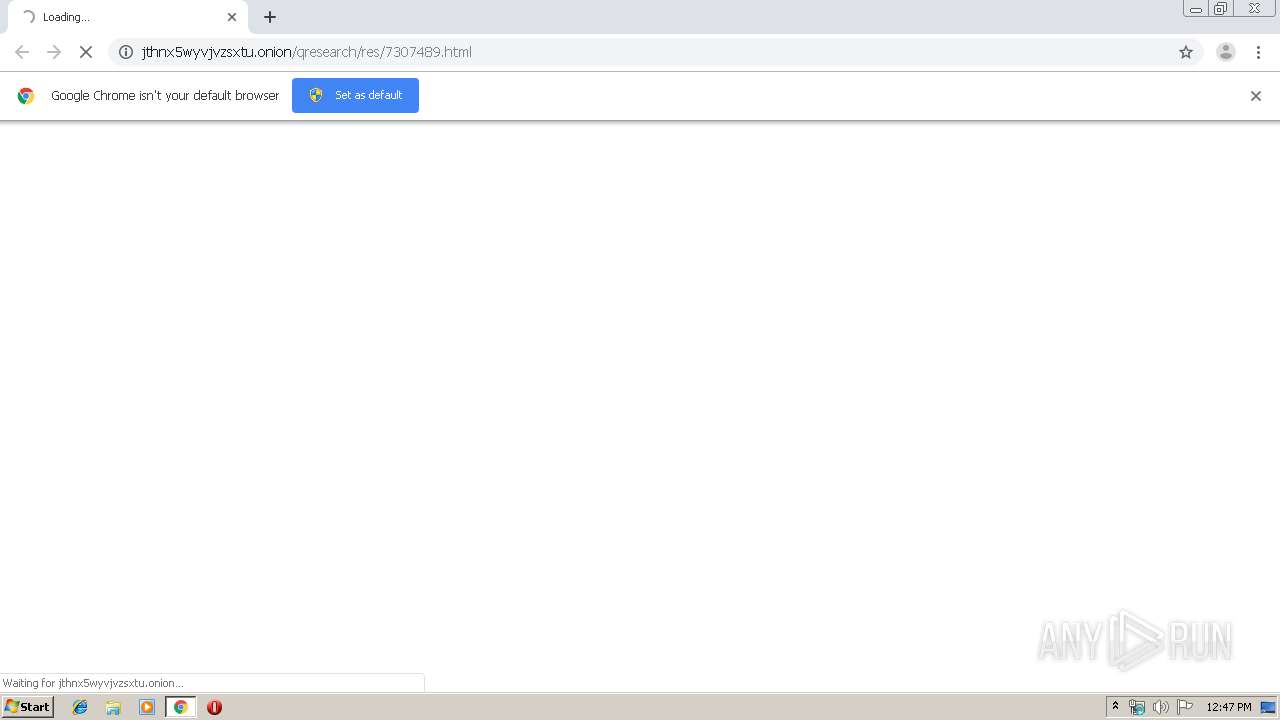
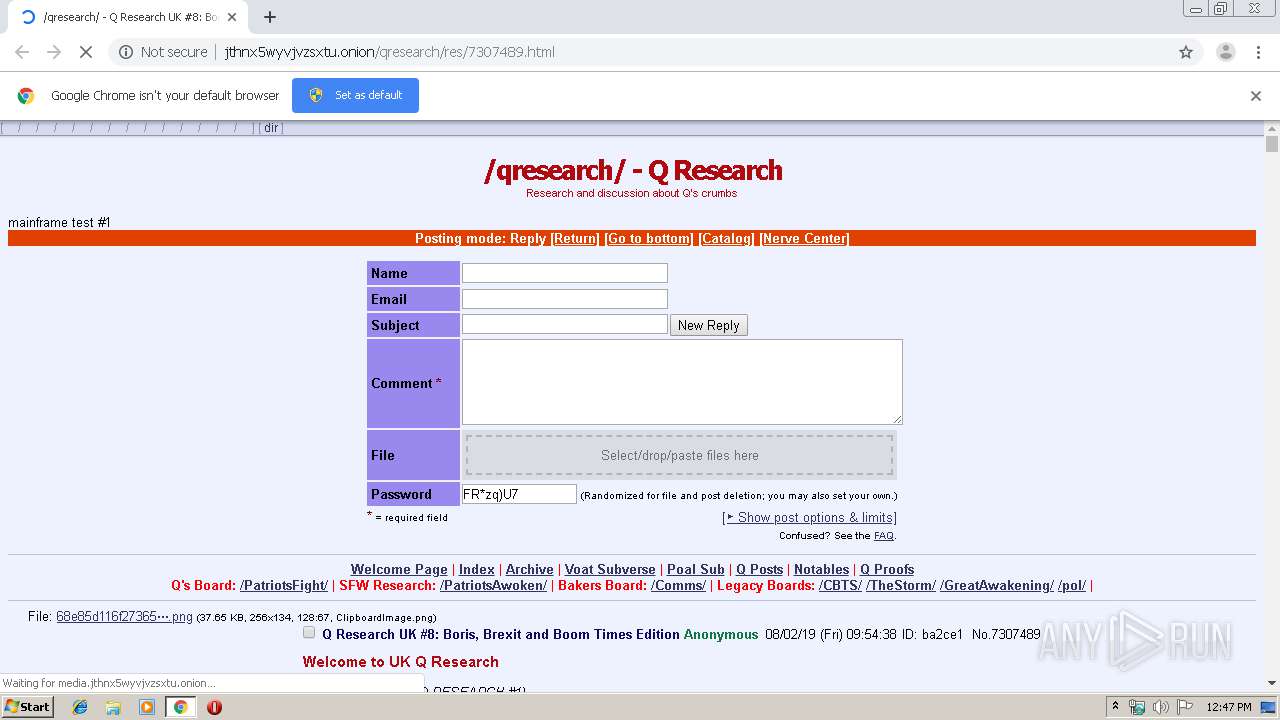
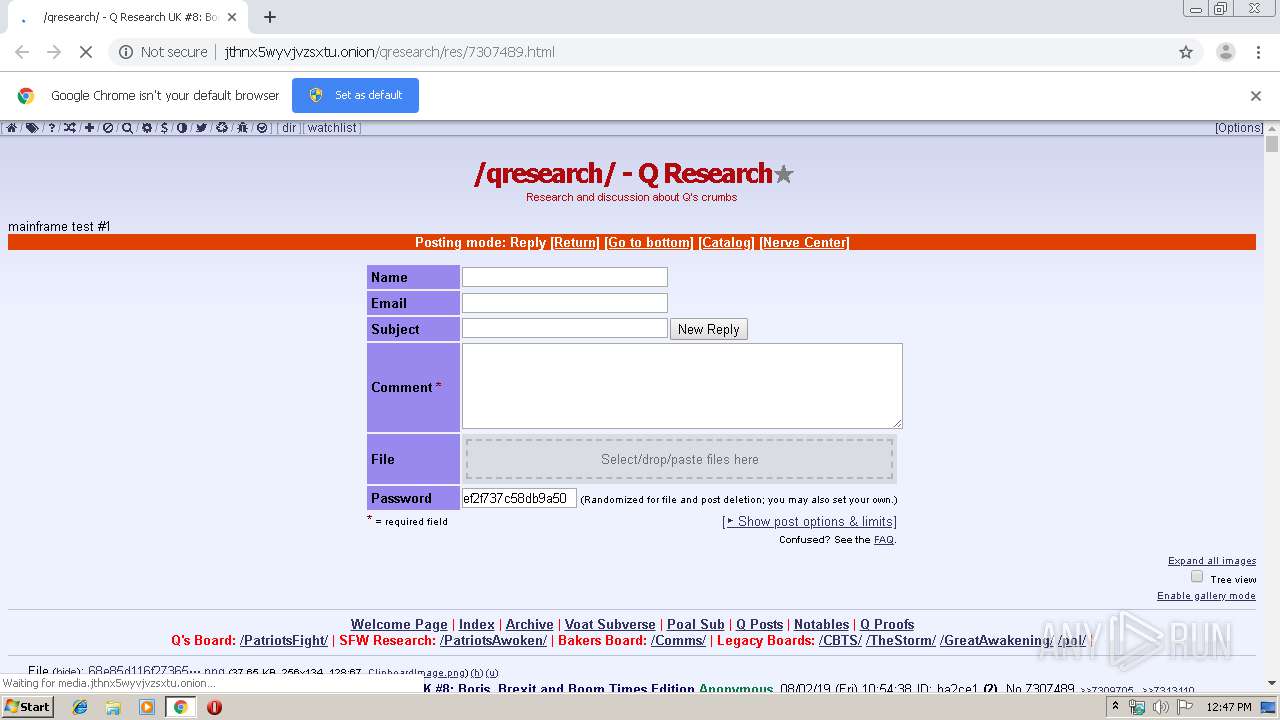
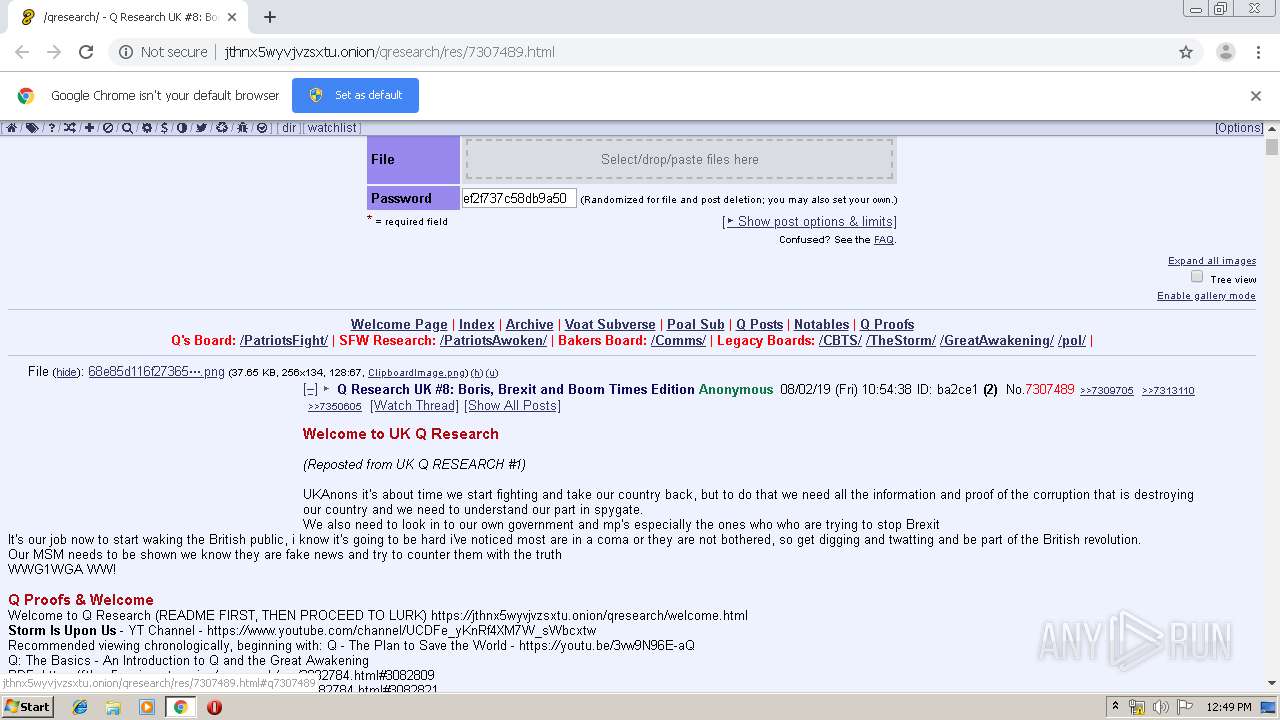
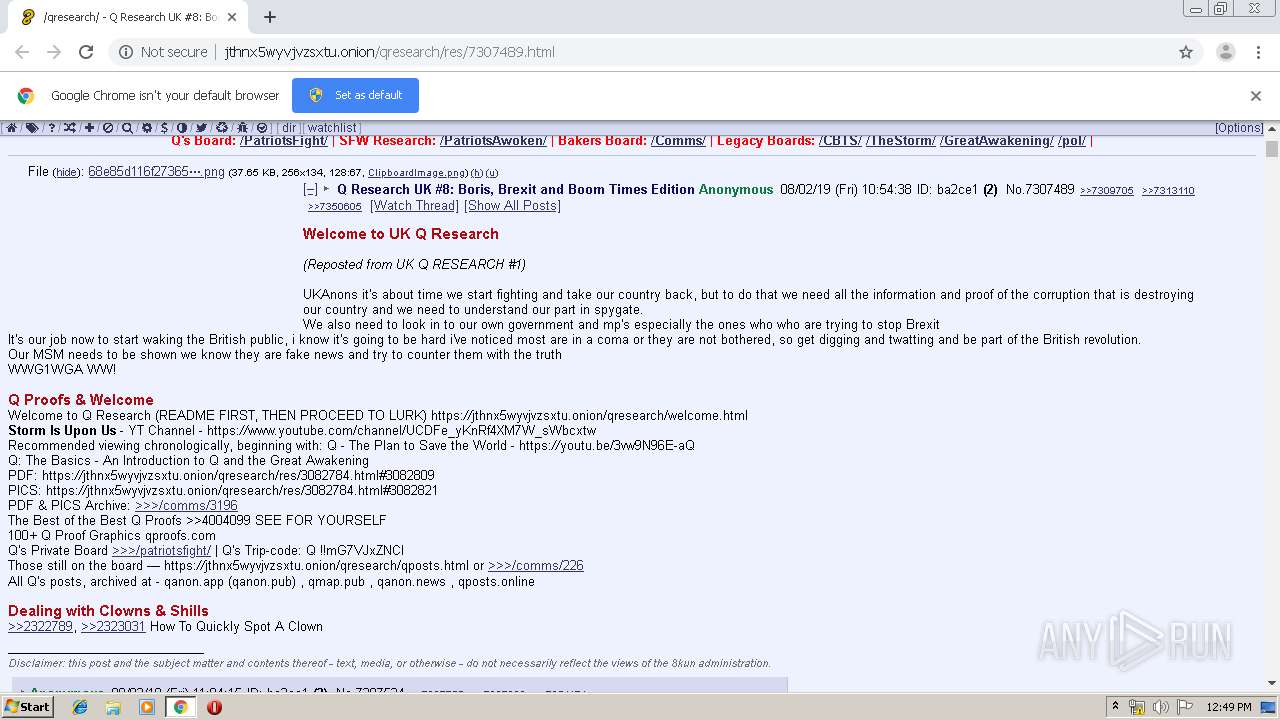
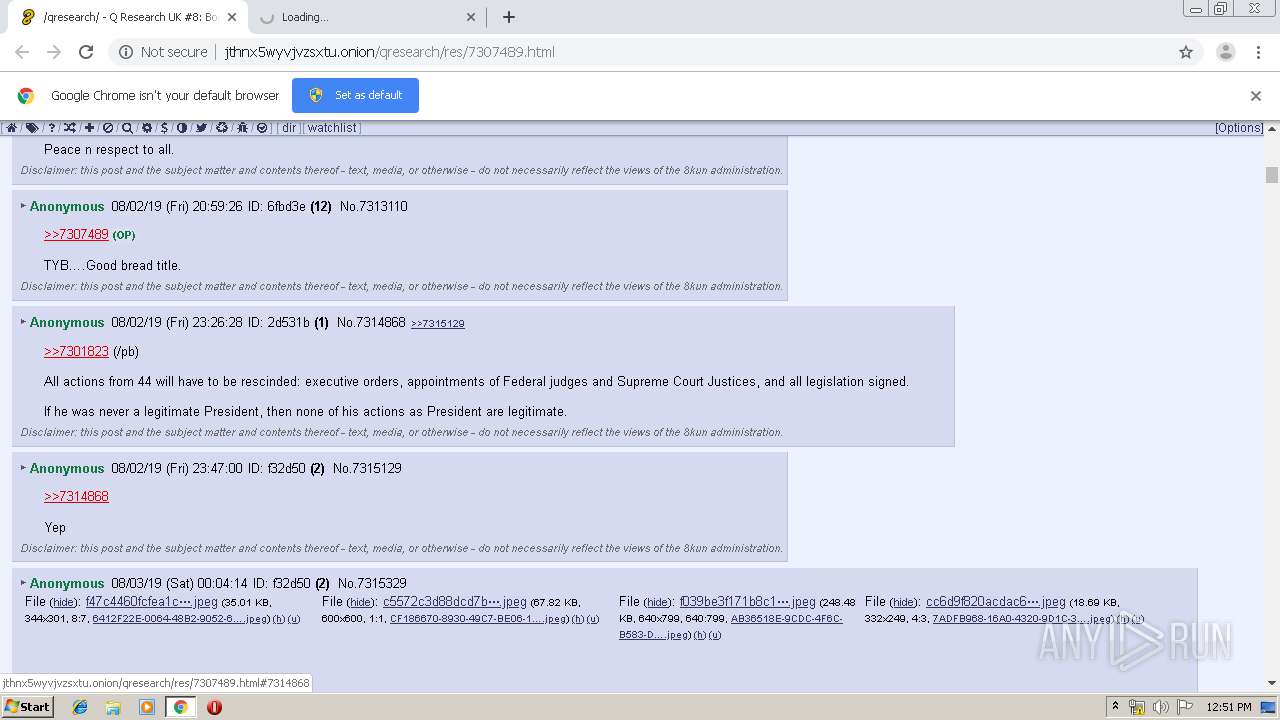
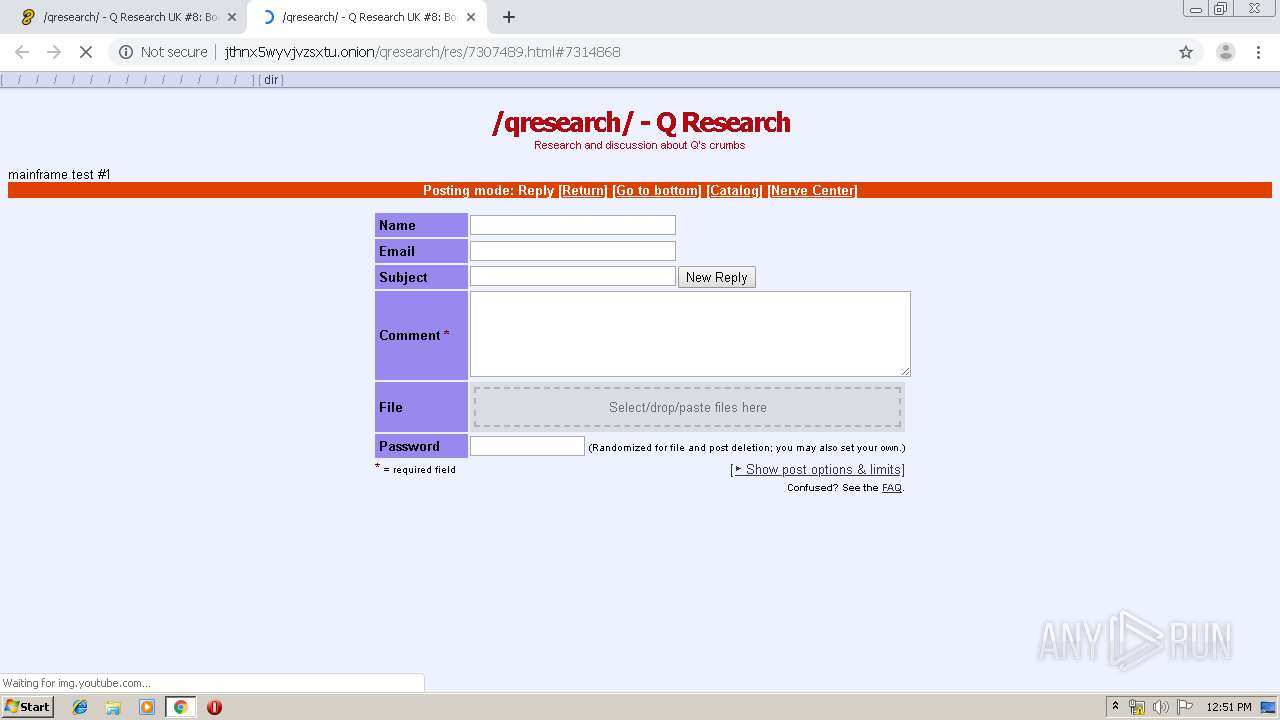
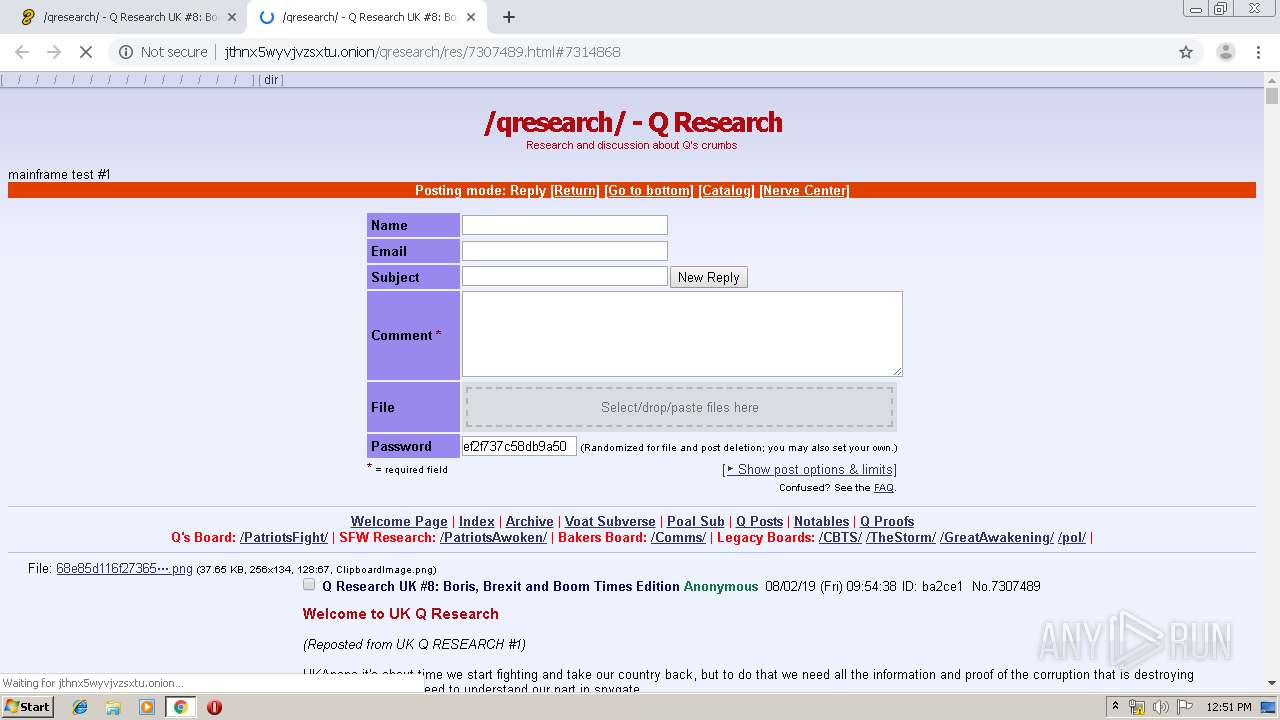
| URL: | http://jthnx5wyvjvzsxtu.onion/qresearch/res/7307489.html |
| Full analysis: | https://app.any.run/tasks/5b96ced8-6346-46ee-82a9-94bda12619b5 |
| Verdict: | No threats detected |
| Analysis date: | November 06, 2019, 12:46:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D19444FC5D4260D6976A1EFFFB44E1A |
| SHA1: | E76C5B8220821F7C70643E6DB127E14D0DCCD9AE |
| SHA256: | EF0306EA648E738A05ED5AD68B56696CF4BB35CF51AF2F9A0431C26D09477EBA |
| SSDEEP: | 3:N1KUr+vTriReKLMfULzKLIJ:CUr+SsZfULGIJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2060)
INFO
Application launched itself
- chrome.exe (PID: 2060)
Reads the hosts file
- chrome.exe (PID: 2060)
- chrome.exe (PID: 1944)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13035242394811726113 --mojo-platform-channel-handle=628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8475997794276268726 --mojo-platform-channel-handle=1128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8765268016570754788 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4690056294334104825 --mojo-platform-channel-handle=3472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13123306437249348453 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16341631237380202365 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://jthnx5wyvjvzsxtu.onion/qresearch/res/7307489.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5286559510603736794 --mojo-platform-channel-handle=3352 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17260838000307010328 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1332 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4326827102500146445 --mojo-platform-channel-handle=2532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
635
Read events
519
Write events
110
Delete events
6
Modification events
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2060-13217518030571875 |
Value: 259 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2060) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
33
Text files
240
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a2b3.TMP | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a2b3.TMP | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a2b3.TMP | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4869ae8c-87df-47d5-8218-f6450a5fba16.tmp | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
166
TCP/UDP connections
38
DNS requests
43
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
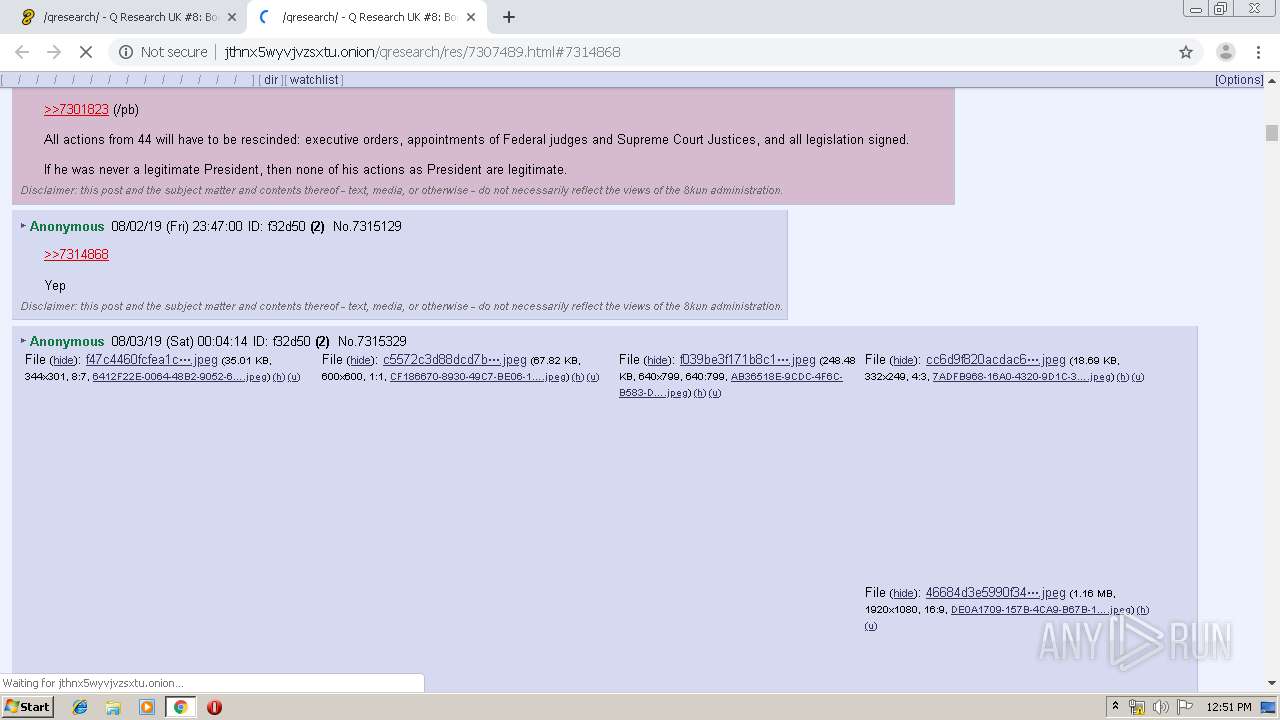
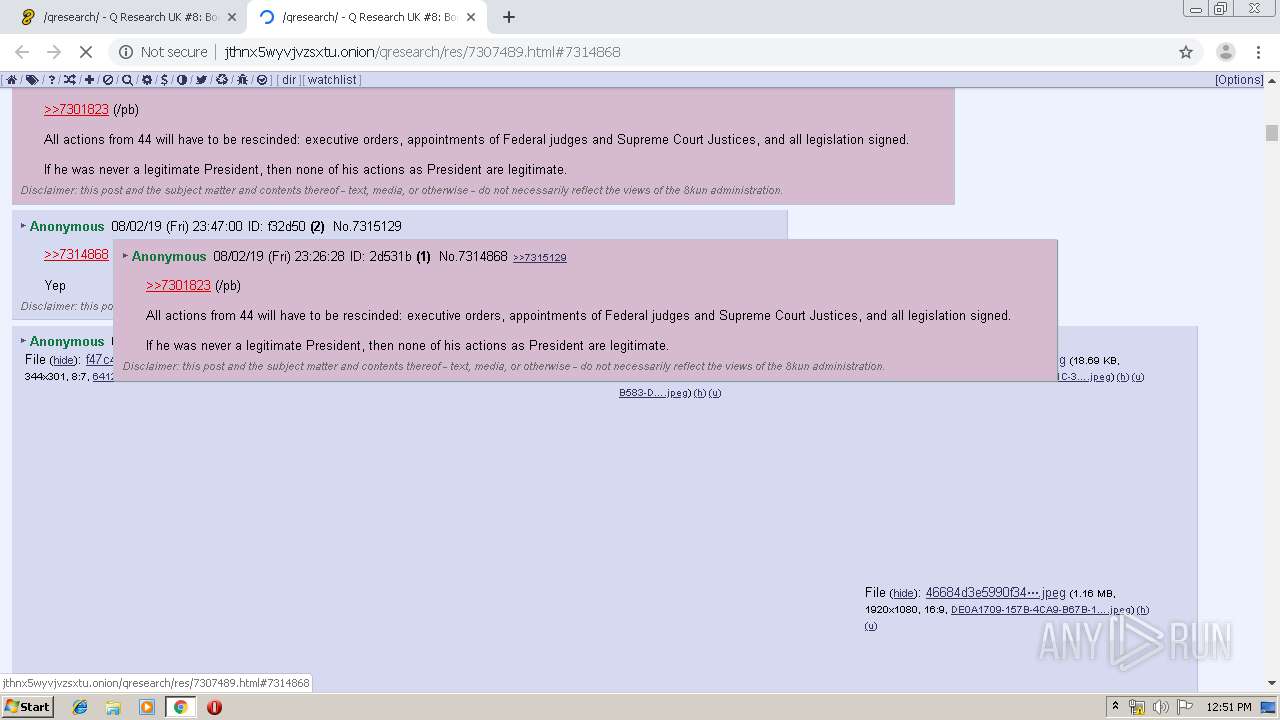
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/68e85d116f27365cc47a4e47ada04037c46bdb7c7f70f22c0ece3b2451b80253.png | unknown | html | 174 b | unknown |
1944 | chrome.exe | GET | 200 | 10.228.40.19:80 | http://jthnx5wyvjvzsxtu.onion/stylesheets/board/qresearch.css | unknown | text | 562 b | malicious |
1944 | chrome.exe | GET | — | 10.228.40.19:80 | http://jthnx5wyvjvzsxtu.onion/static/flags/flags.css | unknown | — | — | malicious |
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/ec0342cbd80d886b8b95df517a3dfa483ef798214b792987a2bcccf39f29c5ba.png | unknown | html | 186 b | unknown |
1944 | chrome.exe | GET | 200 | 10.228.40.19:80 | http://jthnx5wyvjvzsxtu.onion/stylesheets/font-awesome/css/font-awesome.min.css | unknown | text | 5.22 Kb | malicious |
1944 | chrome.exe | GET | 200 | 10.228.40.19:80 | http://jthnx5wyvjvzsxtu.onion/main.js | unknown | text | 190 Kb | malicious |
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/13be4ad8c3a8c5dac3a00e79562175c375a8c06814981588f9beca1611fe3aa6.jpeg | unknown | html | 174 b | unknown |
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/1085217cb71ac0e84f974006affc8fd1878d8f1c4a85945275d27a70ff0fefd3.png | unknown | html | 174 b | unknown |
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/f47c4460fcfea1c97f700208ad574a083c8dd08ad5d5cf876453174ad77e26d2.jpeg | unknown | html | 186 b | unknown |
1944 | chrome.exe | GET | 404 | 10.215.155.124:80 | http://media.jthnx5wyvjvzsxtu.onion/file_store/thumb/c5572c3d88dcd7b75a35e3ef873da4545ad52e340a4bed9edbbdae75d2736796.jpeg | unknown | html | 174 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | chrome.exe | 10.228.40.19:80 | jthnx5wyvjvzsxtu.onion | — | — | unknown |
1944 | chrome.exe | 172.217.17.132:443 | www.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 10.215.155.124:80 | media.jthnx5wyvjvzsxtu.onion | — | — | unknown |
1944 | chrome.exe | 172.217.17.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 216.58.211.110:80 | img.youtube.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.168.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.168.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 74.125.100.104:80 | r3---sn-5hnekn7z.gvt1.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 216.58.211.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.168.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jthnx5wyvjvzsxtu.onion |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
media.jthnx5wyvjvzsxtu.onion |
| unknown |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
img.youtube.com |
| whitelisted |
twitter.com |
| whitelisted |
sys.jthnx5wyvjvzsxtu.onion |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |