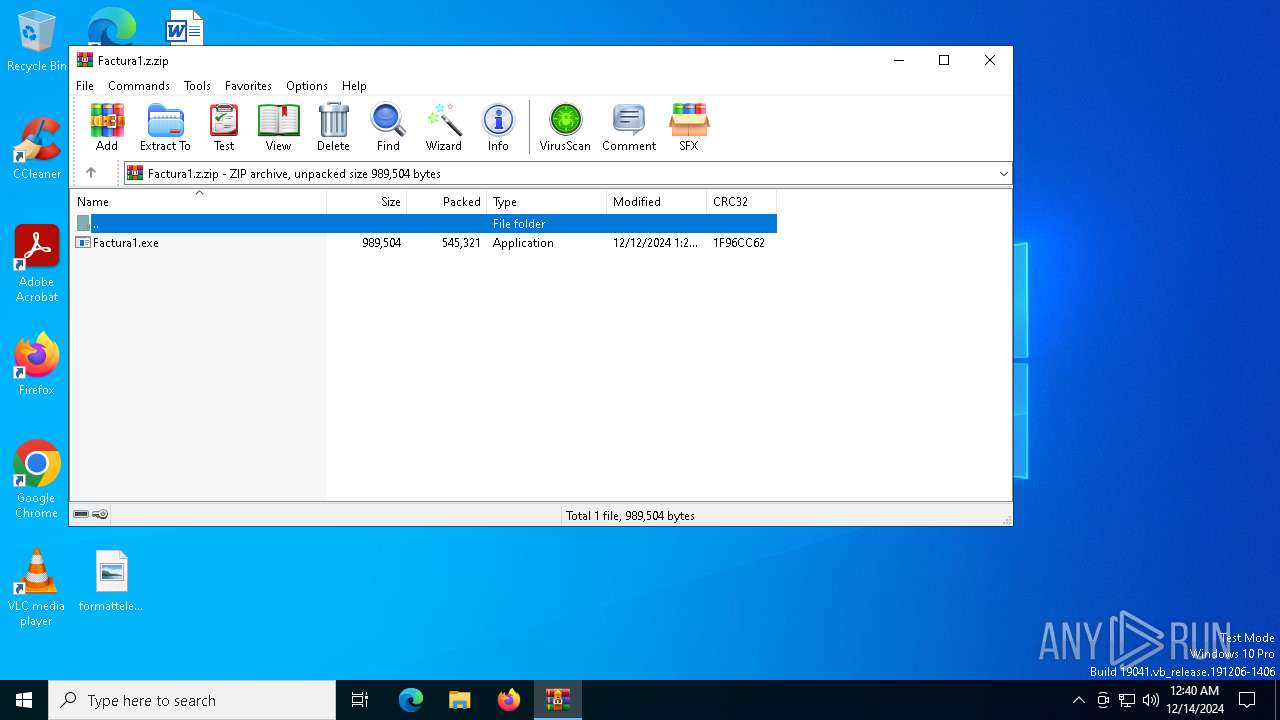
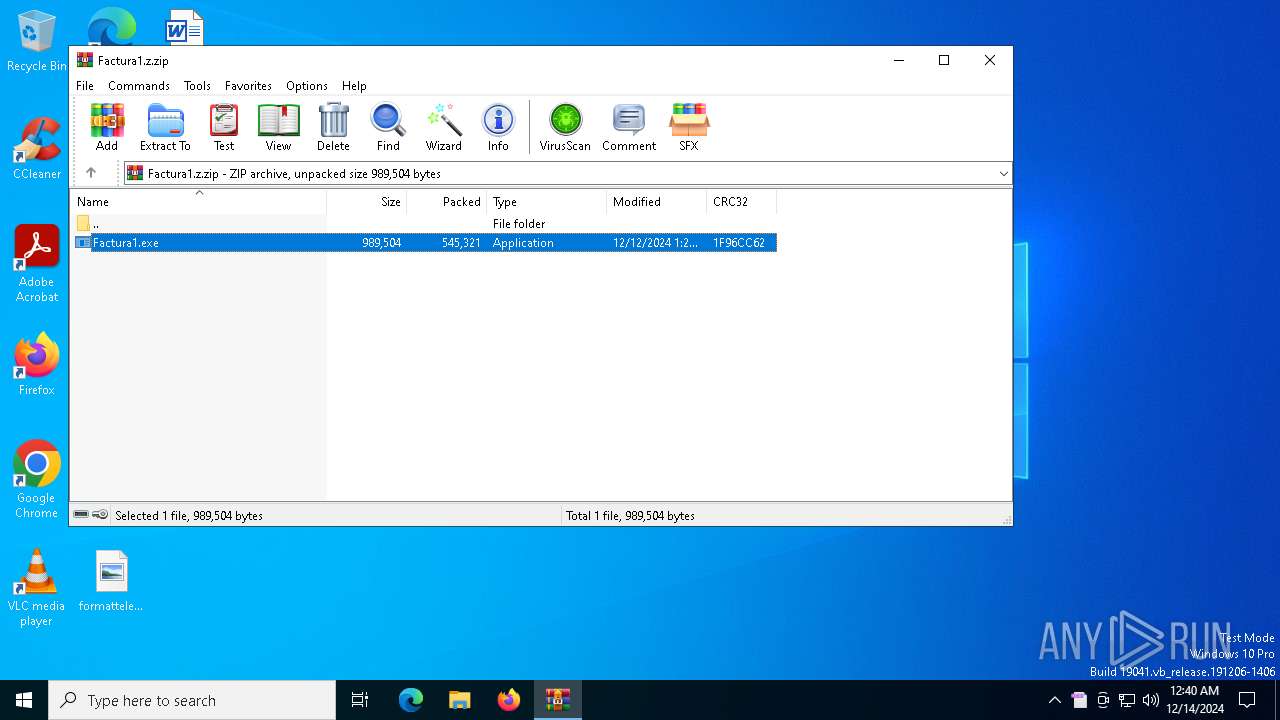
| File name: | Factura1.z |
| Full analysis: | https://app.any.run/tasks/7e96100c-fa29-4a2d-942f-98defc0524f5 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 00:40:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F0FF0681B0ED5A93A40F1435D8A5AB5A |
| SHA1: | 9A4734E4E1A04CA1A3EE5D419399CCEAC517EB2C |
| SHA256: | EF42B737BD1279EC01BD9819CE5FF75597B07A5BB3C3BFBF94ACDDFEEAED4518 |
| SSDEEP: | 24576:NiLwmMeMFHT4D7RdKERPq4ouNXaham8JeogyARR1Y5vafT2JIyj1g0jge1zYV:sLwmfMFHT4D7LKERPq4ouNXa0m8Jeogl |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6172)
Create files in the Startup directory
- epistemology.exe (PID: 6972)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6172)
Executable content was dropped or overwritten
- Factura1.exe (PID: 6944)
Starts itself from another location
- Factura1.exe (PID: 6944)
Executes application which crashes
- epistemology.exe (PID: 6972)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 6172)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6172)
Checks supported languages
- Factura1.exe (PID: 6944)
- epistemology.exe (PID: 6972)
Reads mouse settings
- Factura1.exe (PID: 6944)
- epistemology.exe (PID: 6972)
The sample compiled with english language support
- WinRAR.exe (PID: 6172)
- Factura1.exe (PID: 6944)
Reads the machine GUID from the registry
- Factura1.exe (PID: 6944)
Create files in a temporary directory
- Factura1.exe (PID: 6944)
- epistemology.exe (PID: 6972)
Creates files or folders in the user directory
- Factura1.exe (PID: 6944)
- epistemology.exe (PID: 6972)
- WerFault.exe (PID: 6192)
Reads the software policy settings
- WerFault.exe (PID: 6192)
Checks proxy server information
- WerFault.exe (PID: 6192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:12 13:27:16 |
| ZipCRC: | 0x1f96cc62 |
| ZipCompressedSize: | 545321 |
| ZipUncompressedSize: | 989504 |
| ZipFileName: | Factura1.exe |
Total processes
133
Monitored processes
5
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6172 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Factura1.z.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6192 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6972 -s 700 | C:\Windows\SysWOW64\WerFault.exe | epistemology.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6172.14588\Factura1.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6172.14588\Factura1.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 6, 0 Modules
| |||||||||||||||
| 6972 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6172.14588\Factura1.exe" | C:\Users\admin\AppData\Local\chiffons\epistemology.exe | Factura1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Version: 3, 3, 6, 0 Modules
| |||||||||||||||
| 7108 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6172.14588\Factura1.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | epistemology.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
Total events
5 035
Read events
5 027
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Factura1.z.zip | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
10
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_epistemology.exe_afd3361ecf25ed244c9911a853d561f949b9567_99e852e1_e215cc62-5d39-44ea-8aa1-89babf5821f0\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6944 | Factura1.exe | C:\Users\admin\AppData\Local\Temp\autBECF.tmp | binary | |
MD5:1548B54244DD2B383280EBB1C9220D2E | SHA256:003F9E722F896D52143258205271C7BA4EF97C7EAB67BCC975D77B8CE7484986 | |||
| 6192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC864.tmp.dmp | binary | |
MD5:73C4D40BD1391D865C8FFA22399598B5 | SHA256:257378088EA2185F57AD094DC23CED6CECEC348314E25574F563A5C69000A200 | |||
| 6972 | epistemology.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\epistemology.vbs | binary | |
MD5:0223B266864B7D8F302E3AEE56347610 | SHA256:96E6F67D4E5B9EBBF30371C0126778AF4B431678965E8F7664E93D61BCD7C8C7 | |||
| 6944 | Factura1.exe | C:\Users\admin\AppData\Local\chiffons\epistemology.exe | executable | |
MD5:28EA8E92608217AC405A71E3388EEEE2 | SHA256:18B7930562B9F73F383204F2A09E2A76AB3D772A0D3813EA42BBFF257430B5AD | |||
| 6972 | epistemology.exe | C:\Users\admin\AppData\Local\Temp\autC288.tmp | binary | |
MD5:1548B54244DD2B383280EBB1C9220D2E | SHA256:003F9E722F896D52143258205271C7BA4EF97C7EAB67BCC975D77B8CE7484986 | |||
| 6192 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:33165BB531E6A818B6D2428726C24B69 | SHA256:14B8A576E369F061E8023D570DD0FEA0BD6430CB3F8EAF00C1A9156E3C451E55 | |||
| 6192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC97F.tmp.xml | xml | |
MD5:8E9B8AB82143846D9024C32DEDD55685 | SHA256:89210A14D499C5956E0628476F6A7E7187A727B5A37E598382BE02D5E23E9654 | |||
| 6192 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FA84E4BCC92AA5DB735AB50711040CDE | SHA256:6D7205E794FDE4219A62D9692ECDDF612663A5CF20399E79BE87B851FCA4CA33 | |||
| 6944 | Factura1.exe | C:\Users\admin\AppData\Local\Temp\nonplacental | binary | |
MD5:792C91CCA65ED7BC875CEC68914C50E9 | SHA256:BC54B51E707388C35629A2AB58B06568AC0EB9C7C9F81E1CBA6D6F2A1B3553A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
37
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3552 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |