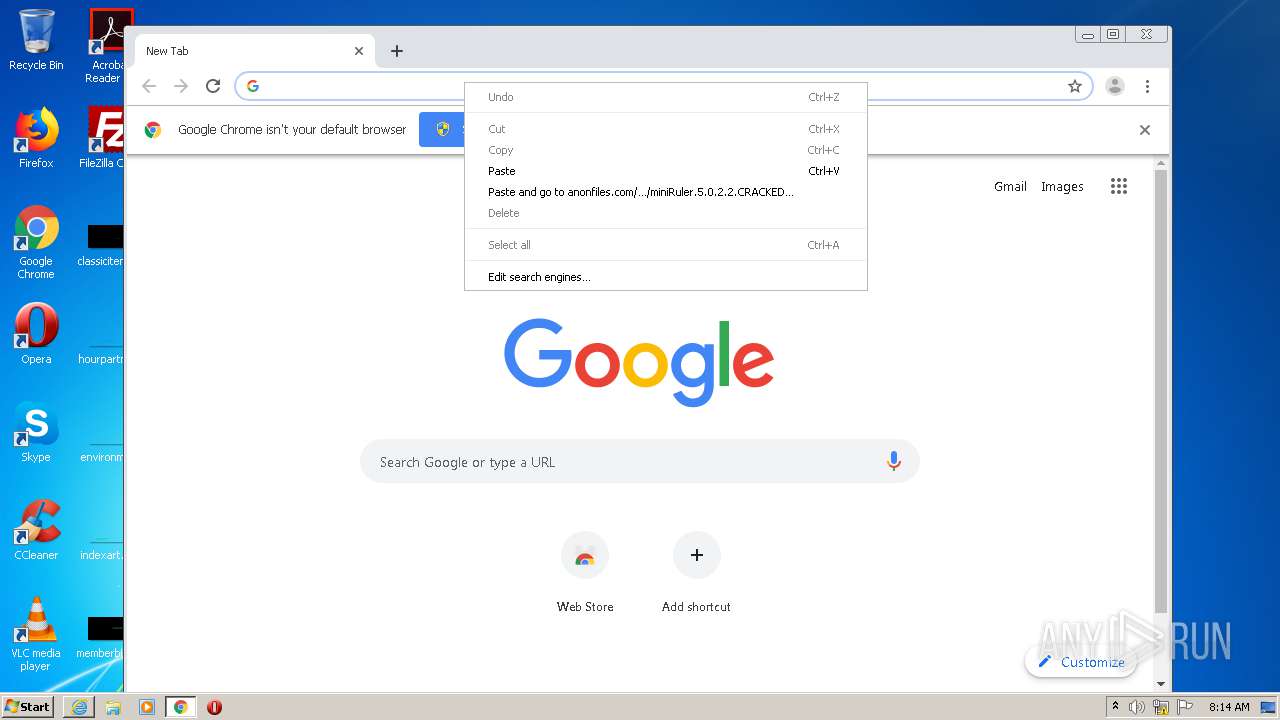
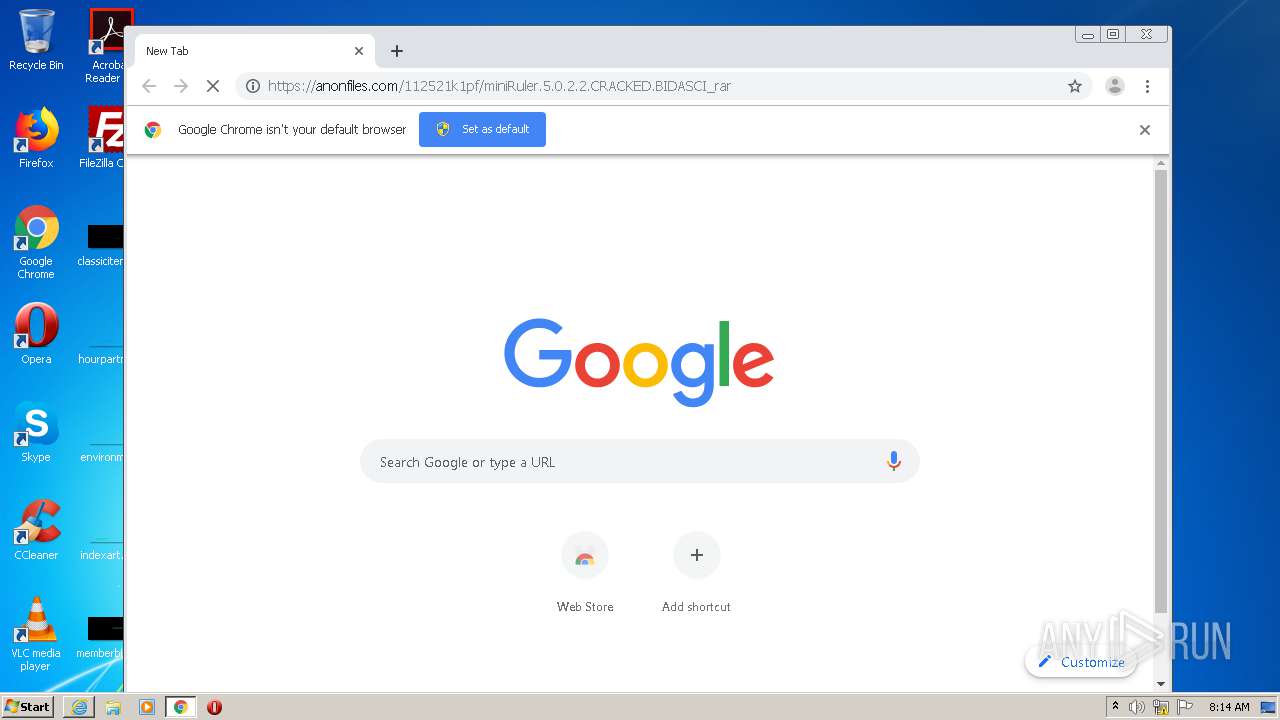
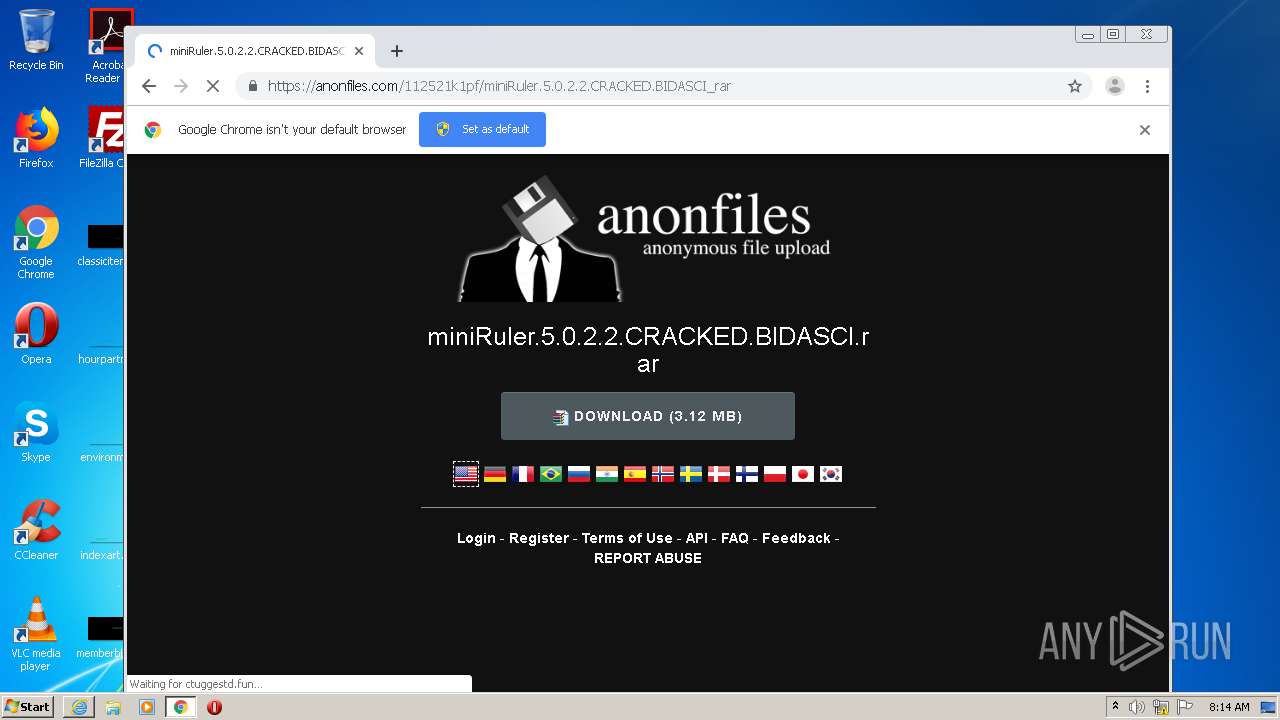
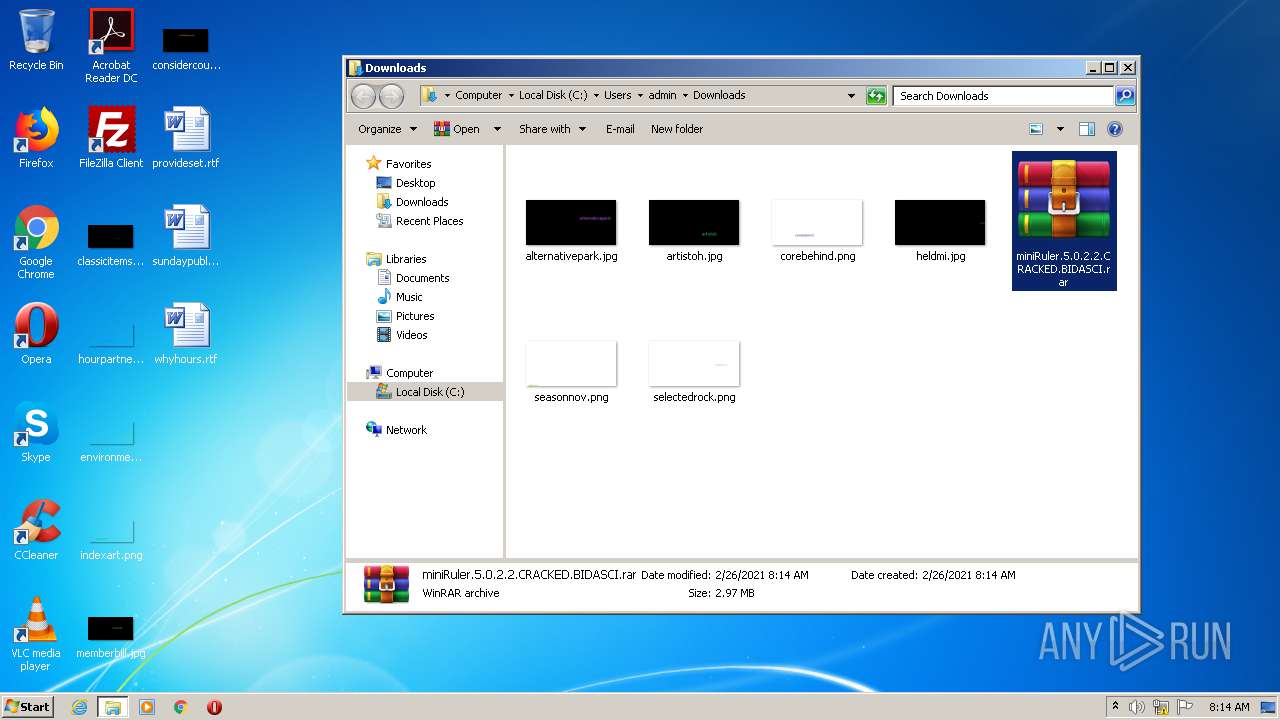
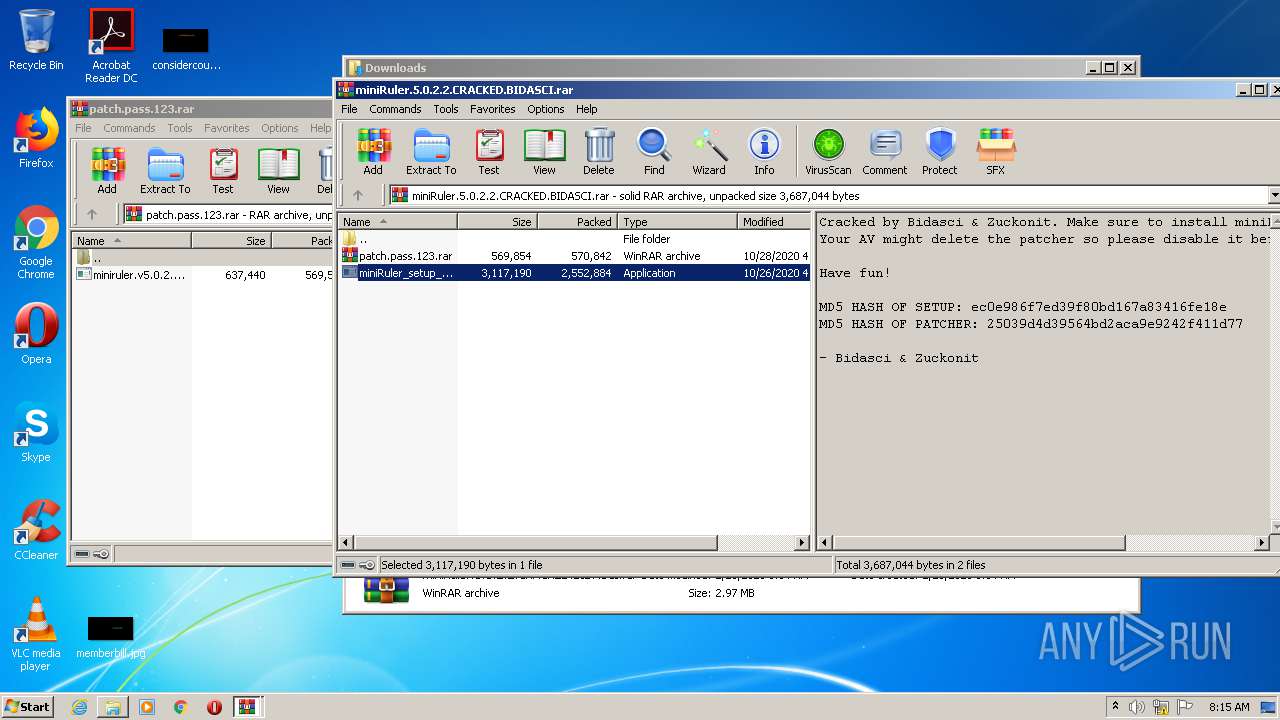
| URL: | https://anonfiles.com/112521k1pf/miniRuler.5.0.2.2.CRACKED.BIDASCI_rar |
| Full analysis: | https://app.any.run/tasks/94fb617a-6cfa-4dd5-b8ea-9f98437ff12e |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2021, 08:12:43 |
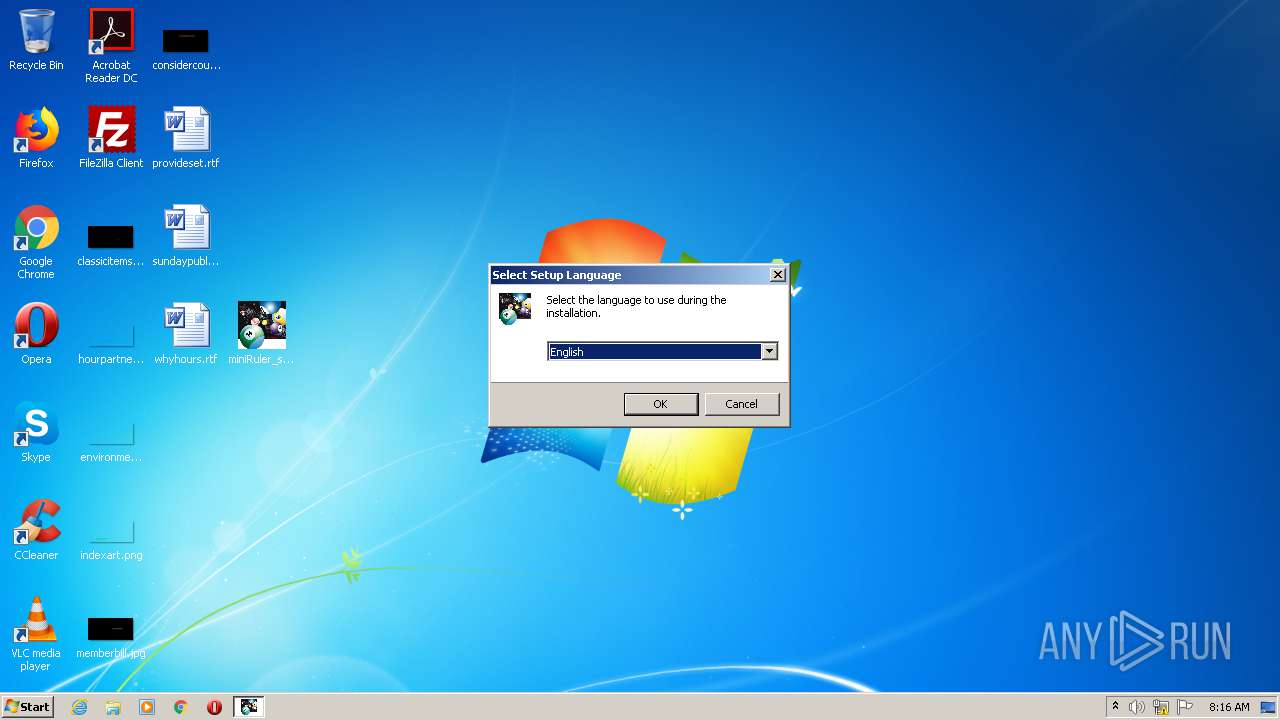
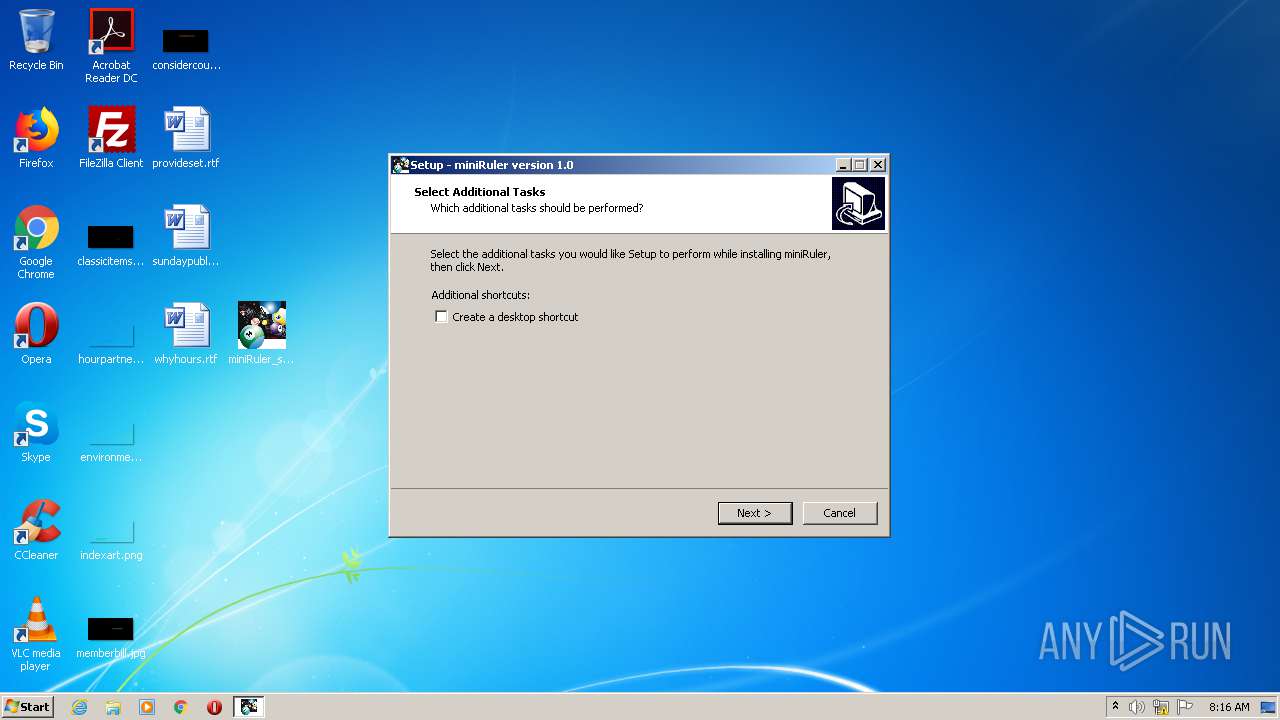
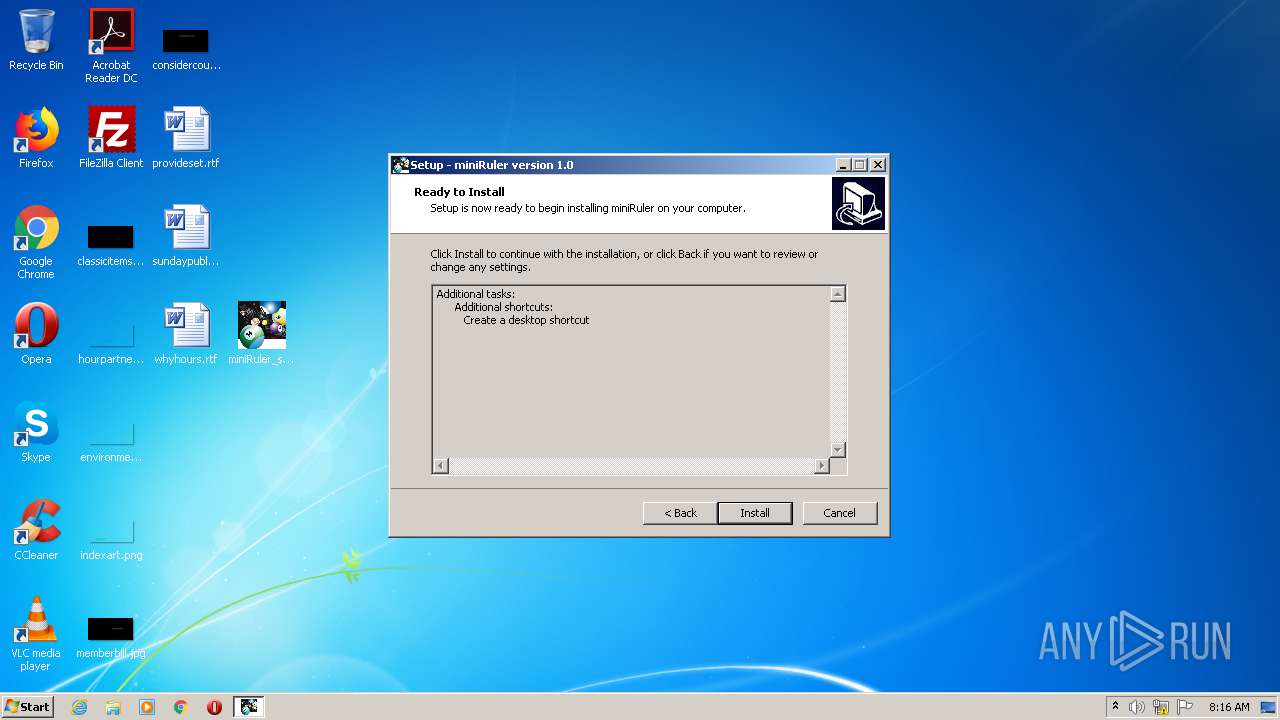
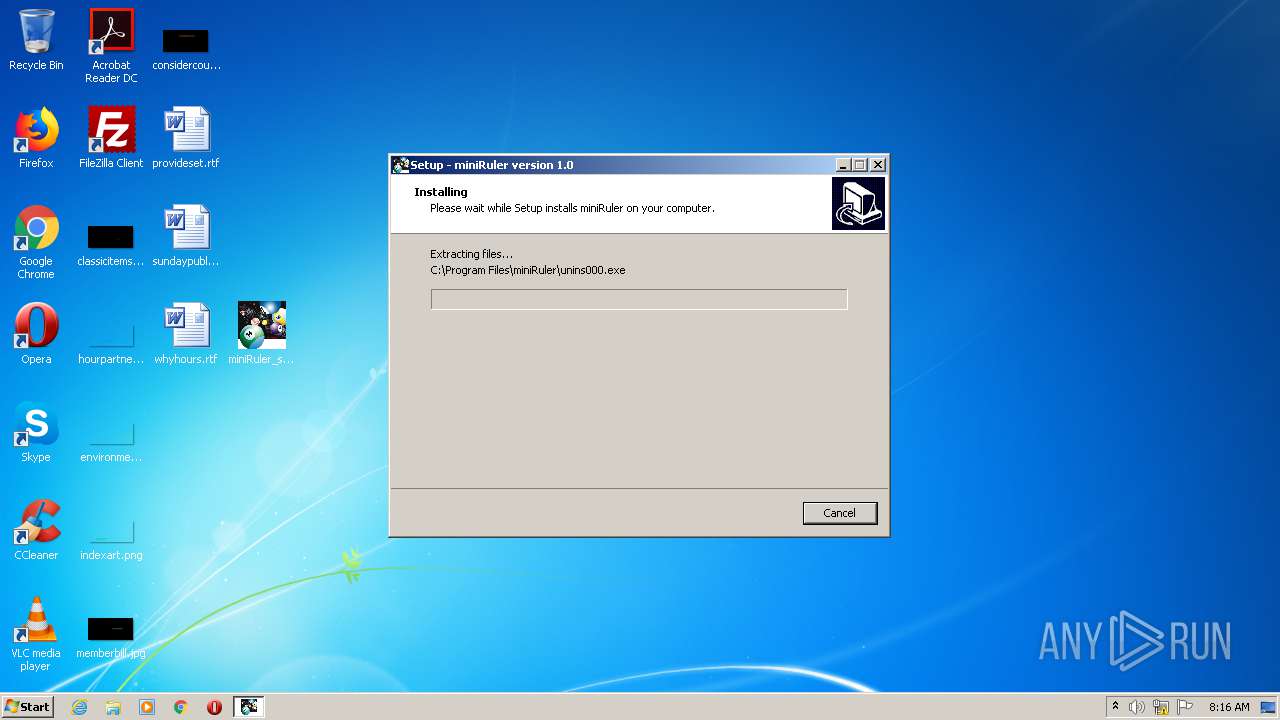
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
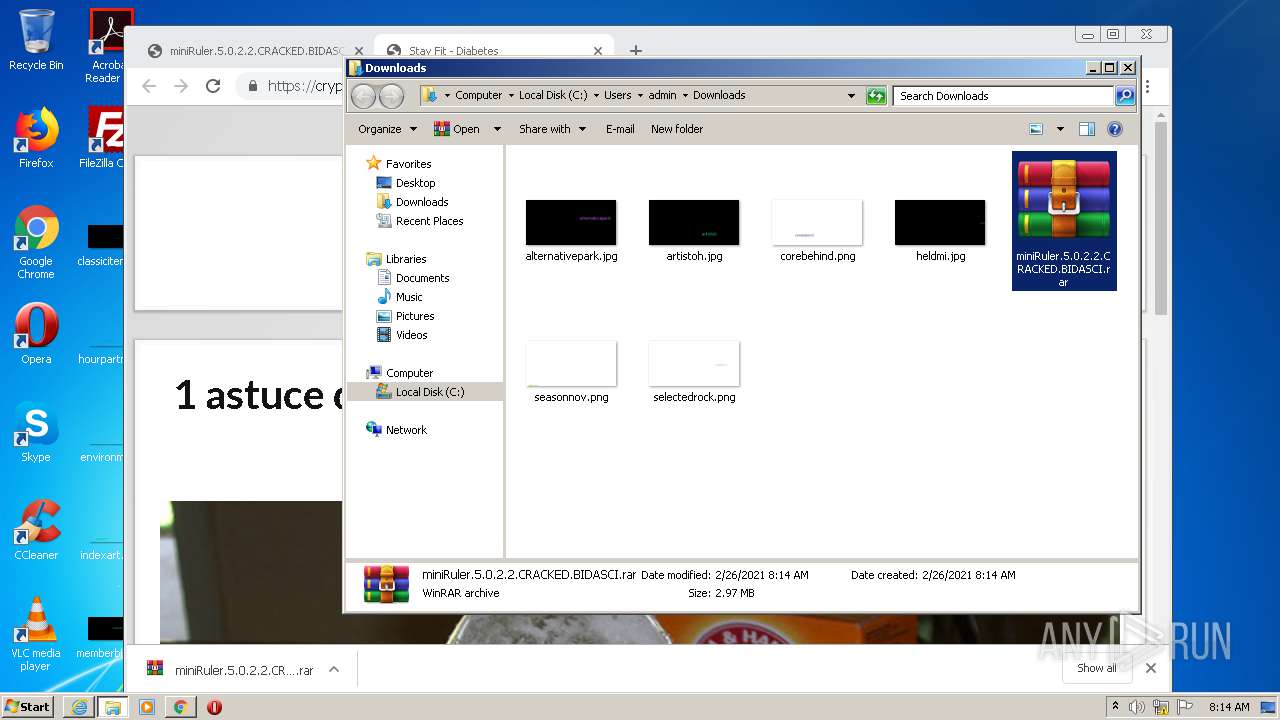
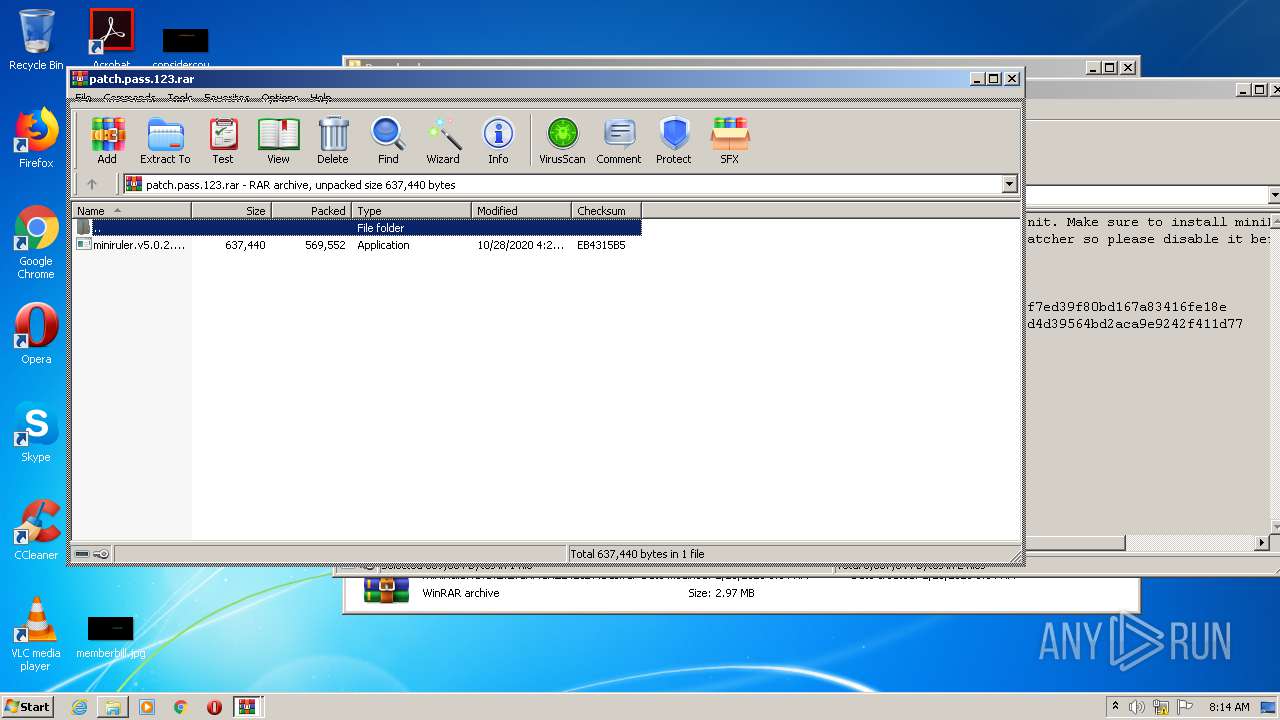
| MD5: | 53D94456F727AA683F0B348E361C1285 |
| SHA1: | E08AA33CB4051A2DBE750DDC7615F7B16EEFC4D9 |
| SHA256: | EF3F8F83645A33F142F66A66F93D57C708C440C6EC7042A640F450A8CAA050E7 |
| SSDEEP: | 3:N8M2sXQXUOGXMYq0+yBs6X+n:2M22QXWcY7xX+n |
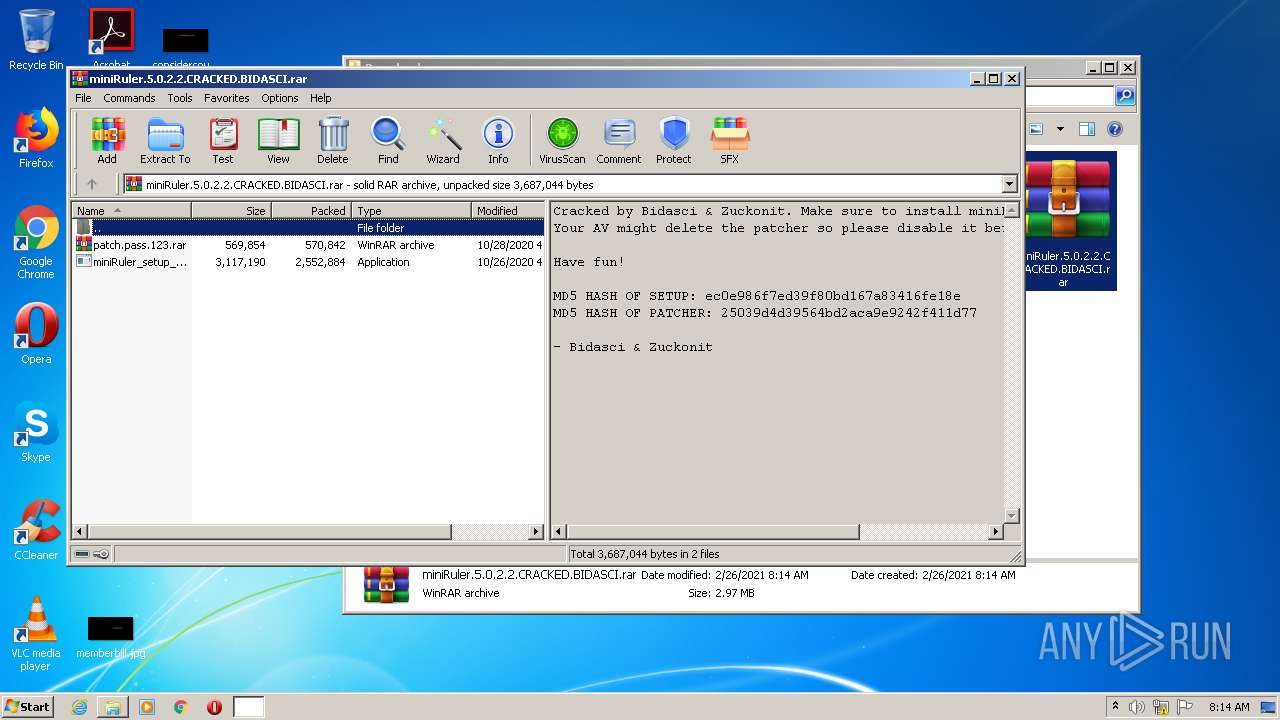
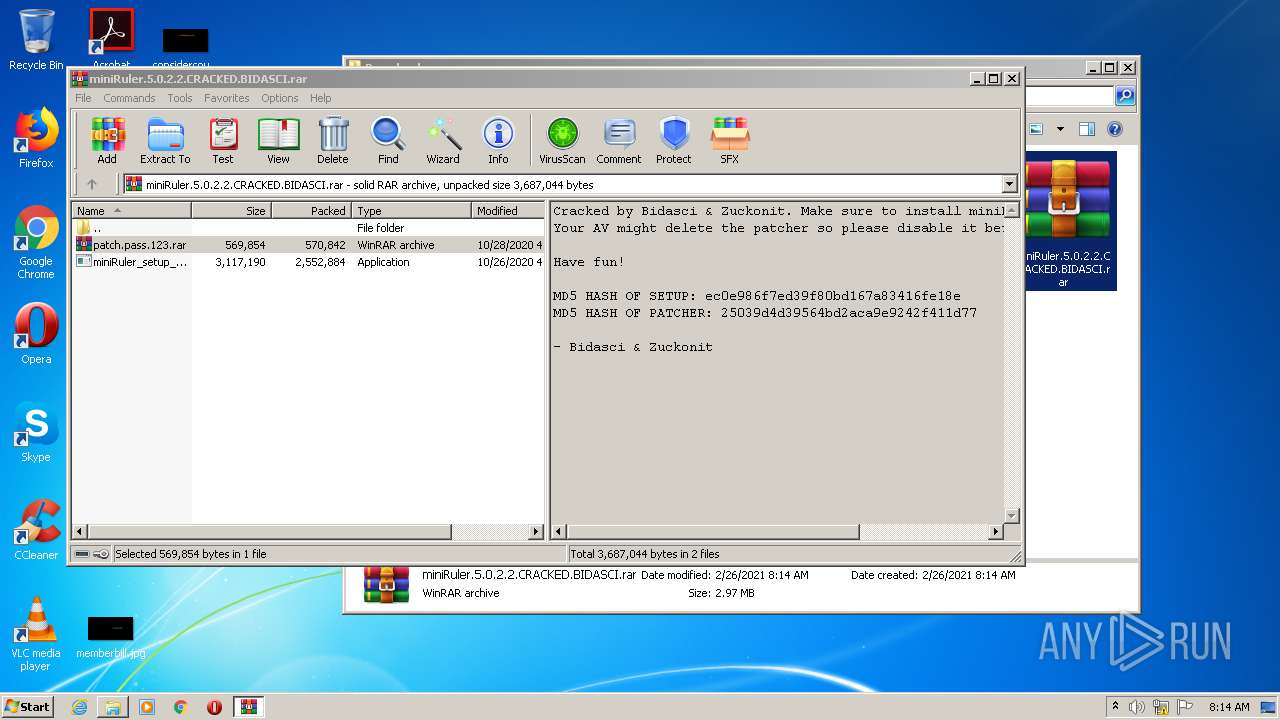
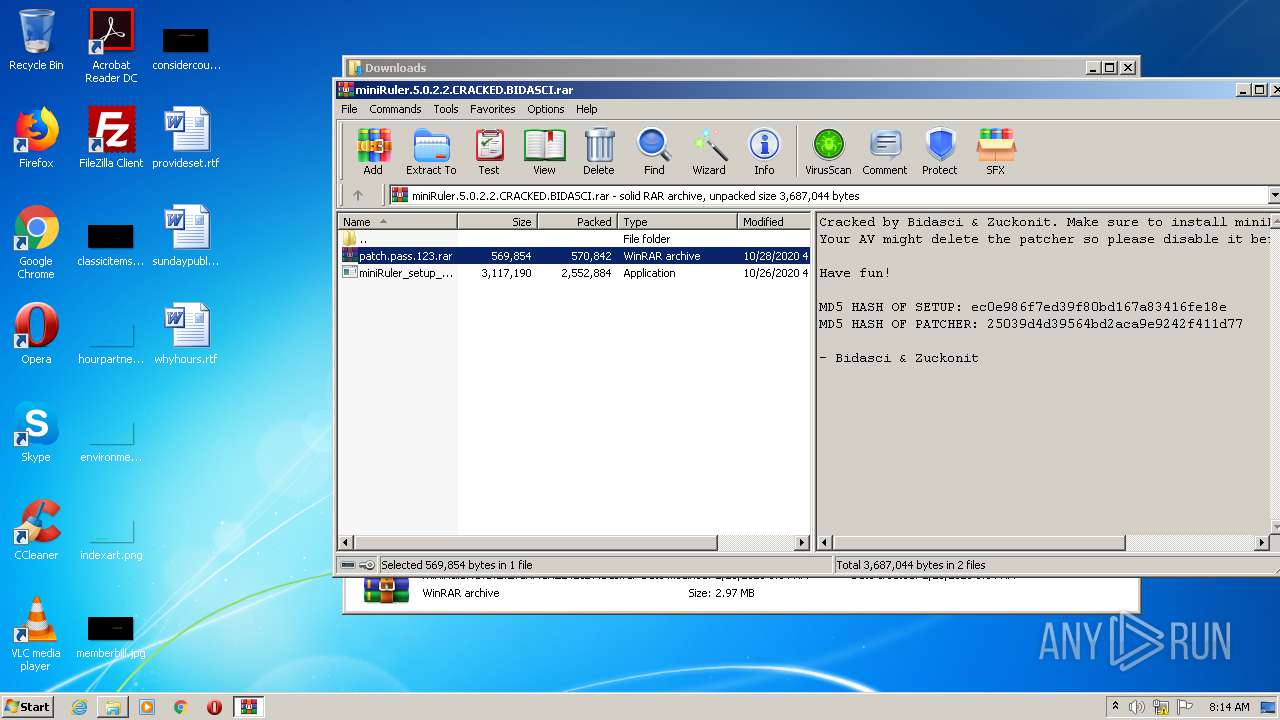
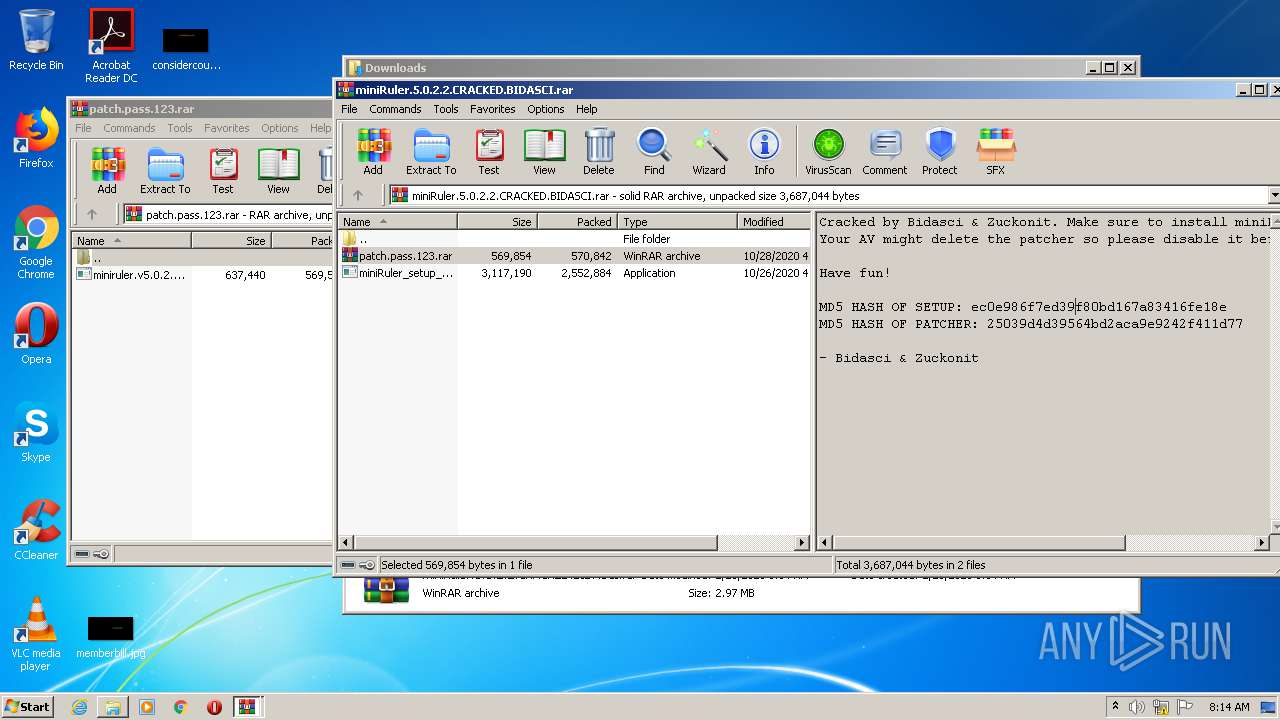
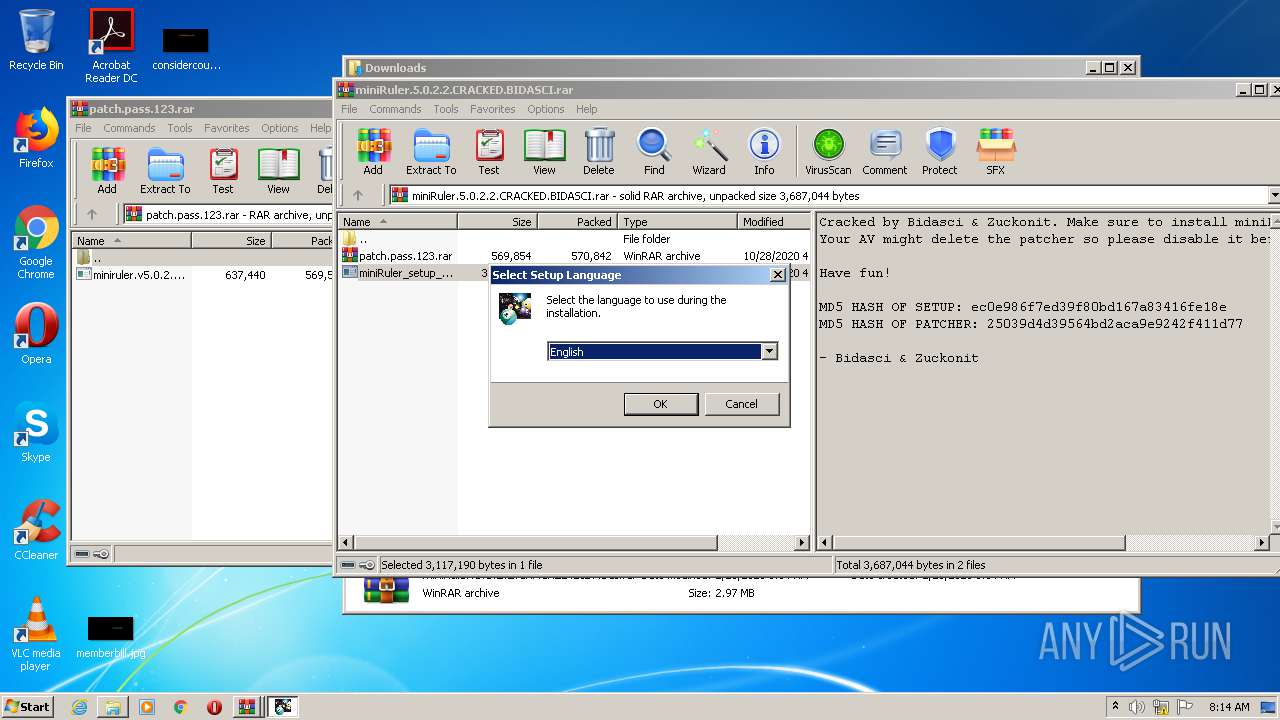
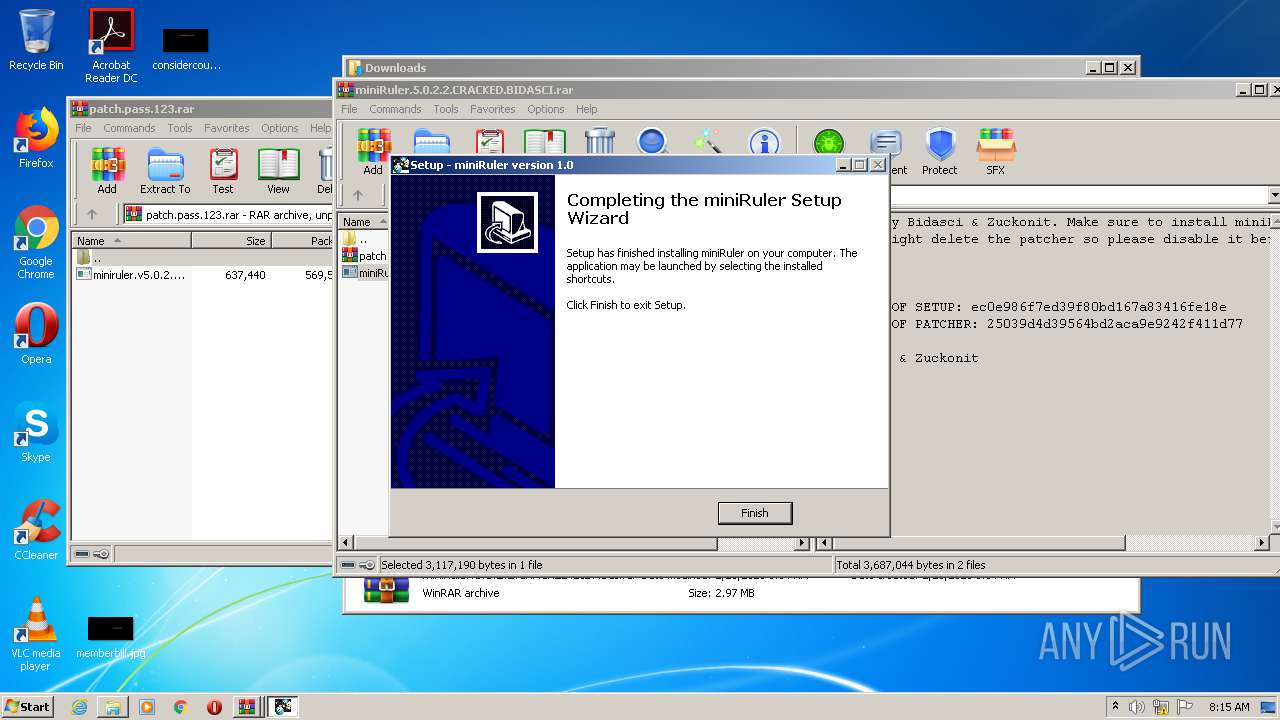
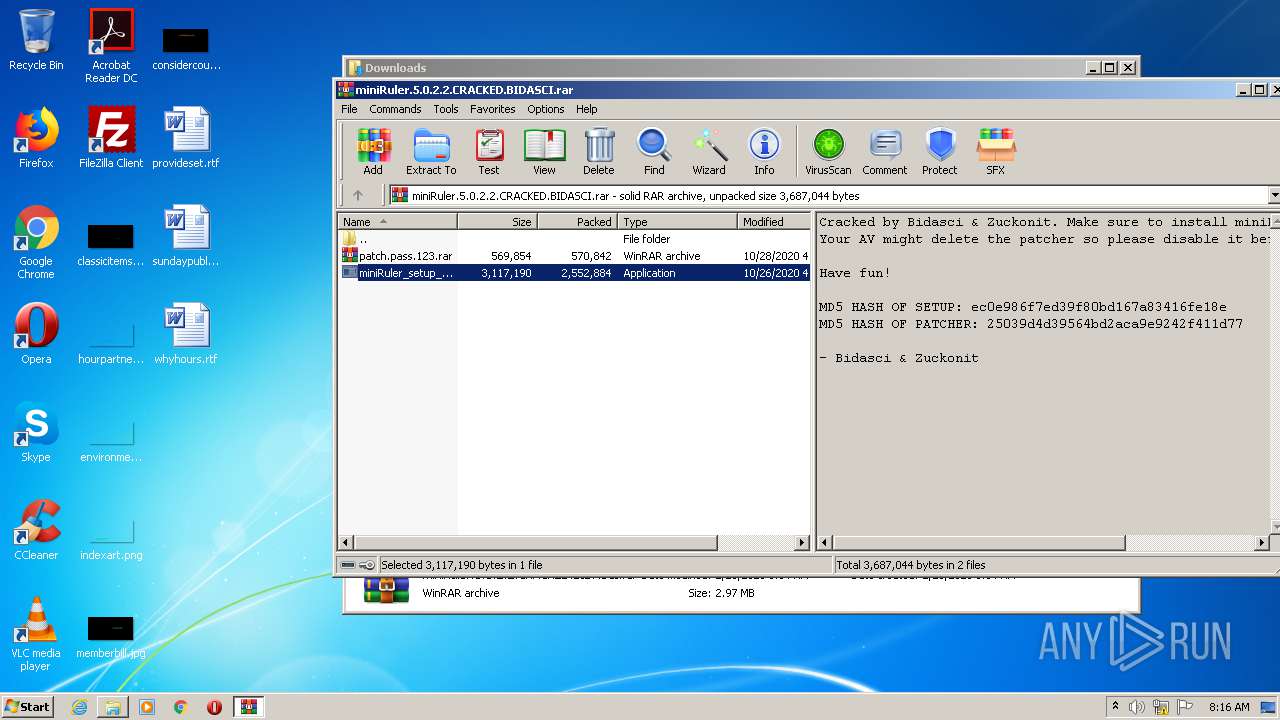
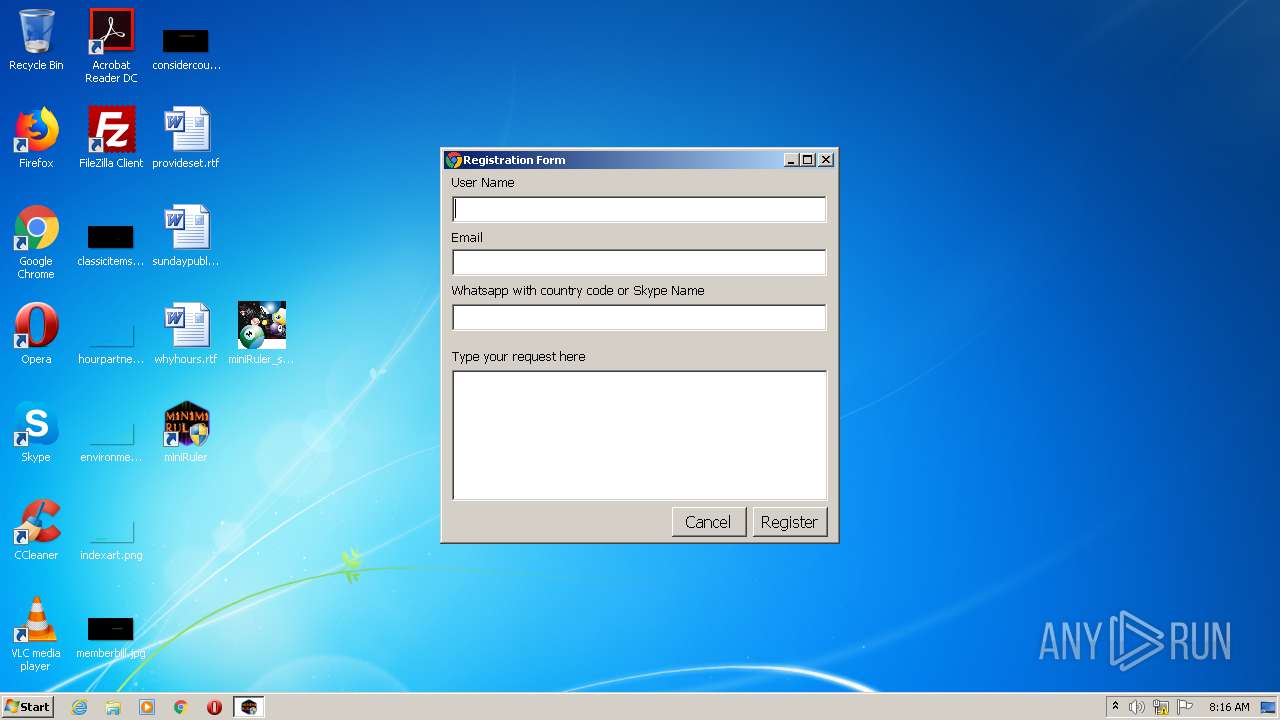
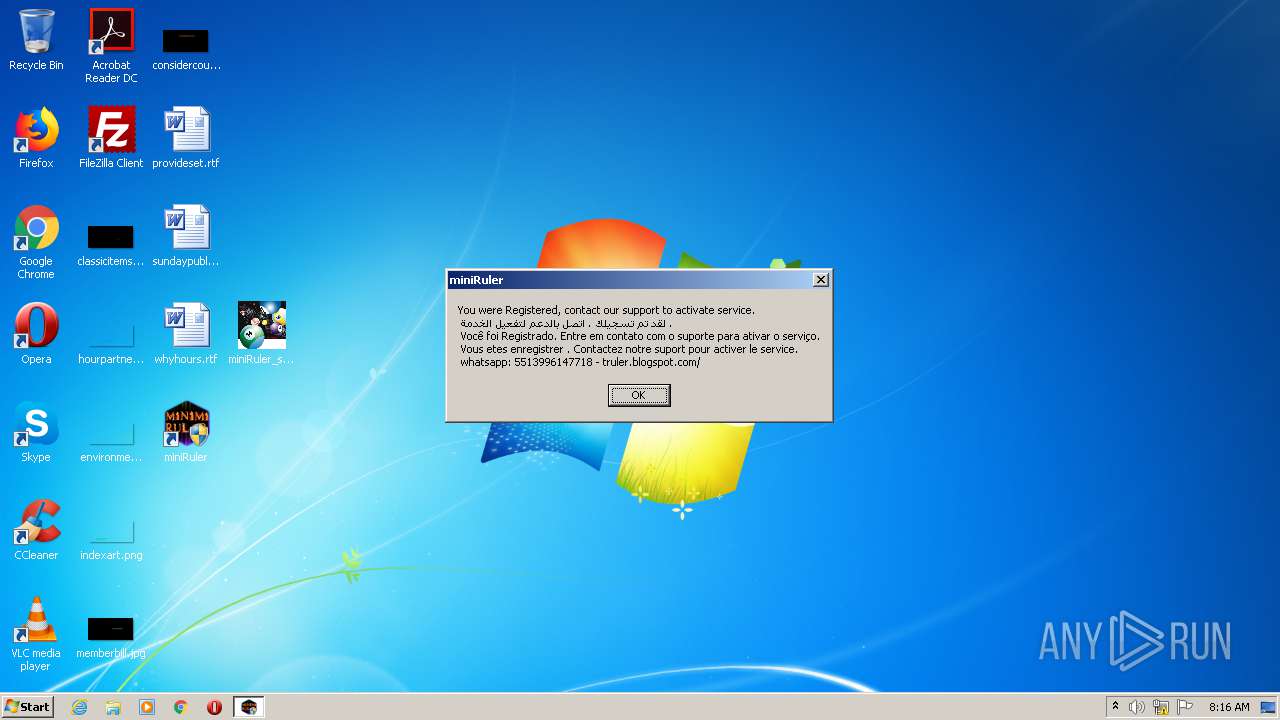
MALICIOUS
Application was dropped or rewritten from another process
- miniRuler_setup_nera.exe (PID: 2628)
- miniRuler_setup_nera.exe (PID: 3000)
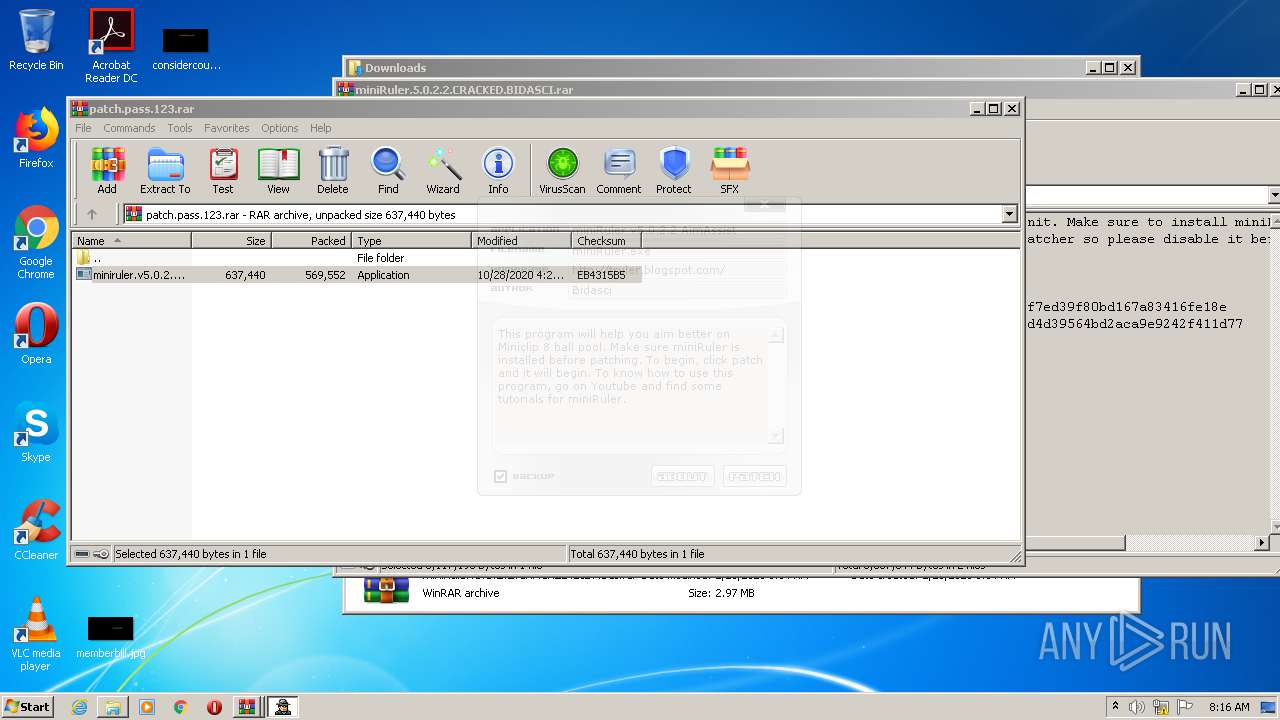
- miniruler.v5.0.2.2.bidasci.patch.exe (PID: 2492)
- miniruler.v5.0.2.2.bidasci.patch.exe (PID: 3464)
- miniRuler_setup_nera.exe (PID: 3356)
- miniRuler_setup_nera.exe (PID: 3828)
- miniRuler.exe (PID: 2528)
- miniRuler.exe (PID: 2164)
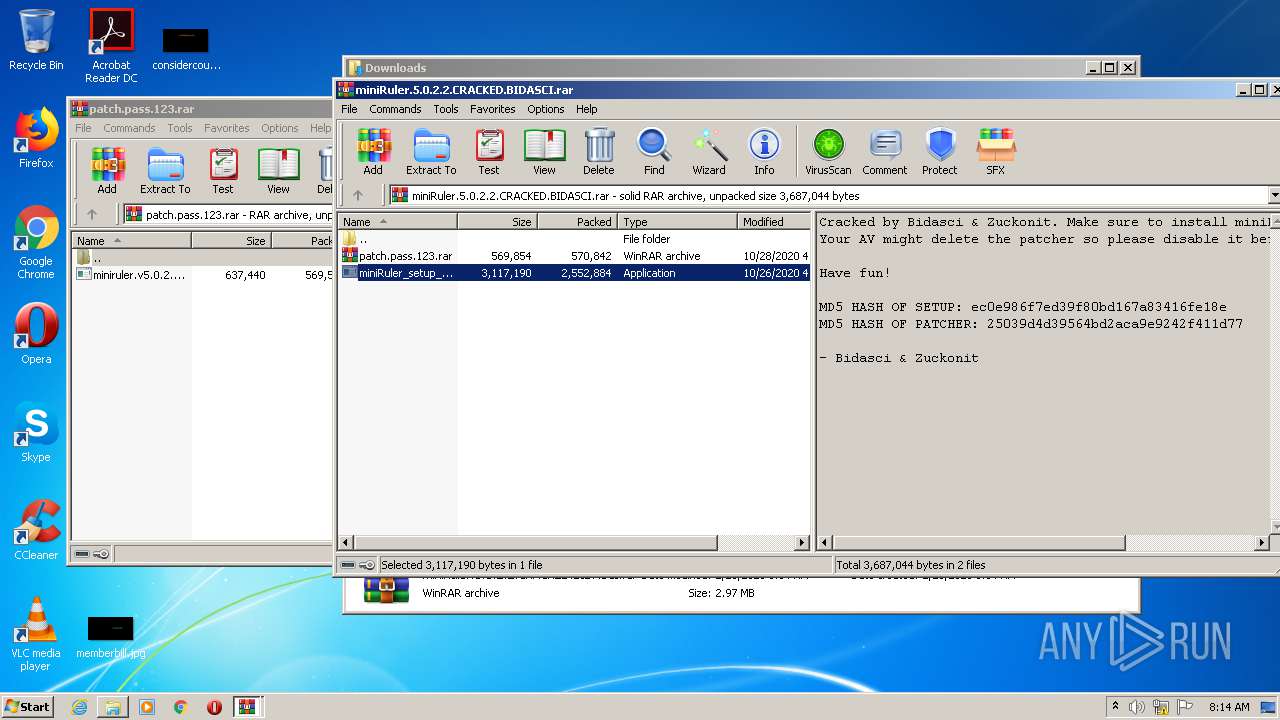
Loads dropped or rewritten executable
- miniruler.v5.0.2.2.bidasci.patch.exe (PID: 2492)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3152)
Application launched itself
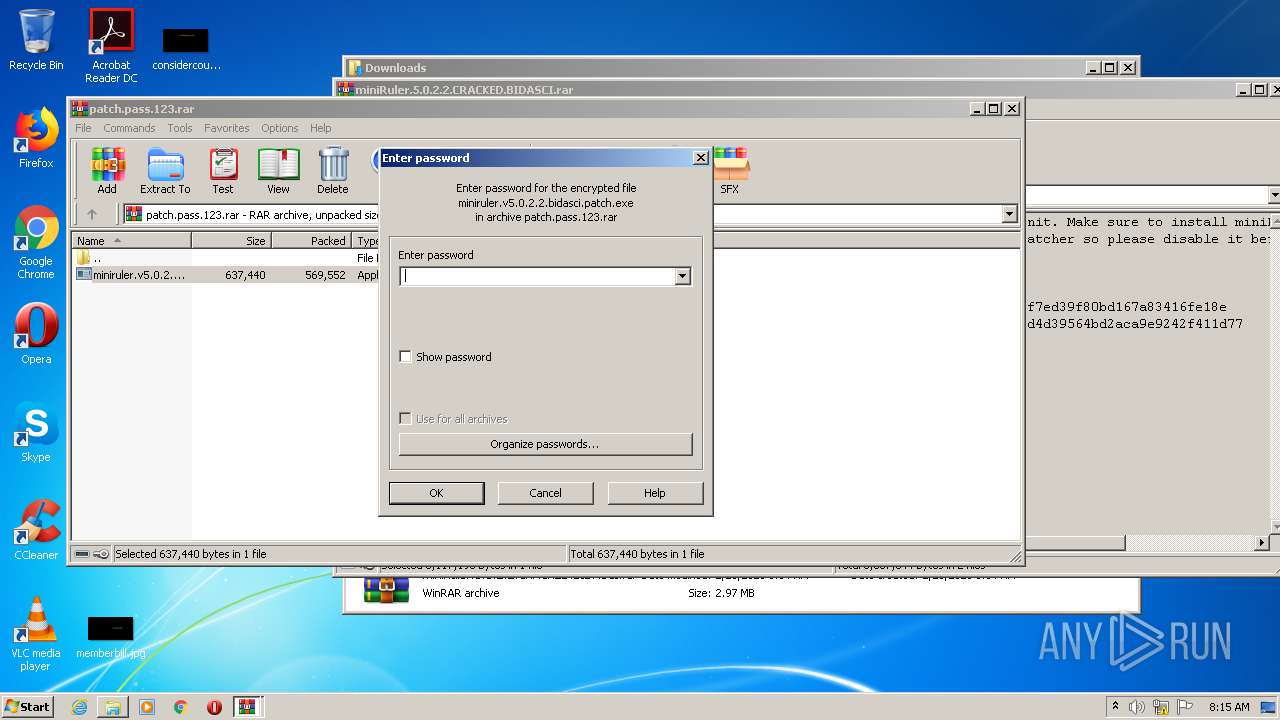
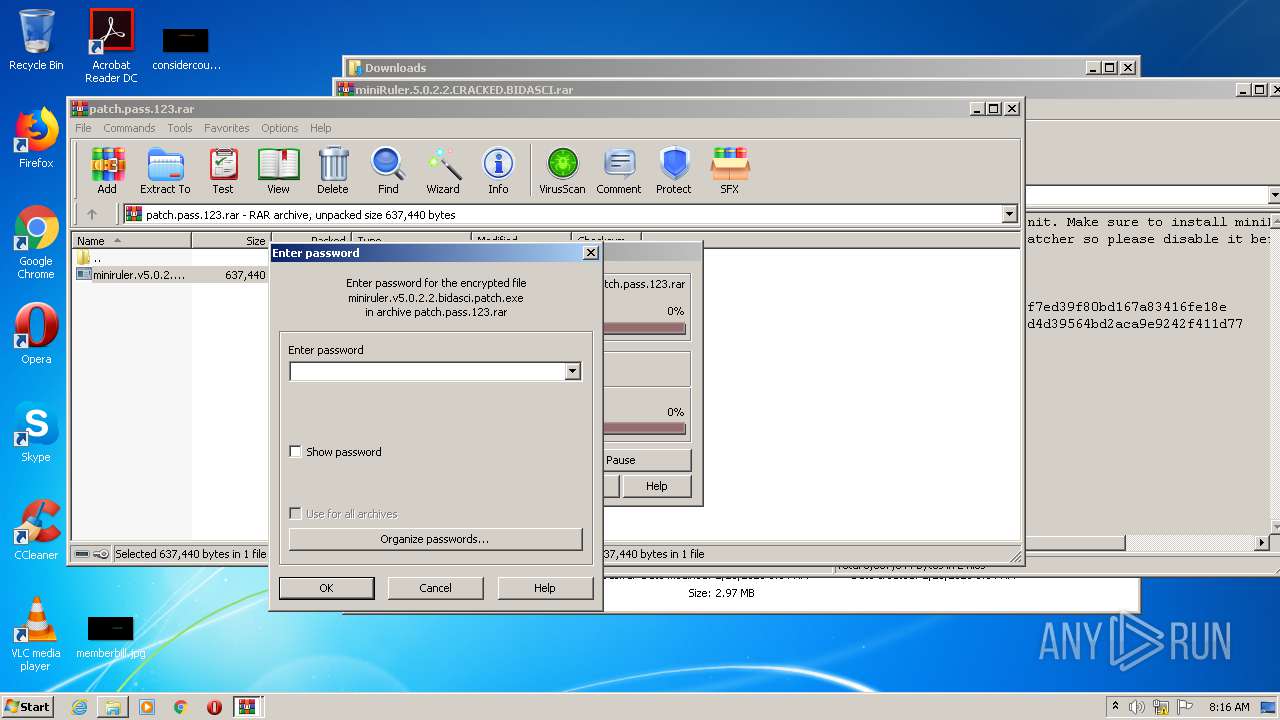
- WinRAR.exe (PID: 2208)
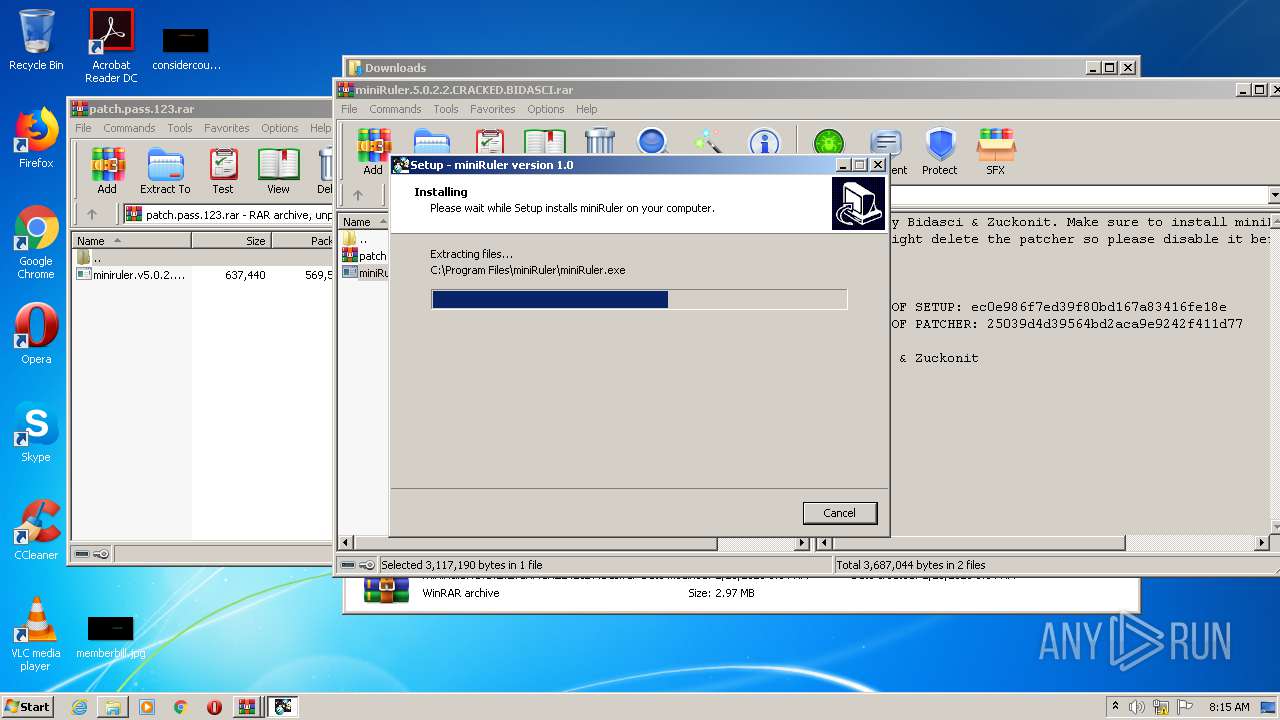
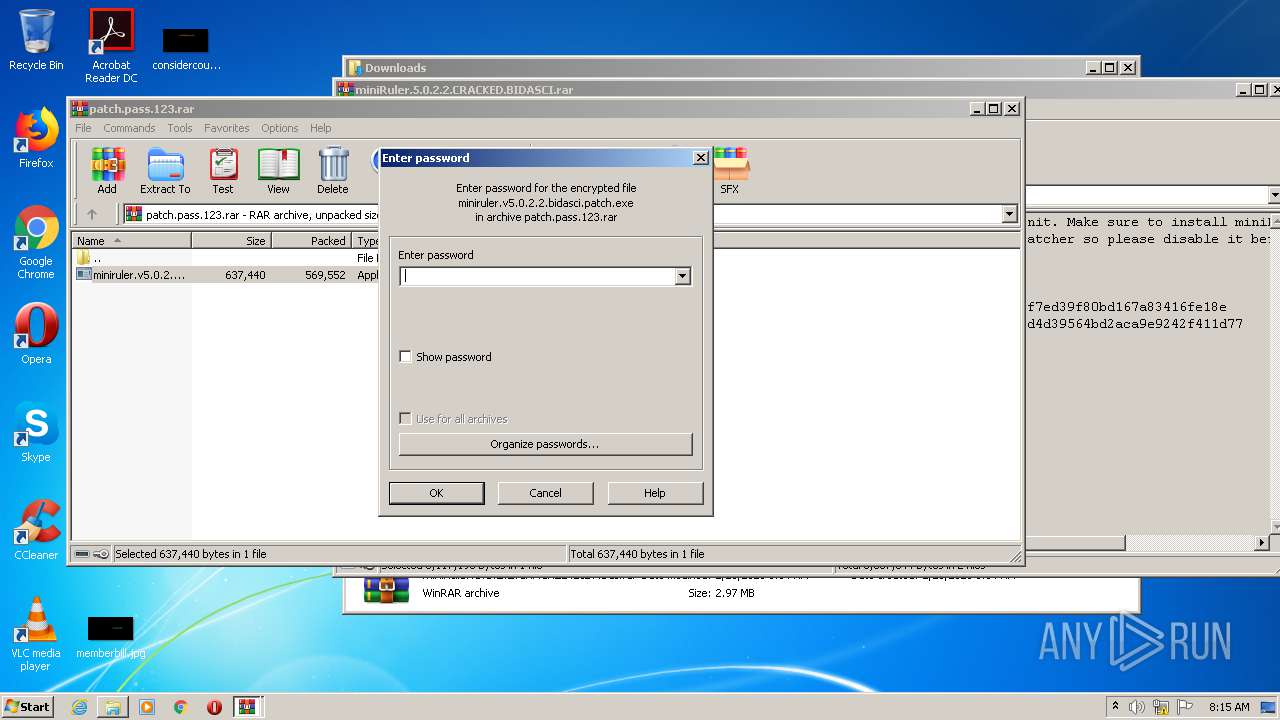
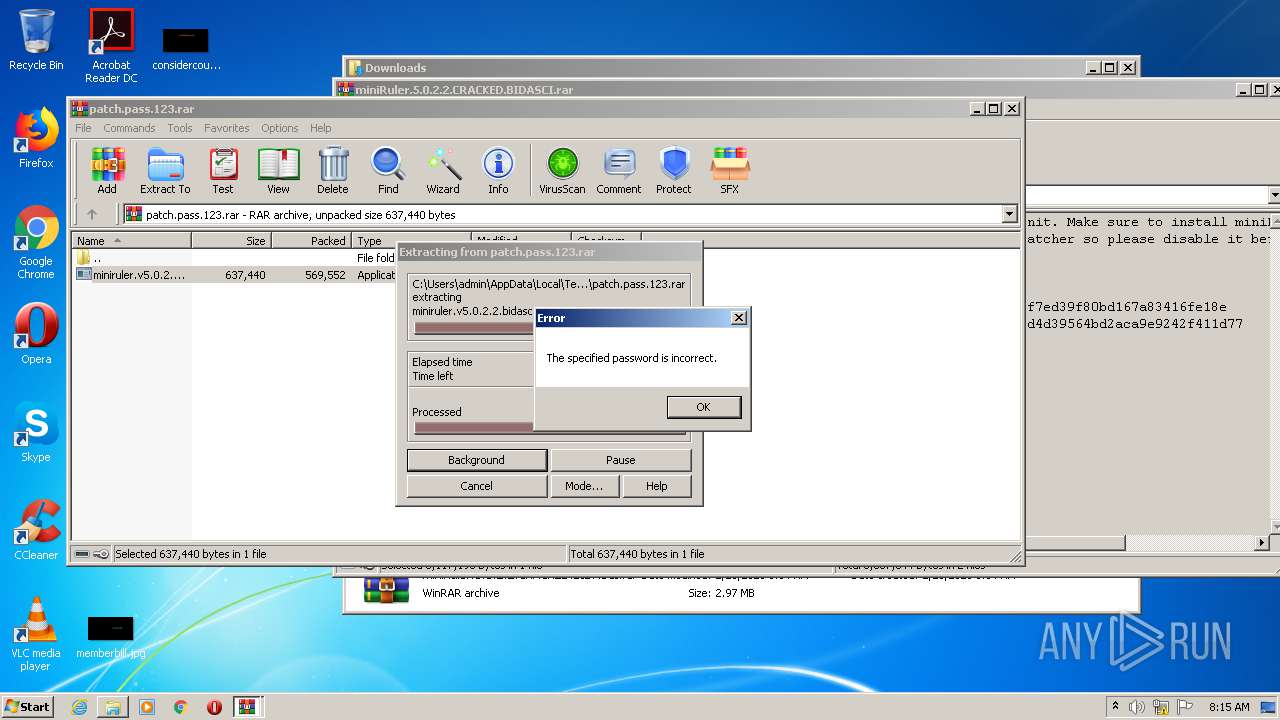
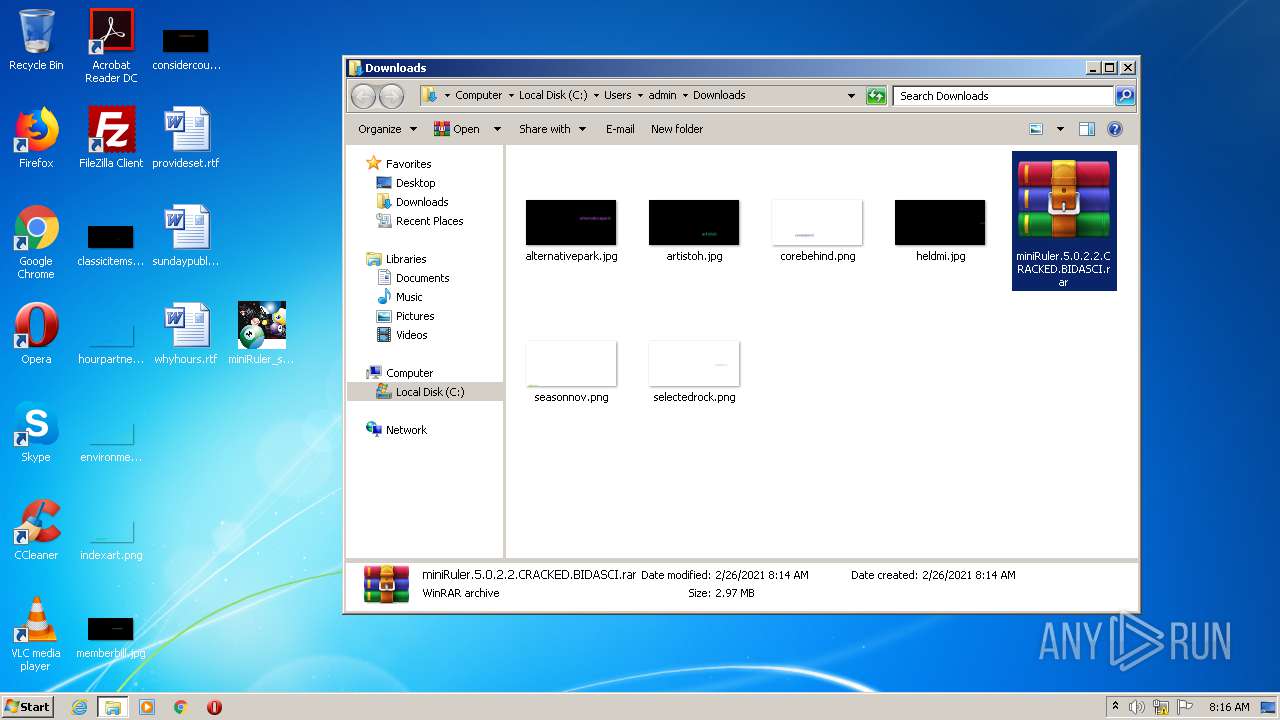
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2208)
- miniRuler_setup_nera.exe (PID: 2628)
- miniRuler_setup_nera.exe (PID: 3000)
- miniRuler_setup_nera.tmp (PID: 3244)
- miniruler.v5.0.2.2.bidasci.patch.exe (PID: 2492)
- miniRuler_setup_nera.exe (PID: 3356)
- WinRAR.exe (PID: 2856)
- miniRuler_setup_nera.exe (PID: 3828)
- miniRuler_setup_nera.tmp (PID: 3364)
Reads Windows owner or organization settings
- miniRuler_setup_nera.tmp (PID: 3244)
- miniRuler_setup_nera.tmp (PID: 3364)
Reads the Windows organization settings
- miniRuler_setup_nera.tmp (PID: 3244)
- miniRuler_setup_nera.tmp (PID: 3364)
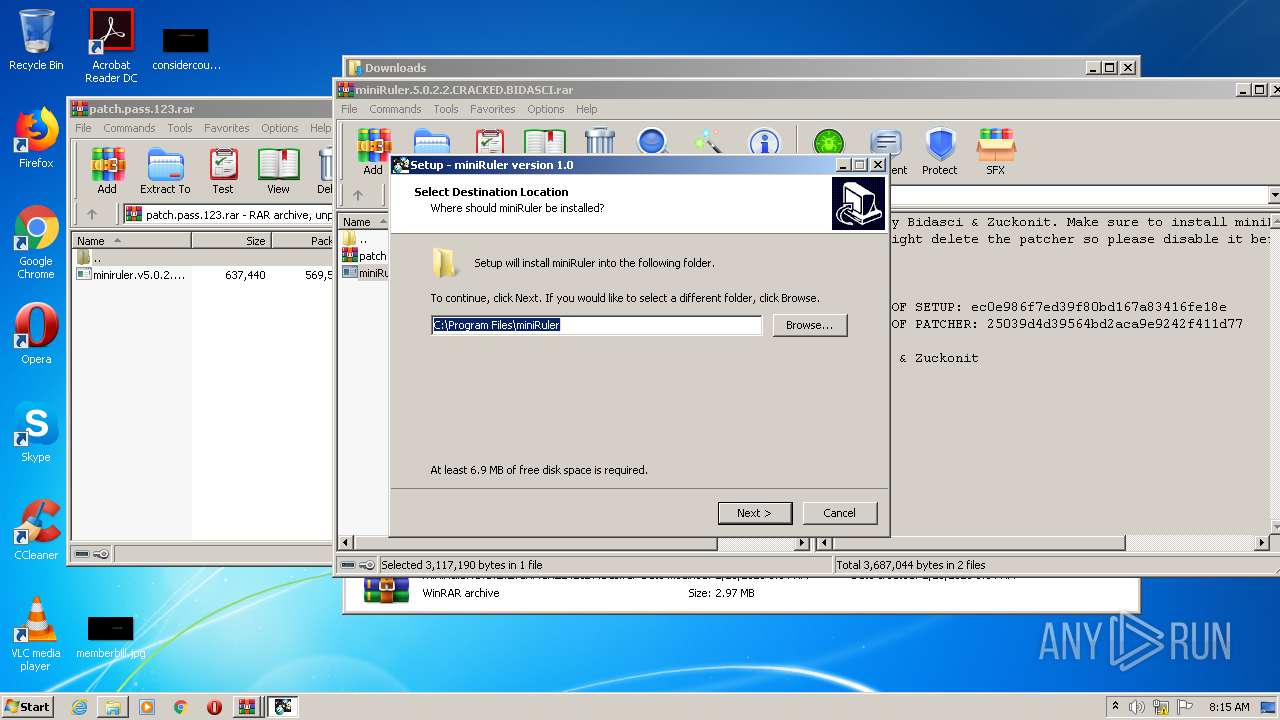
Creates a directory in Program Files
- miniRuler_setup_nera.tmp (PID: 3244)
Drops a file with too old compile date
- miniruler.v5.0.2.2.bidasci.patch.exe (PID: 2492)
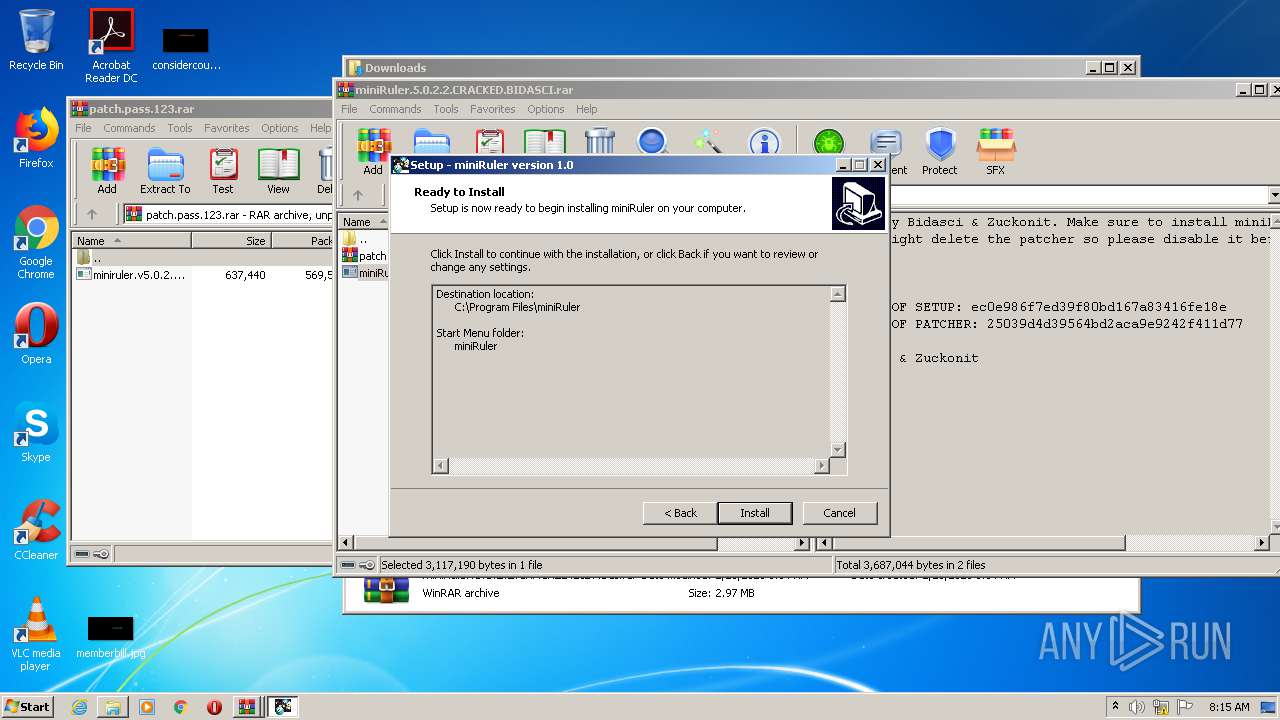
Searches for installed software
- miniRuler_setup_nera.tmp (PID: 3364)
Creates files in the program directory
- miniRuler.exe (PID: 2528)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 1004)
Reads internet explorer settings
- iexplore.exe (PID: 1004)
Creates files in the user directory
- iexplore.exe (PID: 1004)
- iexplore.exe (PID: 2188)
Application launched itself
- iexplore.exe (PID: 2188)
- chrome.exe (PID: 3152)
Changes settings of System certificates
- iexplore.exe (PID: 2188)
Changes internet zones settings
- iexplore.exe (PID: 2188)
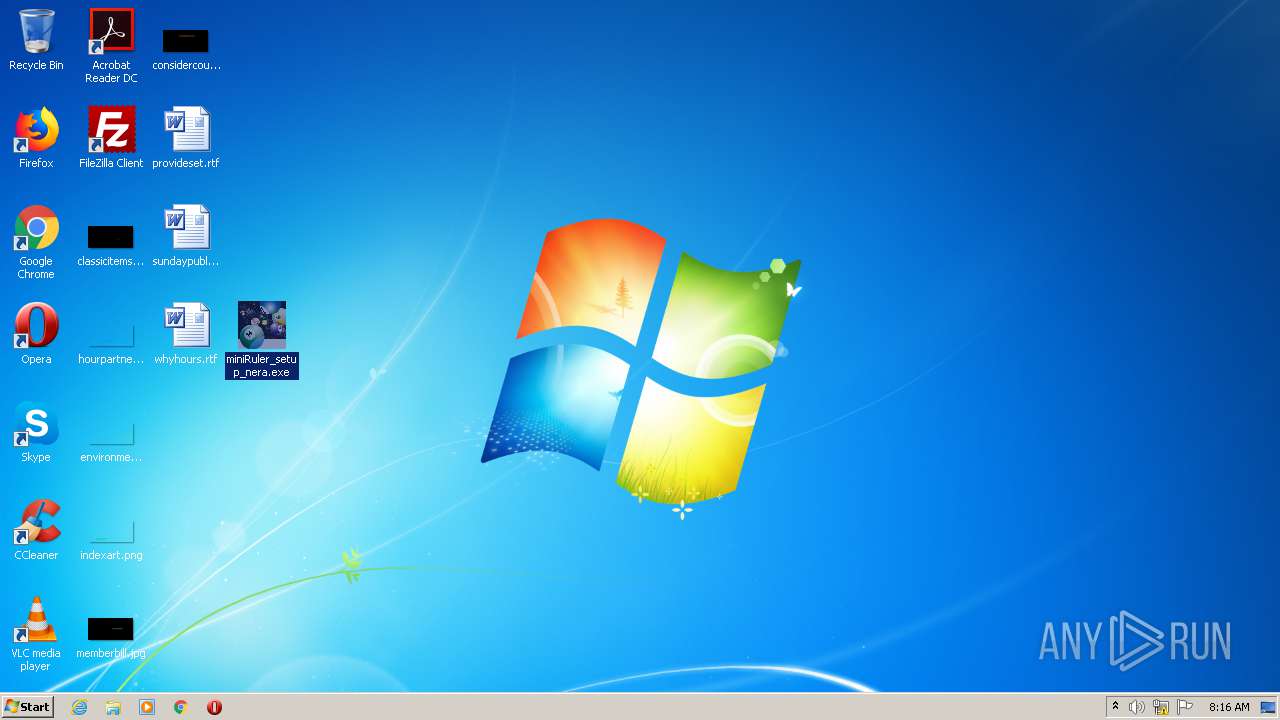
Manual execution by user
- chrome.exe (PID: 3152)
- WinRAR.exe (PID: 2208)
- miniRuler_setup_nera.exe (PID: 3356)
- miniRuler.exe (PID: 2528)
- miniRuler.exe (PID: 2164)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2188)
Reads the hosts file
- chrome.exe (PID: 3152)
- chrome.exe (PID: 2884)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2188)
Application was dropped or rewritten from another process
- miniRuler_setup_nera.tmp (PID: 2312)
- miniRuler_setup_nera.tmp (PID: 3244)
- miniRuler_setup_nera.tmp (PID: 1444)
- miniRuler_setup_nera.tmp (PID: 3364)
Creates a software uninstall entry
- miniRuler_setup_nera.tmp (PID: 3244)
- miniRuler_setup_nera.tmp (PID: 3364)
Creates files in the program directory
- miniRuler_setup_nera.tmp (PID: 3244)
- miniRuler_setup_nera.tmp (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
111
Monitored processes
53
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15729519329460207769 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4896748907303352790 --mojo-platform-channel-handle=3720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x69e2a9d0,0x69e2a9e0,0x69e2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2188 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8441111772395782174 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\AppData\Local\Temp\is-P1EE4.tmp\miniRuler_setup_nera.tmp" /SL5="$301D8,2371567,807424,C:\Users\admin\Desktop\miniRuler_setup_nera.exe" | C:\Users\admin\AppData\Local\Temp\is-P1EE4.tmp\miniRuler_setup_nera.tmp | — | miniRuler_setup_nera.exe | |||||||||||
User: admin Company: nera software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6569514422646644789 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=954187653602704010 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1098741042281252302 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,6178357602867733123,18281382414307144700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=921655031041769706 --mojo-platform-channel-handle=2520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 898
Read events
2 592
Write events
284
Delete events
22
Modification events
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1160484904 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30870551 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
12
Suspicious files
98
Text files
398
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab74FD.tmp | — | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar74FE.tmp | — | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_74769C49053B24360F9391815BF0585B | der | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_74769C49053B24360F9391815BF0585B | binary | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\miniRuler.5.0.2.2.CRACKED[1].htm | html | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\app[1].js | text | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6L3J4UZT.txt | text | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
80
DNS requests
51
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
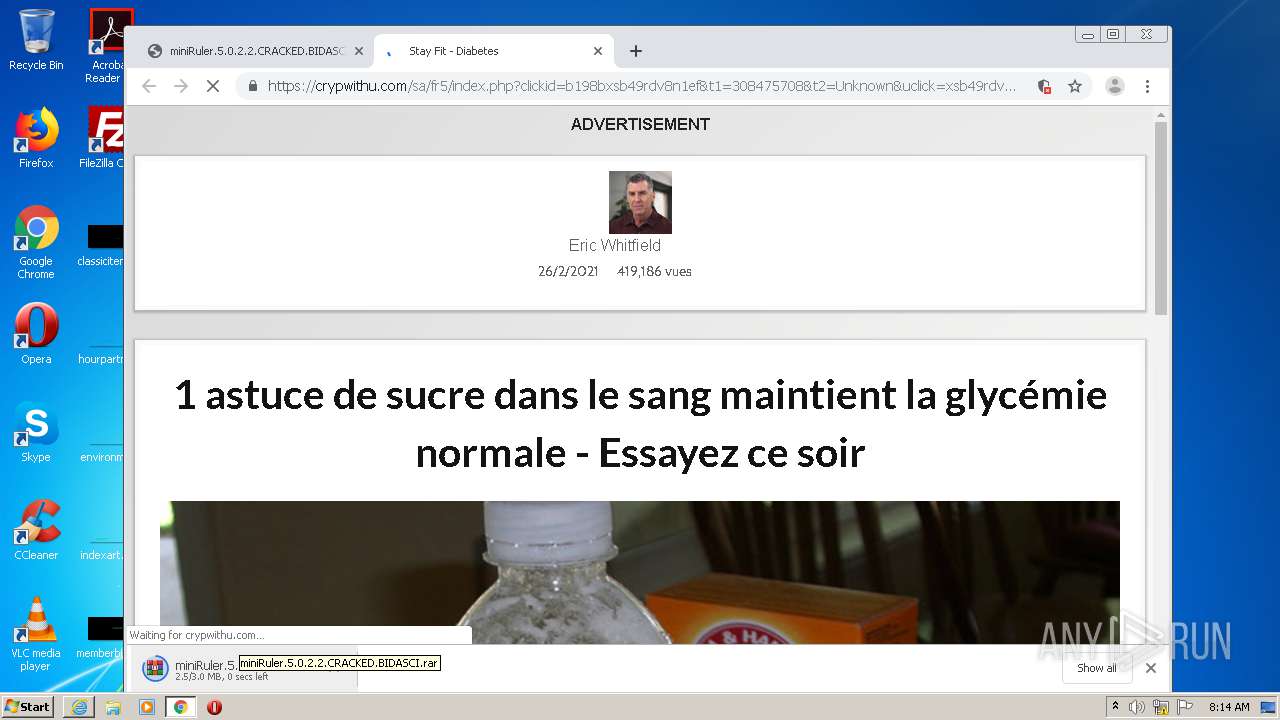
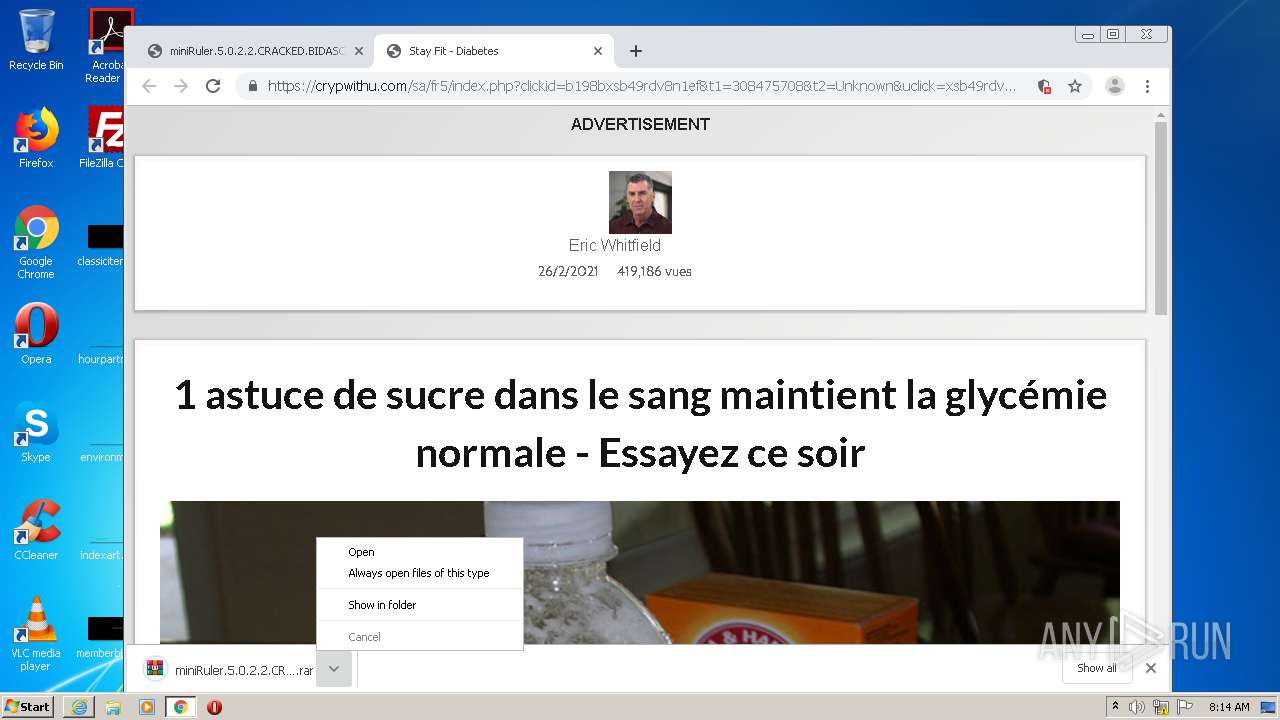
2884 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://infopicked.com/aS/feedclick?s=fXcoZpIQ9sz9nyjafGjN0ObIryAadW7-nGX5km14SumR2x9ubvrPZrUC6hWIeTga6IkCbg7sKEuYDMm3vSUGcDcdXBK6ua5HFwXMzDiLAuK-OTrhrMoN5MZTps4EeX4dsOyE_yhG9DLGVWViaJip_hKp_TFHeXidvZgbJfb5n9xVnESv9uZTcl7KasuddG0pn-RJM7CzoL5DDH2ix4mMj3B9C6I2SzYg84ybo_B_KvWVg_EntSCCbbLxwXlD1A7cjb7ufGESaVW4N5TeuV1uq1ctjXFLFZbDaffYyz5n_vEf-gbVsRGXy4Cuf4EeHlZVy00-zYV_AlYnhZQwRTPG3pOhCDY2ul_DG7y8NwSfnPzJkpWL01KZD4dIw1XEABJKldywHtz2J9f_rQdkhTTJnPsC-aWj4f2F5sy7lZpIEcFKrV_89HBso7IxZjxs0u1UiOO7tyzr8m4w13HnyYfw8p5h7x0_pF-0-kgLkn32ifNLh5v_8_BOtneqRHyjQa4bqO_oGiN9NLNTjZUHGrZsq85gIctuIP9y5GPRw6qe1Ic97nWbqMwF8SjR16MuNhqD8rMdiw7zO3EeEdFrxWSo6qcOU7BZLsIg3XovizcAXjd-4Z013FK9lITtYJiku76k-9wWjmV3K4OGuJFbOrQ0dKyBP7T2hu4jdMc7OxKhBvCHKI5qt9efgi1GEkr0Tf2aOae16MYs_-2AxYMq1c_Ml1h_vzPukVQQu4OELlmLRm0vo-xWu96qcfq_6tx46WSyf-SKhSIB1mAycj6H3AzYttR5hSrvFfluP0LXX4wiKPOZujpGyrOqOZr4vl8sQq_qXqm4AOQ0QrS77b_LpM-v0j5oEKoEFwRlmzLhOwoHJtaZ4jRxdfeF4oN_tyjgZYQbv-_LJOYGptsRFGudcebxUc6F-dACt4RbilSZqhhs5C08jAffcN0ndjYn3kqb_NLYBFr68yLsao_50Awx3xDhft3eCn5KAACSnFdYWMWnv0bQ3bZA2wdDi_KEvvRIg4OgdaxF5ixoS1QAY-4rYdKs_0-pcN4yINgzrtg5Yuugvl7nAA319rQT5cwGXvlfKPPUQFvOfg4yb5RI-VhEmT6WG3hNoGLohWPse4JCp3hoa4-gngA9SL4TWj_LFKaQfdCIV7zGDkXThF6fxRzXxISqKOuPuqwl0TjCrmIrP2lNhVXc1TJLY5jgsYGrivroMtcMcqnNvhGdhwxahSsPlvn6vuXaUOR19twE1uS4jI_UmXUMz-RUi8nAZnqi8nndef0IhhRgl11k0YQUeZBwbSQFOv3KJijJdR0DCzPAjKRW0Vlxv4cWEWW8fiUD5n2n65WDPkUinJsOMwsNczsij9A4vmLlnbCBlQRK0ugXIIKJGst9h04uvGGFJt8pw-VDmwYuSG3fulkNVC8jUkHjxc_arwl-qu6FJ3iciTfTxZa9i69yRSW3l9TPaYvw4gVLSve7Fqeklq2v6BsiYKVJ68R9GlsjRmChuYPS8pA5qrxZdtFcN1G3tnReLB7juoeCFdv_jZC4PWwYLzDgcm6cqkr2ISbnMwD-u9Rfq5257qy4S6llkkLEB146pQ | US | — | — | whitelisted |
2884 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p203248.infopicked.com/adServe/adClick?ai=KbK6RS3RVCSfIRoa0tEsb5zoEDhpYSukAf7UBwyFf_dWl3geJBaKYIaDgaTYSa7X63XaK9p6dSBt-VPrAybZaBnc19aGt8rkRCELinACFl3InhvPmPT4BYf18T9CpHqCT2L9NFyVXF55Q47z-CV1ol2k4XVJzHJXkUYvcc0zaJmktJmalqtYdTexpvVW-m3409glE_mXQqzuCIRdm0Z938z_3QEi3YKP4Beck_20WyNlzoOBX6CyT26WwxxDmdAYZx-Wx37adtCqFYxl-mwIB-4uWOu_Eid1qT9hOgJHcqlq0_AxlYpJO0_zcOQEAmr_Fm3UQKjJlfQmYIJGi_TSUWTfxfs1Jb0VofB33BW-m9pDG-A6O8vm_g3tKy_heZIpllemAWTaPnh7ytE4oS_3pJL4KnOOYIJFKRuNOcPQlyhauS4SJm9wQoLrtg_raixpUqyH51yNysQIn6oQ1yhiTRbRh5WhN0Axej_wmAiUbeoWBGu3Yx722O0dy_yCpLBIIuCJRiown8iNkLg9bBgvMA3uhOQ1qH-F&ui=fXcoZpIQ9sz9nyjafGjN0FY37AsT2AewDS6W1cTWKzjz64Thgjw7kOdZrrnnGWXqPkUinJsOMwsNczsij9A4vmLlnbCBlQRK0ugXIIKJGsvy_6lWCsC1Mw&si=1&oref=30286164771eb5a68a047c937c01cb0e&optunit=sNOoY4uUFdjc0_wlrbLMxQ&rb=oAYhc4sYgTw&rr=0&isco=t | US | — | — | suspicious |
1004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA0zPW1LK6kVbnIocU0gPj0%3D | US | der | 279 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2528 | miniRuler.exe | GET | 200 | 168.235.102.228:80 | http://168.235.102.228/pass.php?p=8&i=%E6%AE%B0%E6%AE%A4%E6%AE%AE%E6%AE%B0%E6%AE%9F%E6%AE%9F%E6%AE%AE%E6%AE%AF&u=%E6%AF%8D%E6%AF%90%E6%AF%99%E6%AF%95%E6%AF%9A&c=%E6%AF%81%E6%AE%BF%E6%AE%B1%E6%AE%BE%E6%AE%99%E6%AE%BC%E6%AE%AF&n=%E6%AF%96%E6%AF%93%E6%AF%92%E6%AF%94%E6%AF%96%E6%AF%93%E6%AF%96%E6%AF%93%E6%AF%94%E6%AF%92%E6%AF%96&e=%E6%AF%93%E6%AF%94%E6%AF%92%E6%AF%96%E6%AF%94%E6%AF%96%E6%AF%93%E6%AF%94%E6%AF%96&w=%E6%AF%93%E6%AF%92%E6%AF%94%E6%AF%96%E6%AF%93%E6%AF%93%E6%AF%94%E6%AF%96%E6%AF%92%E6%AF%96&o=%E6%AF%93%E6%AF%92%E6%AF%94%E6%AF%96%E6%AF%93%E6%AF%94%E6%AF%96%E6%AF%93%E6%AF%94%E6%AF%96%E6%AF%92%E6%AF%93%E6%AF%94%E6%AF%96 | US | text | 48 b | unknown |
1004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA0zPW1LK6kVbnIocU0gPj0%3D | US | der | 279 b | whitelisted |
1004 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1004 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
1004 | iexplore.exe | 151.101.2.133:80 | ocsp2.globalsign.com | Fastly | US | malicious |
1004 | iexplore.exe | 151.101.66.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2188 | iexplore.exe | 13.107.22.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1004 | iexplore.exe | 151.101.130.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2188 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2884 | chrome.exe | 142.250.185.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2188 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1004 | iexplore.exe | 65.9.67.193:443 | djv99sxoqpv11.cloudfront.net | AT&T Services, Inc. | US | unknown |
2884 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ocsp.digicert.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
ocsp2.globalsign.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
s.symcd.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |