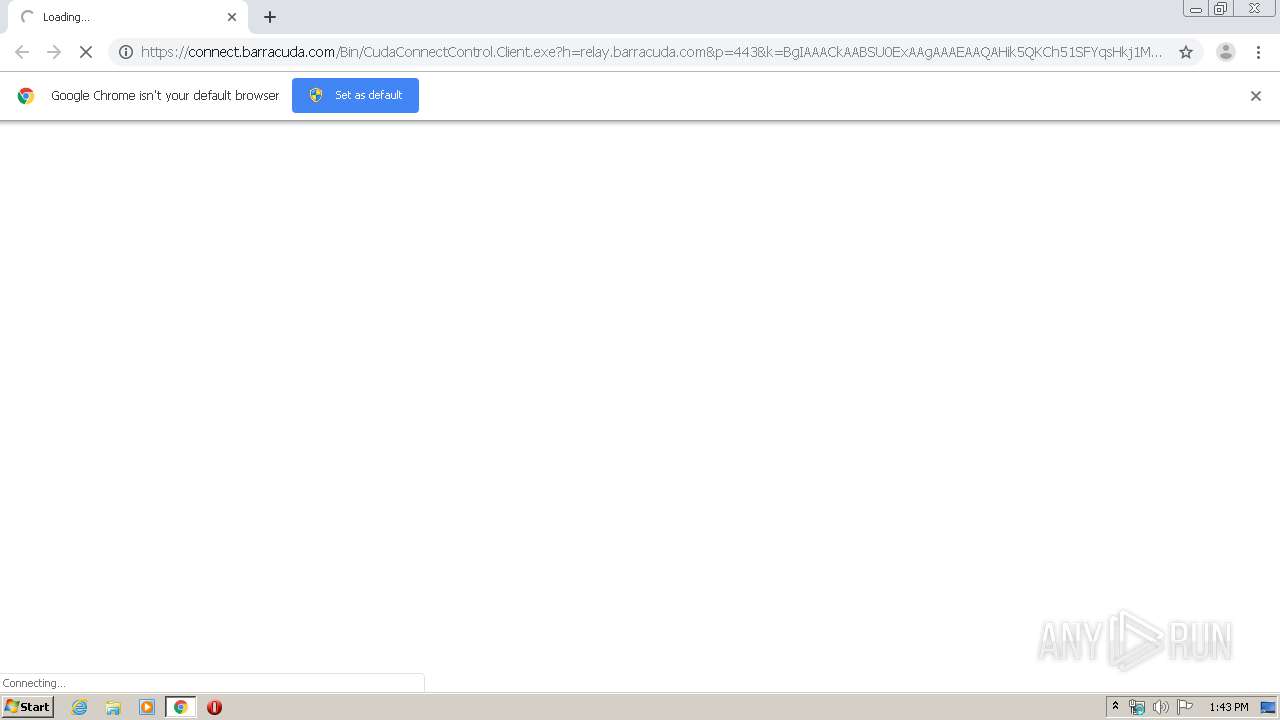
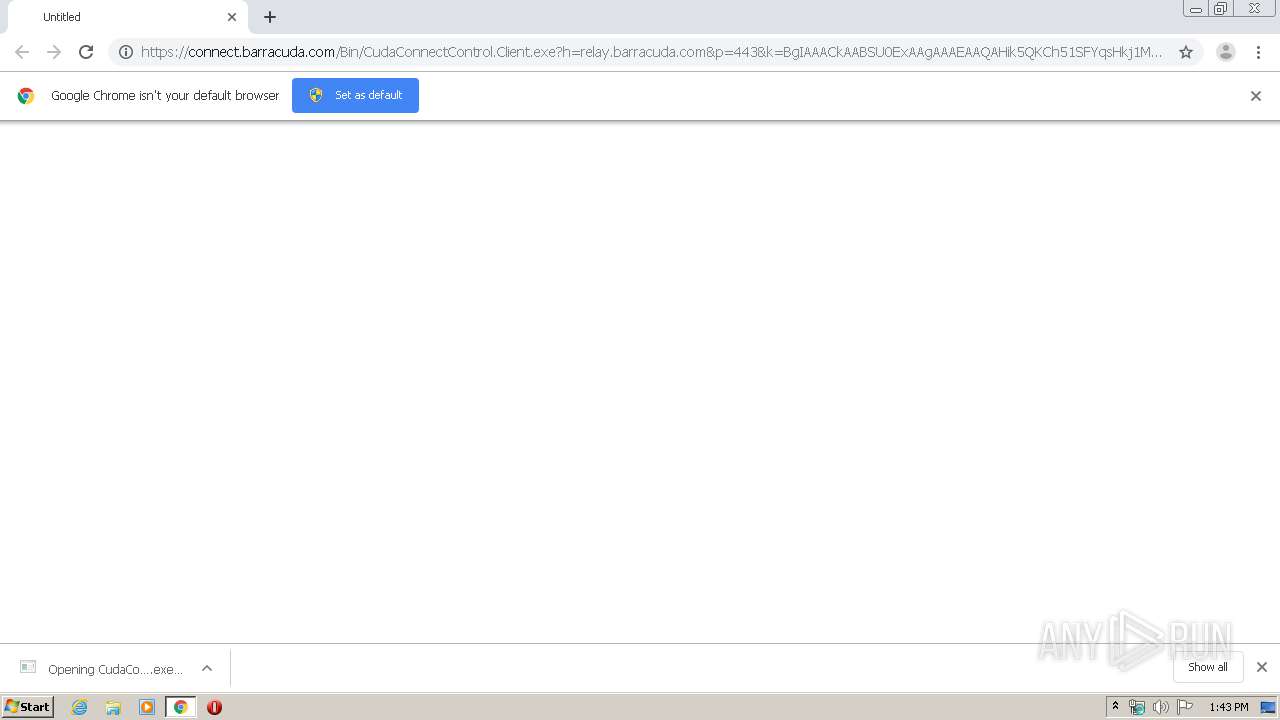
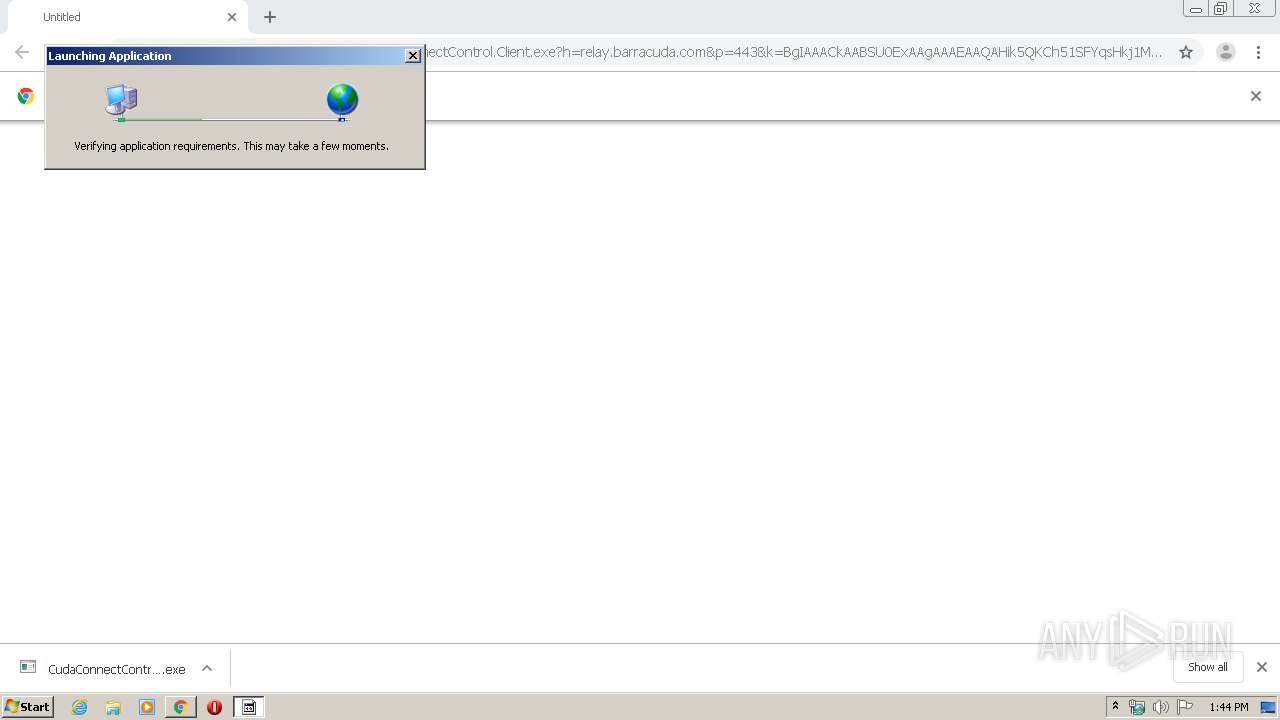
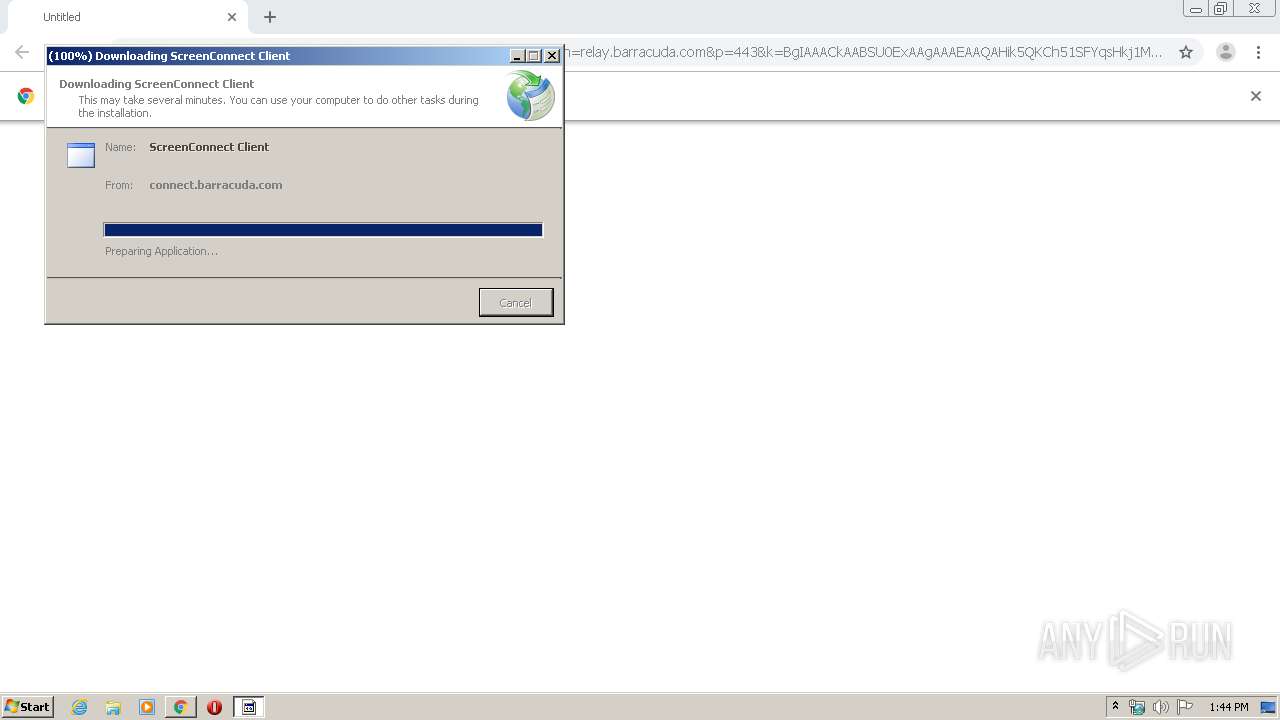
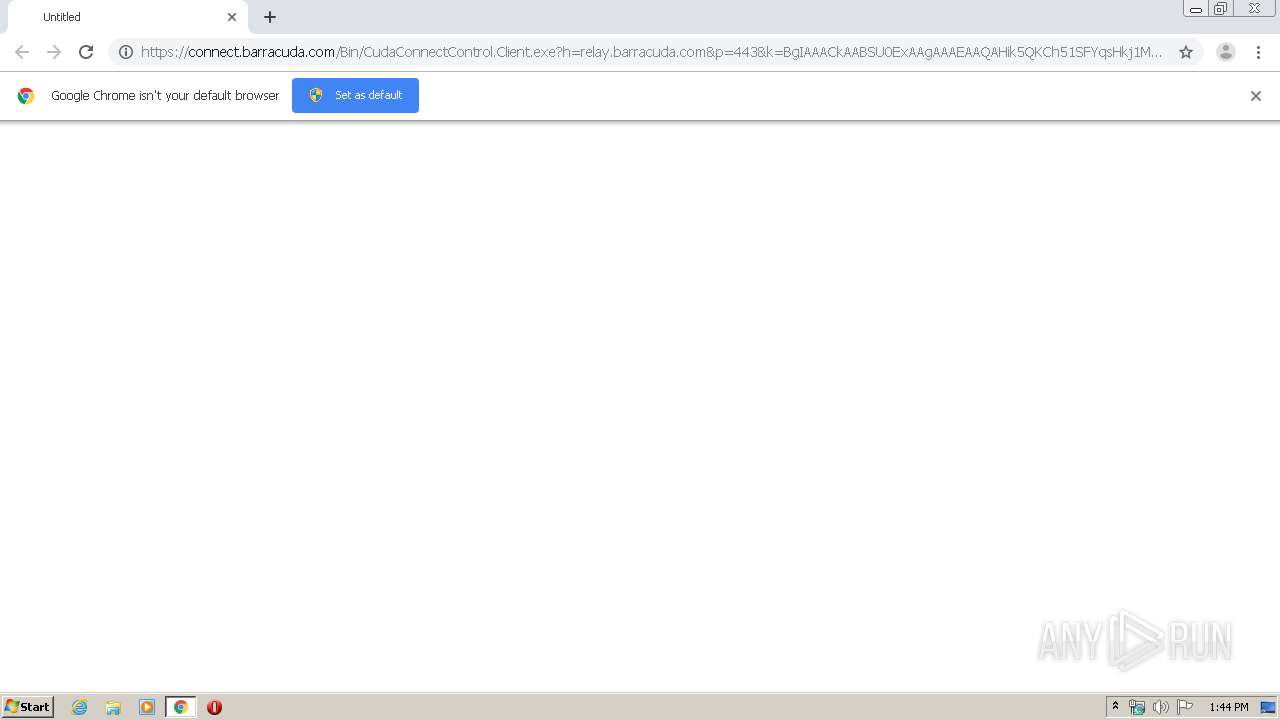
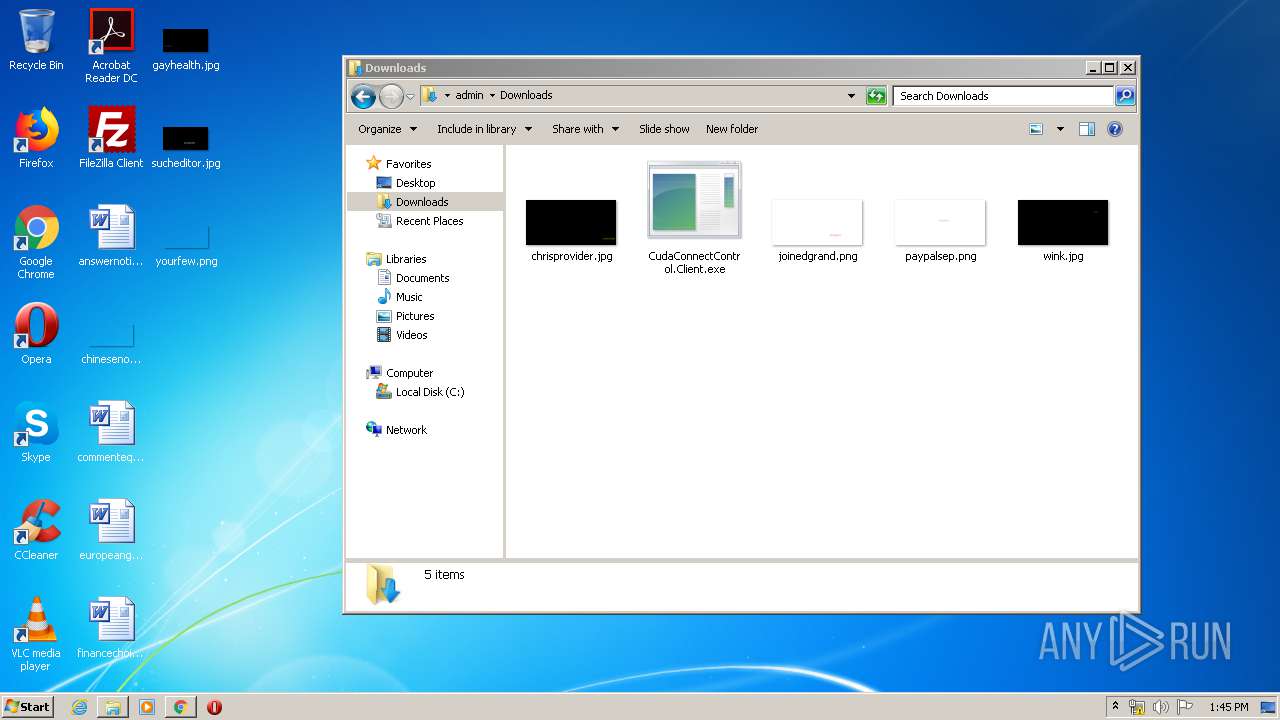
| URL: | https://connect.barracuda.com/Bin/CudaConnectControl.Client.exe?h=relay.barracuda.com&p=443&k=BgIAAACkAABSU0ExAAgAAAEAAQAHik5QKCh51SFYqsHkj1MJhVc8Gniu8piQR3LwsFHBsYPJ%2BDht5wSsvX6DNMkWLf5njjKQbkzxfvN%2BGhLfQghXAJkpaSna5NM%2B%2B56j%2F01iK7aQTVUcibPicmOZn1fNrW3AJ4236oJCVeCXM69ZNjQVeOCQoRthUQZUe9bkqDPXS0xKSt81VXiKHpIVNo305utR064UKV9WClUw1VTa2v71AmUsqgcKnGZMKZbiPnLegfmTlUNdUroSLeUkkf8cnXLGHPecLgyg3s3QwqGNg7nVhdLfwsIbg27ZuB64SceHitYorH2RB7e%2Fc1W5lxJAUwh%2FjpQf4AJFB1r8KR7lakG9&s=a4ee4c24-3cad-4aba-8a5b-8c949551c491&i=02592500&e=Support&y=Guest&r= |
| Full analysis: | https://app.any.run/tasks/d1156ea4-614f-4afb-8869-12d38f9a699e |
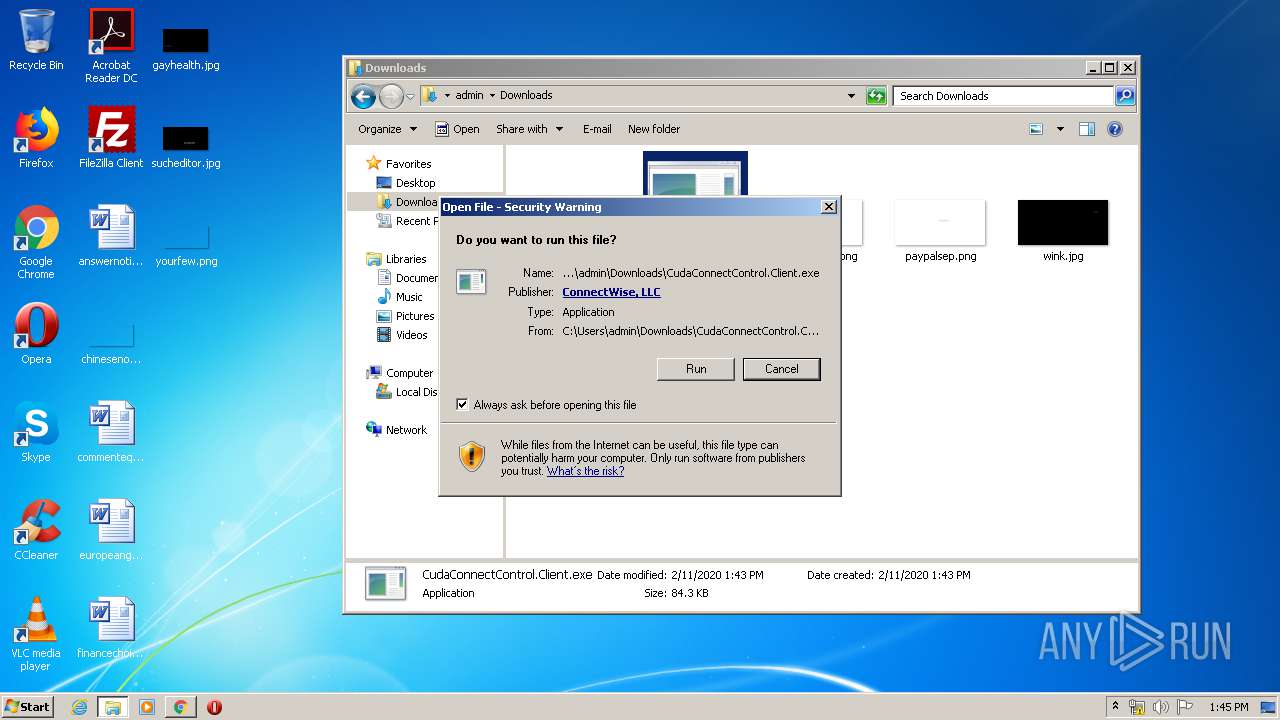
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2020, 13:43:40 |
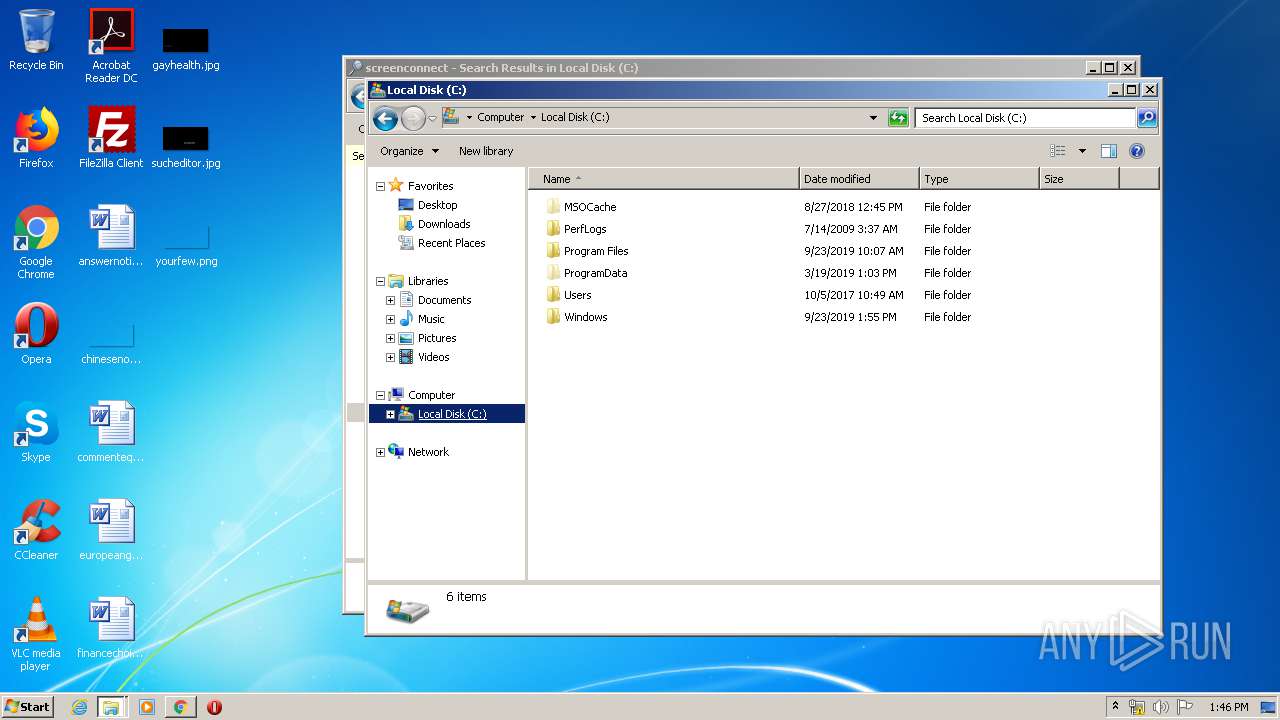
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 672B5A3D2EEA6E69053C90E96B2683E6 |
| SHA1: | D668EA12683AC996887E4DB76D7E87CB23911853 |
| SHA256: | EF6BBD710BC00FEE9141B9CB1AEBBF309A231DFF830C304BFDD2ED5B30DEC549 |
| SSDEEP: | 12:2Z1LjrCE6v+xRQwuFgOVIWQv2uIs+39OaG1K8Jec4gX49IQ0uEIfRrZM:2TDa+x2jUuuvI9OZI86R5C |
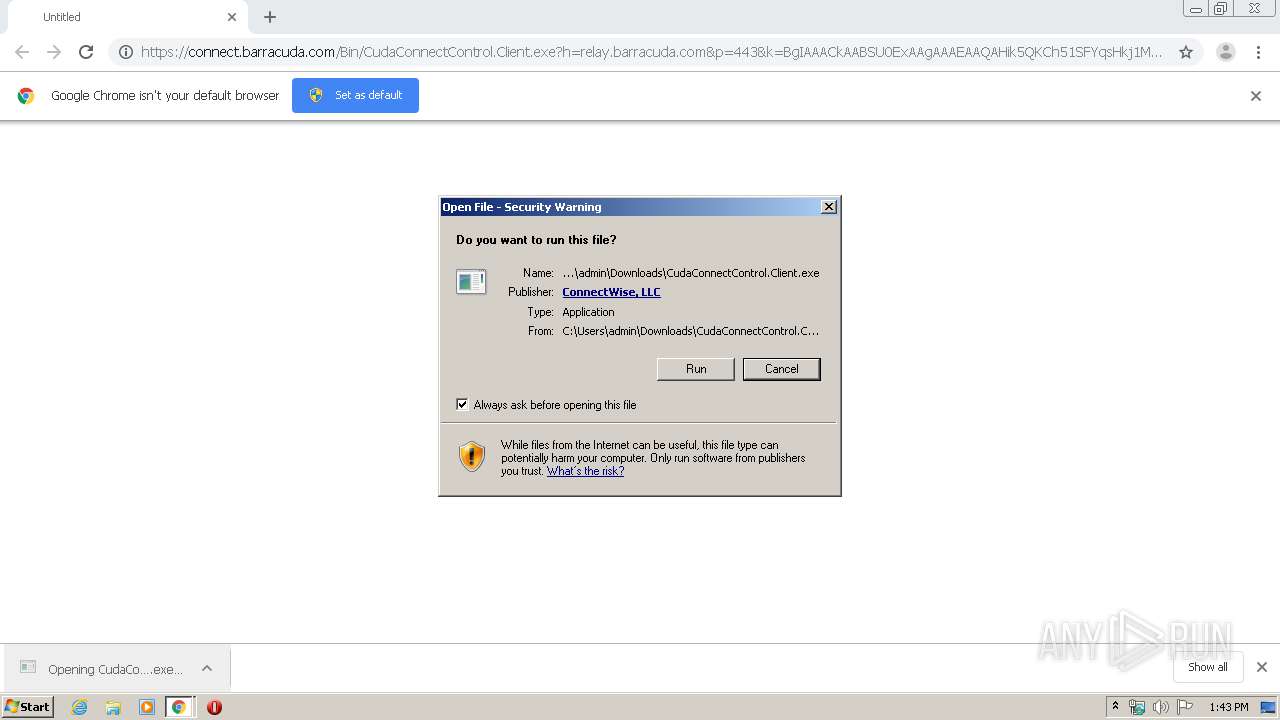
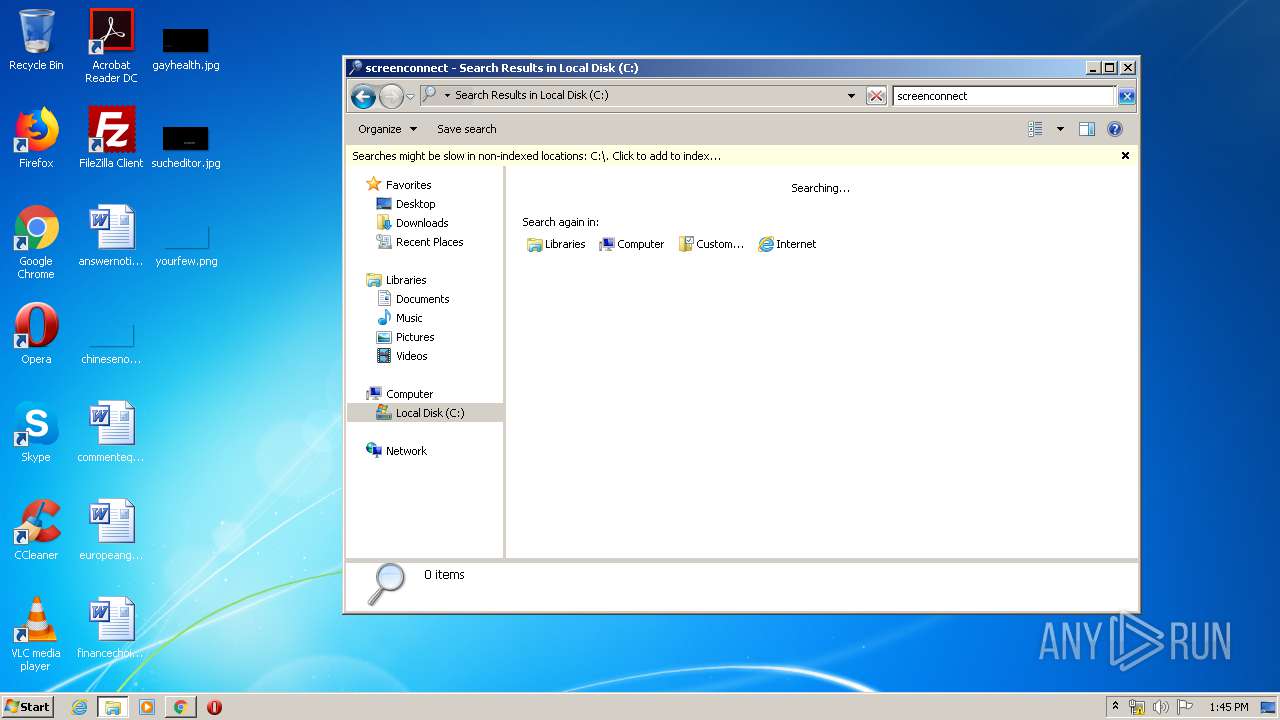
MALICIOUS
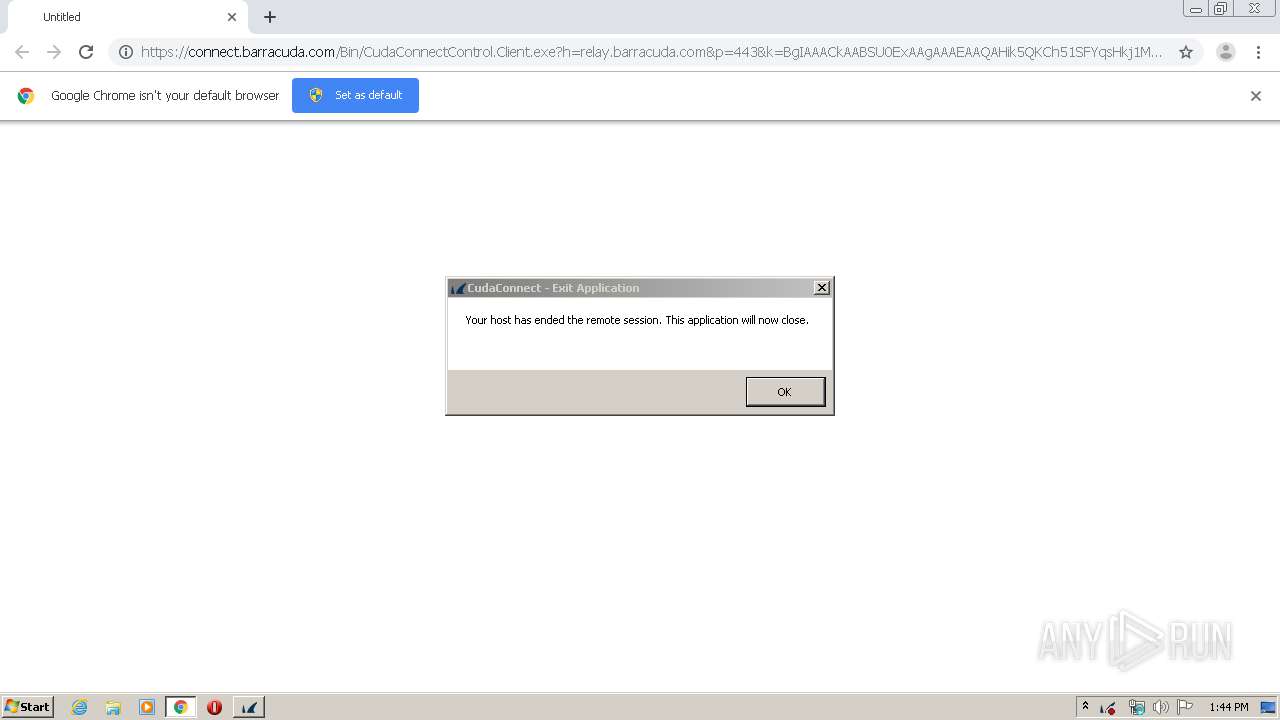
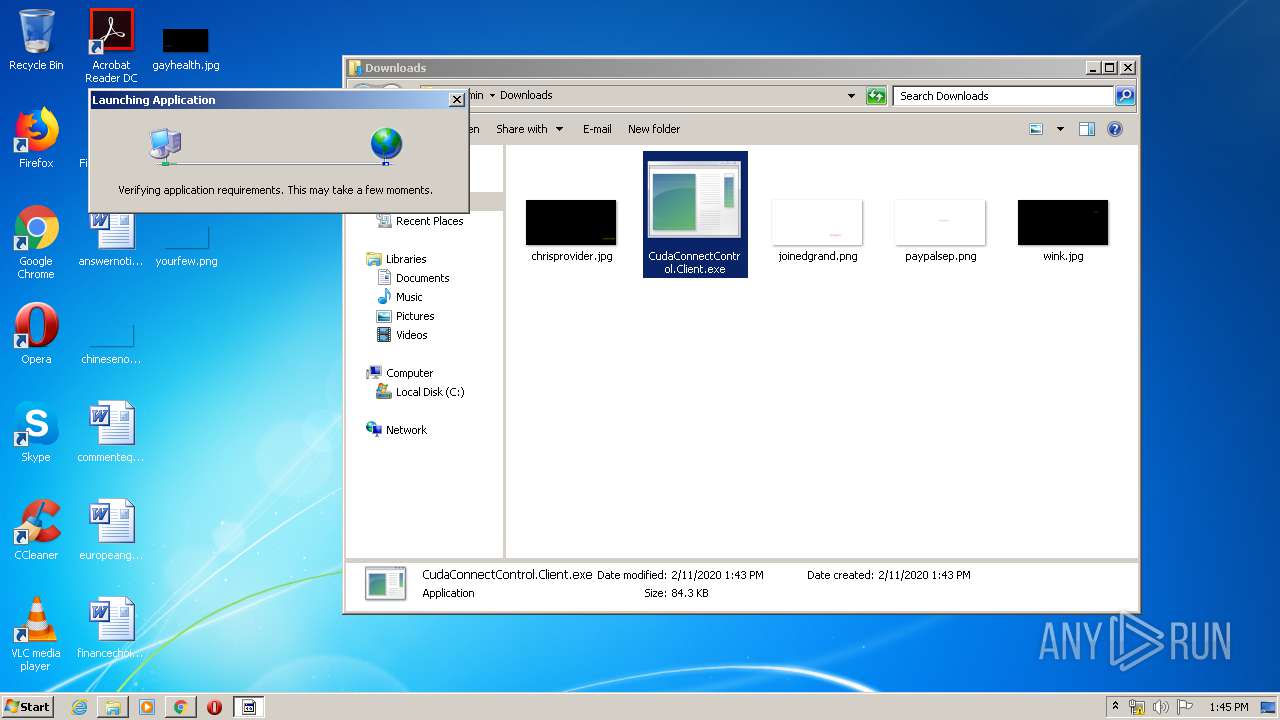
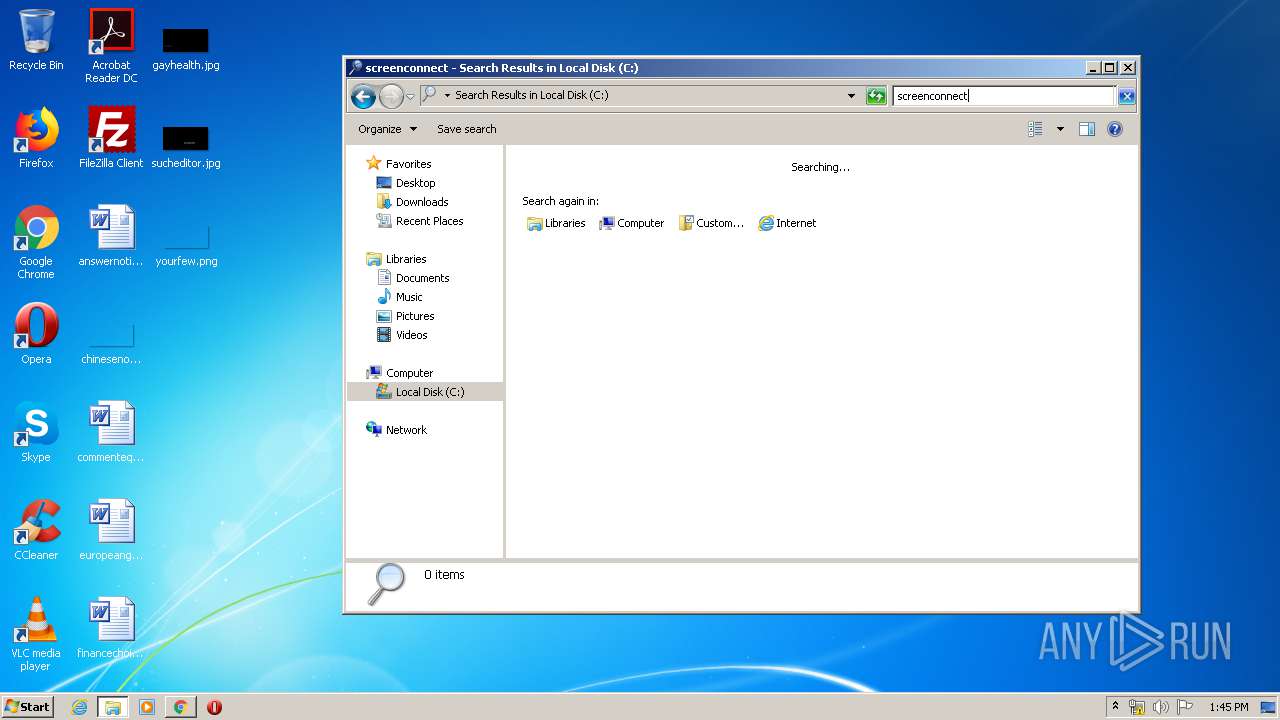
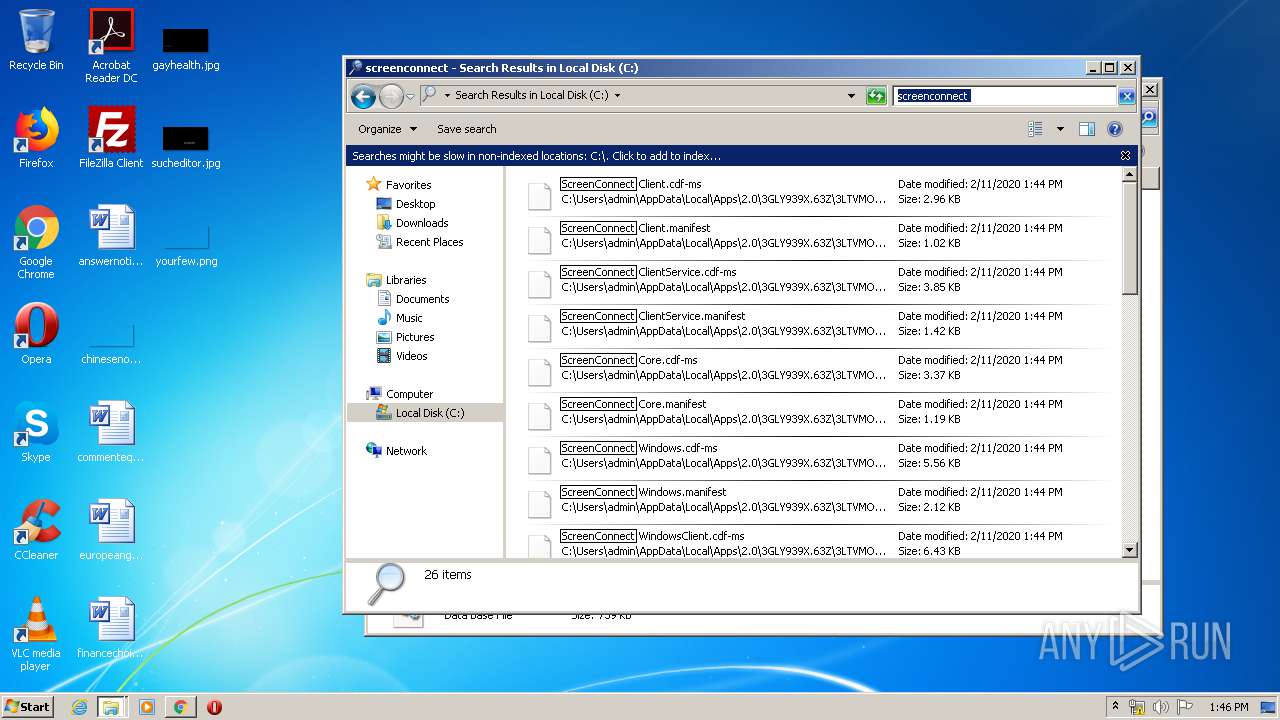
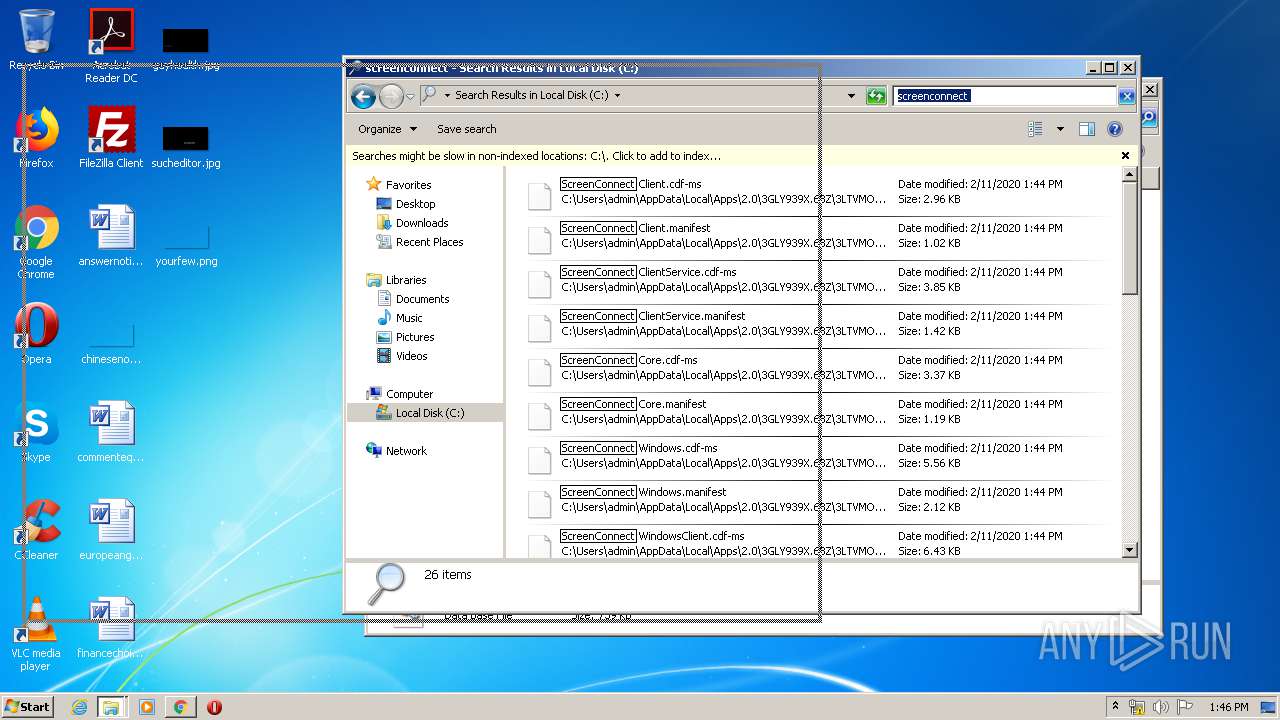
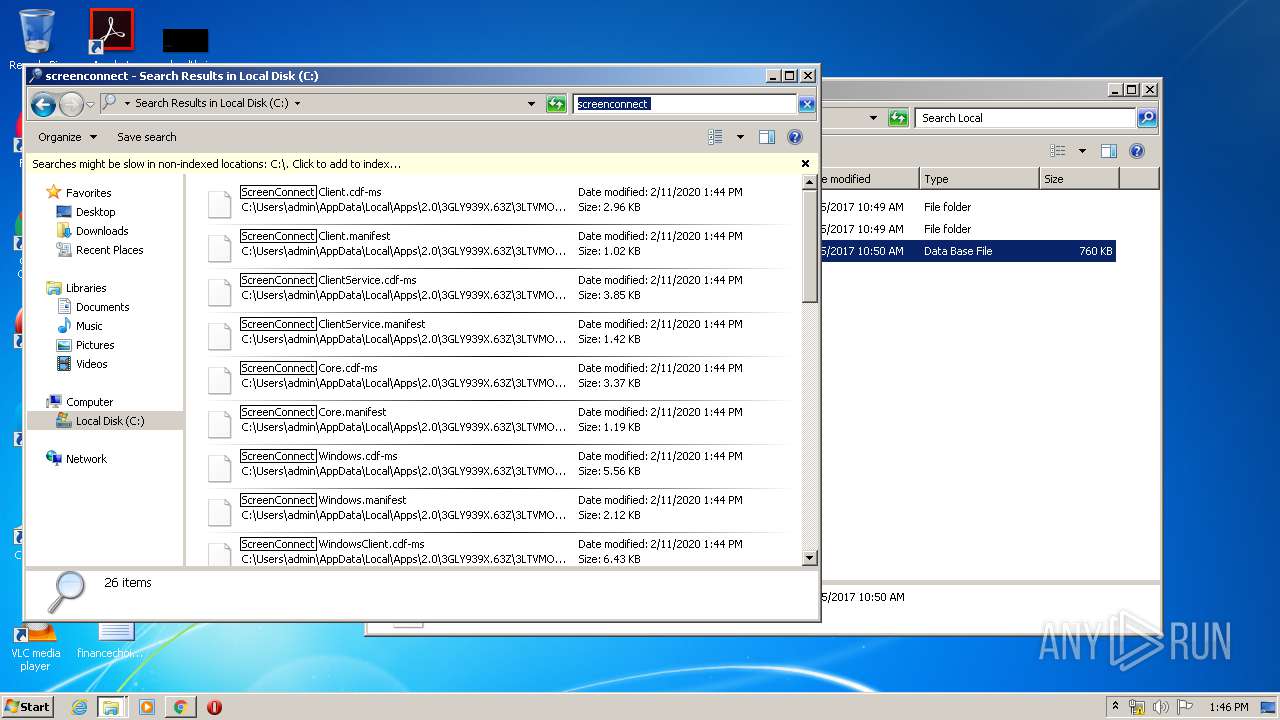
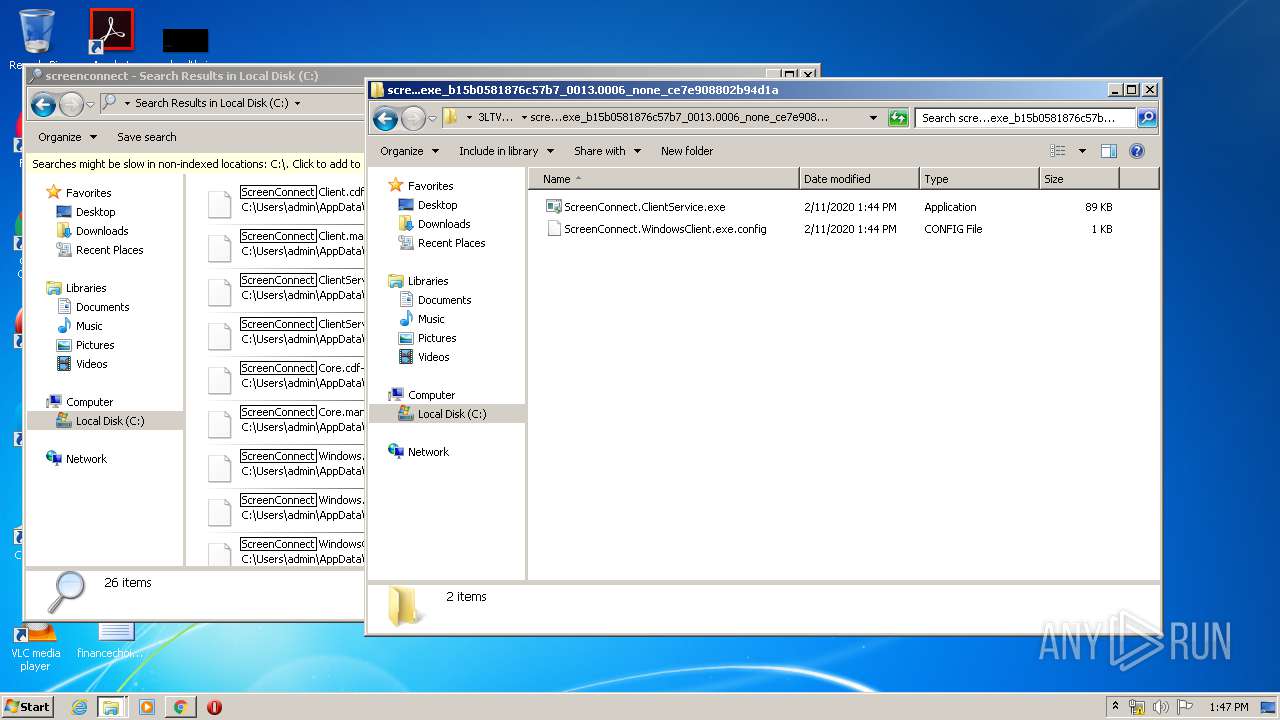
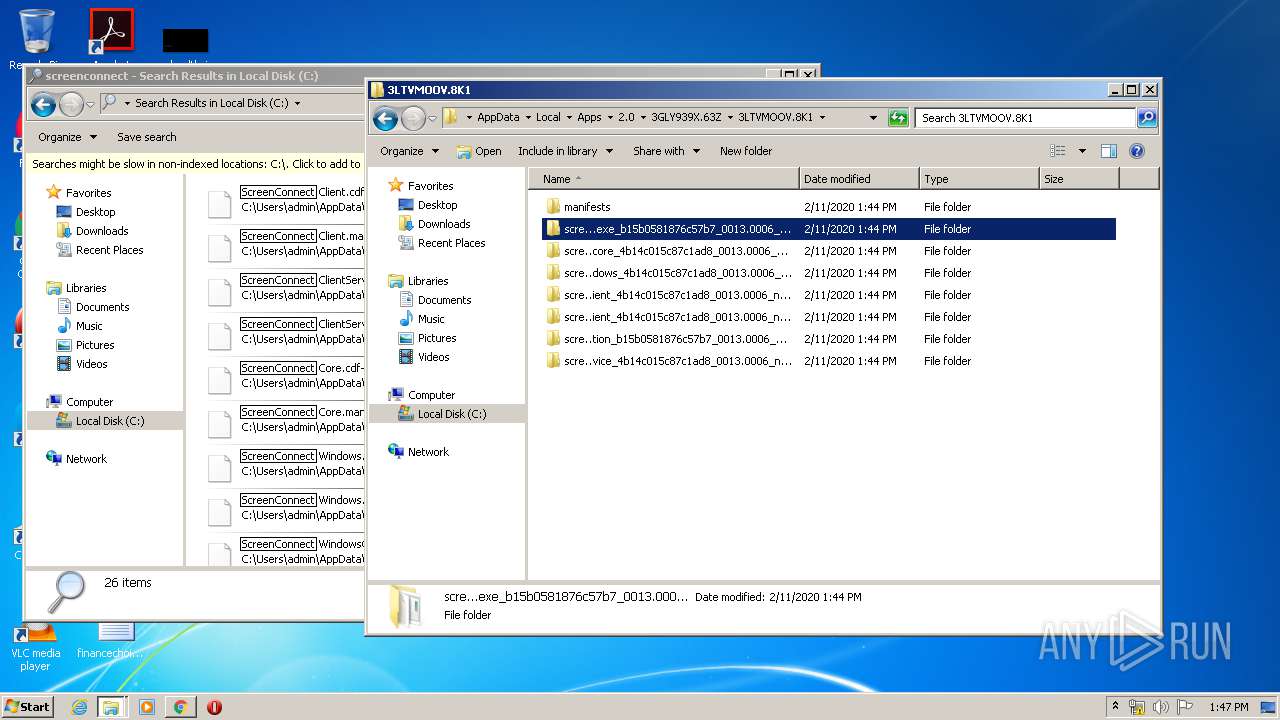
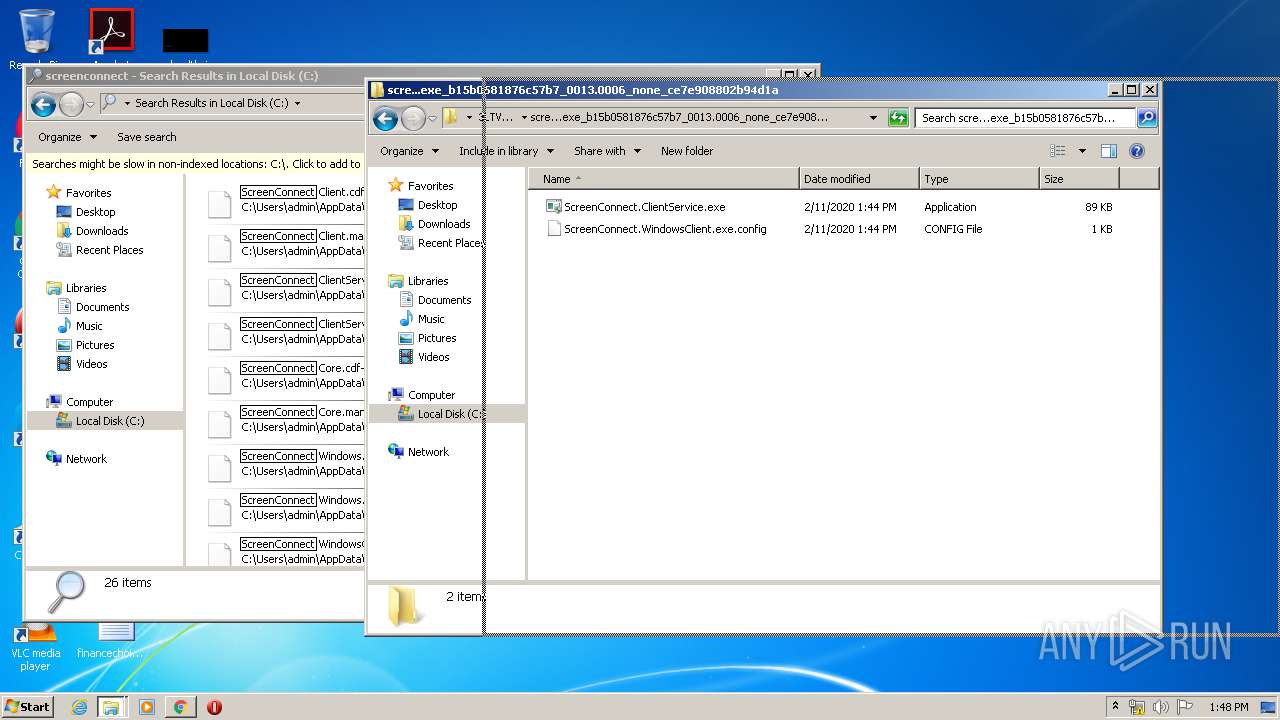
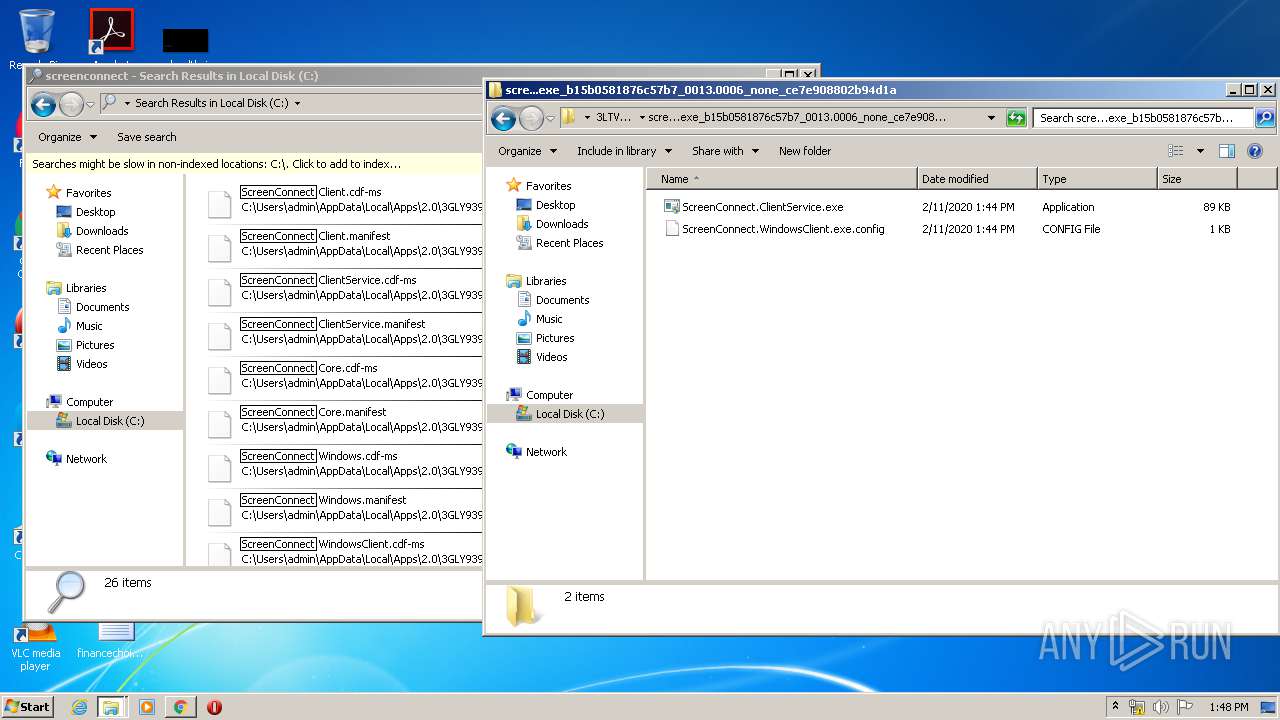
Application was dropped or rewritten from another process
- CudaConnectControl.Client.exe (PID: 2864)
- ScreenConnect.WindowsClient.exe (PID: 1604)
- ScreenConnect.ClientService.exe (PID: 2536)
- ScreenConnect.ClientService.exe (PID: 3600)
- ScreenConnect.WindowsClient.exe (PID: 3192)
- ScreenConnect.WindowsClient.exe (PID: 3472)
- CudaConnectControl.Client.exe (PID: 3172)
- ScreenConnect.ClientService.exe (PID: 1708)
- ScreenConnect.WindowsClient.exe (PID: 2316)
- ScreenConnect.ClientService.exe (PID: 1536)
Changes settings of System certificates
- dfsvc.exe (PID: 2908)
- CudaConnectControl.Client.exe (PID: 2864)
- CudaConnectControl.Client.exe (PID: 3172)
Loads dropped or rewritten executable
- ScreenConnect.ClientService.exe (PID: 2536)
- dfsvc.exe (PID: 2908)
- ScreenConnect.ClientService.exe (PID: 3600)
- ScreenConnect.WindowsClient.exe (PID: 3192)
- ScreenConnect.WindowsClient.exe (PID: 3472)
- ScreenConnect.ClientService.exe (PID: 1708)
- ScreenConnect.WindowsClient.exe (PID: 2316)
- ScreenConnect.ClientService.exe (PID: 1536)
- explorer.exe (PID: 372)
- ScreenConnect.WindowsClient.exe (PID: 1604)
Deletes the SafeBoot registry key
- ScreenConnect.ClientService.exe (PID: 3600)
SUSPICIOUS
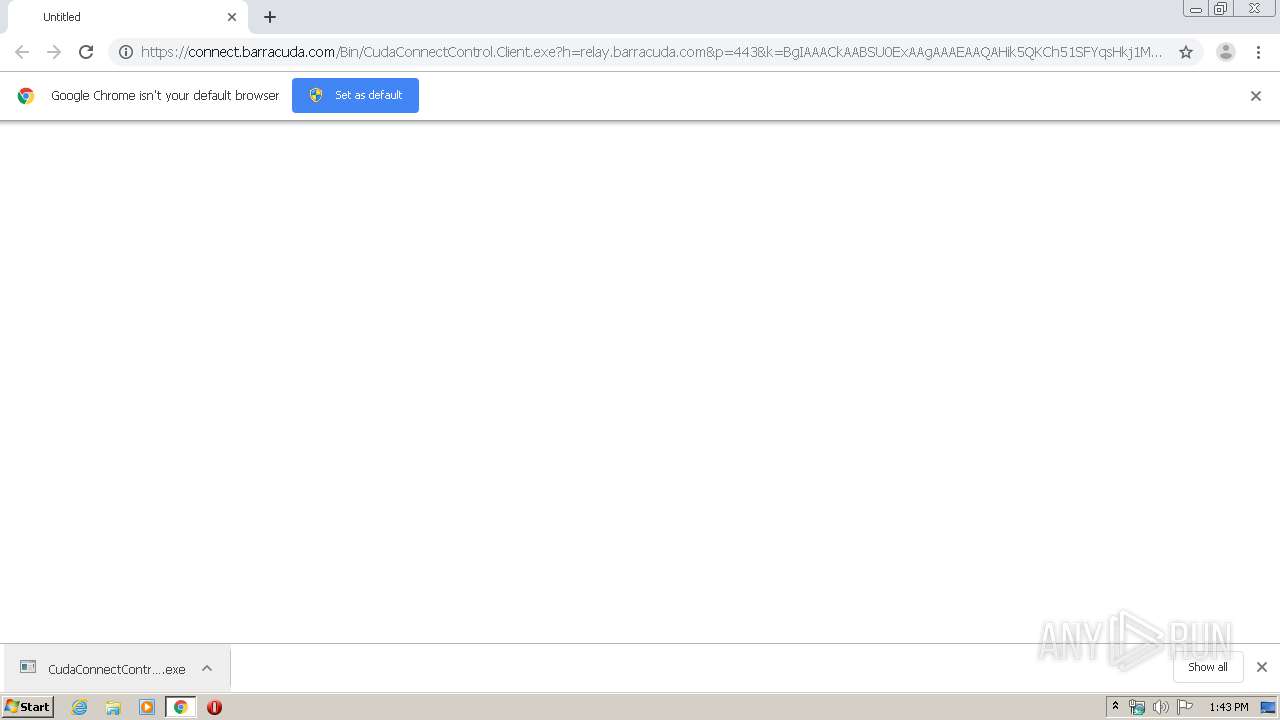
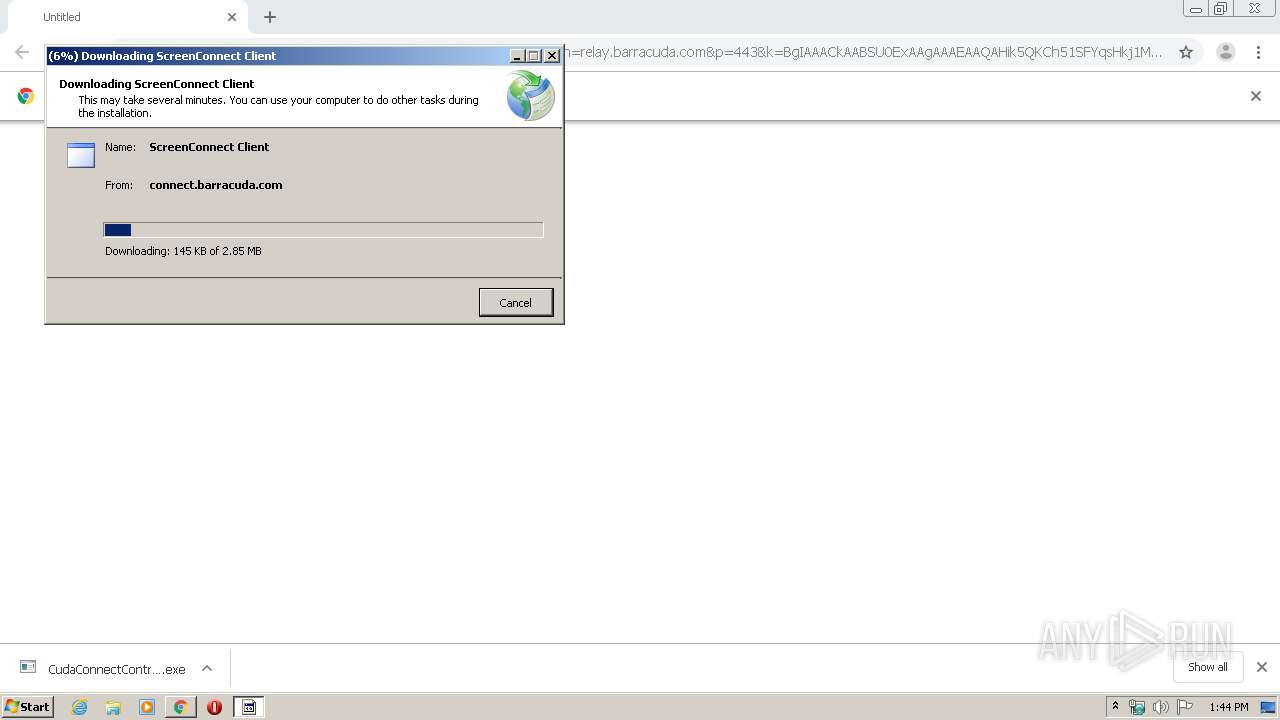
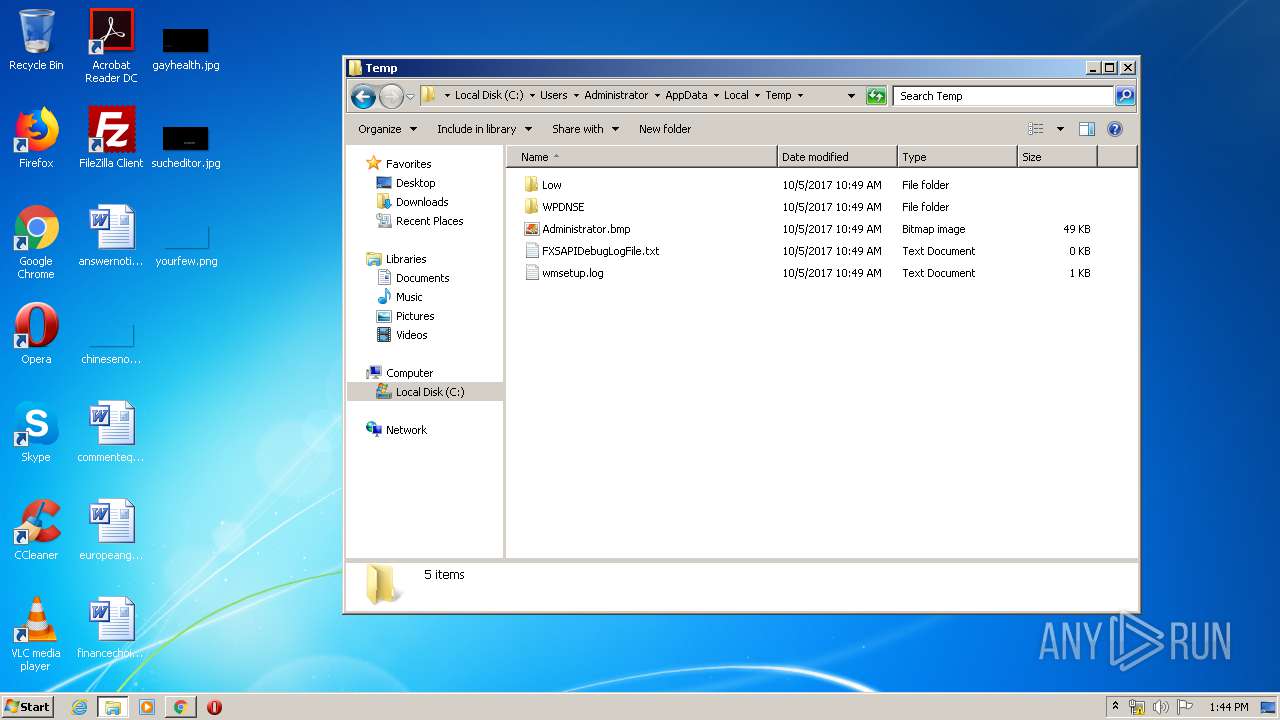
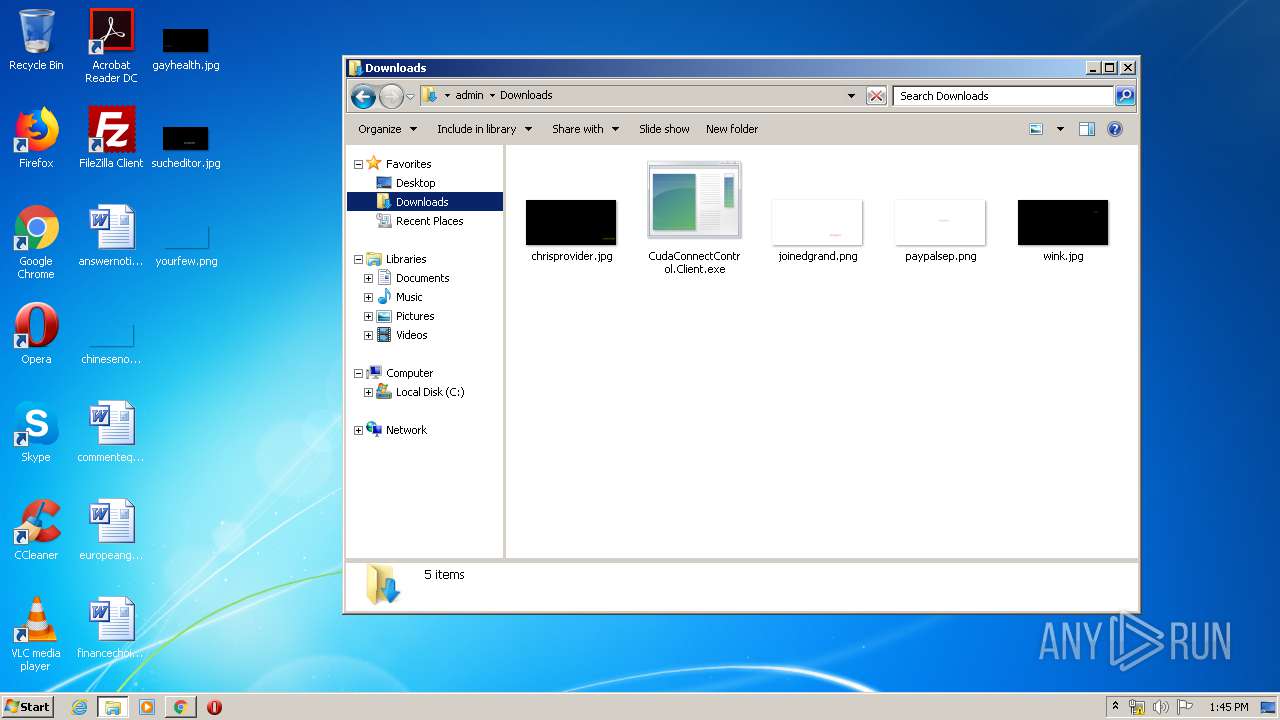
Executable content was dropped or overwritten
- chrome.exe (PID: 3144)
- dfsvc.exe (PID: 2908)
Reads Environment values
- dfsvc.exe (PID: 2908)
Reads Internet Cache Settings
- dfsvc.exe (PID: 2908)
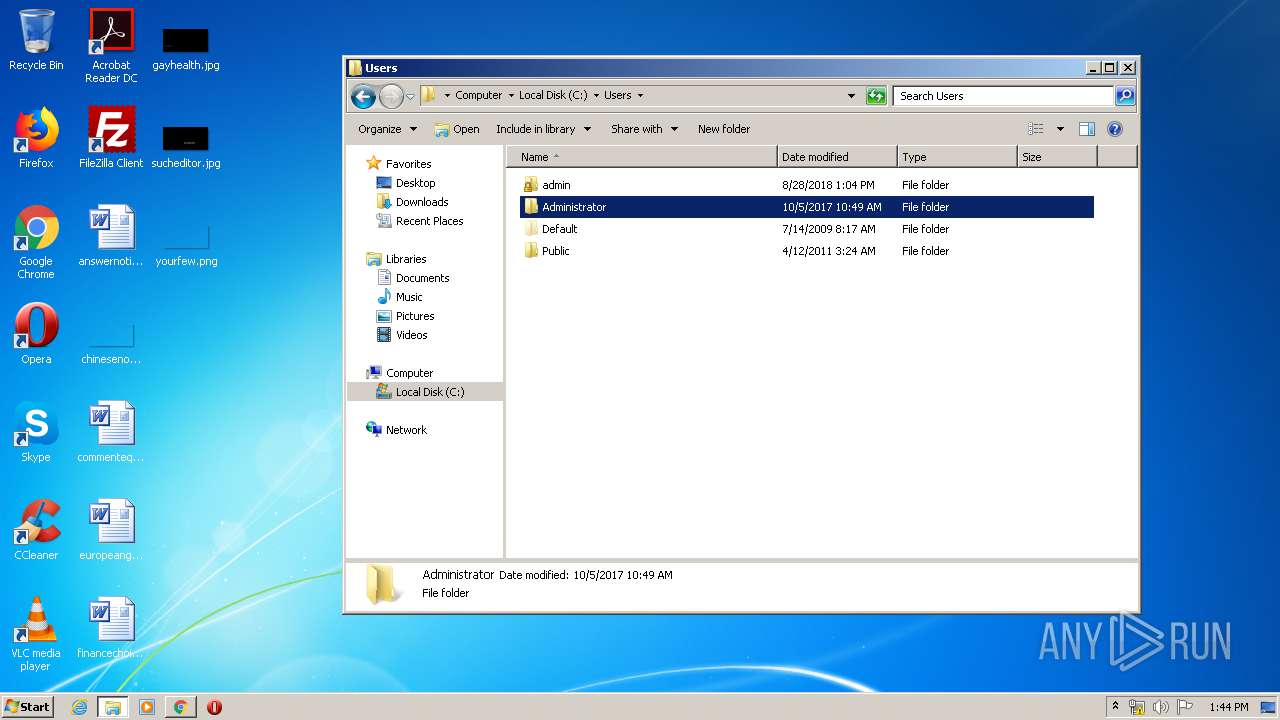
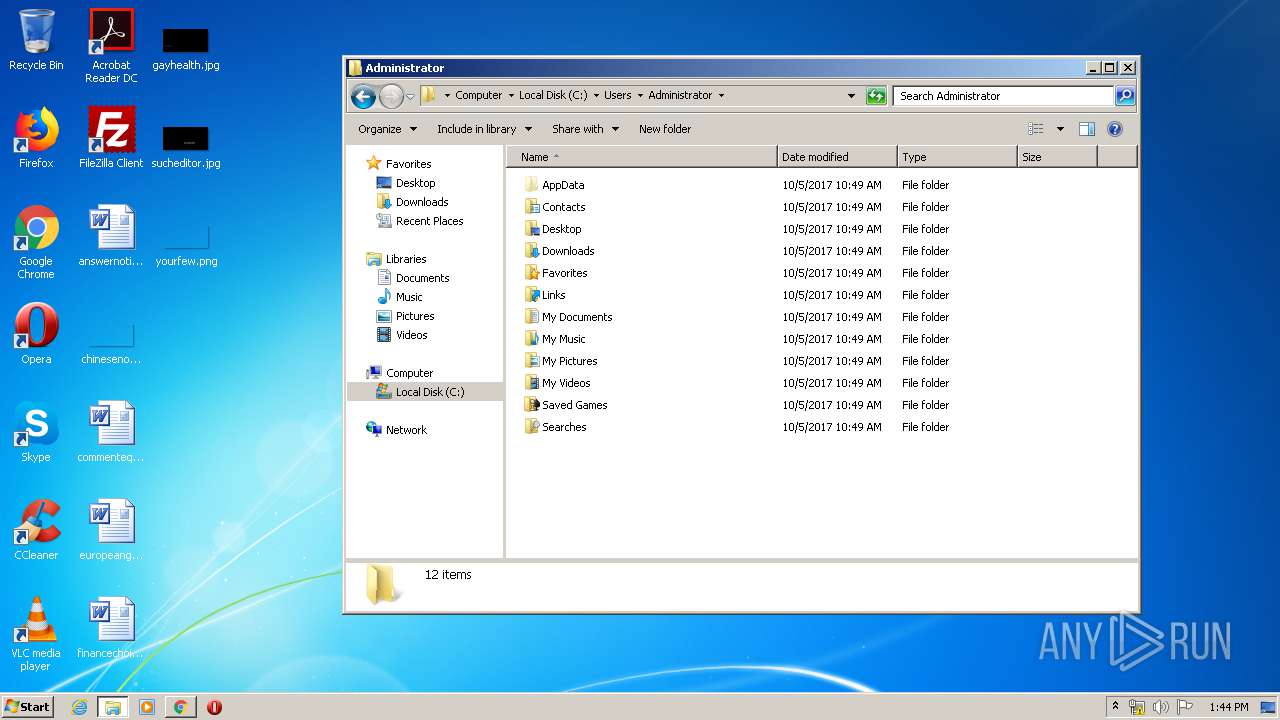
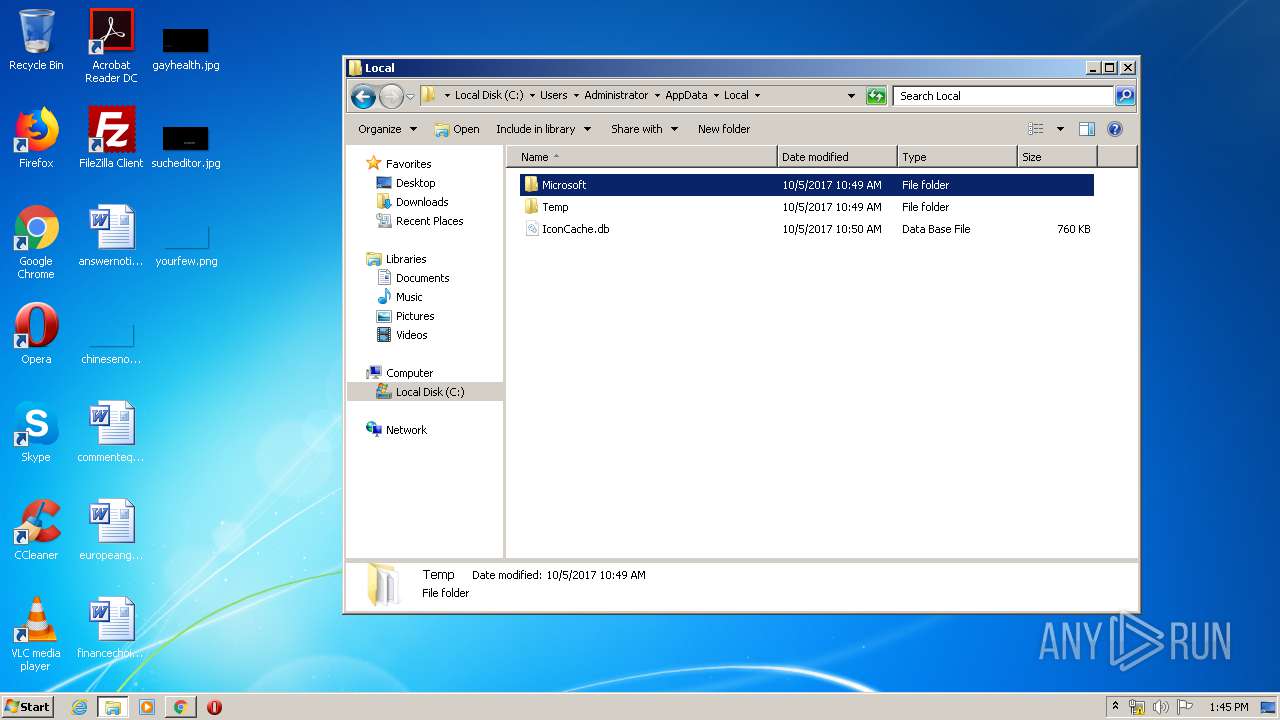
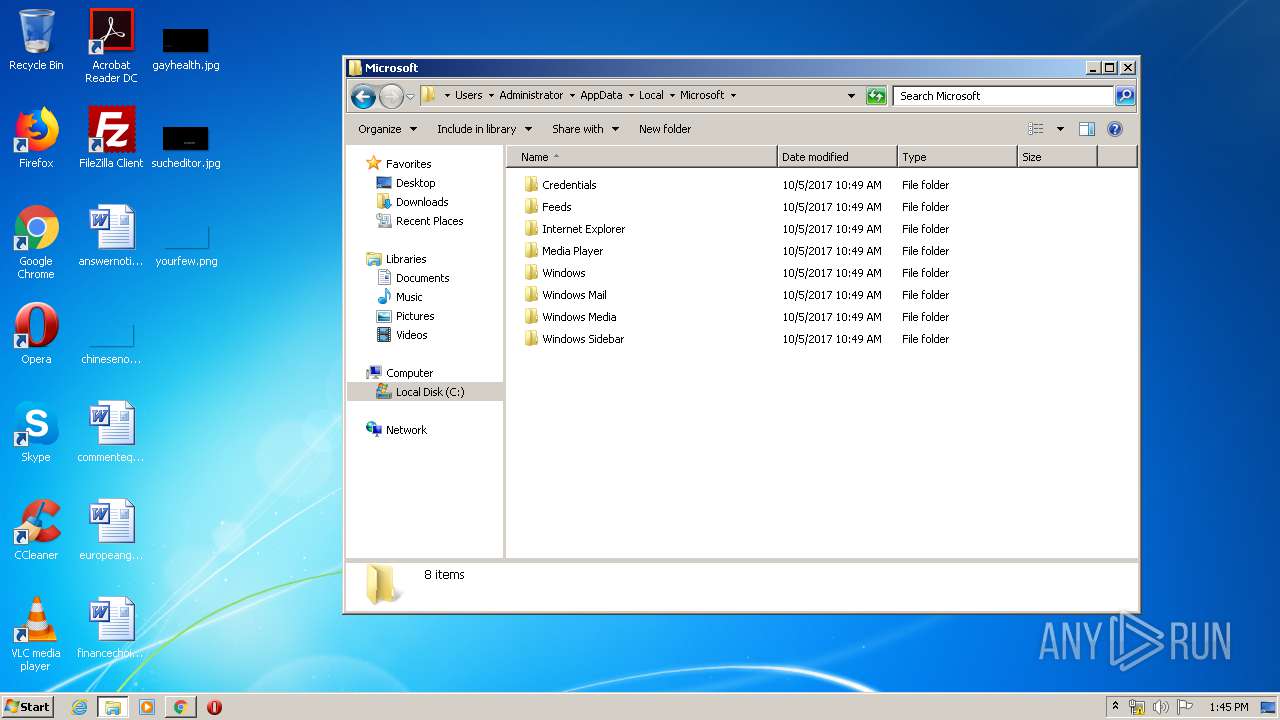
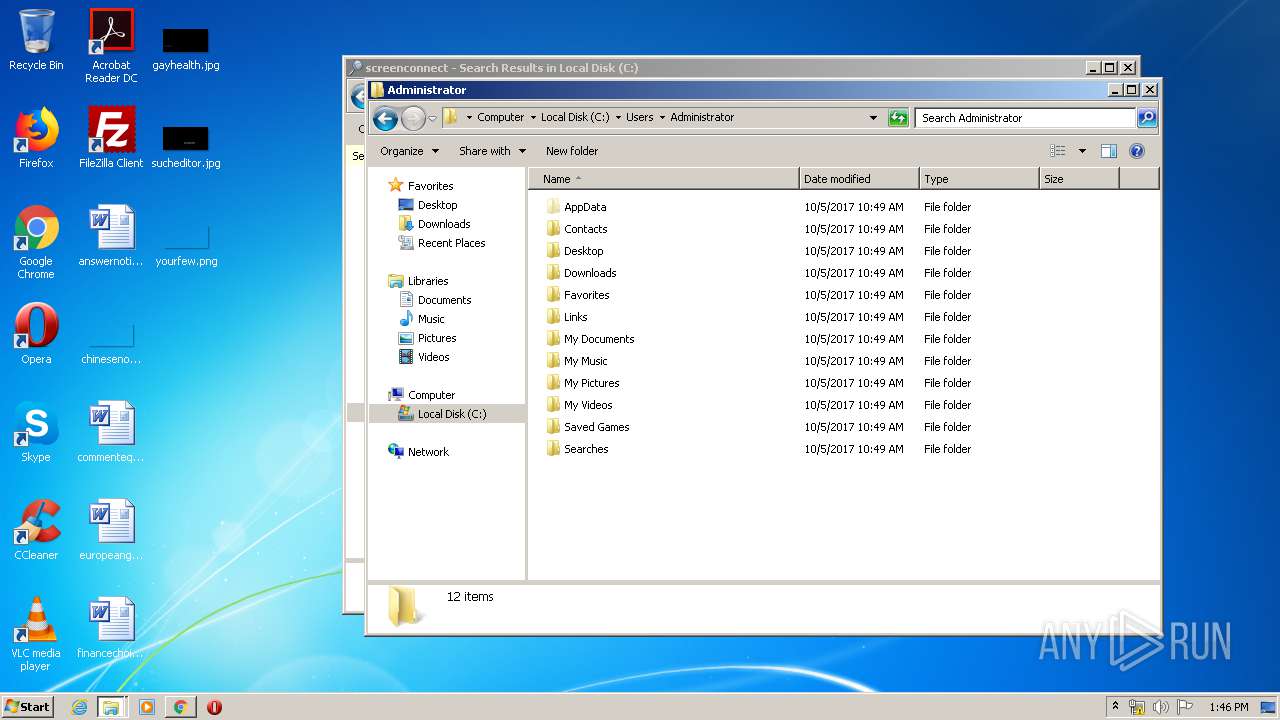
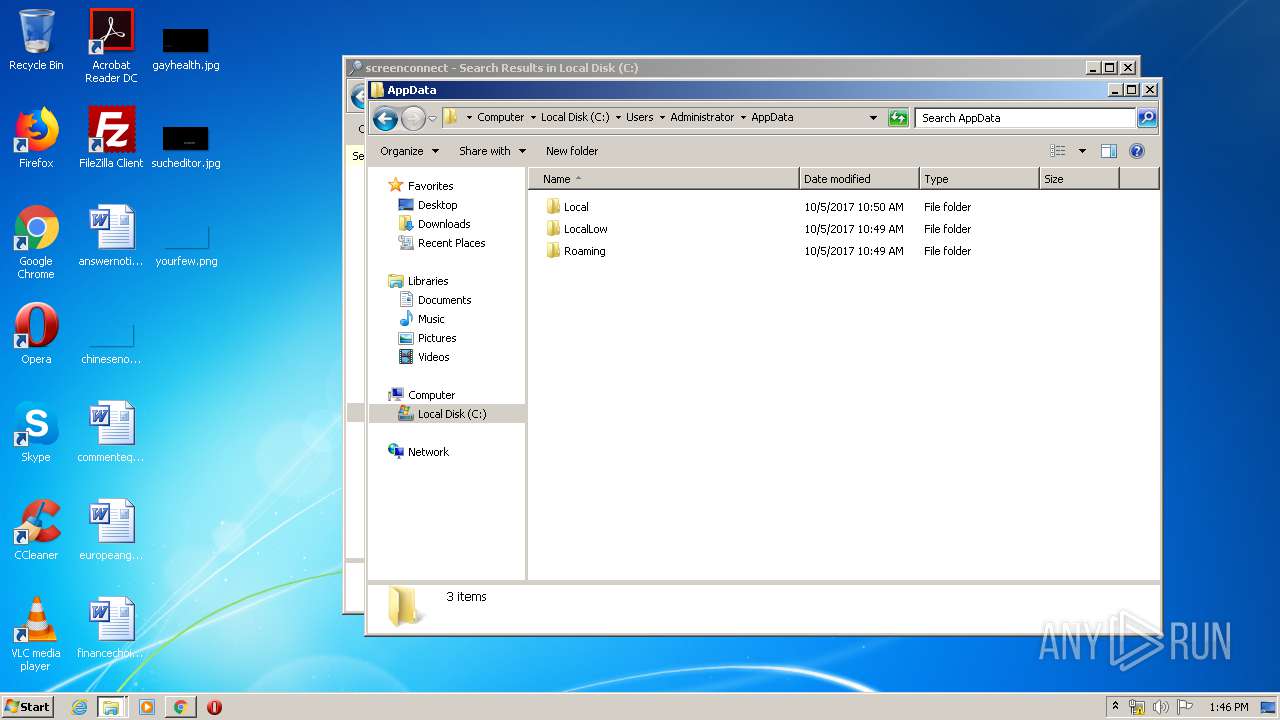
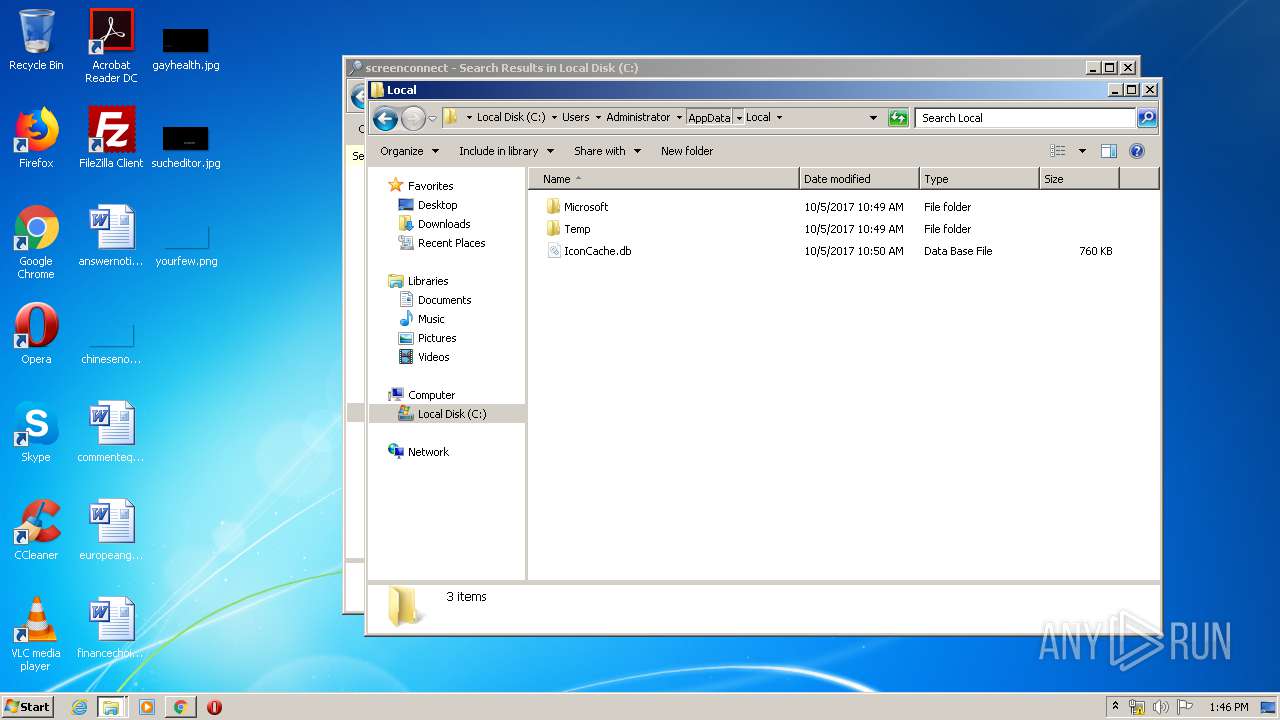
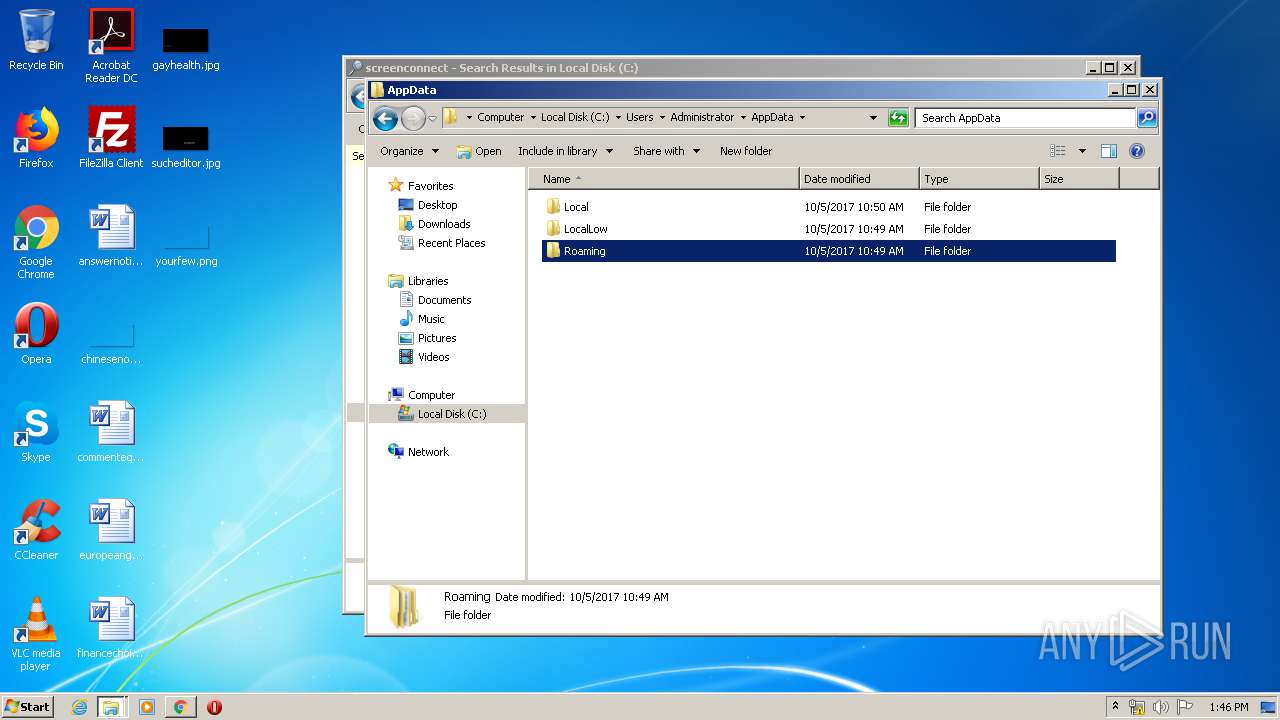
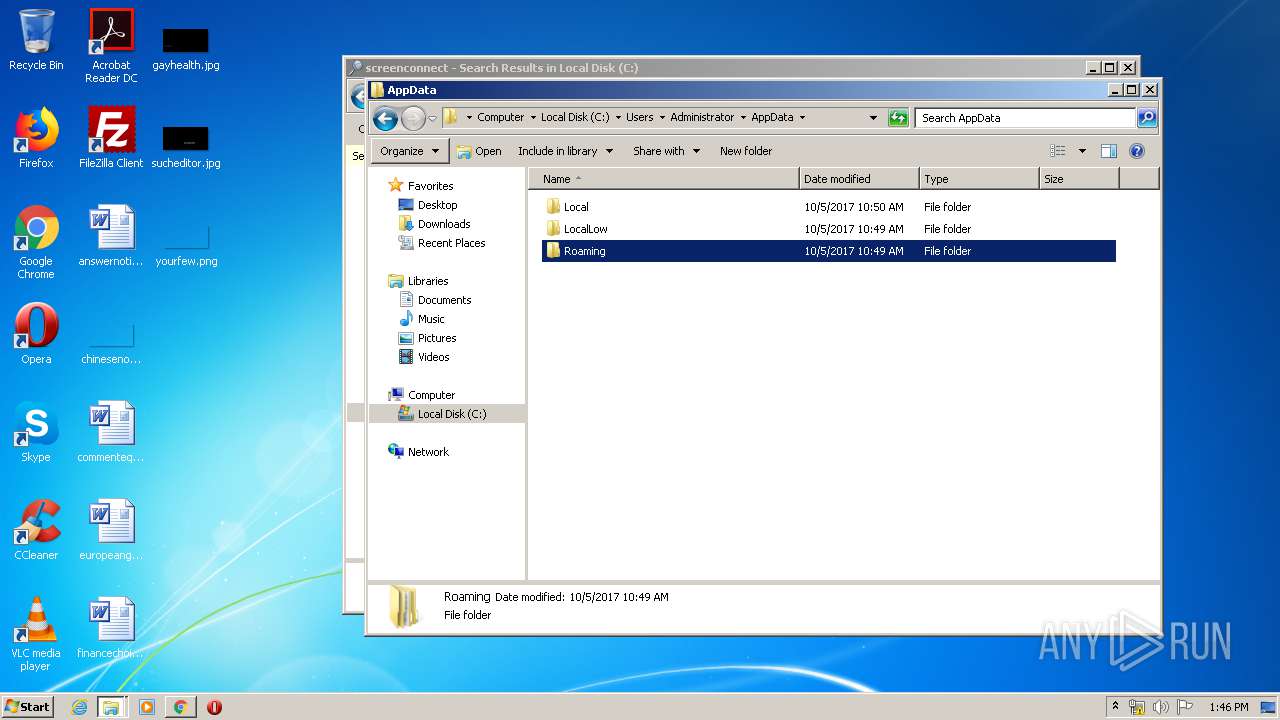
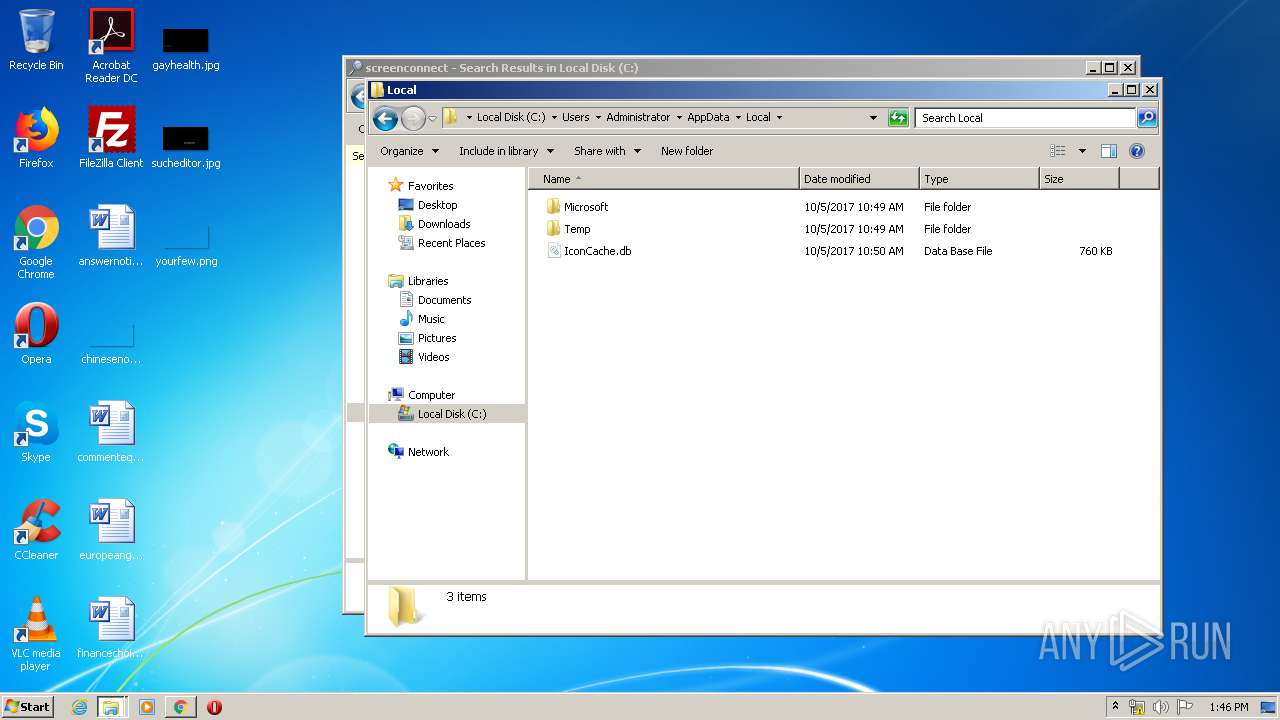
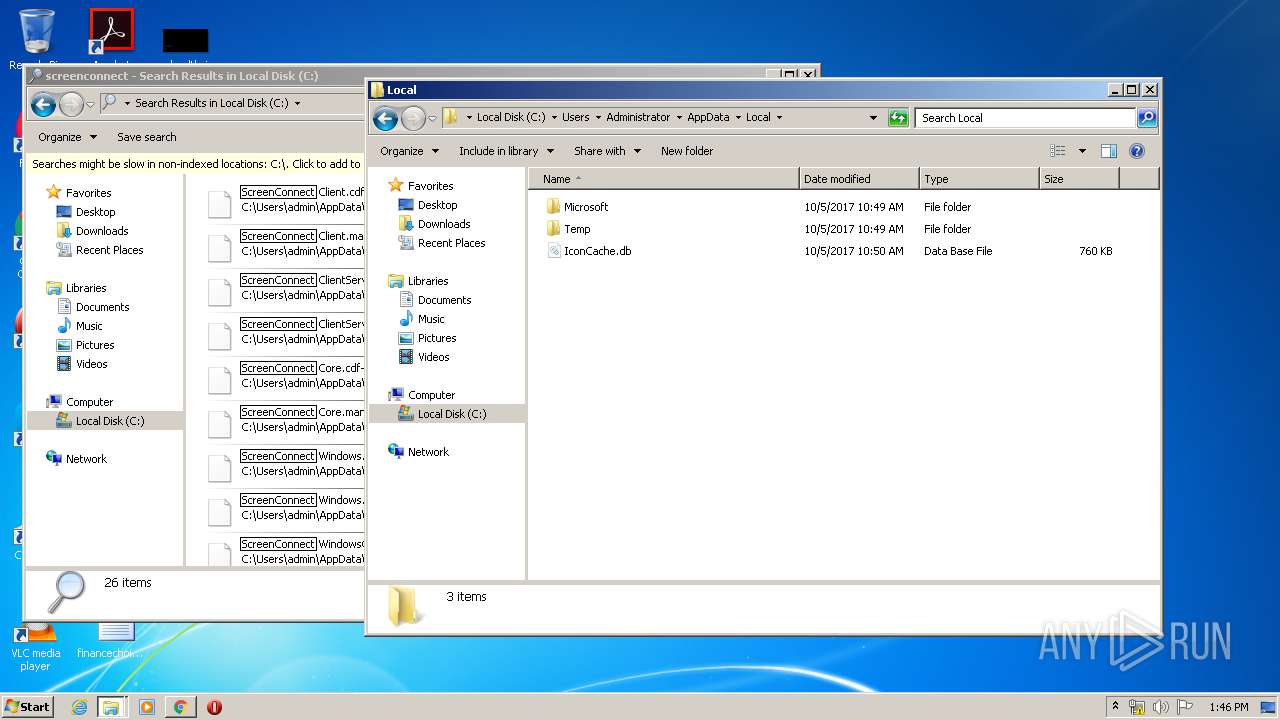
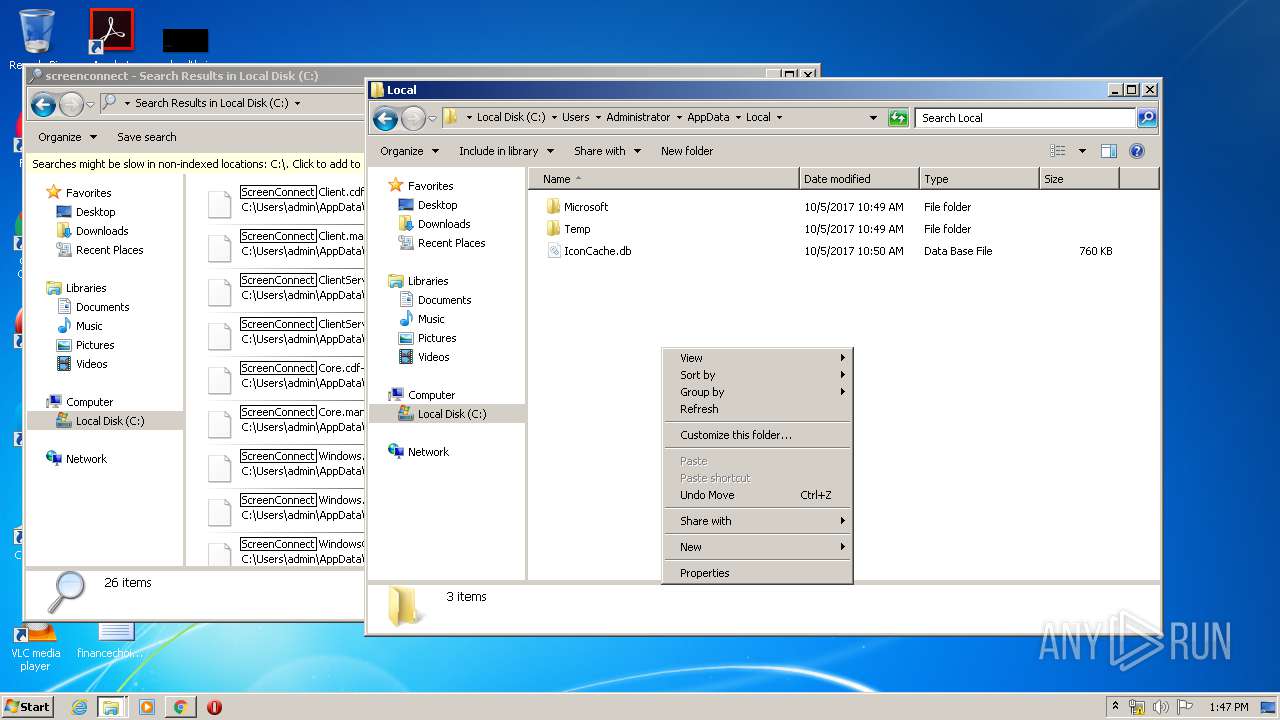
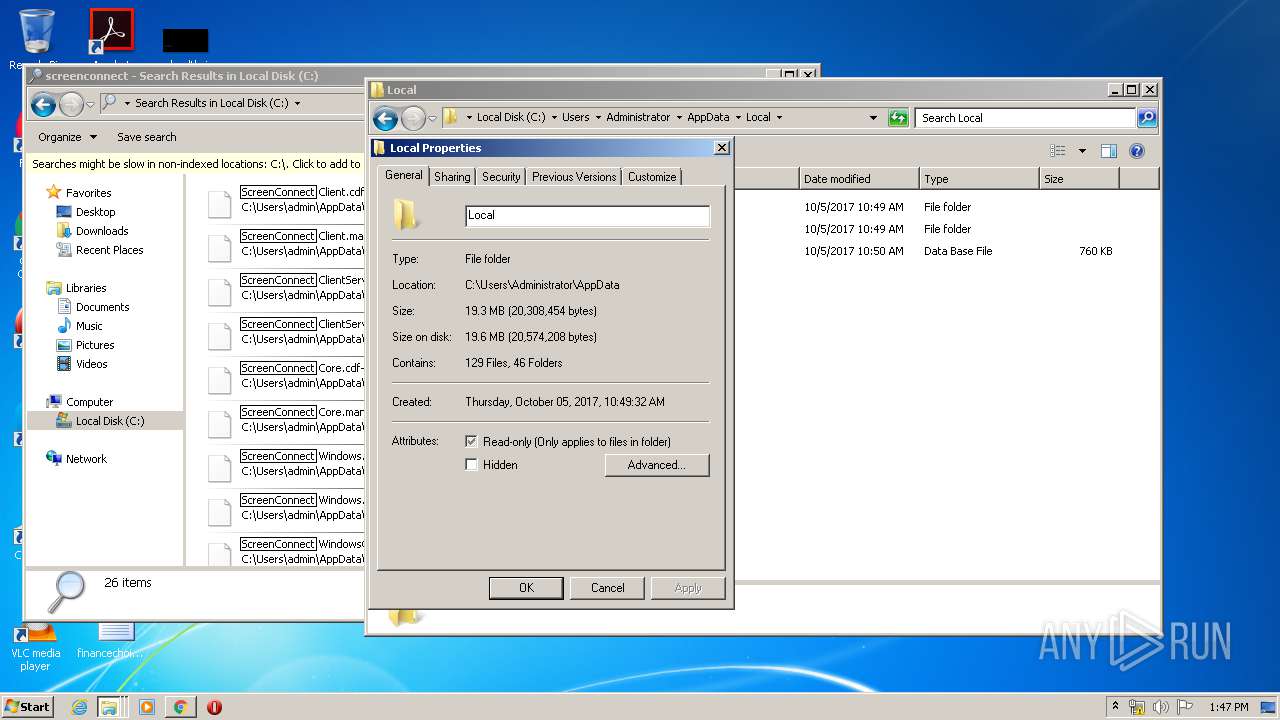
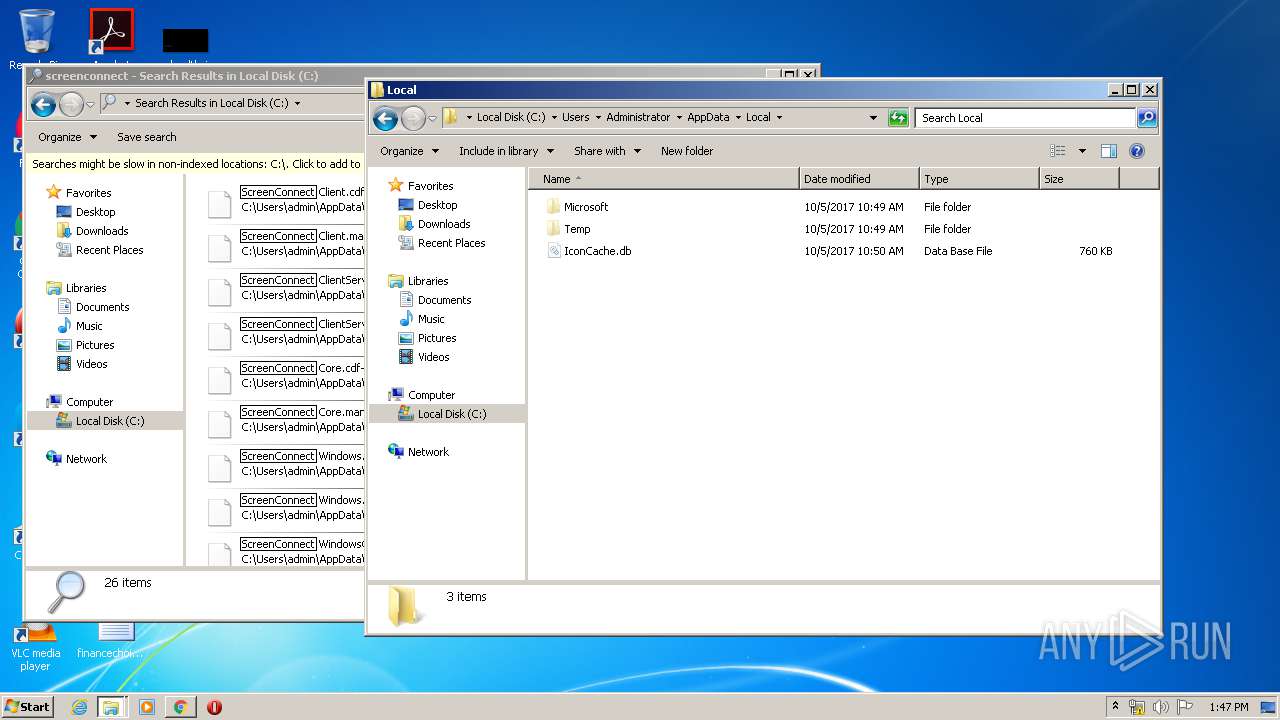
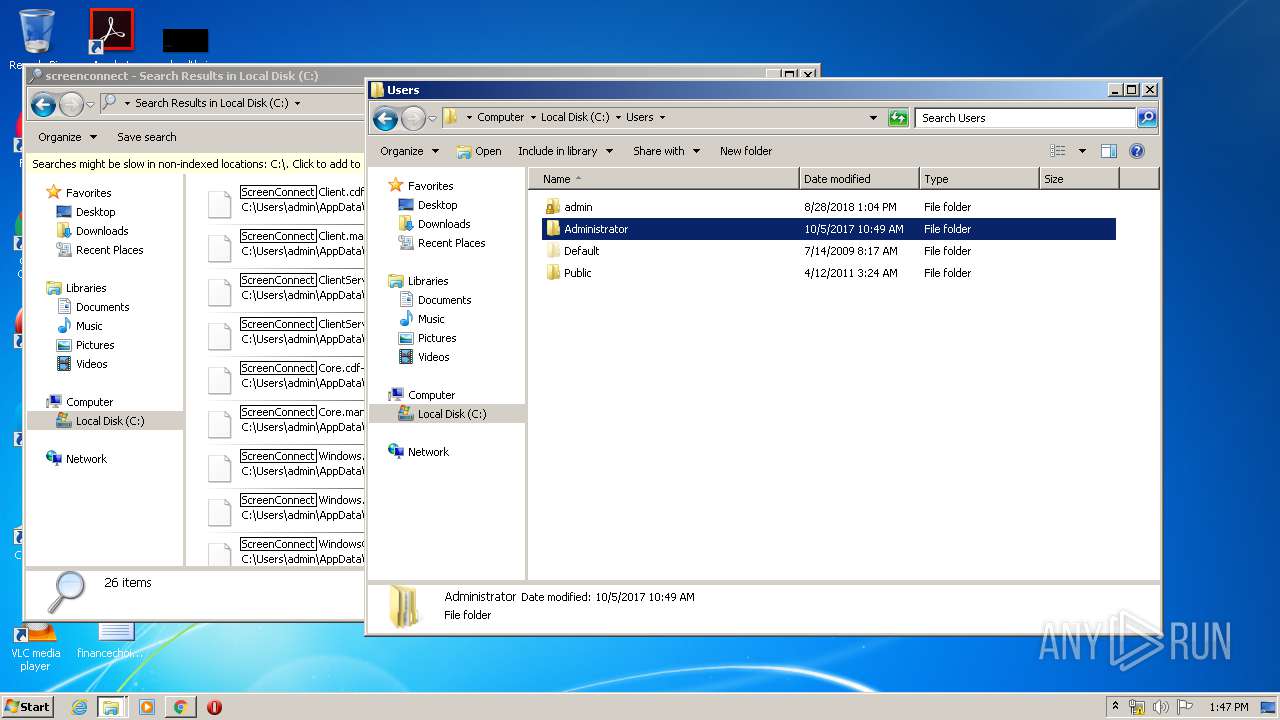
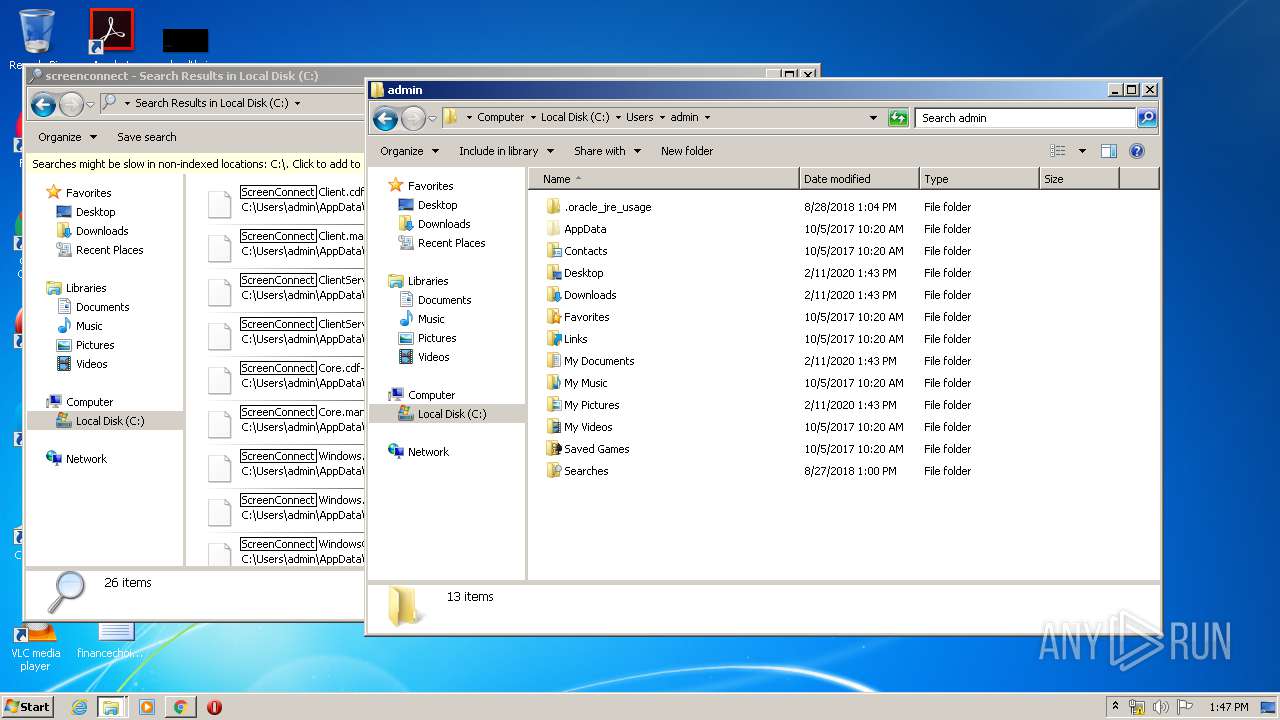
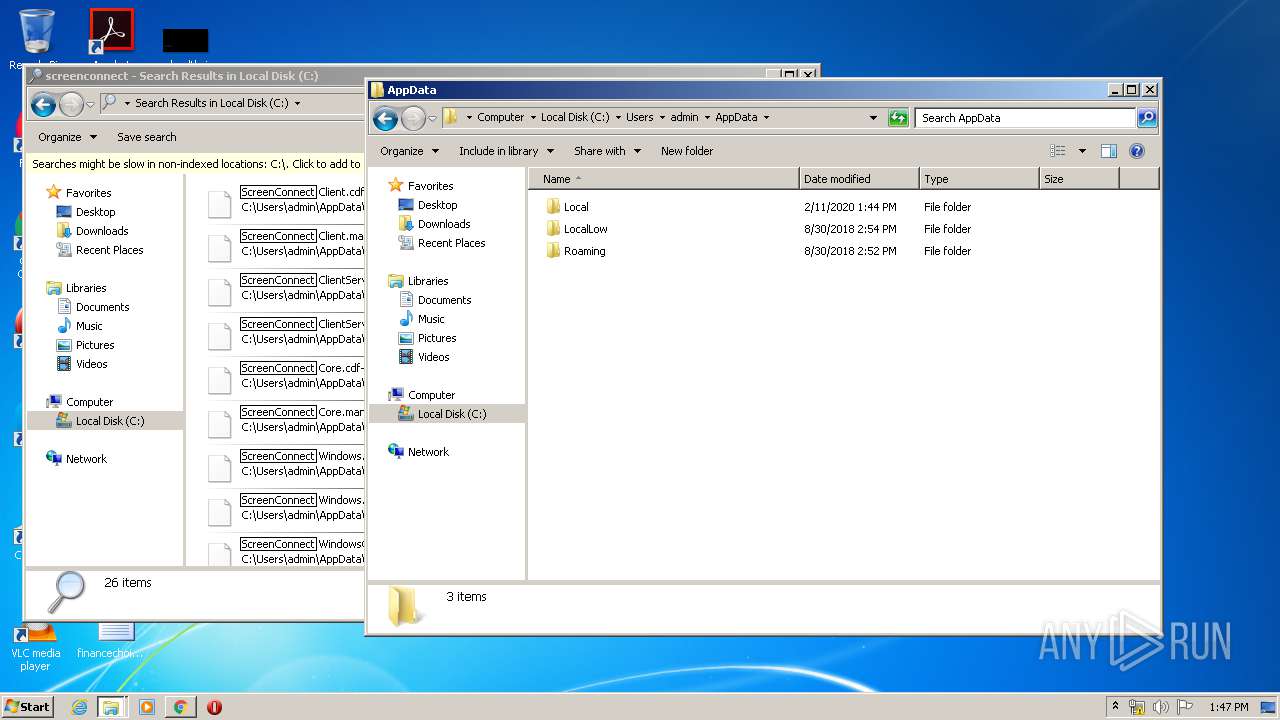
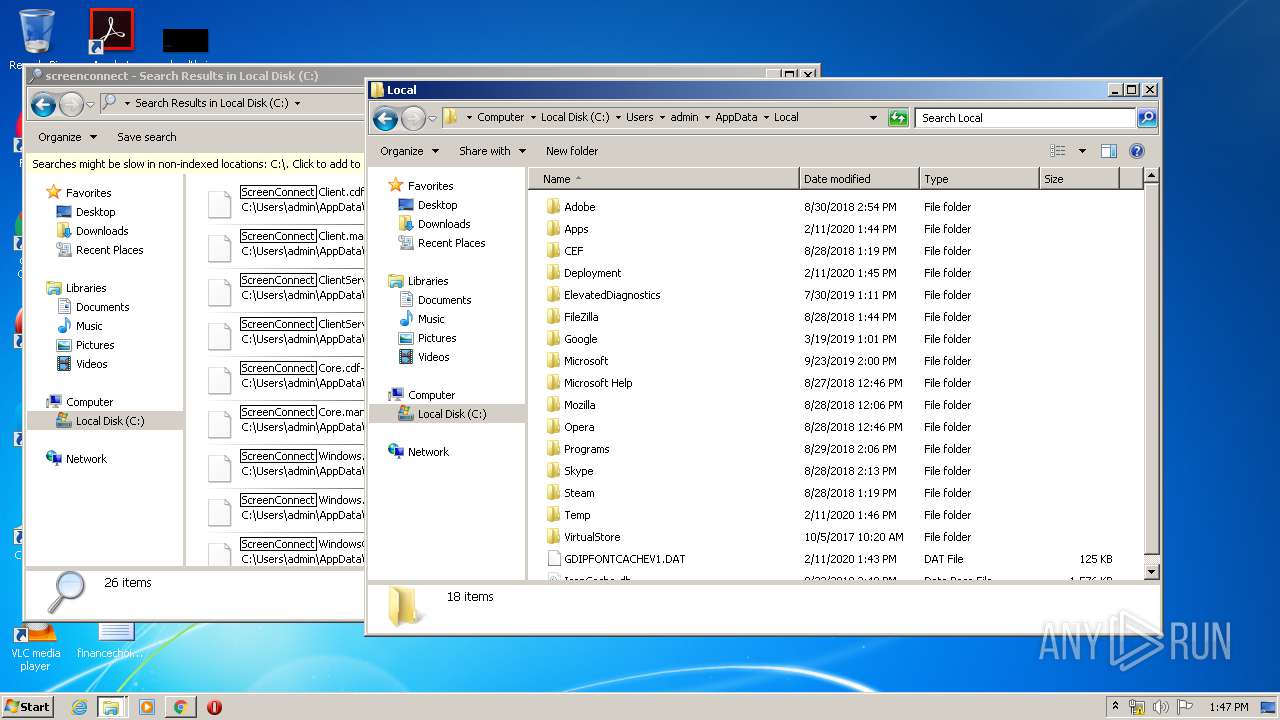
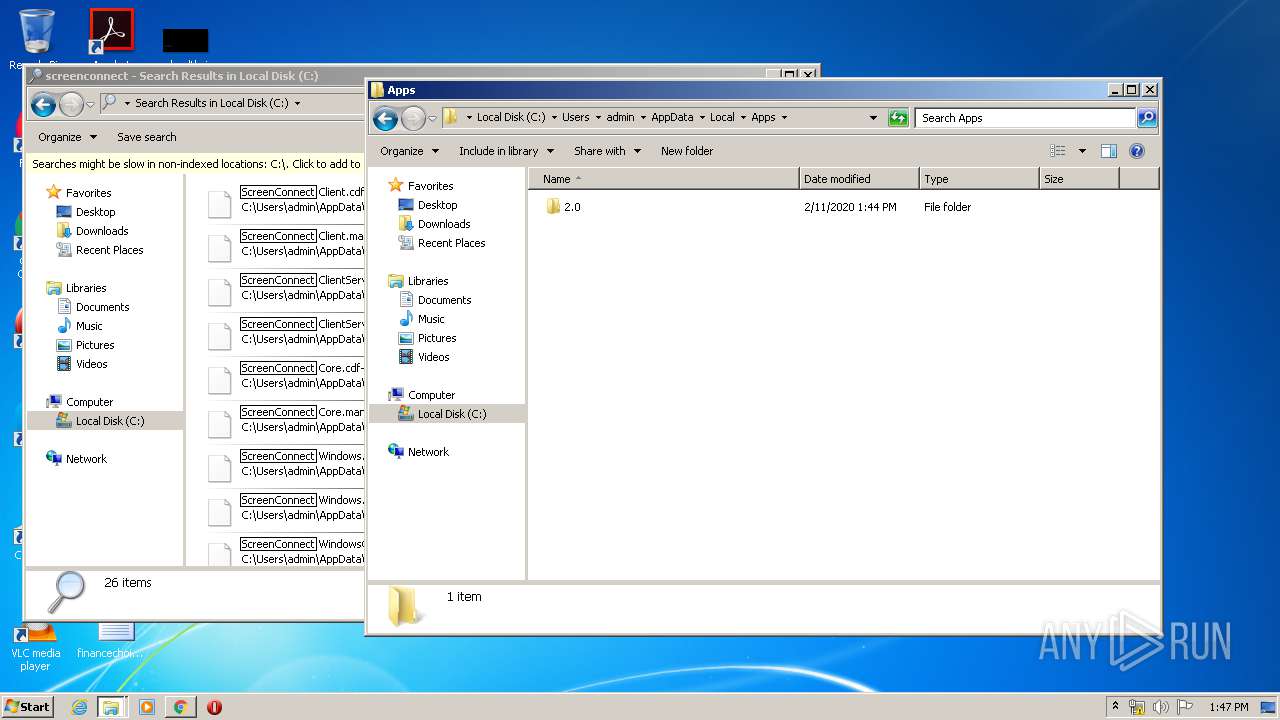
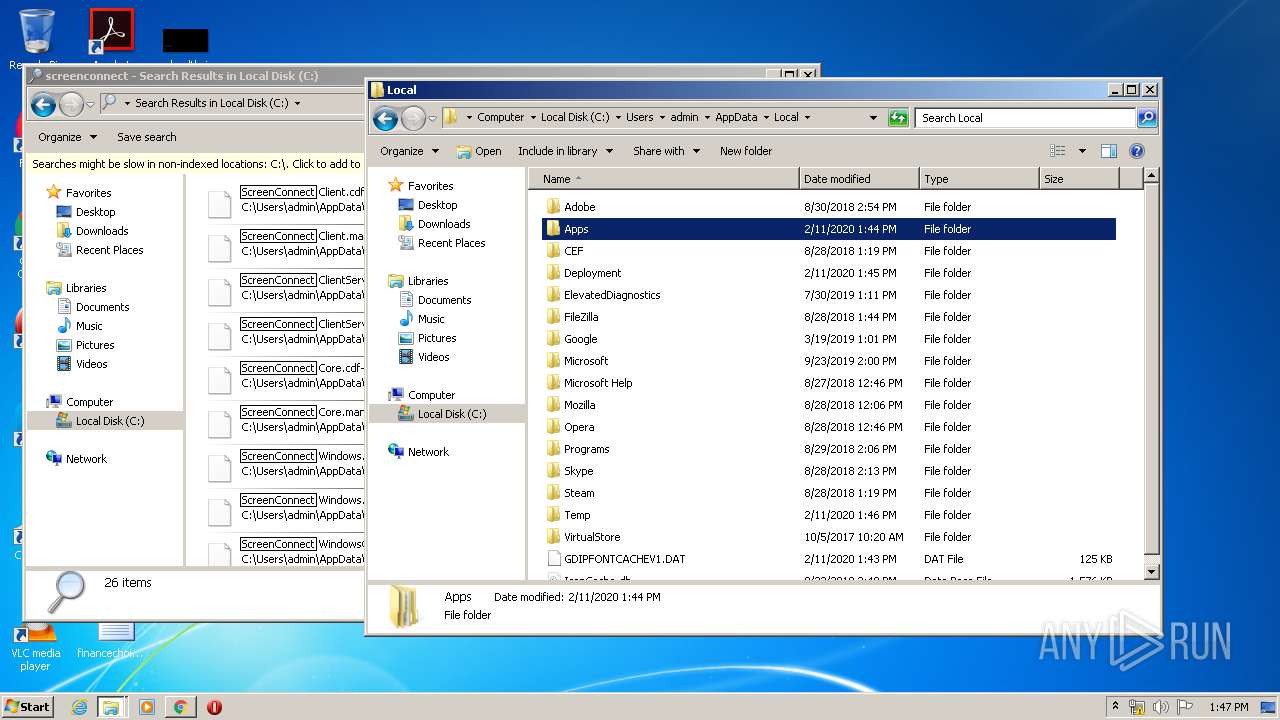
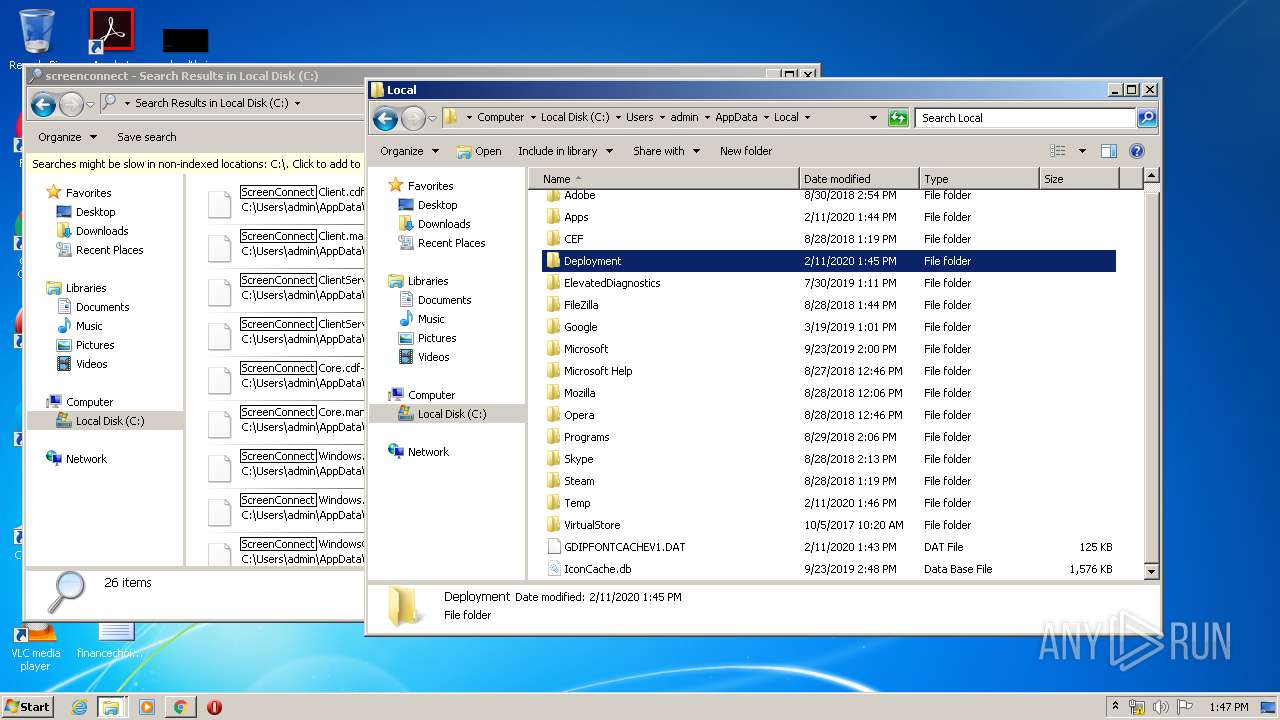
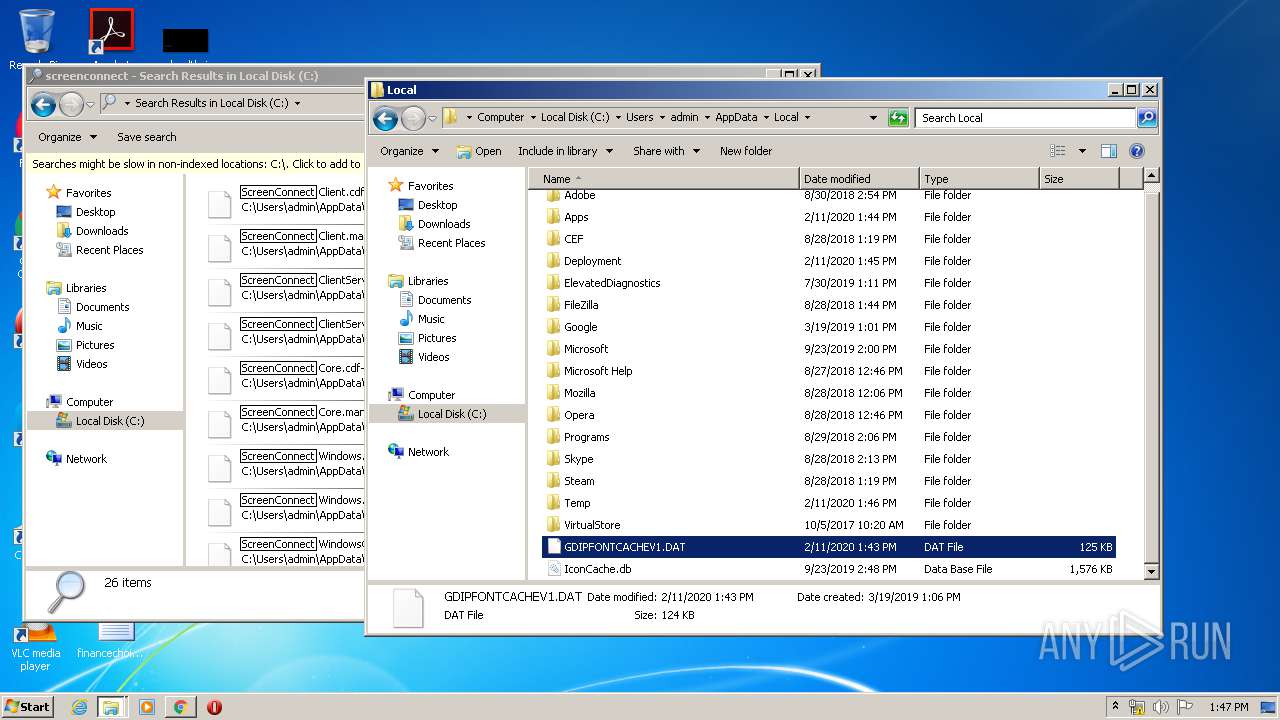
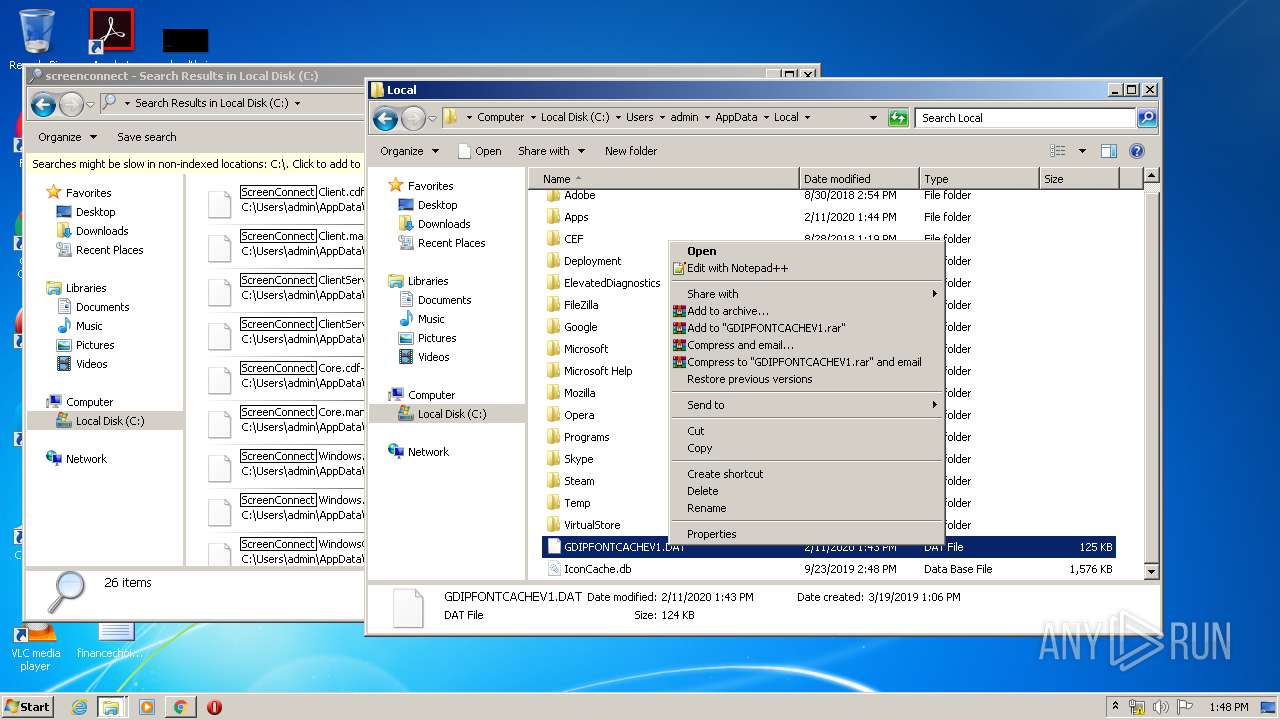
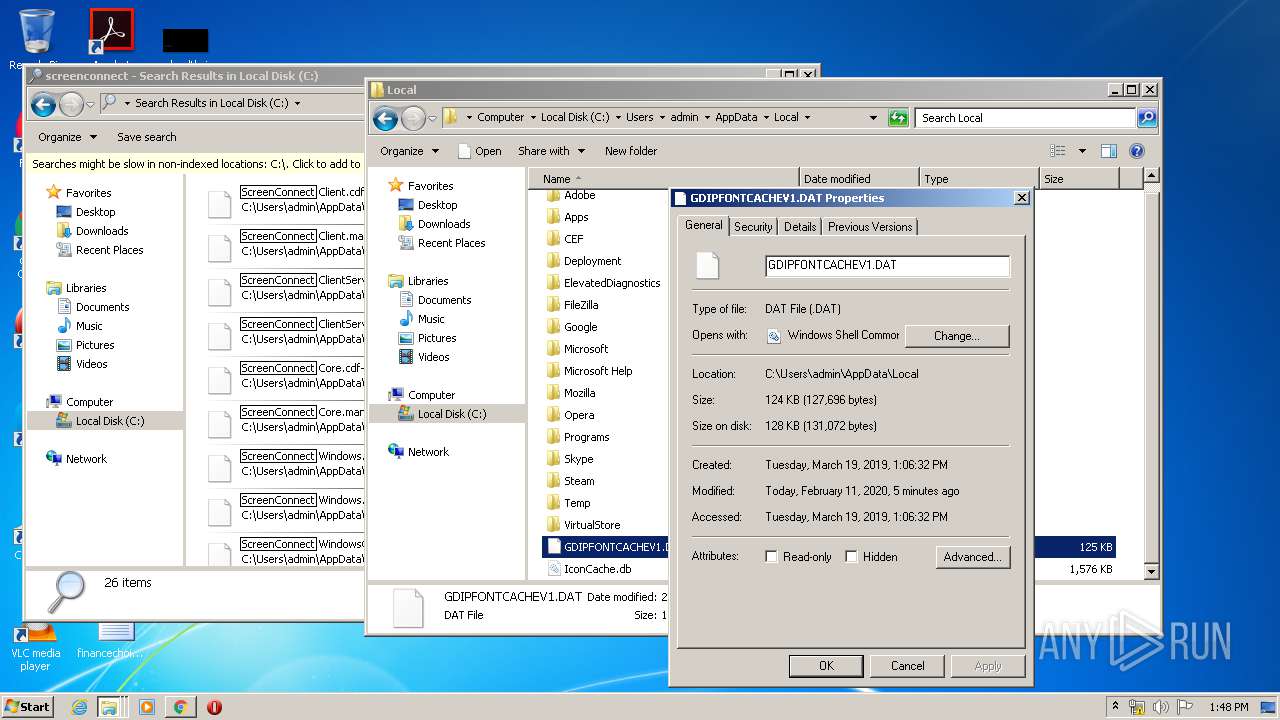
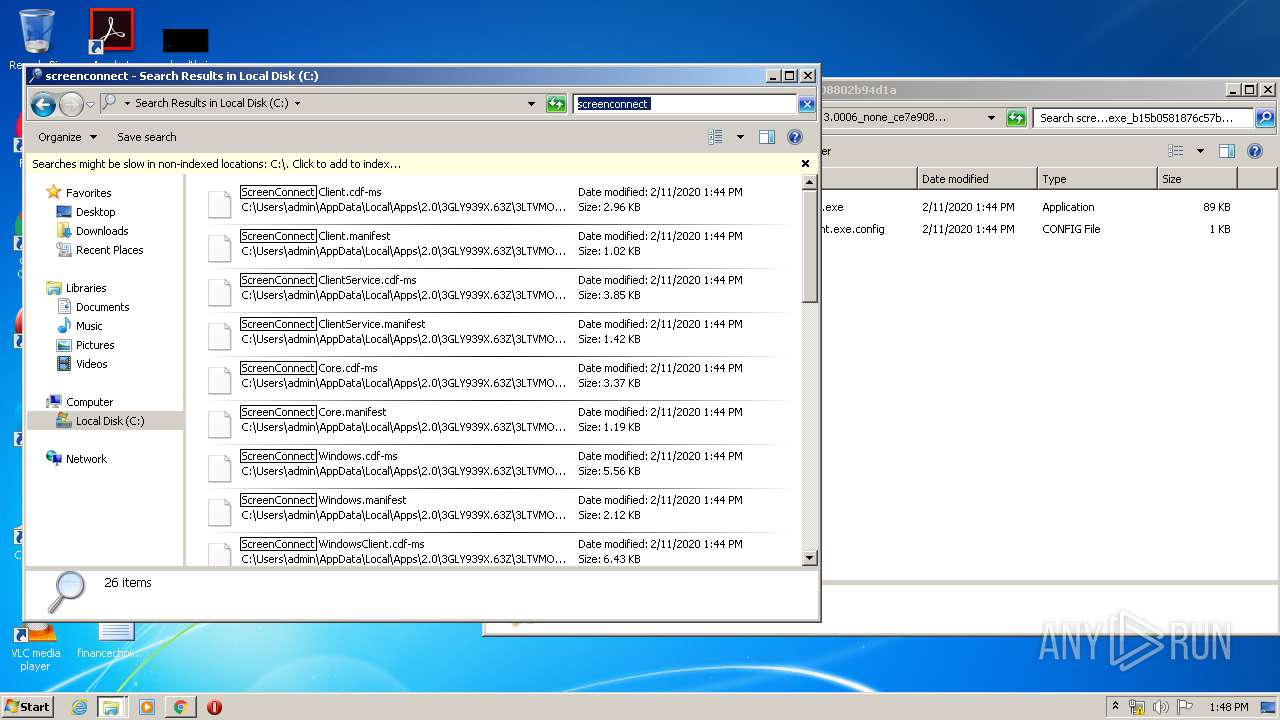
Creates files in the user directory
- dfsvc.exe (PID: 2908)
Reads internet explorer settings
- dfsvc.exe (PID: 2908)
Executed via COM
- DllHost.exe (PID: 1440)
Executed as Windows Service
- ScreenConnect.ClientService.exe (PID: 1536)
- ScreenConnect.ClientService.exe (PID: 3600)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3144)
INFO
Application launched itself
- chrome.exe (PID: 3144)
Reads Internet Cache Settings
- chrome.exe (PID: 3144)
Reads the hosts file
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2720)
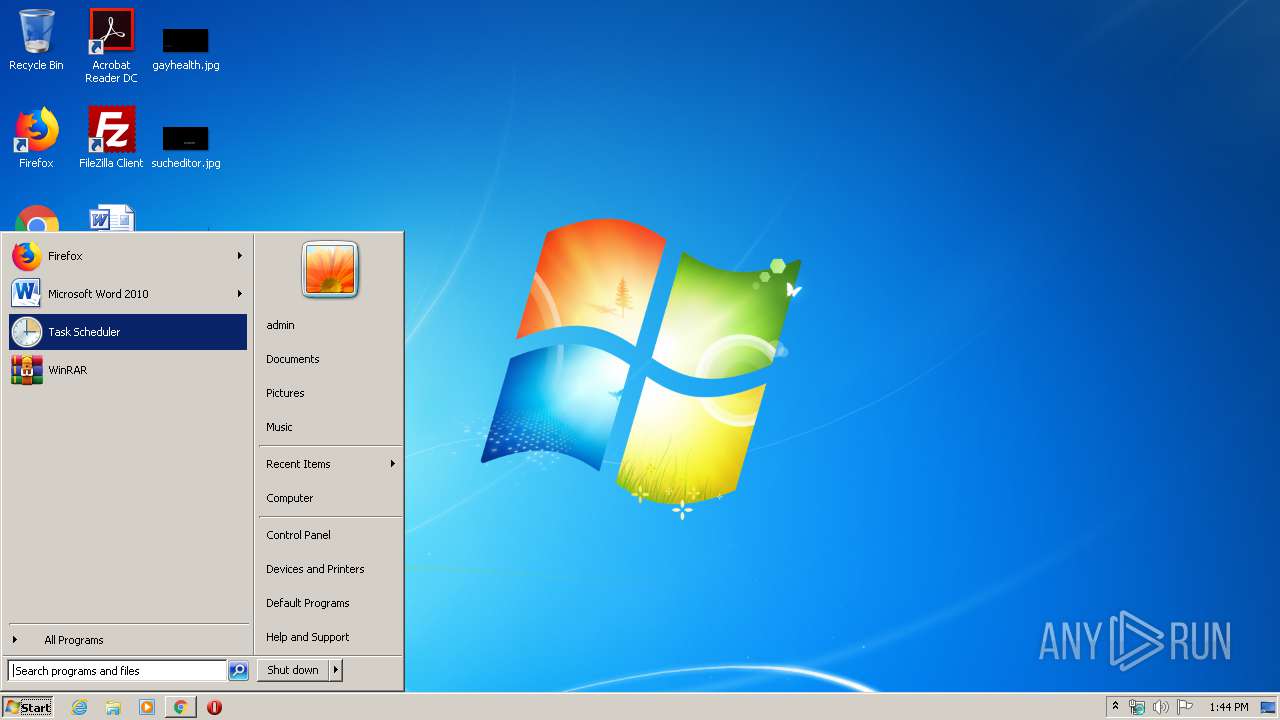
Manual execution by user
- explorer.exe (PID: 3052)
- CudaConnectControl.Client.exe (PID: 3172)
- explorer.exe (PID: 1732)
Reads settings of System Certificates
- chrome.exe (PID: 2720)
- dfsvc.exe (PID: 2908)
- explorer.exe (PID: 372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
41
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,10074203309683244980,14883784099090478254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14930929468269494191 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10074203309683244980,14883784099090478254,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10818144391475121347 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,10074203309683244980,14883784099090478254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2132091741134326195 --mojo-platform-channel-handle=980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
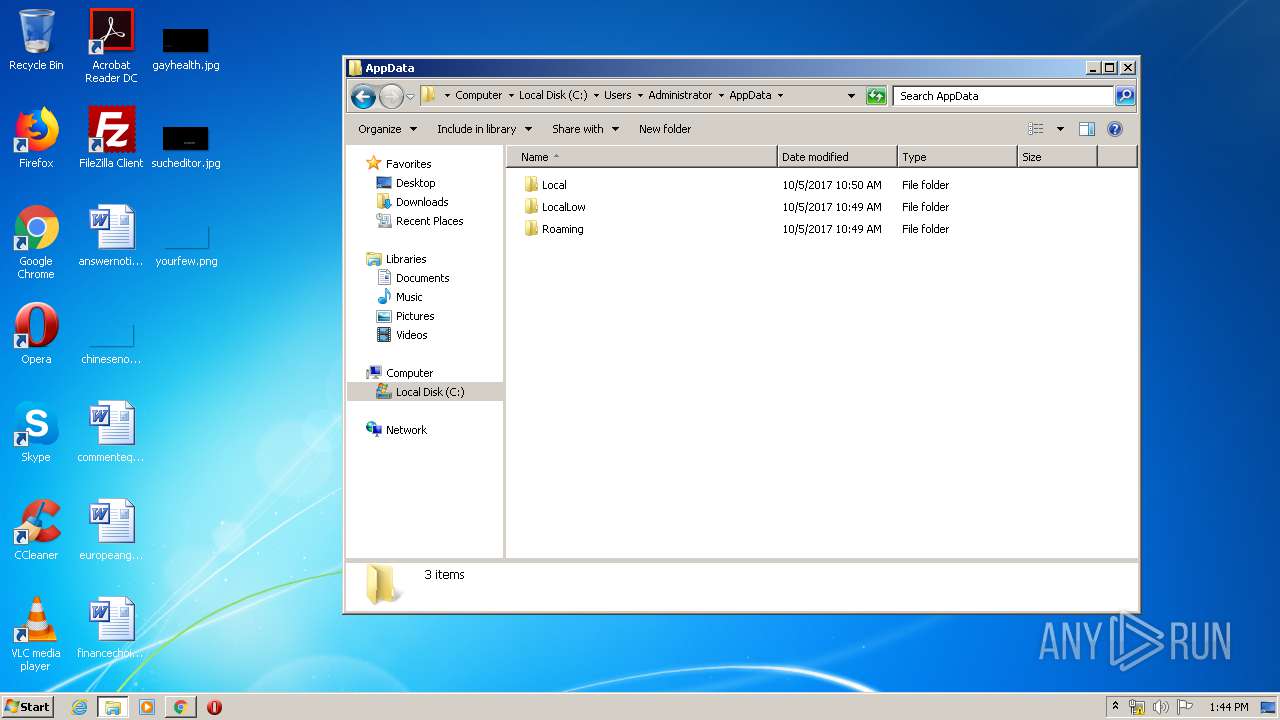
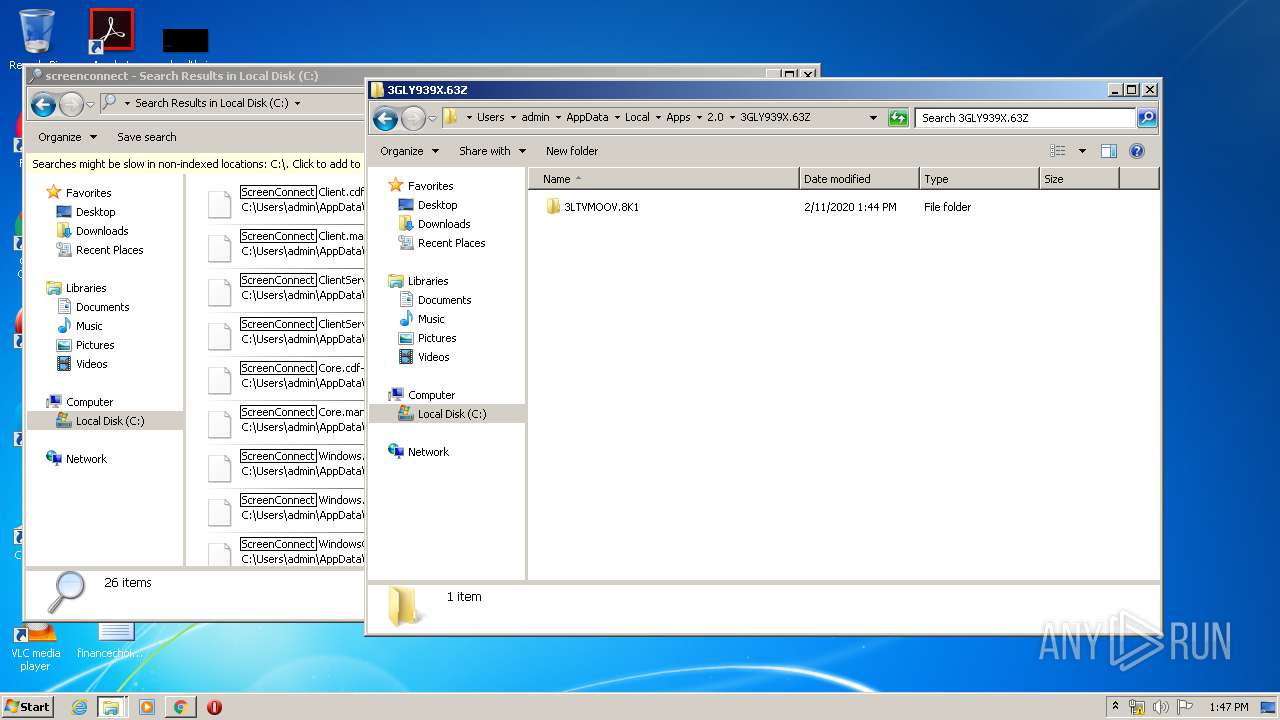
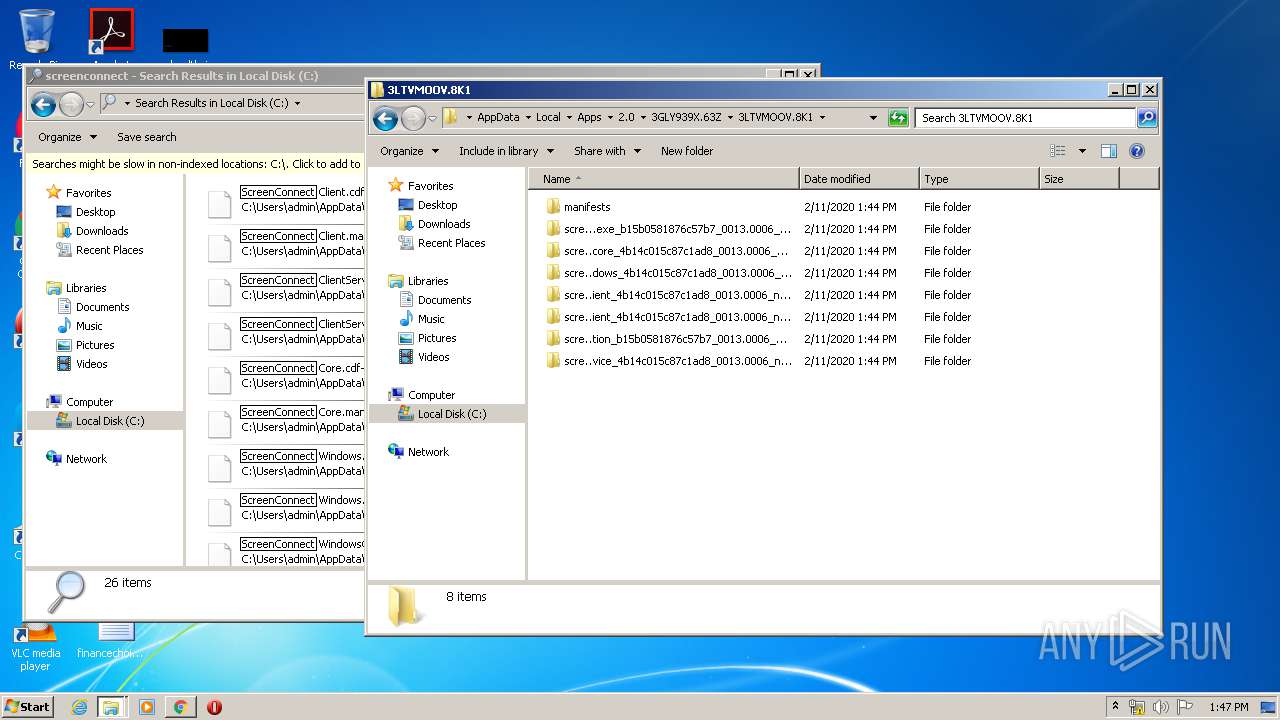
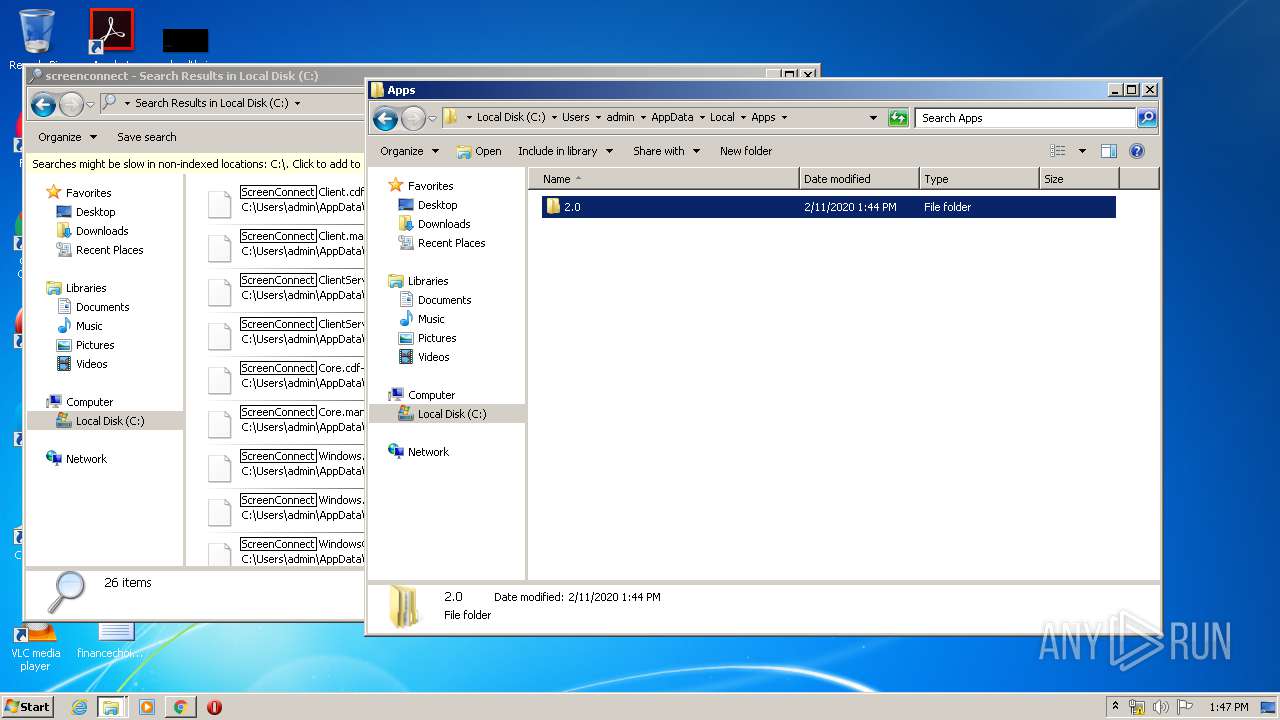
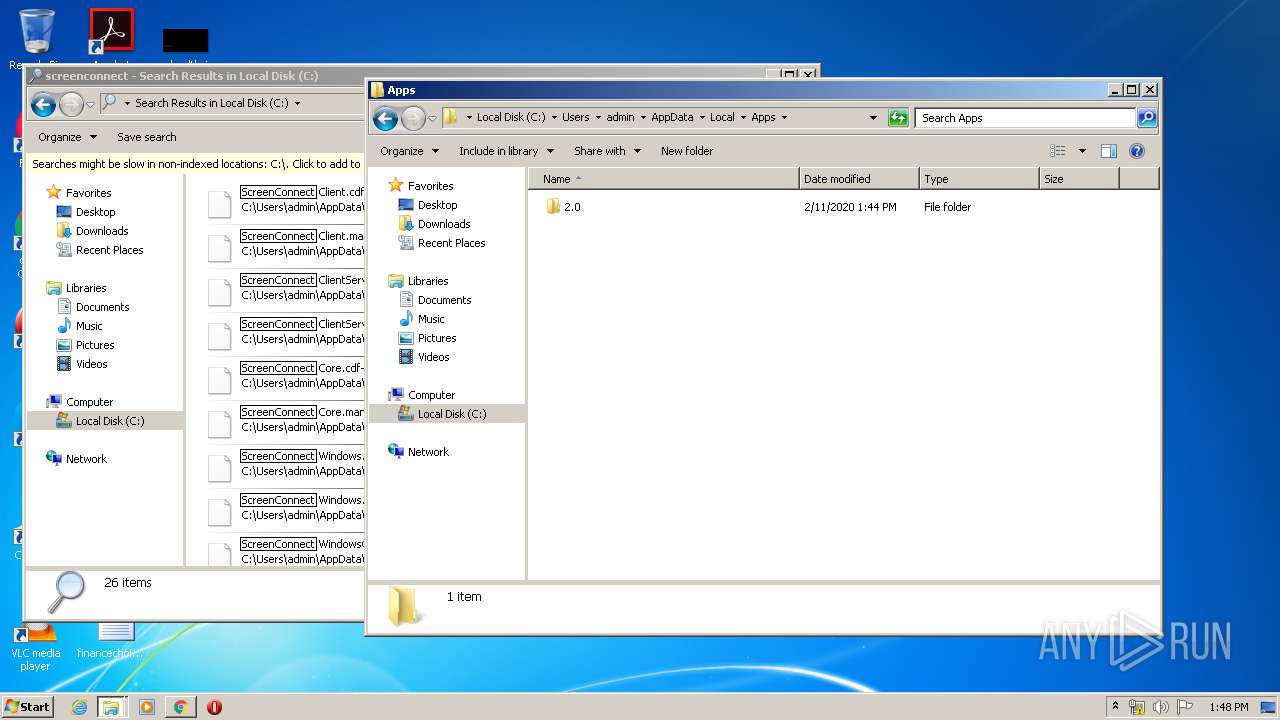
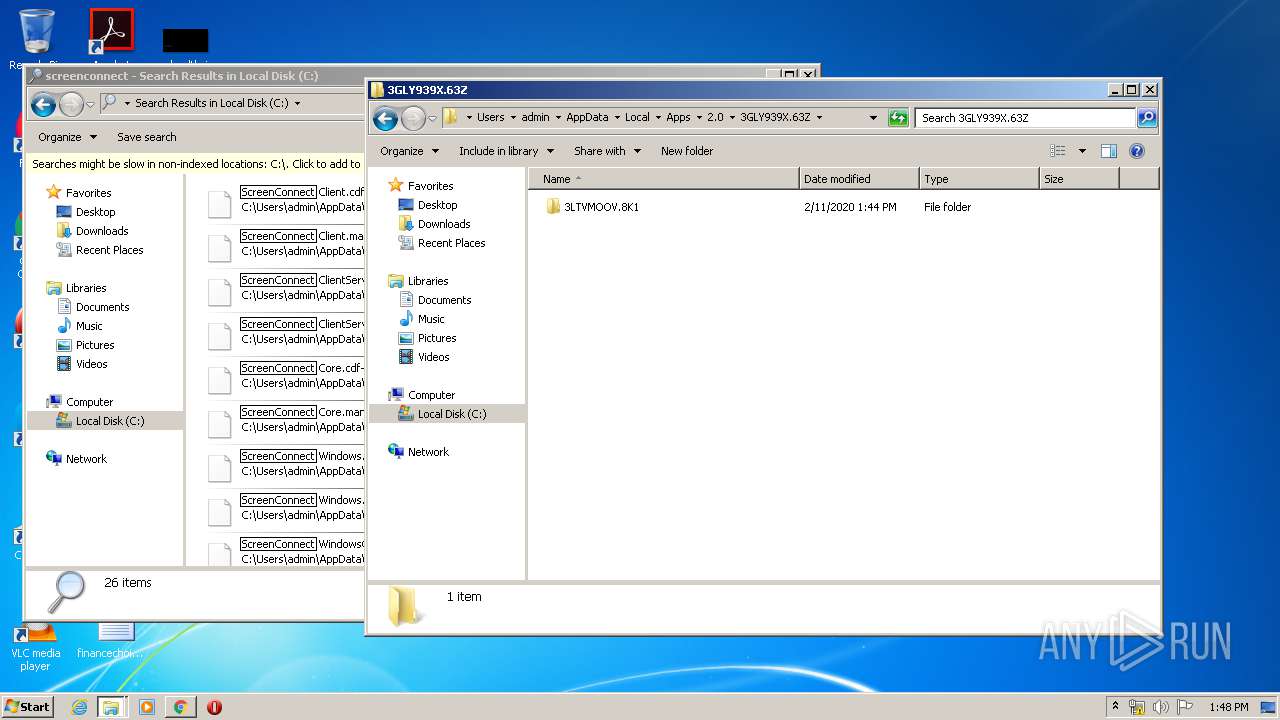
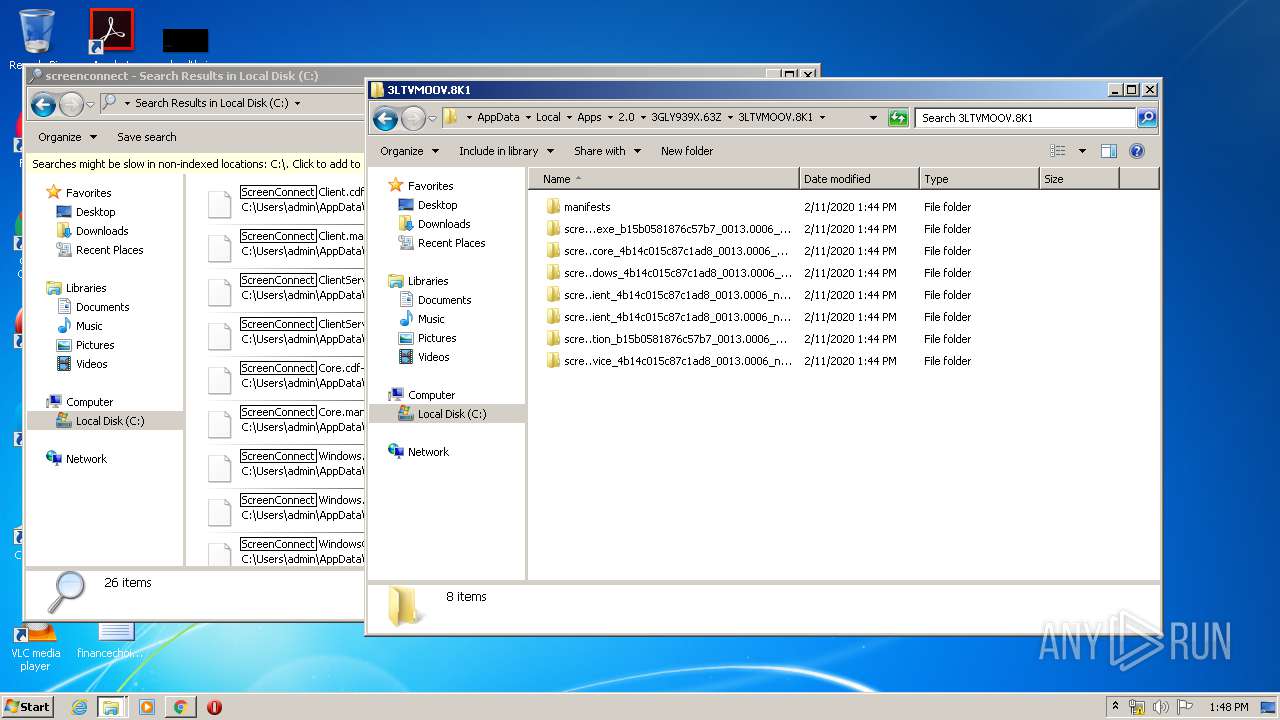
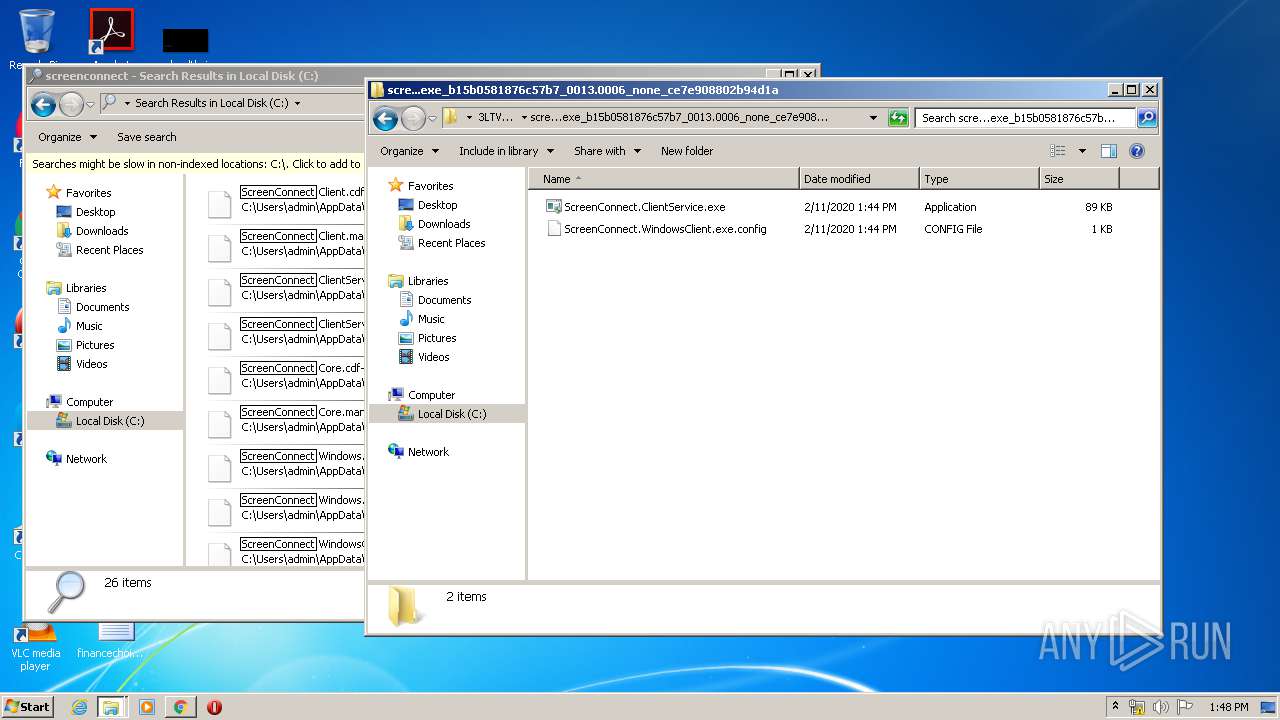
| 1536 | "C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.ClientService.exe" "?y=Guest&h=relay.barracuda.com&p=443&s=a4ee4c24-3cad-4aba-8a5b-8c949551c491&k=BgIAAACkAABSU0ExAAgAAAEAAQAHik5QKCh51SFYqsHkj1MJhVc8Gniu8piQR3LwsFHBsYPJ%2bDht5wSsvX6DNMkWLf5njjKQbkzxfvN%2bGhLfQghXAJkpaSna5NM%2b%2b56j%2f01iK7aQTVUcibPicmOZn1fNrW3AJ4236oJCVeCXM69ZNjQVeOCQoRthUQZUe9bkqDPXS0xKSt81VXiKHpIVNo305utR064UKV9WClUw1VTa2v71AmUsqgcKnGZMKZbiPnLegfmTlUNdUroSLeUkkf8cnXLGHPecLgyg3s3QwqGNg7nVhdLfwsIbg27ZuB64SceHitYorH2RB7e%2fc1W5lxJAUwh%2fjpQf4AJFB1r8KR7lakG9&r=&i=02592500" "1" | C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 19.6.26378.7317 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10074203309683244980,14883784099090478254,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4749824154188698311 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.WindowsClient.exe | — | dfsvc.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 19.6.26378.7317 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,10074203309683244980,14883784099090478254,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14134417760950761469 --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.ClientService.exe" "?y=Guest&h=relay.barracuda.com&p=443&s=a4ee4c24-3cad-4aba-8a5b-8c949551c491&k=BgIAAACkAABSU0ExAAgAAAEAAQAHik5QKCh51SFYqsHkj1MJhVc8Gniu8piQR3LwsFHBsYPJ%2bDht5wSsvX6DNMkWLf5njjKQbkzxfvN%2bGhLfQghXAJkpaSna5NM%2b%2b56j%2f01iK7aQTVUcibPicmOZn1fNrW3AJ4236oJCVeCXM69ZNjQVeOCQoRthUQZUe9bkqDPXS0xKSt81VXiKHpIVNo305utR064UKV9WClUw1VTa2v71AmUsqgcKnGZMKZbiPnLegfmTlUNdUroSLeUkkf8cnXLGHPecLgyg3s3QwqGNg7nVhdLfwsIbg27ZuB64SceHitYorH2RB7e%2fc1W5lxJAUwh%2fjpQf4AJFB1r8KR7lakG9&r=&i=02592500" "1" | C:\Users\admin\AppData\Local\Apps\2.0\3GLY939X.63Z\3LTVMOOV.8K1\scre..tion_b15b0581876c57b7_0013.0006_0df211f7e977d0a8\ScreenConnect.ClientService.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 19.6.26378.7317 Modules
| |||||||||||||||
Total events
9 435
Read events
6 377
Write events
2 993
Delete events
65
Modification events
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3144-13225902230834500 |
Value: 259 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
39
Text files
236
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E42AF97-C48.pma | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3553928a-47de-47bc-acb9-dcd330afa6fc.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa65f6e.TMP | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa65f8d.TMP | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa65ffa.TMP | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa660e5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
2720 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=45.86.202.5&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1581428717&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2720 | chrome.exe | GET | 200 | 74.125.104.108:80 | http://r6---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=45.86.202.5&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1581428717&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2908 | dfsvc.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.digicert.com/DigiCertSHA2AssuredIDCodeSigningCA.crt | US | der | 1.30 Kb | whitelisted |
2720 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | dfsvc.exe | 198.35.20.41:443 | connect.barracuda.com | — | US | unknown |
2720 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2720 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
3600 | ScreenConnect.ClientService.exe | 198.35.20.42:443 | relay.barracuda.com | — | US | unknown |
2720 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2720 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2720 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1536 | ScreenConnect.ClientService.exe | 198.35.20.42:443 | relay.barracuda.com | — | US | unknown |
2720 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2720 | chrome.exe | 172.217.130.73:80 | r4---sn-2gb7sn7r.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connect.barracuda.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
cacerts.digicert.com |
| whitelisted |
relay.barracuda.com |
| unknown |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|