (PID: 3140)
- ipts.exe (PID: 3248)
- ipts.exe (PID: 2936)
- ipts.exe (PID: 3976)
- ipts.exe (PID: 3900)
- ipts.exe (PID: 3240)
- ipts.exe (PID: 1152)
- ipts.exe (PID: 3320)
- ipts.exe (PID: 2648)
- ipts.exe (PID: 3400)
- ipts.exe (PID: 3356)
- ipts.exe (PID: 4620)
- ipts.exe (PID: 4720)
- ipts.exe (PID: 1232)
- ipts.exe (PID: 4808)
- ipts.exe (PID: 5152)
- ipts.exe (PID: 5028)
- ipts.exe (PID: 4424)
- ipts.exe (PID: 5232)
- ipts.exe (PID: 5480)
- ipts.exe (PID: 5372)
- ipts.exe (PID: 5536)
- ipts.exe (PID: 5640)
- ipts.exe (PID: 5888)
- ipts.exe (PID: 5712)
- ipts.exe (PID: 5808)
SUSPICIOUS
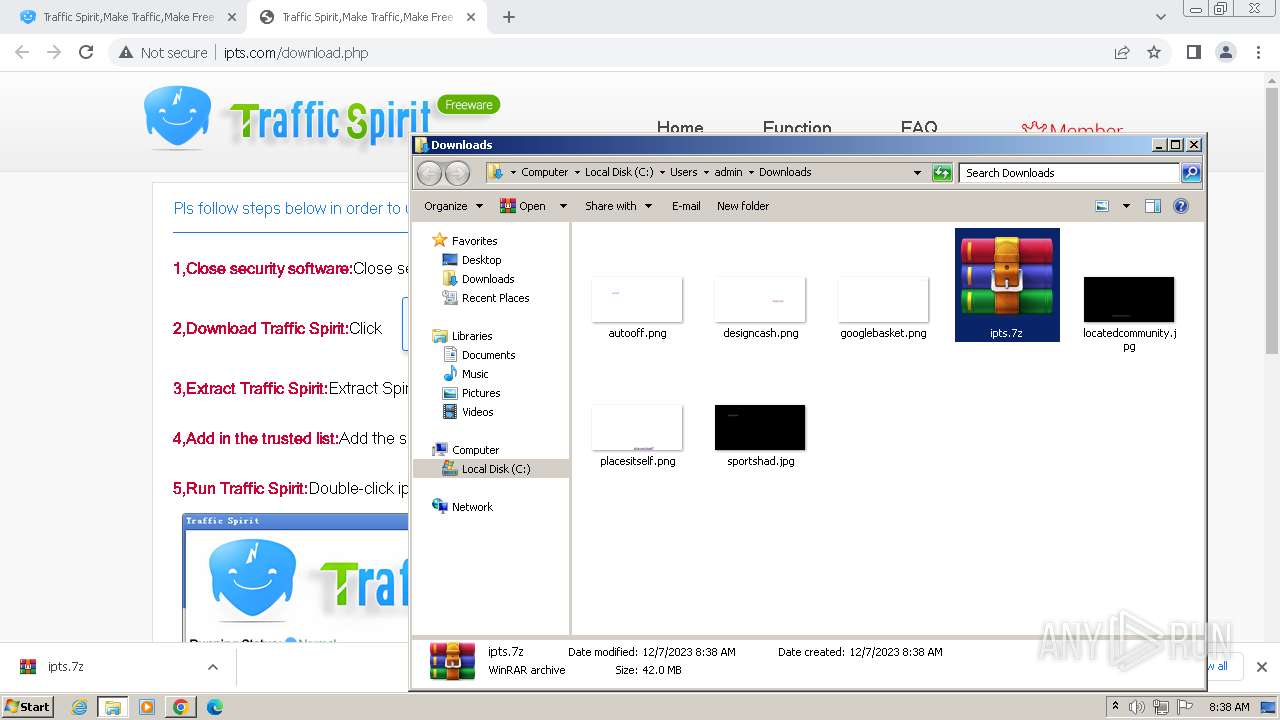
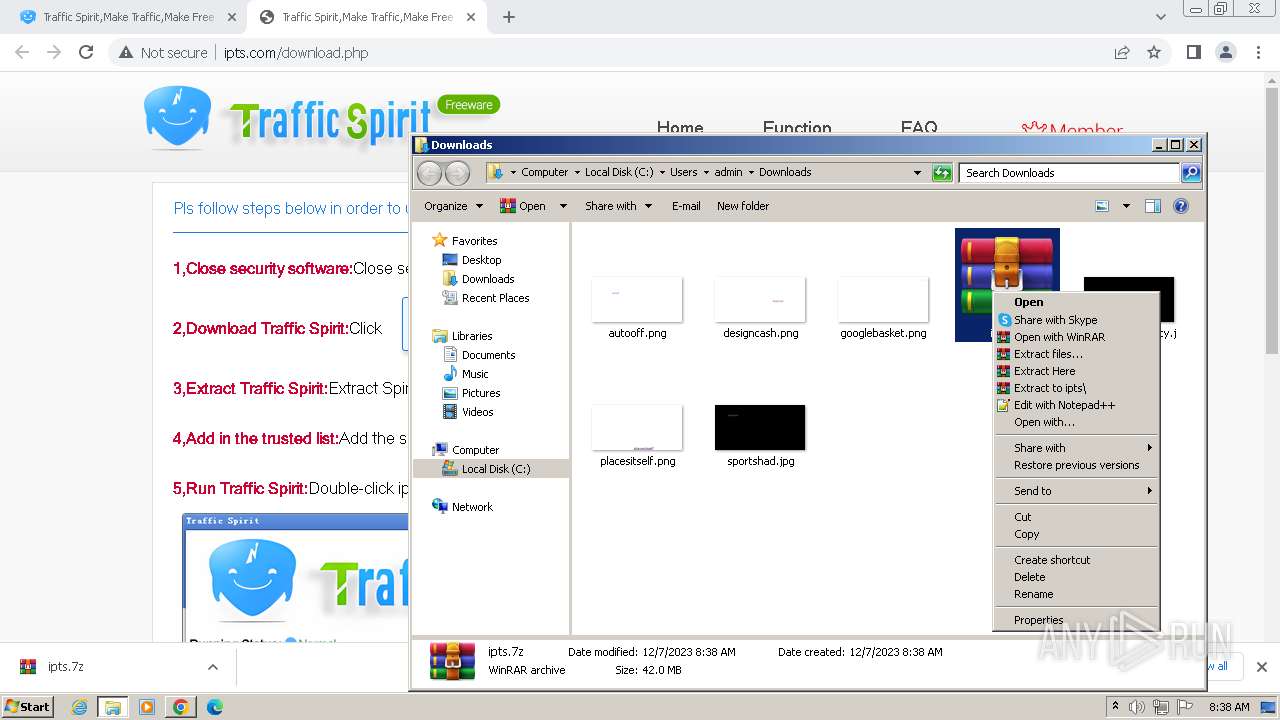
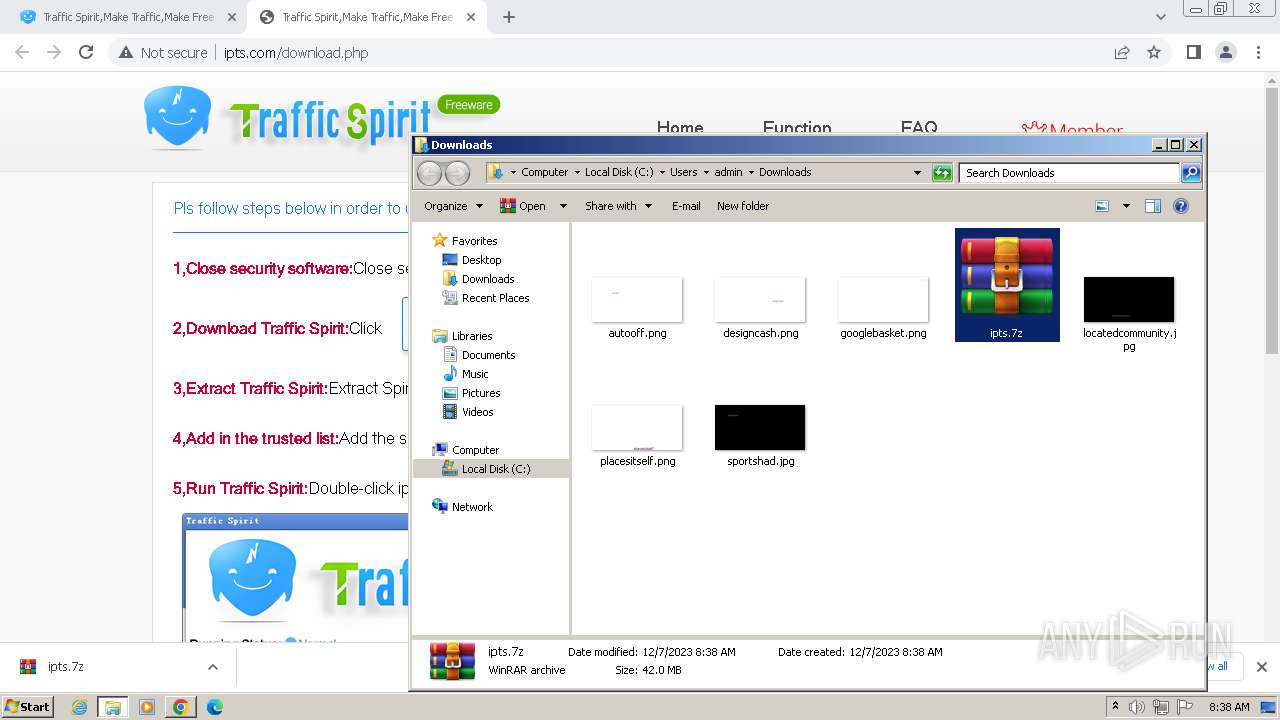
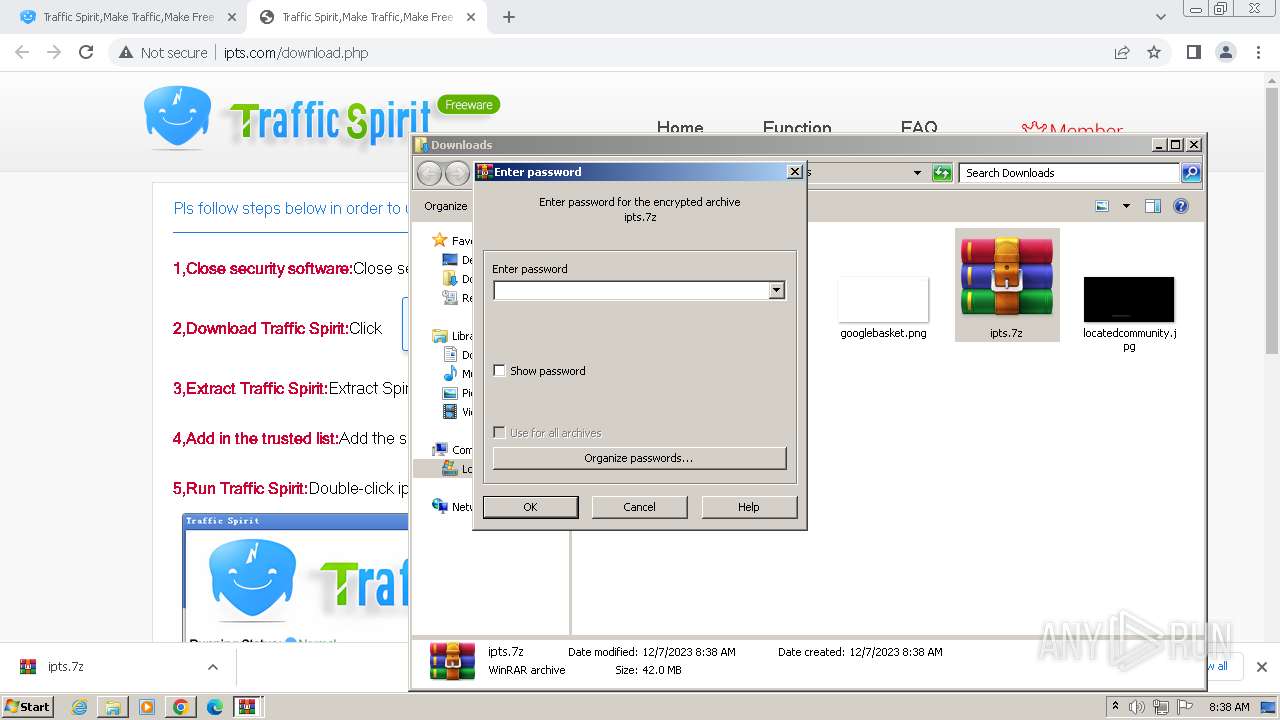
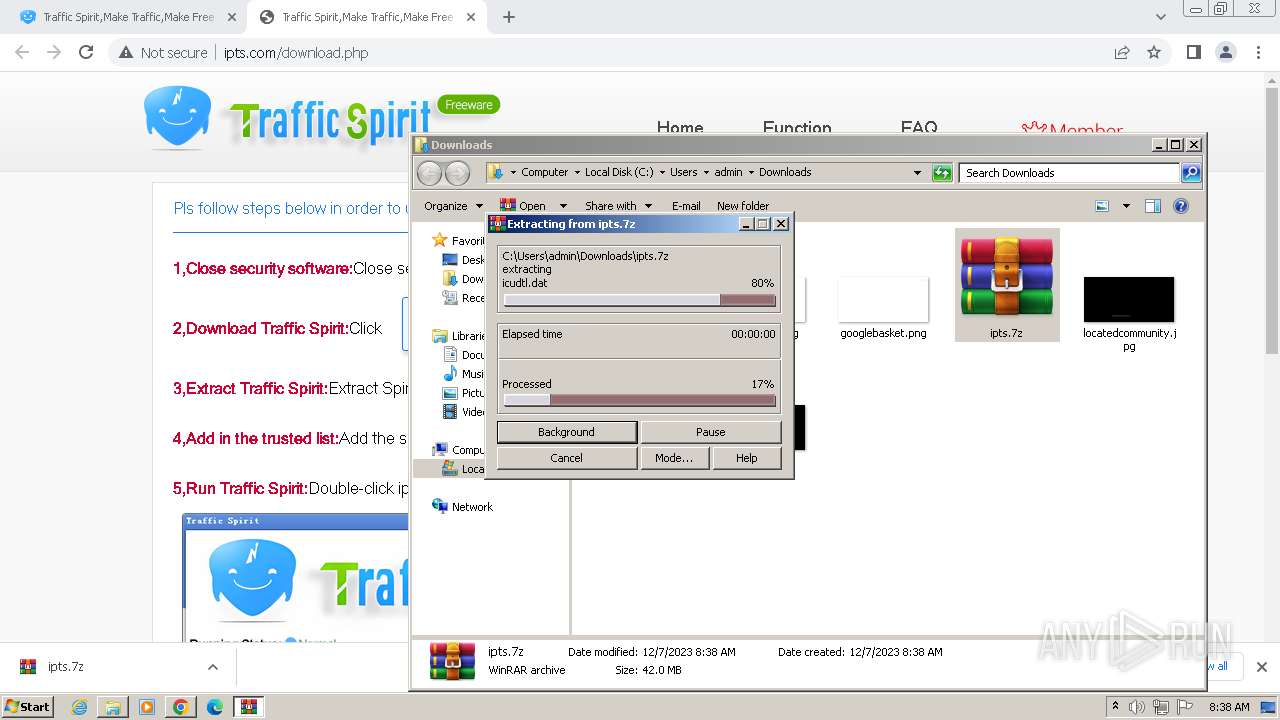
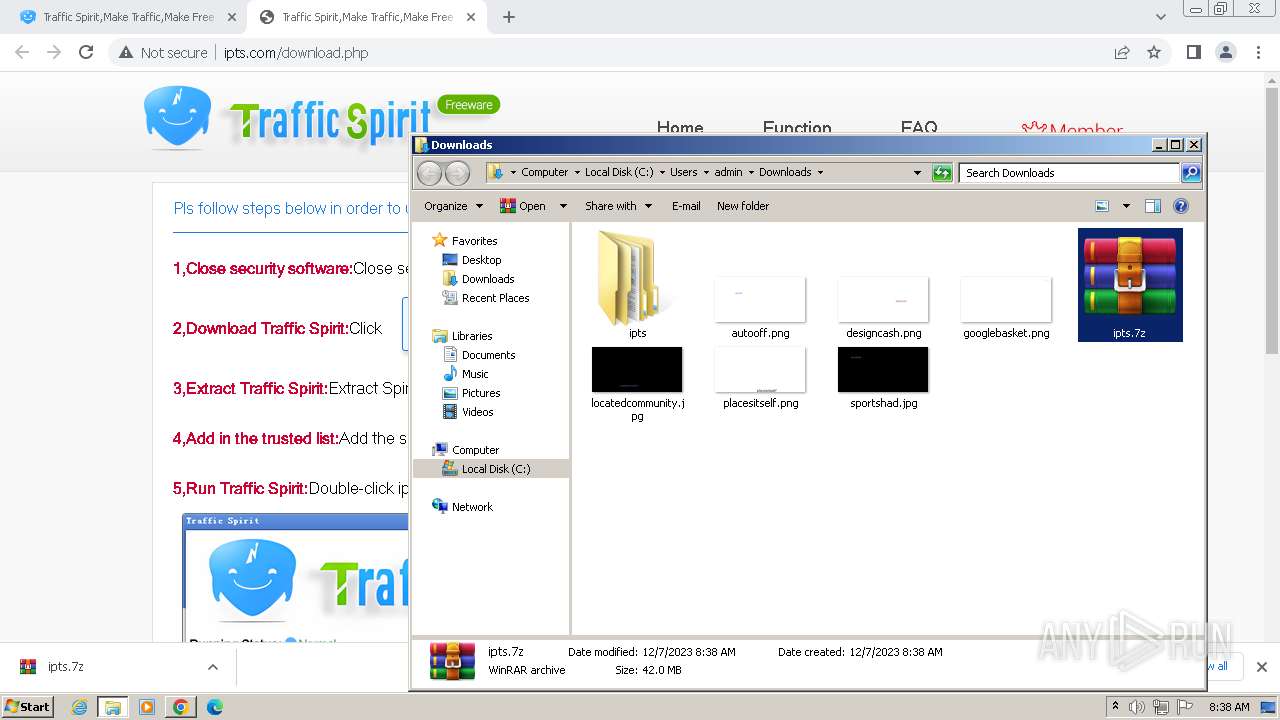
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 2552)
Process drops legitimate windows executable
- WinRAR.exe (PID: 2552)
Reads settings of System Certificates
- ipts.exe (PID: 2624)
- ipts.exe (PID: 2468)
Application launched itself
- ipts.exe (PID: 2468)
- ipts.exe (PID: 2624)
Process requests binary or script from the Internet
- ipts.exe (PID: 2152)
- ipts.exe (PID: 3220)
Connects to unusual port
- ipts.exe (PID: 3220)
INFO
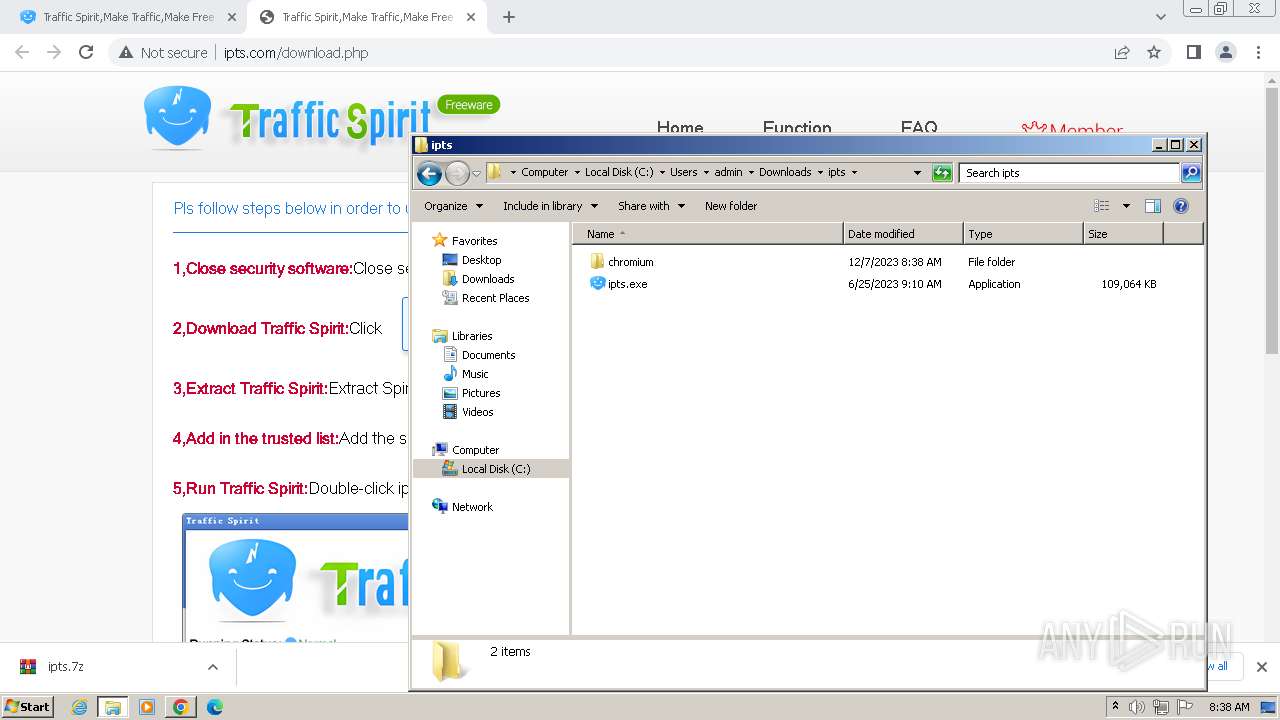
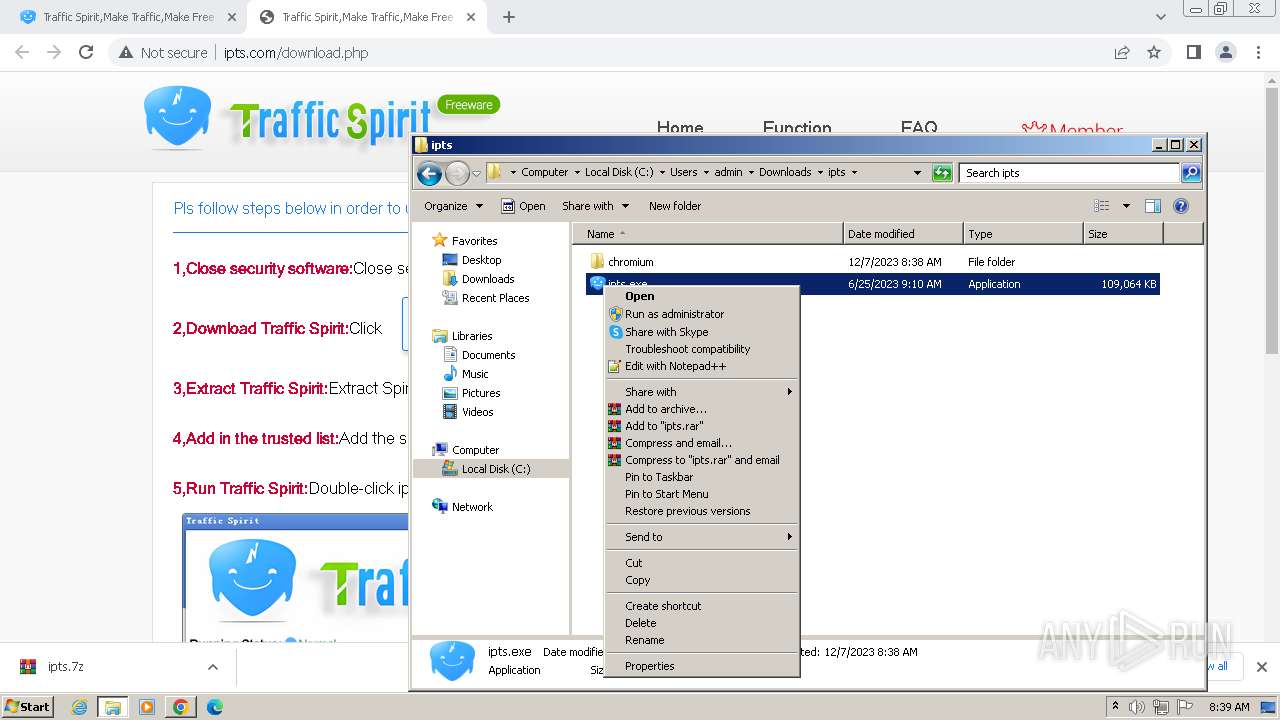
Manual execution by a user
- wmpnscfg.exe (PID: 3556)
- WinRAR.exe (PID: 2552)
- ipts.exe (PID: 2624)
Reads the computer name
- wmpnscfg.exe (PID: 3556)
- ipts.exe (PID: 2624)
- ipts.exe (PID: 2468)
- ipts.exe (PID: 2152)
- ipts.exe (PID: 3752)
- ipts.exe (PID: 3220)
- ipts.exe (PID: 1152)
- ipts.exe (PID: 2648)
Checks supported languages
- wmpnscfg.exe (PID: 3556)
- ipts.exe (PID: 2624)
- ipts.exe (PID: 3900)
- ipts.exe (PID: 2152)
- ipts.exe (PID: 1356)
- ipts.exe (PID: 3752)
- ipts.exe (PID: 2468)
- ipts.exe (PID: 3220)
- ipts.exe (PID: 3792)
- ipts.exe (PID: 3248)
- ipts.exe (PID: 1152)
- ipts.exe (PID: 3140)
- ipts.exe (PID: 2936)
- ipts.exe (PID: 3240)
- ipts.exe (PID: 3976)
- ipts.exe (PID: 3356)
- ipts.exe (PID: 3320)
- ipts.exe (PID: 2648)
- ipts.exe (PID: 3400)
- ipts.exe (PID: 4424)
- ipts.exe (PID: 4620)
- ipts.exe (PID: 1232)
- ipts.exe (PID: 5028)
- ipts.exe (PID: 5152)
- ipts.exe (PID: 4720)
- ipts.exe (PID: 4808)
- ipts.exe (PID: 5536)
- ipts.exe (PID: 5372)
- ipts.exe (PID: 5480)
- ipts.exe (PID: 5232)
- ipts.exe (PID: 5640)
- ipts.exe (PID: 5808)
- ipts.exe (PID: 5888)
- ipts.exe (PID: 5712)
The process uses the downloaded file
- chrome.exe (PID: 1436)
- WinRAR.exe (PID: 2552)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3560)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2552)
Create files in a temporary directory
- ipts.exe (PID: 2624)
- ipts.exe (PID: 2152)
- ipts.exe (PID: 2468)
Reads CPU info
- ipts.exe (PID: 2624)
Process checks computer location settings
- ipts.exe (PID: 1356)
- ipts.exe (PID: 2624)
- ipts.exe (PID: 3248)
- ipts.exe (PID: 2468)
- ipts.exe (PID: 2936)
- ipts.exe (PID: 3240)
- ipts.exe (PID: 3976)
- ipts.exe (PID: 3356)
- ipts.exe (PID: 3320)
- ipts.exe (PID: 3140)
- ipts.exe (PID: 1232)
- ipts.exe (PID: 3400)
- ipts.exe (PID: 4424)
- ipts.exe (PID: 4620)
- ipts.exe (PID: 4808)
- ipts.exe (PID: 5028)
- ipts.exe (PID: 4720)
- ipts.exe (PID: 5152)
- ipts.exe (PID: 5372)
- ipts.exe (PID: 5480)
- ipts.exe (PID: 5232)
- ipts.exe (PID: 5536)
- ipts.exe (PID: 5640)
- ipts.exe (PID: 5808)
- ipts.exe (PID: 5888)
- ipts.exe (PID: 5712)
Application launched itself
- chrome.exe (PID: 3048)
Reads the machine GUID from the registry
- ipts.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
72
Malicious processes
36
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a7a8b38,0x6a7a8b48,0x6a7a8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3972 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=700 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3948 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1152 | "C:\Users\admin\Downloads\ipts\ipts.exe" --type=gpu-process --ub-type=urltask --image-replacement --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1244 --field-trial-handle=880,i,15034960352724101634,11012796498388769304,131072 /prefetch:2 | C:\Users\admin\Downloads\ipts\ipts.exe | ipts.exe | ||||||||||||
User: admin Company: Spiritsoft(www.ipts.com) Integrity Level: MEDIUM Description: Traffic Spirit(http://www.ipts.com) Exit code: 0 Version: 2023.6.26.43 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=3168 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\Downloads\ipts\ipts.exe" --type=renderer --ub-type=urltask --image-replacement --disable-databases --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=2664 --field-trial-handle=880,i,15034960352724101634,11012796498388769304,131072 /prefetch:1 | C:\Users\admin\Downloads\ipts\ipts.exe | ipts.exe | ||||||||||||
User: admin Company: Spiritsoft(www.ipts.com) Integrity Level: LOW Description: Traffic Spirit(http://www.ipts.com) Exit code: 0 Version: 2023.6.26.43 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1132 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\Downloads\ipts\ipts.exe" --type=renderer --first-renderer-process --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=1736 --field-trial-handle=1220,i,15097729437612262155,4109736325751113929,131072 /prefetch:1 | C:\Users\admin\Downloads\ipts\ipts.exe | ipts.exe | ||||||||||||
User: admin Company: Spiritsoft(www.ipts.com) Integrity Level: LOW Description: Traffic Spirit(http://www.ipts.com) Exit code: 0 Version: 2023.6.26.43 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3296 --field-trial-handle=1140,i,18142086002633310574,16095521504409264859,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
7 533
Read events
7 382
Write events
150
Delete events
1
Modification events
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
9
Suspicious files
390
Text files
35
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF210435.TMP | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:23C08E7178FEB5BA68E821CD2D35736E | SHA256:5471CBD1BD61B917801D71D41A45B2CEEE3FE6837782DDD47D84424BFD938BFD | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8175FB7046E977DAAD01289080C116EF | SHA256:19E403B4BEF7D83DD425AB6A54DE943D244A16E5EA121DEC91C417608AEAACB7 | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF210435.TMP | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF210ba7.TMP | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF21201a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
901
DNS requests
435
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/ | unknown | html | 3.75 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/unigiants.png | unknown | image | 3.11 Kb | unknown |
2544 | chrome.exe | GET | 200 | 203.107.86.226:80 | http://sdk.51.la/js-sdk-pro.min.js | unknown | text | 12.5 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/style/style.css | unknown | text | 521 b | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/vipuser.png | unknown | image | 2.29 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/xz_normal.png | unknown | image | 3.32 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/top_bg.png | unknown | image | 166 b | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/logo.png | unknown | image | 16.2 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/banner_bg.png | unknown | image | 1.03 Kb | unknown |
2544 | chrome.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/easy.png | unknown | image | 5.73 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2544 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3048 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2544 | chrome.exe | 47.88.10.215:80 | www.ipts.com | Alibaba US Technology Co., Ltd. | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2544 | chrome.exe | 203.107.86.226:80 | sdk.51.la | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2544 | chrome.exe | 142.250.184.232:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2544 | chrome.exe | 216.239.34.36:443 | region1.google-analytics.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.ipts.com |
| unknown |
sdk.51.la |
| unknown |
www.googletagmanager.com |
| whitelisted |
collect-v6.51.la |
| unknown |
region1.google-analytics.com |
| whitelisted |
vip.ipts.com |
| unknown |
www.spiritsoft.cn |
| unknown |
www.unigiants.com |
| unknown |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (cutt .ly) |
3220 | ipts.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (cutt .ly in TLS SNI) |
3220 | ipts.exe | Potential Corporate Privacy Violation | AV POLICY Observed TikTok Domain in TLS SNI (tiktok.com) |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3220 | ipts.exe | Not Suspicious Traffic | INFO [ANY.RUN] Firebase Web App Development Platform (firebaseio .com) |
3220 | ipts.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3220 | ipts.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2 ETPRO signatures available at the full report