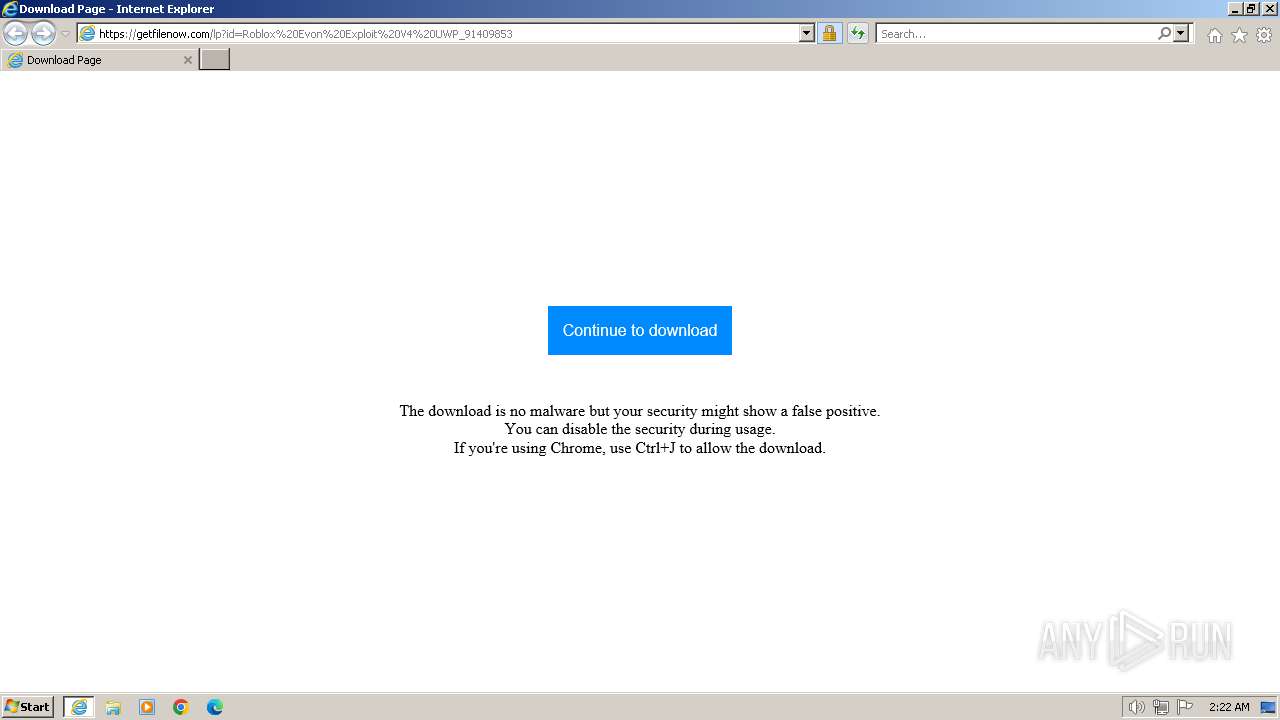
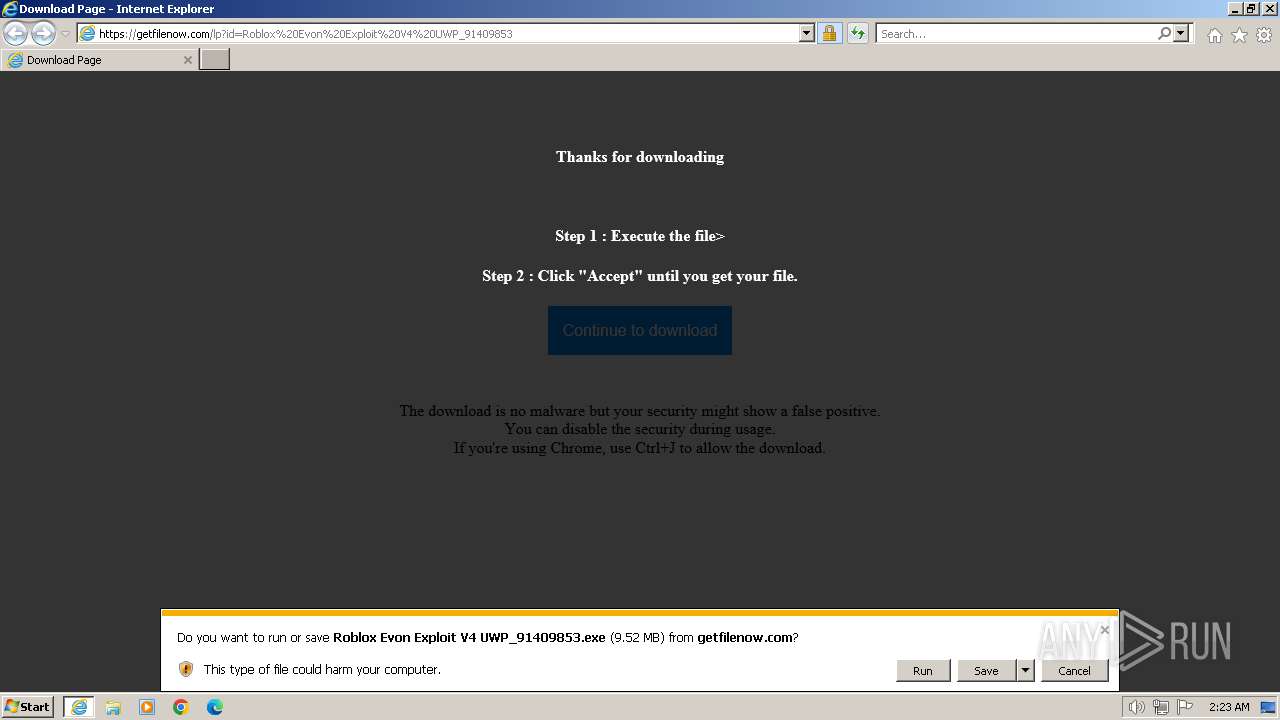
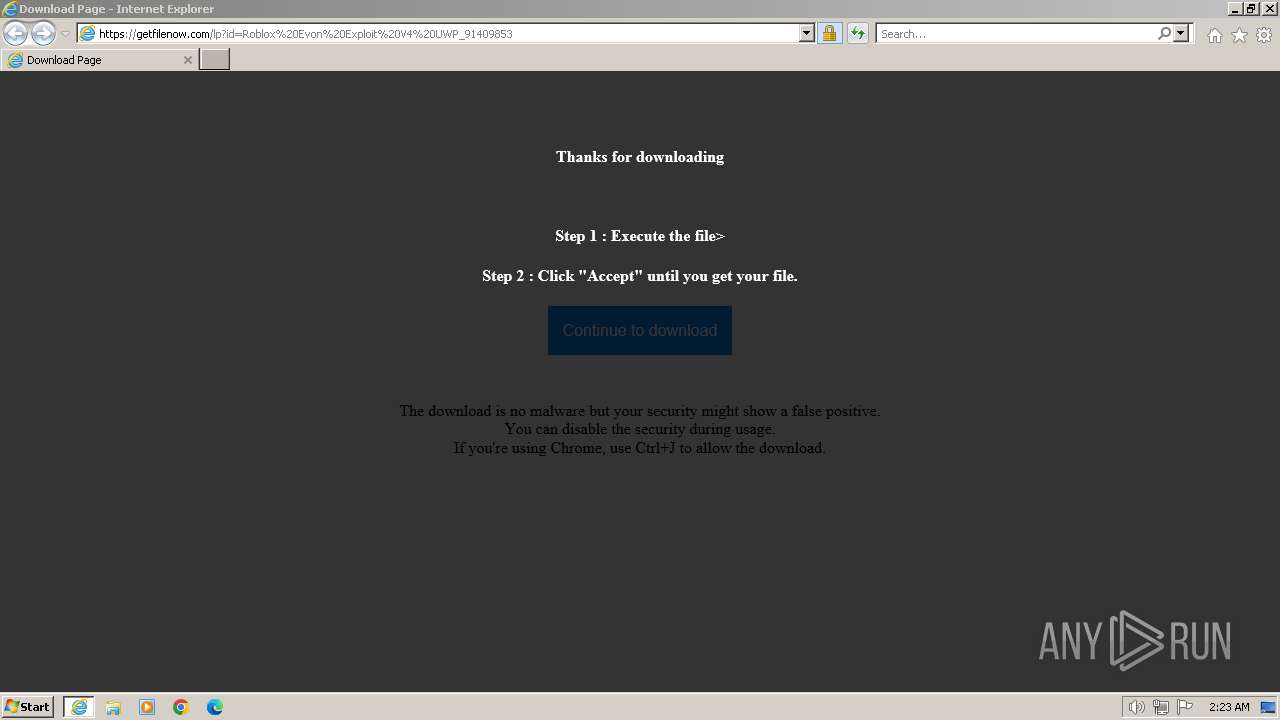
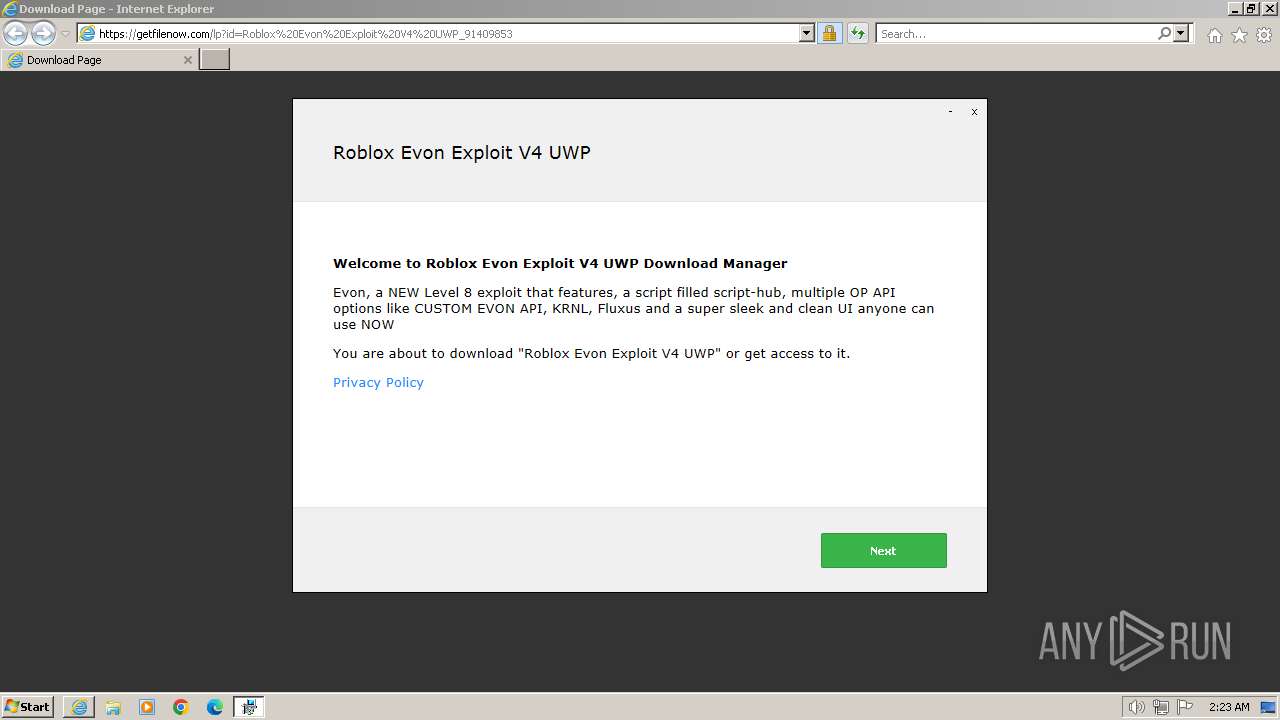
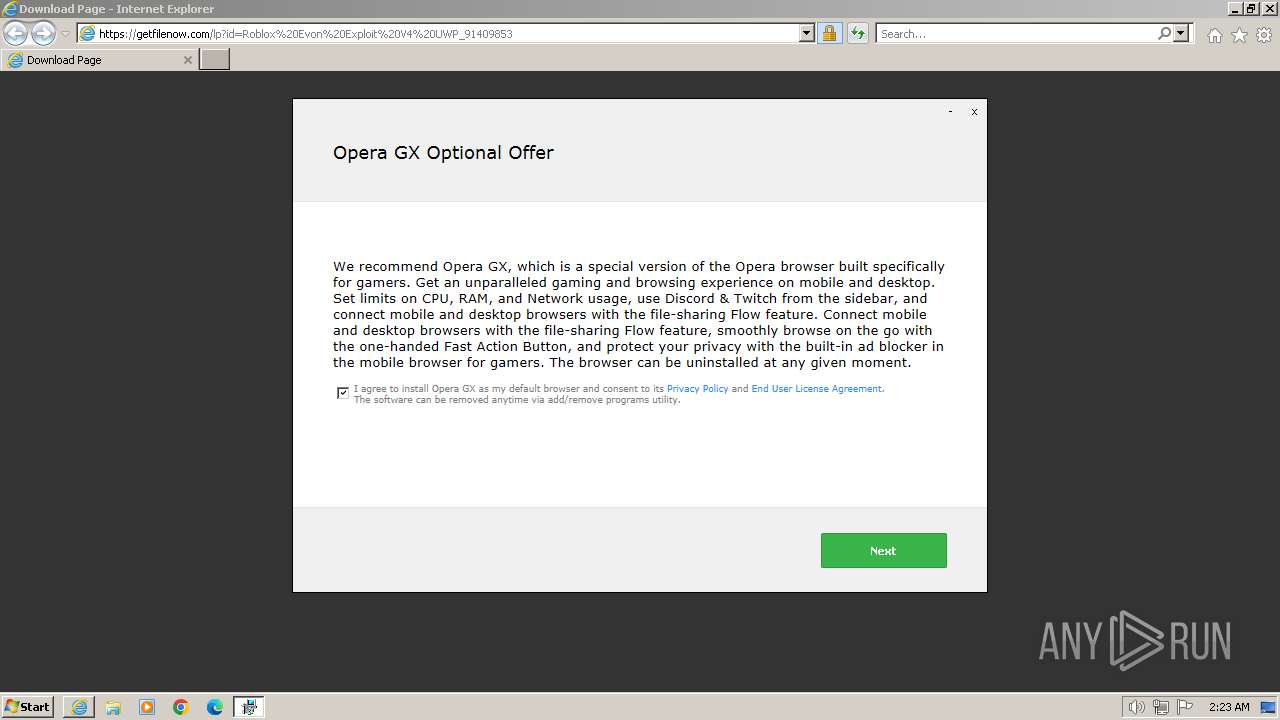
| URL: | https://getfilenow.com/lp?id=Roblox%20Evon%20Exploit%20V4%20UWP_91409853 |
| Full analysis: | https://app.any.run/tasks/3cd1e588-1ae3-4924-9a66-f54a72bf8f17 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2024, 02:22:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1092F628E26803E8F78E06AA90344A1C |
| SHA1: | 15357010C38280A65838E198BCBE6152D8F5ED32 |
| SHA256: | EEF35E7887B5BC138355DBBCF009372BA9CE004A5A561B460B0C8855A0EC9340 |
| SSDEEP: | 3:N8hOAtRaAacEc29VzRAKNlE:20CEc23ZE |
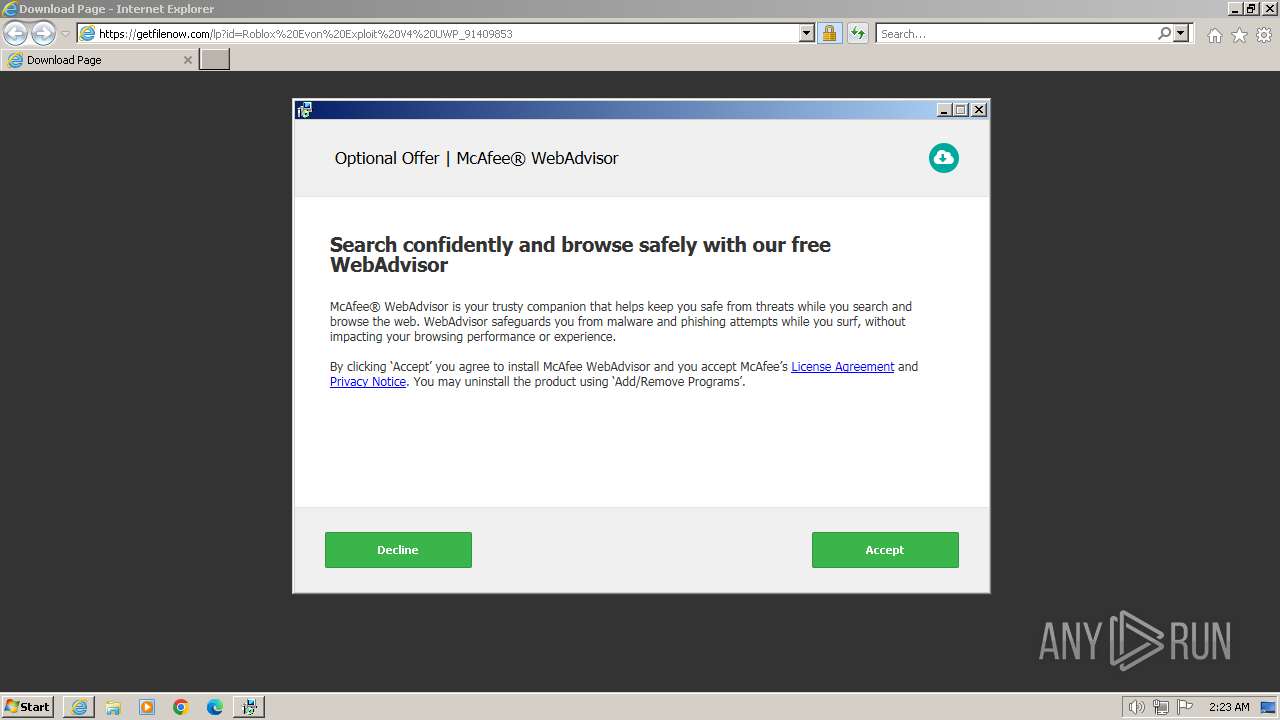
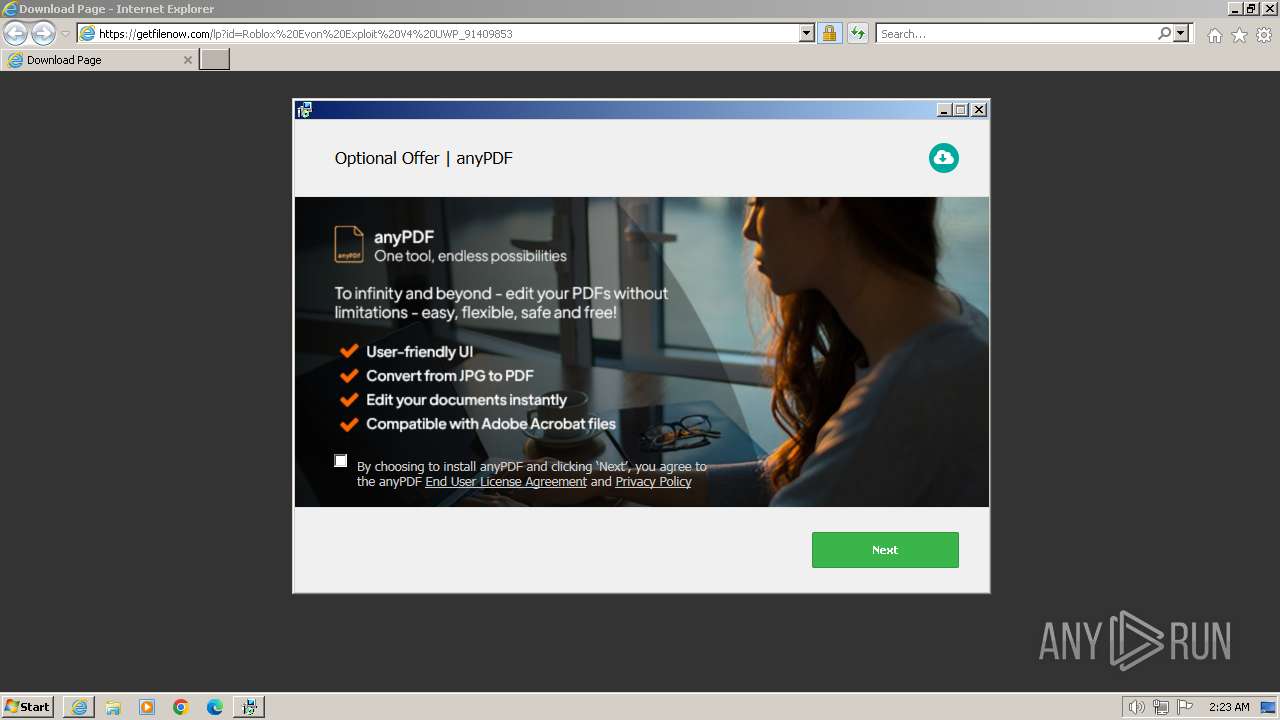
MALICIOUS
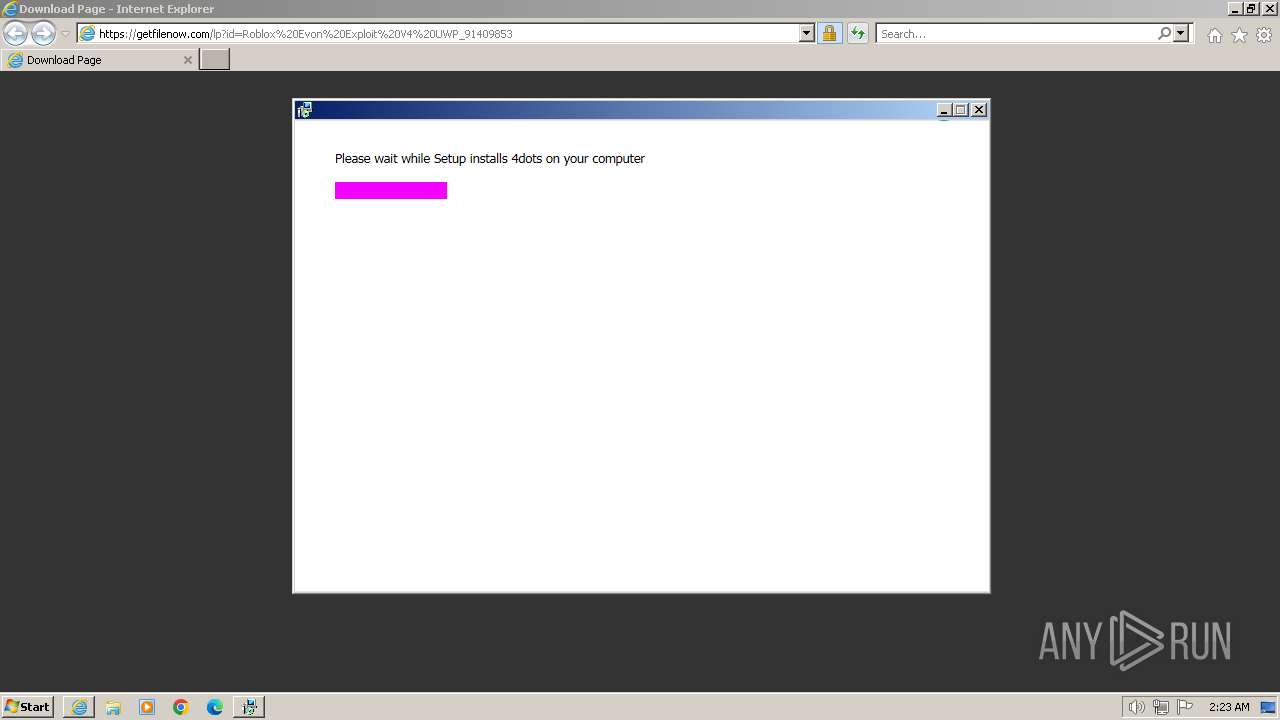
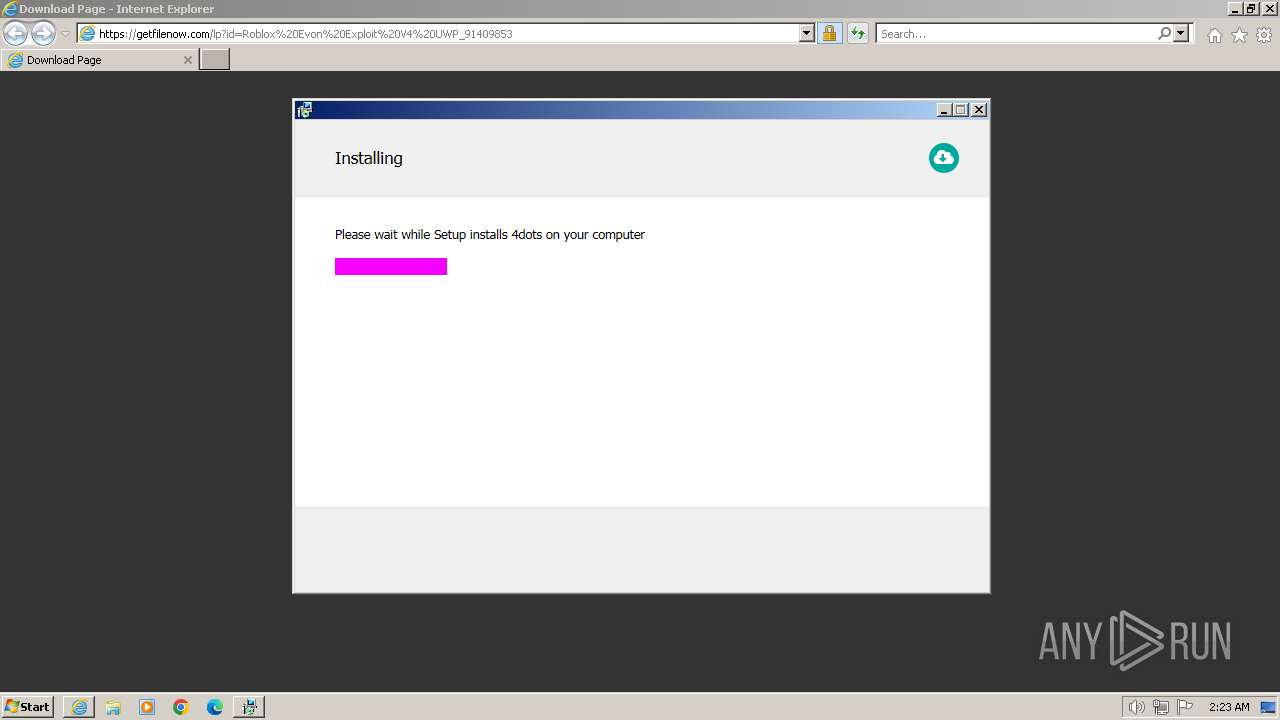
Drops the executable file immediately after the start
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
Actions looks like stealing of personal data
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
SUSPICIOUS
Reads the Internet Settings
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
Reads security settings of Internet Explorer
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
Checks Windows Trust Settings
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
Executable content was dropped or overwritten
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
Reads settings of System Certificates
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
The process drops C-runtime libraries
- setup91409853.exe (PID: 2432)
Process drops legitimate windows executable
- setup91409853.exe (PID: 2432)
Reads the Windows owner or organization settings
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
The process creates files with name similar to system file names
- setup91409853.exe (PID: 2432)
Adds/modifies Windows certificates
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
Executing commands from a ".bat" file
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Starts CMD.EXE for commands execution
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Get information on the list of running processes
- cmd.exe (PID: 3800)
- cmd.exe (PID: 992)
Searches for installed software
- setup91409853.exe (PID: 2432)
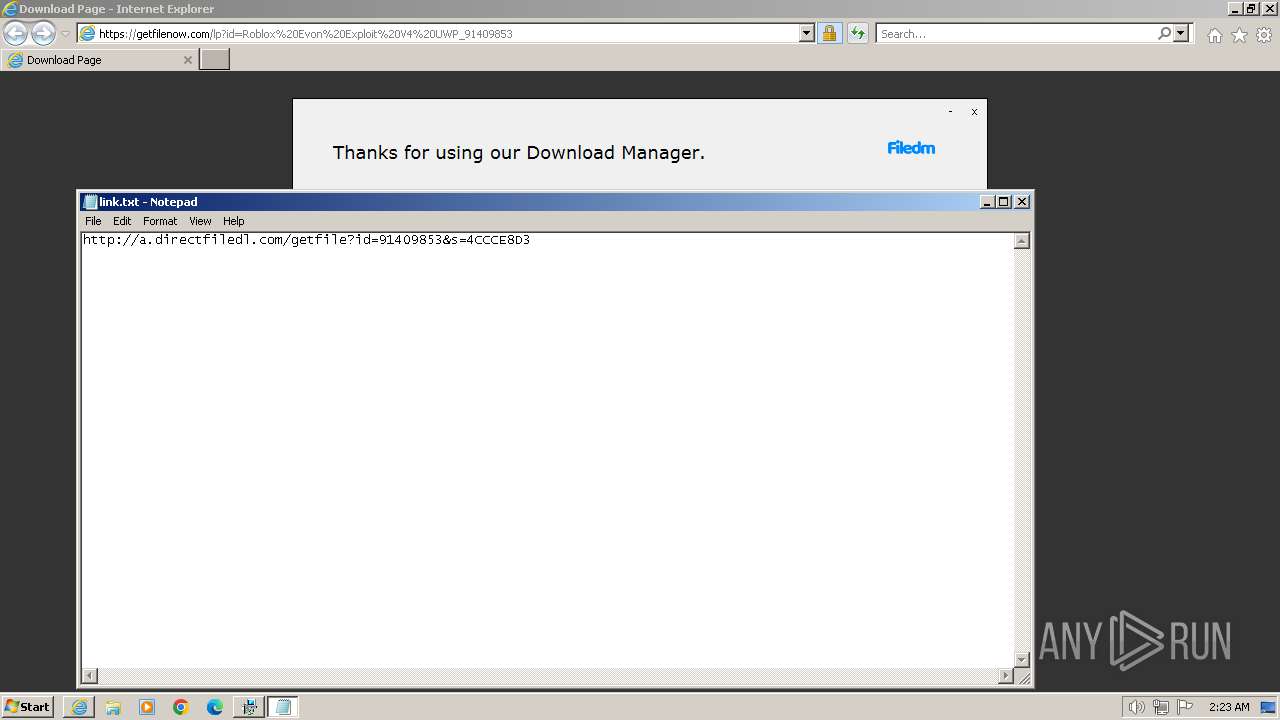
Start notepad (likely ransomware note)
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 992)
- cmd.exe (PID: 3800)
INFO
Application launched itself
- iexplore.exe (PID: 3668)
Checks supported languages
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
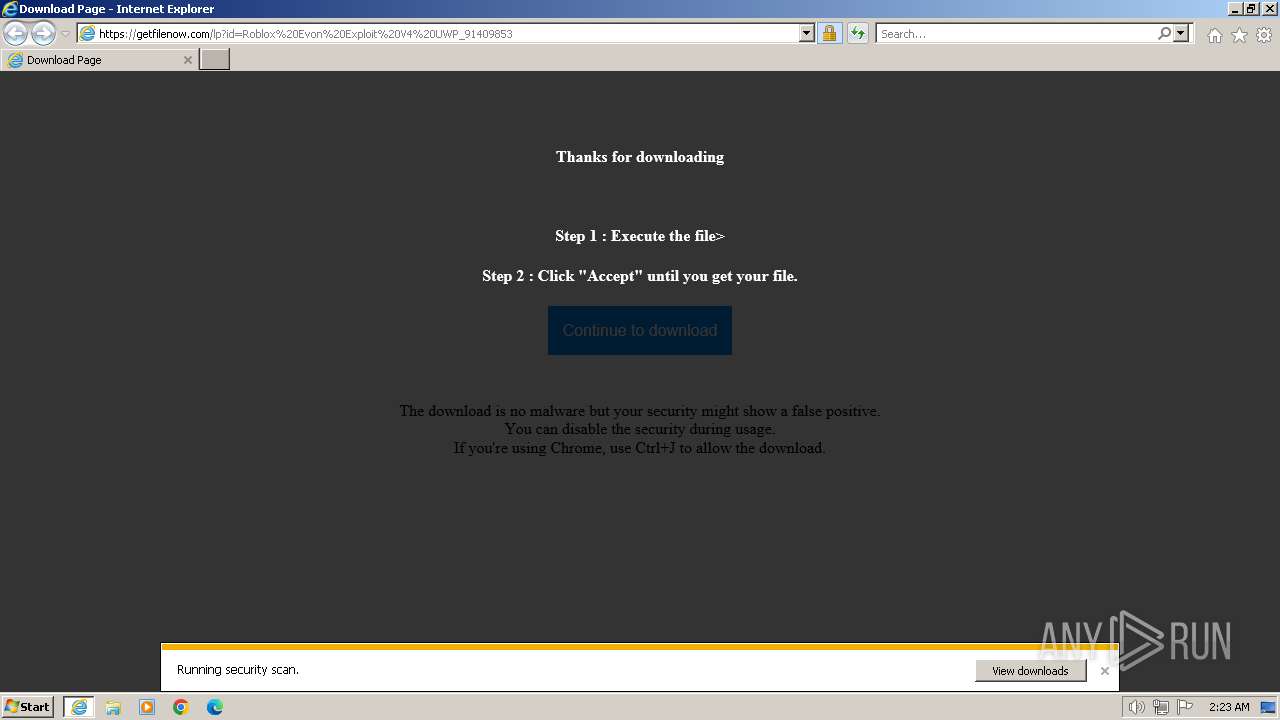
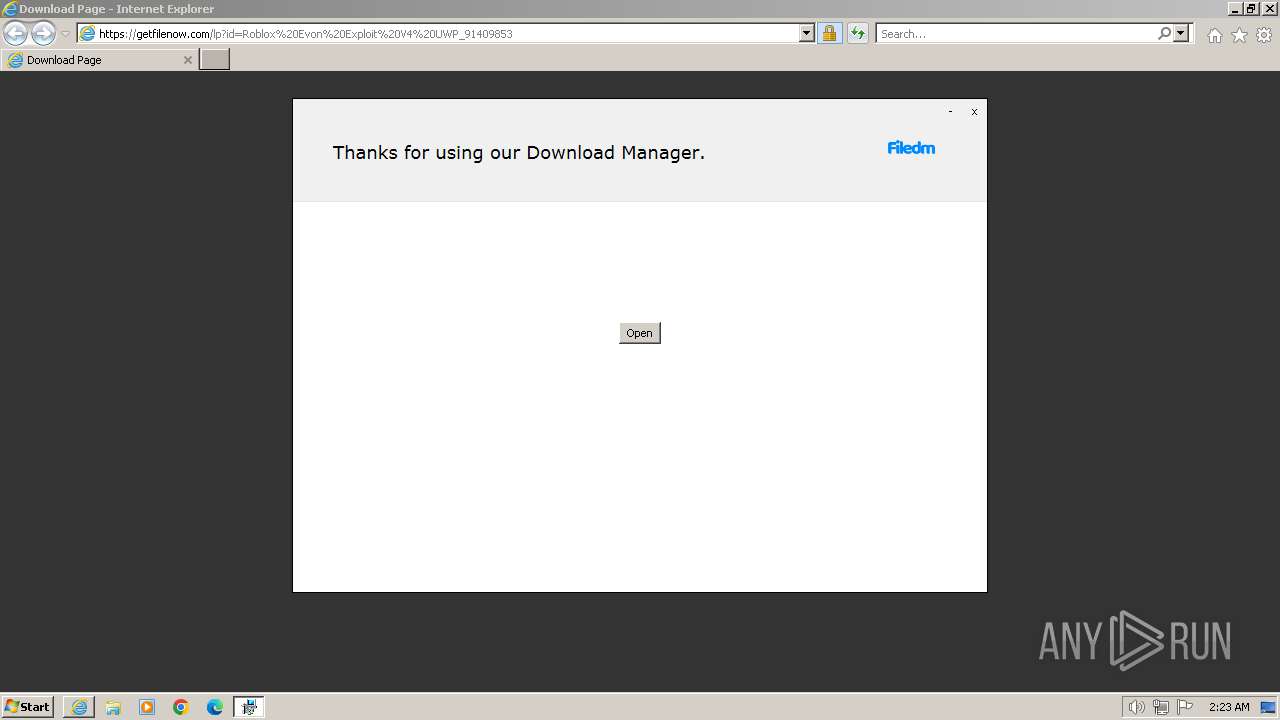
The process uses the downloaded file
- iexplore.exe (PID: 3668)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3668)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3668)
- iexplore.exe (PID: 3972)
Reads the computer name
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3668)
- iexplore.exe (PID: 3972)
Checks proxy server information
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
Reads the machine GUID from the registry
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
Reads the software policy settings
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Creates files or folders in the user directory
- Roblox Evon Exploit V4 UWP_91409853.exe (PID: 2168)
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Create files in a temporary directory
- setup91409853.exe (PID: 2432)
- setup91409853.exe (PID: 1556)
- OfferInstaller.exe (PID: 968)
Reads Environment values
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Reads product name
- setup91409853.exe (PID: 2432)
- OfferInstaller.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
19
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\OfferInstaller.exe" | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\OfferInstaller.exe | setup91409853.exe | ||||||||||||
User: admin Company: Adaware Integrity Level: HIGH Description: OfferInstaller Exit code: 0 Version: 7.14.2.0 Modules
| |||||||||||||||
| 992 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\H2OCleanup.bat"" | C:\Windows\System32\cmd.exe | — | OfferInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | timeout 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | timeout 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | C:\Users\admin\AppData\Local\setup91409853.exe hready | C:\Users\admin\AppData\Local\setup91409853.exe | — | Roblox Evon Exploit V4 UWP_91409853.exe | |||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1792 | find /I "2432" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | tasklist /FI "PID eq 968" /fo csv | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Roblox Evon Exploit V4 UWP_91409853.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Roblox Evon Exploit V4 UWP_91409853.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Download Manager Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 2396 | timeout 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | C:\Users\admin\AppData\Local\setup91409853.exe hhwnd=1180012 hreturntoinstaller hextras=id:e9d303610c1653d-DE-8jA2z | C:\Users\admin\AppData\Local\setup91409853.exe | Roblox Evon Exploit V4 UWP_91409853.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
47 486
Read events
47 144
Write events
272
Delete events
70
Modification events
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090778 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090778 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
26
Suspicious files
18
Text files
28
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF5D9.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF5DA.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:D4406E9626B2B3F701BF31C6CB74D048 | SHA256:1AE3E1561FE90721141829B39AC9D24065C01B8CFADE5FBAD5D23DCB00DA8452 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF5EC.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF5EB.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E70AD96A4F98240E51846AE7701CB214 | SHA256:77531CFD35FD02C7CEABEF3676534271255F43CDE13A8589D02C26534170E148 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:1ABD4B4E006C143D83D7A45F25C02E95 | SHA256:A900B7F3106B56B5AAFB109B788C7DCF169B3D8FCBAF4899A7E911BFA588E8DC | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:3232A772DD3AFFAF5B6EC27C81A66AC0 | SHA256:13FCD7EFC472791CD49014F73B22C75AB679143D3E2139FC1EC16F2070ADB167 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
37
DNS requests
27
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?927e0d673a39dd41 | unknown | — | — | unknown |
3972 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5b0325f31ae0f9b6 | unknown | compressed | 65.2 Kb | unknown |
3972 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b3372c99093cbf50 | unknown | compressed | 65.2 Kb | unknown |
3668 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a973ebecfe8ccbeb | unknown | — | — | unknown |
3668 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?956c1609c0d25c3f | unknown | — | — | unknown |
3972 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | binary | 299 b | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 312 b | unknown |
2168 | Roblox Evon Exploit V4 UWP_91409853.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2168 | Roblox Evon Exploit V4 UWP_91409853.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/s/gts1d4/tE2rewqz3dw/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICECdevec1BTW3CTOOyMl566o%3D | unknown | binary | 471 b | unknown |
2168 | Roblox Evon Exploit V4 UWP_91409853.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3972 | iexplore.exe | 188.114.97.3:443 | getfilenow.com | CLOUDFLARENET | NL | unknown |
3972 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3972 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3668 | iexplore.exe | 188.114.97.3:443 | getfilenow.com | CLOUDFLARENET | NL | unknown |
3668 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3668 | iexplore.exe | 92.123.104.31:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3668 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getfilenow.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.dlsft.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
Threats
7 ETPRO signatures available at the full report
Process | Message |
|---|---|
Roblox Evon Exploit V4 UWP_91409853.exe | Error: (undefined) has no property - value
|
Roblox Evon Exploit V4 UWP_91409853.exe | at initializeDynamicVariables (this://app/main.html(329))
|
Roblox Evon Exploit V4 UWP_91409853.exe | at getFileInfo.@285@39 (this://app/main.html(307))
|
Roblox Evon Exploit V4 UWP_91409853.exe | |
Roblox Evon Exploit V4 UWP_91409853.exe | |
setup91409853.exe | Error: File not found - sciterwrapper:console.tis
|
setup91409853.exe | at sciter:init-script.tis
|
setup91409853.exe | |
setup91409853.exe | |
setup91409853.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|