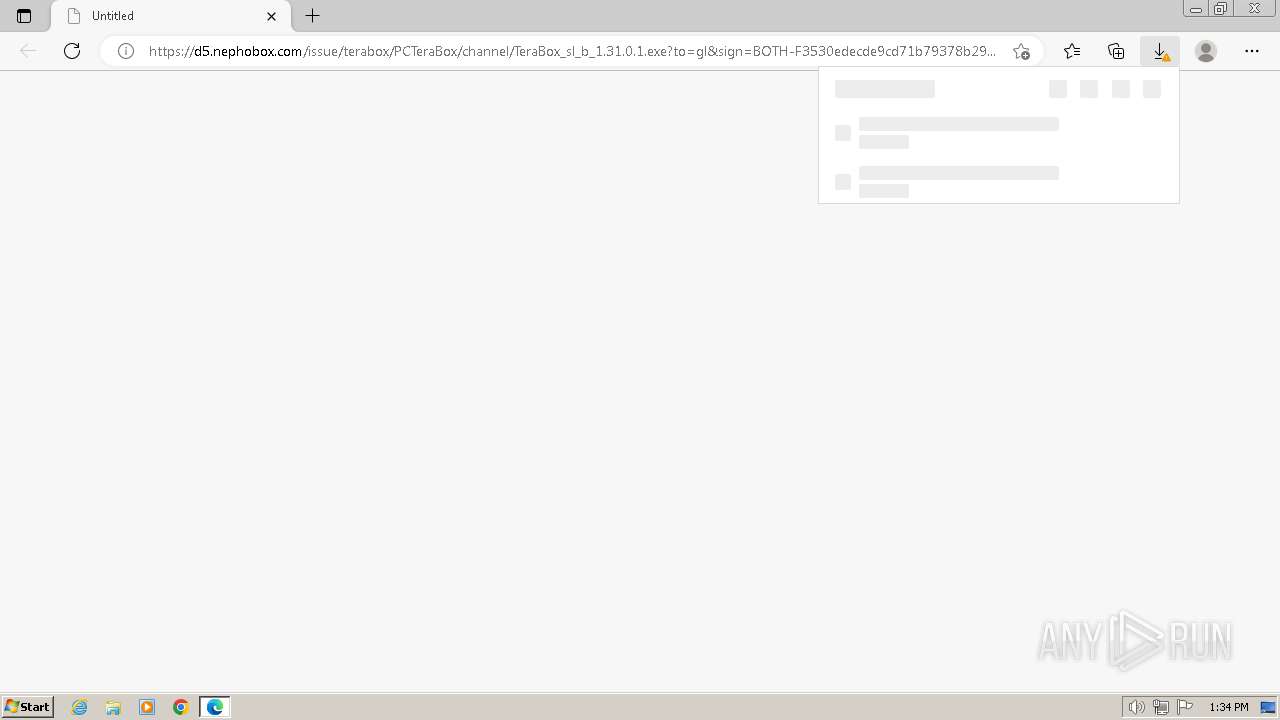
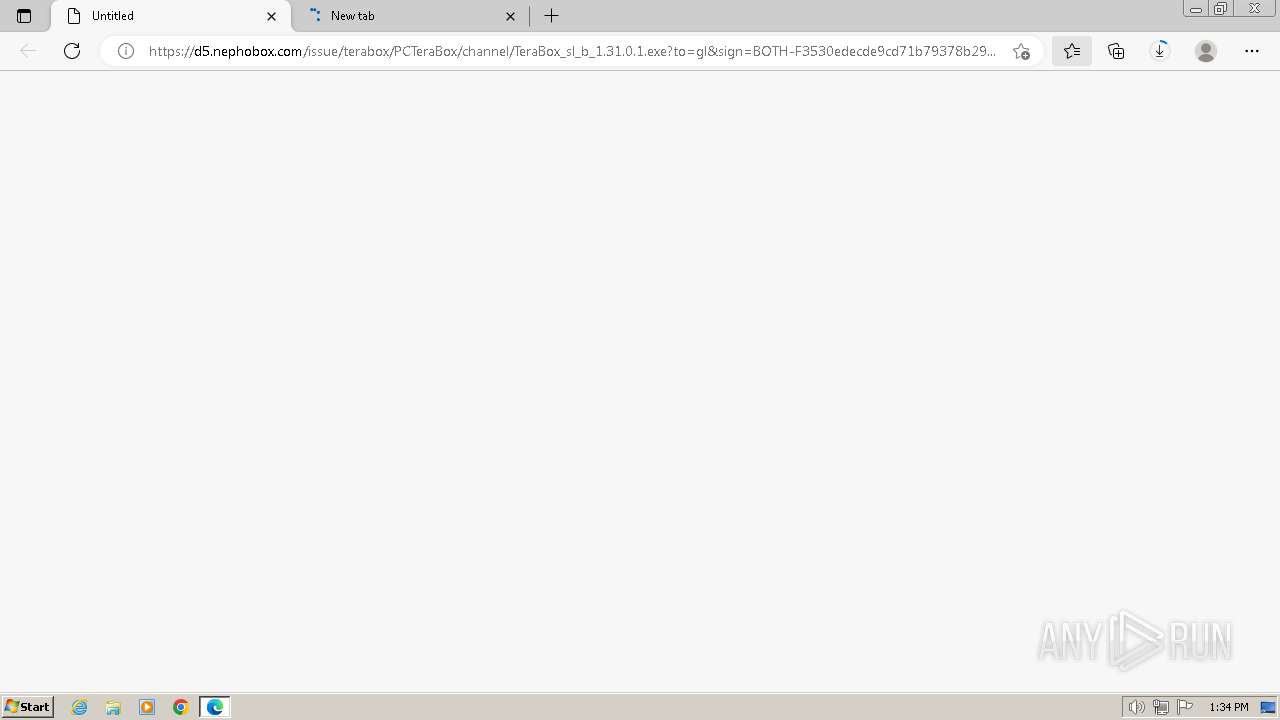
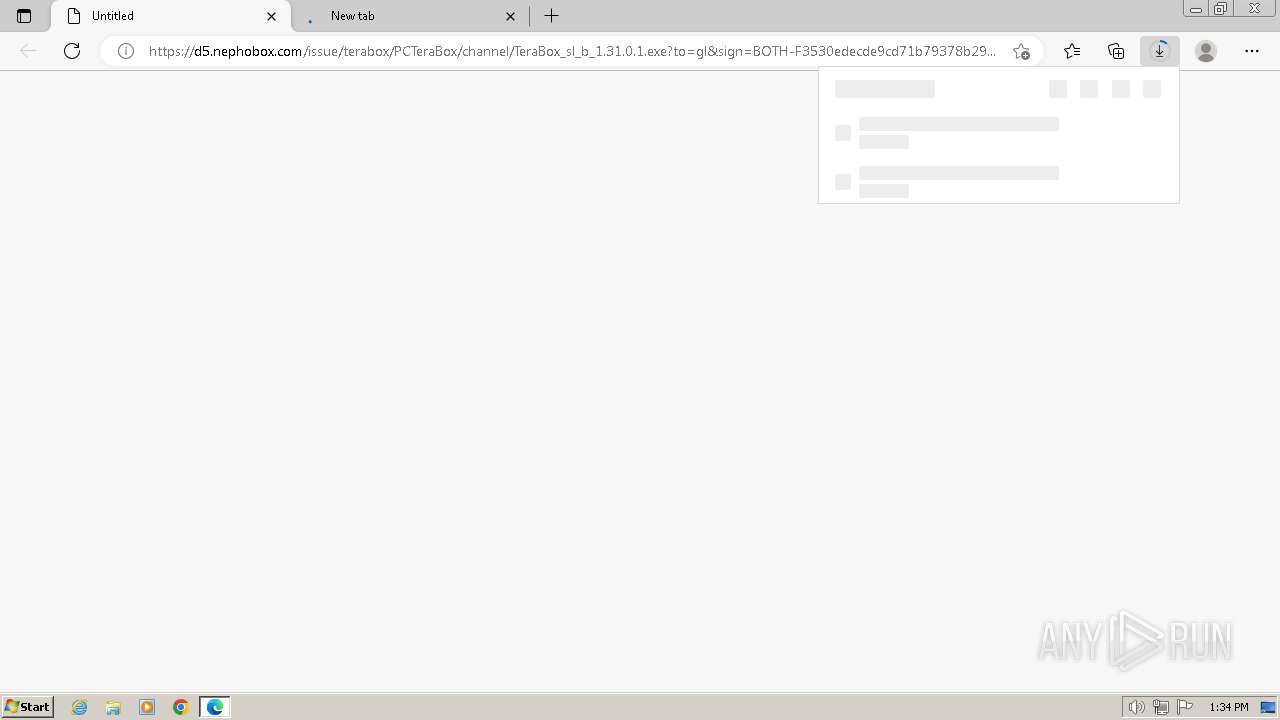
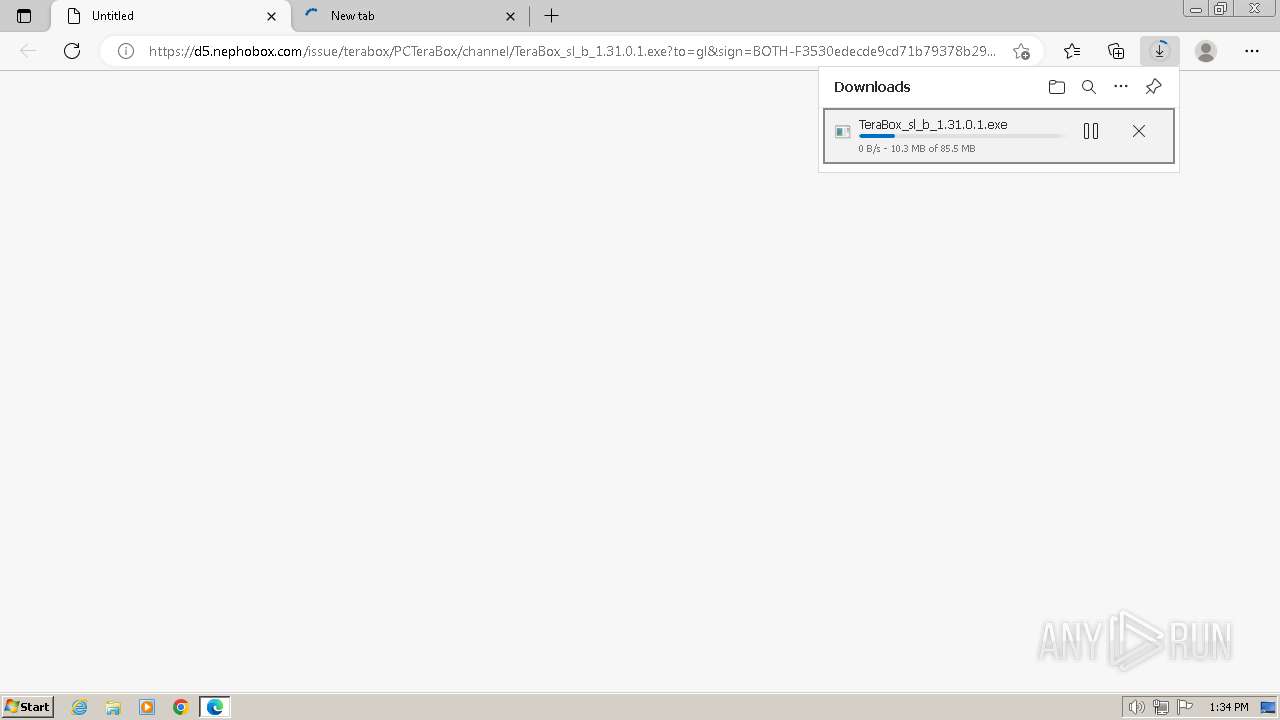
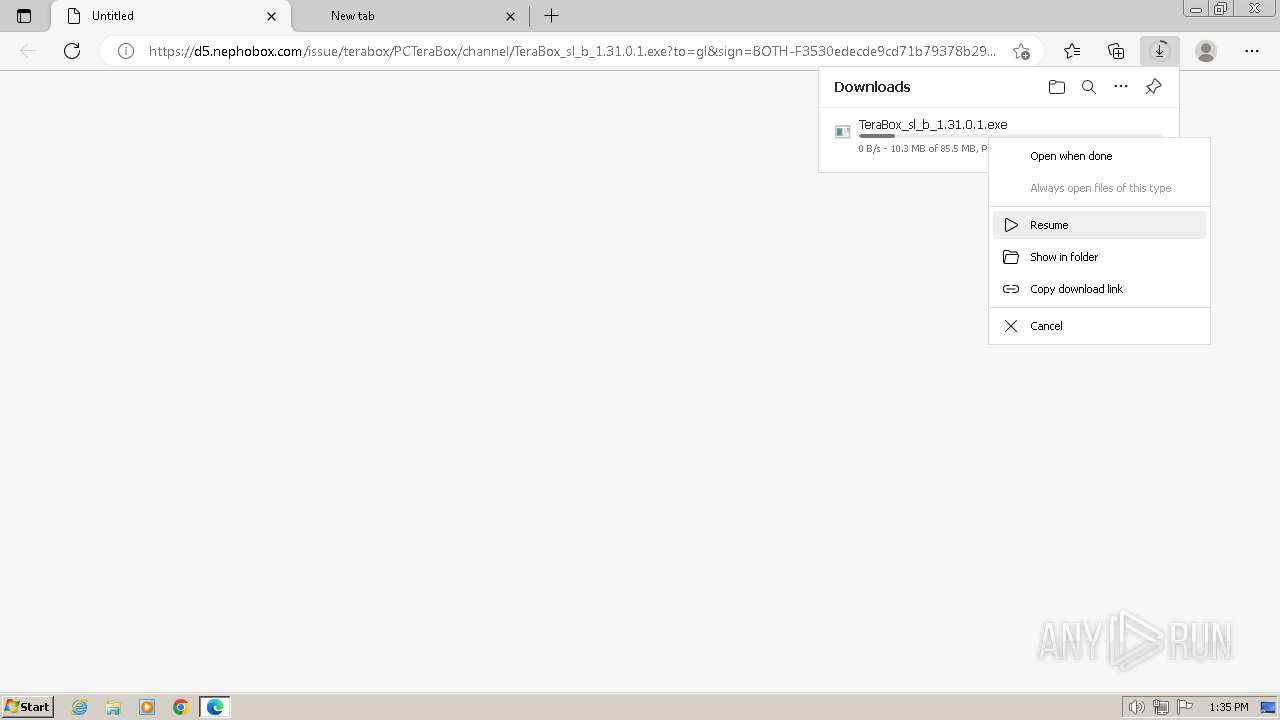
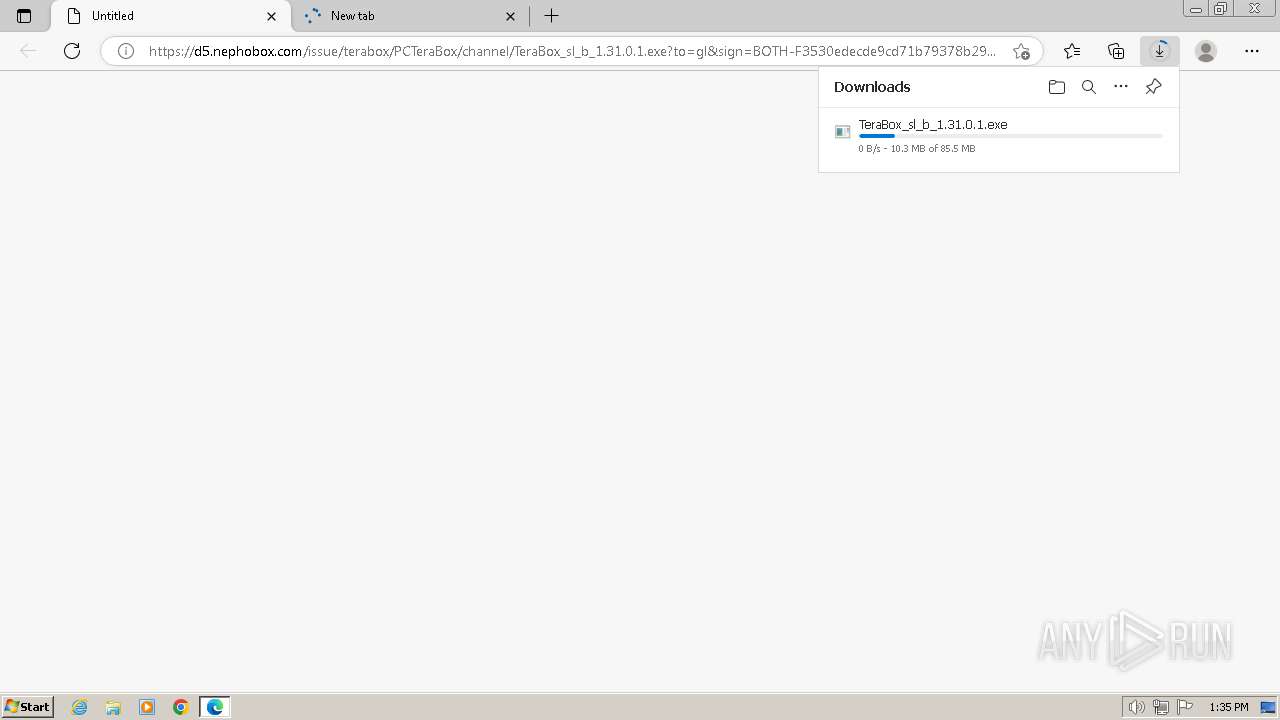
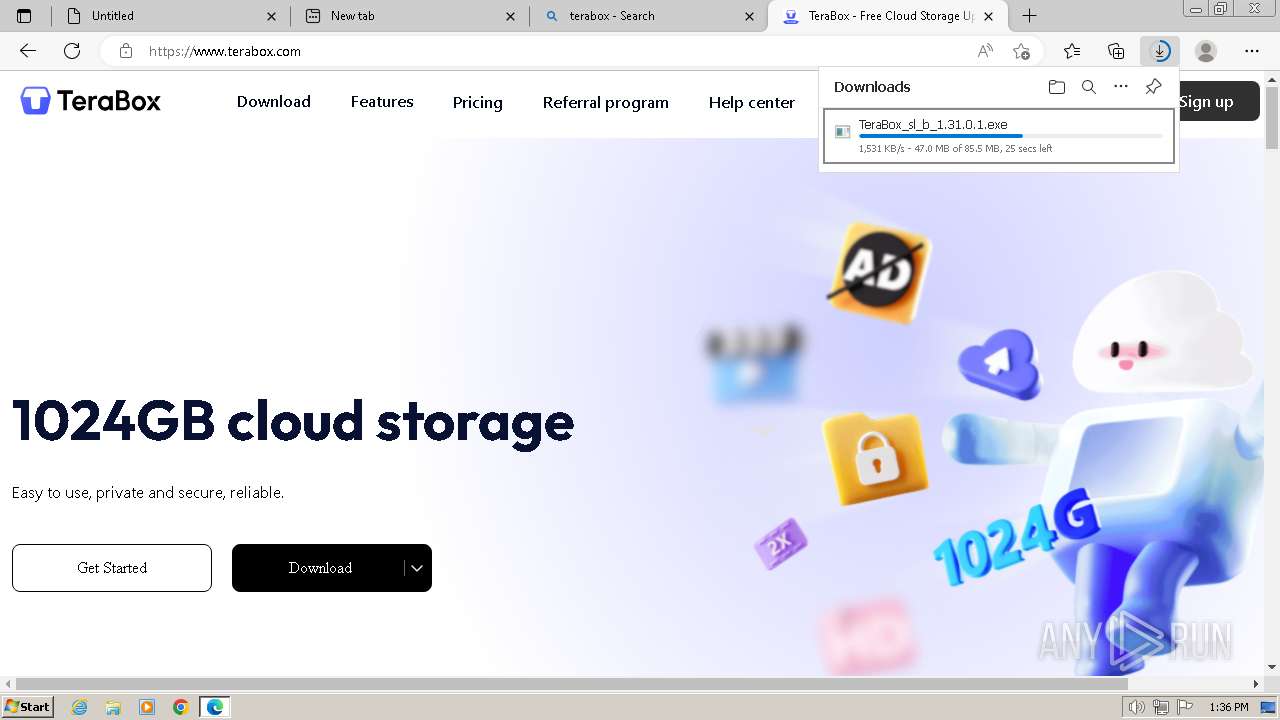
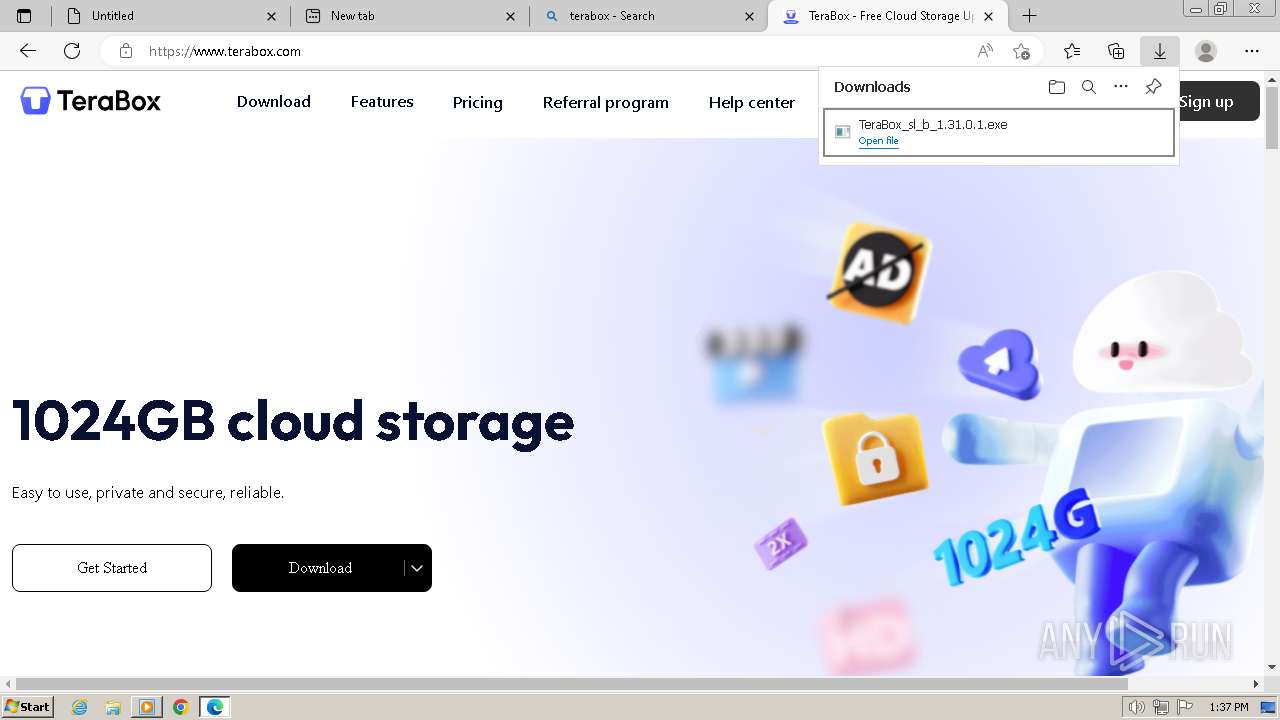
| URL: | https://d5.nephobox.com/issue/terabox/PCTeraBox/channel/TeraBox_sl_b_1.31.0.1.exe?to=gl&sign=BOTH-F3530edecde9cd71b79378b290804a96-Dw1qDqurhvz0szqGrSOHCqTWBAk%3D®ion=tky&pkey=000050ef6c93cfbbbe4ce6416ff1ec8488ab |
| Full analysis: | https://app.any.run/tasks/90a5371e-b10c-4376-afef-e77eea517d7c |
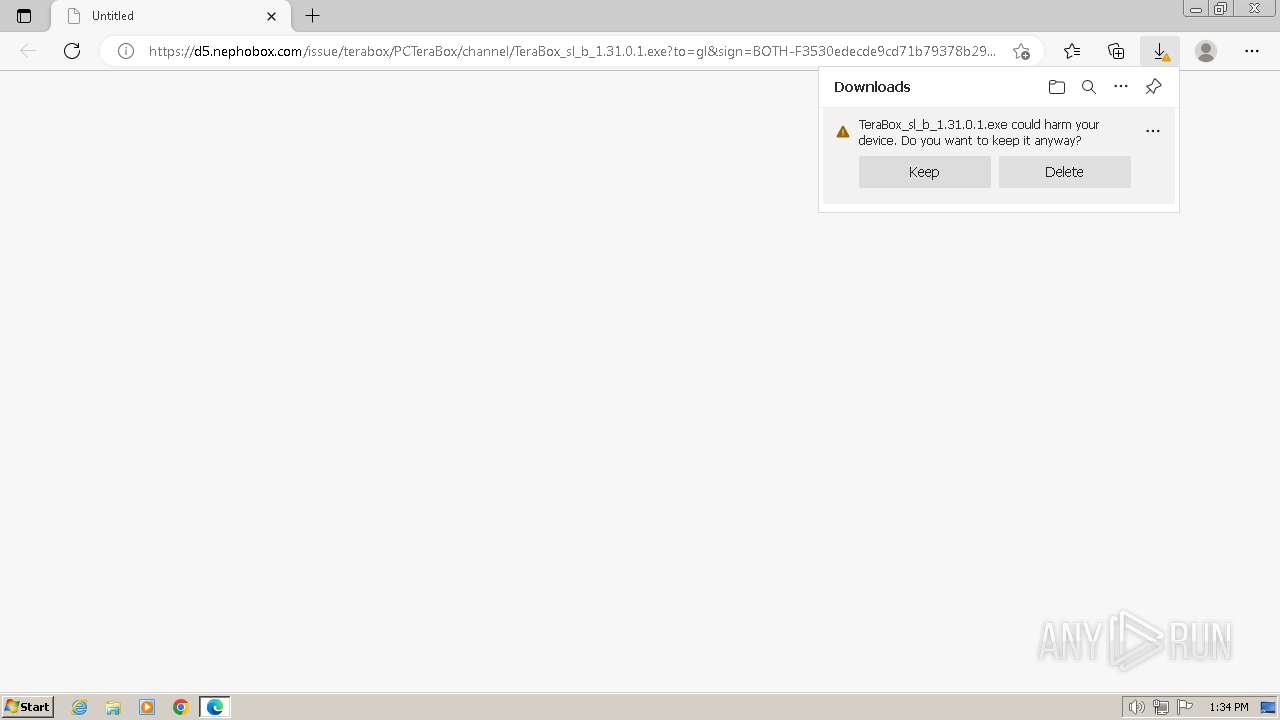
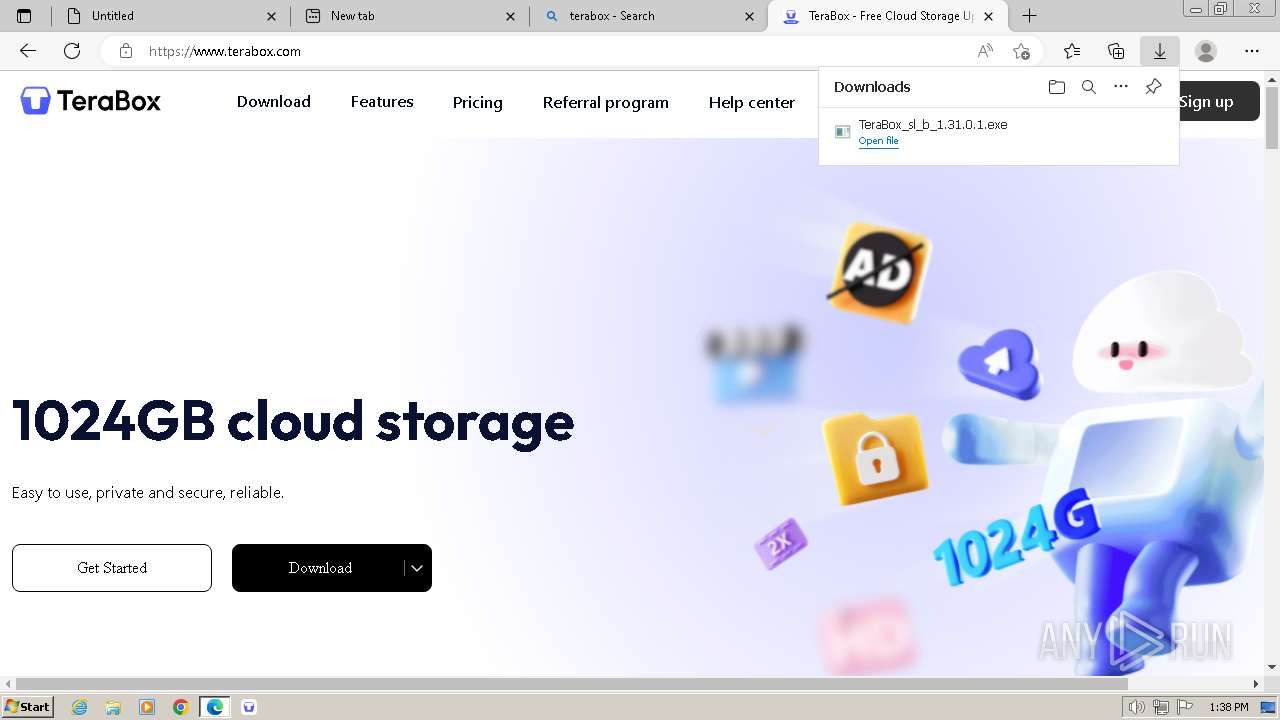
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2024, 12:34:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EFF0F0D29B286F4645383B536ED09F17 |
| SHA1: | 0C583E0F01ABA0FDBD1C4075148476D085F70281 |
| SHA256: | EF3144B19797ABA3529788A60BF7A7B75BD43F29DEC47699357373A1BA80FCA1 |
| SSDEEP: | 6:2IvbKAVVAXOKdyTdqJKM97Mi4fCOKG7fZKu:2I2AV1KYTdqlyi5o |
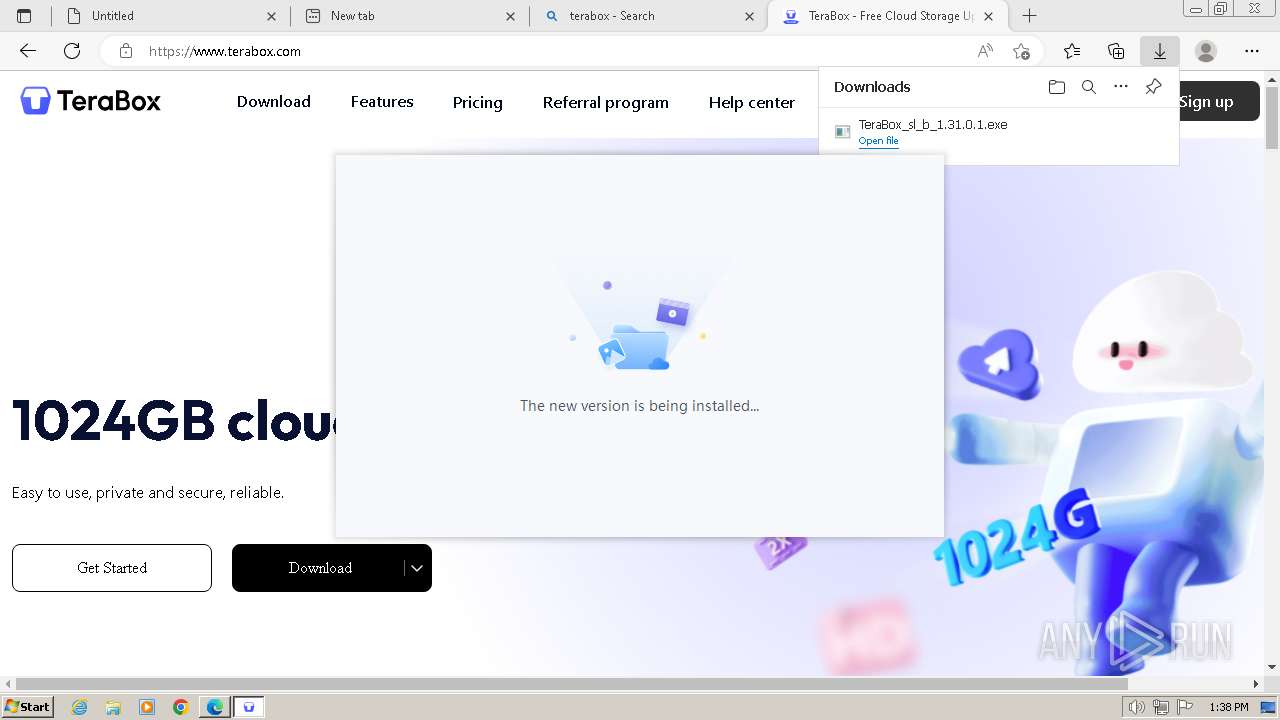
MALICIOUS
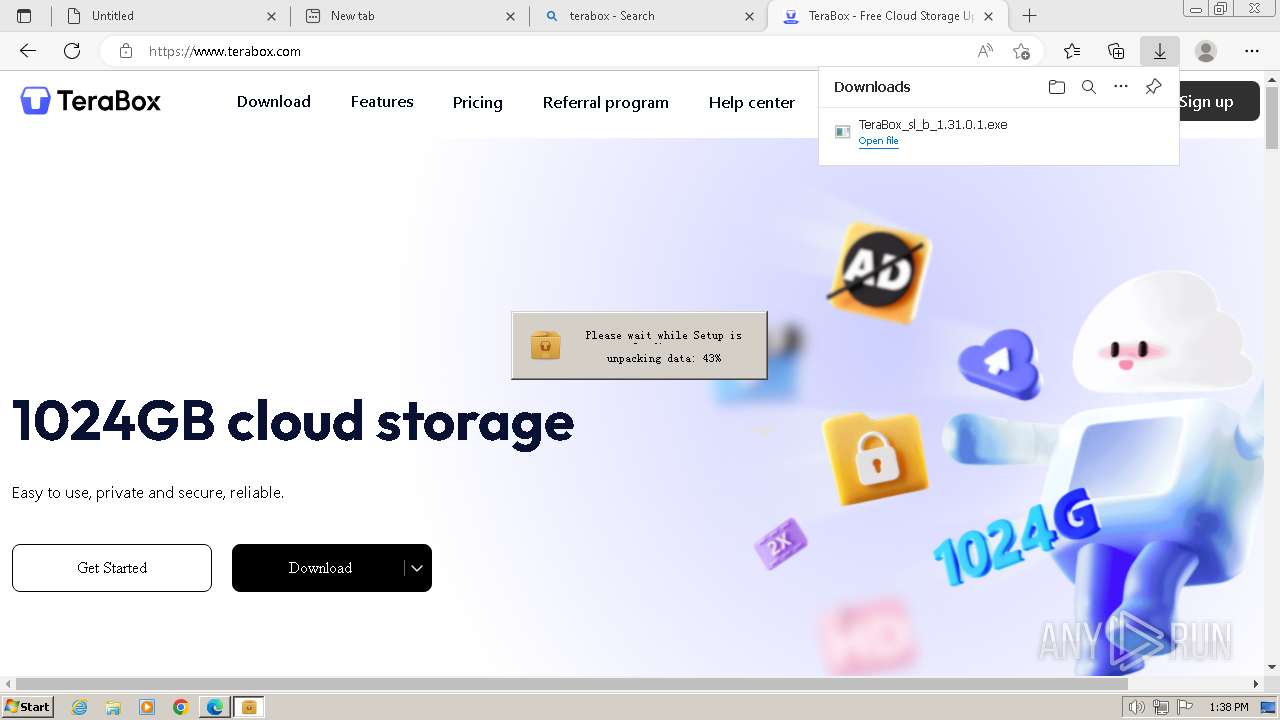
Drops the executable file immediately after the start
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
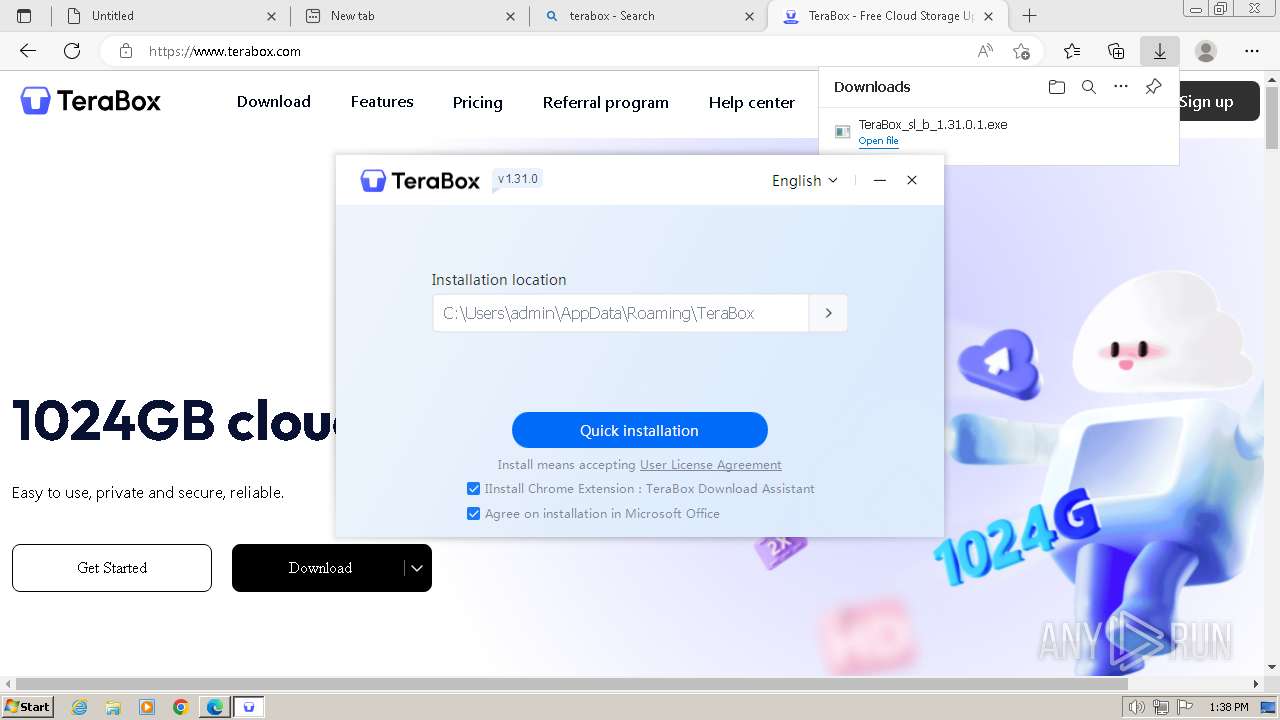
Changes the autorun value in the registry
- TeraBox.exe (PID: 2112)
Registers / Runs the DLL via REGSVR32.EXE
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
Creates a writable file in the system directory
- YunUtilityService.exe (PID: 2376)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
The process creates files with name similar to system file names
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
- TeraBoxRender.exe (PID: 3444)
The process drops C-runtime libraries
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
Process drops legitimate windows executable
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
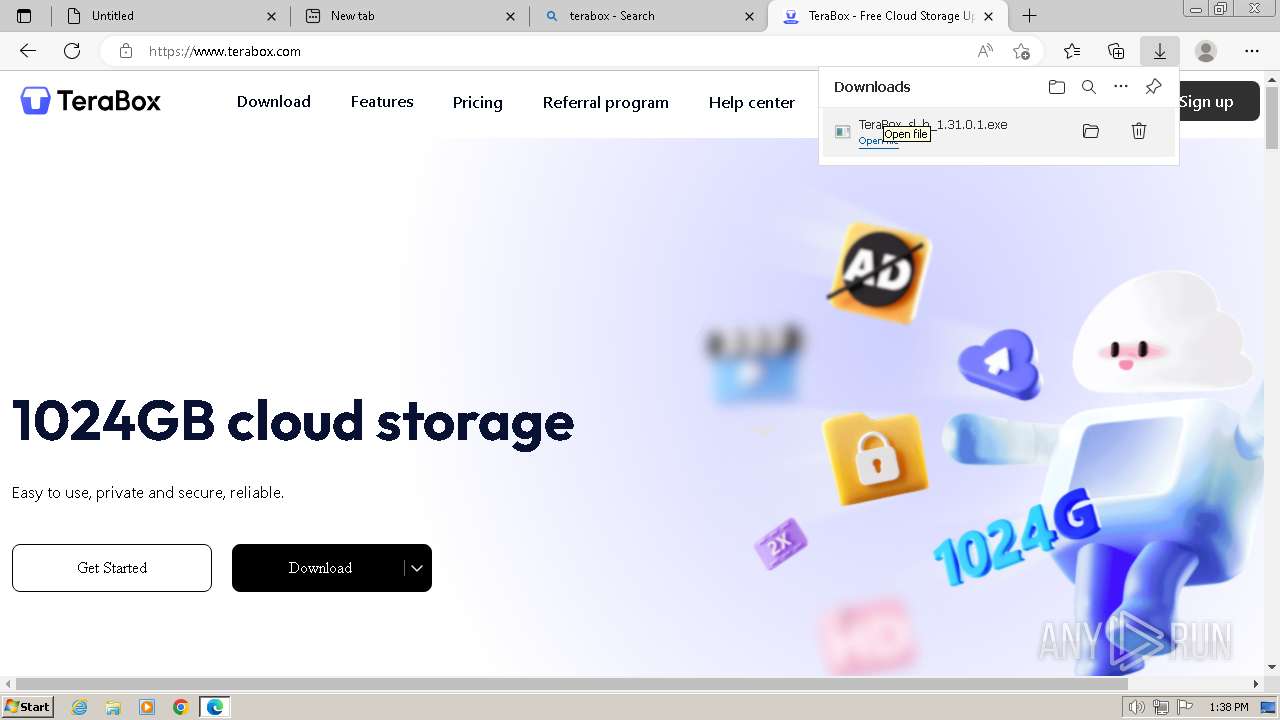
Executable content was dropped or overwritten
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
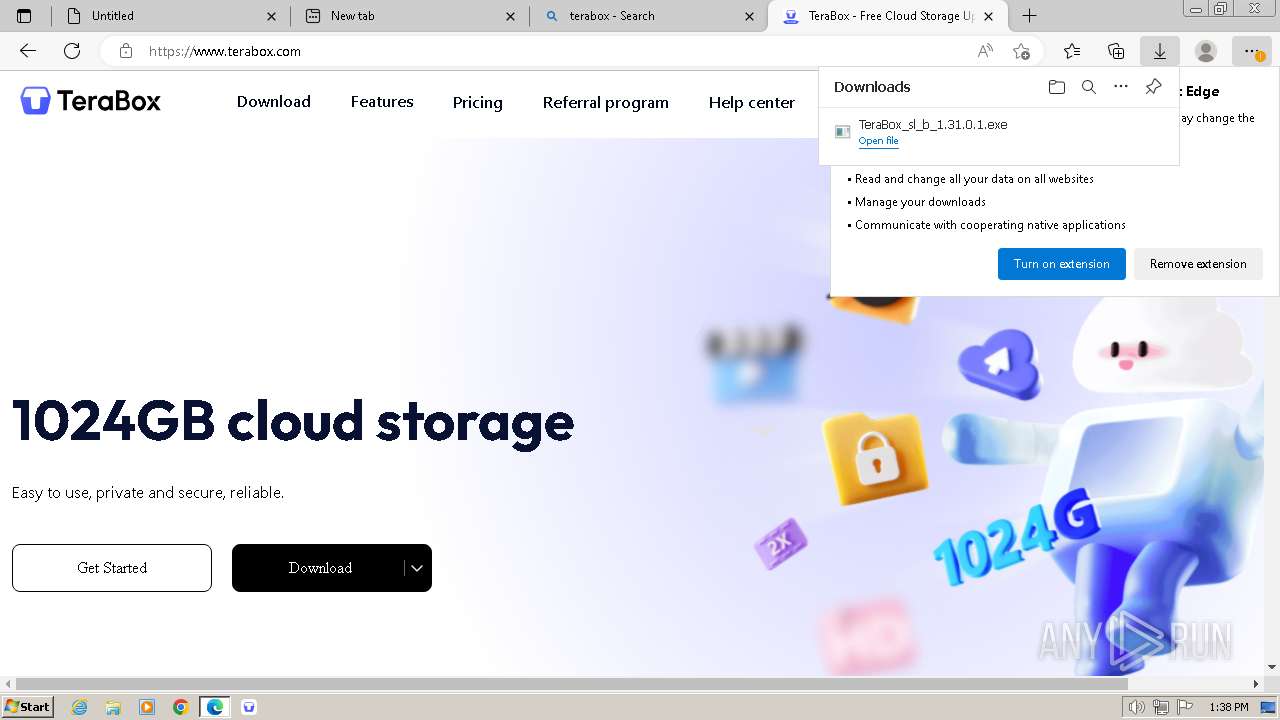
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3972)
- regsvr32.exe (PID: 2600)
Reads the date of Windows installation
- TeraBox.exe (PID: 2112)
Creates a software uninstall entry
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
Reads the Internet Settings
- TeraBoxWebService.exe (PID: 2004)
- TeraBox.exe (PID: 2276)
- AutoUpdate.exe (PID: 368)
Reads security settings of Internet Explorer
- TeraBoxWebService.exe (PID: 2004)
- TeraBox.exe (PID: 2276)
- AutoUpdate.exe (PID: 368)
Checks Windows Trust Settings
- TeraBox.exe (PID: 2276)
- YunUtilityService.exe (PID: 2376)
- AutoUpdate.exe (PID: 368)
Reads settings of System Certificates
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3184)
- AutoUpdate.exe (PID: 368)
Executes as Windows Service
- YunUtilityService.exe (PID: 2376)
Adds/modifies Windows certificates
- YunUtilityService.exe (PID: 2376)
INFO
Drops the executable file immediately after the start
- msedge.exe (PID: 3400)
Manual execution by a user
- wmpnscfg.exe (PID: 2492)
Reads the computer name
- wmpnscfg.exe (PID: 2492)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
- TeraBox.exe (PID: 2112)
- YunUtilityService.exe (PID: 1748)
- TeraBoxWebService.exe (PID: 2004)
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3444)
- TeraBoxRender.exe (PID: 3184)
- YunUtilityService.exe (PID: 2376)
- TeraBoxRender.exe (PID: 2536)
- TeraBoxHost.exe (PID: 3536)
- AutoUpdate.exe (PID: 368)
- TeraBoxHost.exe (PID: 2448)
Checks supported languages
- wmpnscfg.exe (PID: 2492)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
- TeraBox.exe (PID: 2112)
- YunUtilityService.exe (PID: 1748)
- TeraBoxWebService.exe (PID: 2004)
- TeraBoxWebService.exe (PID: 3704)
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3444)
- TeraBoxRender.exe (PID: 2512)
- TeraBoxRender.exe (PID: 3184)
- TeraBoxRender.exe (PID: 3200)
- TeraBoxRender.exe (PID: 2536)
- YunUtilityService.exe (PID: 2376)
- TeraBoxHost.exe (PID: 2448)
- TeraBoxHost.exe (PID: 3536)
- AutoUpdate.exe (PID: 368)
Executable content was dropped or overwritten
- msedge.exe (PID: 3400)
The process uses the downloaded file
- msedge.exe (PID: 4064)
- msedge.exe (PID: 3400)
Create files in a temporary directory
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3184)
Reads Environment values
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
Application launched itself
- msedge.exe (PID: 3400)
Creates files or folders in the user directory
- TeraBox_sl_b_1.31.0.1.exe (PID: 3672)
- TeraBox.exe (PID: 2112)
- TeraBox.exe (PID: 2276)
- TeraBoxWebService.exe (PID: 2004)
- TeraBoxHost.exe (PID: 3536)
- AutoUpdate.exe (PID: 368)
- TeraBoxHost.exe (PID: 2448)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 2112)
- TeraBoxWebService.exe (PID: 2004)
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3184)
- YunUtilityService.exe (PID: 2376)
- TeraBoxHost.exe (PID: 3536)
- AutoUpdate.exe (PID: 368)
Checks proxy server information
- TeraBoxWebService.exe (PID: 2004)
- TeraBox.exe (PID: 2276)
- AutoUpdate.exe (PID: 368)
Process checks computer location settings
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 2512)
- TeraBoxRender.exe (PID: 3200)
Reads the software policy settings
- TeraBox.exe (PID: 2276)
- TeraBoxRender.exe (PID: 3184)
- YunUtilityService.exe (PID: 2376)
- AutoUpdate.exe (PID: 368)
VMProtect protector has been detected
- TeraBoxHost.exe (PID: 3536)
Creates files in the program directory
- TeraBoxHost.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
56
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Users\admin\AppData\Roaming\TeraBox\AutoUpdate\AutoUpdate.exe" -client_info "C:\Users\admin\AppData\Local\Temp\TeraBox_status" -update_cfg_url "aHR0cHM6Ly90ZXJhYm94LmNvbS9hdXRvdXBkYXRl" -srvwnd 3021a -unlogin | C:\Users\admin\AppData\Roaming\TeraBox\AutoUpdate\AutoUpdate.exe | TeraBox.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxUpdate Exit code: 0 Version: 1.31.0.1 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1544 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 524 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3864 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=1024 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=4456 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4092 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4676 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1560 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe" --install | C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe | — | TeraBox_sl_b_1.31.0.1.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: HIGH Description: TeraBox Service Used to Quickly Apply For Disk Space Exit code: 0 Version: 1.31.0.1 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=5328 --field-trial-handle=1336,i,6948227265991936742,8421750198859435237,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
62 058
Read events
61 526
Write events
493
Delete events
39
Modification events
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 14E3B0664C7A2F00 | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3400) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
93
Suspicious files
706
Text files
102
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4e1b1.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e1c1.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e1d1.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4e20f.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:CE3AC3673EB3498DDF7BEC3328D23765 | SHA256:D2304AEDC7D32192364DCDECAF7A17972F3ABF909A79646A47B66917ECA30E9A | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:9D14DCB158E3908F7CBFB13D762D8F6A | SHA256:D339CBEF1BC3E4CDF15D0DCE9E2D77324E5B4F7EE4F2749472BFCEA91BB54ACE | |||
| 3400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:4B74C392839DDD59792975091A30DB00 | SHA256:7A5A3B8CC4D5BB579FA5E6C6A831964FB245A5CFF9AD3B80F5E9DC34DA4A7D53 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
111
DNS requests
148
Threats
56
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.53.40.56:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6db8a07497701bb0 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.53.42.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2004 | TeraBoxWebService.exe | GET | 404 | 210.148.85.47:80 | http://www.terabox.com/box-static/base/widget/httpProxy/_nomd5/crossdomain.xml | unknown | — | — | unknown |
2276 | TeraBox.exe | POST | 200 | 210.148.85.47:80 | http://terabox.com/statistics?clienttype=8&devuid=TBIMXV2%2DO%5F77F09A3E7DE74602BCD00C09CAE10A5D%2DC%5F0%2DD%5F4d51303030302031202020202020202020202020%2DM%5F12A9866C77DE%2DV%5FC4BA3647&channel=00000000000000000000000001000002&version=1.31.0.1&ver=1&id=1719319123FEA6B340BCD946F38B18CA26C7D9A97F&vip=0 | unknown | — | — | unknown |
2376 | YunUtilityService.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | unknown |
2376 | YunUtilityService.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | unknown |
2376 | YunUtilityService.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | unknown |
2376 | YunUtilityService.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDBLeGItEWTEgQyVFBw%3D%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3400 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
400 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
400 | msedge.exe | 34.110.181.92:443 | d5.nephobox.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
400 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1372 | svchost.exe | 23.53.40.56:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.53.42.18:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
3400 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d5.nephobox.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
assets.msn.com |
| whitelisted |
r.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
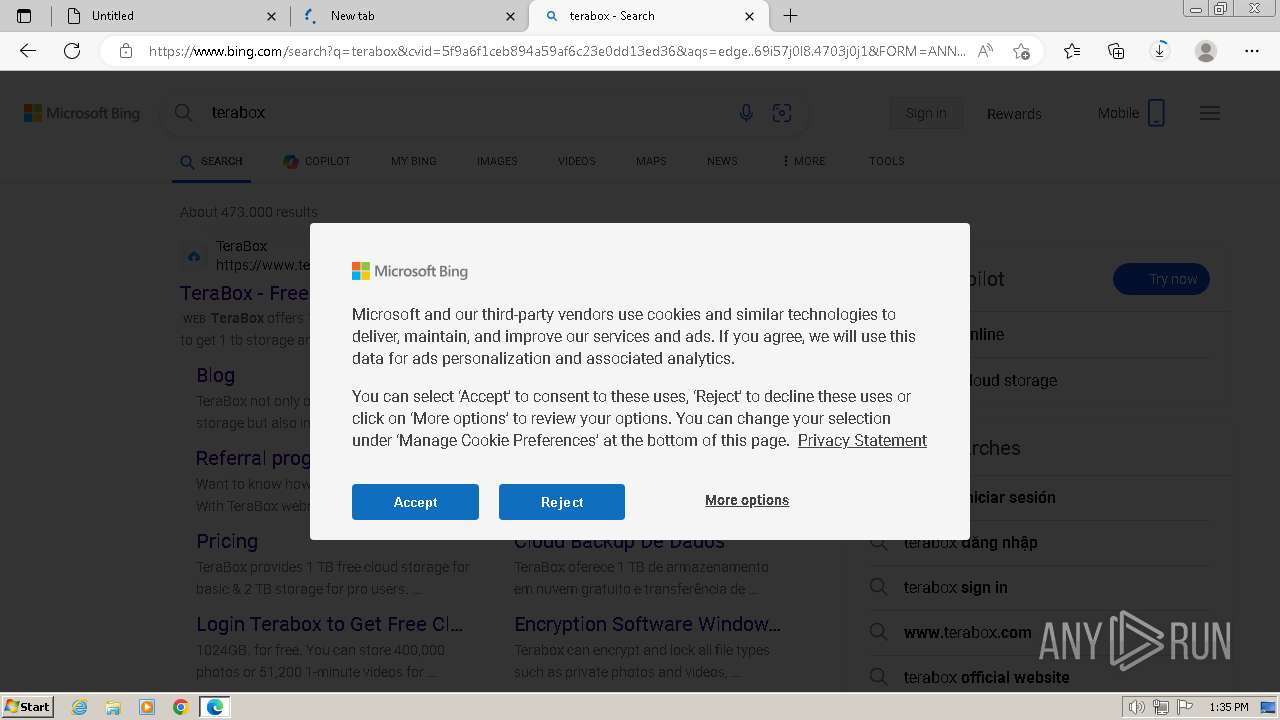
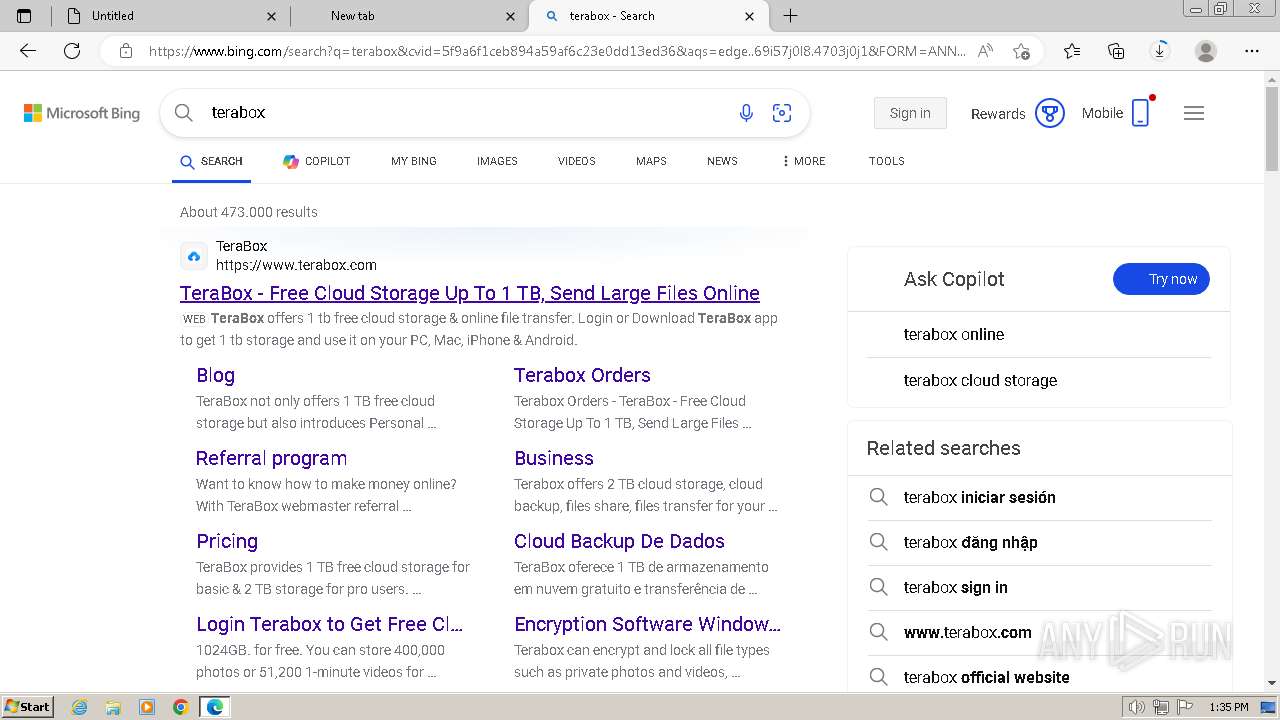
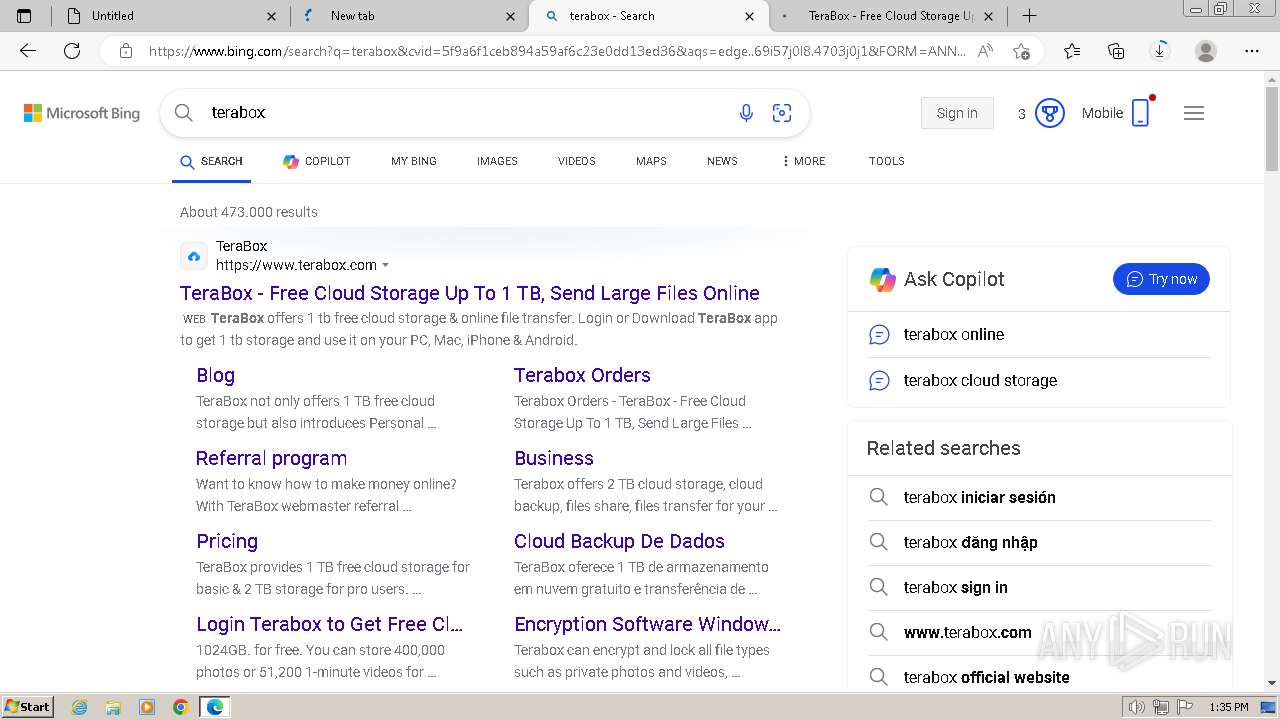
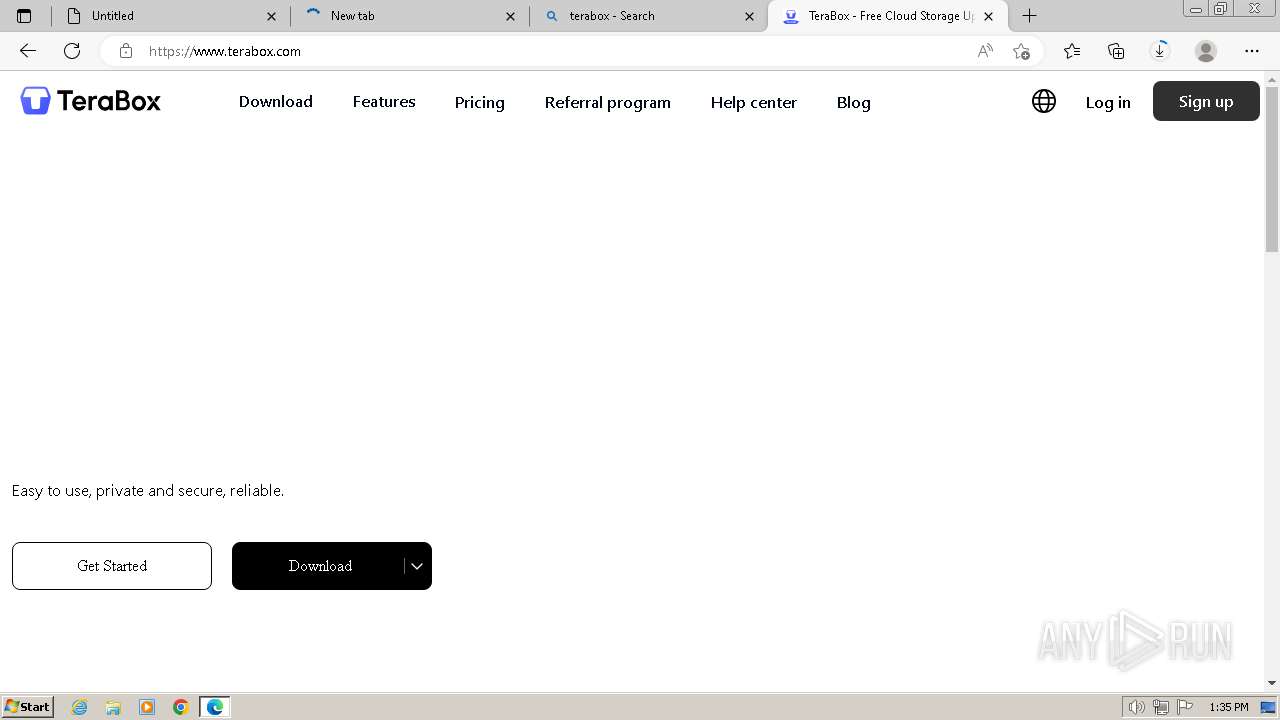
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
400 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
400 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
400 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
Process | Message |
|---|---|
TeraBoxHost.exe | vast_media--[2024-06-25 13:38:50:591] Initialized sdl_video_render_driver=software
|
TeraBoxHost.exe | vast_media--[2024-06-25 13:38:50:591] Initialized sdl_audio_play_driver=directsound
|
TeraBoxHost.exe | vast_media--[2024-06-25 13:38:50:591] Initialized hardware_type=3001
|