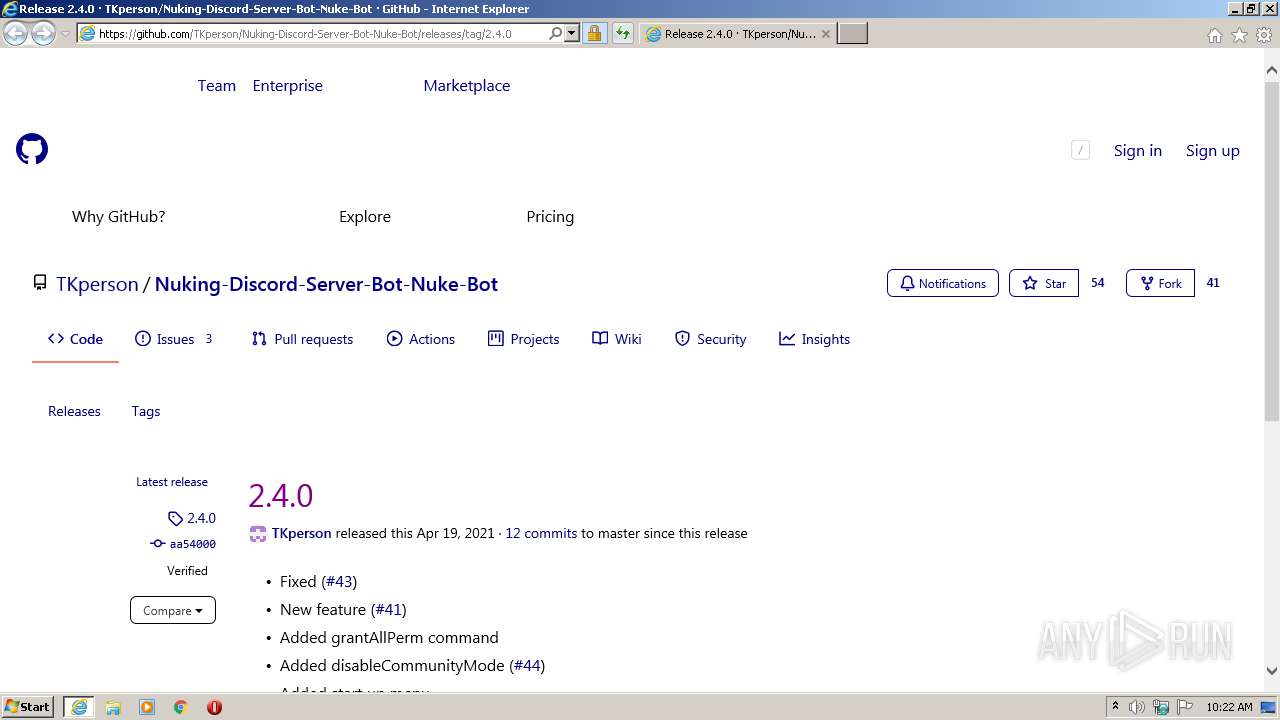
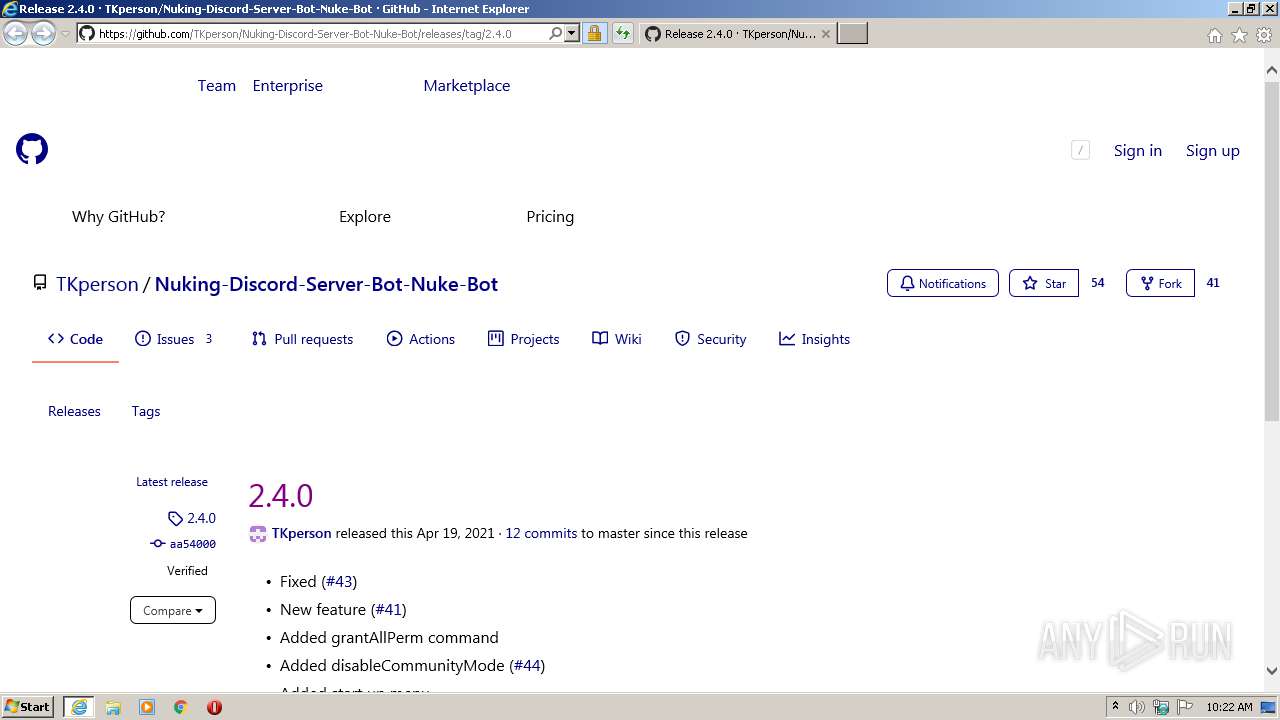
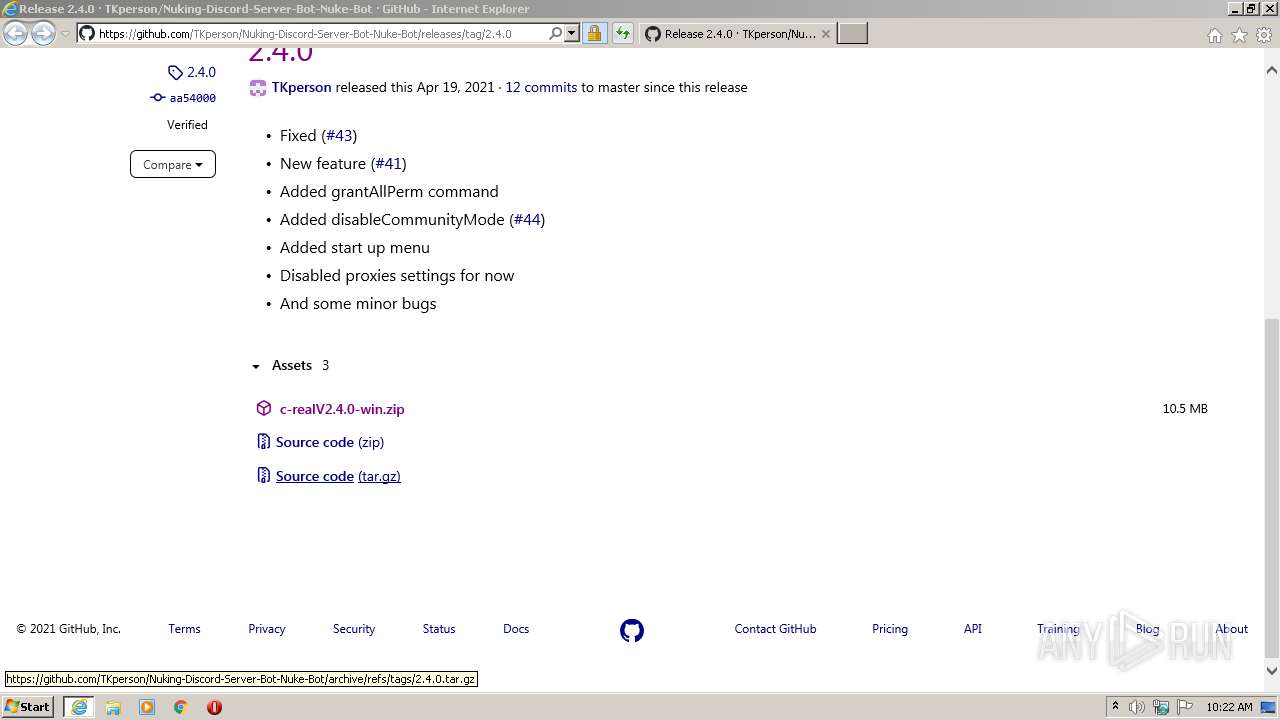
| URL: | https://github.com/TKperson/Nuking-Discord-Server-Bot-Nuke-Bot/releases/tag/2.4.0 |
| Full analysis: | https://app.any.run/tasks/16f1ae90-7871-4dbd-9747-ff00fffcbd42 |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2021, 09:21:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 18AF781DC1D2E6F04B79C0CB44499F39 |
| SHA1: | CB31C1BC4F5CF33C85EFC0F34834FC737616BCE1 |
| SHA256: | EF2F59EC833103267D640E1A750041F935609524941E0EBE6A275B650D2A9836 |
| SSDEEP: | 3:N8tEdsK+y6KXyRcMqKbRh:2uafylXHMxbn |
MALICIOUS
Loads dropped or rewritten executable
- c-realV2.exe (PID: 480)
- c-realV2.exe (PID: 1912)
Drops executable file immediately after starts
- c-realV2.exe (PID: 2748)
- c-realV2.exe (PID: 2628)
SUSPICIOUS
Executable content was dropped or overwritten
- c-realV2.exe (PID: 2748)
- c-realV2.exe (PID: 2628)
Application launched itself
- c-realV2.exe (PID: 2628)
- c-realV2.exe (PID: 2748)
Loads Python modules
- c-realV2.exe (PID: 1912)
- c-realV2.exe (PID: 480)
Drops a file that was compiled in debug mode
- c-realV2.exe (PID: 2748)
- c-realV2.exe (PID: 2628)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1692)
Application launched itself
- iexplore.exe (PID: 1692)
Dropped object may contain Bitcoin addresses
- c-realV2.exe (PID: 2628)
- c-realV2.exe (PID: 2748)
Reads settings of System Certificates
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 1692)
Creates files in the user directory
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 1692)
Changes settings of System certificates
- iexplore.exe (PID: 1692)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1692)
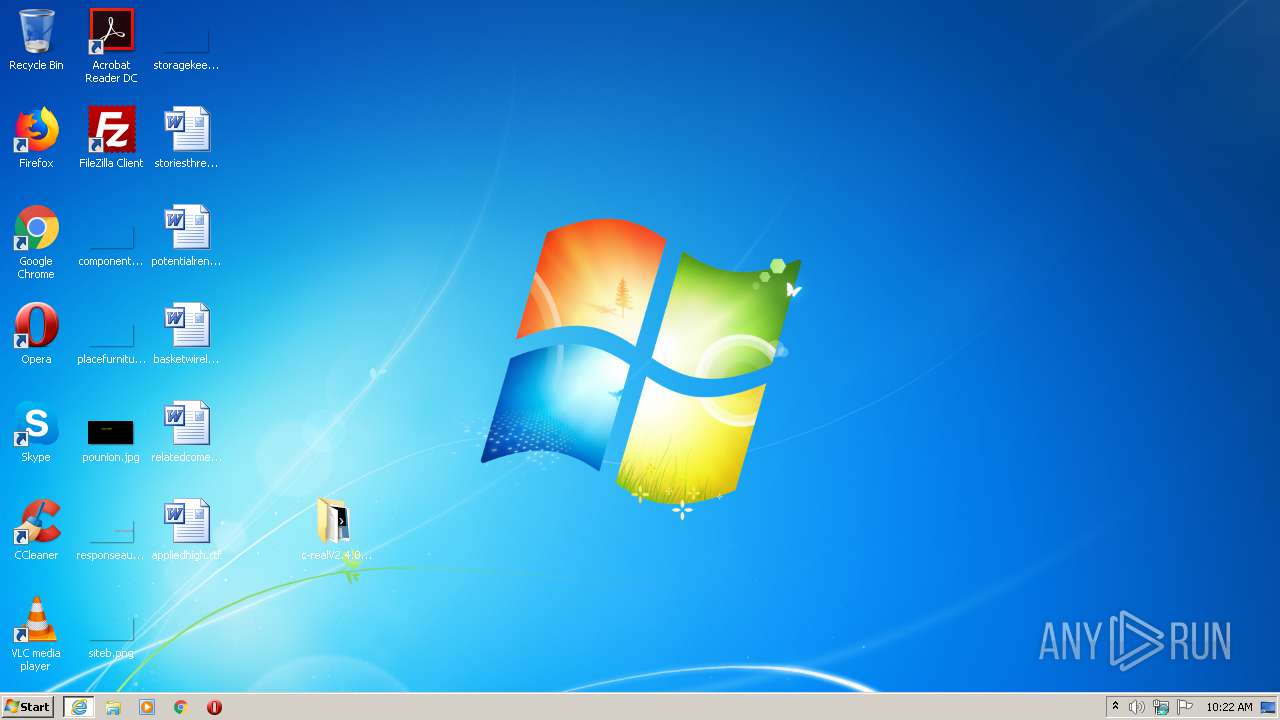
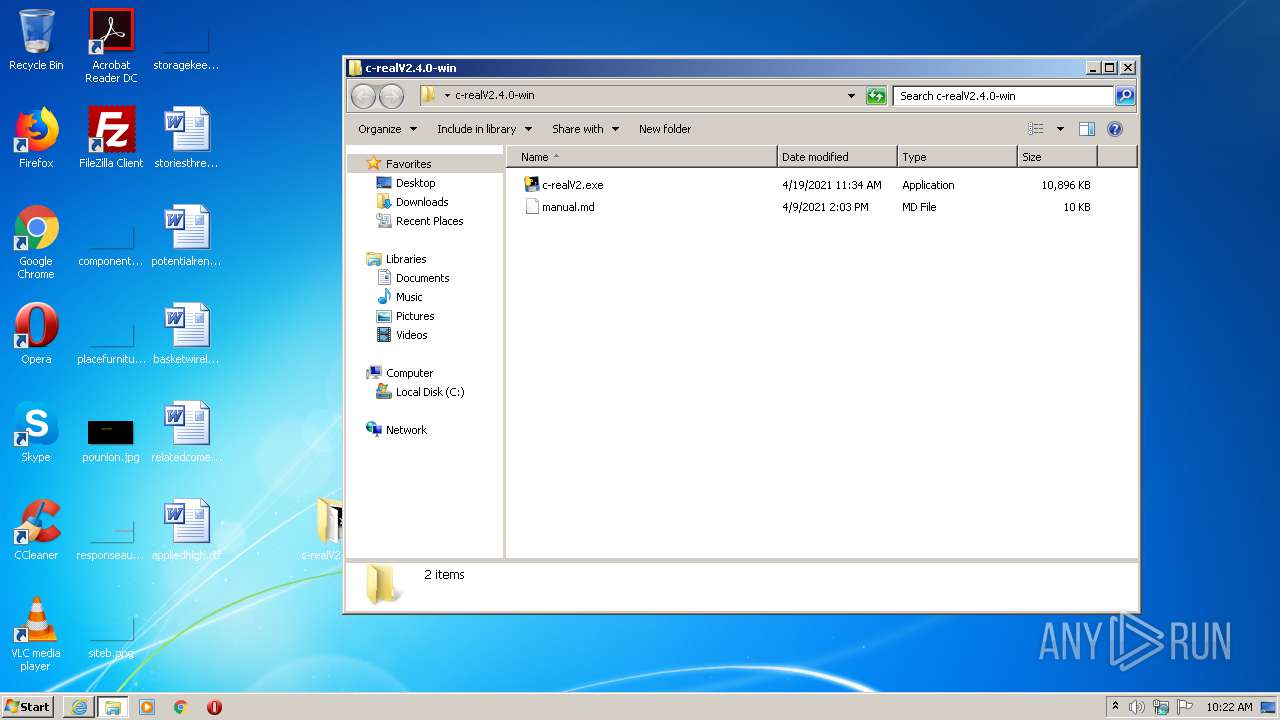
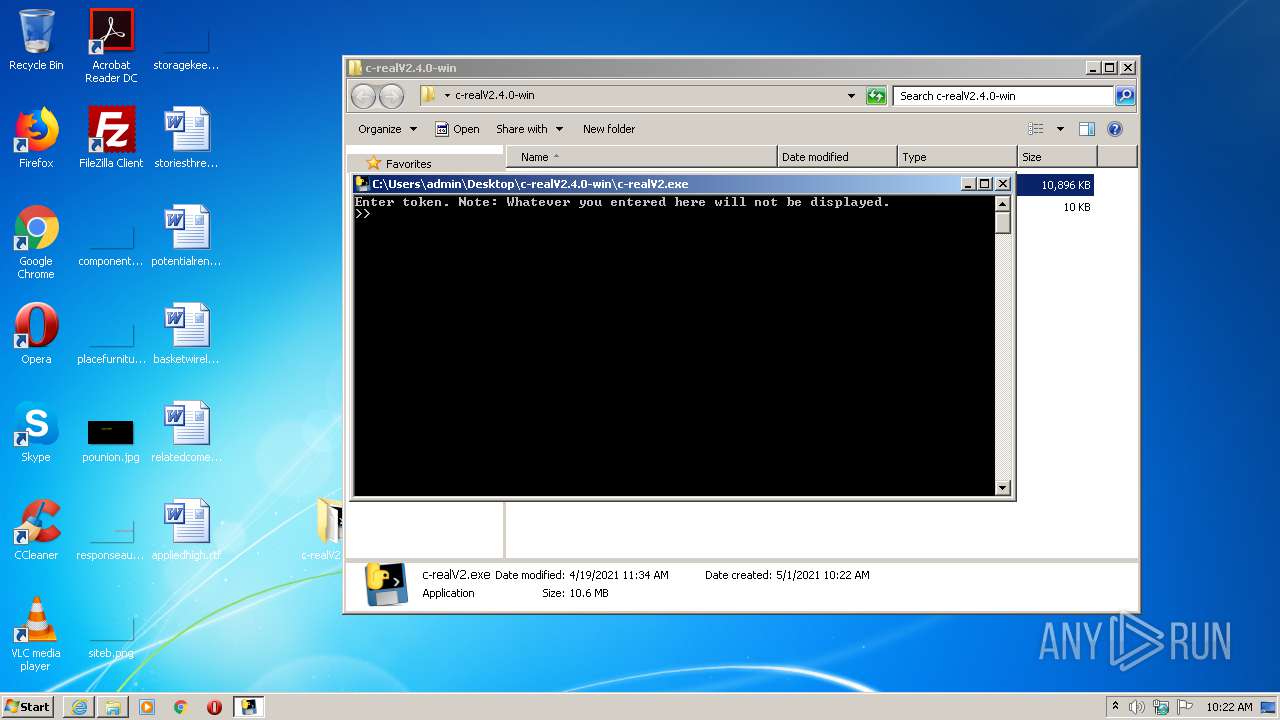
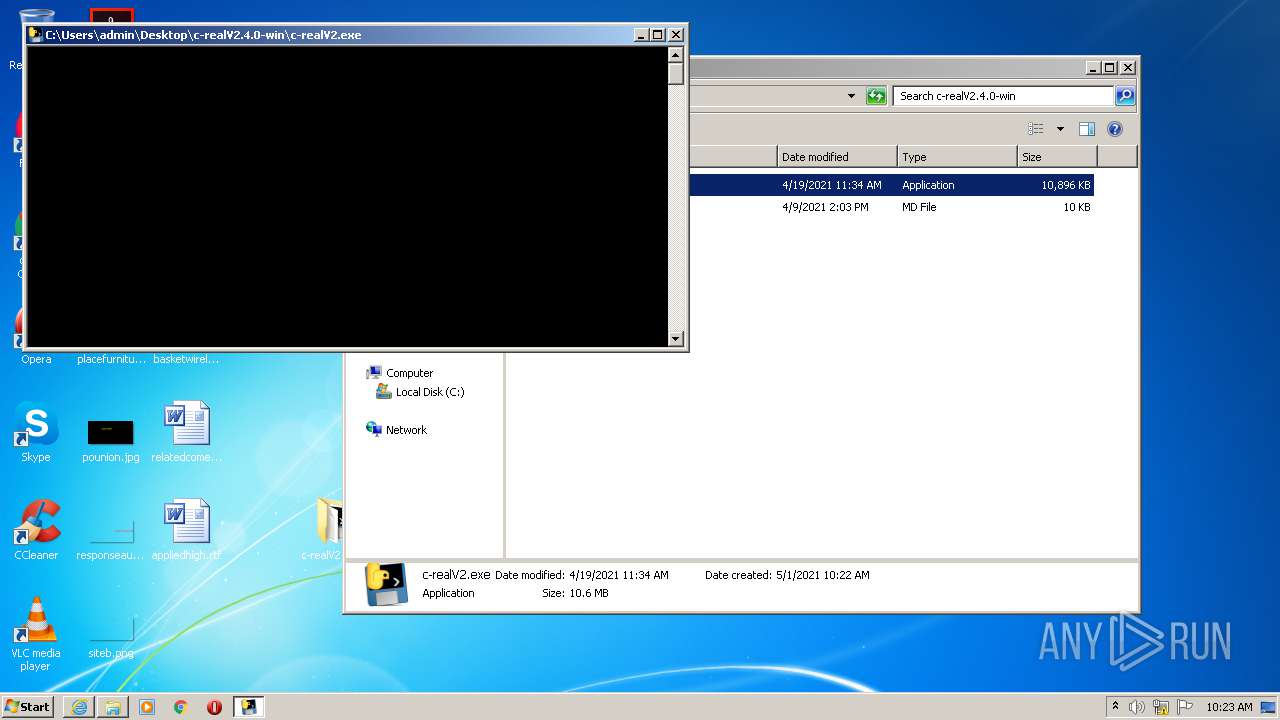
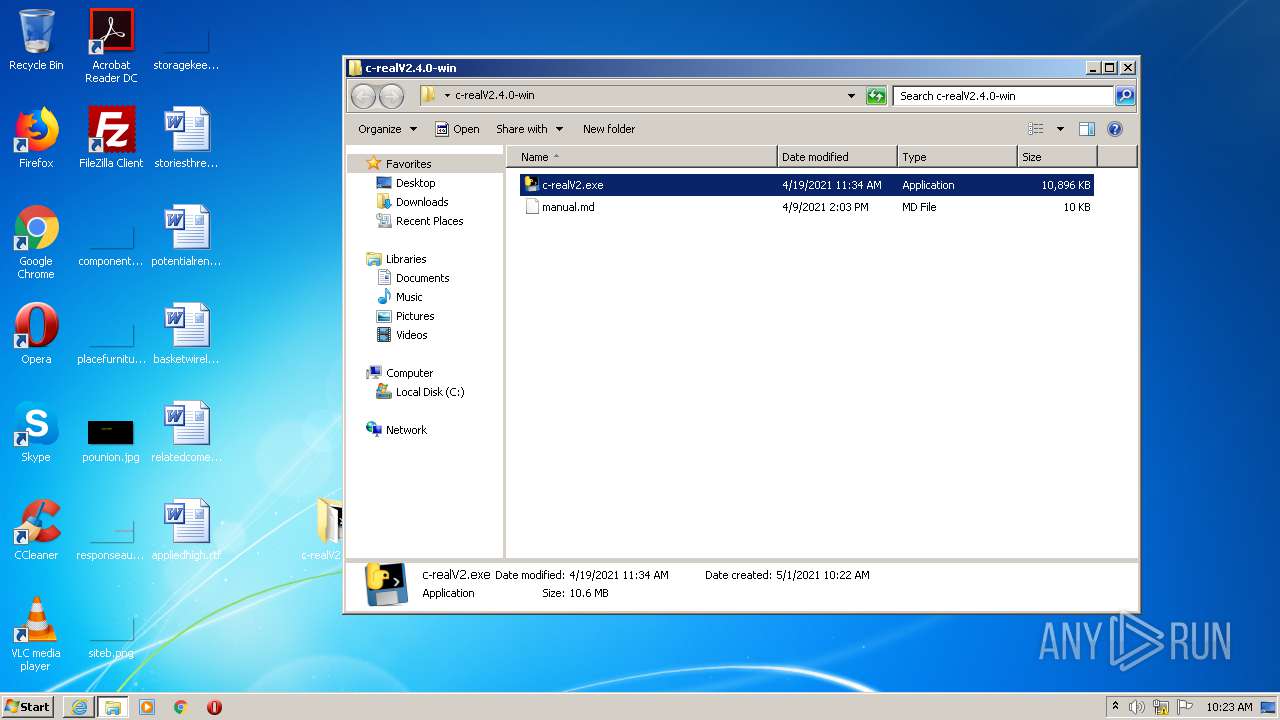
Manual execution by user
- c-realV2.exe (PID: 2628)
- c-realV2.exe (PID: 2748)
Reads internet explorer settings
- iexplore.exe (PID: 3892)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
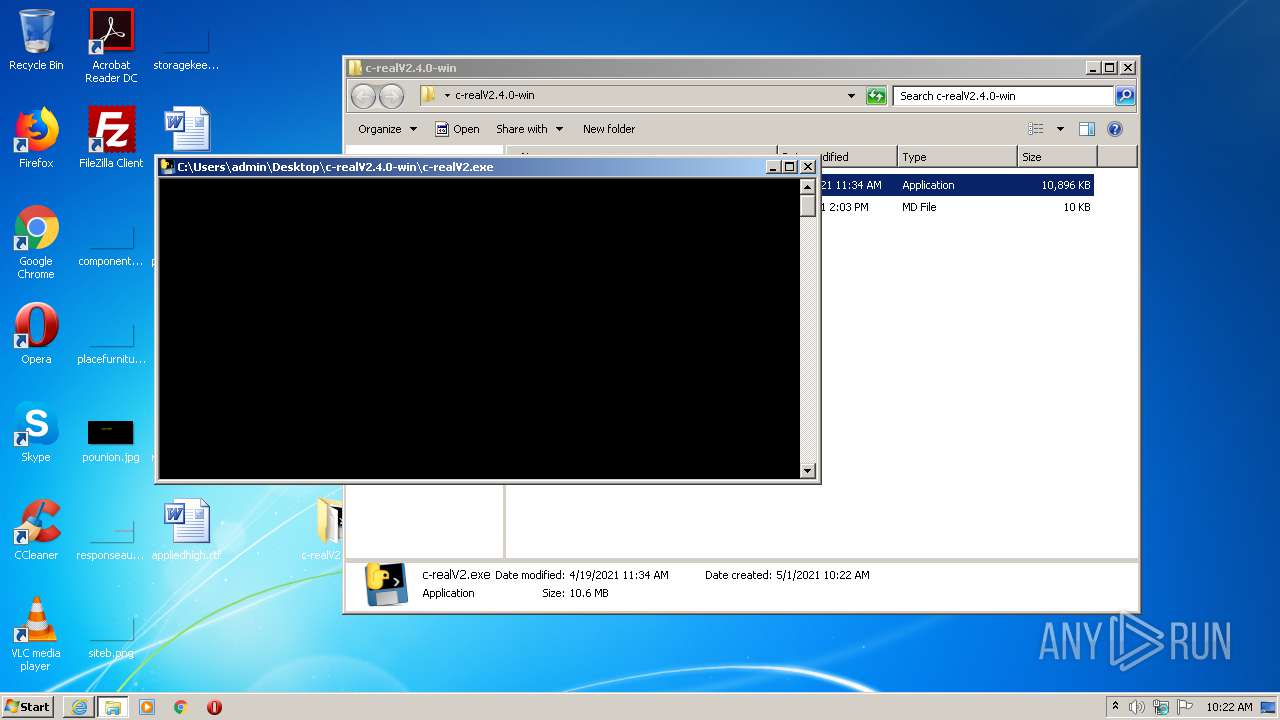
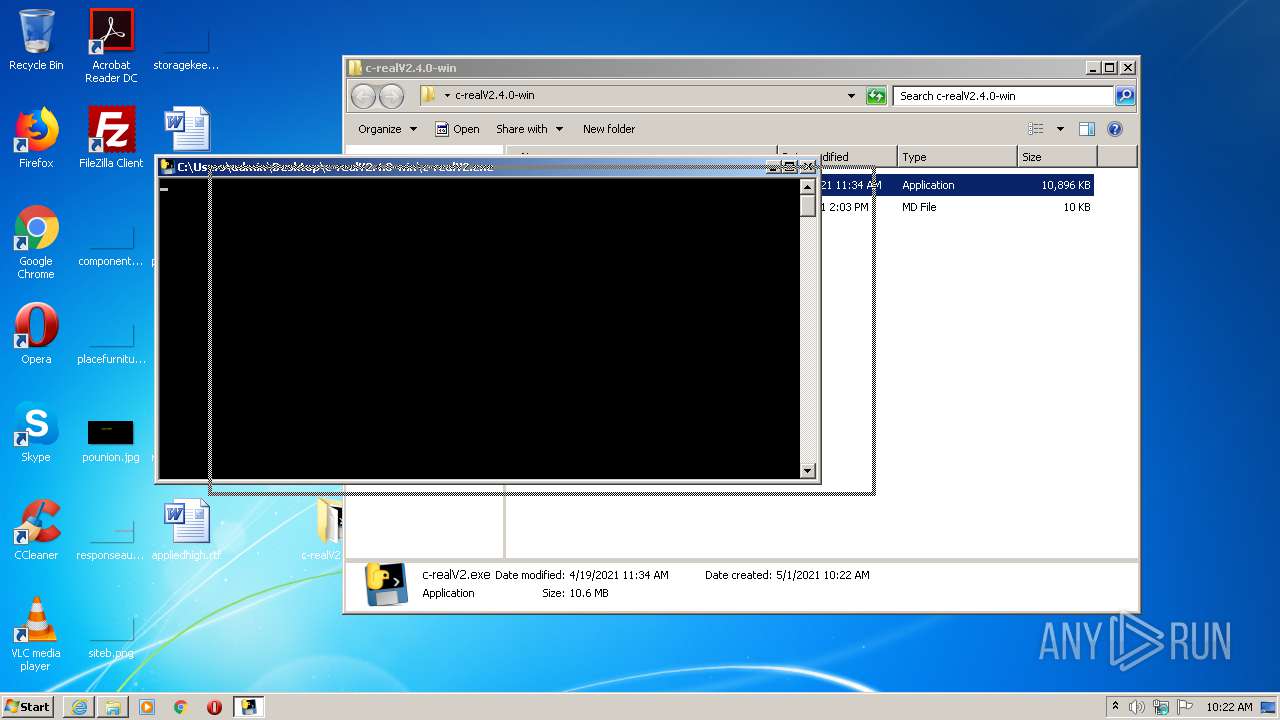
| 480 | "C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe" | C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe | — | c-realV2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/TKperson/Nuking-Discord-Server-Bot-Nuke-Bot/releases/tag/2.4.0" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe" | C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe | c-realV2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe" | C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe" | C:\Users\admin\Desktop\c-realV2.4.0-win\c-realV2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
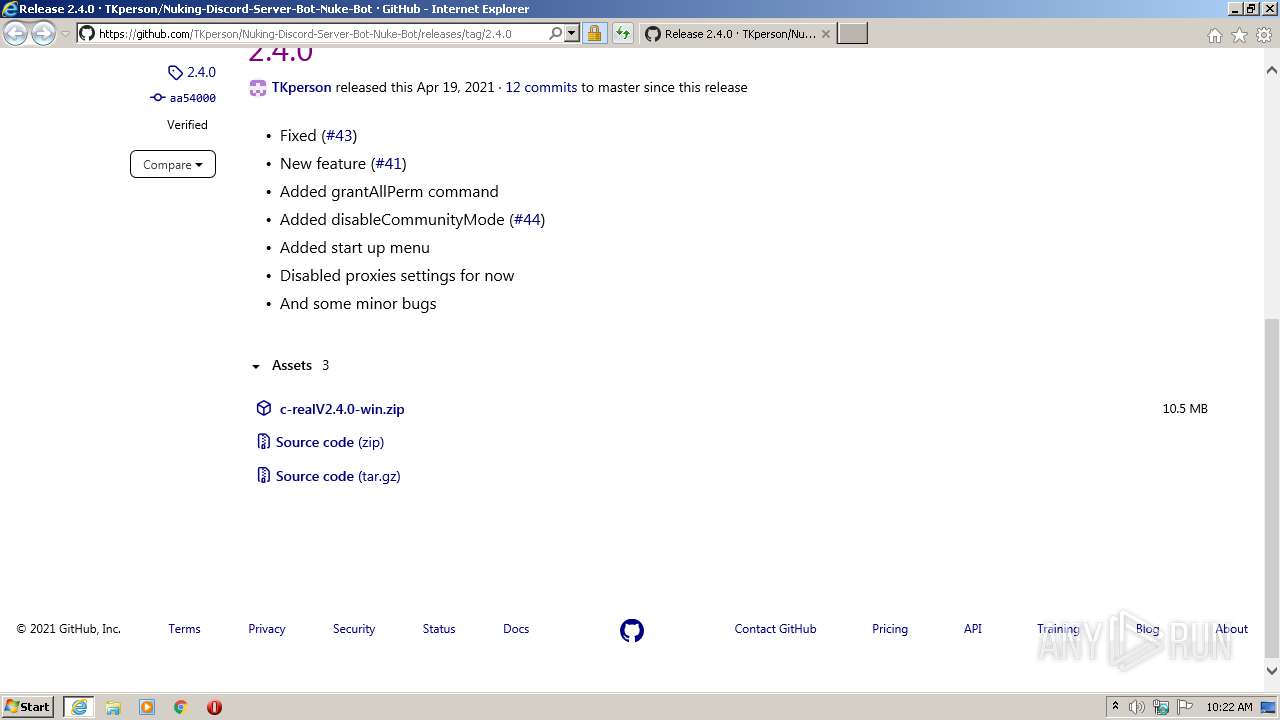
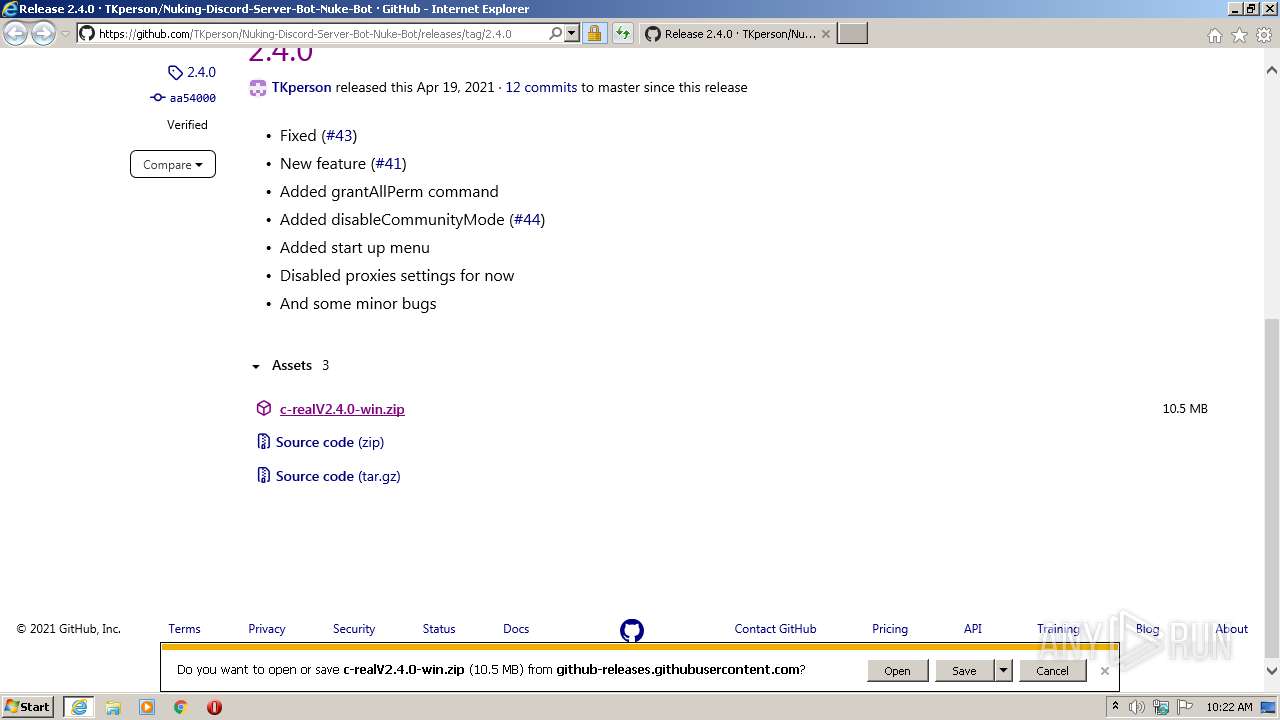
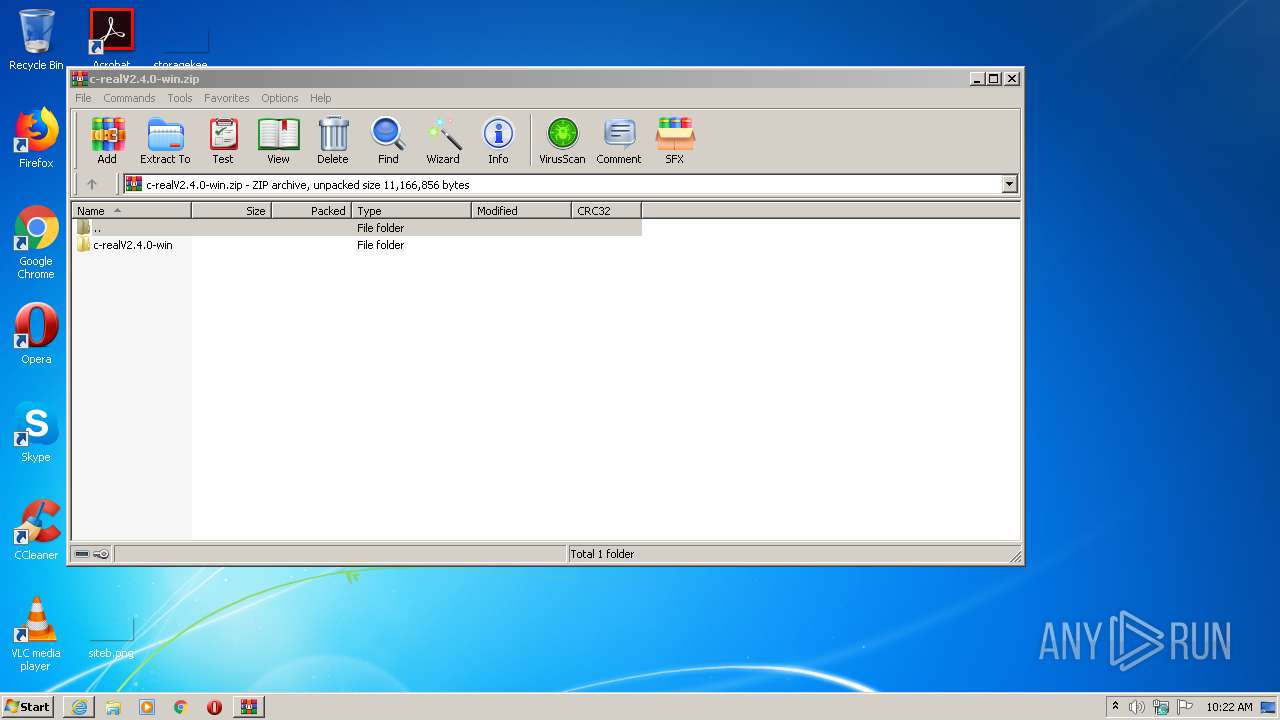
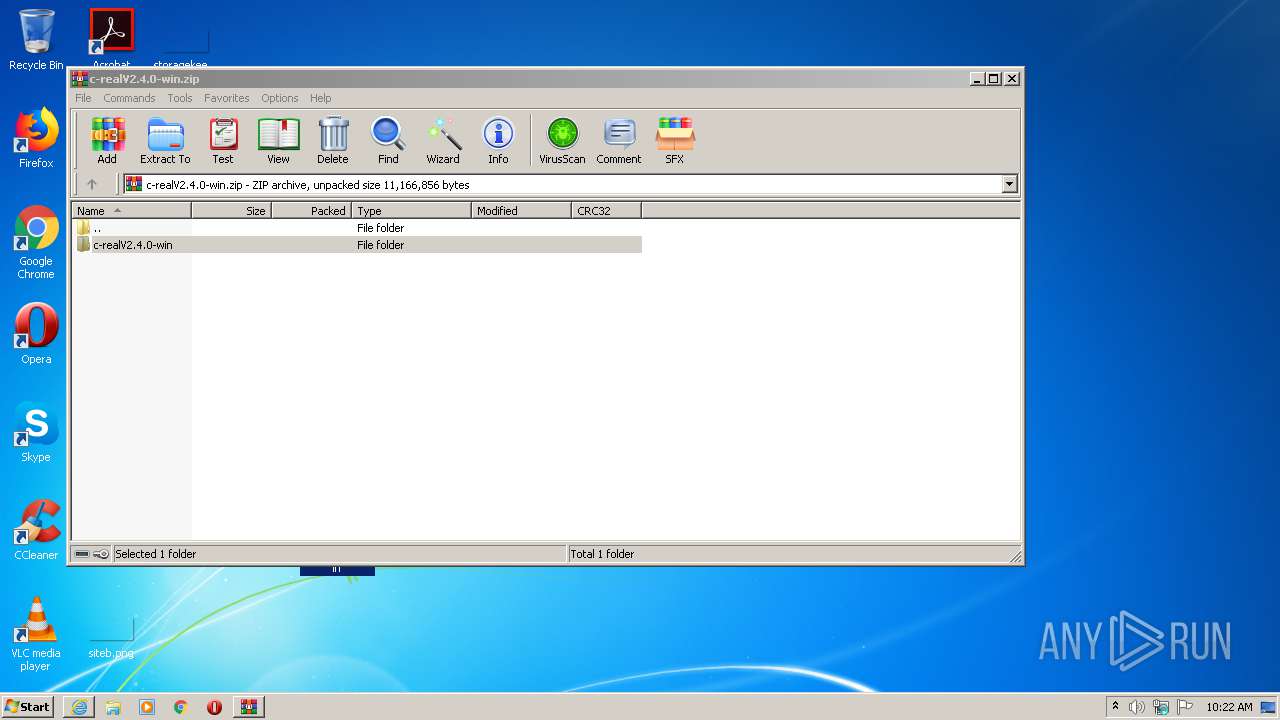
| 3204 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\c-realV2.4.0-win.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1692 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 024
Read events
1 904
Write events
116
Delete events
4
Modification events
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2255276990 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30883435 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
66
Suspicious files
35
Text files
25
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD3D3.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD3D4.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0POLG3FP.txt | — | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabDB64.tmp | — | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarDB65.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2A7611428D62805A3E4E5BC4103D82E4_D0FA13DADFB59BDF00C474952E166CC1 | binary | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\12B578593FDE07EC53D020B1D5DEBF3B_5D74C2DB556F94499BCD6D74A36958A3 | binary | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\2.4[1].htm | html | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\12B578593FDE07EC53D020B1D5DEBF3B_5D74C2DB556F94499BCD6D74A36958A3 | der | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\c-realV2.4.0-win[1].zip | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
30
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3892 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | — | — | whitelisted |
3892 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | — | — | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTGMlruL6P9M9B3if1rTM7wyj%2FQKQQUUGGmoNI1xBEqII0fD6xC8M0pz0sCEA6L83cNktGW8Lth%2BTxBZr4%3D | US | der | 278 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAZnA1u7FP1jr8DWqFNO%2FhY%3D | US | der | 471 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAZnA1u7FP1jr8DWqFNO%2FhY%3D | US | der | 471 b | whitelisted |
1692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3892 | iexplore.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1692 | iexplore.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
3892 | iexplore.exe | 185.199.110.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | malicious |
1692 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
— | — | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1692 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1692 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1692 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
github-releases.githubusercontent.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |