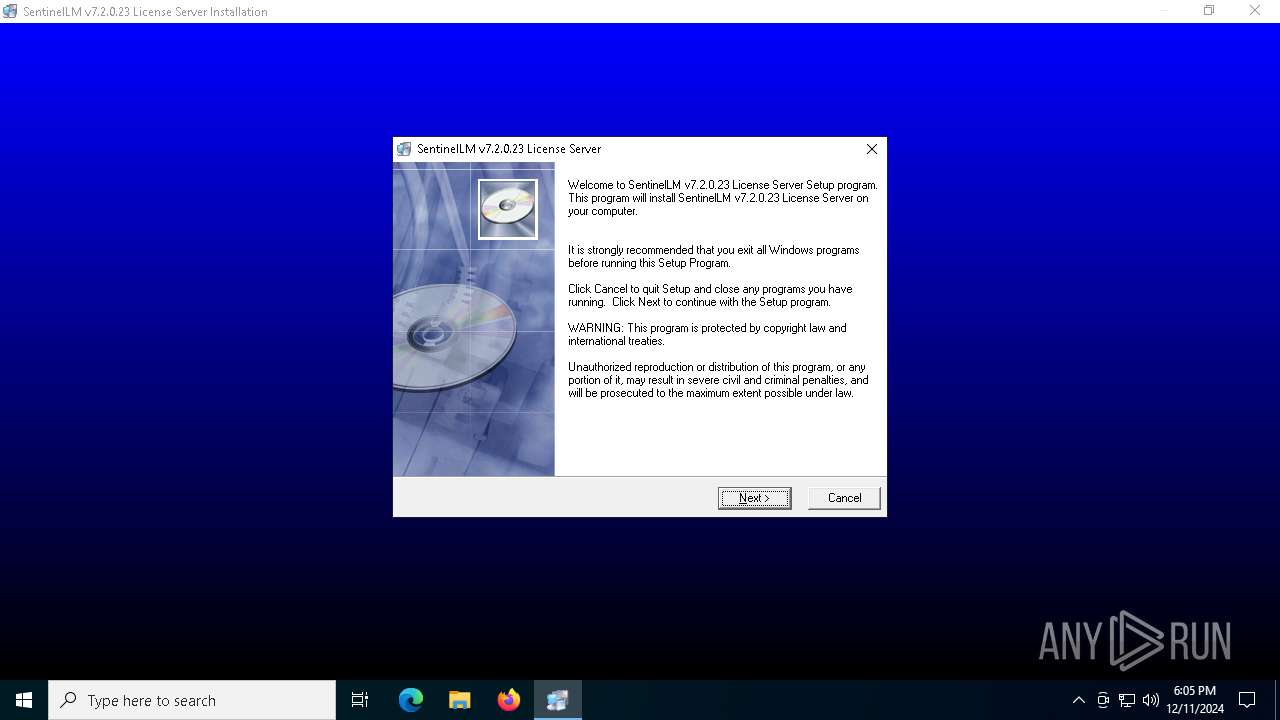
| File name: | License_Server.EXE |
| Full analysis: | https://app.any.run/tasks/adb8ed3b-47d9-4df7-a865-4a6e81700eb0 |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 18:05:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | BB78D79E712F61409BDF56D2BBD1E8C7 |
| SHA1: | 4550B3C1F866D246DD04C6A728F0CE19C41D702A |
| SHA256: | EEF771B6CD728E4A46FC167CB3F3D44734427978714E7EE23785A4AB89D0FC15 |
| SSDEEP: | 98304:OcL4XWFAbwULTW0/qB0KXB2cM9Pl3CbBMA2CfB82teIIyoNJctJ+fSNTI9vEyhUZ:JVnQGwdFfQfE01 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates a software uninstall entry
- License_Server.EXE.exe (PID: 6360)
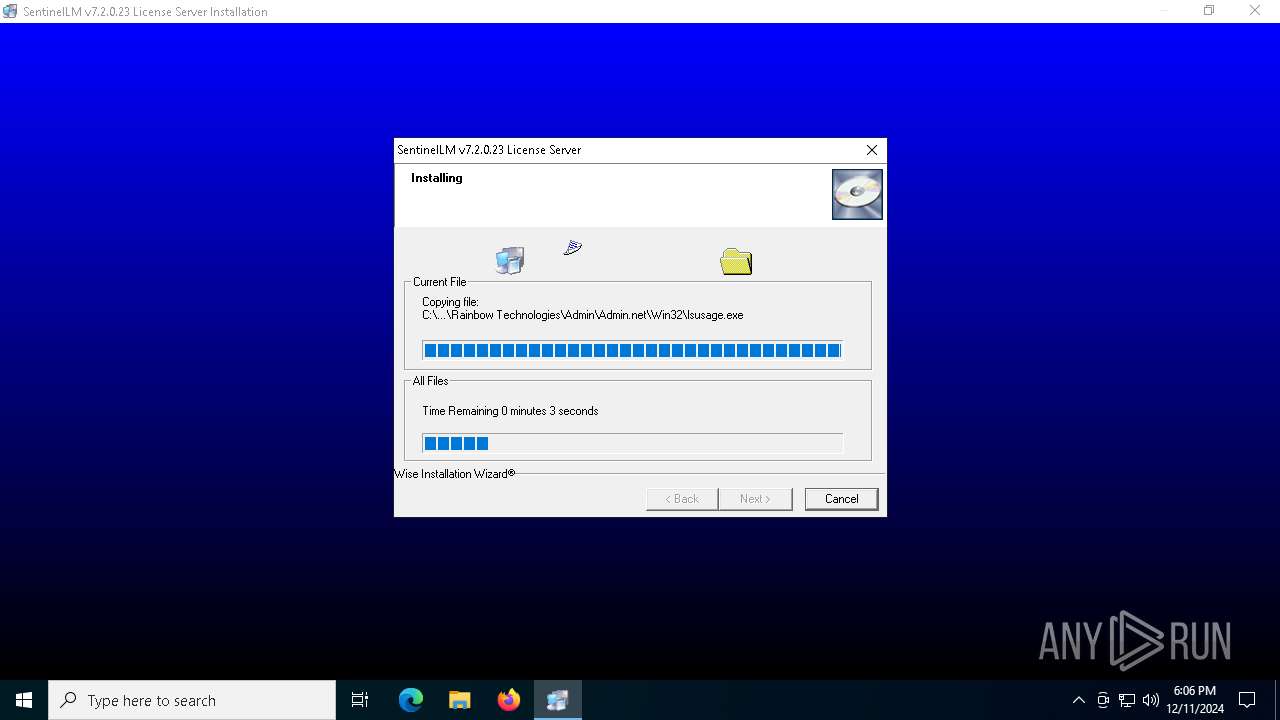
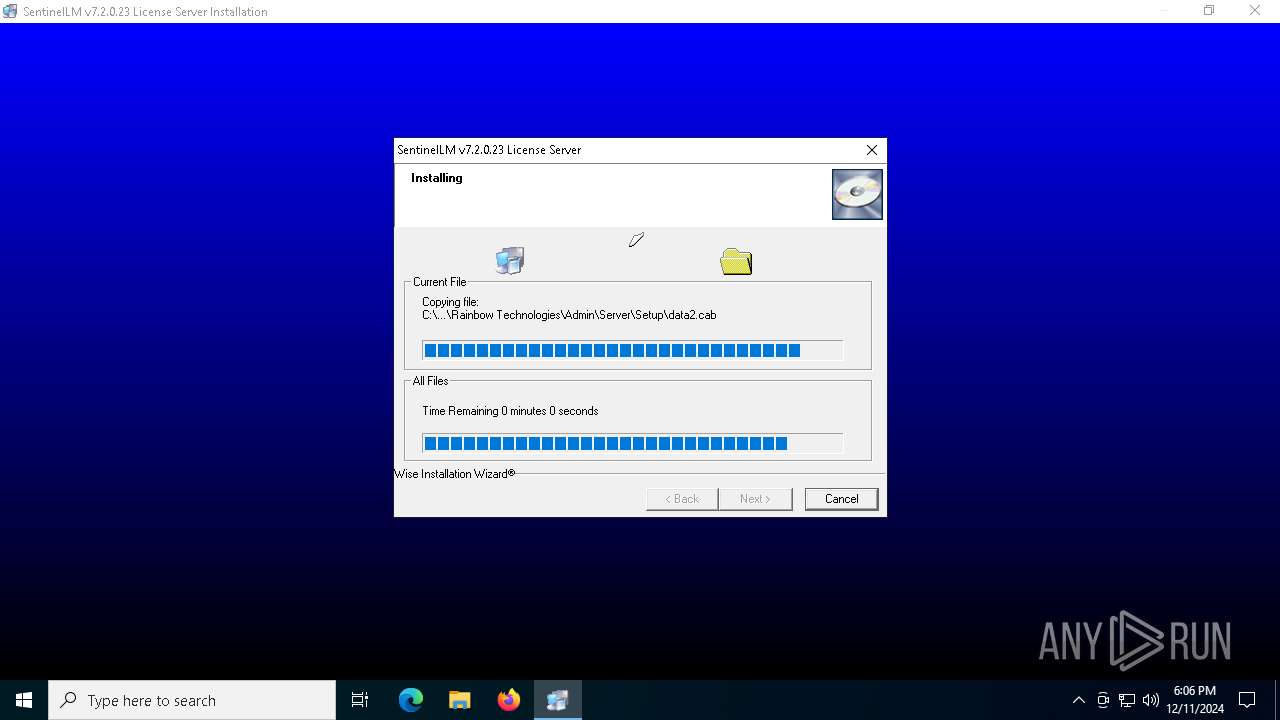
Executable content was dropped or overwritten
- License_Server.EXE.exe (PID: 6360)
- Setup.exe (PID: 2612)
- IKernel.exe (PID: 3436)
Searches for installed software
- License_Server.EXE.exe (PID: 6360)
Creates/Modifies COM task schedule object
- IKernel.exe (PID: 3436)
Application launched itself
- IKernel.exe (PID: 3436)
Reads security settings of Internet Explorer
- IKernel.exe (PID: 5544)
INFO
The sample compiled with english language support
- License_Server.EXE.exe (PID: 6360)
- IKernel.exe (PID: 3436)
- Setup.exe (PID: 2612)
Checks supported languages
- License_Server.EXE.exe (PID: 6360)
- Setup.exe (PID: 2612)
- IKernel.exe (PID: 3436)
- IKernel.exe (PID: 5544)
Reads the computer name
- License_Server.EXE.exe (PID: 6360)
- Setup.exe (PID: 2612)
- IKernel.exe (PID: 3436)
Create files in a temporary directory
- License_Server.EXE.exe (PID: 6360)
- IKernel.exe (PID: 3436)
Creates files in the program directory
- License_Server.EXE.exe (PID: 6360)
- IKernel.exe (PID: 3436)
Checks proxy server information
- IKernel.exe (PID: 5460)
- IKernel.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:09:10 15:38:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 8192 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29aa |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
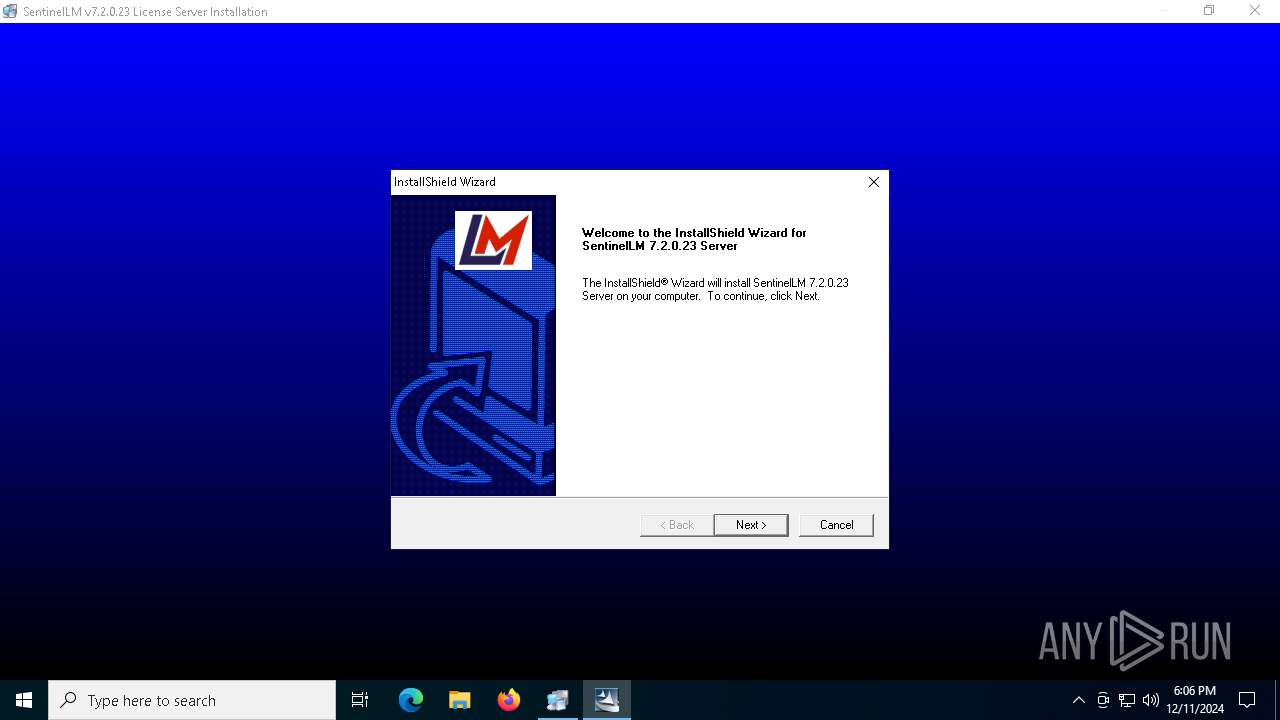
| CompanyName: | SafeNet Inc. |
| FileDescription: | SentinelLM v7.2.0.23 License Server |
| FileVersion: | 1 |
| LegalCopyright: | (C) SafeNet Inc. |
Total processes
134
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
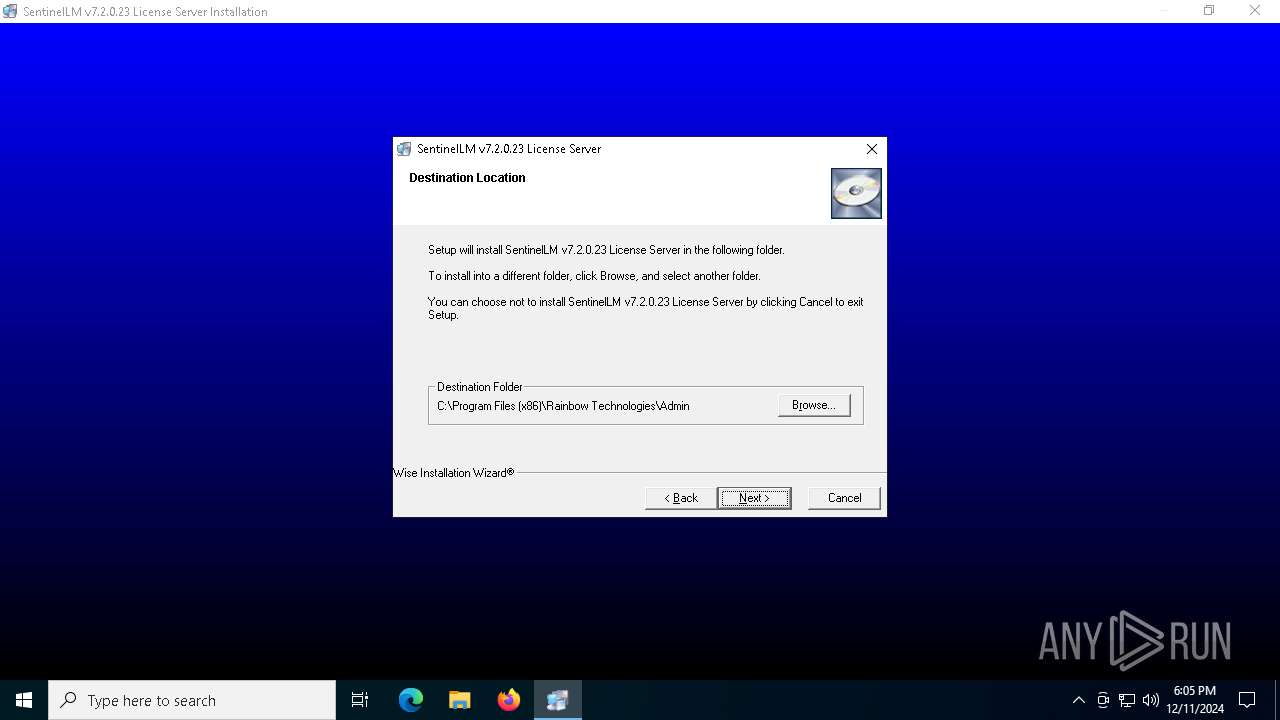
| 2612 | C:\PROGRA~2\RAINBO~1\Admin\Server\Setup\Setup.exe /REGSERVER | C:\Program Files (x86)\Rainbow Technologies\Admin\Server\Setup\Setup.exe | License_Server.EXE.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Launcher Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 3436 | C:\PROGRA~2\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe -Embedding | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | svchost.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 5460 | "C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe" -RegServer | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | — | Setup.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 5544 | "C:\Program Files (x86)\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe" /REGSERVER | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | — | IKernel.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 6192 | "C:\Users\admin\AppData\Local\Temp\License_Server.EXE.exe" | C:\Users\admin\AppData\Local\Temp\License_Server.EXE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6360 | "C:\Users\admin\AppData\Local\Temp\License_Server.EXE.exe" | C:\Users\admin\AppData\Local\Temp\License_Server.EXE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
1 375
Read events
1 214
Write events
161
Delete events
0
Modification events
| (PID) Process: | (6360) License_Server.EXE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SentinelLM v7.2.0.23 License Server |
| Operation: | write | Name: | DisplayName |
Value: SentinelLM v7.2.0.23 License Server | |||
| (PID) Process: | (6360) License_Server.EXE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SentinelLM v7.2.0.23 License Server |
| Operation: | write | Name: | UninstallString |
Value: C:\PROGRA~2\RAINBO~1\Admin\UNWISE.EXE C:\PROGRA~2\RAINBO~1\Admin\Server\Setup\INSTALL.LOG | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{251753FA-FB3B-11D2-8842-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{251753FA-FB3B-11D2-8842-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{7D795704-435D-11D3-88FF-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{7D795704-435D-11D3-88FF-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{8415DDF9-1C1D-11D3-889D-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{8415DDF9-1C1D-11D3-889D-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{8415DE38-1C1D-11D3-889D-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5460) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{8415DE38-1C1D-11D3-889D-00C04F72F303}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
121
Suspicious files
17
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\~GLH0001.TMP | text | |
MD5:0E6AE5811582D5554D28795B4760BF48 | SHA256:7E5862D66AC402D2BF1F0A93CC794989471729EDD22F62845F6CAAED8AC5FB1D | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\~GLH0000.TMP | executable | |
MD5:1DE69F64E93FD216267DF5EF8B5F1067 | SHA256:0C4FA4E51F3F902E93BAA5033B1667BD9D270C16EC48C189882DE36ABB7B394F | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\echoid.dat | text | |
MD5:0E6AE5811582D5554D28795B4760BF48 | SHA256:7E5862D66AC402D2BF1F0A93CC794989471729EDD22F62845F6CAAED8AC5FB1D | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\echoid.exe | executable | |
MD5:BCBFA9F6161A3BF82C8E941BC563001B | SHA256:D0D9FB9D4E1559C5A84E4D9724FB4C9480A6955ECE74D215353E6948F4F00D7F | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\temp.000 | executable | |
MD5:BCBFA9F6161A3BF82C8E941BC563001B | SHA256:D0D9FB9D4E1559C5A84E4D9724FB4C9480A6955ECE74D215353E6948F4F00D7F | |||
| 6360 | License_Server.EXE.exe | C:\Users\admin\AppData\Local\Temp\GLC5806.tmp | executable | |
MD5:5758CB6E80BEE4CDA2944BAA83C9701C | SHA256:BB302CB17EC1ABF9E78B97CF88CDA4651AB754B073897966B3550BDA6E044964 | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\~GLH0003.TMP | executable | |
MD5:BCBFA9F6161A3BF82C8E941BC563001B | SHA256:D0D9FB9D4E1559C5A84E4D9724FB4C9480A6955ECE74D215353E6948F4F00D7F | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\~GLH0008.TMP | executable | |
MD5:34913D0DB342527D1077BF8EA8BC7C6A | SHA256:4A15308F77CE4D54BE9B2F0C218A8C0A49F31503D135D9E73183E716BAEEDFC9 | |||
| 6360 | License_Server.EXE.exe | C:\Users\admin\AppData\Local\Temp\GLJ5827.tmp | executable | |
MD5:2A9204BB75DC2B182EE42C1A935C0674 | SHA256:2CD69888F5613092C8D6CC4366F63868F863CF98A7399B2EC0CA5CEB9E4A725C | |||
| 6360 | License_Server.EXE.exe | C:\Program Files (x86)\Rainbow Technologies\Admin\Admin.net\Win32\ipxecho.exe | executable | |
MD5:50A6060086320ABD836F601ED7FCAC13 | SHA256:ED27FB964208D70DD8AC4E641349DAC8ECD878EDC73C32A68F9001D315417BFB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3612 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5448 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 23.212.110.200:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |