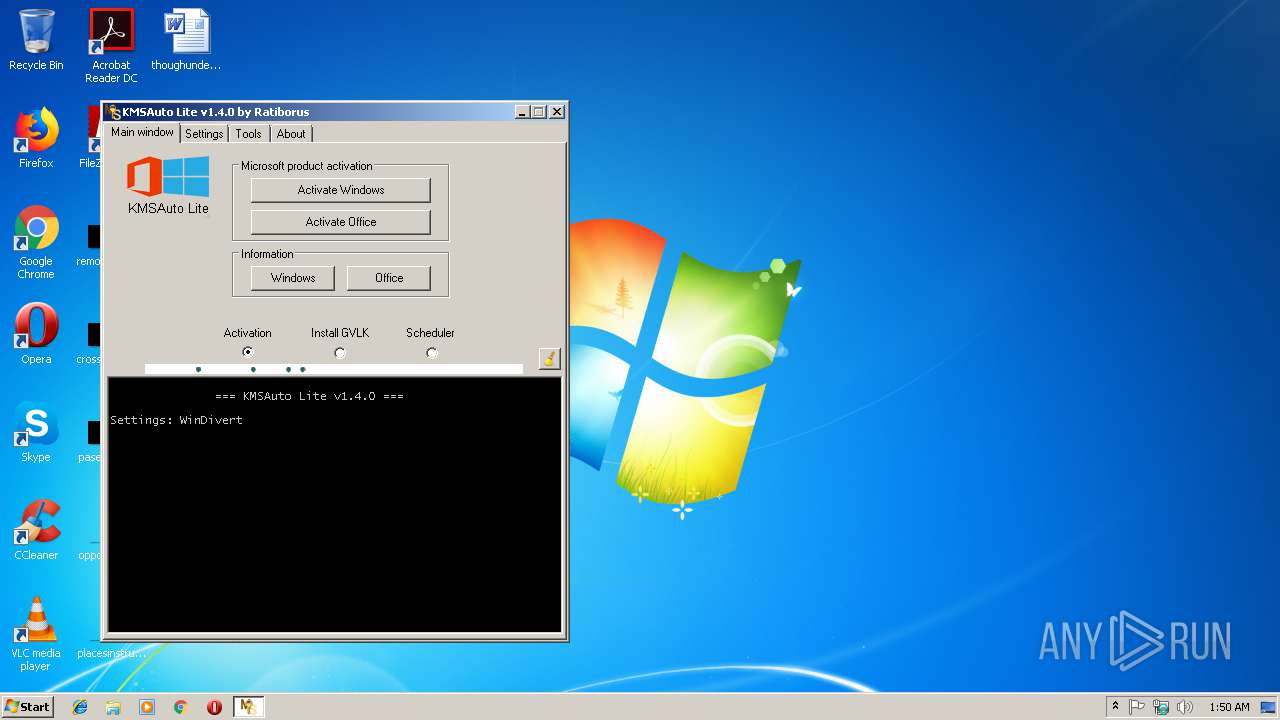
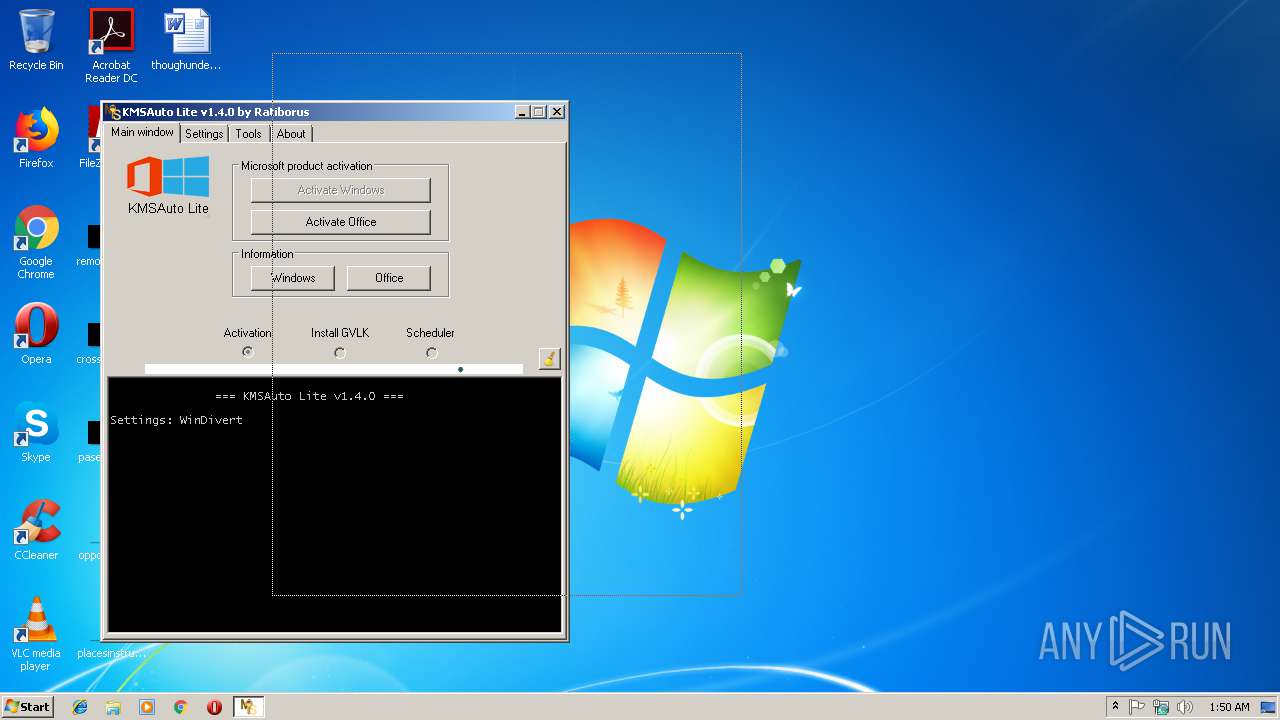
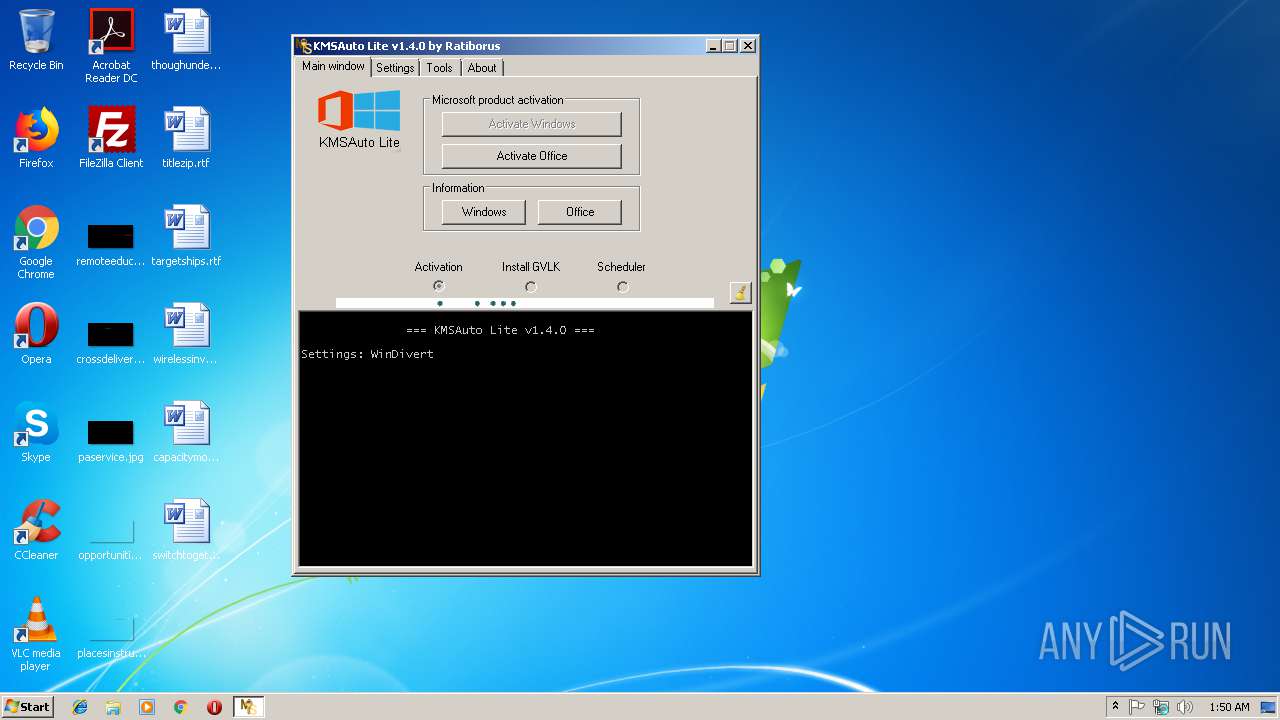
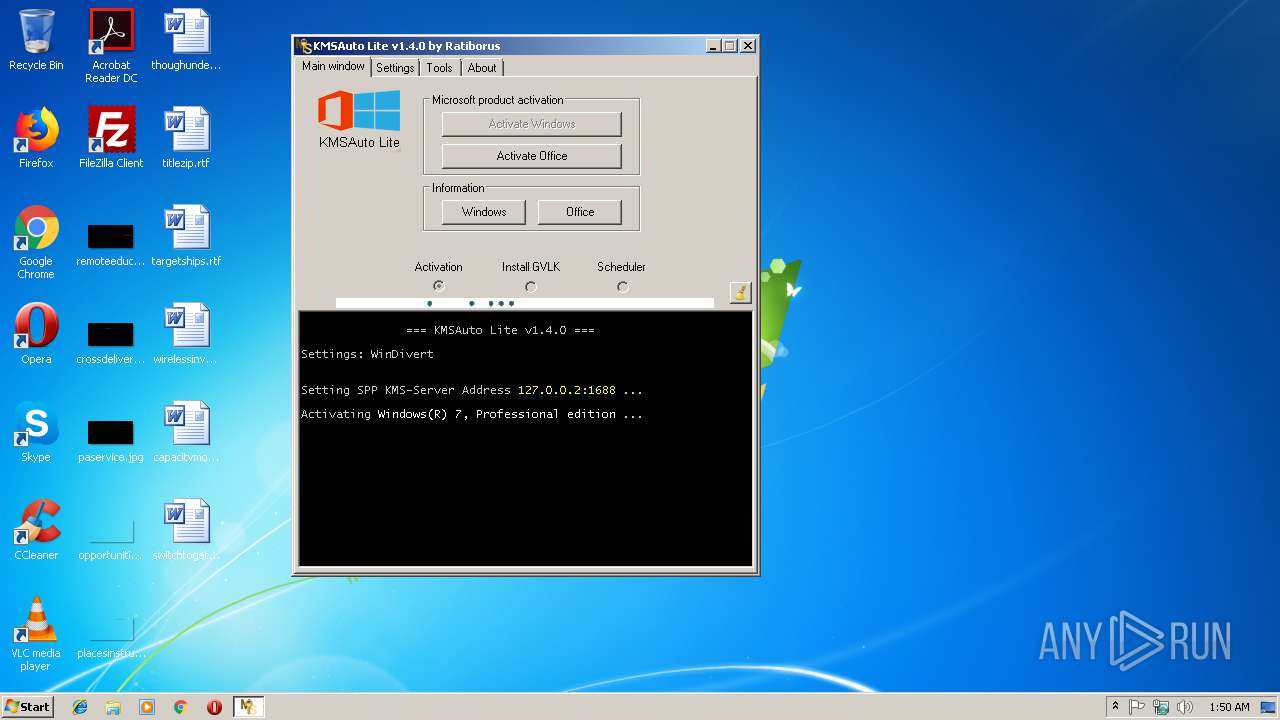
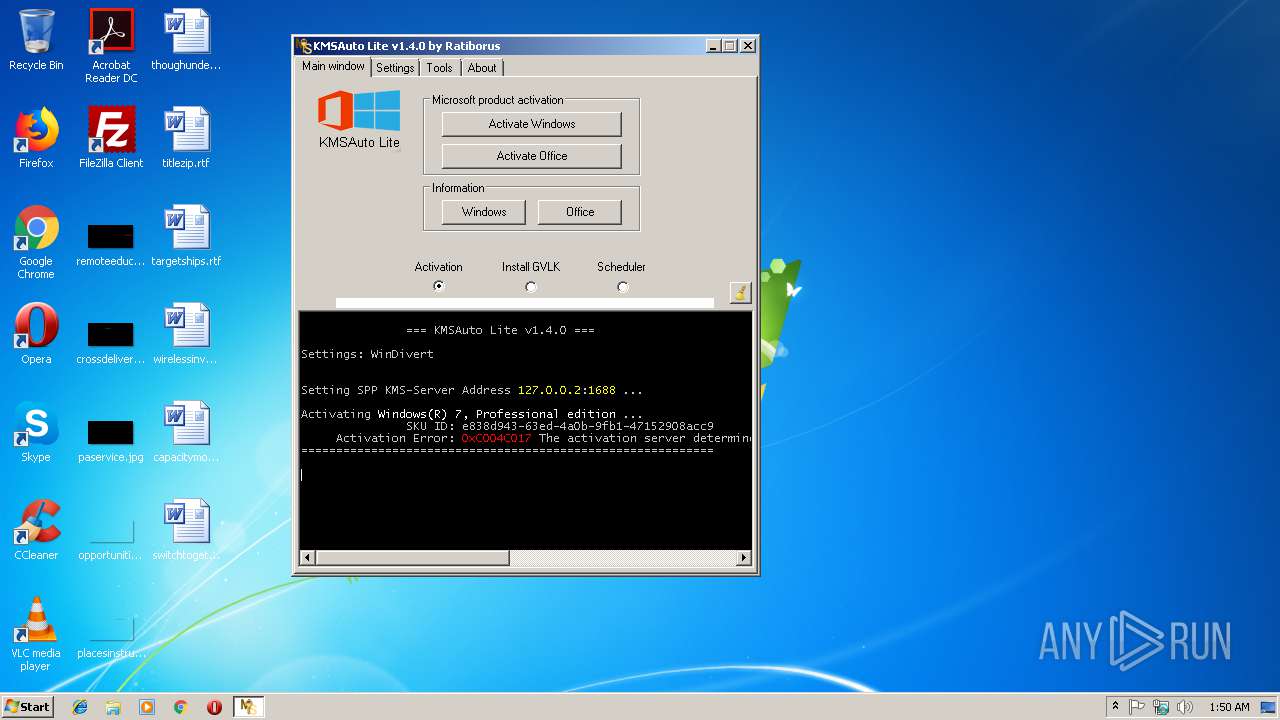
| File name: | KMSAuto.exe |
| Full analysis: | https://app.any.run/tasks/0fdf181b-4f73-47d5-ac96-18af3e6ec441 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 01:50:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 848874FBB3932941804E383C3A7DF4C1 |
| SHA1: | 9E0A0313E6B9850D5C38066193B41C6586660D4F |
| SHA256: | EF46ED3FAA5EF8CD58BDDE77CC7D5547DCA57E3216B7CF3D32D3B77A55C92A26 |
| SSDEEP: | 98304:DTgfYUkkf9GdLj1gsR7eYxSJe6KyvrFQnL39W7hSHUsNKiyzoxQyqoIEU:DTCRt+PxAe6VY39WqUssi3qa |
MALICIOUS
Application was dropped or rewritten from another process
- KMSSS.exe (PID: 2236)
- KMSSS.exe (PID: 2672)
SUSPICIOUS
Creates files in the Windows directory
- KMSAuto.exe (PID: 560)
- KMSSS.exe (PID: 2236)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3212)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 3180)
Creates or modifies windows services
- KMSAuto.exe (PID: 560)
Starts SC.EXE for service management
- cmd.exe (PID: 2788)
- cmd.exe (PID: 2648)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 908)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 2428)
- cmd.exe (PID: 3488)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3868)
- cmd.exe (PID: 2872)
- KMSAuto.exe (PID: 560)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3008)
Executable content was dropped or overwritten
- KMSAuto.exe (PID: 560)
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 560)
Executes scripts
- cmd.exe (PID: 4080)
- cmd.exe (PID: 3624)
Removes files from Windows directory
- KMSAuto.exe (PID: 560)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:29 07:45:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 3665920 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | 1282048 |
| EntryPoint: | 0x4b8e40 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.0 |
| ProductVersionNumber: | 1.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Sep-2018 05:45:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Sep-2018 05:45:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00139000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0013A000 | 0x0037F000 | 0x0037F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.802 |
.rsrc | 0x004B9000 | 0x0000C000 | 0x0000B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.53246 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | English - United States | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 4.32586 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 4.672 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 5.05539 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
104
Monitored processes
48
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Temp\KMSAuto.exe" | C:\Users\admin\AppData\Local\Temp\KMSAuto.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 908 | "C:\Windows\System32\cmd.exe" /c sc.exe start KMSEmulator | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1324 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /ato | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221536791 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2216 | Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS2 dir=out action=allow protocol=TCP localport=1688 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | "C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MSFree Inc. Integrity Level: SYSTEM Description: KMS emulator by Ratiborus. Exit code: 0 Version: 2.0.6.0 Modules
| |||||||||||||||
| 2264 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /skms 127.0.0.2:1688 | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2288 | "C:\Windows\System32\cmd.exe" /c sc.exe start KMSEmulator | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1056 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2300 | sc.exe stop KMSEmulator | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS2 protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2328 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServiceName /d 127.0.0.2 /t REG_SZ /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
513
Read events
236
Write events
277
Delete events
0
Modification events
| (PID) Process: | (560) KMSAuto.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (4012) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
Executable files
1
Suspicious files
0
Text files
66
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | KMSSS.exe | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.log | text | |
MD5:— | SHA256:— | |||
| 560 | KMSAuto.exe | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.exe | executable | |
MD5:463C7CE8E2EC2C33536E9697C0EEBA7D | SHA256:D3ED9D3B8DD6A6A8DFA0A9BB02374B079E8E0C33E600677EF15BFA19264C4F04 | |||
| 2672 | KMSSS.exe | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.log | text | |
MD5:— | SHA256:— | |||
| 560 | KMSAuto.exe | C:\Users\admin\AppData\Local\Temp\slmgr.vbs | text | |
MD5:38482A5013D8AB40DF0FB15EAE022C57 | SHA256:AC5C46B97345465A96E9AE1EDAFF44B191A39BF3D03DC1128090B8FFA92A16F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2164 | wmiprvse.exe | POST | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | unknown | — | — | whitelisted |
2164 | wmiprvse.exe | POST | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | unknown | — | — | whitelisted |
2164 | wmiprvse.exe | POST | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2164 | wmiprvse.exe | 65.52.98.231:443 | activation.sls.microsoft.com | Microsoft Corporation | US | whitelisted |
2164 | wmiprvse.exe | 2.19.38.59:80 | go.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |