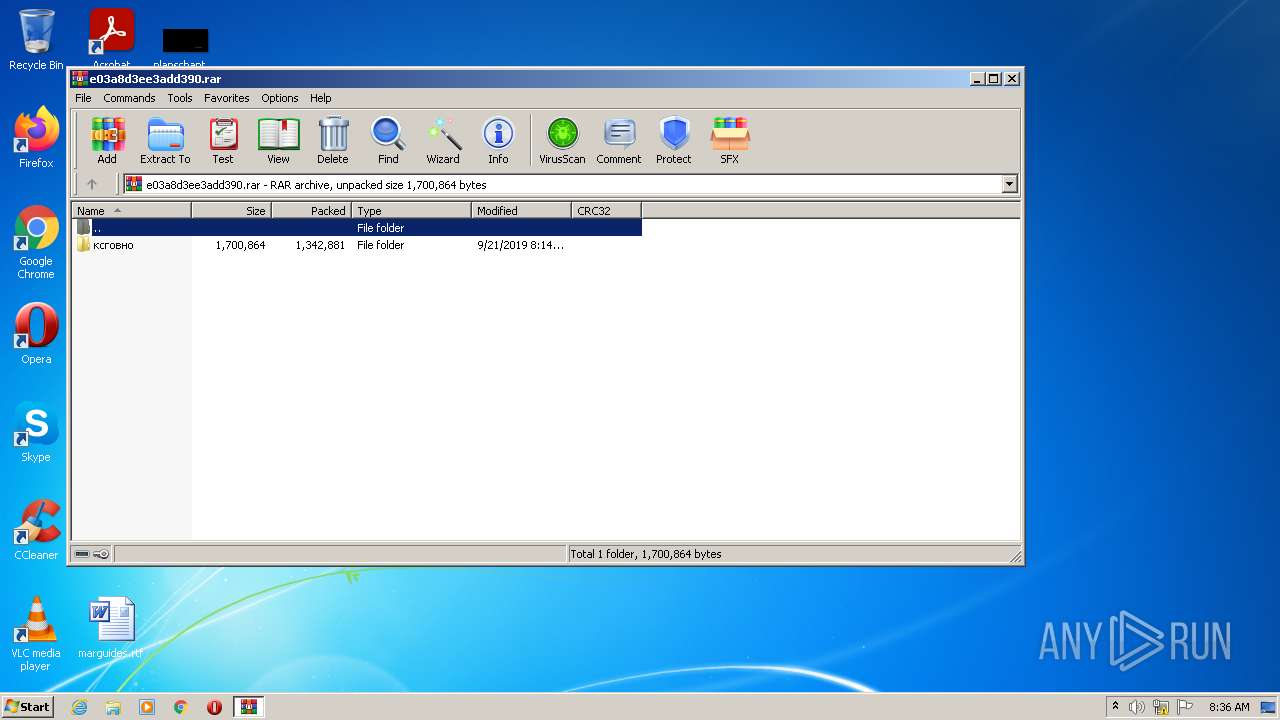
| File name: | e03a8d3ee3add390.rar |
| Full analysis: | https://app.any.run/tasks/278e1ec4-a545-41e4-b9e1-3fe907b2f4ac |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 07:36:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 636E1E622E7176EE18A712EFF8DFB93A |
| SHA1: | EFE7326291C6F0778D888C1870AA9BC8DCFAEB90 |
| SHA256: | EF54BB4D7A1A5BE66D6B7975B1087A5BE4B51C90AC994CE7F770310702E5B07A |
| SSDEEP: | 24576:cbRSBx0mo36b49t0tNbaa/Js1rMpMFeLc8HJg0io3lN3O8P0EXlB:Smc39SHvhsap/LptDA+ |
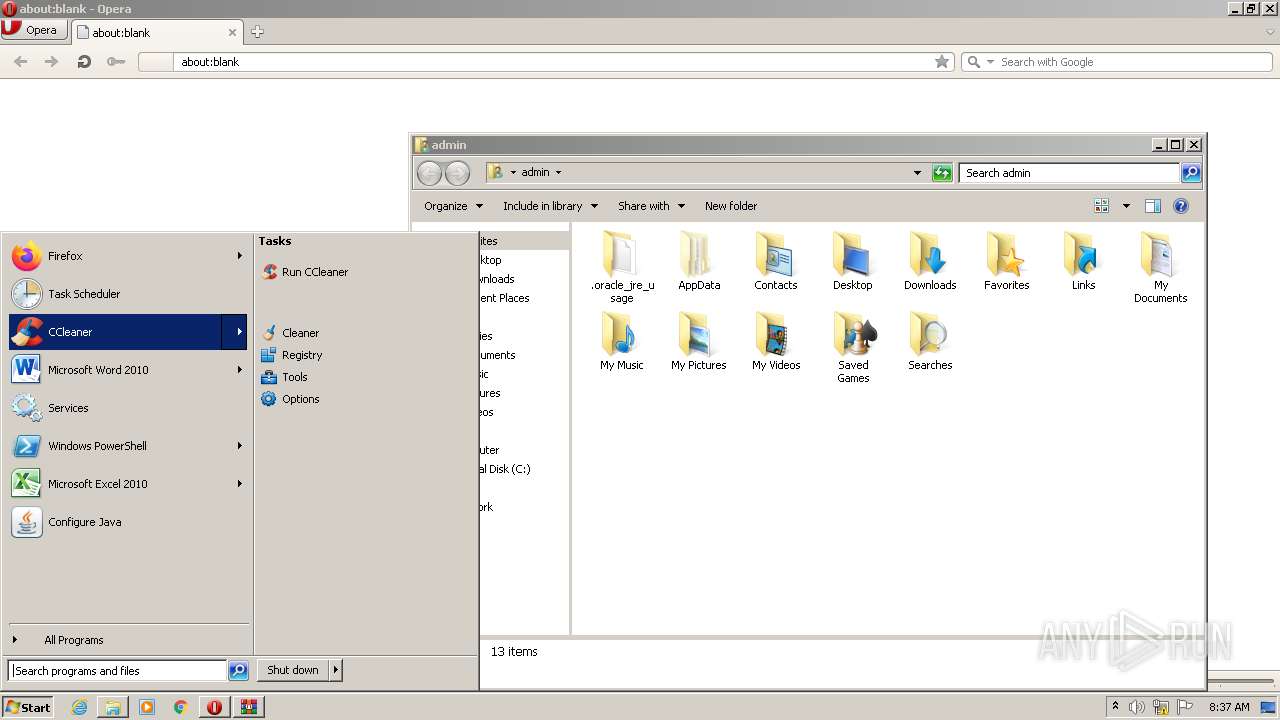
MALICIOUS
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 1620)
- CCleaner.exe (PID: 3160)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 3160)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 3160)
Drops executable file immediately after starts
- CCleaner.exe (PID: 3160)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 3160)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2872)
- CCleaner.exe (PID: 1620)
- CCleaner.exe (PID: 3160)
Checks supported languages
- WinRAR.exe (PID: 2872)
- CCleaner.exe (PID: 1620)
- CCleaner.exe (PID: 3160)
Executed via Task Scheduler
- CCleaner.exe (PID: 3160)
Reads Environment values
- CCleaner.exe (PID: 1620)
- CCleaner.exe (PID: 3160)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 3160)
Reads the date of Windows installation
- CCleaner.exe (PID: 3160)
Drops a file with a compile date too recent
- CCleaner.exe (PID: 3160)
Creates files in the program directory
- CCleaner.exe (PID: 3160)
Reads CPU info
- CCleaner.exe (PID: 3160)
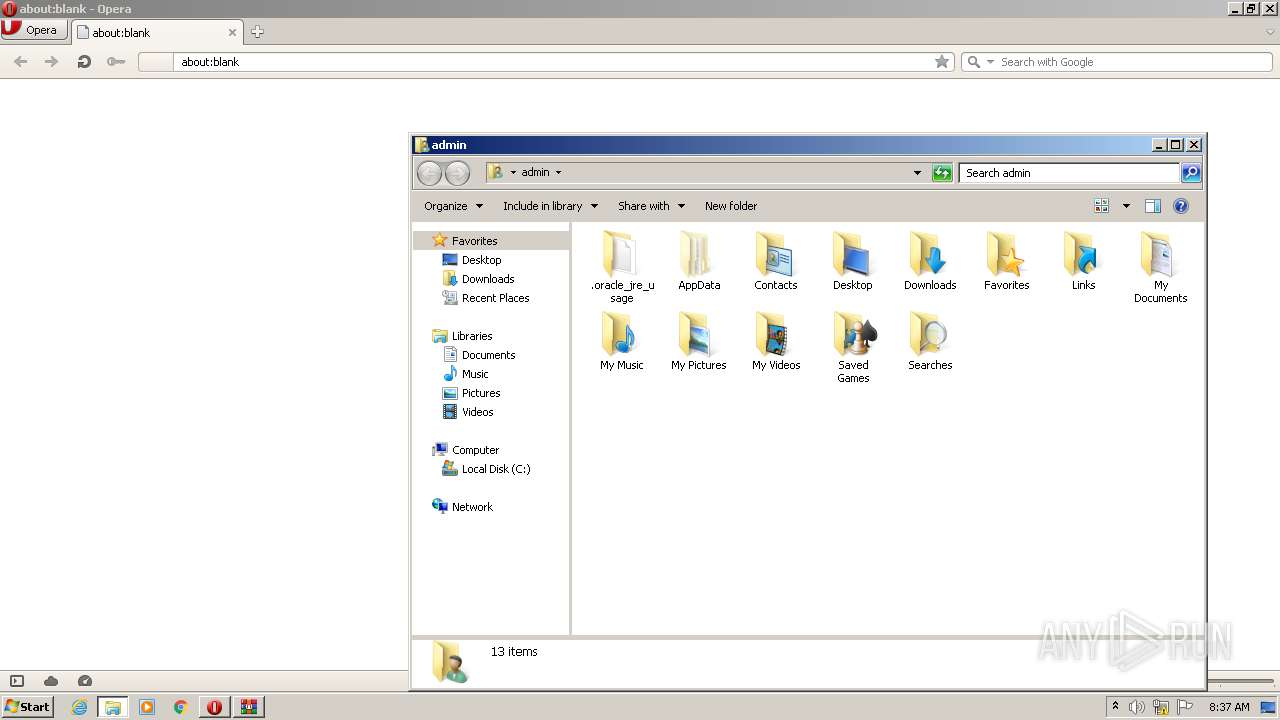
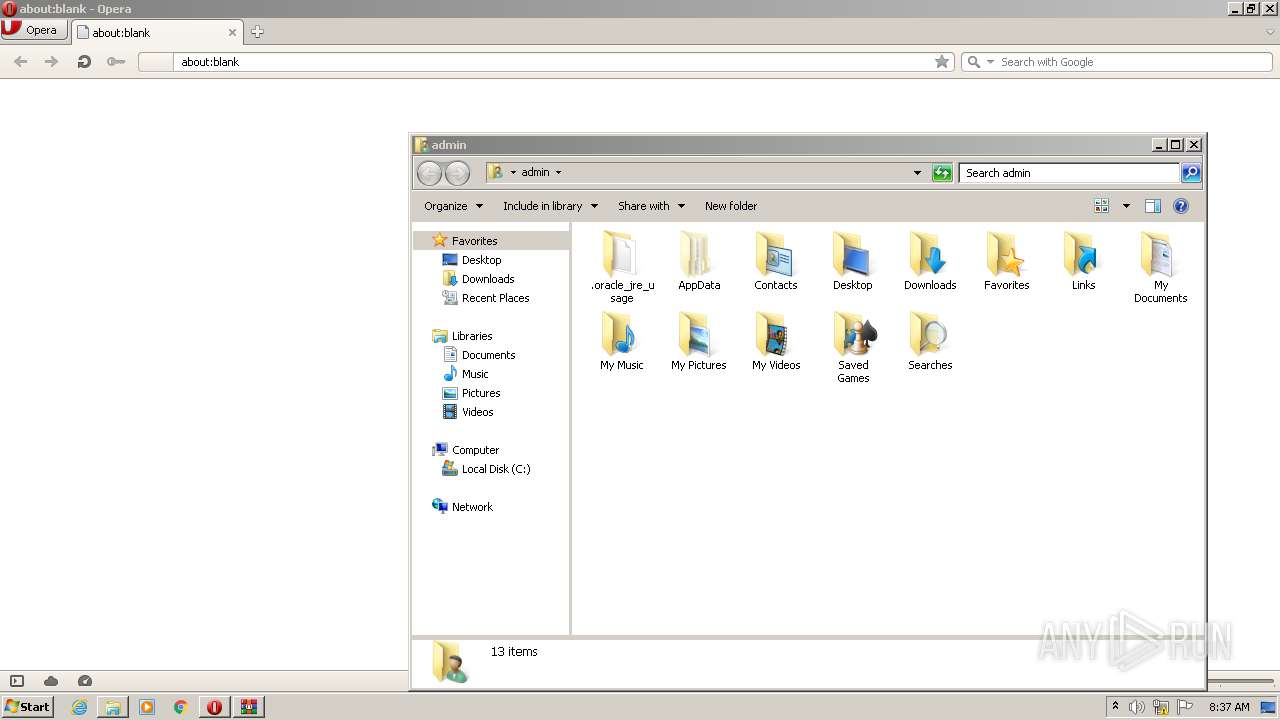
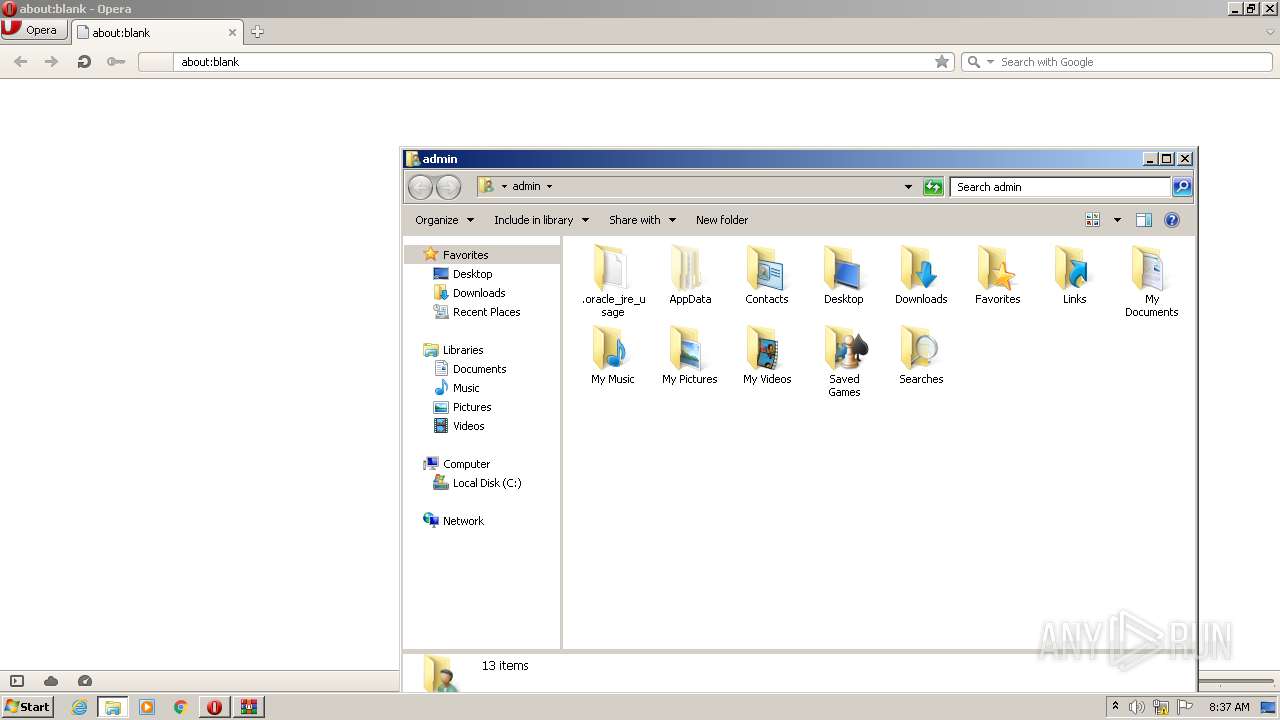
Creates files in the user directory
- CCleaner.exe (PID: 3160)
Executed as Windows Service
- taskhost.exe (PID: 3868)
- taskhost.exe (PID: 4052)
- taskhost.exe (PID: 1148)
Executed via COM
- DllHost.exe (PID: 3948)
Reads internet explorer settings
- CCleaner.exe (PID: 3160)
Removes files from Windows directory
- CCleaner.exe (PID: 3160)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 3160)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 3160)
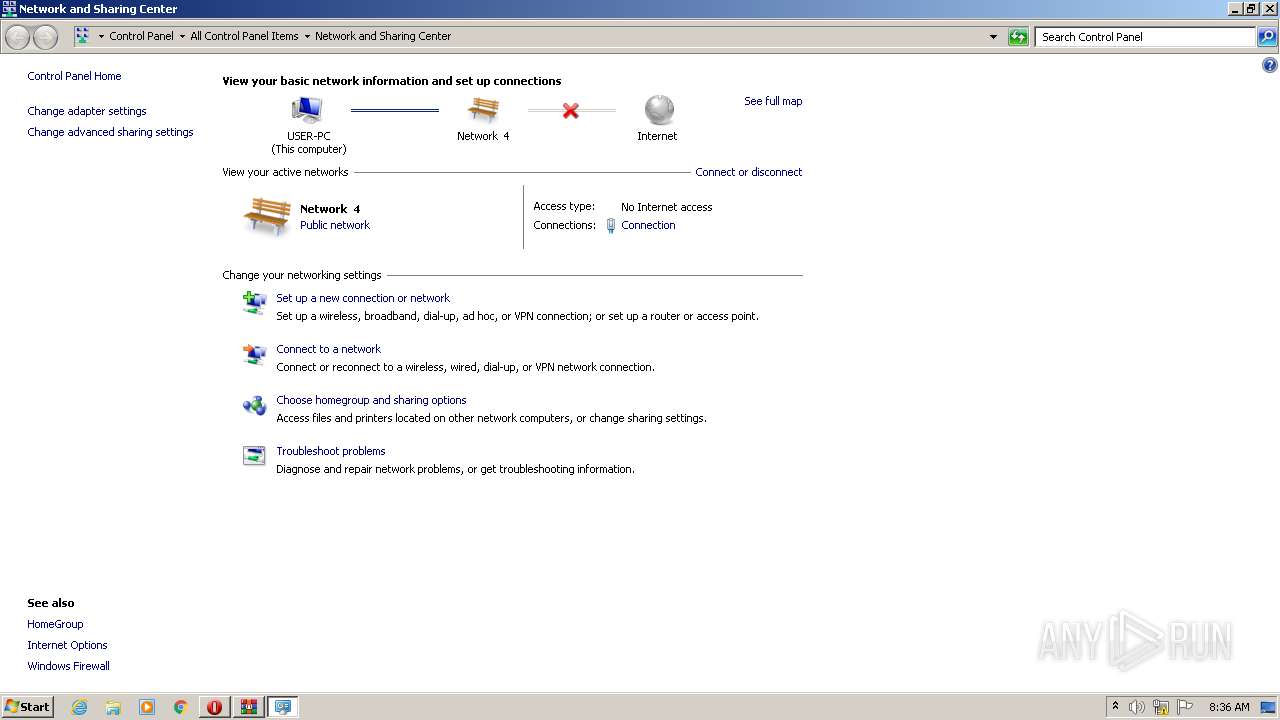
INFO
Reads the computer name
- opera.exe (PID: 2008)
- taskhost.exe (PID: 3868)
- DllHost.exe (PID: 3948)
- taskhost.exe (PID: 4052)
- taskhost.exe (PID: 1148)
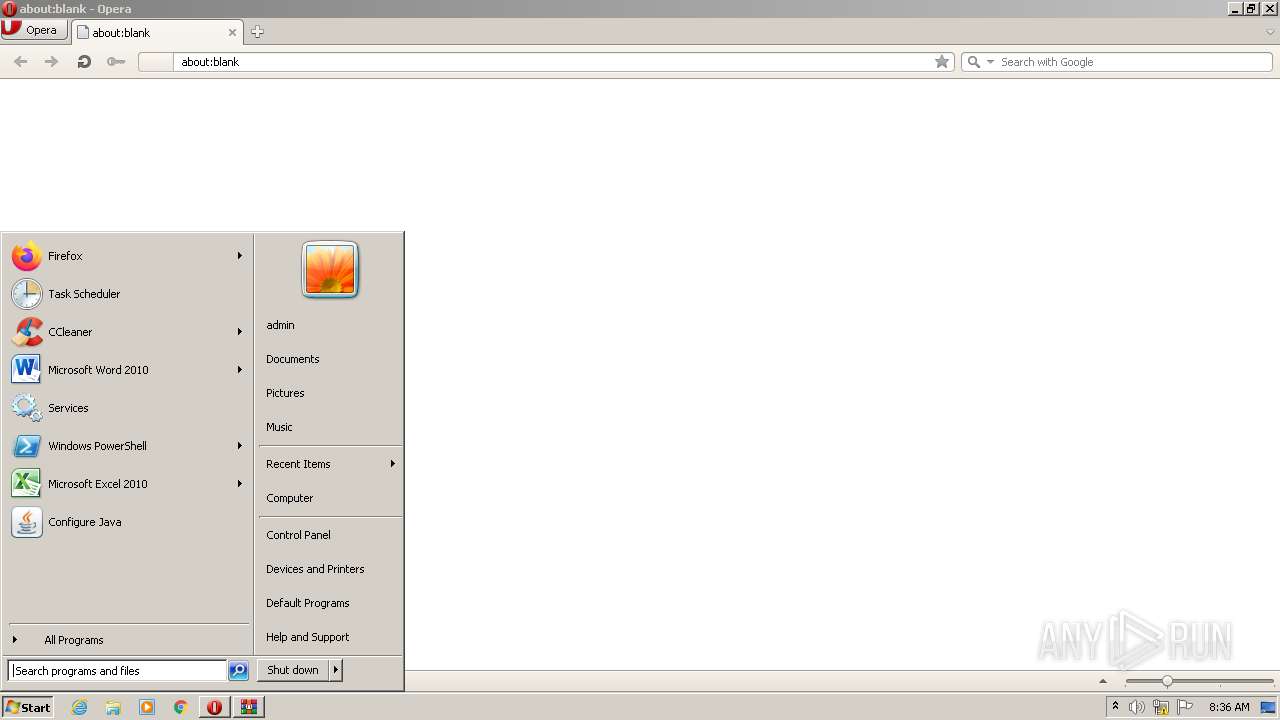
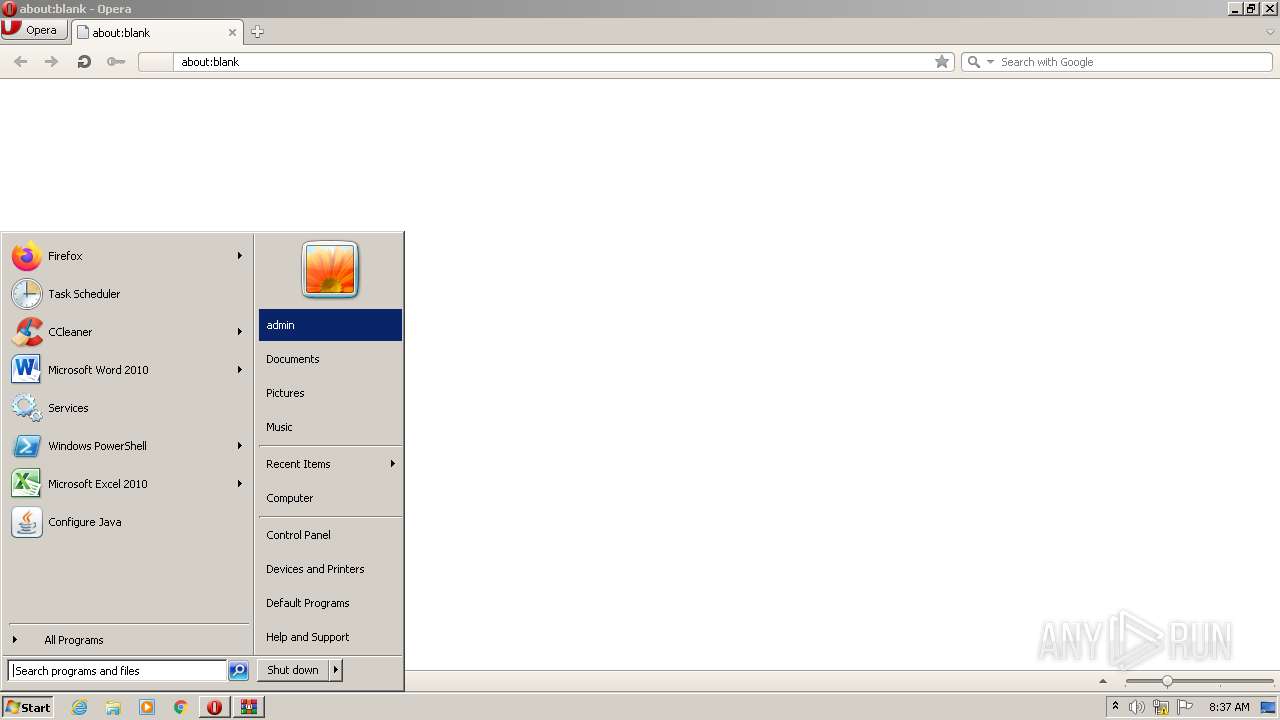
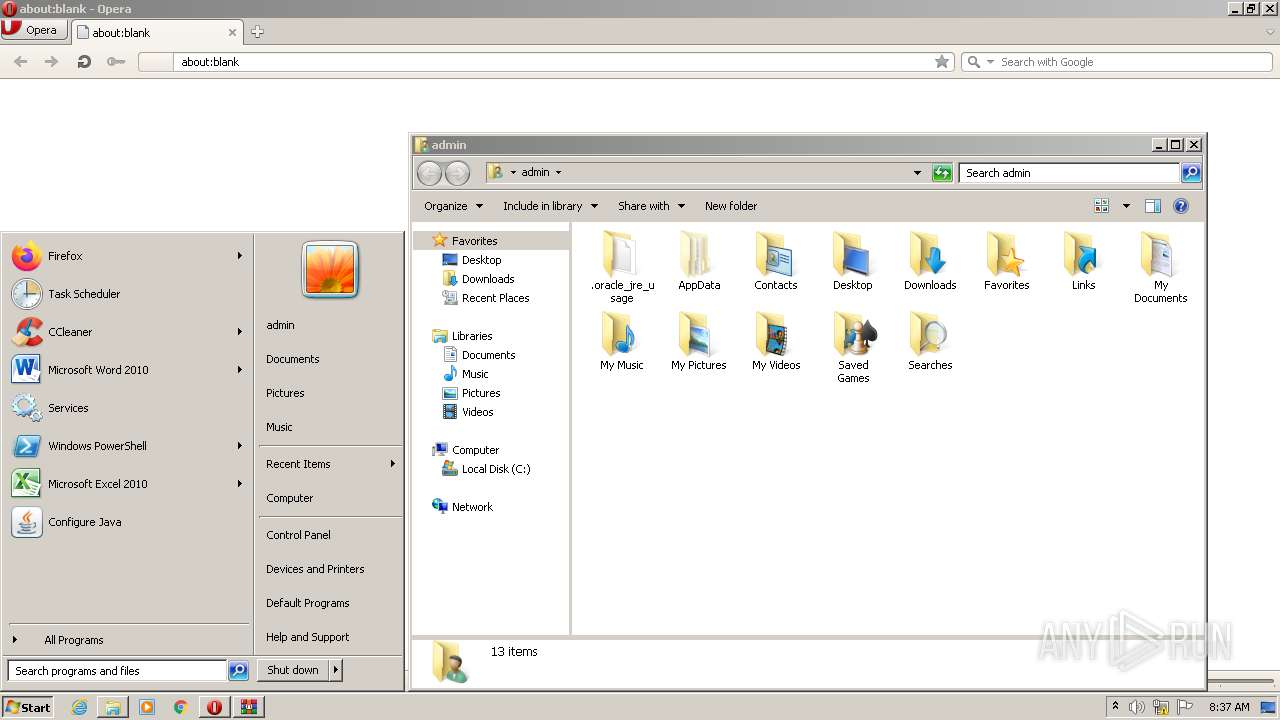
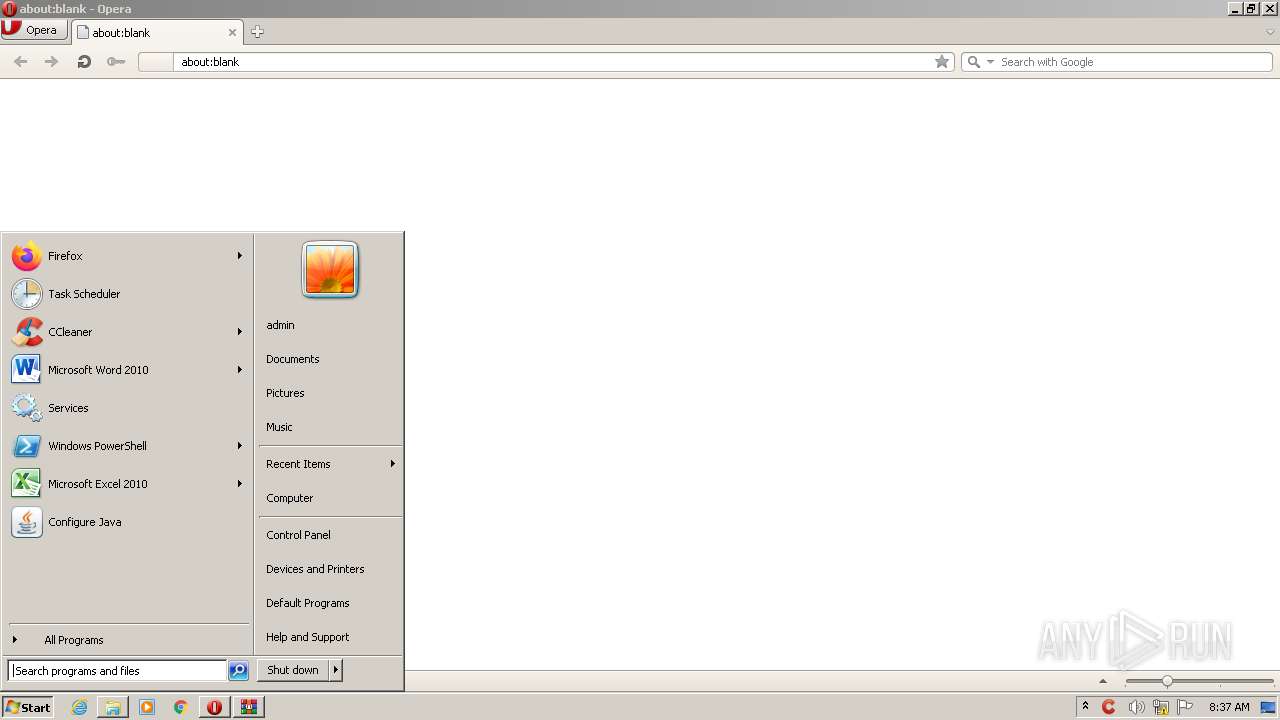
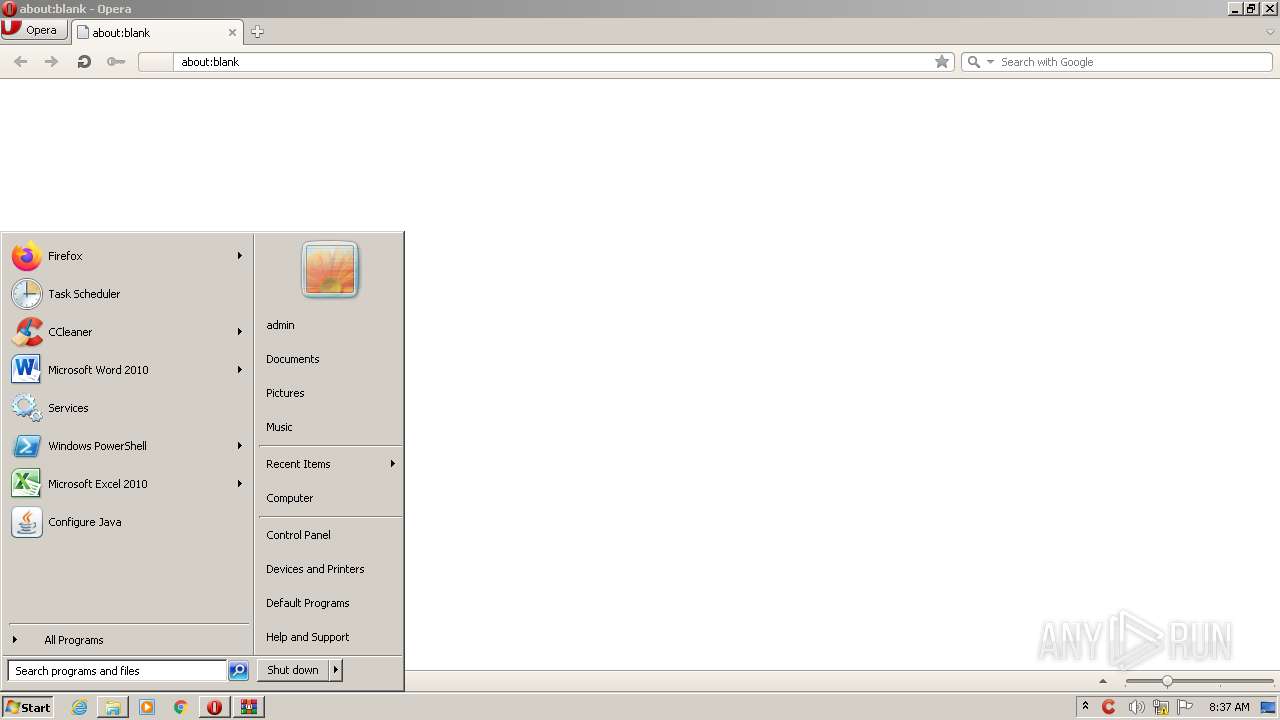
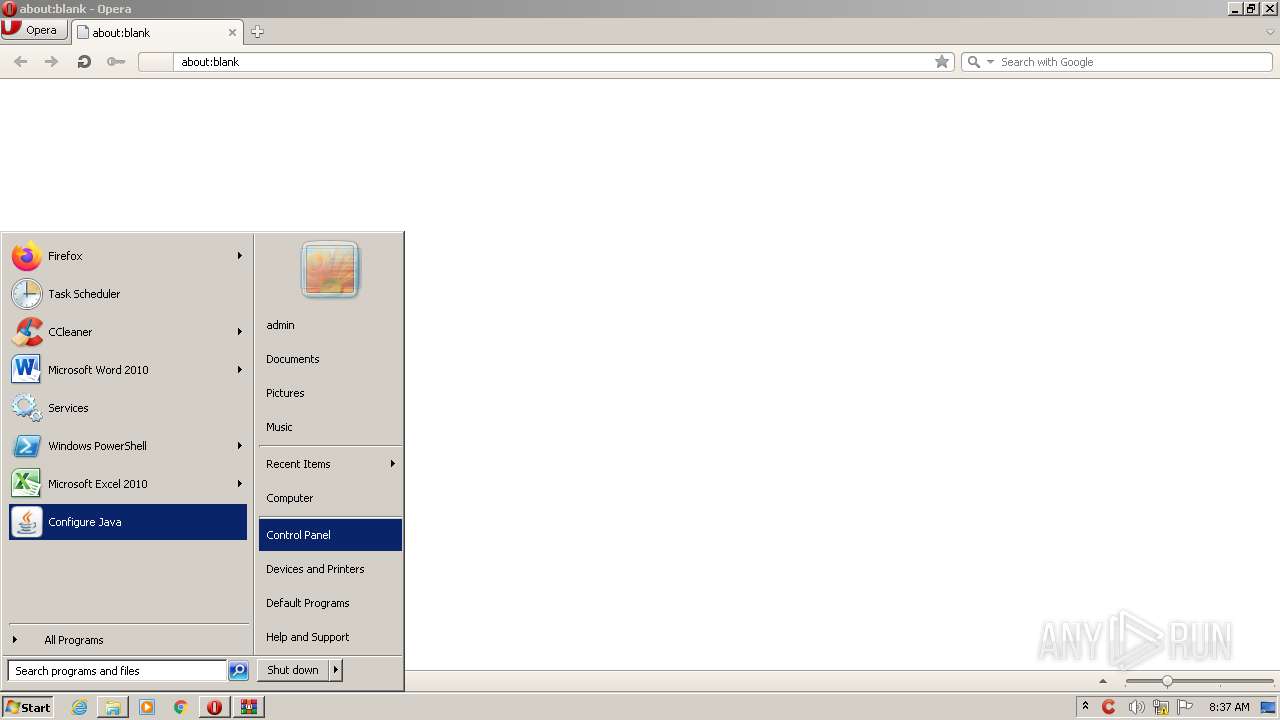
Manual execution by user
- opera.exe (PID: 2008)
- CCleaner.exe (PID: 1620)
Check for Java to be installed
- opera.exe (PID: 2008)
Checks supported languages
- opera.exe (PID: 2008)
- DllHost.exe (PID: 3948)
- taskhost.exe (PID: 3868)
- taskhost.exe (PID: 4052)
- taskhost.exe (PID: 1148)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2008)
Creates files in the user directory
- opera.exe (PID: 2008)
Reads the date of Windows installation
- opera.exe (PID: 2008)
Reads the hosts file
- CCleaner.exe (PID: 3160)
Reads settings of System Certificates
- CCleaner.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1148 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | "C:\Program Files\CCleaner\CCleaner.exe" /AUTOJL | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\e03a8d3ee3add390.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\CCleaner\CCleaner.exe" /AUTOJL /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3868 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 195
Read events
6 970
Write events
178
Delete events
47
Modification events
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\e03a8d3ee3add390.rar | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
72
Text files
15
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\tmp.edb | — | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr808D.tmp | xml | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr800F.tmp | text | |
MD5:— | SHA256:— | |||
| 3160 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\ThumbCacheToDelete\thm8347.tmp | — | |
MD5:— | SHA256:— | |||
| 3160 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\ThumbCacheToDelete\thm8358.tmp | — | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2008 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A2SRMMSS5N6OIIRAHGNB.temp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2008 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3160 | CCleaner.exe | GET | 200 | 23.48.23.10:80 | http://ncc.avast.com/ncc.txt | US | text | 26 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2008 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2008 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2008 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3160 | CCleaner.exe | 23.48.23.10:80 | ncc.avast.com | TRUE INTERNET Co.,Ltd. | US | suspicious |
3160 | CCleaner.exe | 5.62.40.211:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3160 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|