| File name: | picpick_inst.exe |
| Full analysis: | https://app.any.run/tasks/745b53e9-cad8-4a2f-aa15-4436d713d308 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2019, 10:51:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 28D4CC73C604956DFFD7523600D7277E |
| SHA1: | E80FFDF455509BA71E333B15DB002FD94F1ED470 |
| SHA256: | EF683BB953AA5B1B650AEF364FACFCC70C3D73C2074C5E29049AC6770B8C767B |
| SSDEEP: | 196608:S7OPIjlBT9AzNidN/z8zaeCRQDya/xF45hBaULBJgiMVCdxVX4+u3LWrzv:S7OYw8dR4HAaJFO6ULoiMgxx4J3Lwv |
MALICIOUS
Loads dropped or rewritten executable
- picpick_inst.exe (PID: 792)
Application was dropped or rewritten from another process
- picpick.exe (PID: 2240)
- picpick.exe (PID: 2612)
Changes the autorun value in the registry
- picpick.exe (PID: 2612)
SUSPICIOUS
Executable content was dropped or overwritten
- picpick_inst.exe (PID: 792)
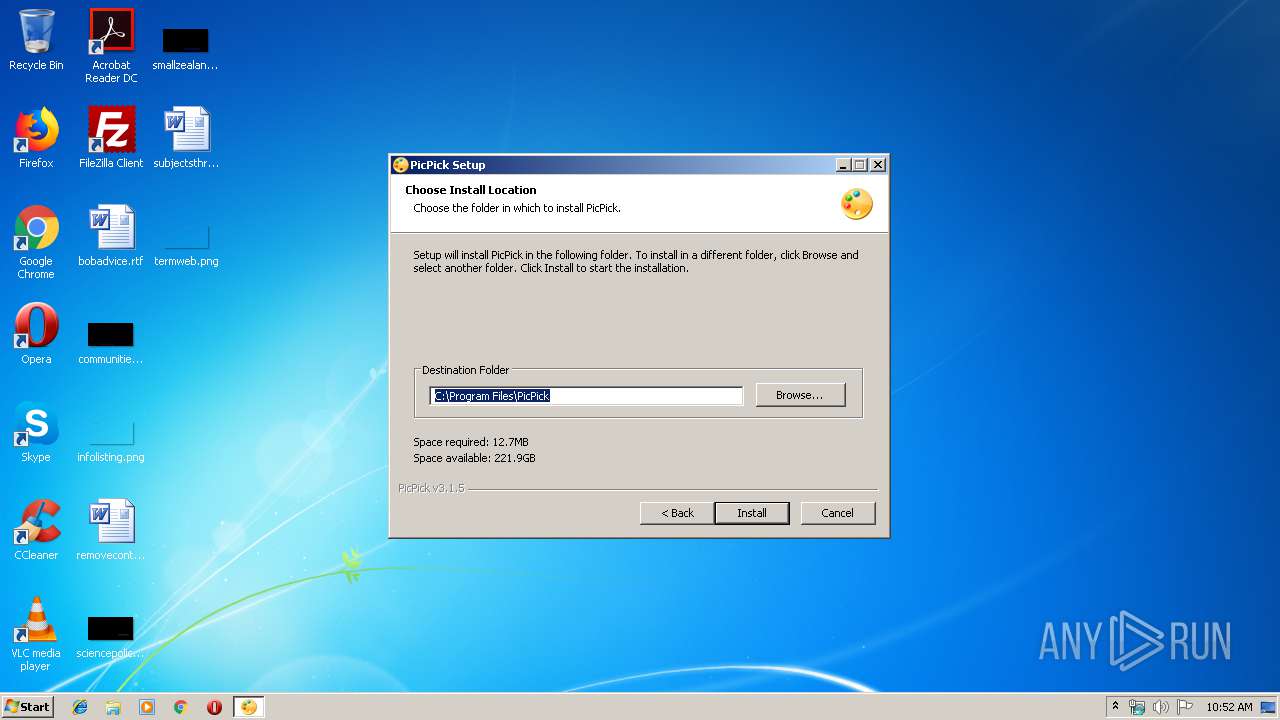
Creates files in the program directory
- picpick_inst.exe (PID: 792)
Creates files in the user directory
- picpick_inst.exe (PID: 792)
- picpick.exe (PID: 2612)
Creates a software uninstall entry
- picpick_inst.exe (PID: 792)
INFO
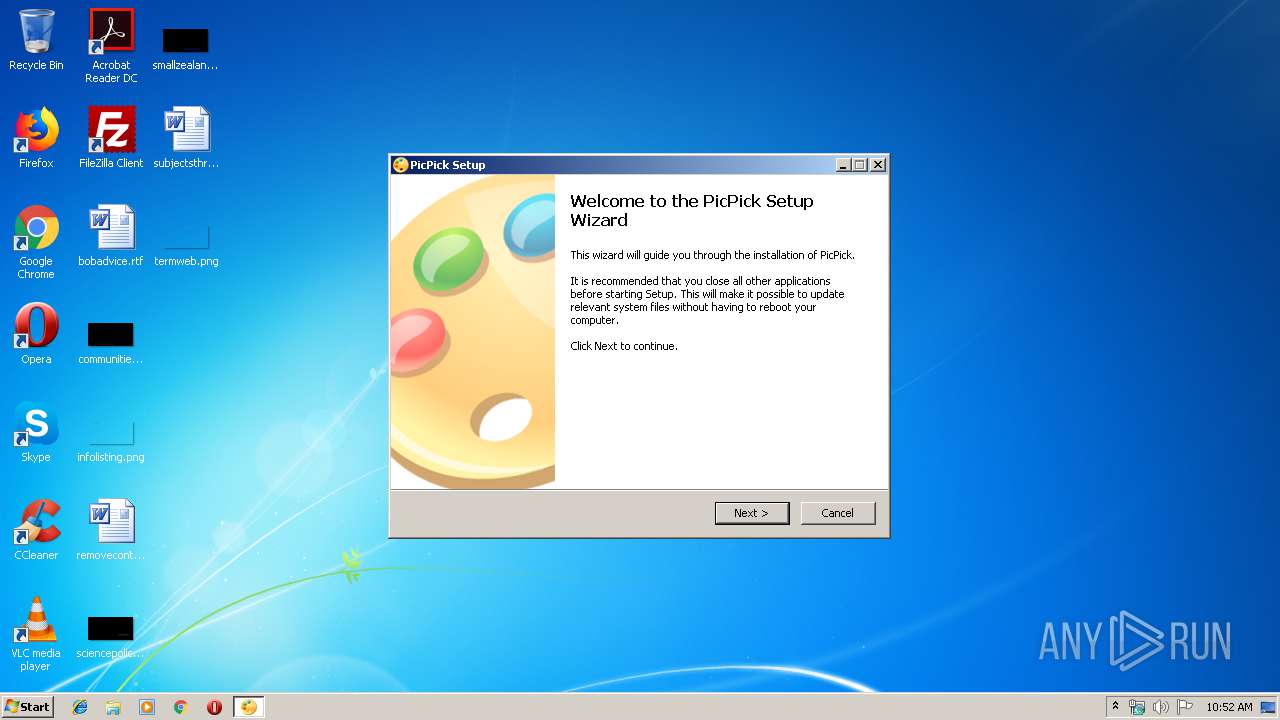
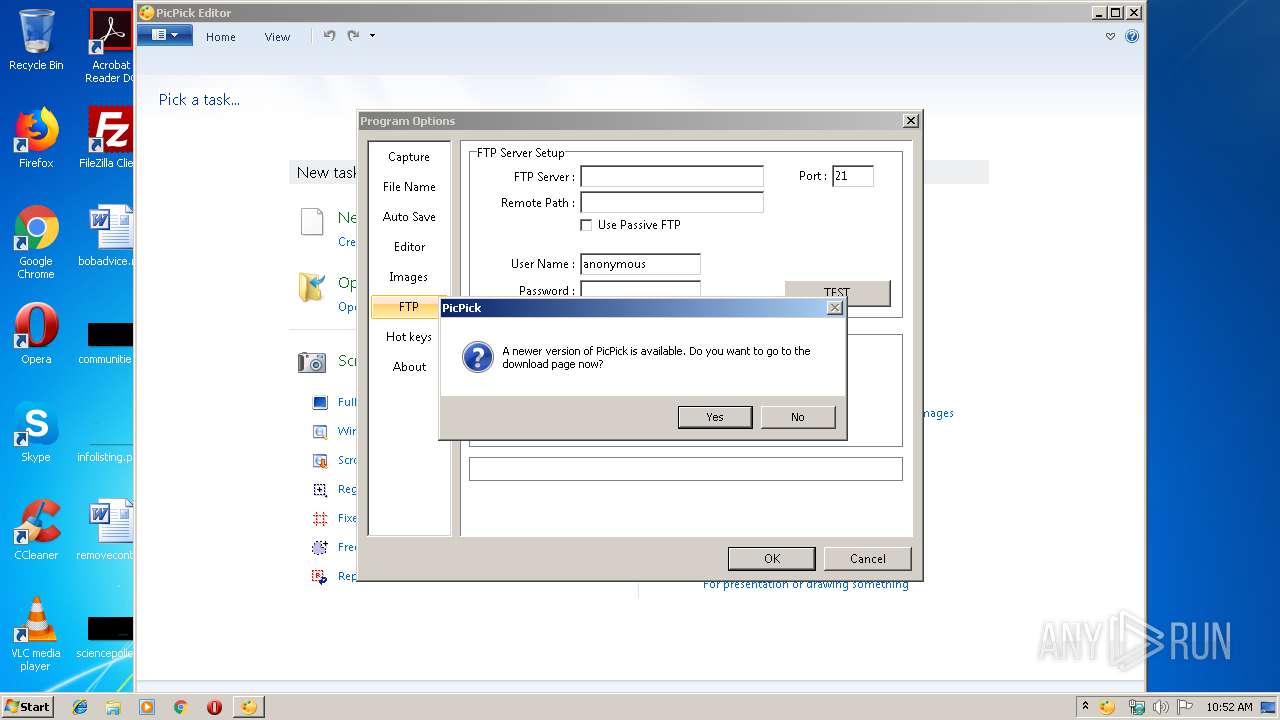
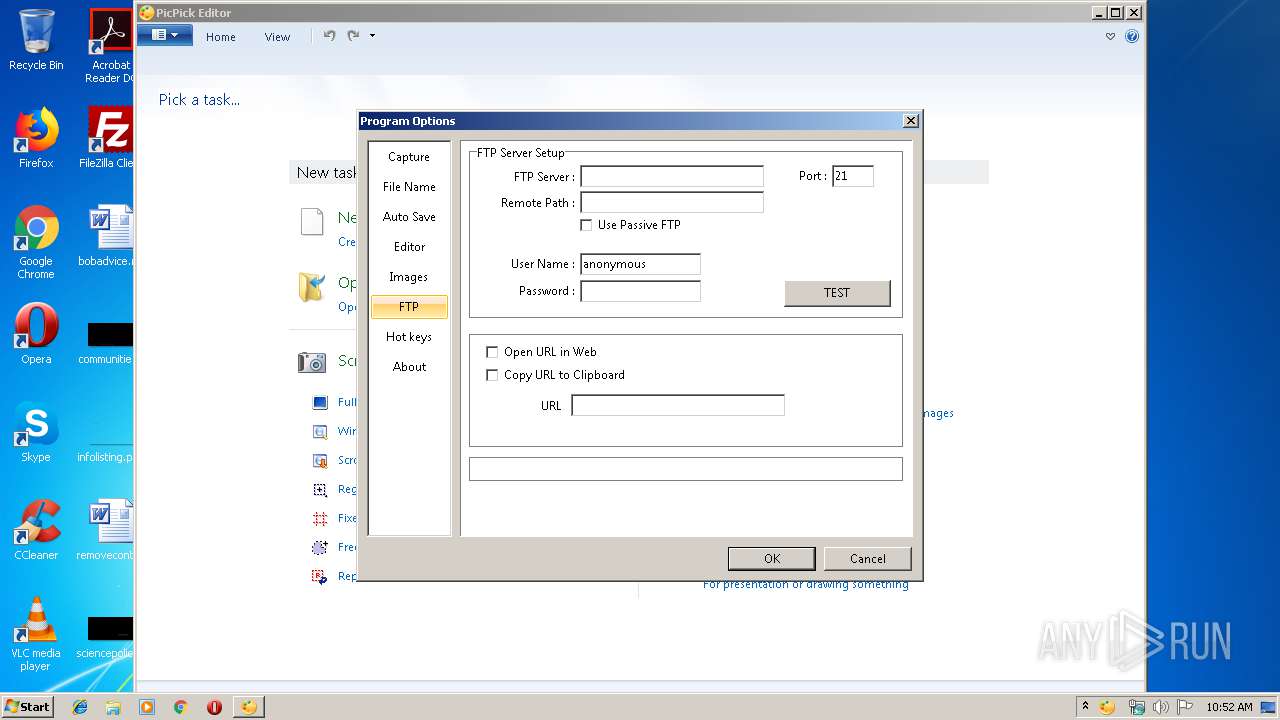
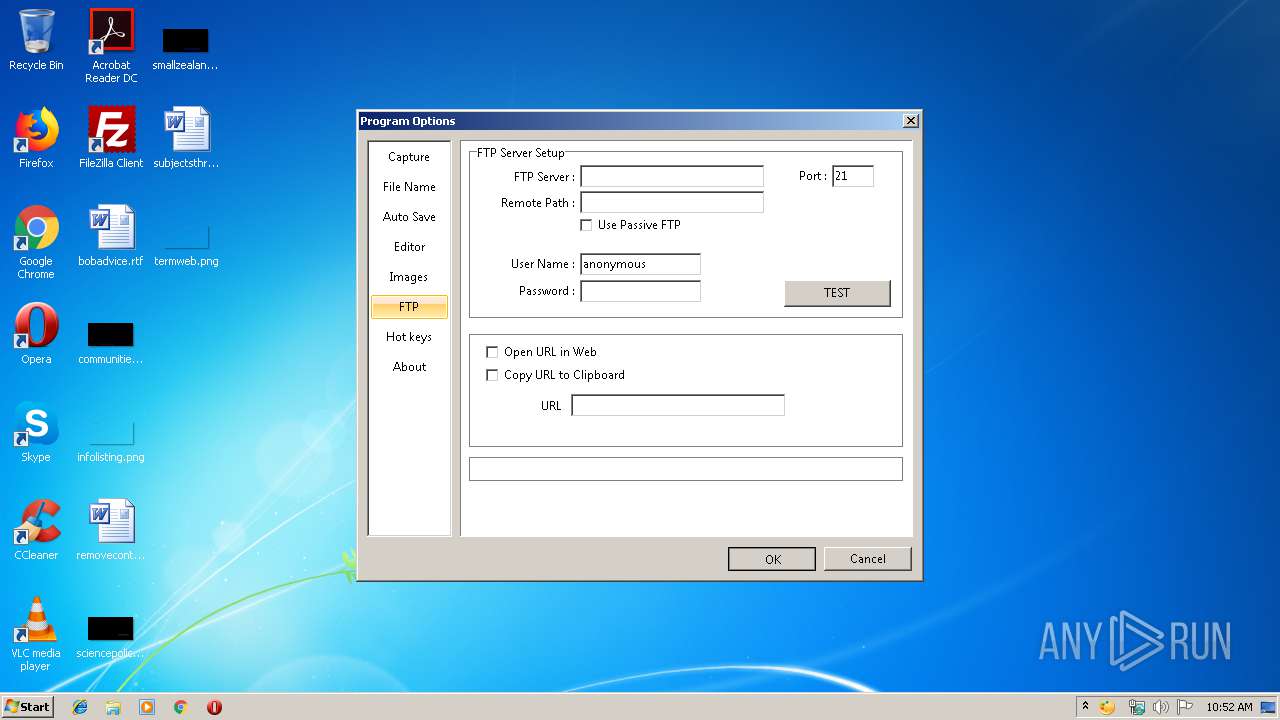
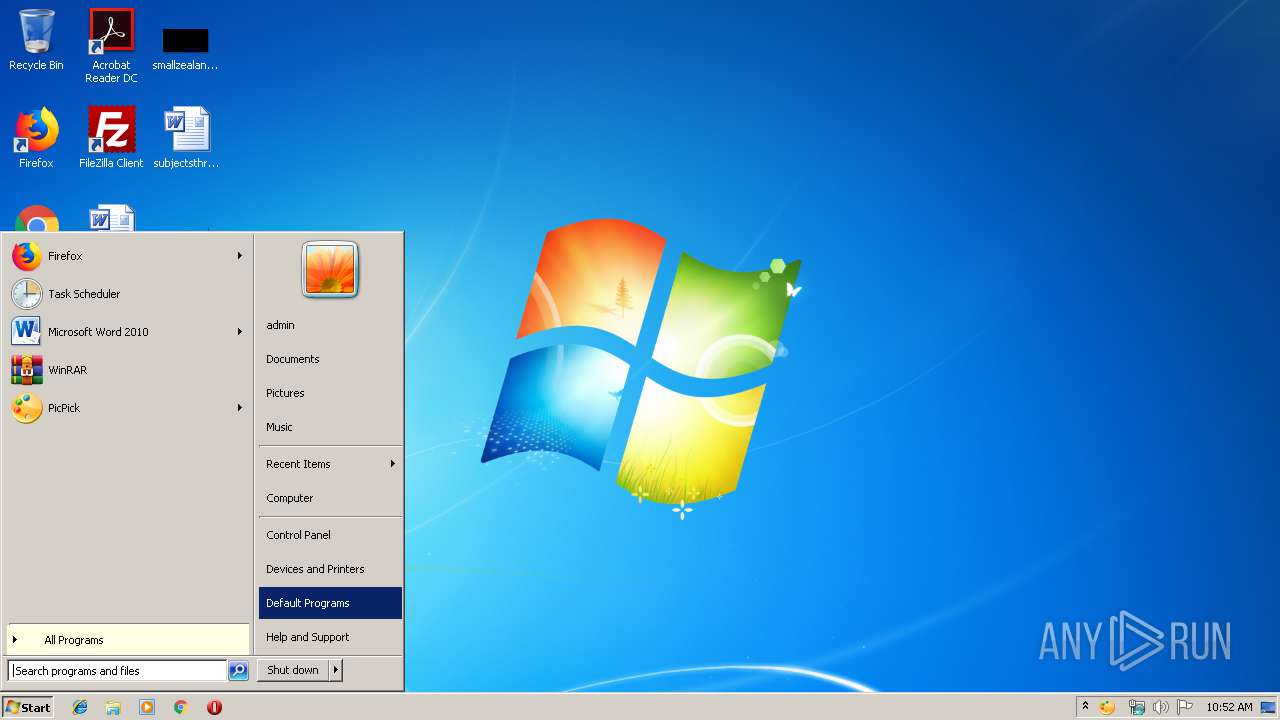
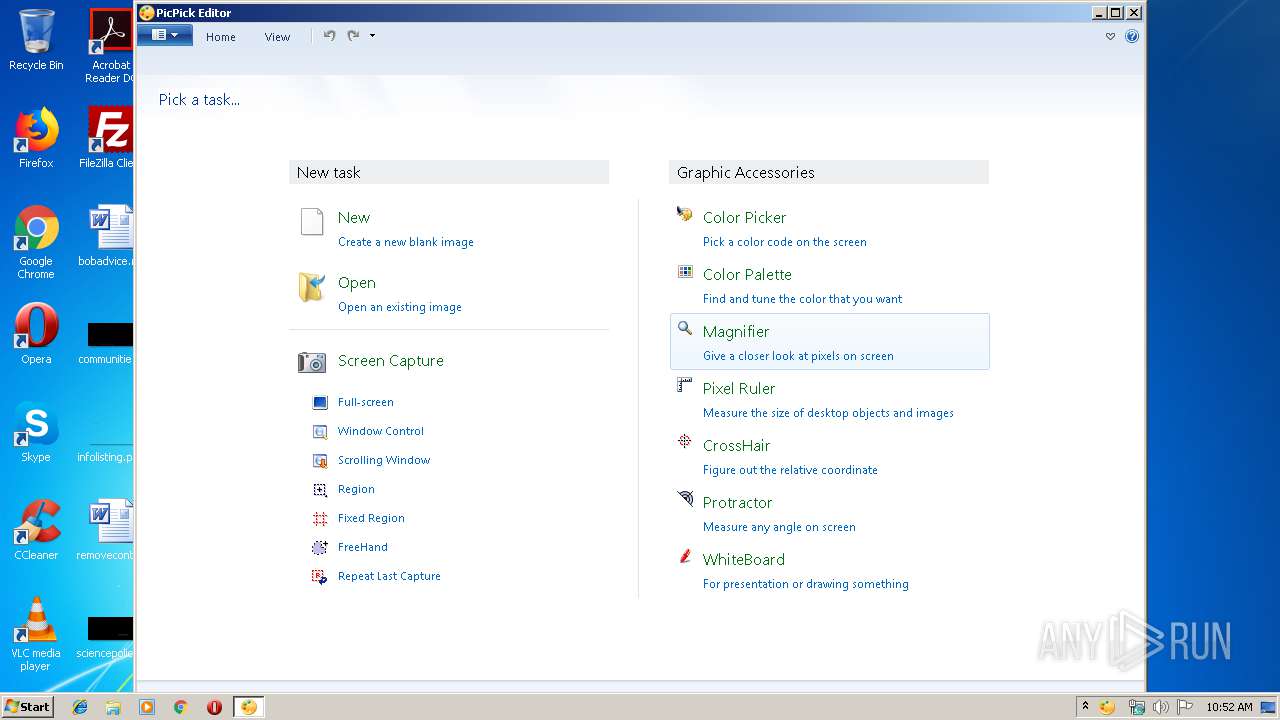
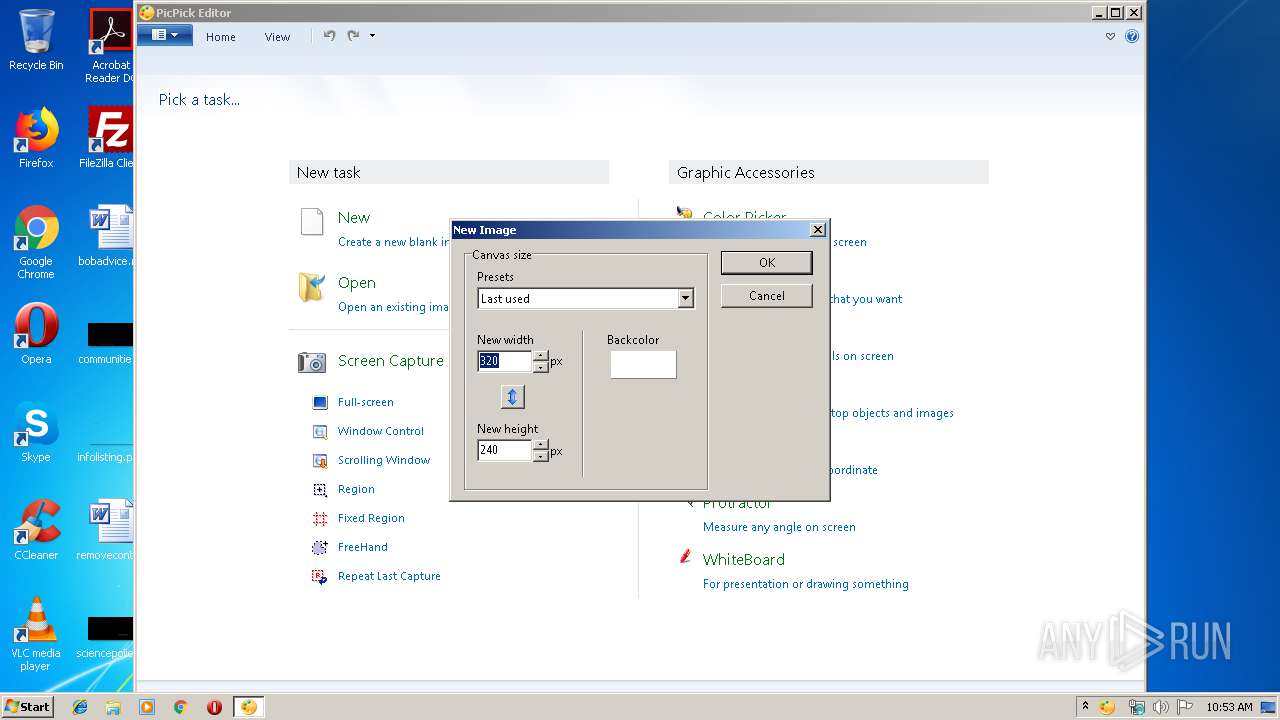
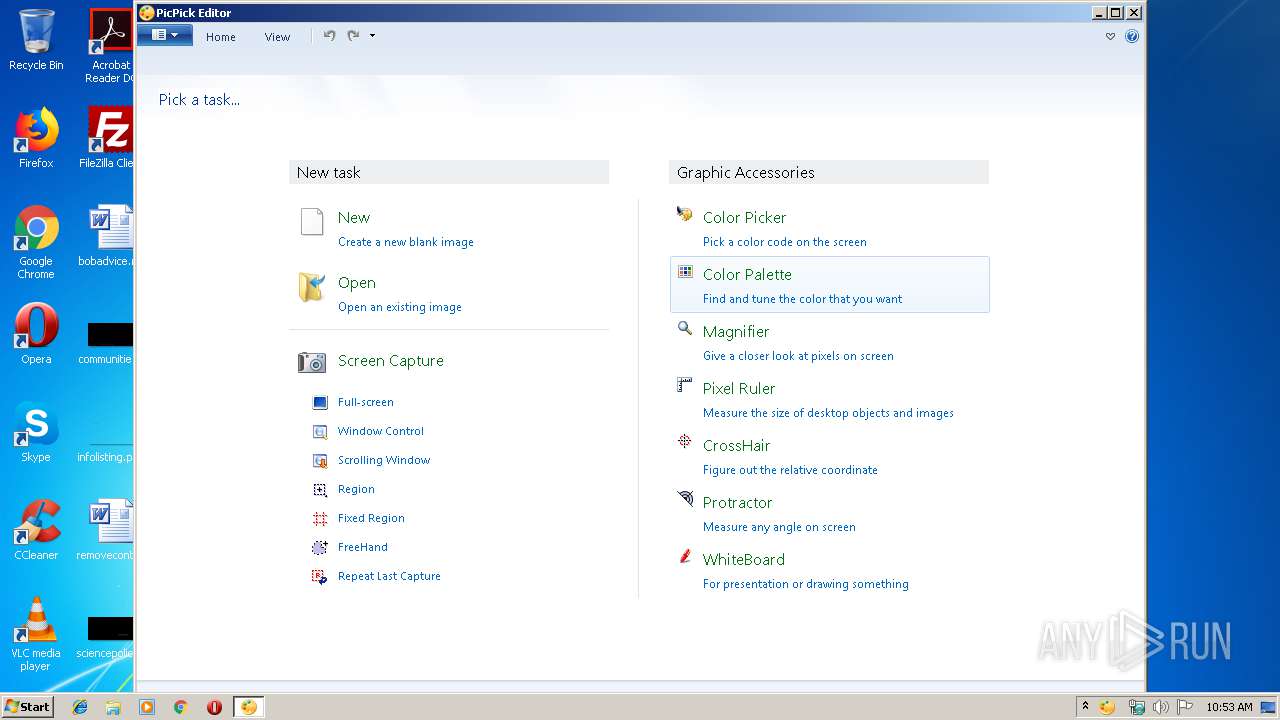
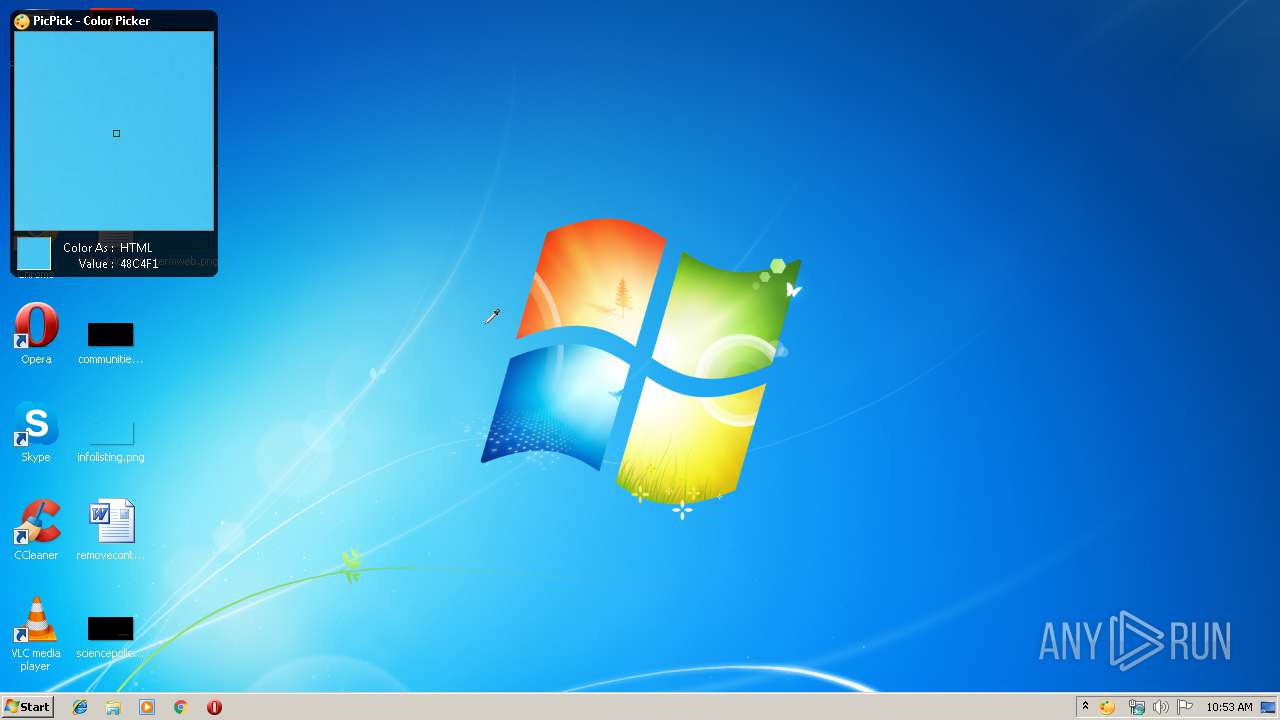
Manual execution by user
- picpick.exe (PID: 2240)
- picpick.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00040000 | 0x000466F0 | 0x00046800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1839 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.75585 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.74851 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.93487 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.58865 | 168 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.43192 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68273 | 502 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.83629 | 236 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.86753 | 226 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\Users\admin\AppData\Local\Temp\picpick_inst.exe" | C:\Users\admin\AppData\Local\Temp\picpick_inst.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
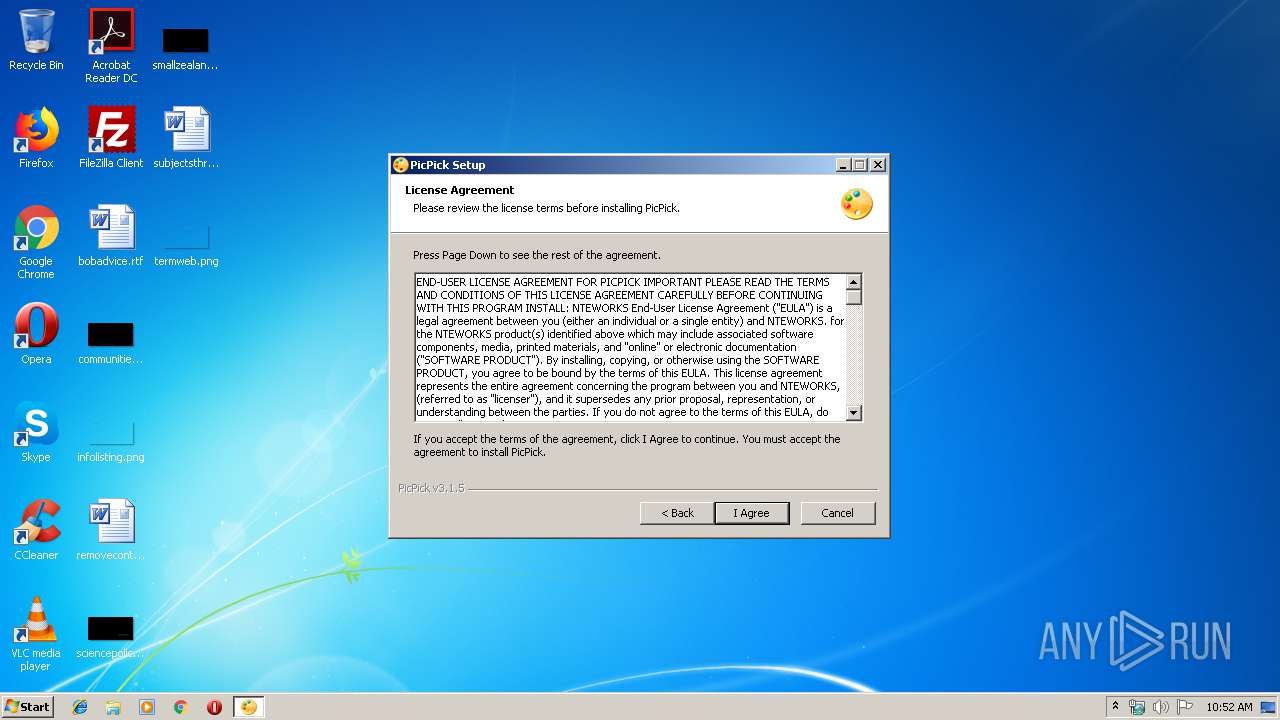
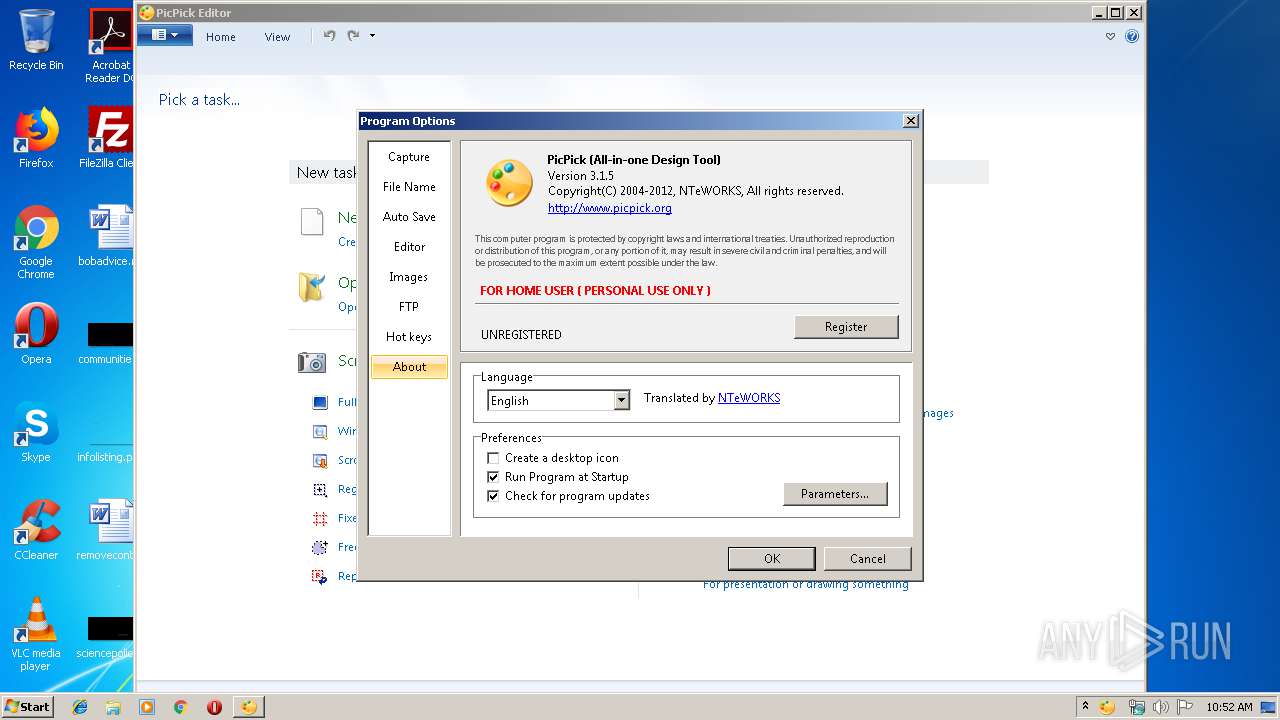
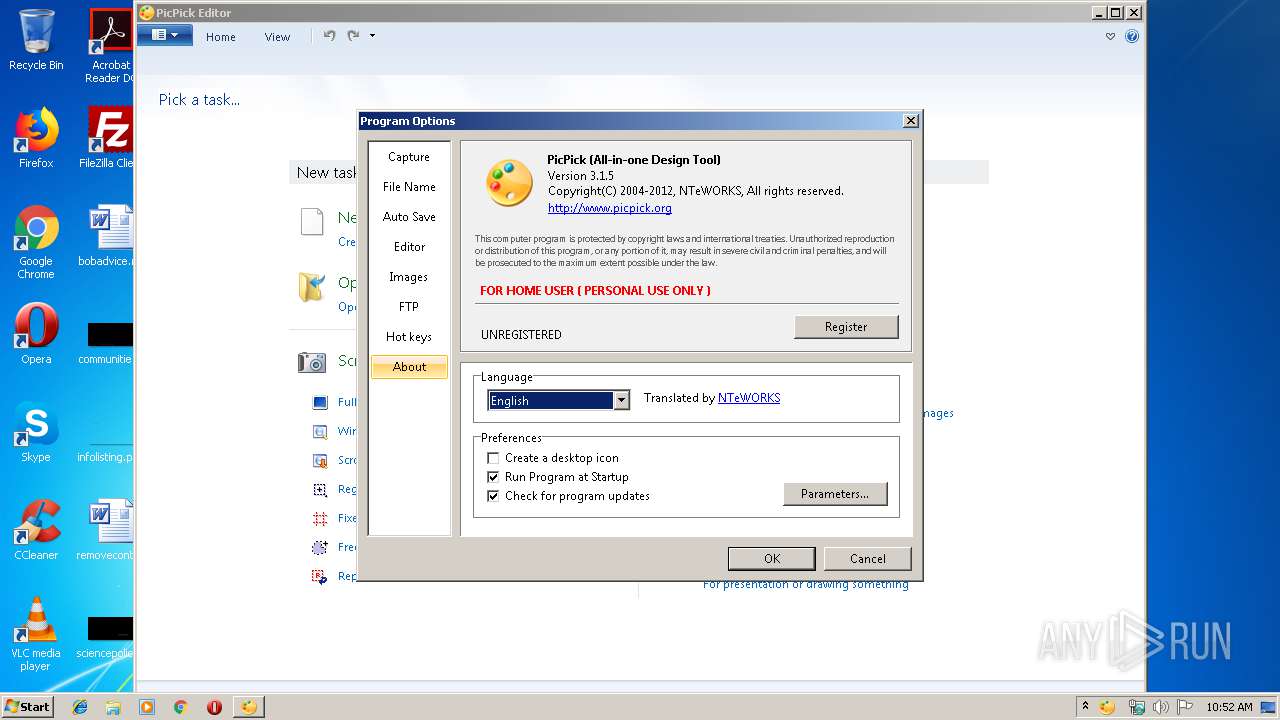
| 2240 | "C:\Program Files\PicPick\picpick.exe" | C:\Program Files\PicPick\picpick.exe | — | explorer.exe | |||||||||||
User: admin Company: NTeWORKS Integrity Level: MEDIUM Description: PicPick Exit code: 0 Version: 3.1.3.0 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\PicPick\picpick.exe" | C:\Program Files\PicPick\picpick.exe | explorer.exe | ||||||||||||
User: admin Company: NTeWORKS Integrity Level: MEDIUM Description: PicPick Exit code: 0 Version: 3.1.3.0 Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\picpick_inst.exe" | C:\Users\admin\AppData\Local\Temp\picpick_inst.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
531
Read events
448
Write events
83
Delete events
0
Modification events
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (792) picpick_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\picpick_inst_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
9
Suspicious files
2
Text files
158
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 792 | picpick_inst.exe | C:\Program Files\PicPick\license.txt | text | |
MD5:— | SHA256:— | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Temp\nsdA796.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 792 | picpick_inst.exe | C:\Program Files\PicPick\picpick.exe | executable | |
MD5:— | SHA256:— | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Temp\nsdA796.tmp\xml.dll | executable | |
MD5:42DF1FBAA87567ADF2B4050805A1A545 | SHA256:E900FCB9D598643EB0EE3E4005DA925E73E70DBAA010EDC4473E99EA0638B845 | |||
| 792 | picpick_inst.exe | C:\Program Files\PicPick\language\Chinese Traditional.ini | text | |
MD5:— | SHA256:— | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Temp\nsdA796.tmp\KillProcDLL.dll | executable | |
MD5:83142EAC84475F4CA889C73F10D9C179 | SHA256:AE2F1658656E554F37E6EAC896475A3862841A18FFC6FAD2754E2D3525770729 | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Temp\nsdA796.tmp\InstallOptions.dll | executable | |
MD5:325B008AEC81E5AAA57096F05D4212B5 | SHA256:C9CD5C9609E70005926AE5171726A4142FFBCCCC771D307EFCD195DAFC1E6B4B | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\picpick_inst_20[1].html | xml | |
MD5:— | SHA256:— | |||
| 792 | picpick_inst.exe | C:\Users\admin\AppData\Local\Temp\nsdA796.tmp\InetLoad.dll | executable | |
MD5:994669C5737B25C26642C94180E92FA2 | SHA256:BF01A1F272E0DAF82DF3407690B646E0FF6B2C562E36E47CF177EDA71CCB6F6C | |||
| 792 | picpick_inst.exe | C:\Program Files\PicPick\language\Croatian.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
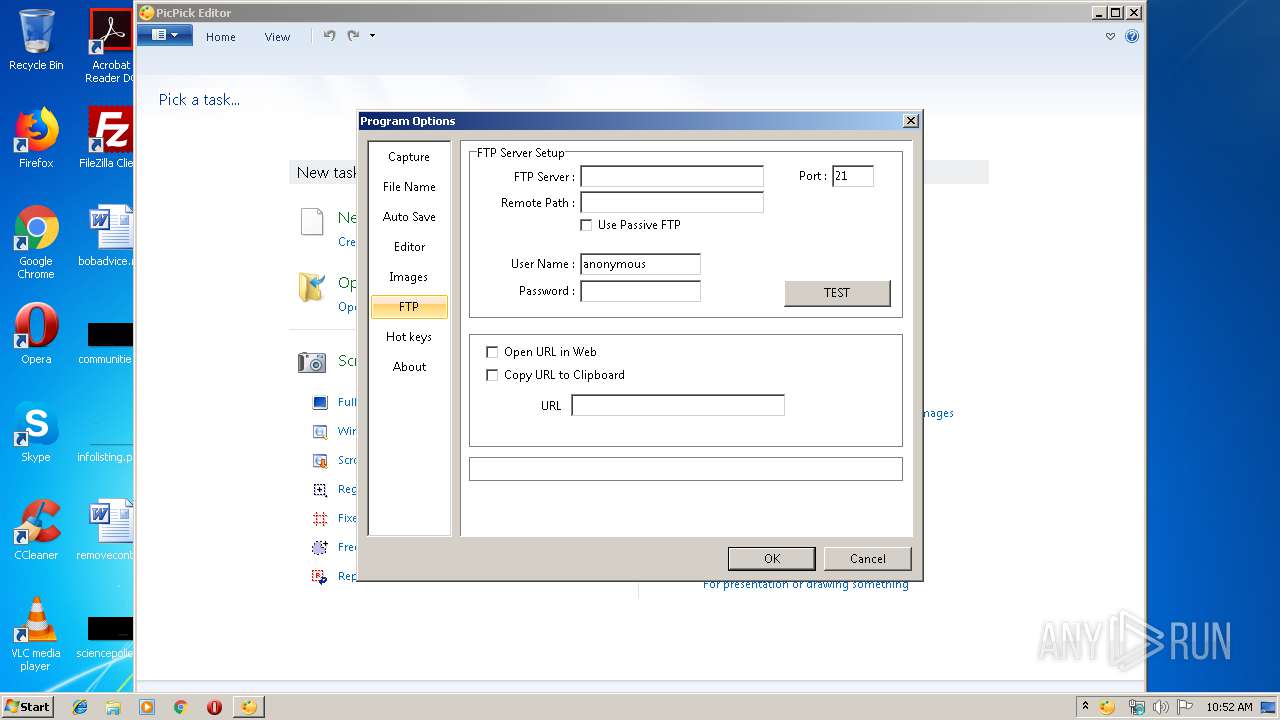
2612 | picpick.exe | GET | — | 192.99.63.220:80 | http://www.picpick.org/update.html?v=3150&l=0409&t=English&3793171 | CA | — | — | suspicious |
792 | picpick_inst.exe | GET | 200 | 192.99.63.220:80 | http://www.picpick.org/picpick_inst_20.html | CA | xml | 93 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
792 | picpick_inst.exe | 192.99.63.220:80 | www.picpick.org | OVH SAS | CA | suspicious |
2612 | picpick.exe | 192.99.63.220:80 | www.picpick.org | OVH SAS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.picpick.org |
| suspicious |
Threats
1 ETPRO signatures available at the full report