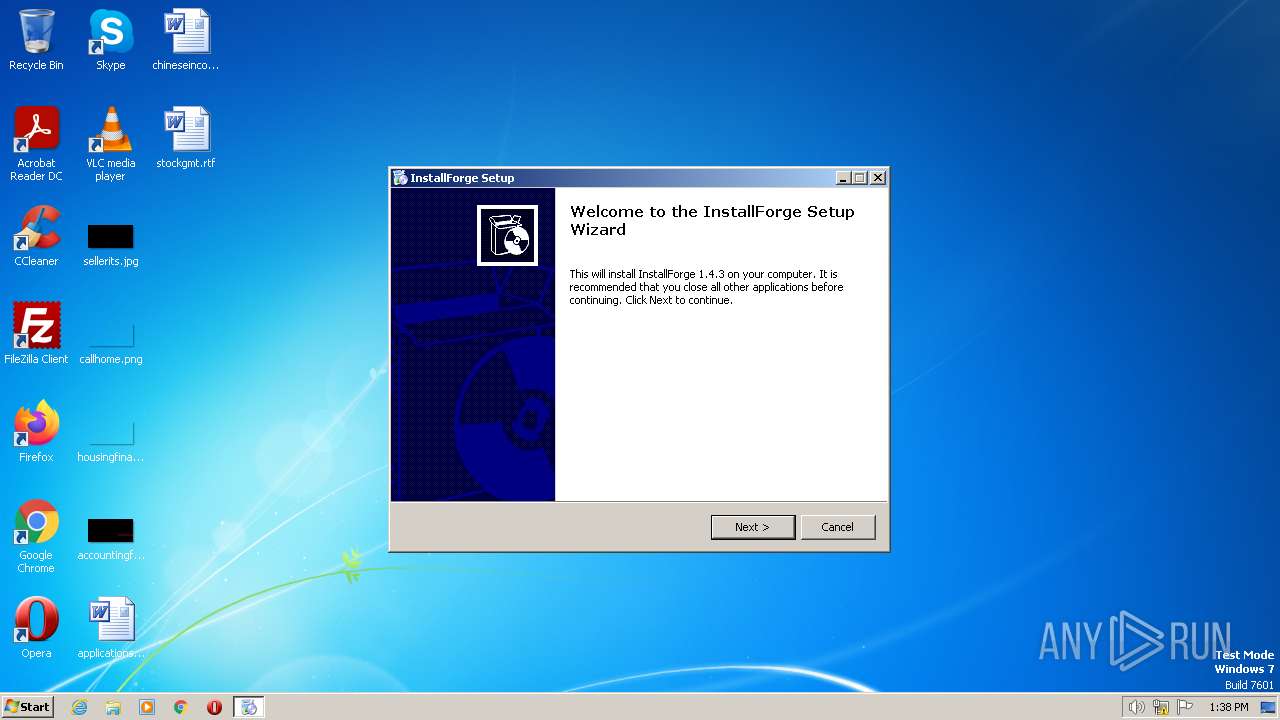
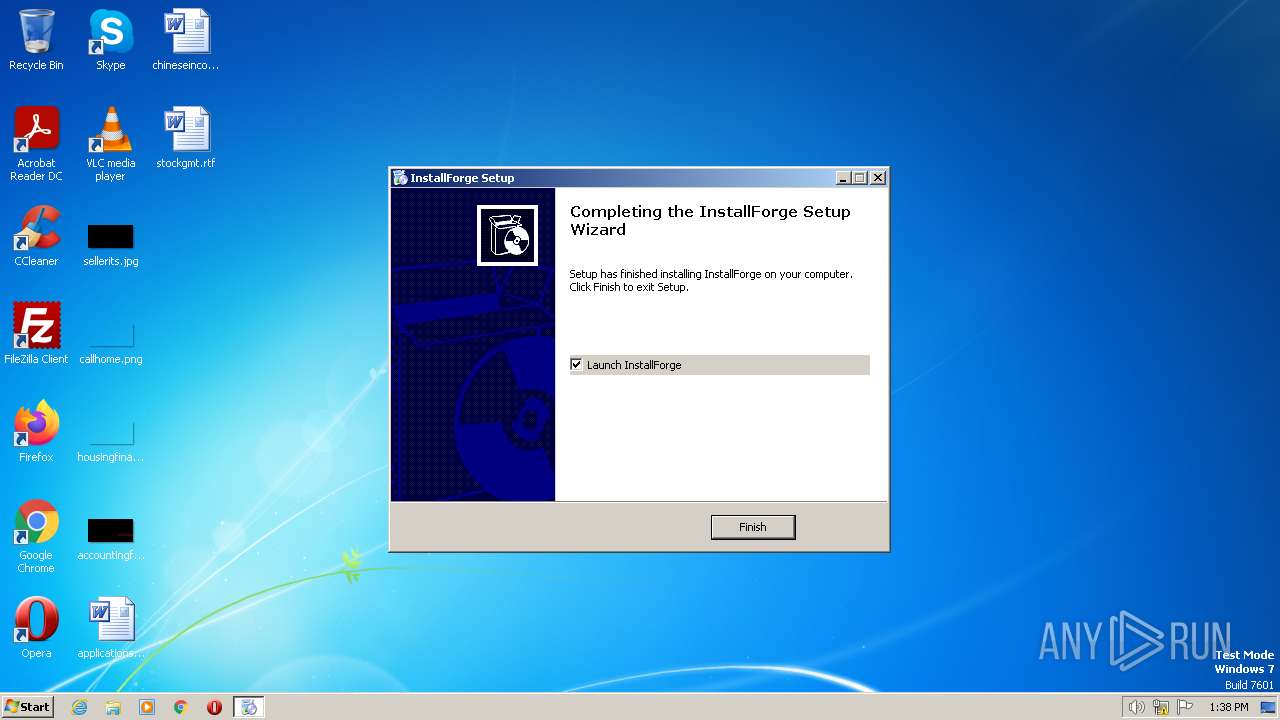
| File name: | IFSetup.exe |
| Full analysis: | https://app.any.run/tasks/96098174-aa92-4334-9669-9a5efda0632a |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2023, 12:38:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6634A65530D13E466A30BBC156937E84 |
| SHA1: | DCEE653892904C05419F6785711B1DAFBC21D126 |
| SHA256: | EF1B434BFCF30A878BEDCFE38E0A6AA2198C0BCFD7D26E3703BC0B6621129E2B |
| SSDEEP: | 49152:6jFpzaQ9DJ6T9f7B/heraIJU7sdGjodQj6F438v:+759y9dJaaxh8U6FSa |
MALICIOUS
Application was dropped or rewritten from another process
- ifbuilderenvx86.exe (PID: 1972)
Loads dropped or rewritten executable
- ifbuilderenvx86.exe (PID: 1972)
SUSPICIOUS
Reads the Internet Settings
- ifbuilderenvx86.exe (PID: 1972)
Executable content was dropped or overwritten
- IFSetup.exe (PID: 3776)
Reads settings of System Certificates
- ifbuilderenvx86.exe (PID: 1972)
Adds/modifies Windows certificates
- IFSetup.exe (PID: 3776)
Checks Windows Trust Settings
- ifbuilderenvx86.exe (PID: 1972)
Reads security settings of Internet Explorer
- ifbuilderenvx86.exe (PID: 1972)
INFO
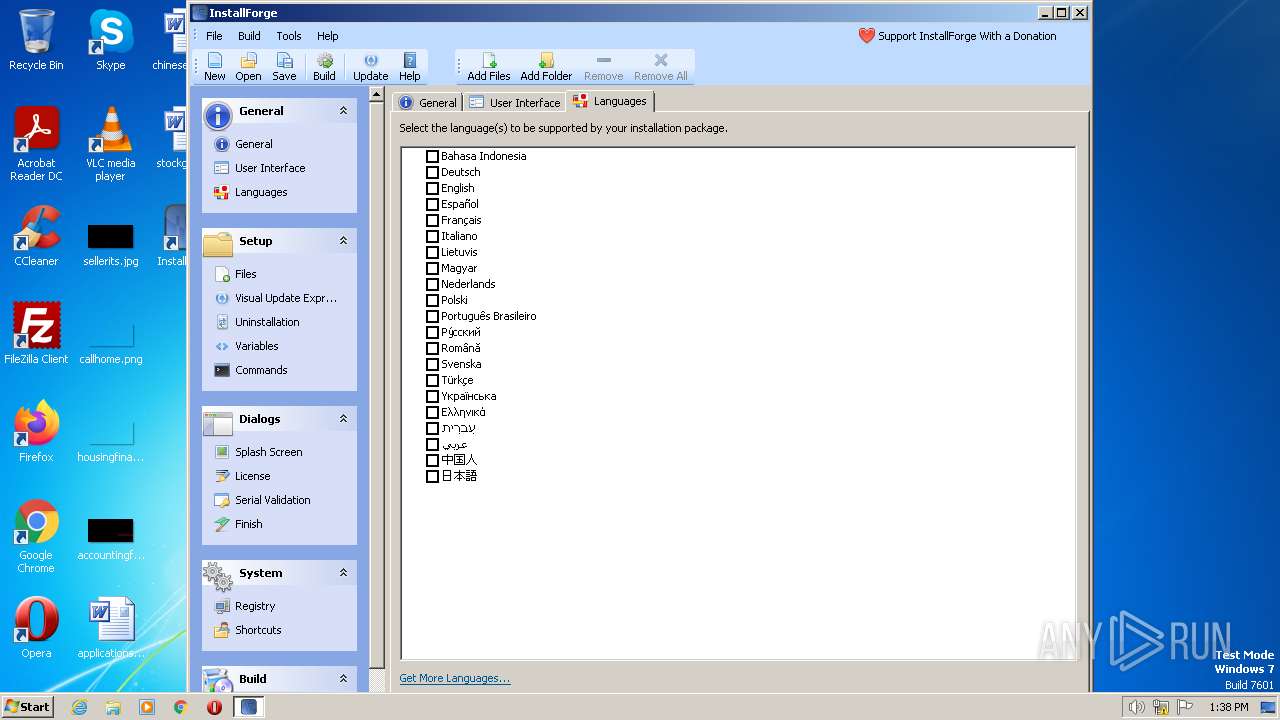
Checks supported languages
- IFSetup.exe (PID: 3776)
- ifbuilderenvx86.exe (PID: 1972)
The process checks LSA protection
- IFSetup.exe (PID: 3776)
- ifbuilderenvx86.exe (PID: 1972)
Reads the computer name
- IFSetup.exe (PID: 3776)
- ifbuilderenvx86.exe (PID: 1972)
Create files in a temporary directory
- IFSetup.exe (PID: 3776)
- ifbuilderenvx86.exe (PID: 1972)
Creates files or folders in the user directory
- IFSetup.exe (PID: 3776)
- ifbuilderenvx86.exe (PID: 1972)
Checks proxy server information
- ifbuilderenvx86.exe (PID: 1972)
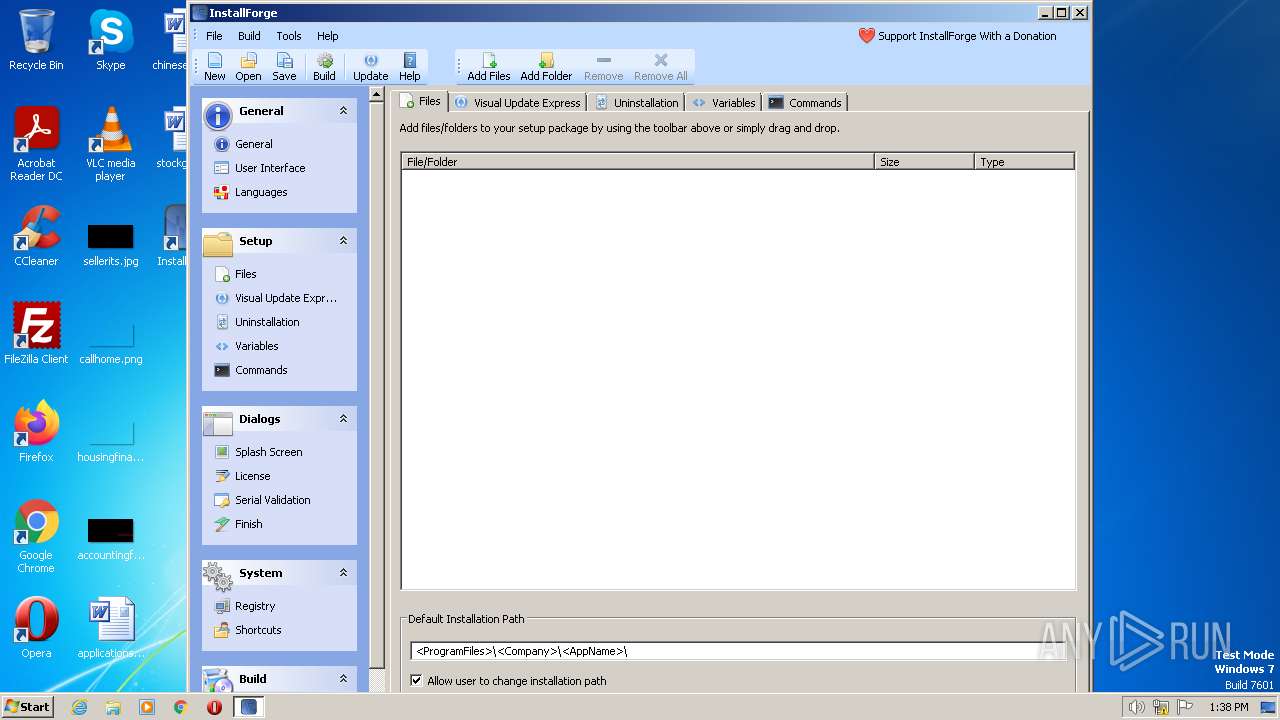
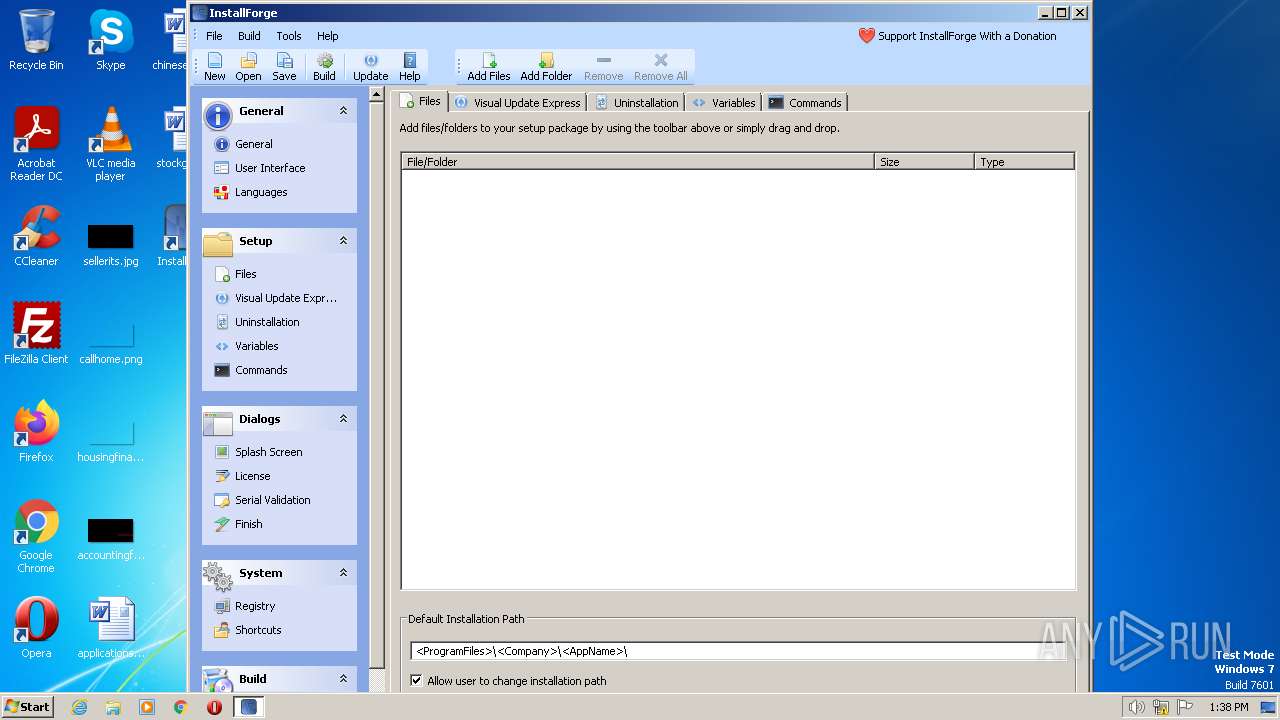
Creates files in the program directory
- IFSetup.exe (PID: 3776)
Reads the machine GUID from the registry
- ifbuilderenvx86.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (47) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (34.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.1) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
EXIF
EXE
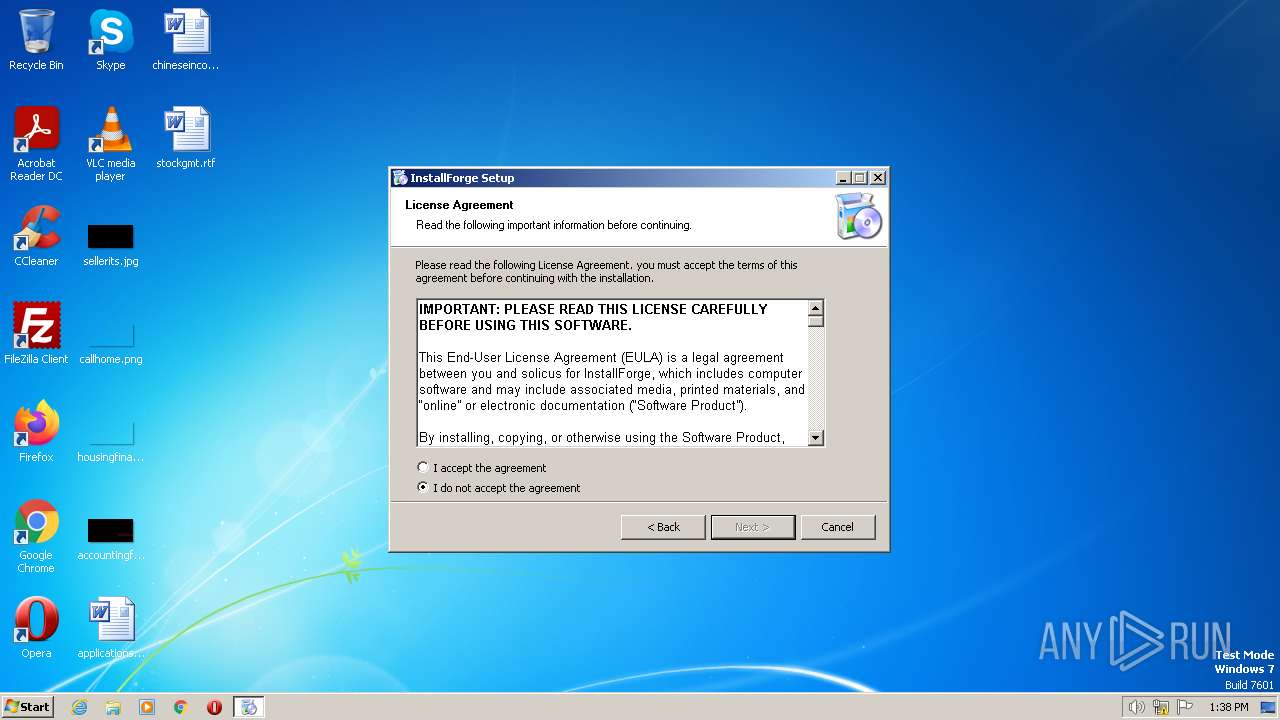
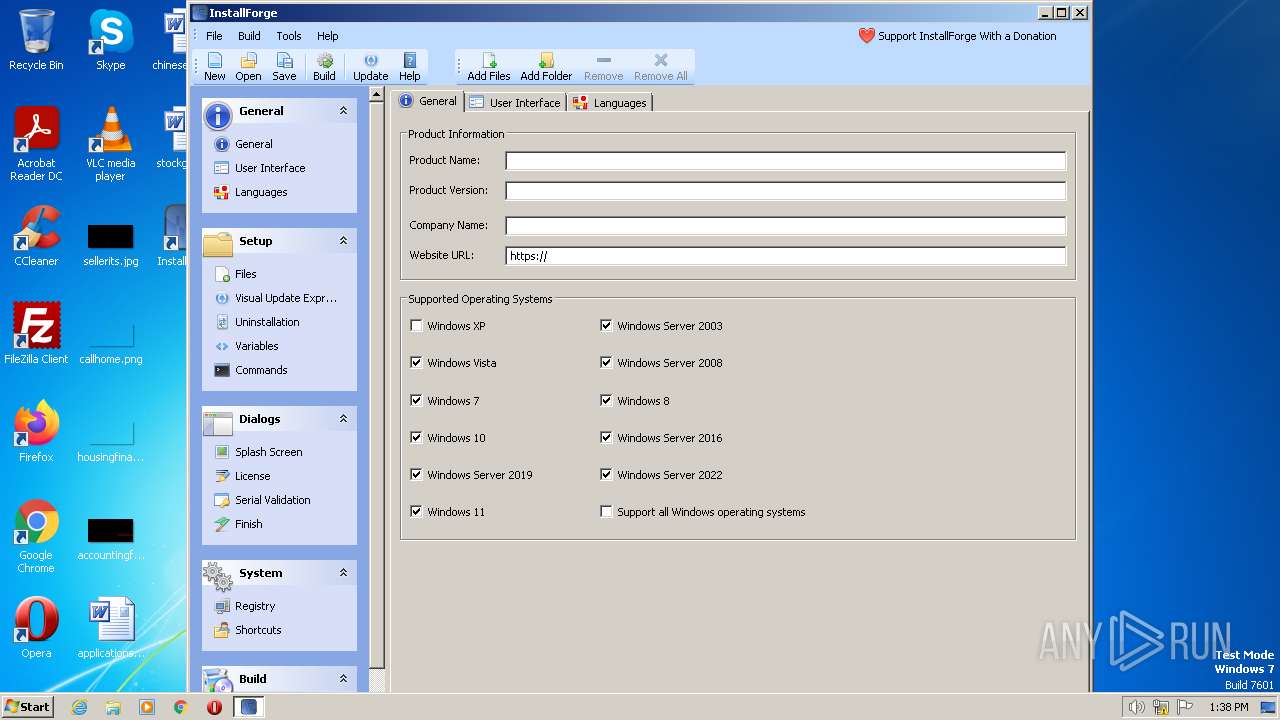
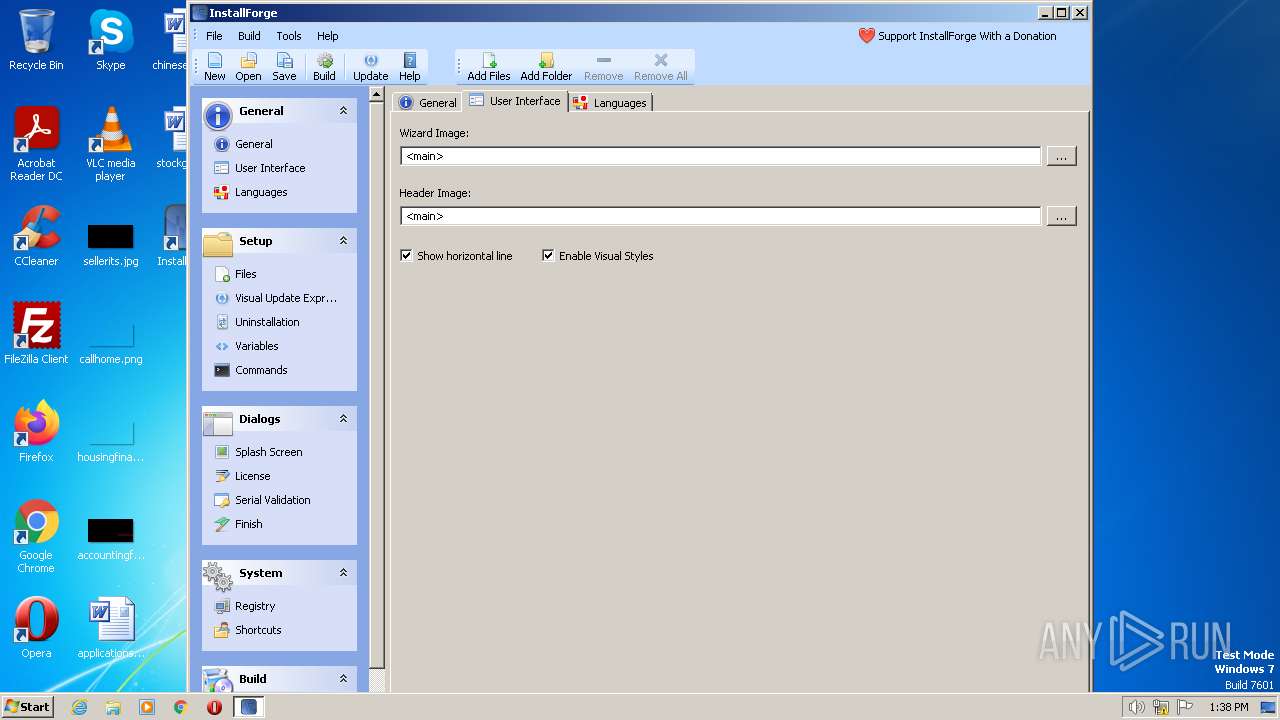
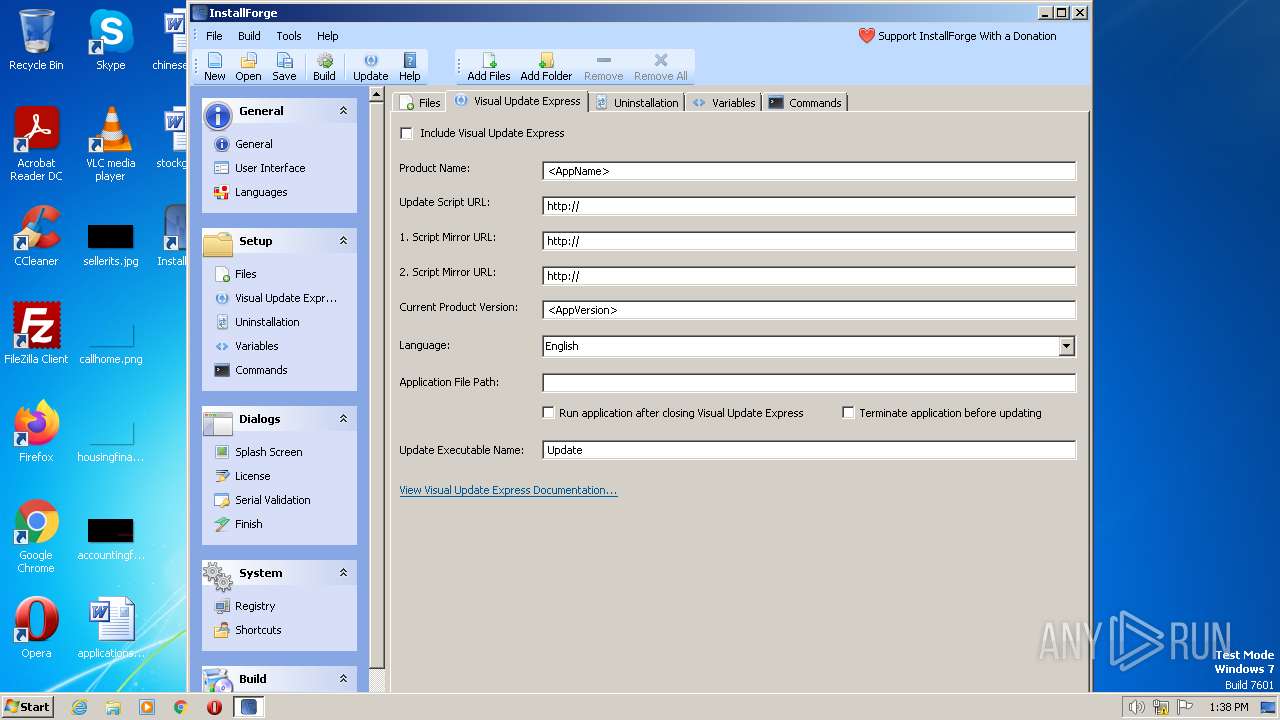
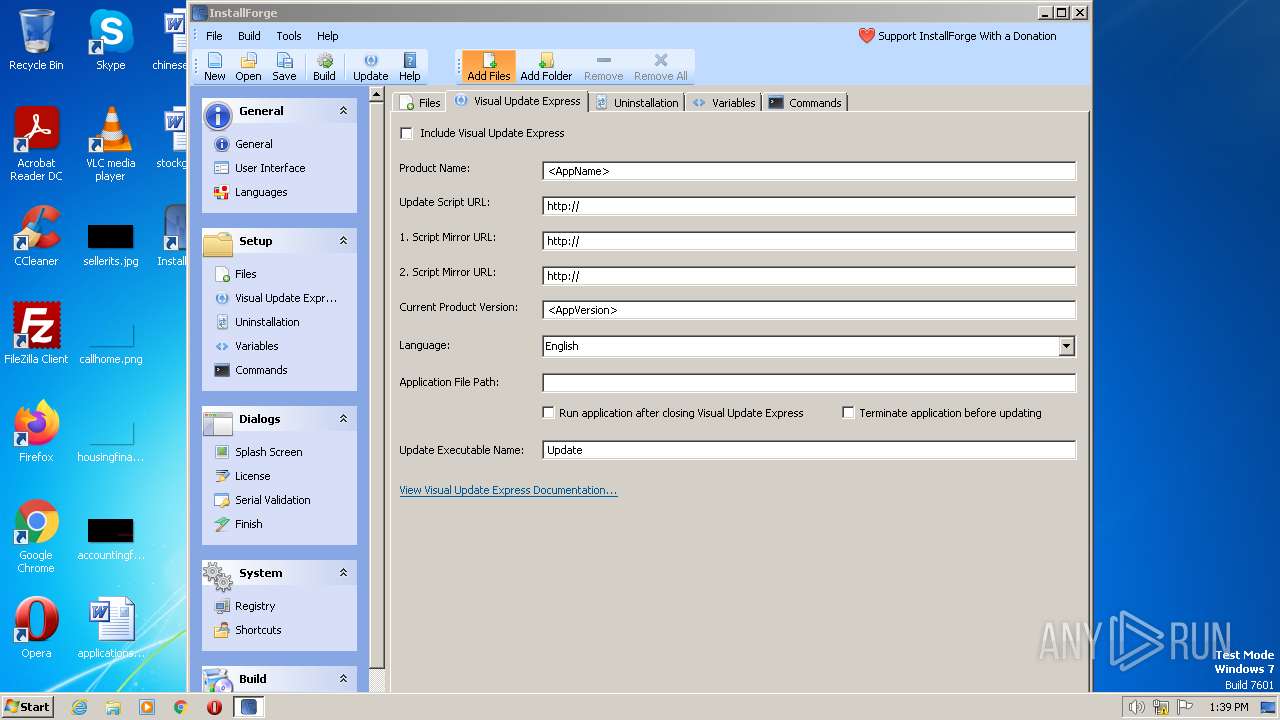
| Comments: | Created with InstallForge 1.4.3 |
|---|---|
| CompanyName: | solicus |
| FileVersion: | 1.4.3 |
| ProductVersion: | 1.4.3 |
| OriginalFileName: | IFSetup.exe |
| InternalName: | IFSetup |
| ProductName: | InstallForge Setup |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.4.3.0 |
| FileVersionNumber: | 1.4.3.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x16276 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 204800 |
| CodeSize: | 795648 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| TimeStamp: | 2023:06:16 19:57:54+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
43
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
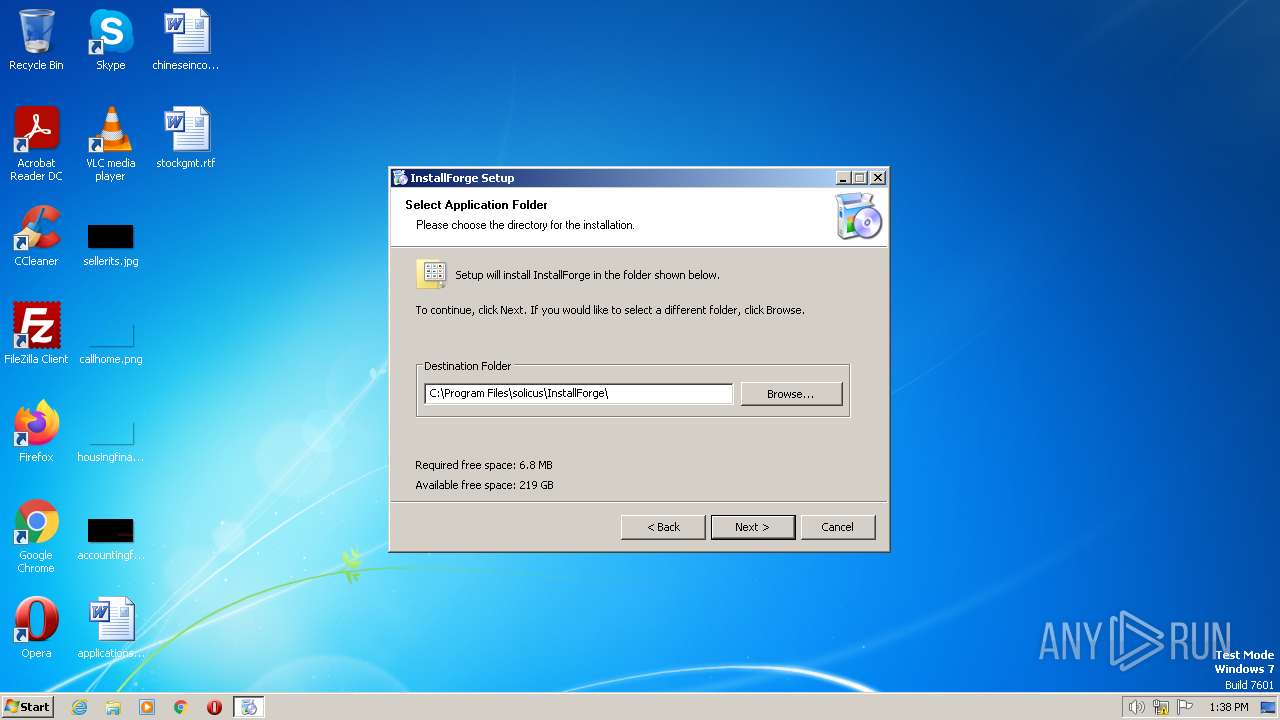
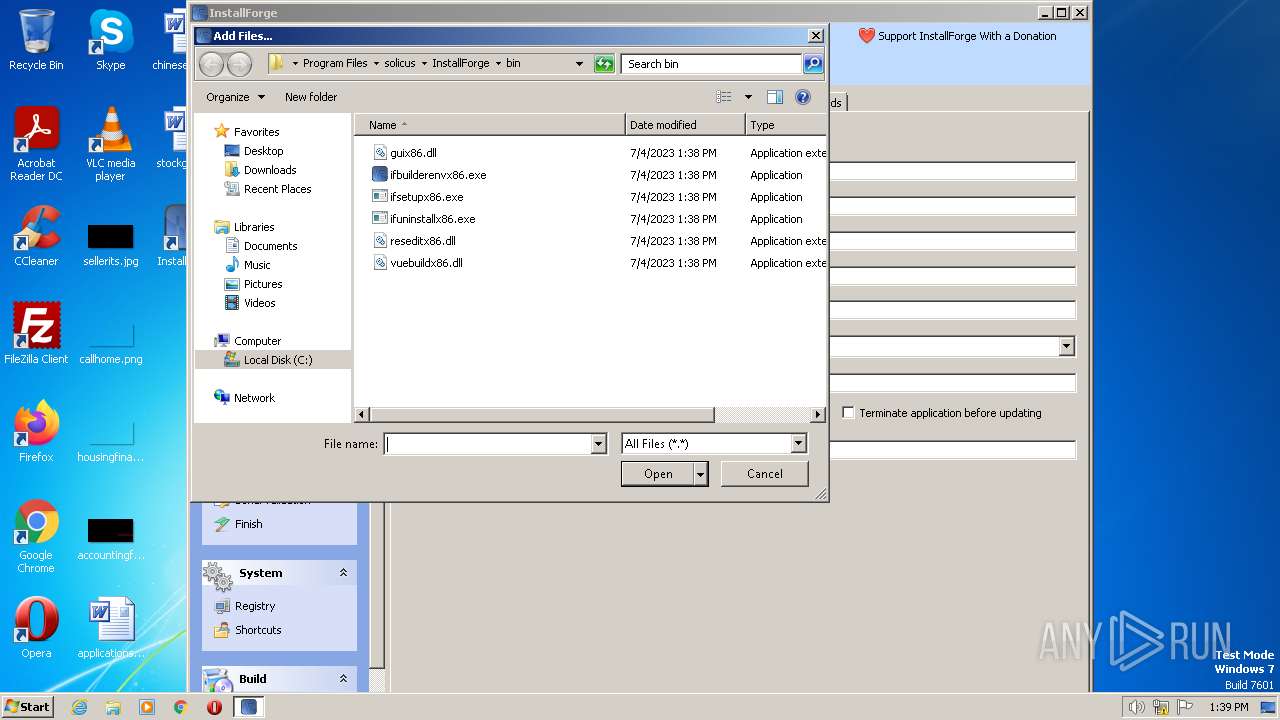
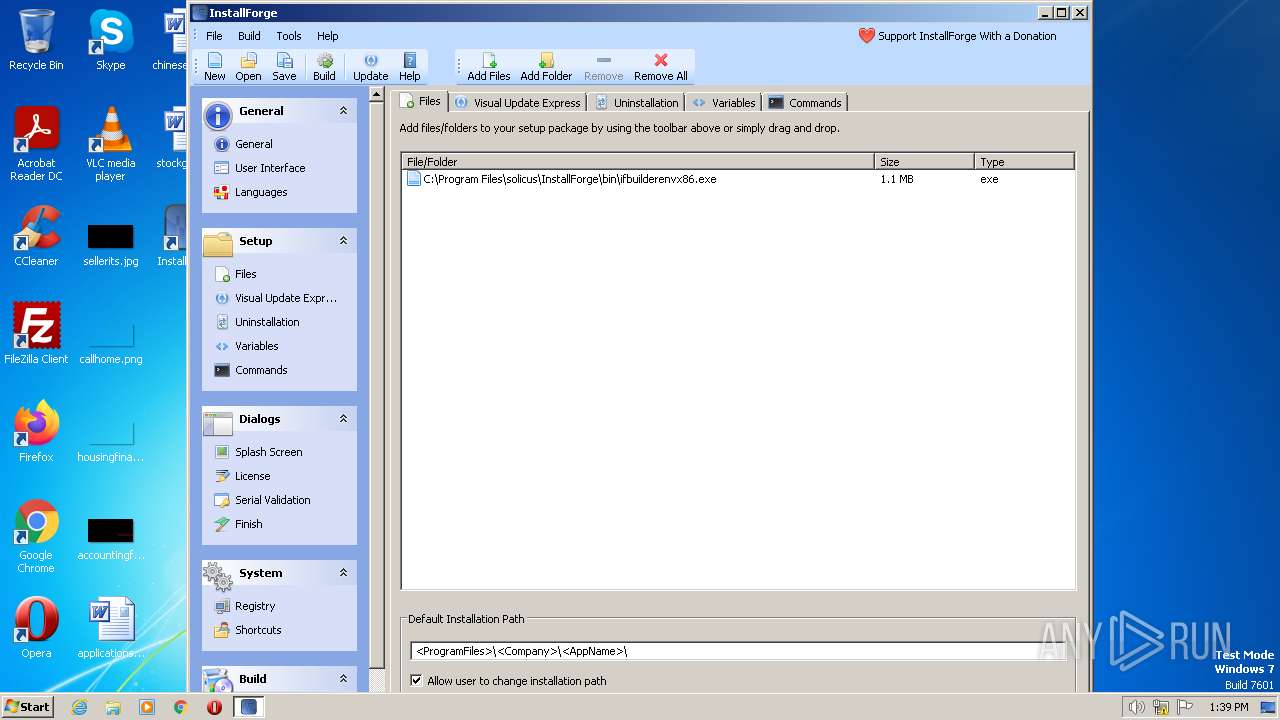
| 1972 | "C:\Program Files\solicus\InstallForge\bin\ifbuilderenvx86.exe" | C:\Program Files\solicus\InstallForge\bin\ifbuilderenvx86.exe | IFSetup.exe | ||||||||||||
User: admin Company: solicus Integrity Level: HIGH Description: InstallForge Builder Environment Exit code: 0 Version: 1.4.3 Modules
| |||||||||||||||
| 3776 | "C:\Users\admin\AppData\Local\Temp\IFSetup.exe" | C:\Users\admin\AppData\Local\Temp\IFSetup.exe | explorer.exe | ||||||||||||
User: admin Company: solicus Integrity Level: HIGH Exit code: 0 Version: 1.4.3 Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\IFSetup.exe" | C:\Users\admin\AppData\Local\Temp\IFSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: solicus Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.4.3 Modules
| |||||||||||||||
Total events
6 100
Read events
6 045
Write events
54
Delete events
1
Modification events
| (PID) Process: | (3776) IFSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1972) ifbuilderenvx86.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
8
Suspicious files
7
Text files
39
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\default.ifl | text | |
MD5:2922D0C758D9C3C10CBDC59F91979D0C | SHA256:20F6D12EAC29BD6DDC6A99DD276C5E200FAC25C976AB4293195B58EC164C253F | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\Startmenu.dat | text | |
MD5:E0BDF877B4CD4789B4051024BB3F12E4 | SHA256:57A3834A5FE31A2B4C39AD1166E3E656964B36A7FCE5E5B43417D134EB058824 | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\licence.rtf | text | |
MD5:A64DF9FE29DFC0F7B0B98680BE73E2E7 | SHA256:3FCCABA3CF733881641866E8C20DB5771E30D9B30ECD1338883714E53C0707F9 | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\setupArchive.archive | compressed | |
MD5:5CCF9E60DCEFA514A8583F185019B9FA | SHA256:6BE6E51B6BC75F5071BF22DEB660514BE721F5B46896D91044E3588AE6CB07C9 | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\setupConfiguration.archive | compressed | |
MD5:70D8493274114B63A87E388CCDE52A3D | SHA256:B1C876933866F8AD5359AF48B3FE941B529487AABC11C3D002E3252E33BF4B50 | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\SC.dat | text | |
MD5:7AC1F2E887D394CA64C6E38803E2D8AF | SHA256:769C9C55DE2019244E812B7ACA6C968B38AB76889DCDCDE3D68A00F85B2ED2ED | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\Desktop.dat | text | |
MD5:34519FE799729D305FA976A4C0052ACB | SHA256:0B127A84237632D878B246A1F3E81CCF161CB34481C75514B45CA809B318CBF5 | |||
| 3776 | IFSetup.exe | C:\Users\admin\AppData\Local\Temp\IF{7F089E0E-2E18-4C4E-A85D-8645839C95B7}\OS.dat | text | |
MD5:2003B4200D267A1A7DE4674F34CAEB45 | SHA256:1974A84C2725340E5688ADB2EE274FB599F1462A7A331A92FE61B78BED1081E4 | |||
| 3776 | IFSetup.exe | C:\Program Files\solicus\InstallForge\bin\reseditx86.dll | executable | |
MD5:B83164608060B018677907622A74527B | SHA256:5389C51DB52FEBA174EE70D1AFB4A4A5D4CB13CCBFF0F74867D3F15B1C6E0C35 | |||
| 3776 | IFSetup.exe | C:\Program Files\solicus\InstallForge\Uninstall.exe | executable | |
MD5:968434C297A3615EF4EC55AA5F9D4E45 | SHA256:3643B2E6521B4D95A5299B0459A02F6A883D471BBBB98A9AD49CEA8C5CE395A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1972 | ifbuilderenvx86.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 2.05 Kb | whitelisted |
1972 | ifbuilderenvx86.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.starfieldtech.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCQCXWGLvhbpGGQ%3D%3D | US | der | 2.10 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
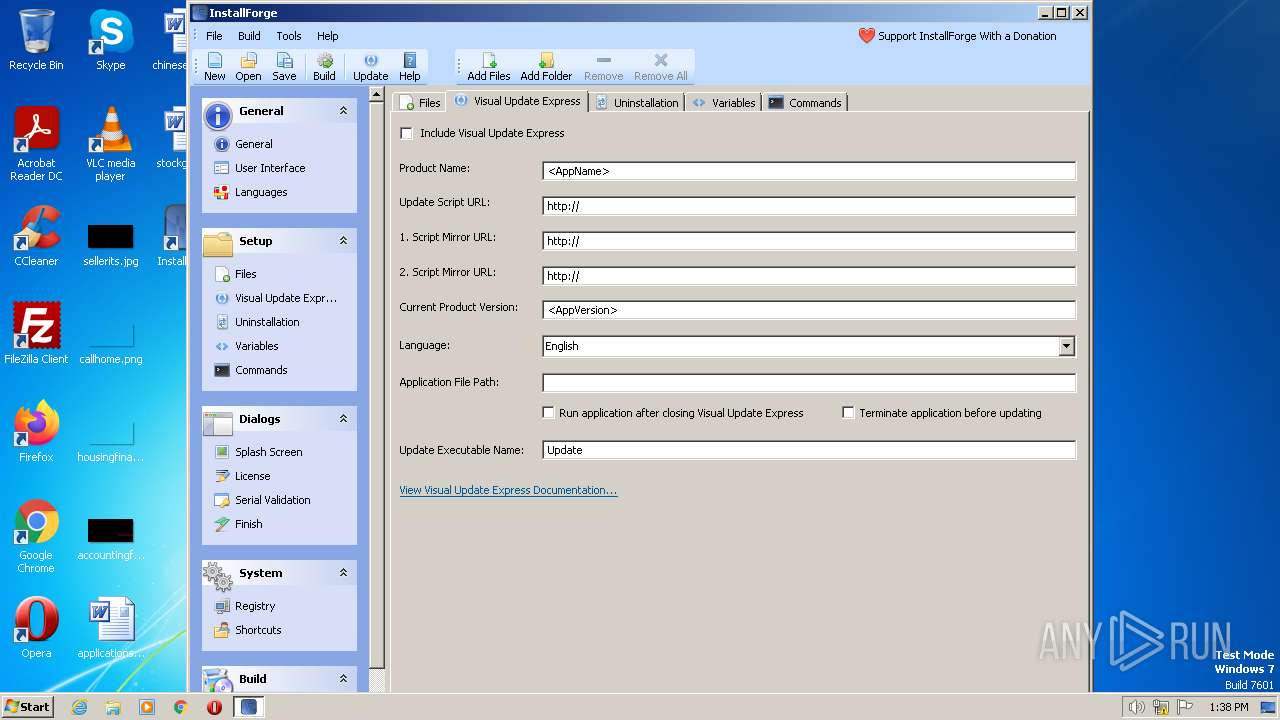
1972 | ifbuilderenvx86.exe | 5.175.14.17:443 | installforge.net | Host Europe GmbH | FR | suspicious |
2744 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1972 | ifbuilderenvx86.exe | 192.124.249.24:80 | ocsp.starfieldtech.com | SUCURI-SEC | US | suspicious |
1972 | ifbuilderenvx86.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
installforge.net |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |