| File name: | update.exe |
| Full analysis: | https://app.any.run/tasks/f36dade3-f3f7-49ca-b5a6-2a8b7706b231 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 05:01:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B8E19C39E310B29F1DC332969005762B |
| SHA1: | 967A36D614D8F1C5A96F5387EE3979C96041E159 |
| SHA256: | EF00C049EE2CBF8AB4709D19311A421FB1FFBB5C04F6293E7855C5F07116F589 |
| SSDEEP: | 24576:9NlQMmJw0unPn7Cx3NQ/ozRg9jwW3vkZLgLsab9dMzvuCx/YHM9EPv9lewrSoGLs:9NlQlJCnPn76dQQzRgu+KLgLUFOBPvTJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Apr-2019 15:13:18 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 快乐的小伙伴 |
| ProductName: | 快乐的小伙伴 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | 快乐的小伙伴 |
| LegalCopyright: | 快乐的小伙伴 |
| Comments: | 快乐的小伙伴 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0000 |
| Pages in file: | 0x0000 |
| Relocations: | 0x0000 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 09-Apr-2019 15:13:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Esp0 | 0x00001000 | 0x00214000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Esp1 | 0x00215000 | 0x00167000 | 0x00166200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99987 |
.rsrc | 0x0037C000 | 0x00009000 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.69824 |
.Esp | 0x00385000 | 0x000001FF | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.89315 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 7.96579 | 30742 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.8235 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 7.27086 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
6 | 7.37615 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
1032 | 4.32193 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_CURSOR |
1033 | 4.22193 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_CURSOR |
1037 | 7.15966 | 234 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
1084 | 7.93408 | 2222 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVFW32.dll |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Users\admin\AppData\Local\Temp\update.exe | explorer.exe | ||||||||||||
User: admin Company: 快乐的小伙伴 Integrity Level: HIGH Description: 快乐的小伙伴 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
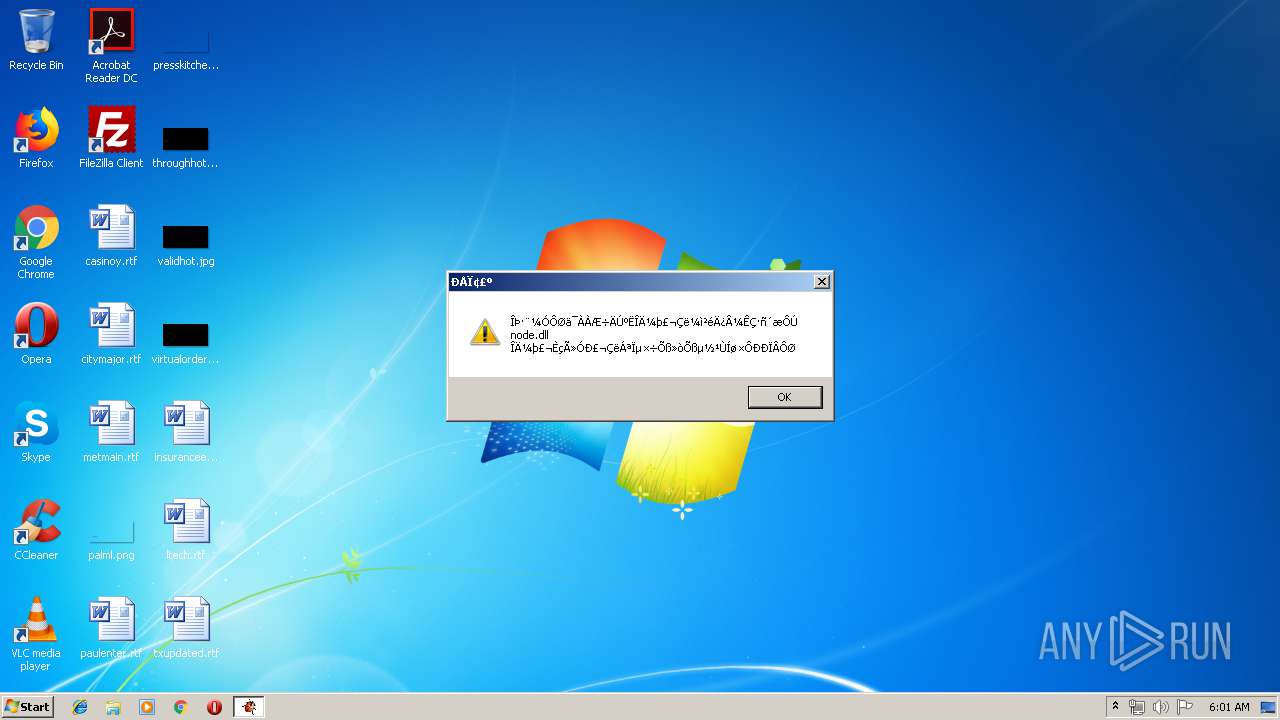
| 3000 | "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Users\admin\AppData\Local\Temp\update.exe | — | explorer.exe | |||||||||||
User: admin Company: 快乐的小伙伴 Integrity Level: MEDIUM Description: 快乐的小伙伴 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
51
Read events
33
Write events
18
Delete events
0
Modification events
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (352) update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\update_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
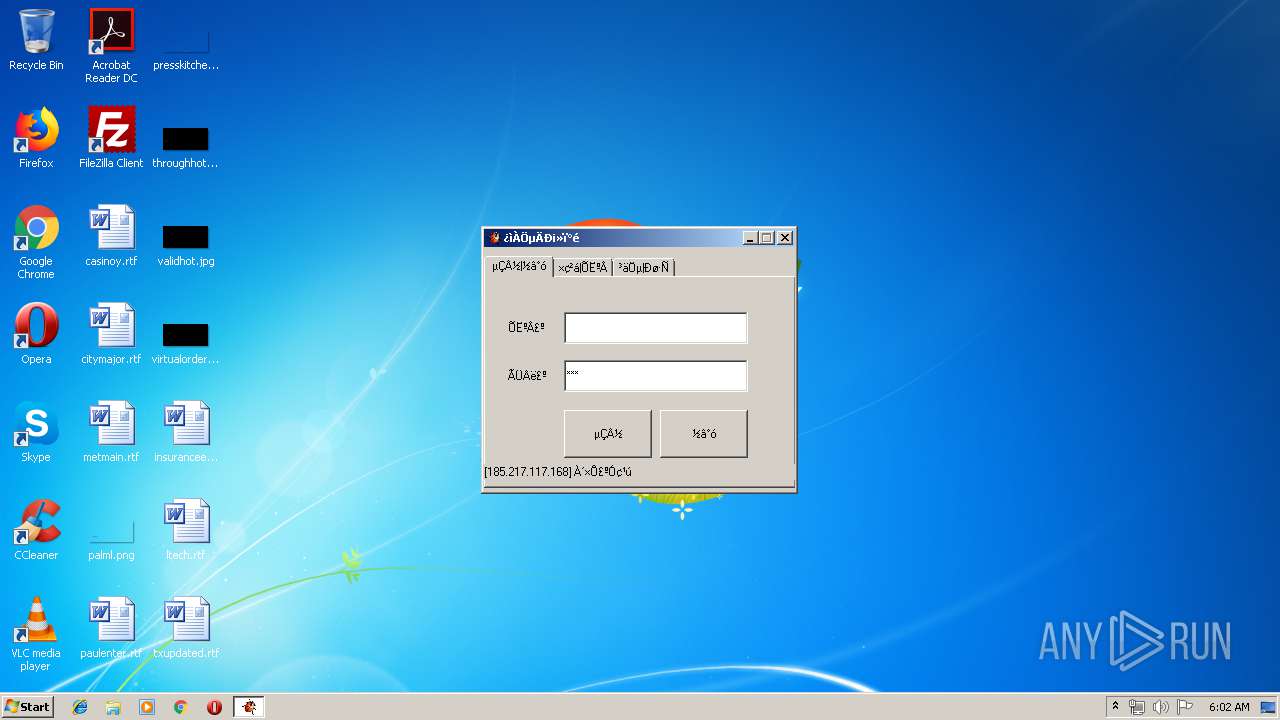
352 | update.exe | GET | — | 203.205.142.186:80 | http://xui.ptlogin2.qq.com/cgi-bin/xlogin?proxy_url=http%3A//qzs.qq.com/qzone/v6/portal/proxy.html&daid=5&&hide_title_bar=1&low_login=0&qlogin_auto_login=1&no_verifyimg=1&link_target=blank&appid=549000912&style=22&target=self&s_url=http%3A%2F%2Fqzs.qq.com%2Fqzone%2Fv5%2Floginsucc.html%3Fpara%3Dizone&pt_qr_app=%E6%89%8B%E6%9C%BAQQ%E7%A9%BA%E9%97%B4&pt_qr_link=http%3A//z.qzone.com/download.html&self_regurl=http%3A//qzs.qq.com/qzone/v6/reg/index.html&pt_qr_help_link=http%3A//z.qzone.com/download.html | CN | — | — | unknown |
352 | update.exe | GET | 200 | 117.25.157.119:80 | http://2019.ip138.com/ic.asp | CN | html | 218 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | update.exe | 203.205.142.186:80 | xui.ptlogin2.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
352 | update.exe | 117.25.157.119:80 | 2019.ip138.com | Xiamen | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xui.ptlogin2.qq.com |
| unknown |
localhost.ptlogin2.qq.com |
| unknown |
2019.ip138.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | update.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
352 | update.exe | Misc activity | SUSPICIOUS [PTsecurity] IP lookup service ip138.com |
1 ETPRO signatures available at the full report