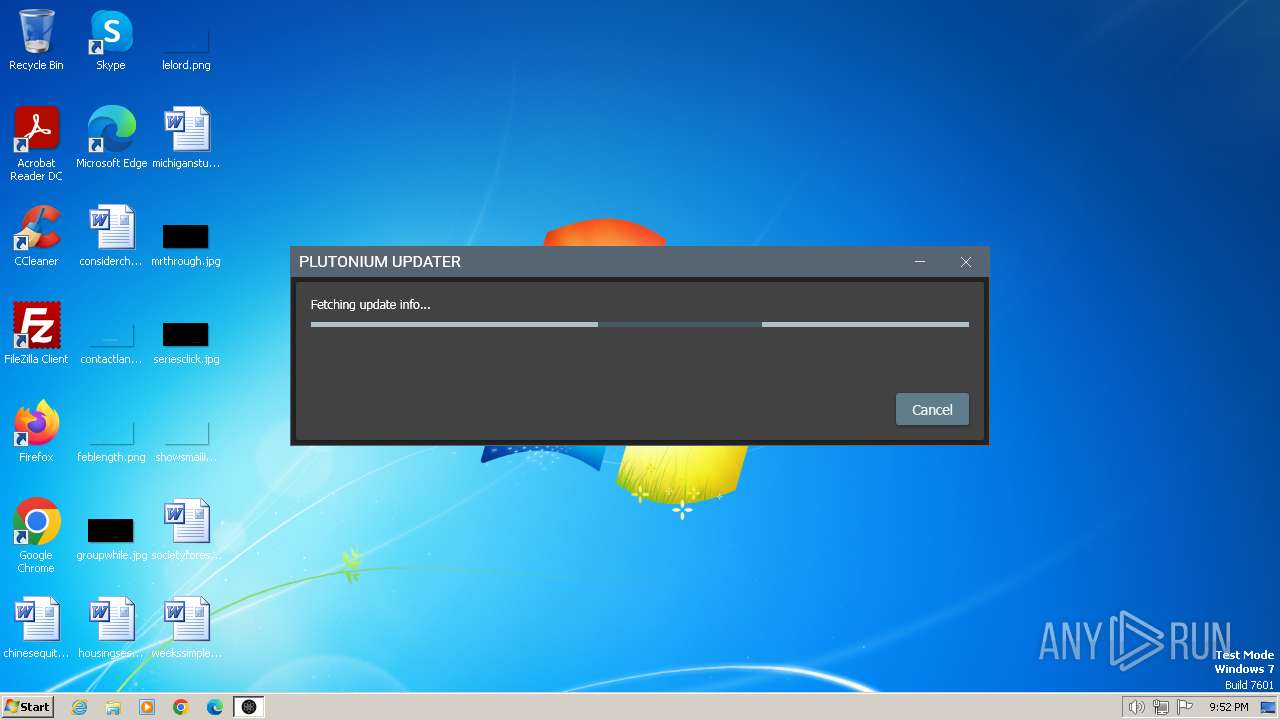
| File name: | plutonium.exe |
| Full analysis: | https://app.any.run/tasks/c63fc0f8-5272-40de-8165-8b7f711eba4a |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2024, 21:49:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1099BAC1C472456EE3BF037CE6813DC6 |
| SHA1: | 12416F16CCFB09BA7A1750881F7EDB97BE79351D |
| SHA256: | EF4D81B7AADB22182DD5E359FB0CA4B389DDC794A27E8638EB89D037014DAC93 |
| SSDEEP: | 98304:bY3bnJQB9JkEXfLRHvupRKcBl+CldaOkigMMDrSthWWwYLEzFL9txCwpXhlZnPnN:Fh03seWi2Fx |
MALICIOUS
Drops the executable file immediately after the start
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
SUSPICIOUS
Reads the Internet Settings
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Reads settings of System Certificates
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Executable content was dropped or overwritten
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Starts itself from another location
- plutonium.new.exe (PID: 2080)
INFO
Checks supported languages
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Reads the computer name
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Reads Environment values
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Reads the machine GUID from the registry
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
- plutonium.exe (PID: 1632)
Create files in a temporary directory
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
Creates files in the program directory
- plutonium.exe (PID: 2040)
- plutonium.new.exe (PID: 2080)
Creates files or folders in the user directory
- plutonium.exe (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:07:20 10:36:57+02:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 4685824 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x479ebe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.210.0 |
| ProductVersionNumber: | 1.0.210.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
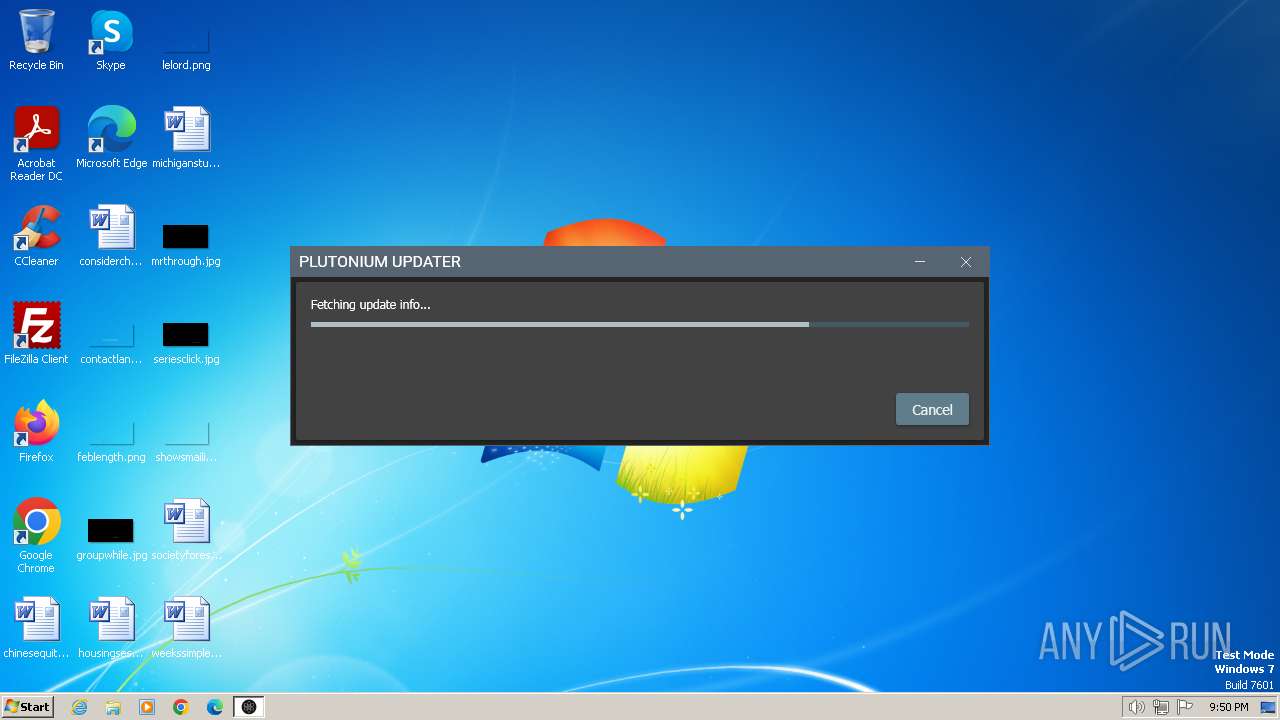
| CompanyName: | Plutonium.Updater.App |
| FileDescription: | Plutonium.Updater.App |
| FileVersion: | 1.0.210.0 |
| InternalName: | Plutonium.Updater.App.exe |
| LegalCopyright: | |
| OriginalFileName: | Plutonium.Updater.App.exe |
| ProductName: | Plutonium.Updater.App |
| ProductVersion: | 1.0.210-b45e05ce |
| AssemblyVersion: | 1.0.210.0 |
Total processes
35
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1632 | "C:\Users\admin\AppData\Local\Temp\plutonium.exe" | C:\Users\admin\AppData\Local\Temp\plutonium.exe | plutonium.new.exe | ||||||||||||
User: admin Company: Plutonium.Updater.App Integrity Level: MEDIUM Description: Plutonium.Updater.App Exit code: 0 Version: 1.0.221.0 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Temp\plutonium.exe" | C:\Users\admin\AppData\Local\Temp\plutonium.exe | explorer.exe | ||||||||||||
User: admin Company: Plutonium.Updater.App Integrity Level: MEDIUM Description: Plutonium.Updater.App Exit code: 0 Version: 1.0.210.0 Modules
| |||||||||||||||
| 2080 | "C:\Users\admin\AppData\Local\Temp\plutonium.new.exe" | C:\Users\admin\AppData\Local\Temp\plutonium.new.exe | plutonium.exe | ||||||||||||
User: admin Company: Plutonium.Updater.App Integrity Level: MEDIUM Description: Plutonium.Updater.App Exit code: 0 Version: 1.0.221.0 Modules
| |||||||||||||||
Total events
12 014
Read events
11 955
Write events
59
Delete events
0
Modification events
| (PID) Process: | (2040) plutonium.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2040) plutonium.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) plutonium.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) plutonium.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) plutonium.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2080) plutonium.new.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2080) plutonium.new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2080) plutonium.new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2080) plutonium.new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2080) plutonium.new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
17
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\AppCore.dll | executable | |
MD5:80C3806A12959987AC012E28F63AD150 | SHA256:B5338B858E5C65F9C36BBC817673BA5E1A05EED8F4DCF007B6BC4FF6140FC8F8 | |||
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\WebCore.dll | executable | |
MD5:90B16ABE7F82DCAE822174B4503F4E1B | SHA256:B4D361BF13F98C96C21C3DEC94D14914FF80C3515A48CD3DF974378CD6052082 | |||
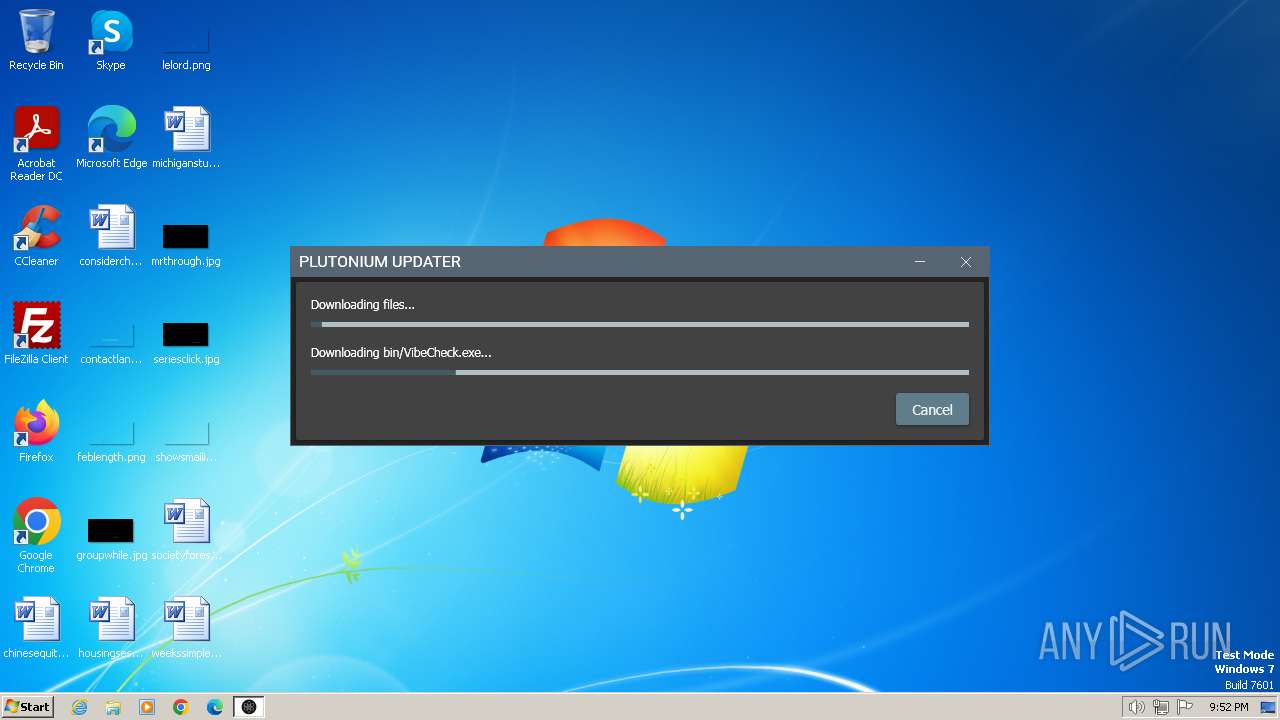
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\VibeCheck.exe | executable | |
MD5:BE1EE42858B55352E0FB154D76F31562 | SHA256:4B053F45887ED35E584B3DDC4C44BAA1533372161B96DEAAA2C3C1EA6FCE7F2B | |||
| 2080 | plutonium.new.exe | C:\Users\admin\AppData\Local\Temp\plutonium.exe | executable | |
MD5:72CB7C6D98E9E47274733825C9176679 | SHA256:85D1D1CA4D5881D9B98928C2006FB0EEC9655E2705FE74088E6F974A19703F0F | |||
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\steam_api64.dll | executable | |
MD5:F3DB5801DC9B75DA671B39041E2E8BCF | SHA256:A44E5537939AE4EEBC69000589AA9B2437A667813A1657CC779198BAE9B815A9 | |||
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\discord_game_sdk.dll | executable | |
MD5:955AF9BE4A97316D73AFAE1E7365E97E | SHA256:D8E7D9FEB3DE8482B186AE44FD1C9ABB41FE2B3B3D2C7CD3A4D742EBBAD30CDF | |||
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-bootstrapper-win32.exe | executable | |
MD5:65AA1F9A6419A431EFFAD74AA9DACD0E | SHA256:08197C2BE38C6AD8361B0C4A88984D30805FB5D66BFC111D8308DB3873B80883 | |||
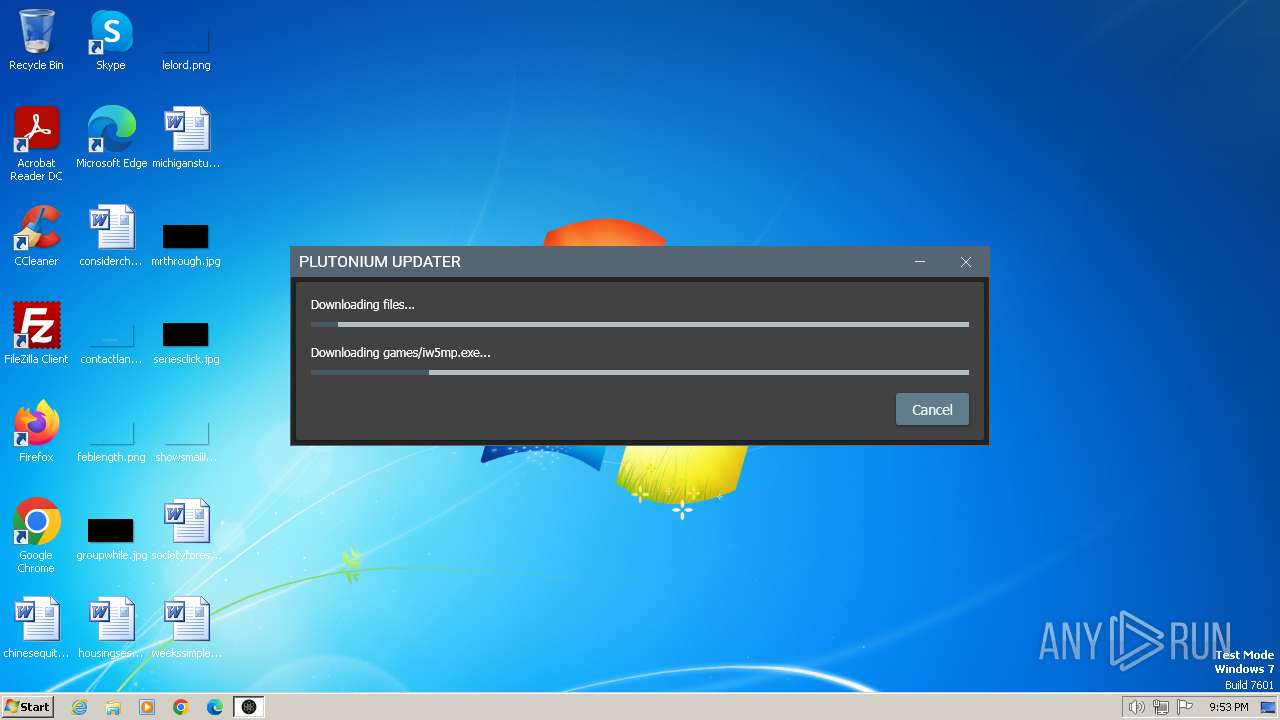
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\iw5sp.exe | executable | |
MD5:6199A36AC2928AC23AC495CC2B528477 | SHA256:0EAD93EB151F1FFFE4EDD3EE3C29DB4209C951506AB44BE05735F1687123B4F0 | |||
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-launcher-win32.exe | executable | |
MD5:335CC1AAECB7F28BA66BF2D2EB758C7E | SHA256:53DB63A60232C5D31D95D46FEB62706312A3A92AD669A55892B73651AE5F08C1 | |||
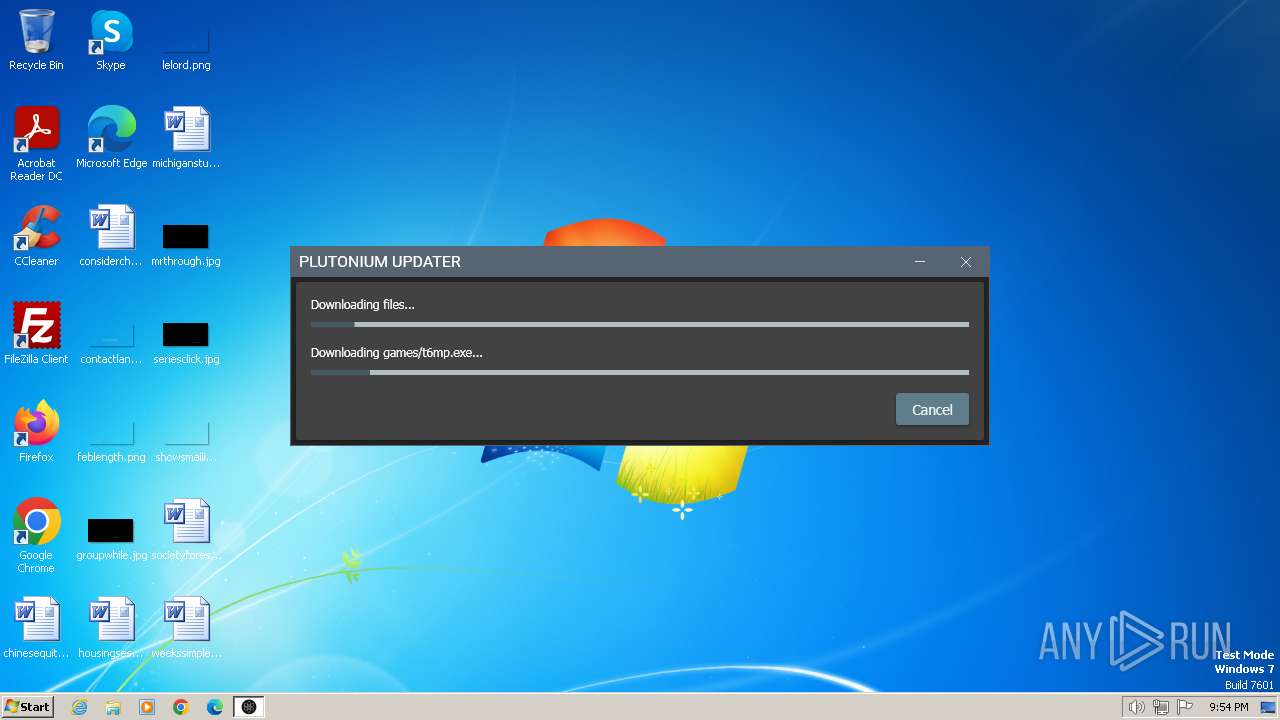
| 1632 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\iw5mp.exe | executable | |
MD5:607FB4AF50010C99157FE3AF8DAAA2B0 | SHA256:DB3E87DCEE15A172D393A32CD79159FD07BFEF8B318A1E9BF3CF5FC98734BDE2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2040 | plutonium.exe | 104.21.235.12:443 | cdn.plutonium.pw | CLOUDFLARENET | — | unknown |
2080 | plutonium.new.exe | 104.21.235.12:443 | cdn.plutonium.pw | CLOUDFLARENET | — | unknown |
1632 | plutonium.exe | 104.21.235.12:443 | cdn.plutonium.pw | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.plutonium.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |