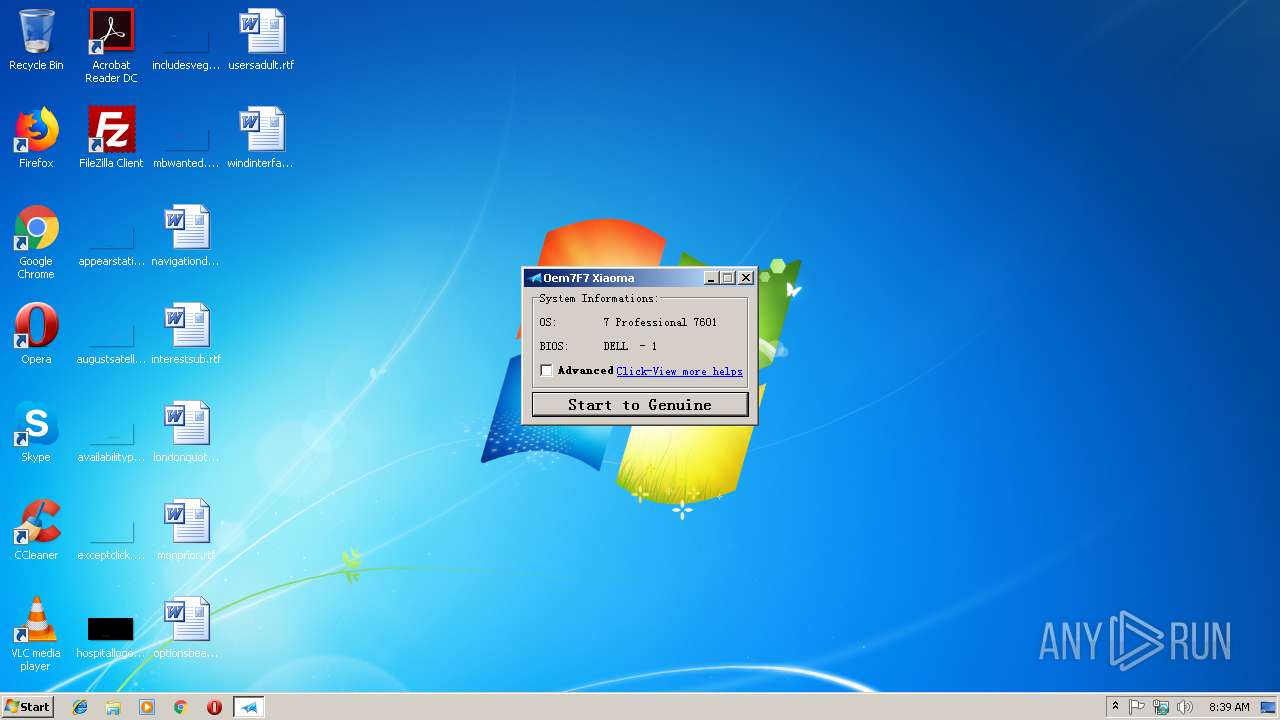
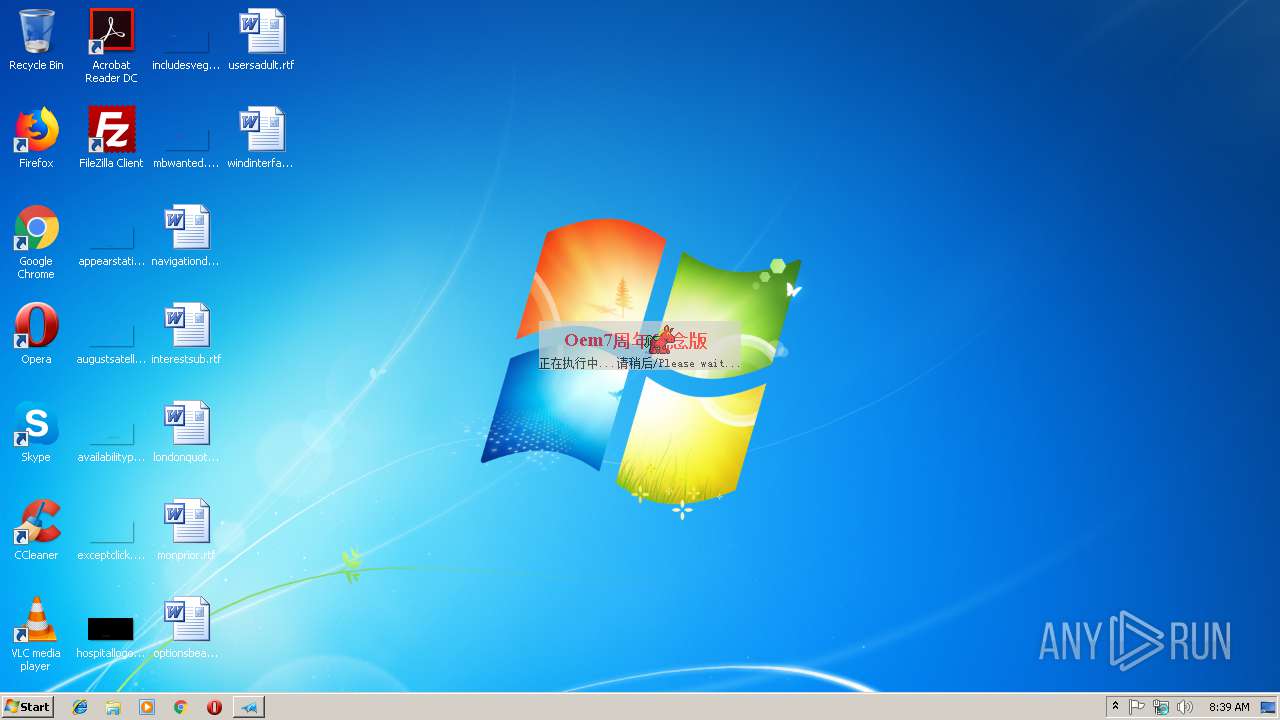
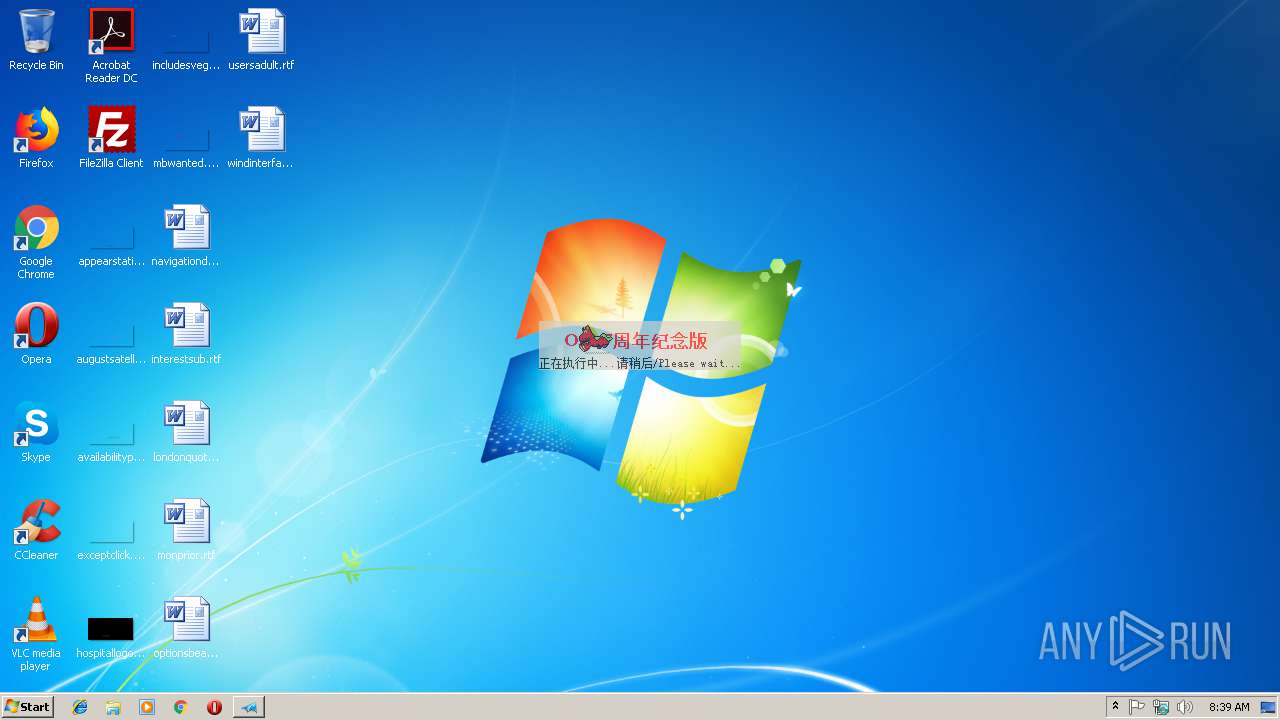
| File name: | Oem7F7.exe |
| Full analysis: | https://app.any.run/tasks/ebf257a7-46c8-47cc-b80d-550b46574e72 |
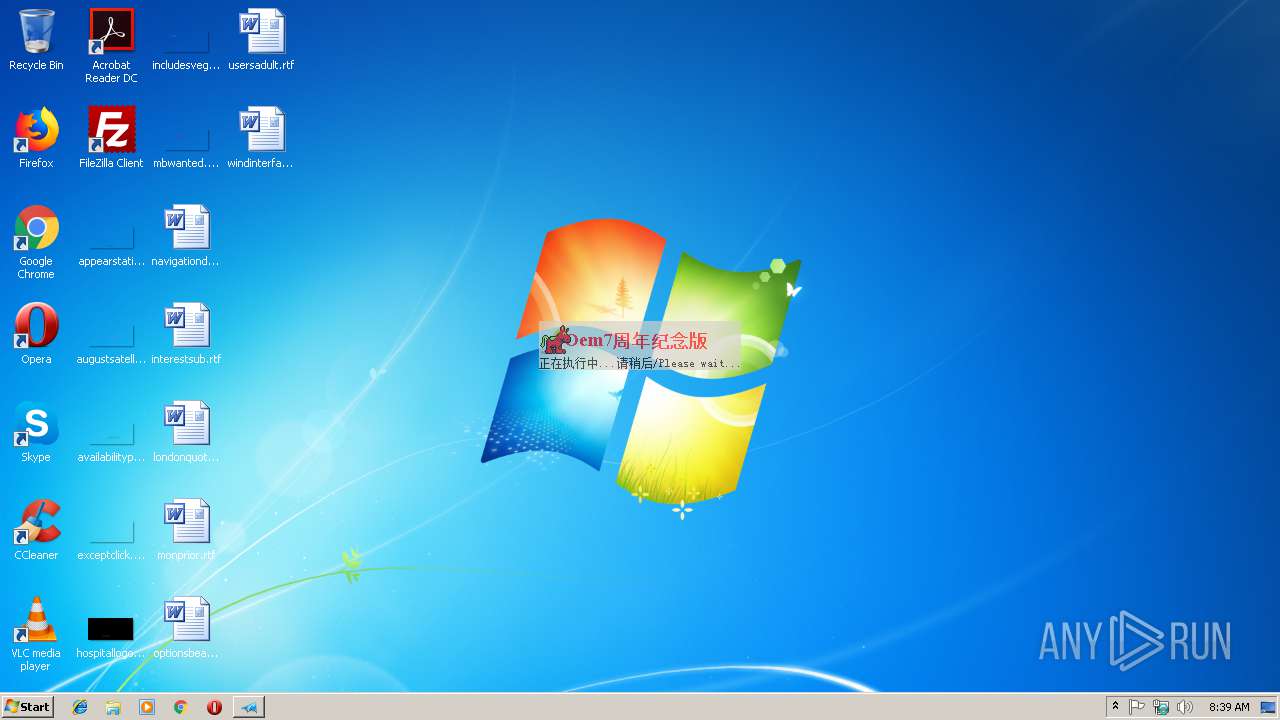
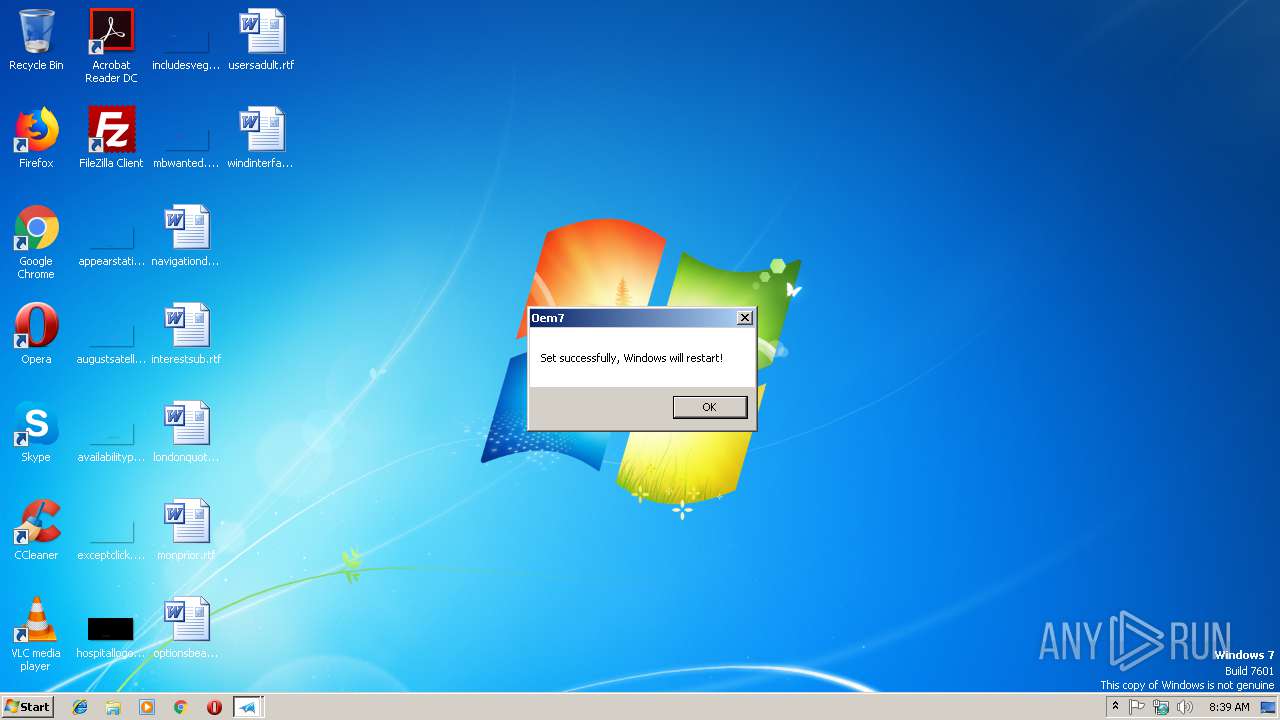
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2018, 08:38:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2B13B58CCBB7F3CE02C9BF957F7F529E |
| SHA1: | EE82D4425CE1F6D5193822139A5F0ABC8883CF38 |
| SHA256: | EF1EDC756D5635B96D1700223A31C71BF3B1020222DE4EE184161B44B16221EC |
| SSDEEP: | 12288:abvnf8UaJEjEKUBKuJyECjDW76LS/Uc7xX0gmbKgPdr/uduQXqOFuzsj5uJZv355:WvoTKUsEyEyK+LS3g9KXqKtu73aBi |
MALICIOUS
Application was dropped or rewritten from another process
- boot.exe (PID: 3132)
SUSPICIOUS
Low-level read access rights to disk partition
- run.exe (PID: 2568)
- run.exe (PID: 2252)
- boot.exe (PID: 3132)
Executes scripts
- cmd.exe (PID: 3640)
- cmd.exe (PID: 3328)
Starts CMD.EXE for commands execution
- Oem7F7.exe (PID: 3556)
Uses ATTRIB.EXE to modify file attributes
- Oem7F7.exe (PID: 3556)
Uses ICACLS.EXE to modify access control list
- Oem7F7.exe (PID: 3556)
Executable content was dropped or overwritten
- Oem7F7.exe (PID: 3556)
Reads Environment values
- Oem7F7.exe (PID: 3556)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (71.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.1) |
| .exe | | | Win16/32 Executable Delphi generic (5.5) |
| .exe | | | Generic Win/DOS Executable (5.3) |
| .exe | | | DOS Executable Generic (5.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:07:28 14:09:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 827392 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | 1712128 |
| EntryPoint: | 0x26bf00 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 7.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 605356316 |
| FileDescription: | 小马在线:www.pccppc.com |
| FileVersion: | 7.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Oem7 Final Release |
| ProductVersion: | 7.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jul-2010 12:09:42 |
| Detected languages: |
|
| CompanyName: | 605356316 |
| FileDescription: | 小马在线:www.pccppc.com |
| FileVersion: | 7.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Oem7 Final Release |
| ProductVersion: | 7.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Jul-2010 12:09:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
OEM0 | 0x00001000 | 0x001A2000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
OEM1 | 0x001A3000 | 0x000CA000 | 0x000C9200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93428 |
.rsrc | 0x0026D000 | 0x00013000 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.37616 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15974 | 763 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 2.50944 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 2.61639 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.99202 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 4.26408 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 2.60736 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 7.98196 | 39782 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 3.10685 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.18628 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 4.17076 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
61
Monitored processes
15
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | cscript //nologo C:\Windows\system32\slmgr.vbs -ilc C:\Users\admin\AppData\Local\Temp\license.xrm-ms | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1620 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\run.exe /inst sys >C:\Users\admin\AppData\Local\Temp\tmp.dll | C:\Windows\System32\cmd.exe | — | Oem7F7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2172 | "C:\Windows\System32\icacls.exe" D:\MBWEI /remove administrators | C:\Windows\System32\icacls.exe | — | Oem7F7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | C:\Users\admin\AppData\Local\Temp\run.exe /inst sys | C:\Users\admin\AppData\Local\Temp\run.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2568 | C:\Users\admin\AppData\Local\Temp\run.exe /inst sys | C:\Users\admin\AppData\Local\Temp\run.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2760 | "C:\Windows\System32\compact.exe" /u /a /i D:\MBWEI | C:\Windows\System32\compact.exe | — | Oem7F7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: File Compress Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | "C:\Windows\System32\icacls.exe" D:\MBWEI /inheritance:r | C:\Windows\System32\icacls.exe | — | Oem7F7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\Oem7F7.exe" | C:\Users\admin\AppData\Local\Temp\Oem7F7.exe | — | explorer.exe | |||||||||||
User: admin Company: 605356316 Integrity Level: MEDIUM Description: 小马在线:www.pccppc.com Exit code: 3221226540 Version: 7.0.0.0 | |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\boot.exe" /nt60 sys | C:\Users\admin\AppData\Local\Temp\boot.exe | — | Oem7F7.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Windows\System32\cmd.exe" /c cscript //nologo %windir%\system32\slmgr.vbs -ipk YKHFT-KW986-GK4PY-FDWYH-7TP9F >C:\Users\admin\AppData\Local\Temp\tmp2.dll | C:\Windows\System32\cmd.exe | — | Oem7F7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
463
Read events
459
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3556) Oem7F7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) Oem7F7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | Oem7F7.exe | C:\Users\admin\AppData\Local\Temp\run.exe | — | |
MD5:— | SHA256:— | |||
| 2568 | run.exe | \Device\HarddiskVolume1 | — | |
MD5:— | SHA256:— | |||
| 1620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tmp.dll | — | |
MD5:— | SHA256:— | |||
| 2252 | run.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 3760 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tmp.dll | — | |
MD5:— | SHA256:— | |||
| 3640 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tmp3.dll | — | |
MD5:— | SHA256:— | |||
| 3328 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tmp2.dll | — | |
MD5:— | SHA256:— | |||
| 3556 | Oem7F7.exe | C:\Users\admin\AppData\Local\Temp\boot.exe | executable | |
MD5:1386B69045A421D6314B6F25D5784090 | SHA256:8A29ADCAB8ED51D3D9A31C7AA932ECCA1937561B827CB800E8E2F5F0F9DAC97B | |||
| 3556 | Oem7F7.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\MBWEI | binary | |
MD5:— | SHA256:— | |||
| 3556 | Oem7F7.exe | C:\Users\admin\AppData\Local\Temp\license.xrm-ms | xml | |
MD5:F25832AF6A684360950DBB15589DE34A | SHA256:266D64637CF12FF961165A018F549FF41002DC59380605B36D65CF1B8127C96F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report