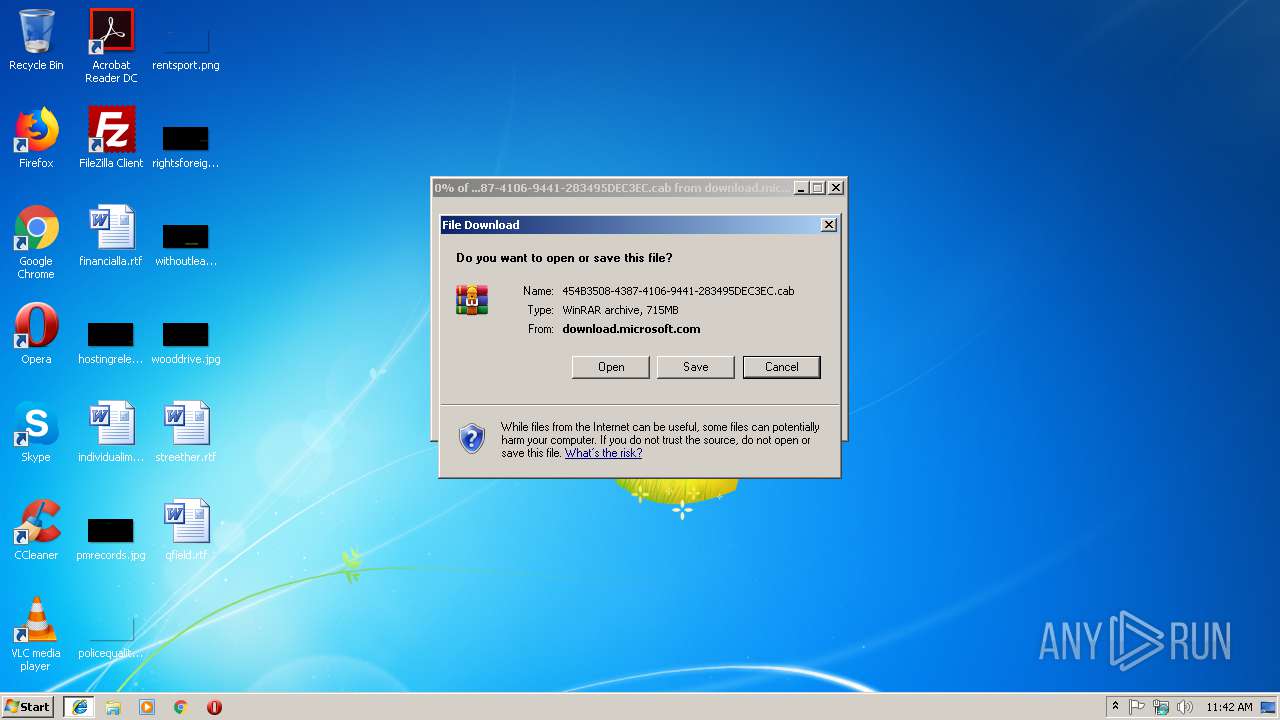
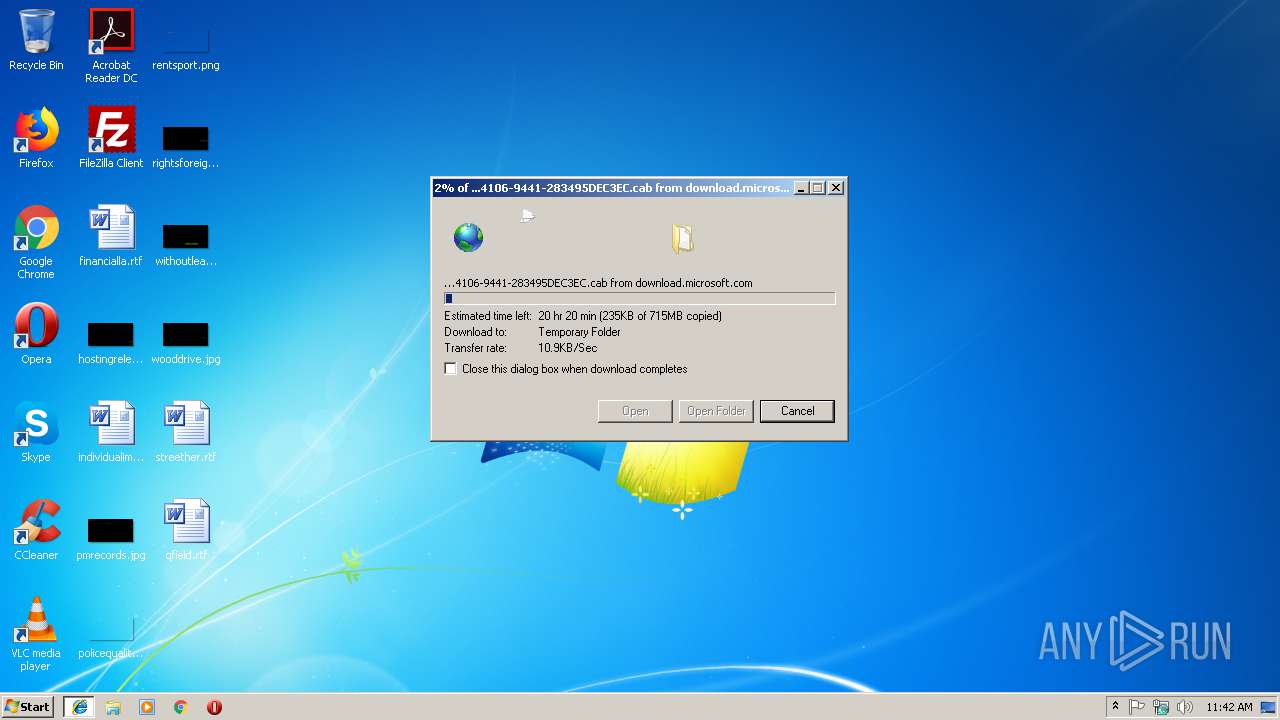
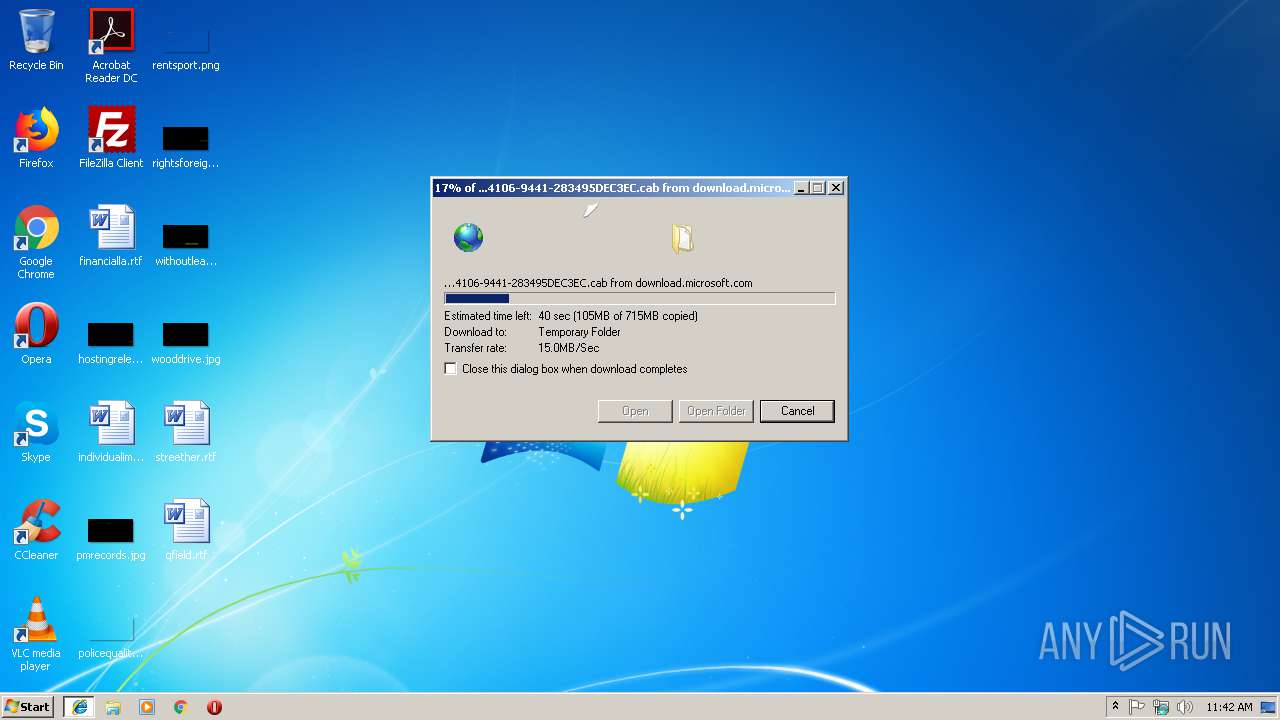
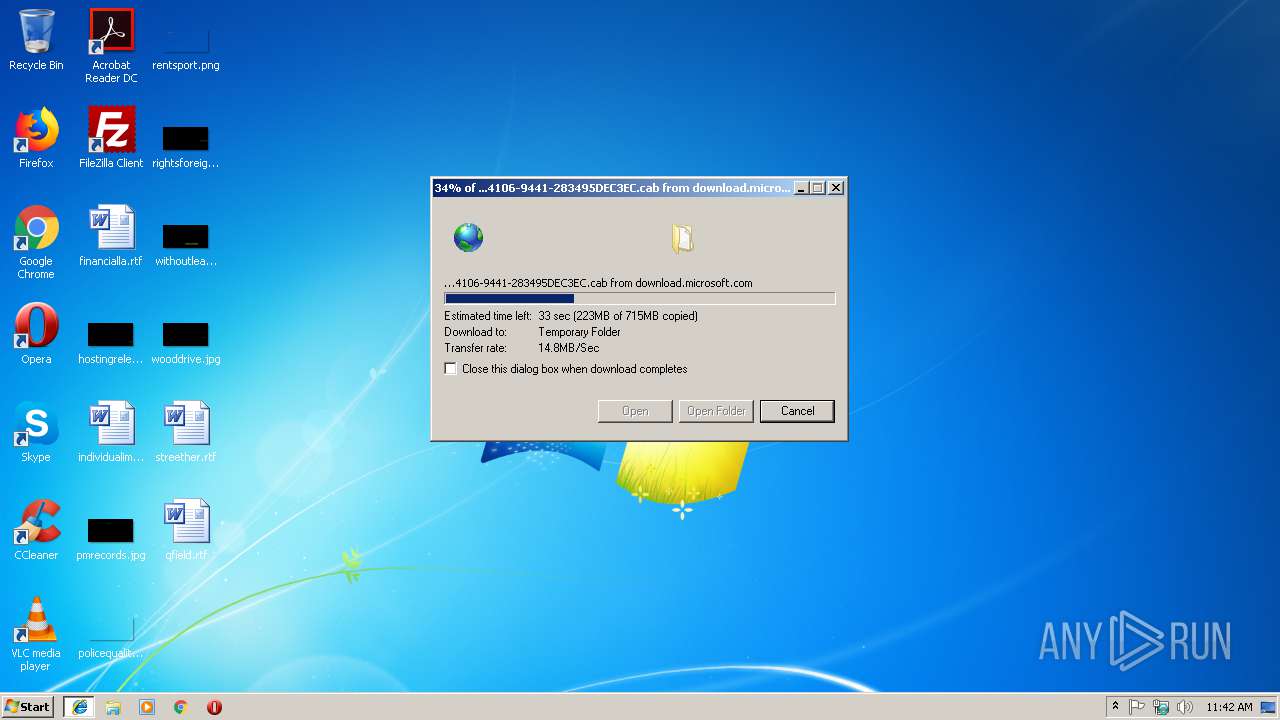
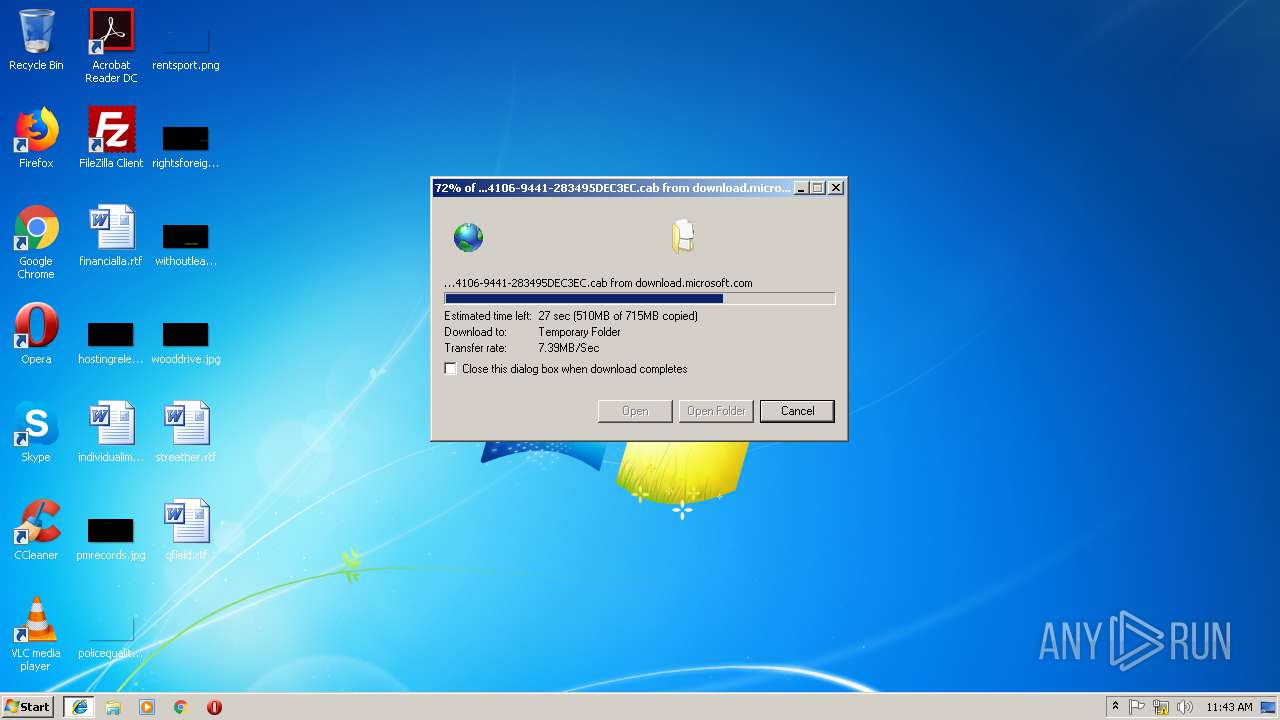
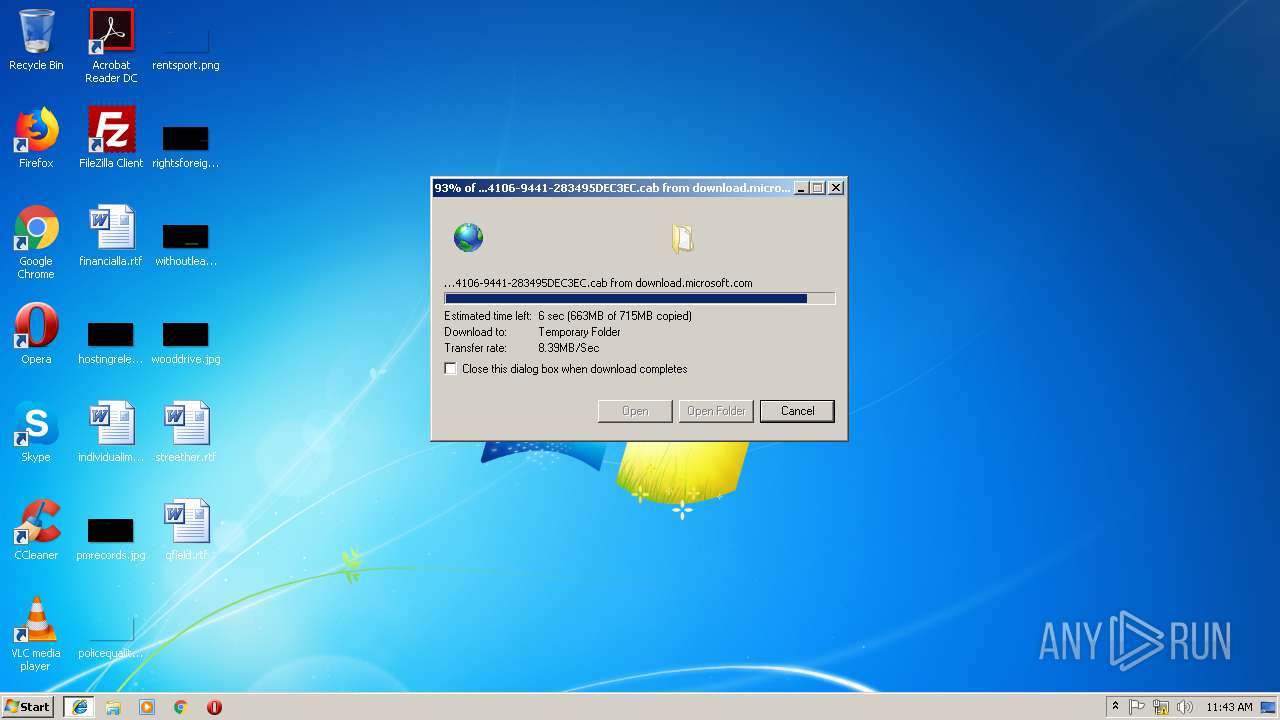
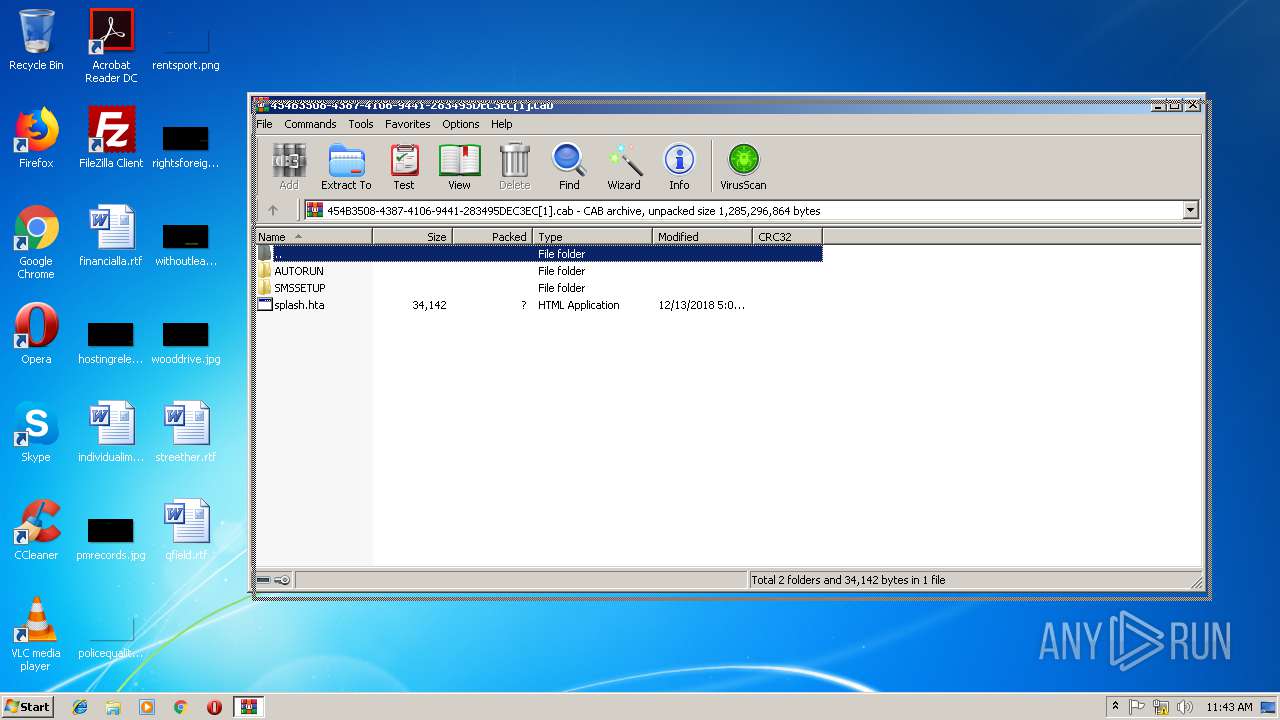
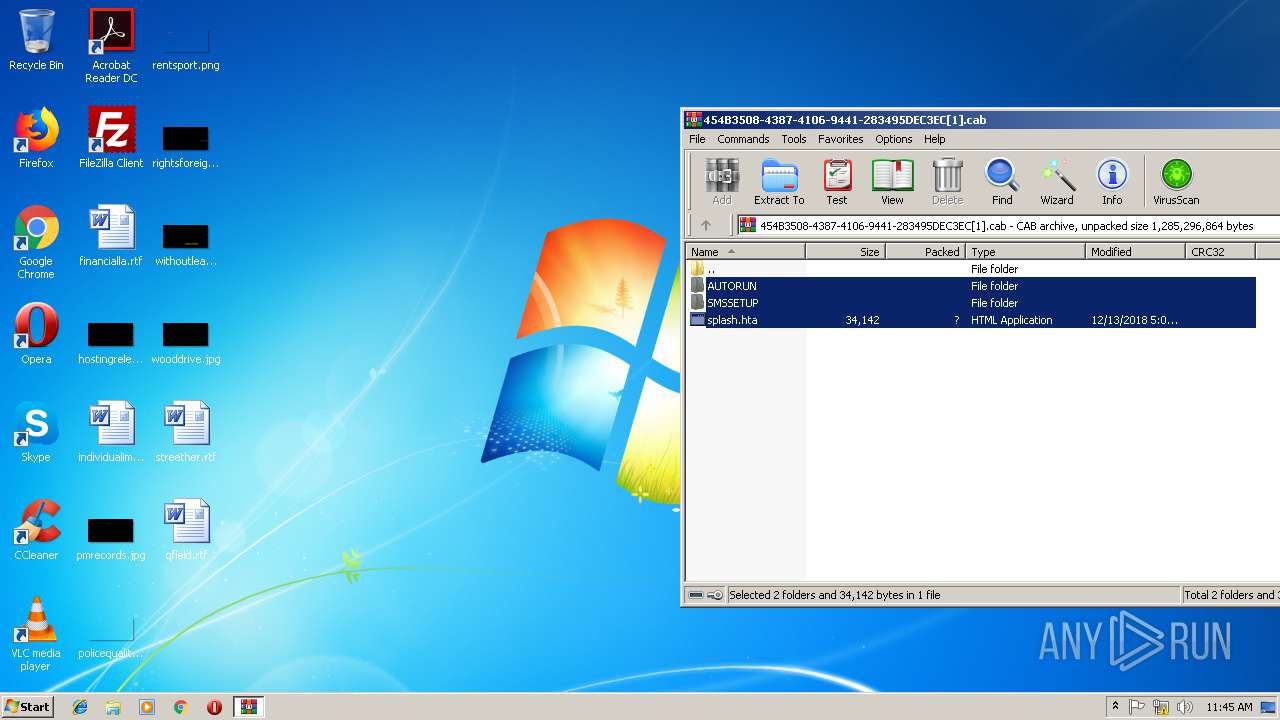
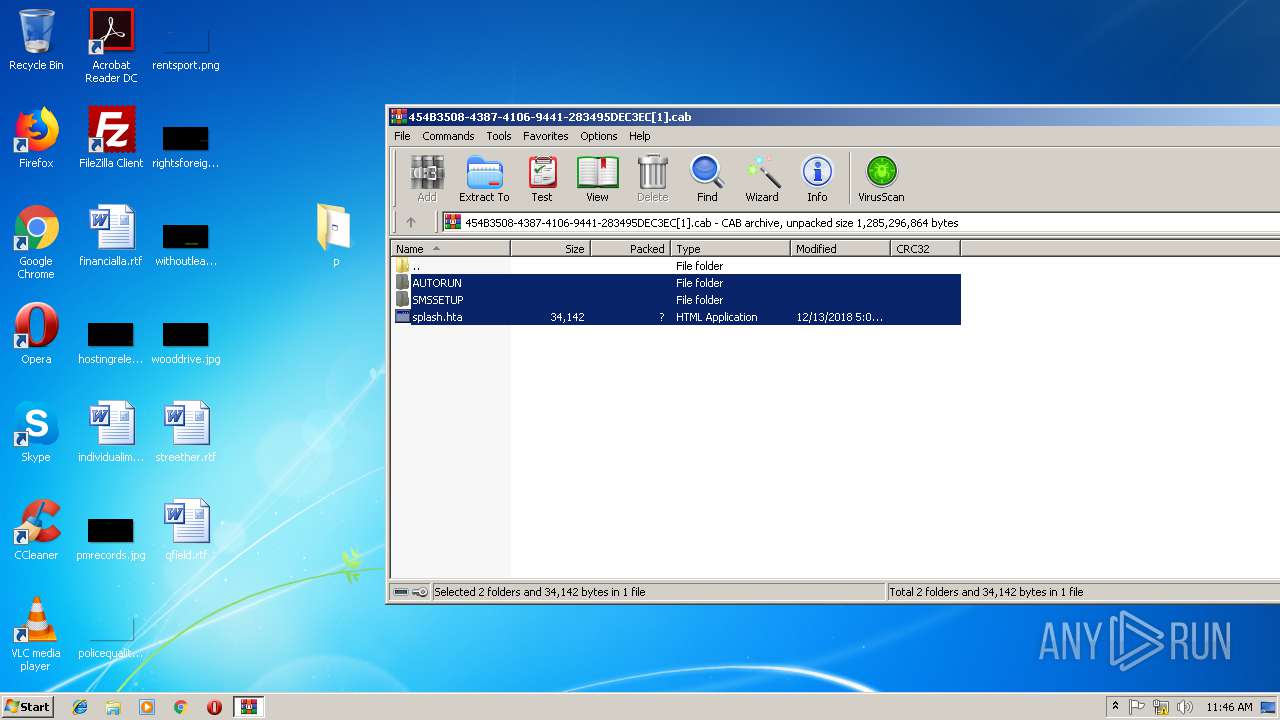
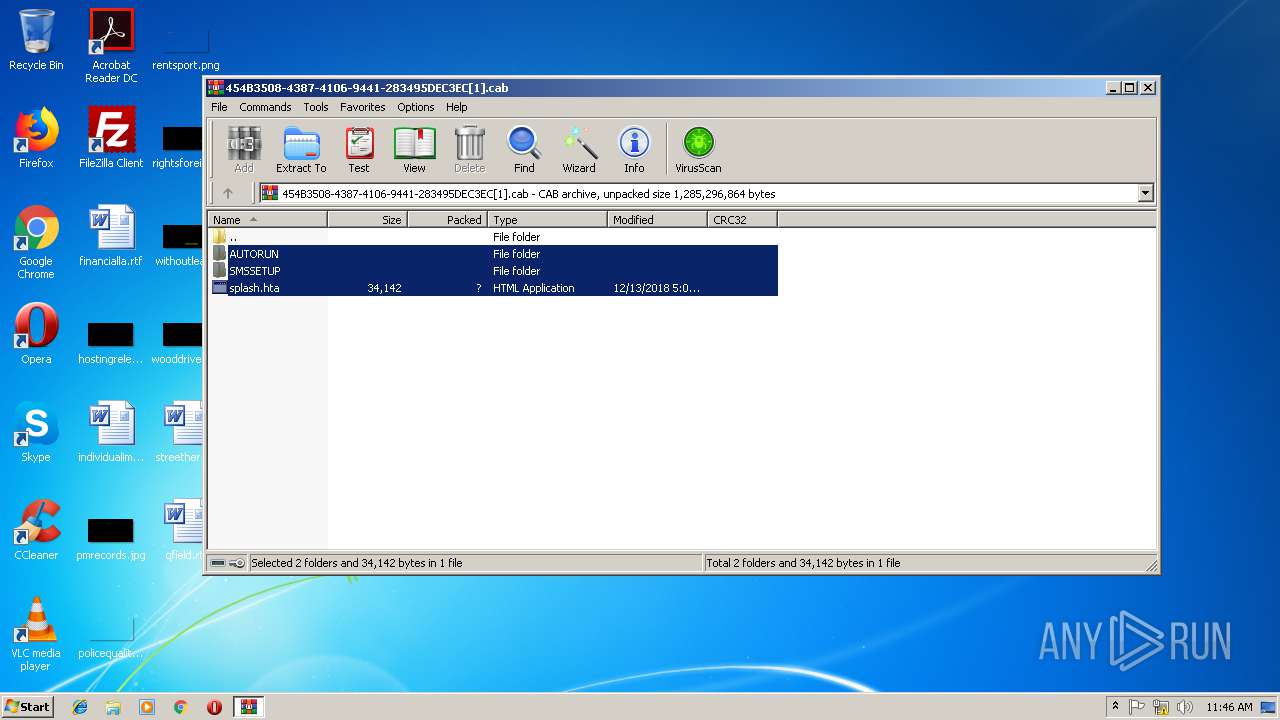
| URL: | http://download.microsoft.com/download/2/B/3/2B3F17E5-C934-4D0C-A3BB-E1FD765A05B0/454B3508-4387-4106-9441-283495DEC3EC.cab |
| Full analysis: | https://app.any.run/tasks/83a6009f-7ab1-4d7c-be20-86fd9a9633fc |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2018, 11:41:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4B3926BB996A02B1EC4596BE3D9179FC |
| SHA1: | A3DFAF3A034A18E0C5C871F379B26CB293CA4284 |
| SHA256: | EF56BAF5139EC3CBC8ADACCDC04CAF3E8ED3B7361FD67A0CE34102FCD8F152D1 |
| SSDEEP: | 3:N1KaKElyKRtR8LXbWK3WPgkcWshtnnIRdgTyPNR4UNmX:Ca5TD8vdWPHshtIRd6oJmX |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2344)
SUSPICIOUS
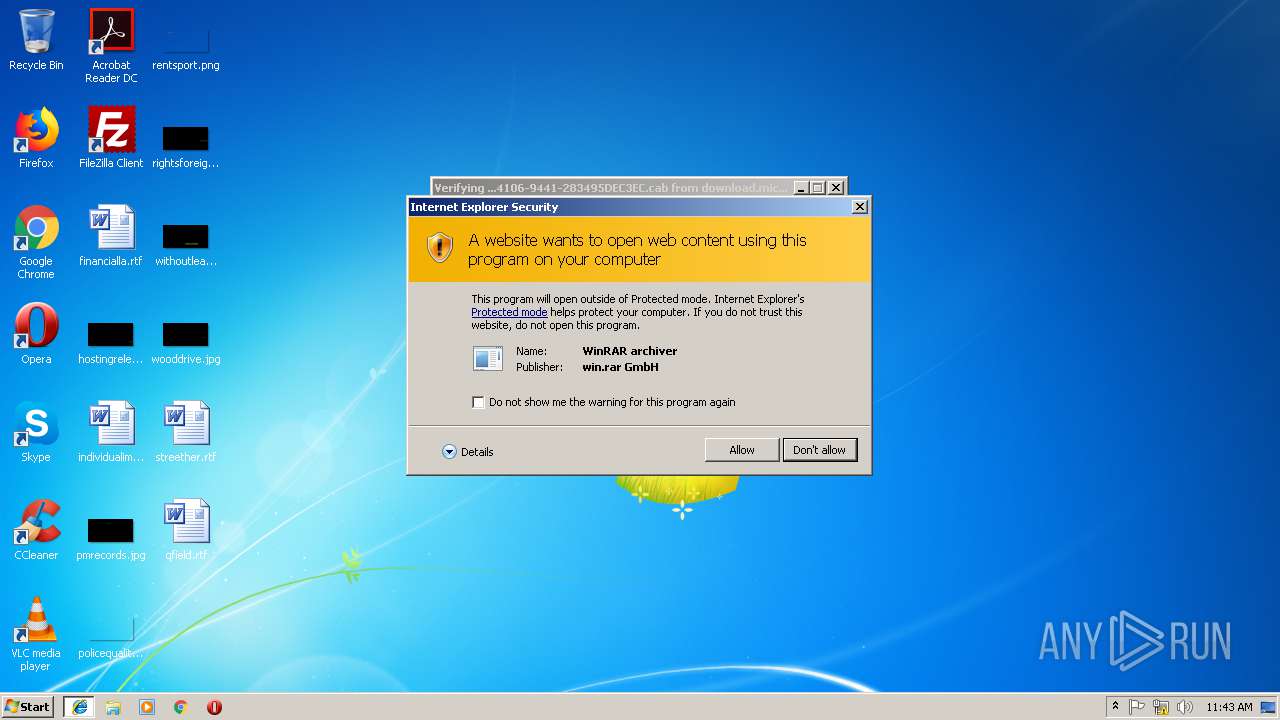
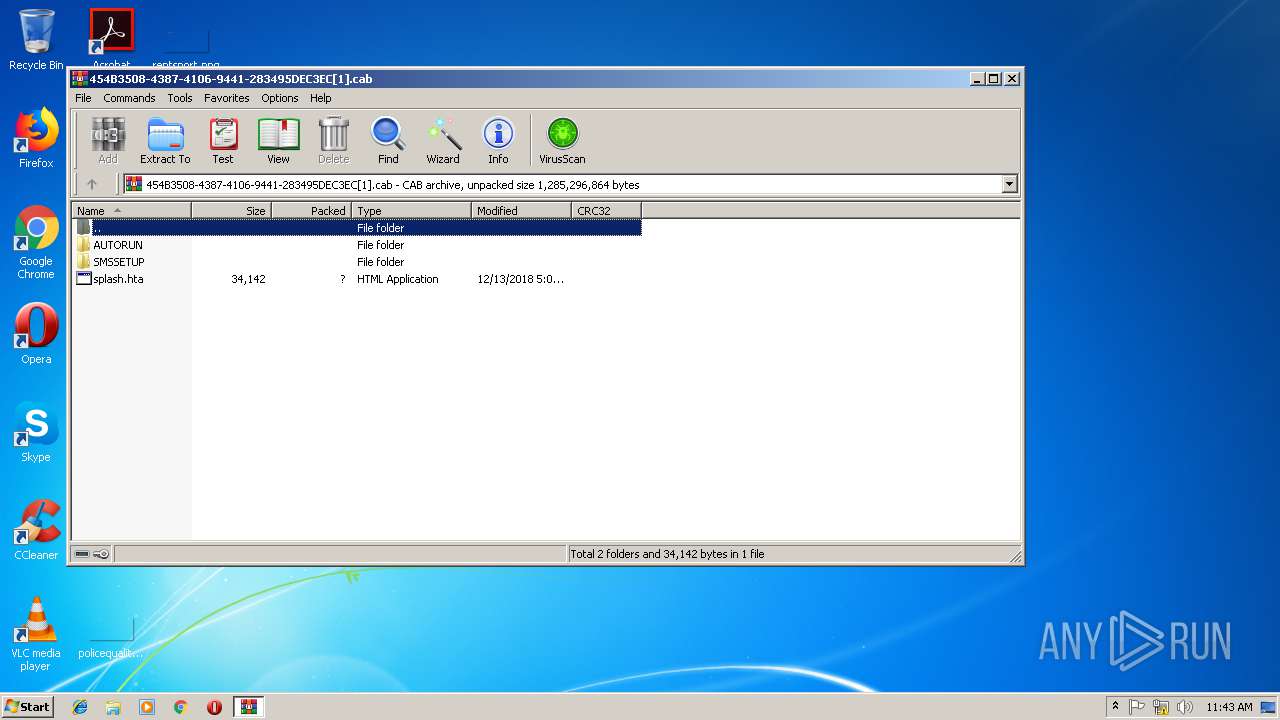
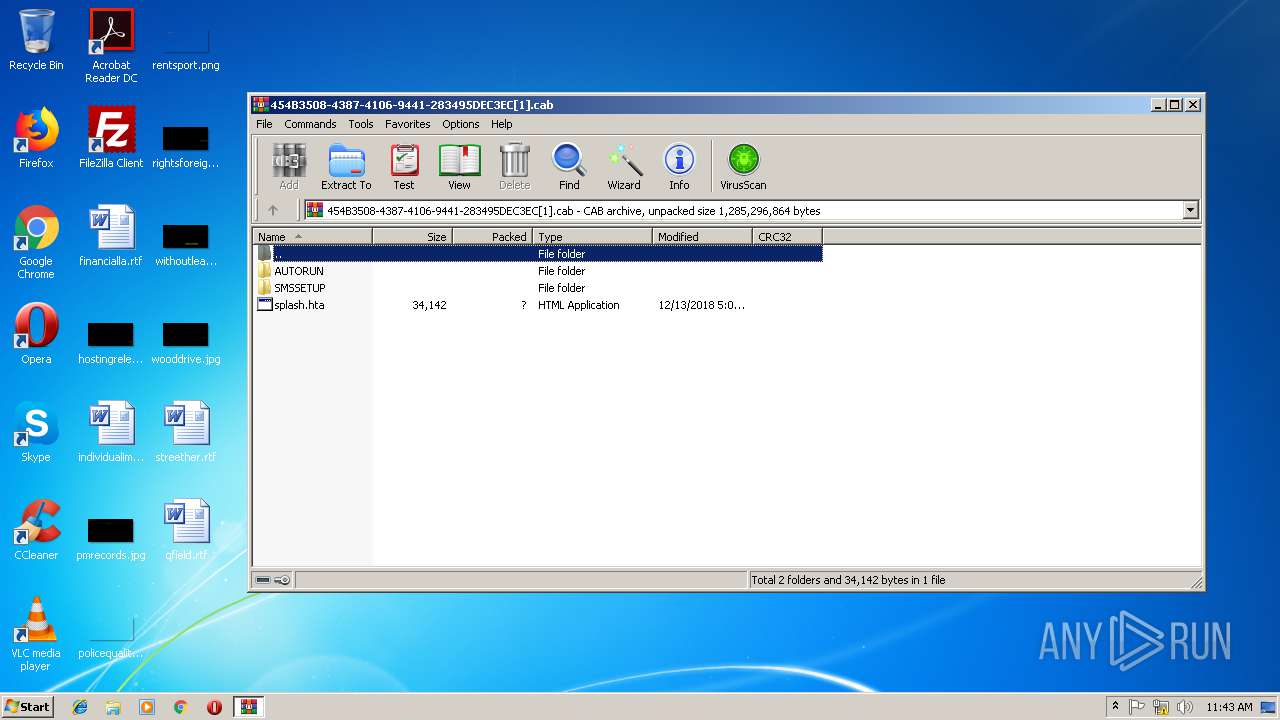
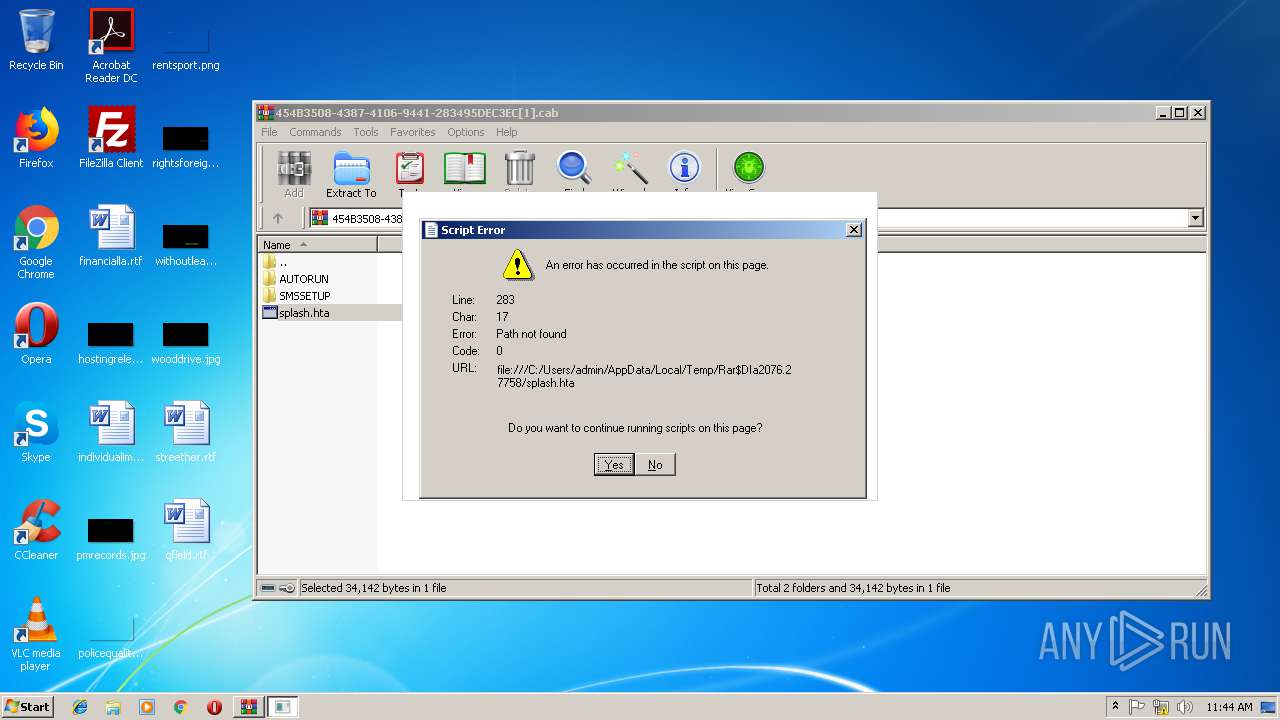
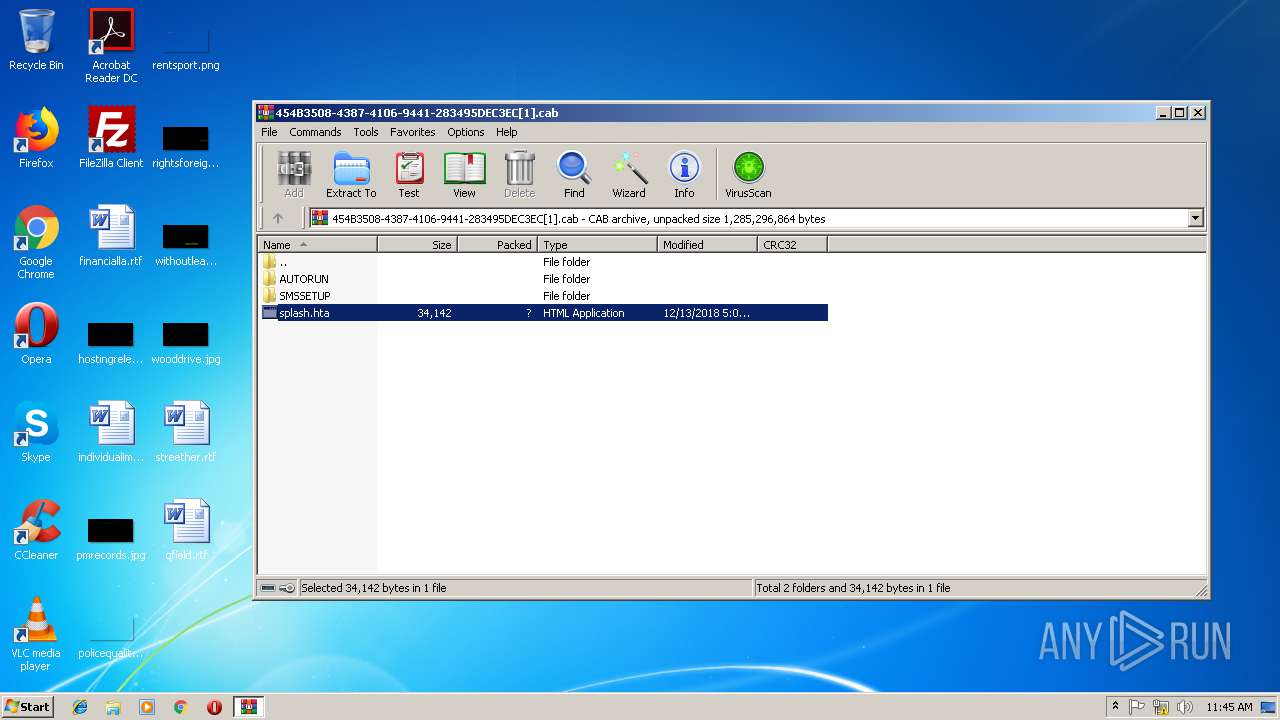
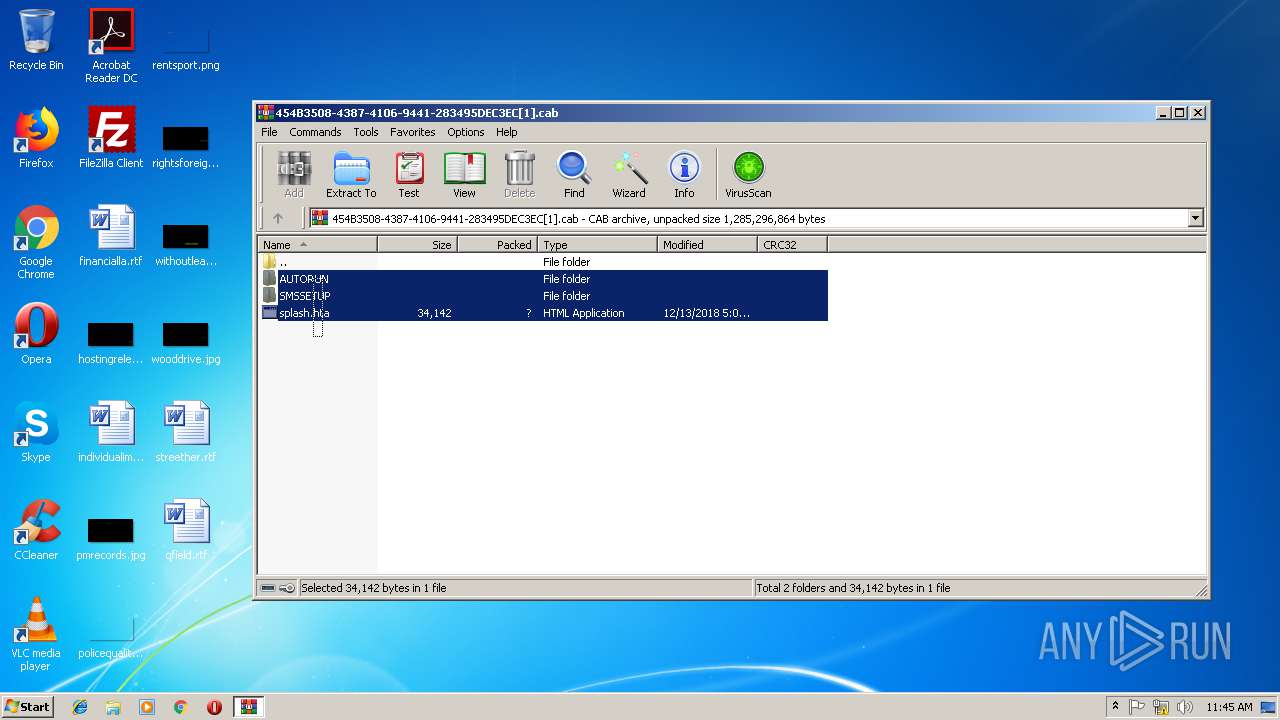
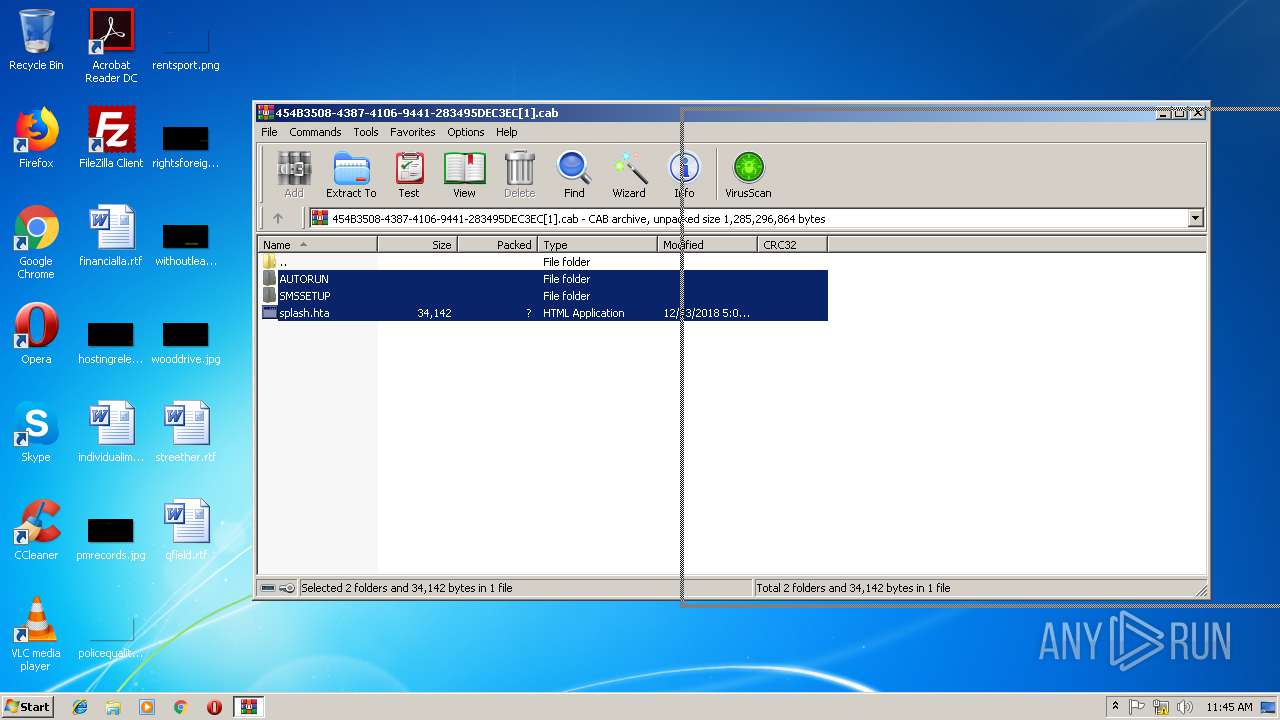
Starts MSHTA.EXE for opening HTA or HTMLS files
- WinRAR.exe (PID: 2076)
- mshta.exe (PID: 1796)
Application launched itself
- mshta.exe (PID: 1796)
Executable content was dropped or overwritten
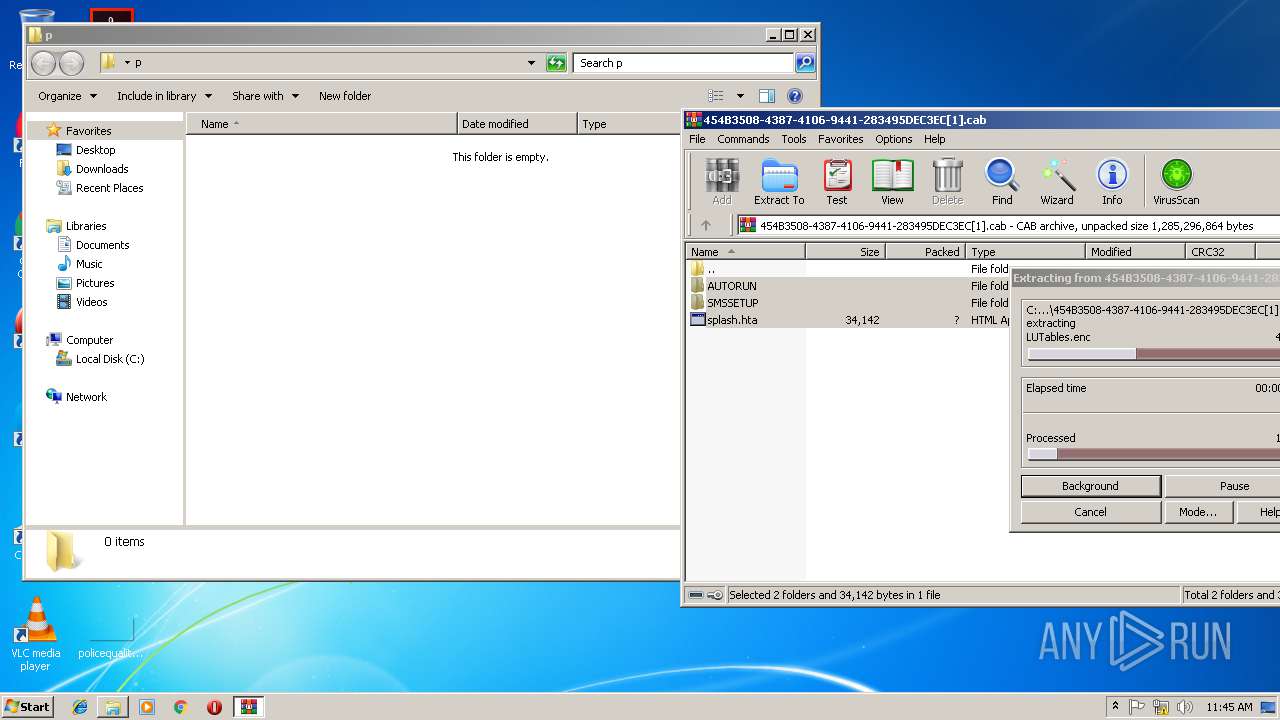
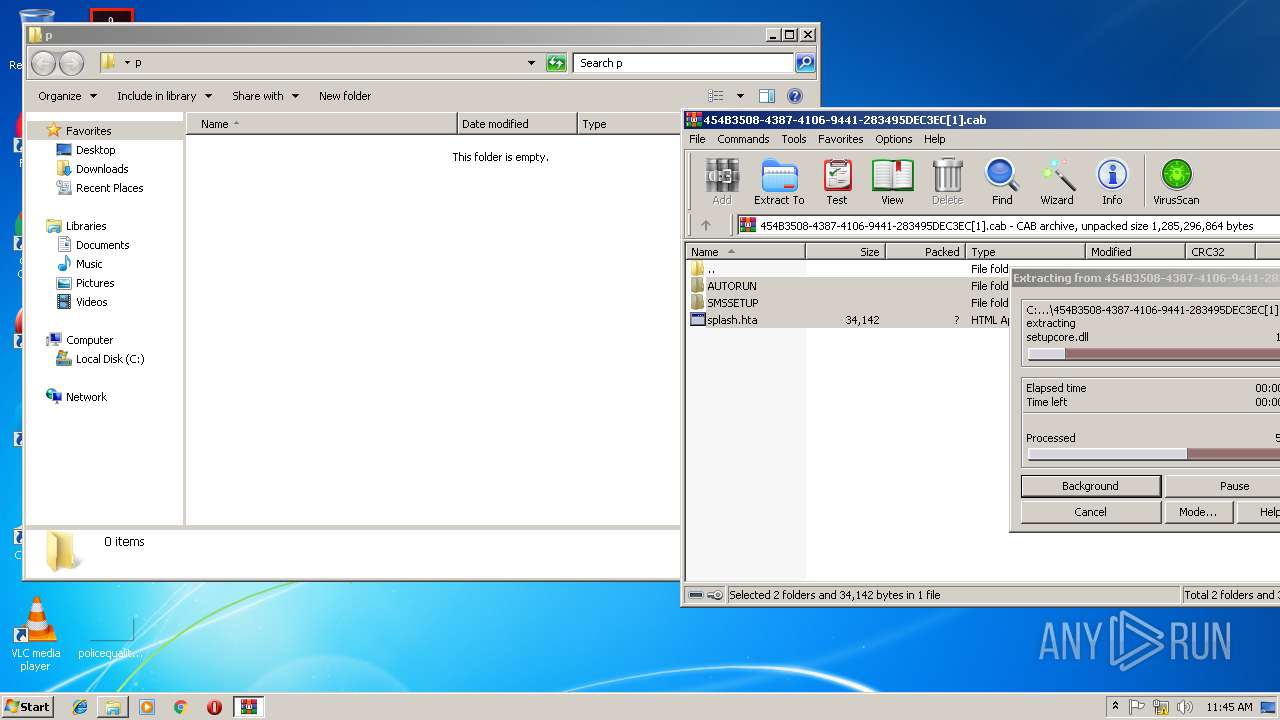
- WinRAR.exe (PID: 2076)
INFO
Application launched itself
- iexplore.exe (PID: 3008)
Reads settings of System Certificates
- iexplore.exe (PID: 3008)
Changes internet zones settings
- iexplore.exe (PID: 3008)
Creates files in the user directory
- iexplore.exe (PID: 3196)
Reads Internet Cache Settings
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 3196)
Reads internet explorer settings
- mshta.exe (PID: 3732)
- mshta.exe (PID: 1796)
- mshta.exe (PID: 1516)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
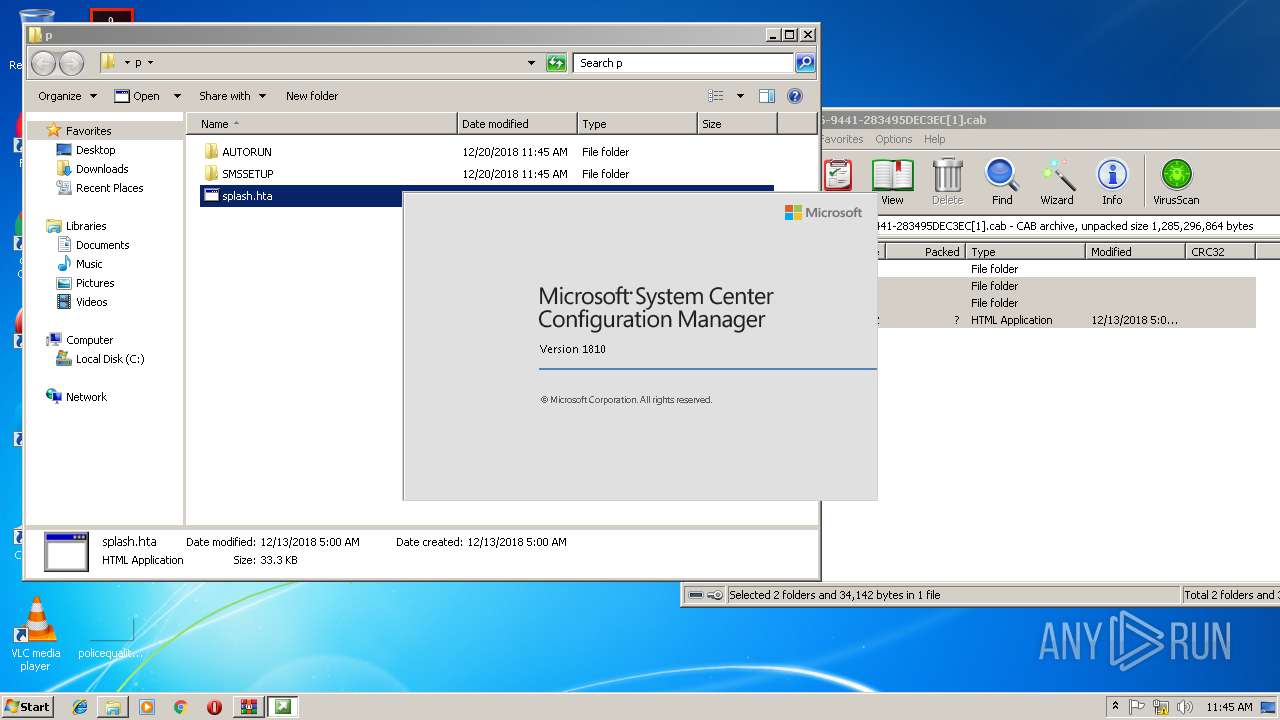
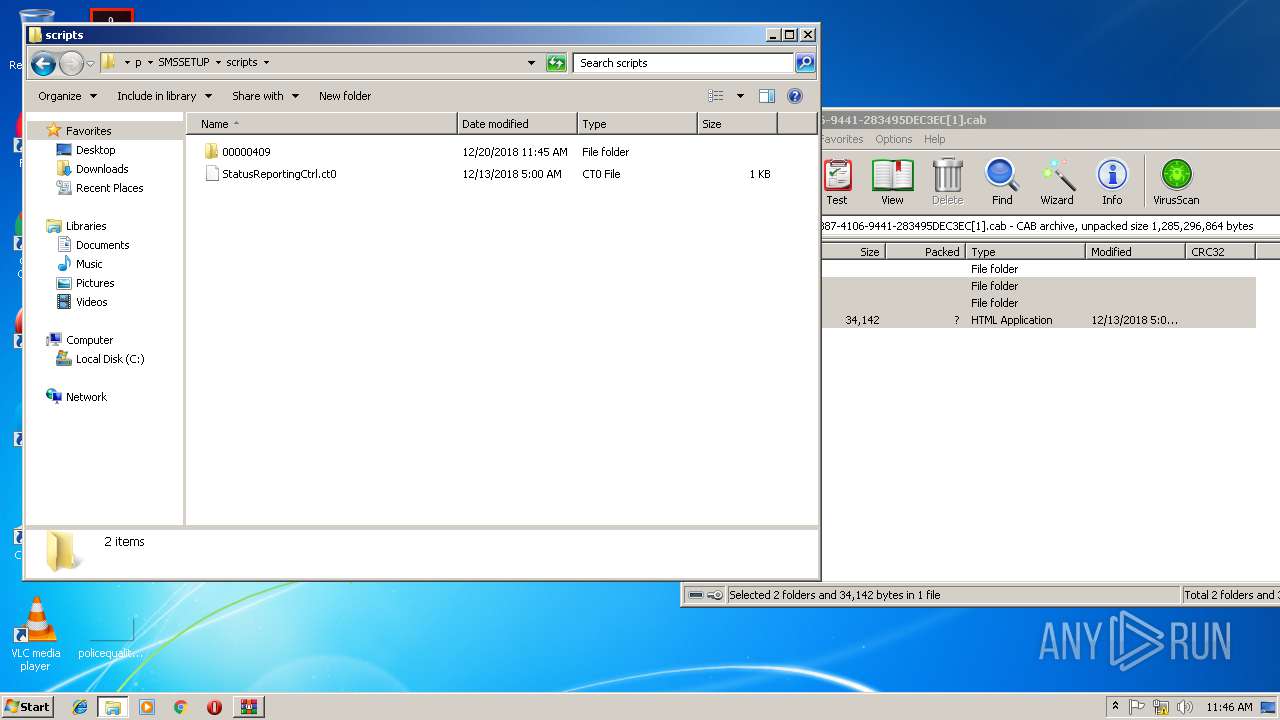
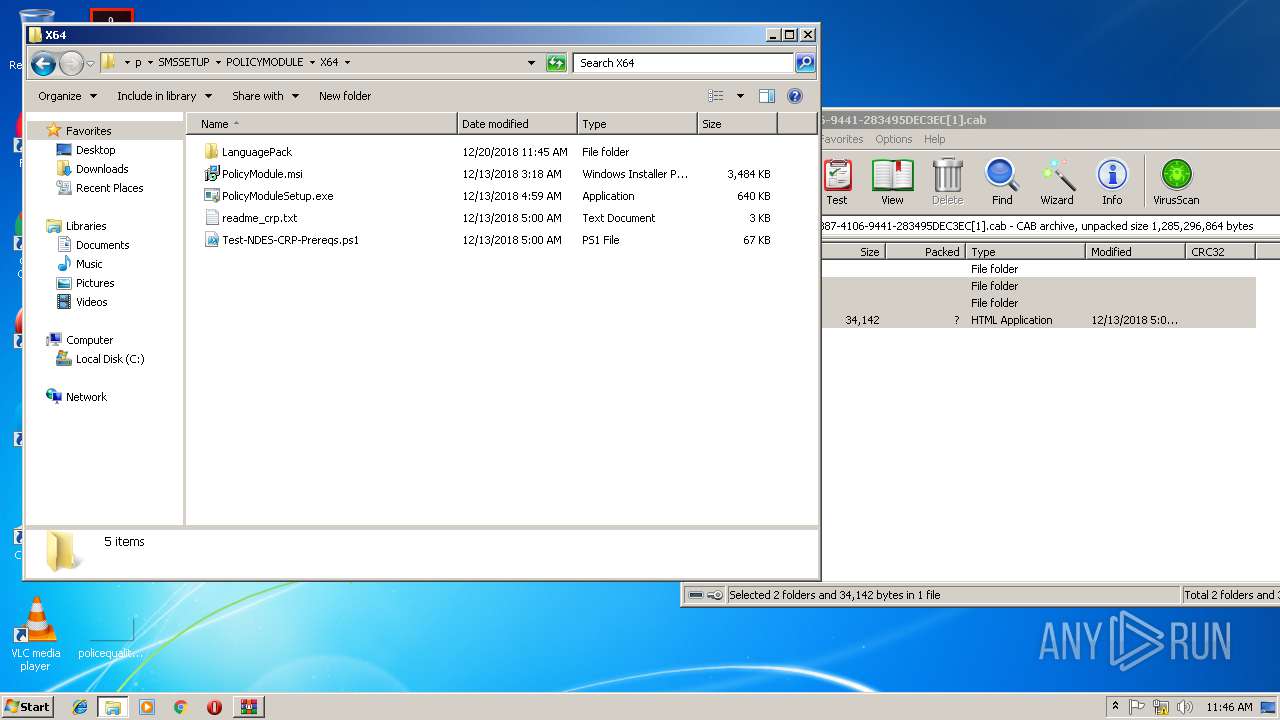
| 1516 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\p\SMSSETUP\BIN\X64\00000409\autorun.hta" | C:\Windows\System32\mshta.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
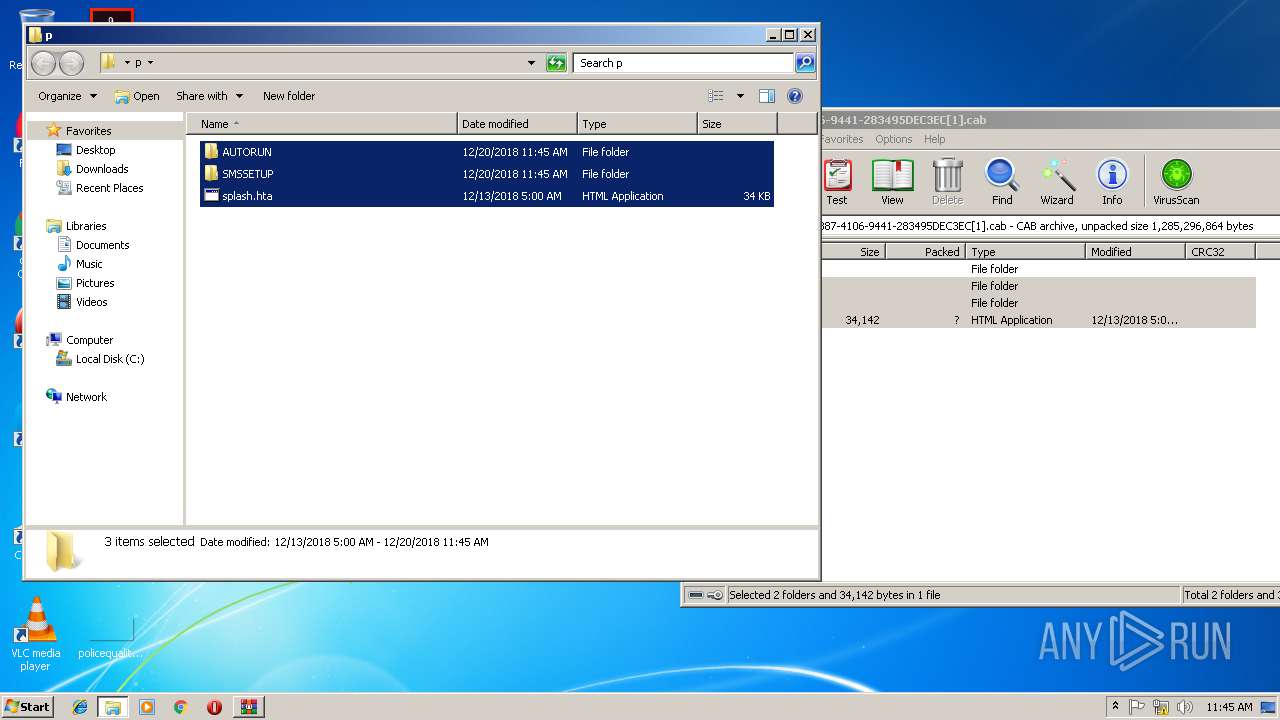
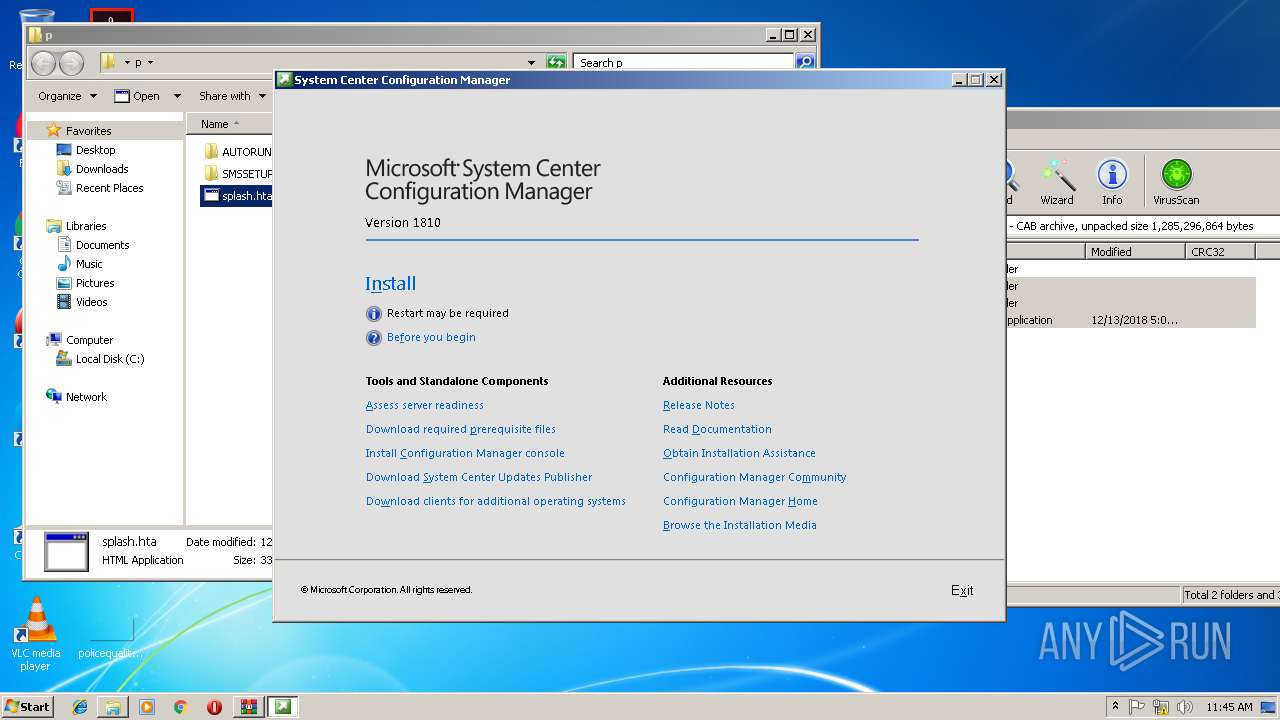
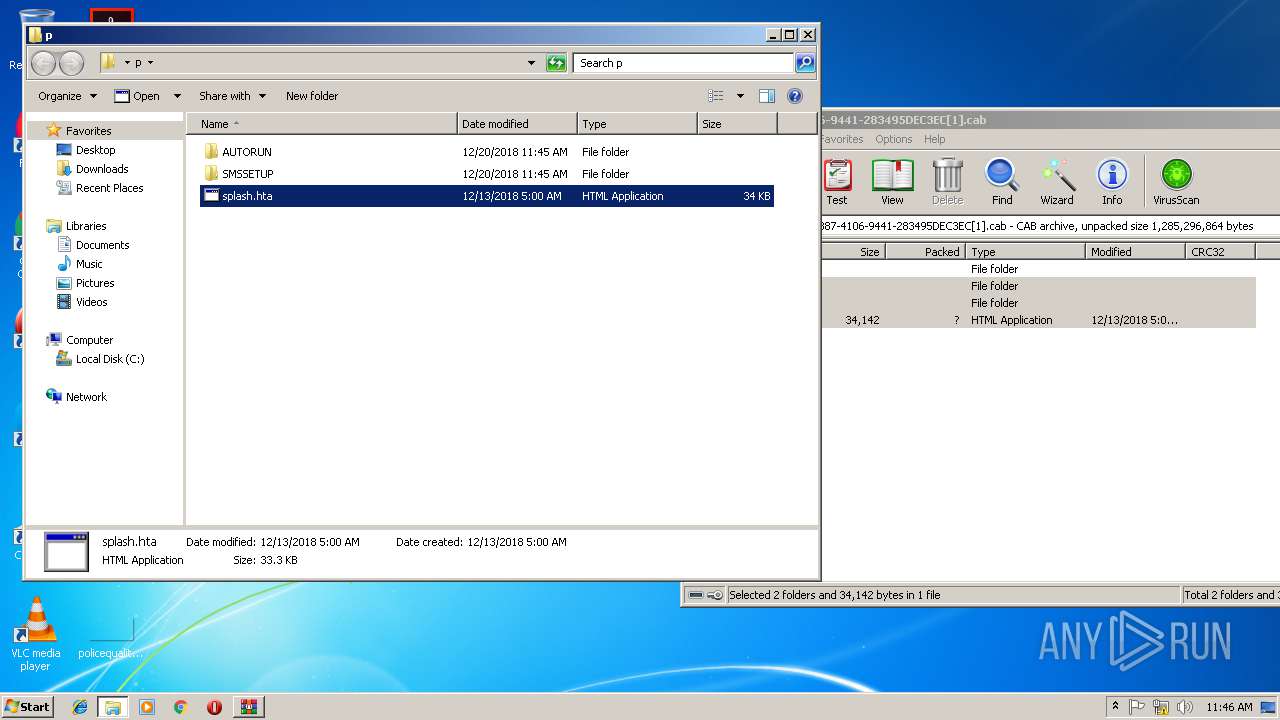
| 1796 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\p\splash.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
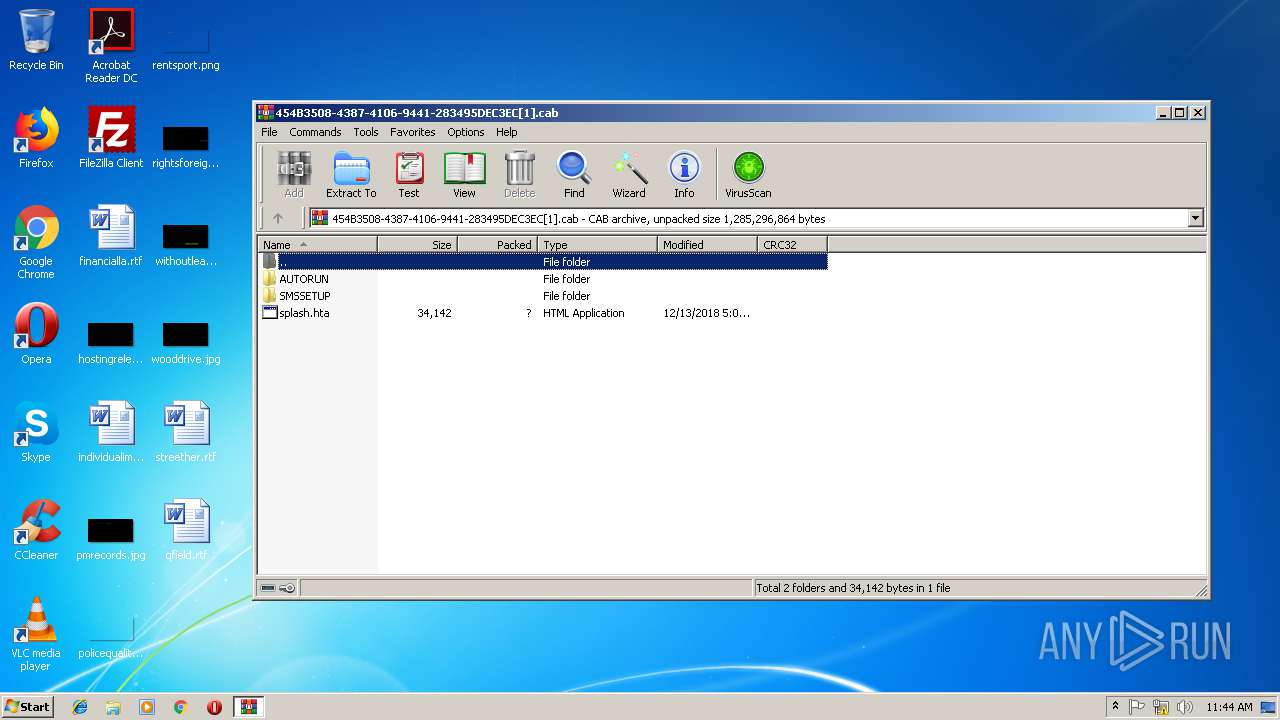
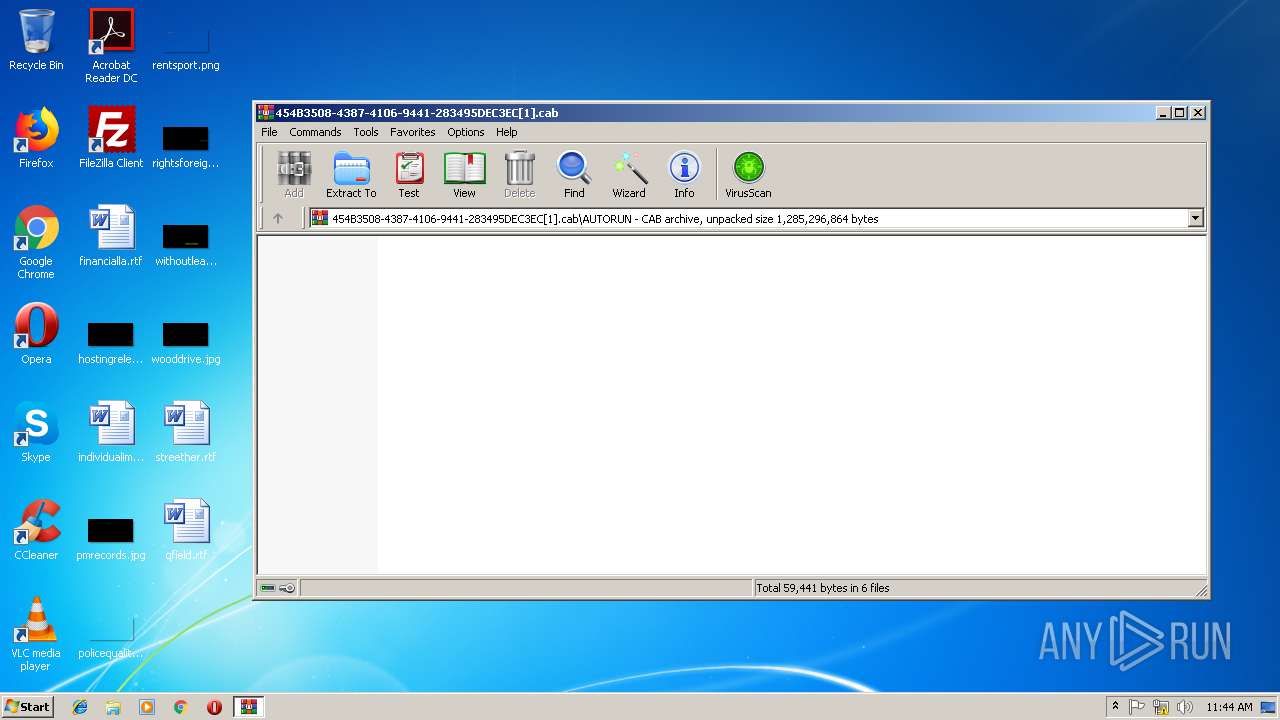
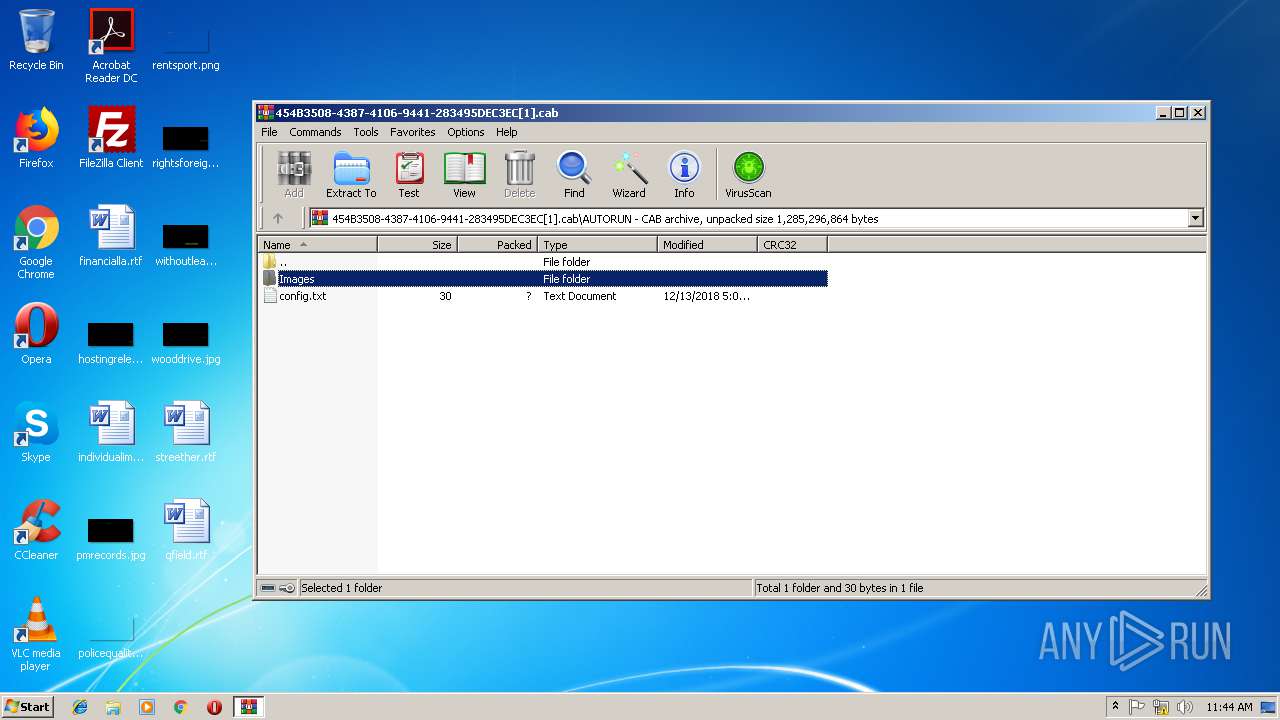
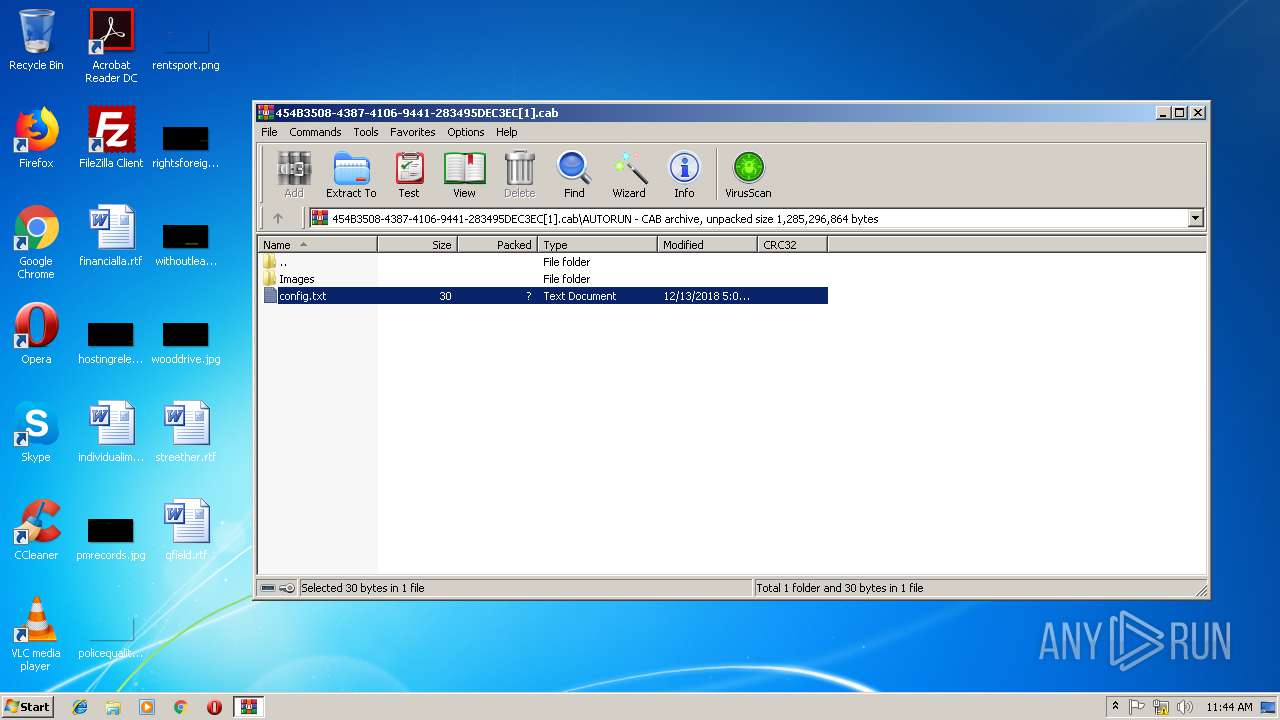
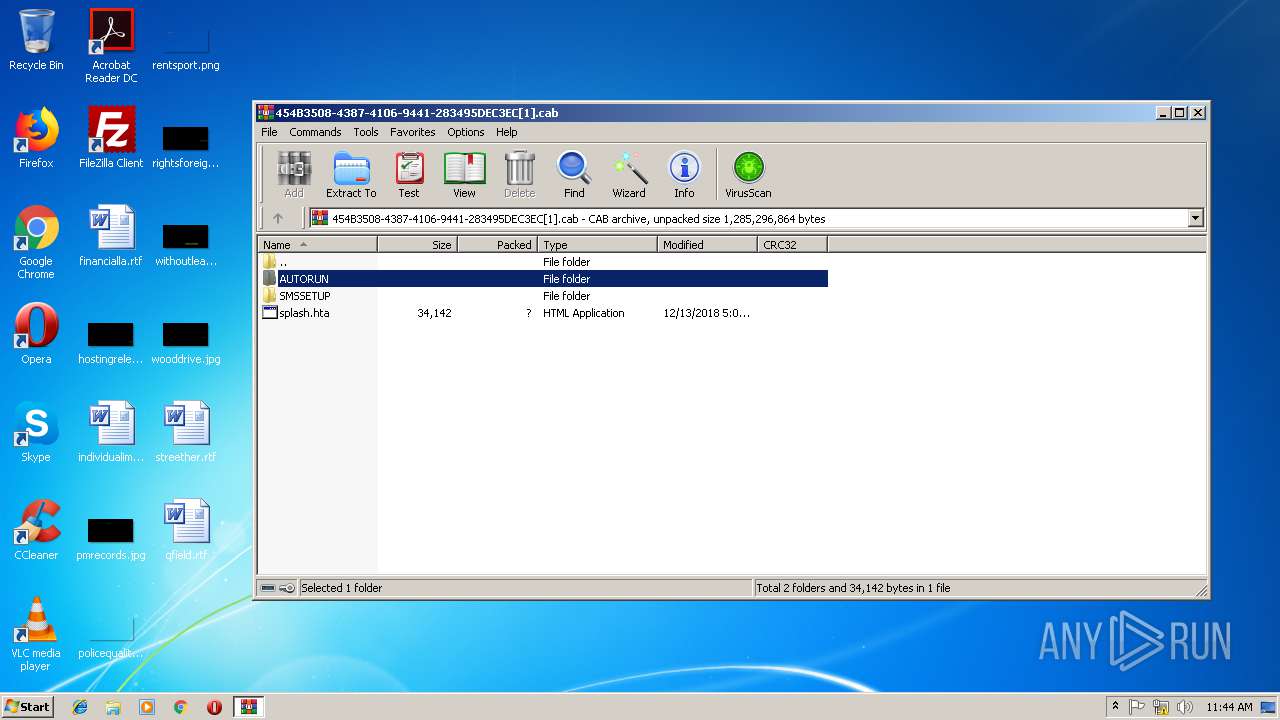
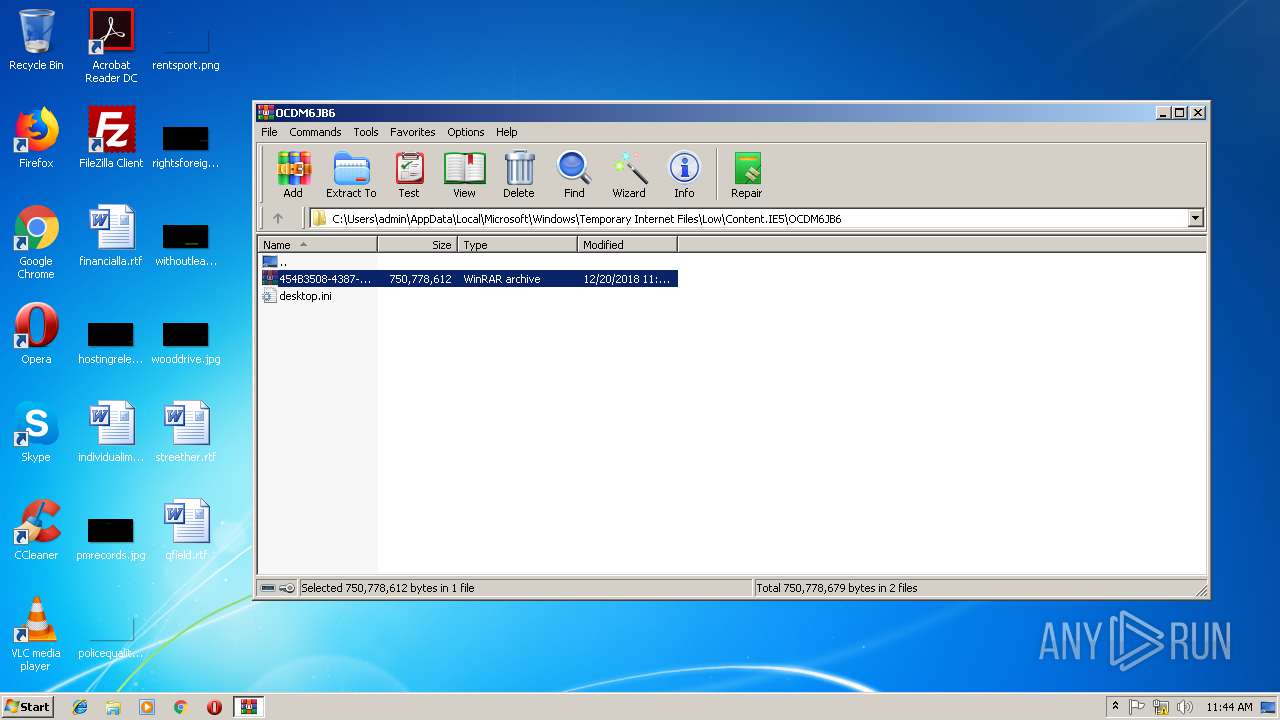
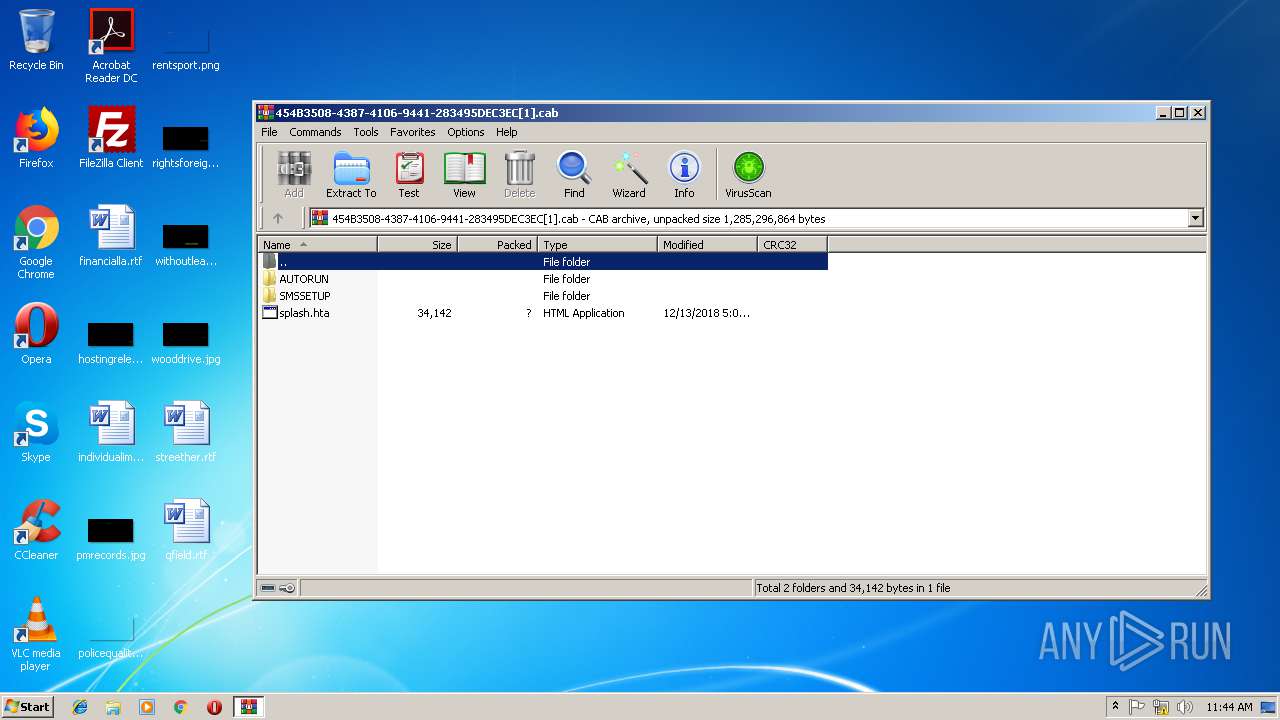
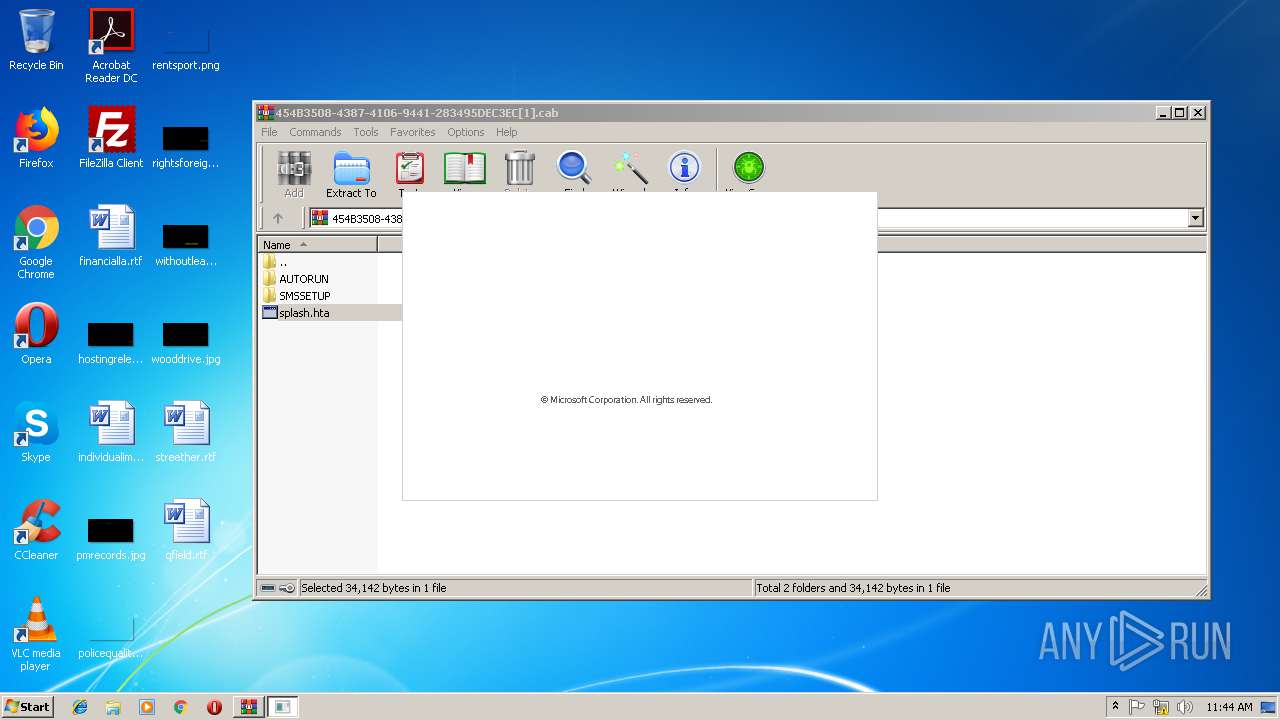
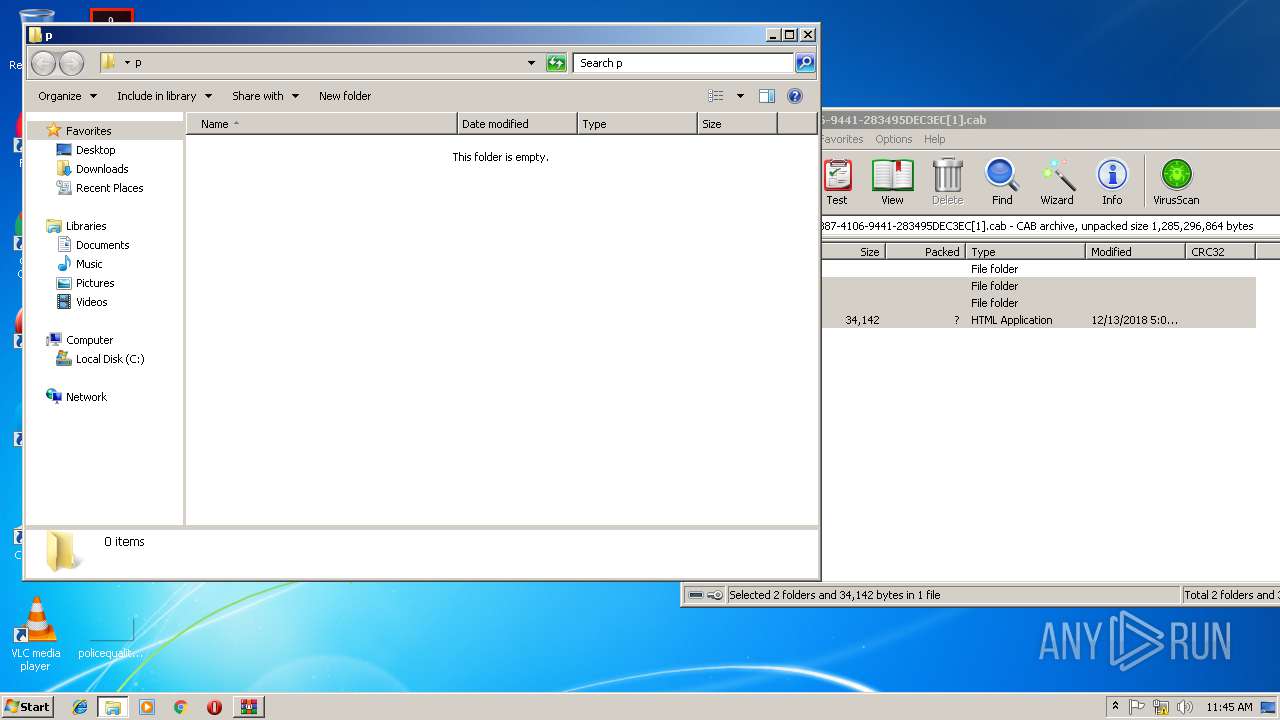
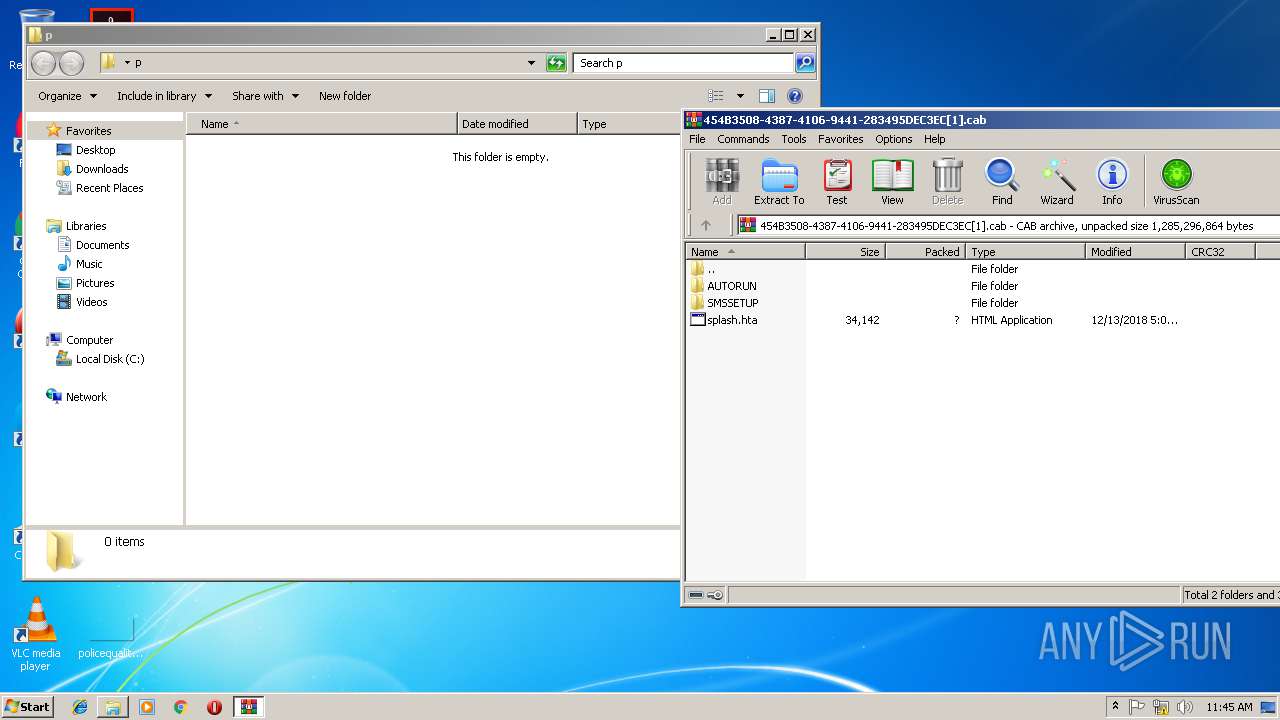
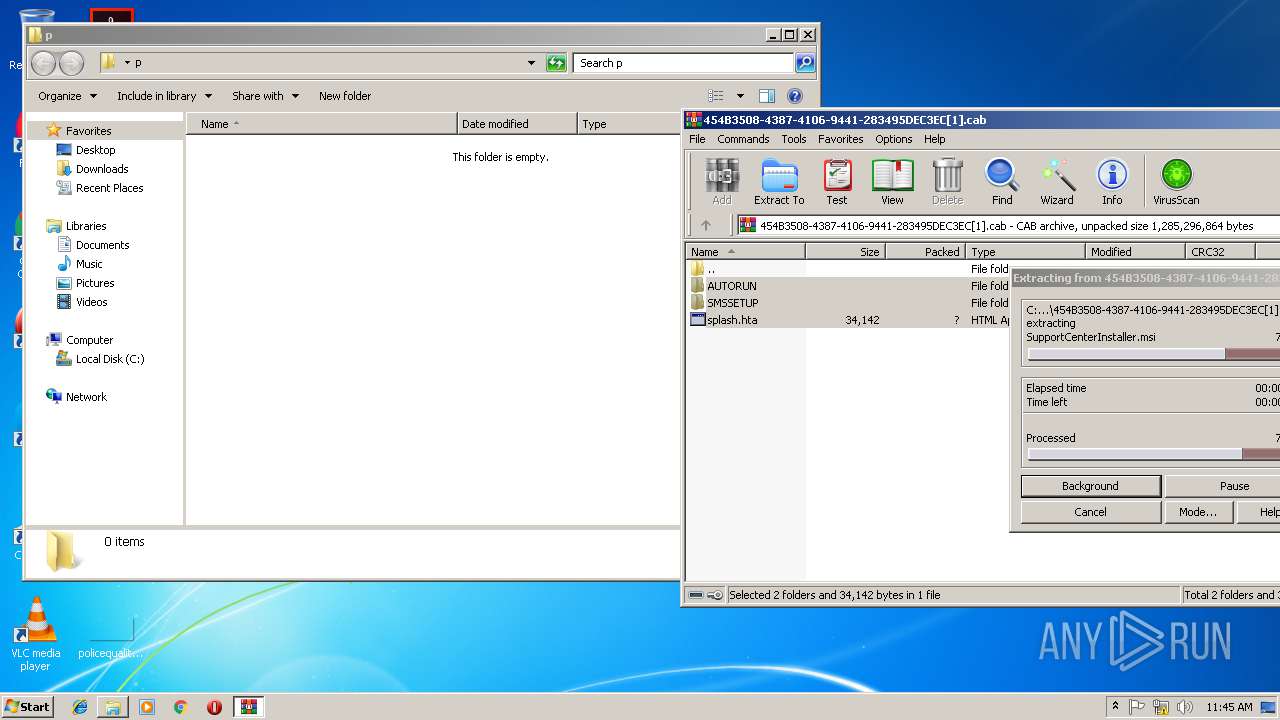
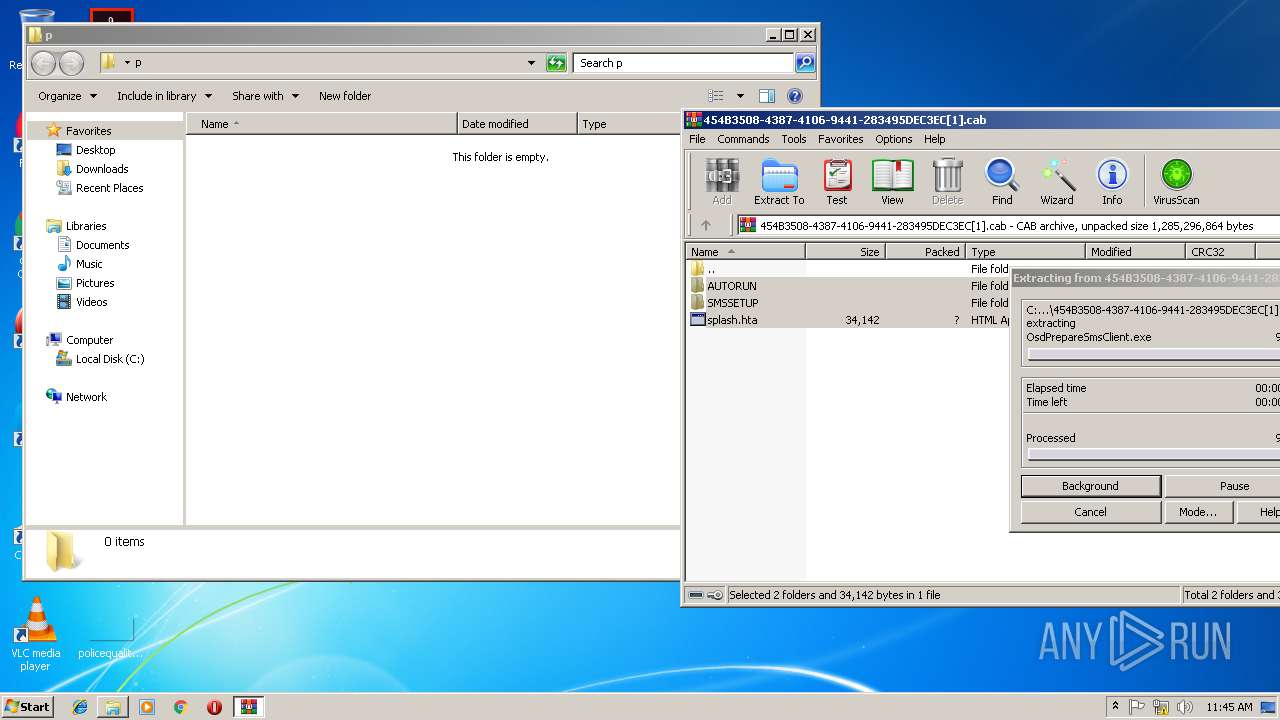
| 2076 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\454B3508-4387-4106-9441-283495DEC3EC[1].cab" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2344 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3008 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
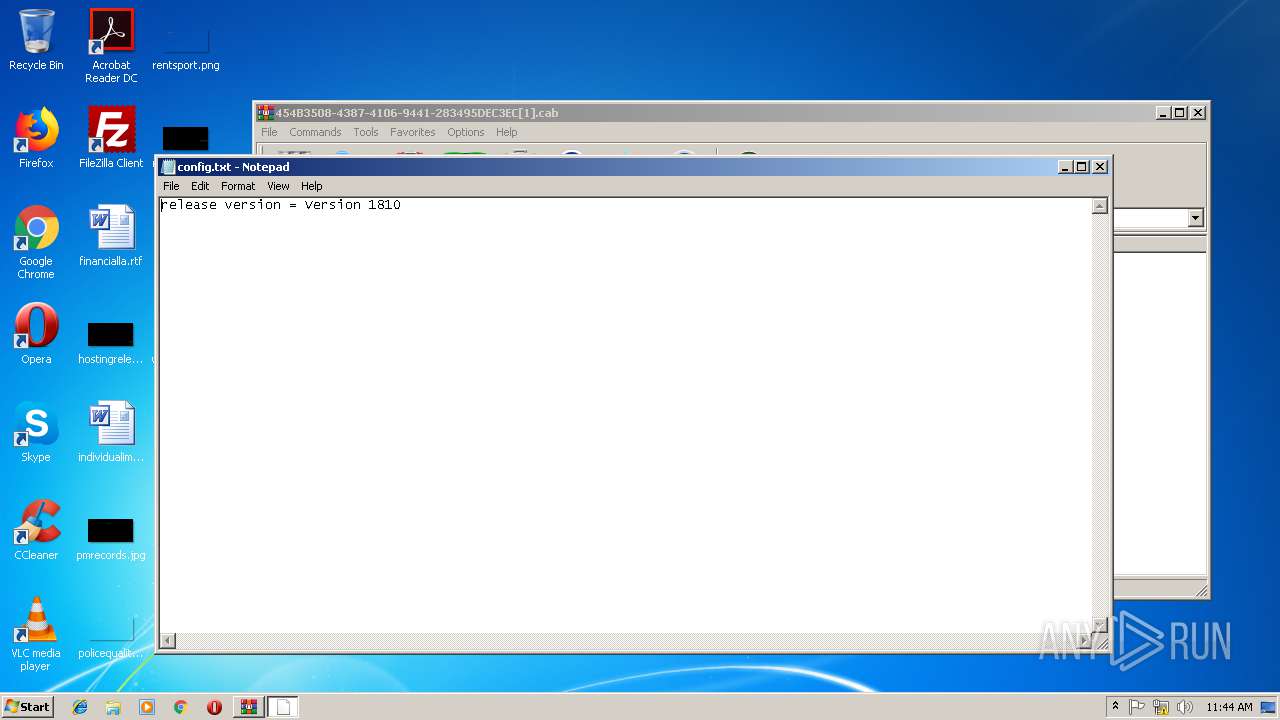
| 3512 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2076.25758\config.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3732 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2076.27758\splash.hta" | C:\Windows\System32\mshta.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 832
Read events
1 697
Write events
131
Delete events
4
Modification events
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4930C2D1-044C-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C00040014000B002A000B00B202 | |||
Executable files
389
Suspicious files
5
Text files
378
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3008 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3008 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0D63AD4B3E4AF0FE.TMP | — | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\454B3508-4387-4106-9441-283495DEC3EC[1].cab | — | |
MD5:— | SHA256:— | |||
| 3008 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF55612B440F125A7A.TMP | — | |
MD5:— | SHA256:— | |||
| 3008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4930C2D1-044C-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4930C2D2-044C-11E9-91D7-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
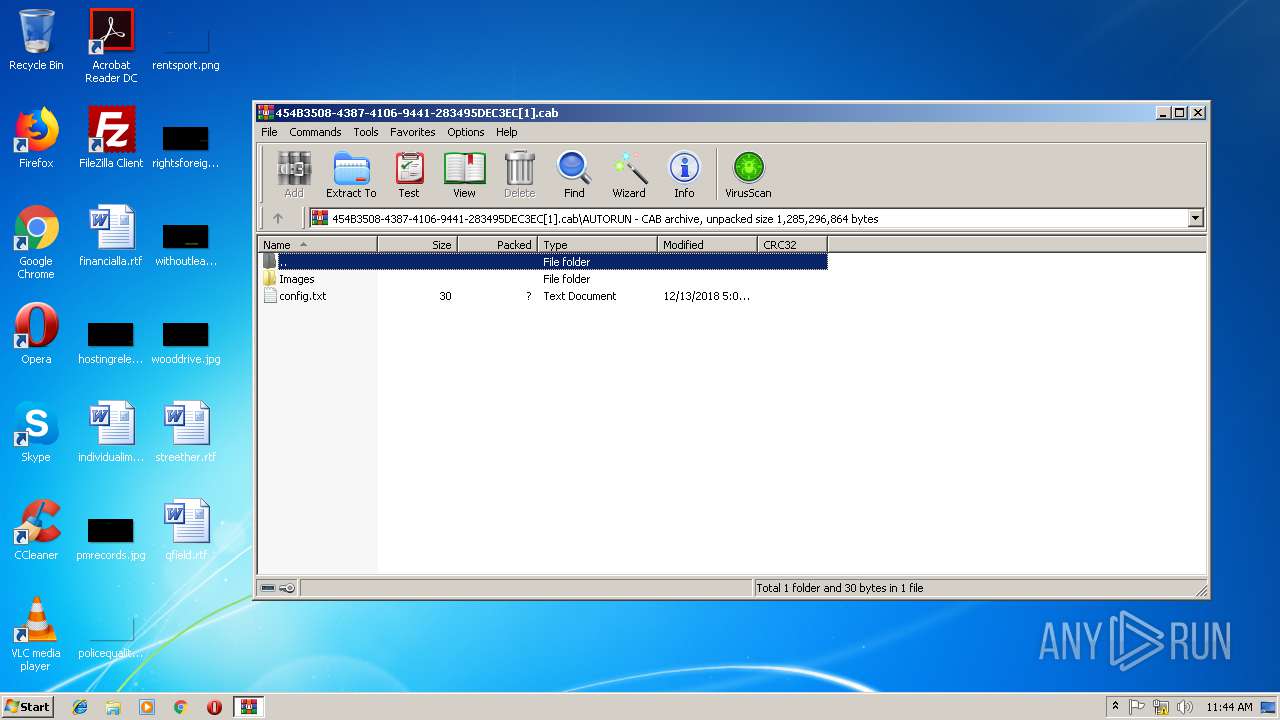
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2076.32895\AUTORUN\Images\Information_16.png | image | |
MD5:— | SHA256:— | |||
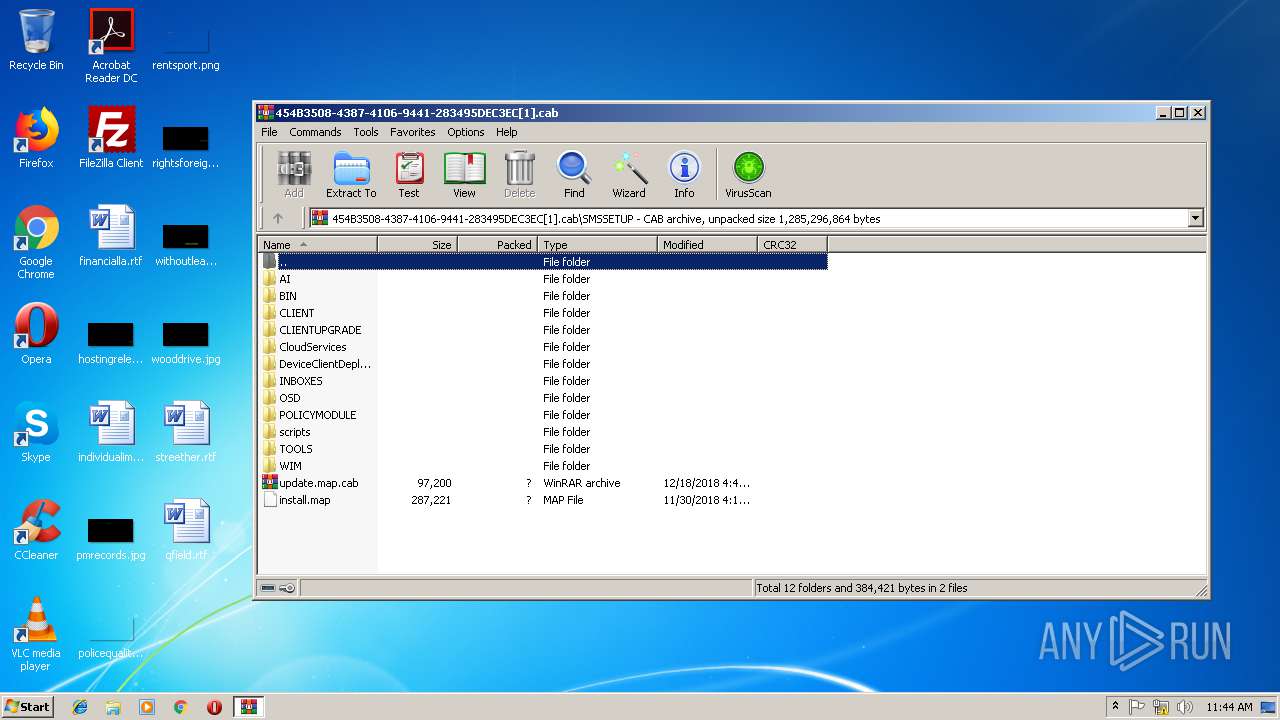
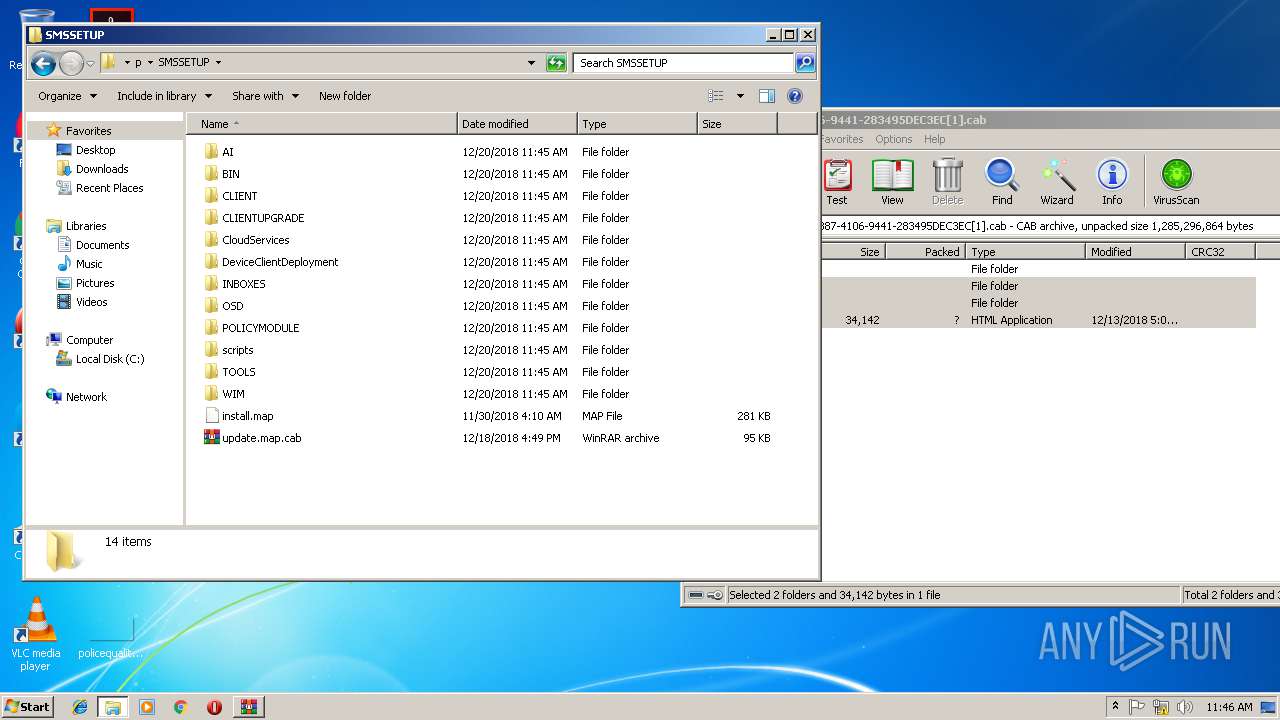
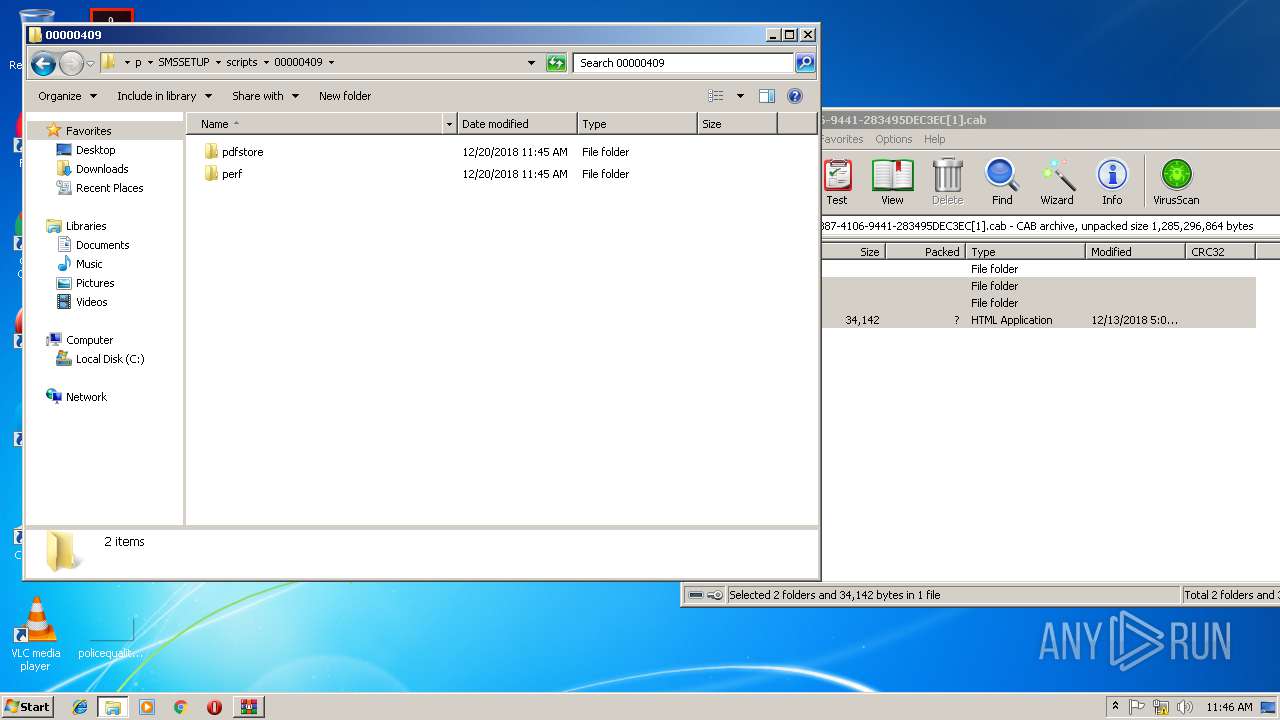
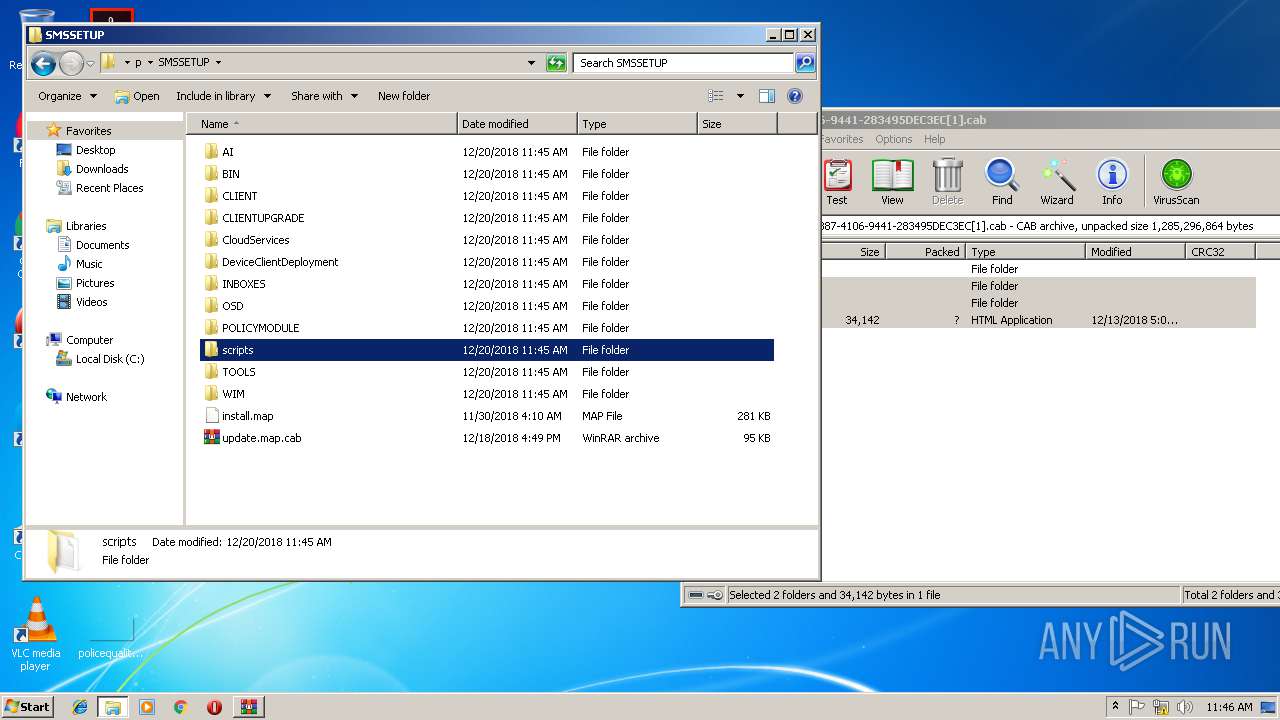
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2076.32895\SMSSETUP\update.map.cab | compressed | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2076.32895\SMSSETUP\AI\LUTables.enc | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | iexplore.exe | GET | — | 2.18.233.19:80 | http://download.microsoft.com/download/2/B/3/2B3F17E5-C934-4D0C-A3BB-E1FD765A05B0/454B3508-4387-4106-9441-283495DEC3EC.cab | unknown | — | — | whitelisted |
3008 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3196 | iexplore.exe | 2.18.233.19:80 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3196 | iexplore.exe | Web Application Attack | SC WEB_APPLICATION_ATTACK Suspicious Generic - Path Traversal for Unix in Zip archive |
3196 | iexplore.exe | unknown | SURICATA TCPv4 invalid checksum |
3196 | iexplore.exe | unknown | SURICATA TCPv4 invalid checksum |
3196 | iexplore.exe | Web Application Attack | SC WEB_APPLICATION_ATTACK Suspicious Generic - Path Traversal for Windows in Zip archive |
3196 | iexplore.exe | Web Application Attack | SC WEB_APPLICATION_ATTACK Suspicious Generic - Path Traversal for Unix in Zip archive |
3196 | iexplore.exe | unknown | SURICATA TCPv4 invalid checksum |
3196 | iexplore.exe | Web Application Attack | SC WEB_APPLICATION_ATTACK Suspicious Generic - Path Traversal for Unix in Zip archive |
3196 | iexplore.exe | unknown | SURICATA TCPv4 invalid checksum |
3196 | iexplore.exe | unknown | SURICATA TCPv4 invalid checksum |