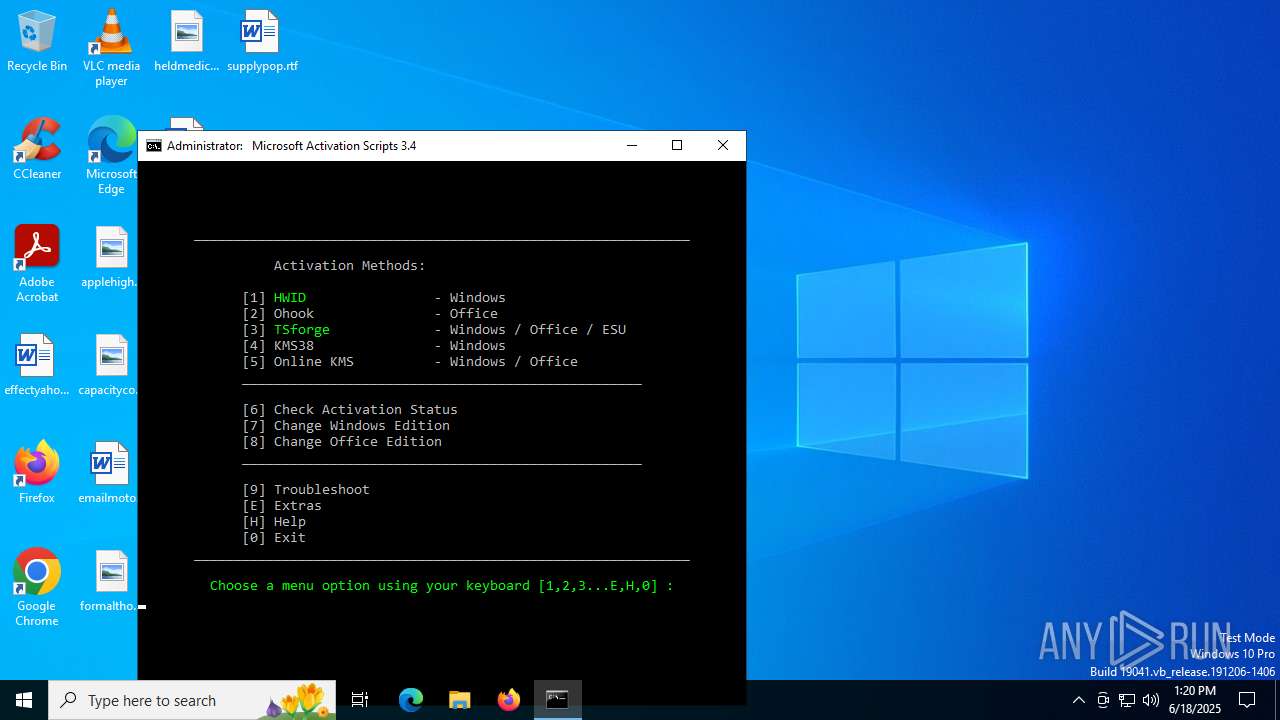
| download: | /massgrave/Microsoft-Activation-Scripts/raw/commit/67abcd0c8925832fcf4365b9cf3706ab6fbf8571/MAS/All-In-One-Version-KL/MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/e28d3903-d8cf-4e28-afd8-158d8dec8a40 |
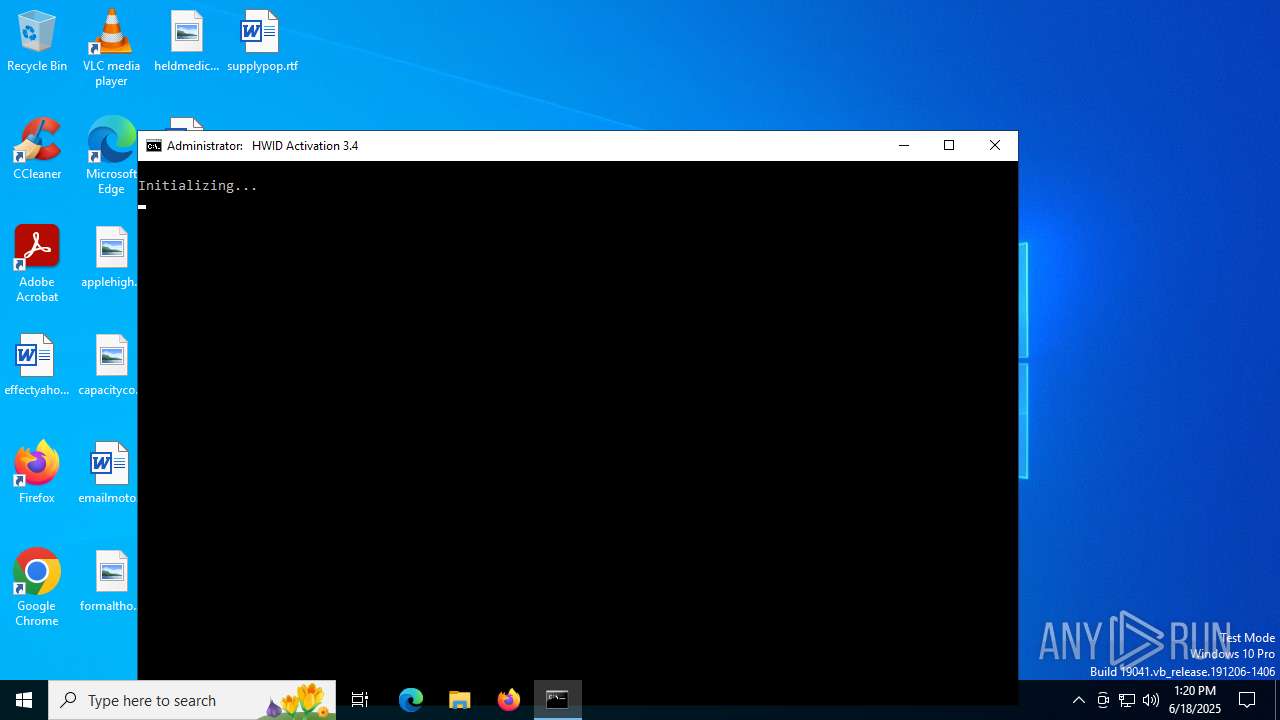
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2025, 13:20:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (312), with CRLF line terminators |
| MD5: | B5A6AFF691AC3D6277C496C50F0A5DE1 |
| SHA1: | 68AE780E33C0E226350A8A2787EB2C62E9105D3D |
| SHA256: | EF2F705B9E8BE2816598E2E8B70BADB200733F2287B917D6C9666D95C63AFBF9 |
| SSDEEP: | 6144:x2Iw0Mqx05wrUcEvTUQWObw7nccN4PK0yk4Bcub:x2Iw0T6cEvTU9O6c+EK0yk4BN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- cmd.exe (PID: 1520)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 1296)
- powershell.exe (PID: 6368)
- powershell.exe (PID: 728)
Starts SC.EXE for service management
- cmd.exe (PID: 1520)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Executing commands from ".cmd" file
- cmd.exe (PID: 1520)
- powershell.exe (PID: 4236)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Windows service management via SC.EXE
- sc.exe (PID: 4112)
- sc.exe (PID: 4520)
- sc.exe (PID: 2076)
- sc.exe (PID: 7000)
- sc.exe (PID: 7020)
- sc.exe (PID: 4984)
- sc.exe (PID: 2648)
- sc.exe (PID: 6548)
- sc.exe (PID: 2976)
- sc.exe (PID: 2532)
- sc.exe (PID: 1480)
- sc.exe (PID: 5244)
- sc.exe (PID: 1136)
- sc.exe (PID: 1944)
- sc.exe (PID: 6460)
- sc.exe (PID: 2792)
- sc.exe (PID: 4236)
- sc.exe (PID: 6652)
- sc.exe (PID: 6636)
- sc.exe (PID: 1484)
- sc.exe (PID: 2072)
- sc.exe (PID: 1332)
- sc.exe (PID: 1216)
- sc.exe (PID: 4752)
- sc.exe (PID: 5564)
- sc.exe (PID: 2696)
- sc.exe (PID: 6688)
- sc.exe (PID: 6304)
- sc.exe (PID: 6940)
- sc.exe (PID: 1564)
- sc.exe (PID: 728)
- sc.exe (PID: 320)
- sc.exe (PID: 3676)
- sc.exe (PID: 1880)
- sc.exe (PID: 4864)
- sc.exe (PID: 6840)
- sc.exe (PID: 472)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1520)
- cmd.exe (PID: 6940)
- powershell.exe (PID: 4236)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 1296)
- cmd.exe (PID: 2876)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1520)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6128)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 6404)
- powershell.exe (PID: 6368)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 1712)
- powershell.exe (PID: 728)
- cmd.exe (PID: 6940)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1520)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Executes script without checking the security policy
- powershell.exe (PID: 4236)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4680)
- powershell.exe (PID: 6368)
- powershell.exe (PID: 4104)
- powershell.exe (PID: 6936)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 3160)
- powershell.exe (PID: 6124)
- powershell.exe (PID: 2792)
- powershell.exe (PID: 7092)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2620)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1520)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6128)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 6404)
- powershell.exe (PID: 6368)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 1712)
- powershell.exe (PID: 728)
- cmd.exe (PID: 6940)
Executing commands from a ".bat" file
- cmd.exe (PID: 1520)
- powershell.exe (PID: 4236)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Hides command output
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6128)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 3504)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 984)
- cmd.exe (PID: 5424)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 5928)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 1712)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6128)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 5116)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6128)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 5116)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
- powershell.exe (PID: 2620)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5348)
- cmd.exe (PID: 2876)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3688)
Probably file/command deobfuscation
- cmd.exe (PID: 6404)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6368)
- powershell.exe (PID: 728)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2876)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 5424)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2876)
INFO
Checks operating system version
- cmd.exe (PID: 1520)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 2876)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 4768)
- powershell.exe (PID: 4104)
Starts MODE.COM to configure console settings
- mode.com (PID: 5496)
- mode.com (PID: 3608)
- mode.com (PID: 5124)
- mode.com (PID: 6344)
Checks supported languages
- mode.com (PID: 5496)
- mode.com (PID: 3608)
- mode.com (PID: 5124)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3588)
- WMIC.exe (PID: 4040)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
407
Monitored processes
273
Malicious processes
10
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | reg query "HKCU\Control Panel\International\Geo" /v Name | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | sc query Winmgmt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | find /i "virustotal.com" C:\WINDOWS\System32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Type | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | sc query ClipSVC | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v DisplayName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v EditionID | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v ErrorControl | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
95 583
Read events
95 581
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3160) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (3160) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
Executable files
0
Suspicious files
1
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aowa33zb.4iq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5172 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yencpd3y.zea.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4236 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:98756F9FE725C60858C48D8DE4002EB9 | SHA256:AF40B2F1394C36ECBD4AE0F0E3488379808478A700B6B5E48B566D85B9A0D5B7 | |||
| 2192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3htqtayo.y02.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4120 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dujtlq0z.153.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4120 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x55fm5rs.bkv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dbgunevg.lew.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5172 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3t1w4dob.yve.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rcavbxww.vak.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cqcrfv1t.cyq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.16.148:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3556 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
436 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3556 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6232 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.16.148:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3556 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activated.win |
| unknown |
updatecheck34.activated.win |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
l.root-servers.net |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |