| download: | download.php |
| Full analysis: | https://app.any.run/tasks/7c1b484c-5c70-4f87-ac43-fd66780027e8 |
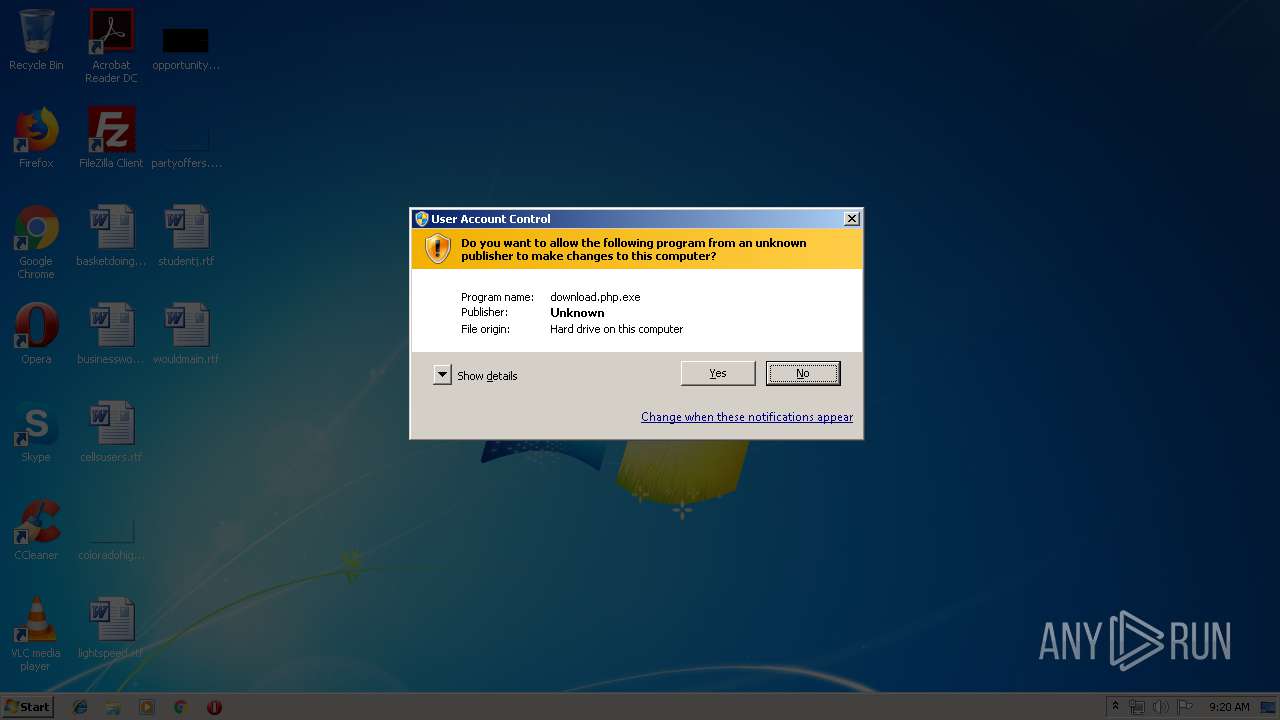
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 08:20:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
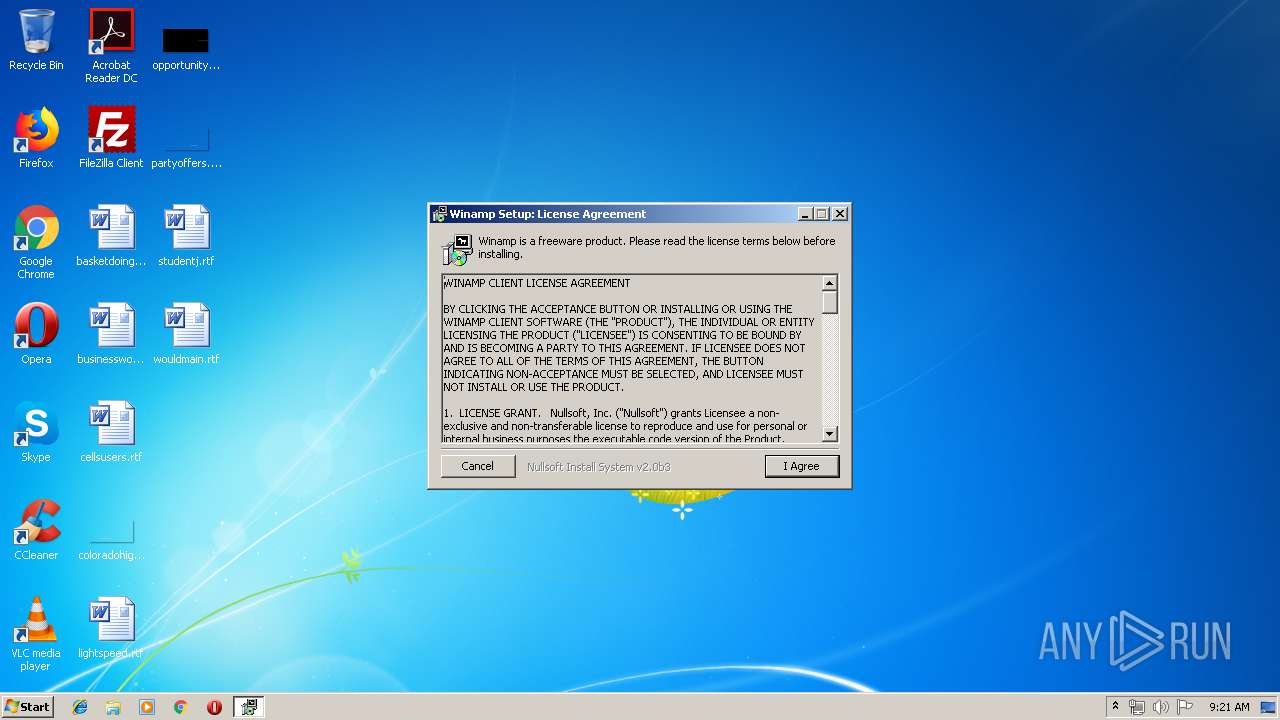
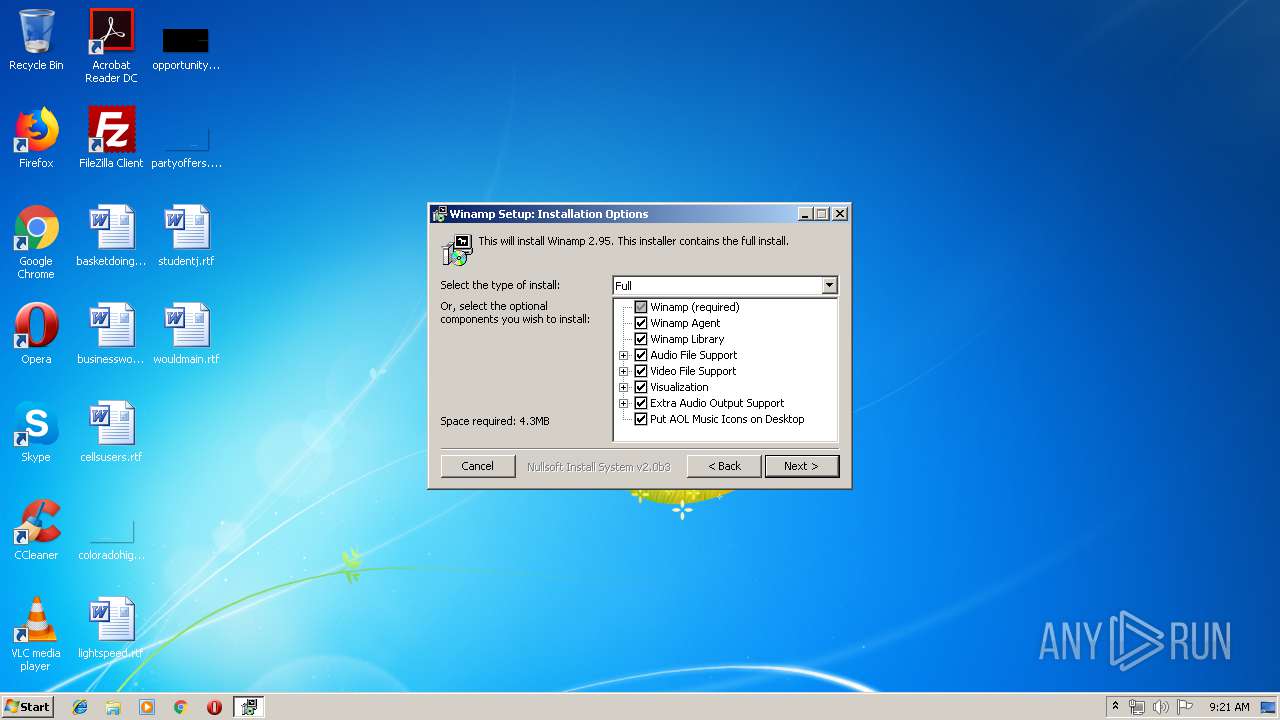
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1F19A5F196D8D79880D9B66D160034B6 |
| SHA1: | D859A19D4C614A789D302F4EDD2E4DF65A2C0869 |
| SHA256: | EF1423999CBEFD4F2A3A98ACEE2B194A4260268CB4517ABDA9F12963E866B7E5 |
| SSDEEP: | 49152:bO19djKdy5E/hVtfp0JqIfKJ2kIo/t/zIWy2aGJ7ndnaD4f23D:b0dZE/P70JryJLZ7IEaGFdaM+z |
MALICIOUS
Application was dropped or rewritten from another process
- AOLOnDesktop.exe (PID: 2408)
Loads dropped or rewritten executable
- AOLOnDesktop.exe (PID: 2408)
- download.php.exe (PID: 2384)
SUSPICIOUS
Creates COM task schedule object
- download.php.exe (PID: 2384)
Executable content was dropped or overwritten
- download.php.exe (PID: 2384)
Creates files in the program directory
- download.php.exe (PID: 2384)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:03:16 18:41:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 155136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4046 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Mar-2003 17:41:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Mar-2003 17:41:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005DCA | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47033 |
.rdata | 0x00007000 | 0x000011D4 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23449 |
.data | 0x00009000 | 0x00023BFC | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.01799 |
.rsrc | 0x0002D000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.56443 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50665 | 744 | UNKNOWN | English - United States | RT_ICON |
102 | 2.73222 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.69903 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.93214 | 348 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.61256 | 196 | UNKNOWN | English - United States | RT_DIALOG |
109 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
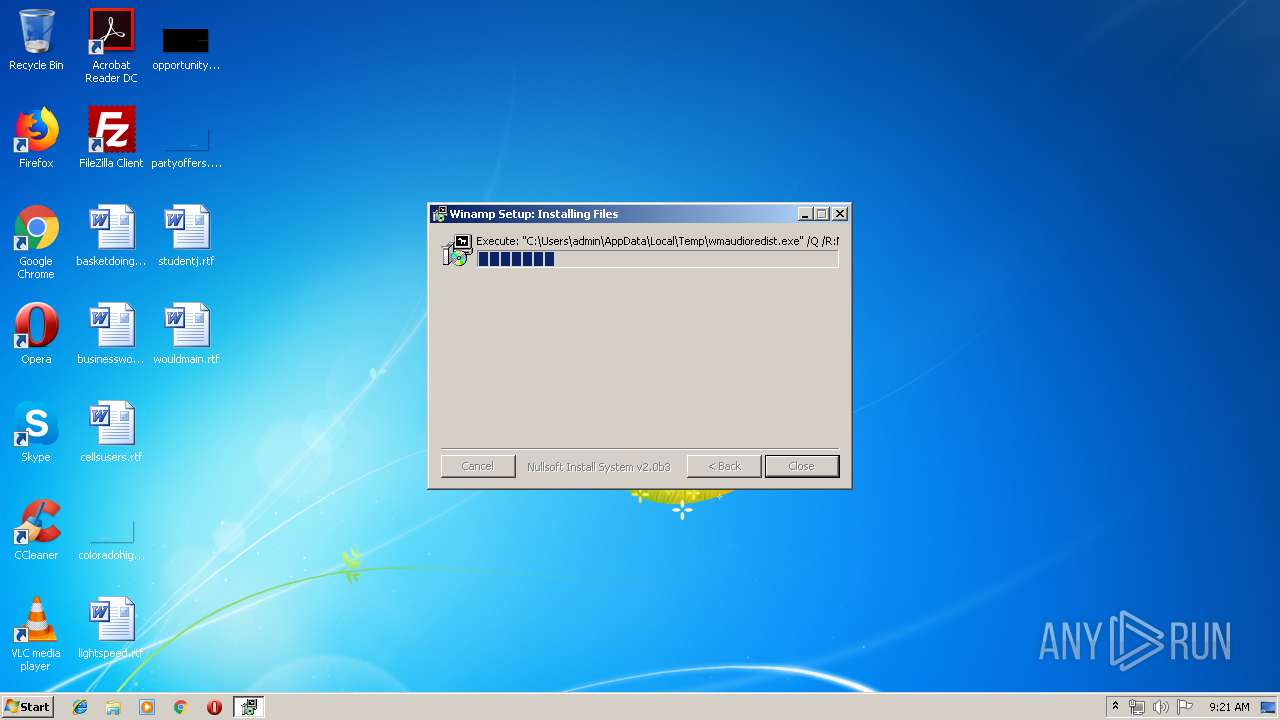
| 2312 | "C:\Users\admin\AppData\Local\Temp\wmaudioredist.exe" /Q /R:N | C:\Users\admin\AppData\Local\Temp\wmaudioredist.exe | — | download.php.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\download.php.exe" | C:\Users\admin\AppData\Local\Temp\download.php.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Winamp\AOD\AOLOnDesktop.exe" | C:\Program Files\Winamp\AOD\AOLOnDesktop.exe | — | download.php.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\AppData\Local\Temp\download.php.exe" | C:\Users\admin\AppData\Local\Temp\download.php.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
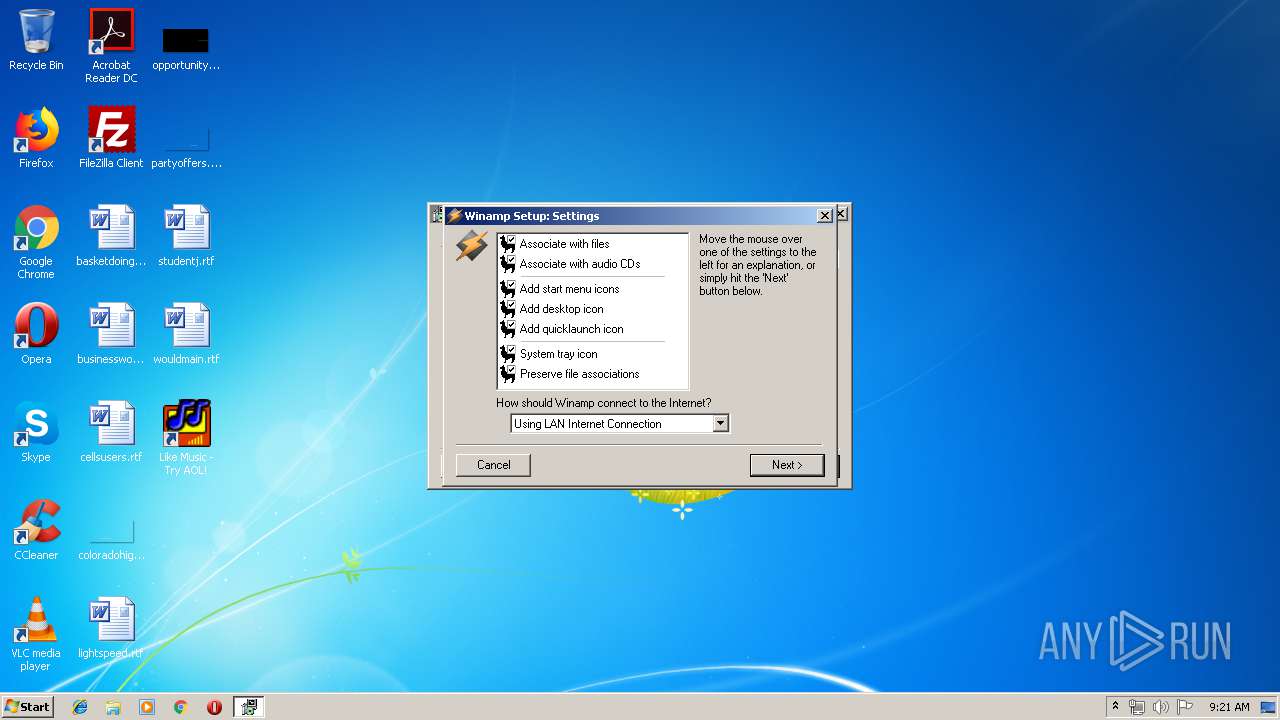
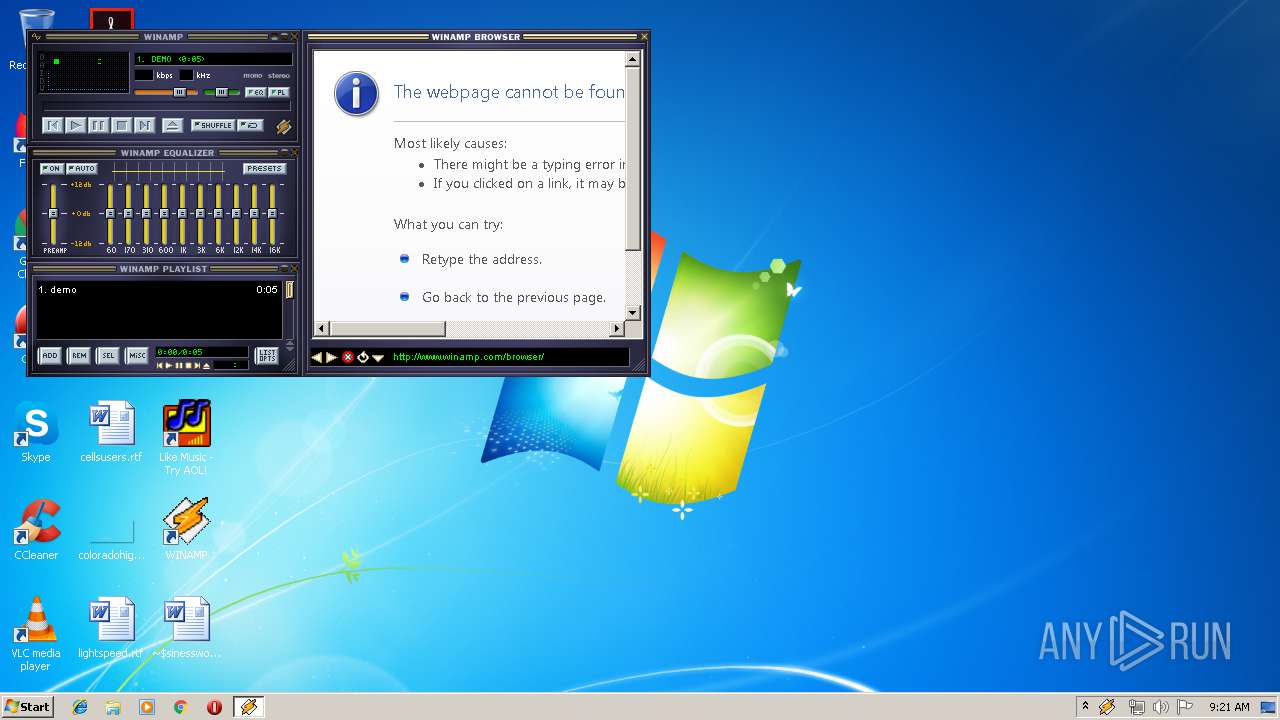
| 3808 | "C:\Program Files\Winamp\Winamp.exe" /INSTALL | C:\Program Files\Winamp\Winamp.exe | — | download.php.exe | |||||||||||
User: admin Company: Nullsoft Integrity Level: HIGH Description: Winamp Exit code: 0 Version: 2.95 | |||||||||||||||
Total events
91
Read events
25
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CDDBControlWinamp.CddbDisc.1 |
| Operation: | write | Name: | |
Value: CddbDisc Class | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CDDBControlWinamp.CddbDisc.1\CLSID |
| Operation: | write | Name: | |
Value: {fba38bcf-e23d-4979-811e-1326bbadb8c8} | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CDDBControlWinamp.CddbDisc |
| Operation: | write | Name: | |
Value: CddbDisc Class | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CDDBControlWinamp.CddbDisc\CLSID |
| Operation: | write | Name: | |
Value: {fba38bcf-e23d-4979-811e-1326bbadb8c8} | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CDDBControlWinamp.CddbDisc\CurVer |
| Operation: | write | Name: | |
Value: CDDBControlWinamp.CddbDisc.1 | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{fba38bcf-e23d-4979-811e-1326bbadb8c8} |
| Operation: | write | Name: | |
Value: CddbDisc Class | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{fba38bcf-e23d-4979-811e-1326bbadb8c8}\ProgID |
| Operation: | write | Name: | |
Value: CDDBControlWinamp.CddbDisc.1 | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{fba38bcf-e23d-4979-811e-1326bbadb8c8}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: CDDBControlWinamp.CddbDisc | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{fba38bcf-e23d-4979-811e-1326bbadb8c8}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\Winamp\Plugins\cddbcontrolwinamp.dll | |||
| (PID) Process: | (2384) download.php.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{fba38bcf-e23d-4979-811e-1326bbadb8c8}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
28
Suspicious files
0
Text files
8
Unknown types
114
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | download.php.exe | C:\Users\admin\AppData\Local\Temp\wmaudioredist.exe | — | |
MD5:— | SHA256:— | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\demo.mp3 | mp3 | |
MD5:5B9FC63F9D440BC6078CBDD21AB2A9D9 | SHA256:235EF3F11F9D0D7E79C64C380F939B6B1C6C1EF7C34FCEAA31075114C7280C49 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\winamp.m3u | text | |
MD5:A9FCF40B19E3F8CB024C56C5877E7455 | SHA256:DFBCBDD41A68CB584FEC4810494577D9C17D1445D5883572B6770B257150701F | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\winampa.exe | executable | |
MD5:5CDC66EF7A6F570A583BD72C23E68FF2 | SHA256:CCAC28D8D019EC3589D1A8E6E1B7212B270320A9542749EF8510D844A5A2B917 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\Plugins\out_wm.dll | executable | |
MD5:24CDEEB658E64C9C4A76520DD4FE1D4F | SHA256:22448FF8CED438A1B9E8ECC416A432774988C24424CA860CB56BD91FE616FF3F | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\whatsnew.txt | text | |
MD5:A94750CF375C4E33882F4C4B1CB3EBEA | SHA256:FAAE09C2B587503C21569B8B50F2BB0045D4C79F74FC964A68AA7755975F6898 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\winamp.exe | executable | |
MD5:12FCB383F0FAF2F3CC037A6A2FFE84B0 | SHA256:BCA7A9FE1626B487D1B47BB5210670CF572D1A4CCE23062076641D583B268561 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\Plugins\in_vorbis.dll | executable | |
MD5:7D79F27332A6B132896EE96E882334FE | SHA256:56F71FBB665A66605C982B100A90C6E24CA8ADEE1A37DD141ADE7D67500A0926 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\Plugins\enc_vorbis.dll | executable | |
MD5:B00281645BBBEA2E6638C96620642B27 | SHA256:91AB948E6A690A2B8EFEC0A9D9B6EB4EFE8572BD41591F7CDCF4BE9C6E062AA5 | |||
| 2384 | download.php.exe | C:\Program Files\Winamp\Plugins\in_cdda.dll | executable | |
MD5:1D231CE9B3CC4A24612D1F4EBDE357F4 | SHA256:A68A3AB17416DBADFA22D186954E35CEFA8A1A0049A7AE1862613EBD36600B02 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
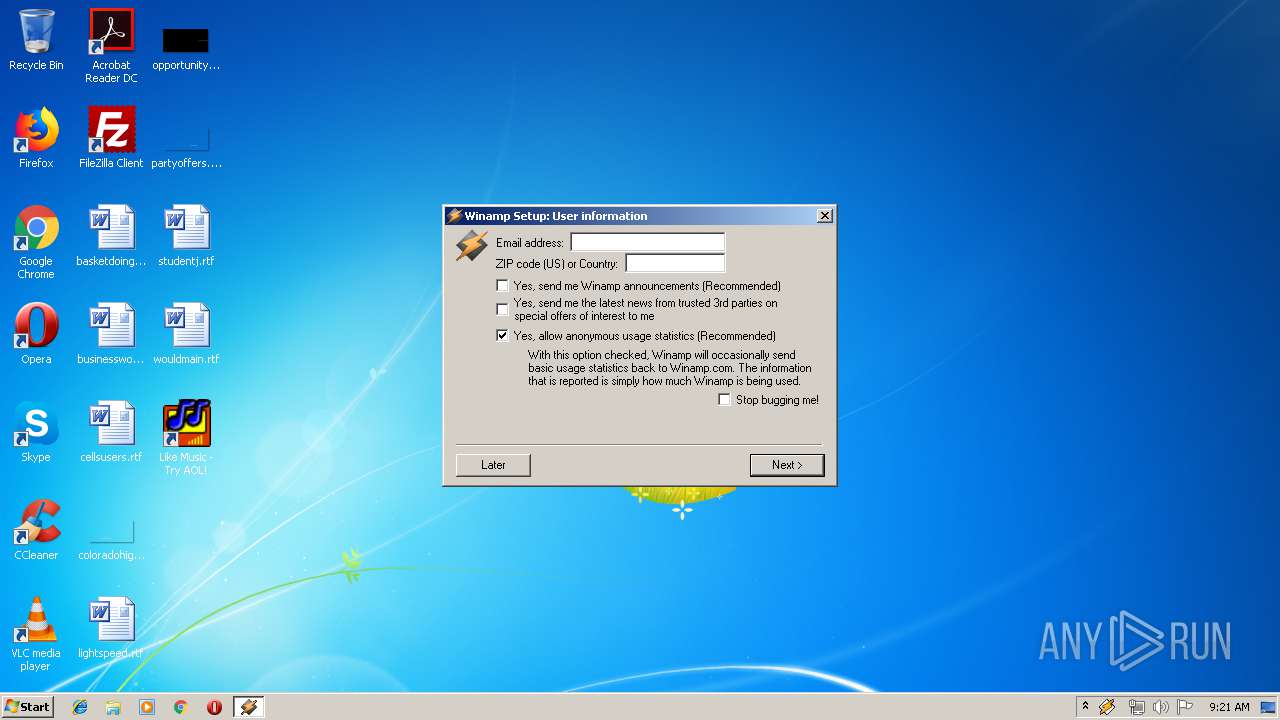
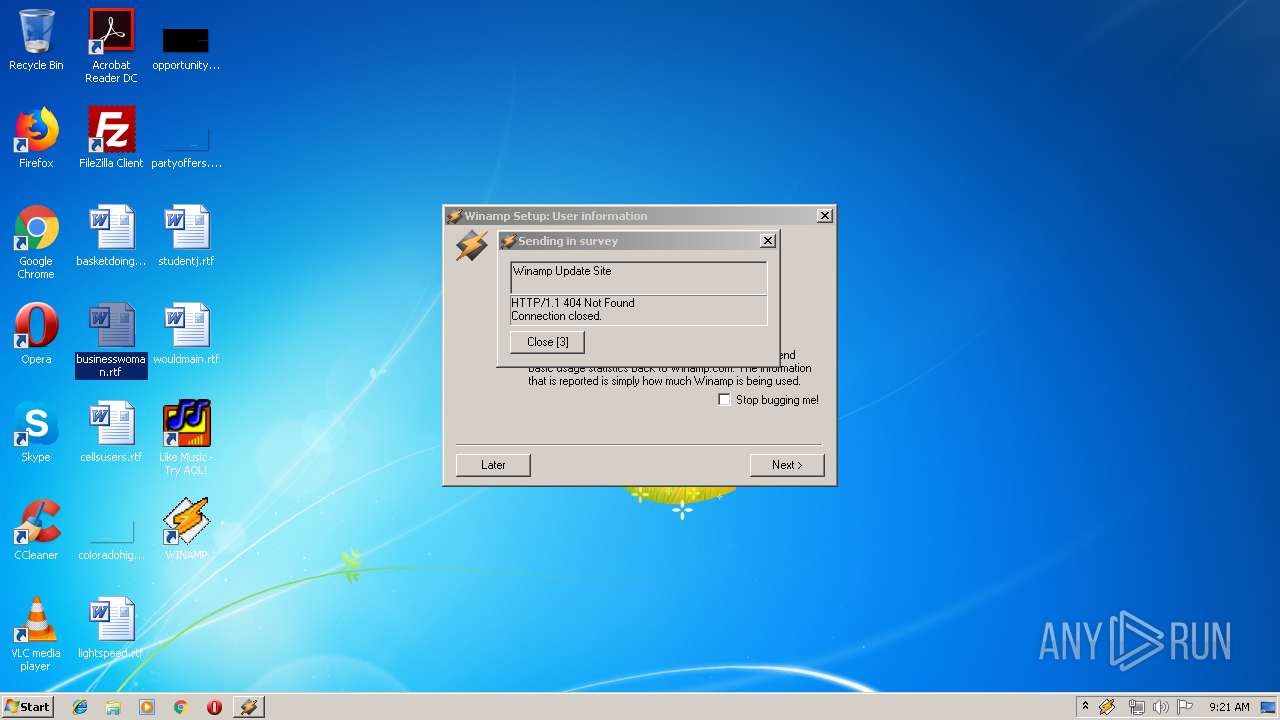
— | — | GET | 404 | 5.39.58.65:80 | http://www.winamp.com/update/do_im.jhtml?ID=C3258228D33D3944A1B76CAC5D4723BB&ZIP=&EMAIL=&ML=n&NETCREATIONS=n&OBJS=wa2.95&V=2.95 | FR | html | 216 b | malicious |
— | — | GET | 404 | 5.39.58.65:80 | http://www.winamp.com/update/updatelinks.jhtml?i=y&v=2.95&r=n | FR | html | 222 b | malicious |
— | — | GET | 404 | 5.39.58.65:80 | http://www.winamp.com/browser/ | FR | html | 179 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 5.39.58.65:80 | www.winamp.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.winamp.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |